Powerpoint Templates and Google slides for Phishing
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Methods To Identify Crypto Phishing Scams Guide For Blockchain BCT SS V
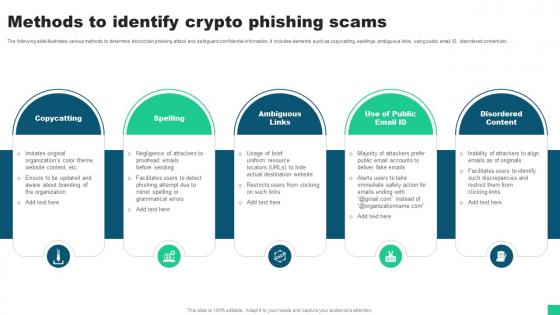
Methods To Identify Crypto Phishing Scams Guide For Blockchain BCT SS VThe following slide illustrates various methods to determine blockchain phishing attack and safeguard confidential information. It includes elements such as copycatting, spellings, ambiguous links, using public email ID, disordered content etc. Introducing Methods To Identify Crypto Phishing Scams Guide For Blockchain BCT SS V to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Copycatting, Spelling, Ambiguous Links using this template. Grab it now to reap its full benefits.
-
 Overview Of Phishing Attack In Blockchain Technology Guide For Blockchain BCT SS V
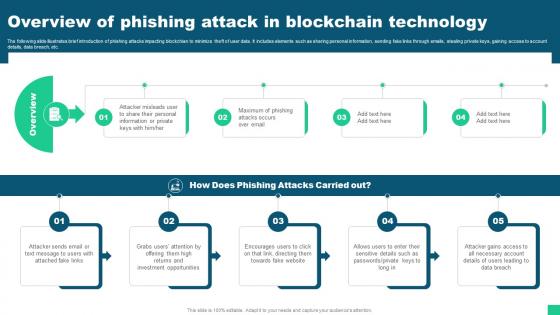
Overview Of Phishing Attack In Blockchain Technology Guide For Blockchain BCT SS VThe following slide illustrates brief introduction of phishing attacks impacting blockchian to minimize theft of user data. It includes elements such as sharing personal information, sending fake links through emails, stealing private keys, gaining access to account details, data breach, etc. Introducing Overview Of Phishing Attack In Blockchain Technology Guide For Blockchain BCT SS V to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Overview, Phishing Attacks Carried, Investment Opportunities using this template. Grab it now to reap its full benefits.
-
 Ways To Prevent Crypto Phishing And Sensitive Information Leakage Guide For Blockchain BCT SS V
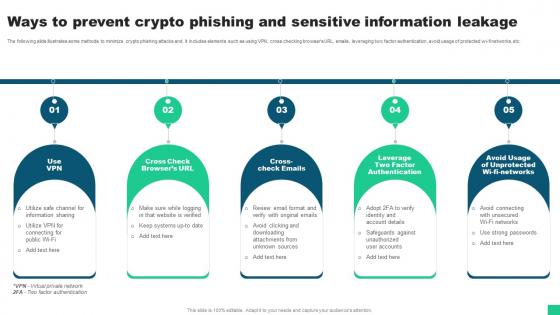
Ways To Prevent Crypto Phishing And Sensitive Information Leakage Guide For Blockchain BCT SS VThe following slide illustrates some methods to minimize crypto phishing attacks and. It includes elements such as using VPN, cross checking browsers URL, emails, leveraging two factor authentication, avoid usage of protected wi-fi networks, etc. Introducing Ways To Prevent Crypto Phishing And Sensitive Information Leakage Guide For Blockchain BCT SS V to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Cross Check Emails, Factor Authentication, Unprotected Wi Fi Networks using this template. Grab it now to reap its full benefits.
-
 Ethical Hacking And Network Security Security Measures To Prevent Phishing Attacks
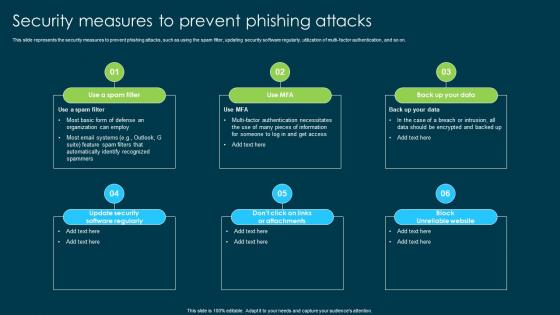
Ethical Hacking And Network Security Security Measures To Prevent Phishing AttacksThis slide represents the security measures to prevent phishing attacks, such as using the spam filter, updating security software regularly, utilization of multi-factor authentication, and so on. Introducing Ethical Hacking And Network Security Security Measures To Prevent Phishing Attacks to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Prevent Phishing Attacks, Spam Filter, Updating Security Software Regularly, Utilization Of Multi Factor Authentication, using this template. Grab it now to reap its full benefits.
-
 Ethical Hacking And Network Security Types Of Phishing Attack
Ethical Hacking And Network Security Types Of Phishing AttackThis slide represents the types of phishing attacks such a spear-phishing, clone phishing, whaling, BEC, vishing, and snowshoeing phishing. Increase audience engagement and knowledge by dispensing information using Ethical Hacking And Network Security Types Of Phishing Attack. This template helps you present information on three stages. You can also present information on Business Email Compromise, Clone Phishing, Snowshoeing, Phishing Attack using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
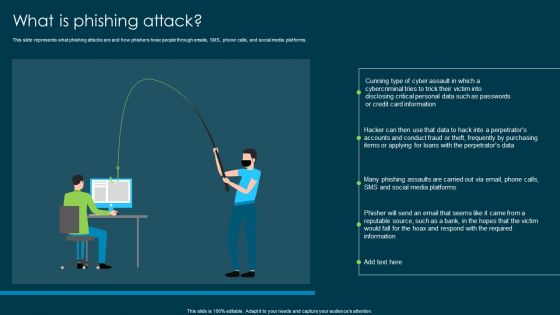 Ethical Hacking And Network Security What Is Phishing Attack
Ethical Hacking And Network Security What Is Phishing AttackThis slide represents what phishing attacks are and how phishers hoax people through emails, SMS, phone calls, and social media platforms. Introducing Ethical Hacking And Network Security What Is Phishing Attack to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Phishing Attacks, Phishers Hoax, Social Media Platforms, System Hacking, Corporate Or Personal Data, using this template. Grab it now to reap its full benefits.
-
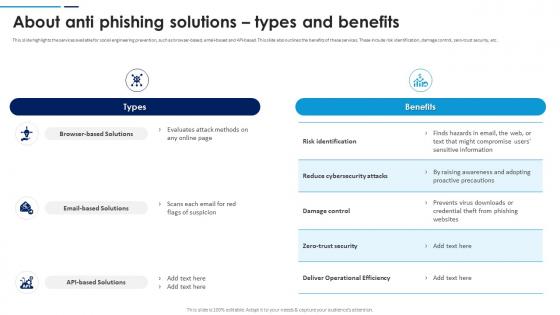 Social Engineering Attacks Prevention About Anti Phishing Solutions Types And Benefits
Social Engineering Attacks Prevention About Anti Phishing Solutions Types And BenefitsThis slide highlights the services available for social engineering prevention, such as browser-based, email-based and API-based. This slide also outlines the benefits of these services. These include risk identification, damage control, zero-trust security, etc. Present the topic in a bit more detail with this Social Engineering Attacks Prevention About Anti Phishing Solutions Types And Benefits. Use it as a tool for discussion and navigation on Reduce Cybersecurity Attacks, Zero Trust Security, Deliver Operational Efficiency. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
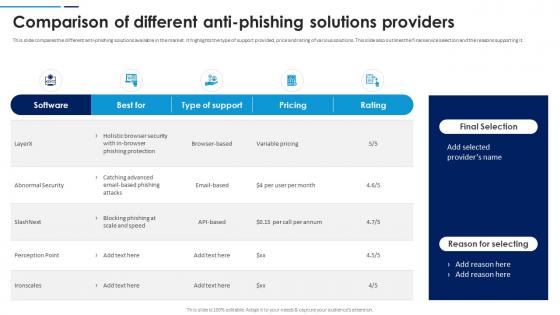 Social Engineering Attacks Prevention Comparison Of Different Anti-Phishing Solutions Providers
Social Engineering Attacks Prevention Comparison Of Different Anti-Phishing Solutions ProvidersThis slide compares the different anti-phishing solutions available in the market. It highlights the type of support provided, price and rating of various solutions. This slide also outlines the final service selection and the reasons supporting it. Deliver an outstanding presentation on the topic using this Social Engineering Attacks Prevention Comparison Of Different Anti-Phishing Solutions Providers. Dispense information and present a thorough explanation of Anti Phishing Solutions, Final Service Selection, Reasons Supporting, Abnormal Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
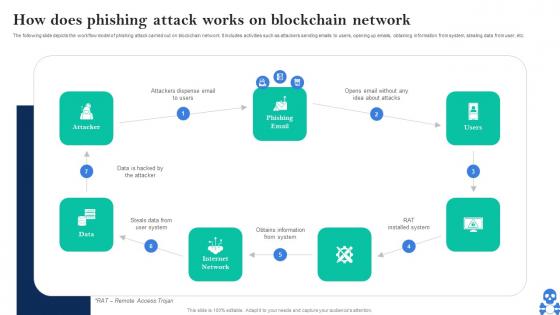 Cyber Threats In Blockchain How Does Phishing Attack Works On Blockchain Network BCT SS V
Cyber Threats In Blockchain How Does Phishing Attack Works On Blockchain Network BCT SS VThe following slide depicts the workflow model of phishing attack carried out on blockchain network. It includes activities such as attackers sending emails to users, opening up emails, obtaining information from system, stealing data from user, etc. Increase audience engagement and knowledge by dispensing information using Cyber Threats In Blockchain How Does Phishing Attack Works On Blockchain Network BCT SS V This template helps you present information on Seven stages. You can also present information on Steals Data From User System, Obtains Information From System using this PPT design. This layout is completely editable so personaize it now
-
 Cyber Threats In Blockchain Methods To Identify Crypto Phishing Scams BCT SS V
Cyber Threats In Blockchain Methods To Identify Crypto Phishing Scams BCT SS VThe following slide illustrates various methods to determine blockchain phishing attack and safeguard confidential information. It includes elements such as copycatting, spellings, ambiguous links, using public email ID, disordered content etc. Increase audience engagement and knowledge by dispensing information using Cyber Threats In Blockchain Methods To Identify Crypto Phishing Scams BCT SS V This template helps you present information on Five stages. You can also present information on Copycatting, Spelling, Ambiguous Links using this PPT design. This layout is completely editable so personaize it now
-
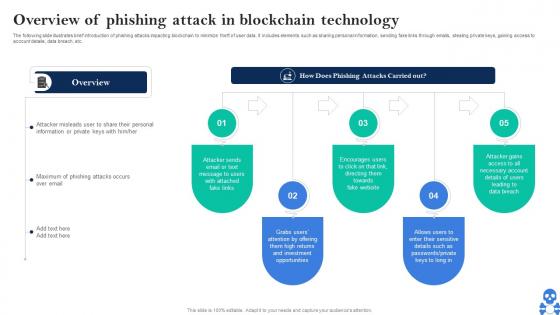 Cyber Threats In Blockchain Overview Of Phishing Attack In Blockchain Technology BCT SS V
Cyber Threats In Blockchain Overview Of Phishing Attack In Blockchain Technology BCT SS VThe following slide illustrates brief introduction of phishing attacks impacting blockchain to minimize theft of user data. It includes elements such as sharing personal information, sending fake links through emails, stealing private keys, gaining access to account details, data breach, etc. Introducing Cyber Threats In Blockchain Overview Of Phishing Attack In Blockchain Technology BCT SS V to increase your presentation threshold. Encompassed with Five stages, this template is a great option to educate and entice your audience. Dispence information on Opportunities, Fake Website, Data Breach using this template. Grab it now to reap its full benefits.
-
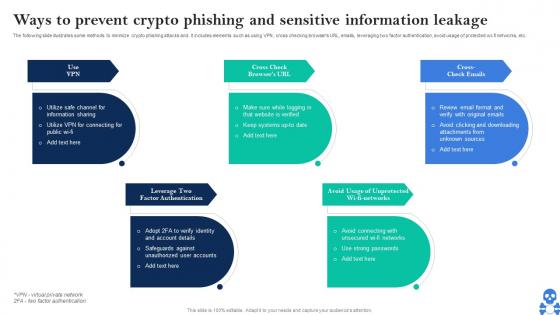 Cyber Threats In Blockchain Ways To Prevent Crypto Phishing And Sensitive Information Leakage BCT SS V
Cyber Threats In Blockchain Ways To Prevent Crypto Phishing And Sensitive Information Leakage BCT SS VThe following slide illustrates some methods to minimize crypto phishing attacks and. it includes elements such as using VPN, cross checking browsers URL, emails, leveraging two factor authentication, avoid usage of protected wi-fi networks, etc. Introducing Cyber Threats In Blockchain Ways To Prevent Crypto Phishing And Sensitive Information Leakage BCT SS V to increase your presentation threshold. Encompassed with Five stages, this template is a great option to educate and entice your audience. Dispence information on Use VPN, Factor Authentication, Avoid Usage Of Unprotected using this template. Grab it now to reap its full benefits.
-
 E Commerce Fraud Icon Using Phishing Attacks
E Commerce Fraud Icon Using Phishing AttacksPresenting our set of slides with E Commerce Fraud Icon Using Phishing Attacks. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on E Commerce Fraud, Using Phishing Attacks.
-
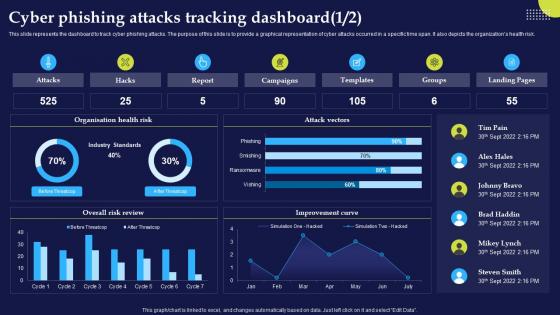 Cyber Phishing Attacks Tracking Dashboard Phishing Attacks And Strategies
Cyber Phishing Attacks Tracking Dashboard Phishing Attacks And StrategiesThis slide represents the dashboard to track cyber phishing attacks. The purpose of this slide is to provide a graphical representation of cyber attacks occurred in a specific time span. It also depicts the organizations health risk.Deliver an outstanding presentation on the topic using this Cyber Phishing Attacks Tracking Dashboard Phishing Attacks And Strategies. Dispense information and present a thorough explanation of Cyber Phishing Attacks, Tracking Dashboard using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
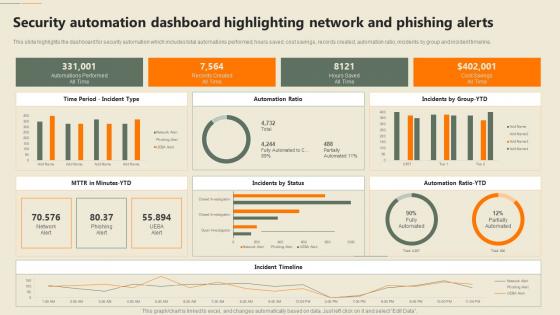
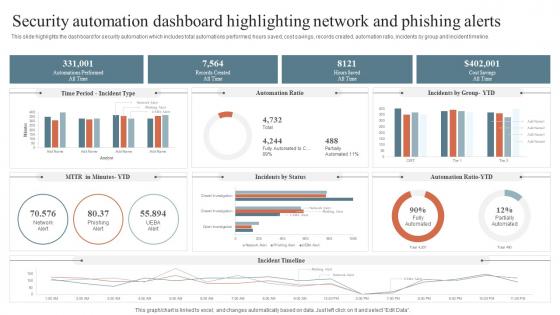 Security Automation Dashboard Highlighting Network And Phishing Alerts Security Orchestration Automation
Security Automation Dashboard Highlighting Network And Phishing Alerts Security Orchestration AutomationThis slide highlights the dashboard for security automation which includes total automations performed, hours saved, cost savings, records created, automation ratio, incidents by group and incident timeline. Deliver an outstanding presentation on the topic using this Security Automation Dashboard Highlighting Network And Phishing Alerts Security Orchestration Automation. Dispense information and present a thorough explanation of Security Automation, Dashboard Highlighting, Network And Phishing Alerts using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
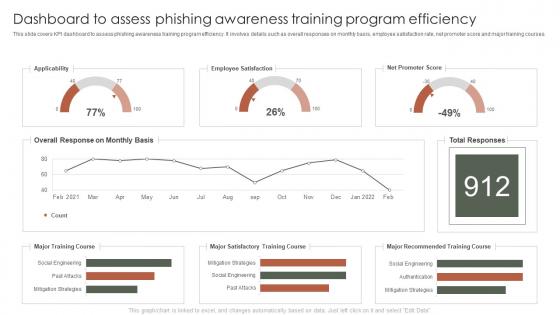 Dashboard To Assess Phishing Awareness Training Program Efficiency
Dashboard To Assess Phishing Awareness Training Program EfficiencyThis slide covers KPI dashboard to assess phishing awareness training program efficiency. It involves details such as overall responses on monthly basis, employee satisfaction rate, net promoter score and major training courses. Introducing our Dashboard To Assess Phishing Awareness Training Program Efficiency set of slides. The topics discussed in these slides are Applicability, Employee Satisfaction, Net Promoter Score. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Phishing Incident Management Dashboard For Effective Awareness Training
Phishing Incident Management Dashboard For Effective Awareness TrainingThis slide covers phishing incident management dashboard for effective awareness training. It involves details such as average resolution time, new incidents, incident status, resolved vs unresolved incidents and created vs closed incidents. Introducing our Phishing Incident Management Dashboard For Effective Awareness Training set of slides. The topics discussed in these slides are Phishing, Incident Management, Dashboard, Effective Awareness Training. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 F652 Security Automation In Information Technology Security Automation Dashboard Highlighting Phishing
F652 Security Automation In Information Technology Security Automation Dashboard Highlighting PhishingThis slide highlights the dashboard for security automation which includes total automations performed, hours saved, cost savings, records created, automation ratio, incidents by group and incident timeline. Present the topic in a bit more detail with this F652 Security Automation In Information Technology Security Automation Dashboard Highlighting Phishing. Use it as a tool for discussion and navigation on Automation, Dashboard, Phishing Alerts. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
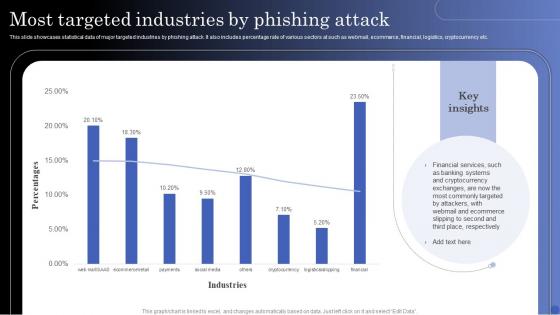 Most Targeted Industries By Phishing Attack
Most Targeted Industries By Phishing AttackThis slide showcases statistical data of major targeted industries by phishing attack. It also includes percentage rate of various sectors at such as webmail, ecommerce, financial, logistics, cryptocurrency etc. Introducing our Most Targeted Industries By Phishing Attack set of slides. The topics discussed in these slides are Cryptocurrency, Banking Systems, Financial Services. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Ultimate Guide For Blockchain Various Types Of Crypto Phishing Attacks BCT SS
Ultimate Guide For Blockchain Various Types Of Crypto Phishing Attacks BCT SSIntroducing Ultimate Guide For Blockchain Various Types Of Crypto Phishing Attacks BCT SS to increase your presentation threshold. Encompassed with Three stages, this template is a great option to educate and entice your audience. Dispence information on Spear Phishing, Whaling Phishing using this template. Grab it now to reap its full benefits.
-
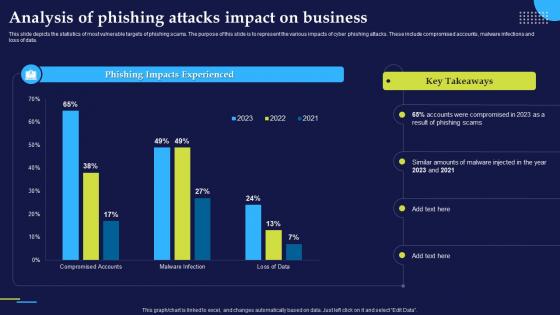 Analysis Of Phishing Attacks Impact On Business Phishing Attacks And Strategies
Analysis Of Phishing Attacks Impact On Business Phishing Attacks And StrategiesThis slide depicts the statistics of most vulnerable targets of phishing scams. The purpose of this slide is to represent the various impacts of cyber phishing attacks. These include compromised accounts, malware infections and loss of data.Present the topic in a bit more detail with this Analysis Of Phishing Attacks Impact On Business Phishing Attacks And Strategies. Use it as a tool for discussion and navigation on Phishing Impacts Experienced, Amounts Malware, Phishing Scams. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Impact Of Phishing Cyber Scams On Phishing Attacks And Strategies
Impact Of Phishing Cyber Scams On Phishing Attacks And StrategiesThis slide talks about the damage caused by phishing attacks. The purpose of this slide is to explain the impact of phishing scams on organizations. The key points included are information loss, damaged credibility, direct financial loss and productivity loss.Increase audience engagement and knowledge by dispensing information using Impact Of Phishing Cyber Scams On Phishing Attacks And Strategies. This template helps you present information on six stages. You can also present information on Businesses Incur Reputational, Phishing Assault, Maintenance Reconfiguration using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Table Of Contents Phishing Attacks And Strategies To Mitigate Them
Table Of Contents Phishing Attacks And Strategies To Mitigate ThemDeliver an outstanding presentation on the topic using this Table Of Contents Phishing Attacks And Strategies To Mitigate Them. Dispense information and present a thorough explanation of Phishing Attacks Overview, Types Phishing, Attacks Prevention using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
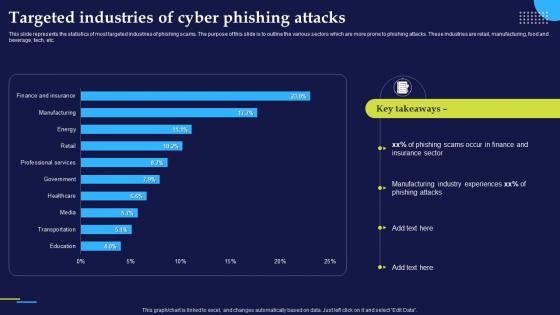 Targeted Industries Of Cyber Phishing Attacks Phishing Attacks And Strategies
Targeted Industries Of Cyber Phishing Attacks Phishing Attacks And StrategiesThis slide represents the statistics of most targeted industries of phishing scams. The purpose of this slide is to outline the various sectors which are more prone to phishing attacks. These industries are retail, manufacturing, food and beverage, tech, etc.Present the topic in a bit more detail with this Targeted Industries Of Cyber Phishing Attacks Phishing Attacks And Strategies. Use it as a tool for discussion and navigation on Phishing Scams, Manufacturing Industry, Phishing Attacks. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Vishing Cyber Scams In Different Businesses Phishing Attacks And Strategies
Vishing Cyber Scams In Different Businesses Phishing Attacks And StrategiesThis slide demonstrates the various types of vishing scams. The purpose of this slide is to illustrate the ways in which attackers conduct scams in different businesses using vishing technique. These are banking vishing and internal revenue service vishing.Present the topic in a bit more detail with this Vishing Cyber Scams In Different Businesses Phishing Attacks And Strategies. Use it as a tool for discussion and navigation on Internal Revenue, Remote Application, Vishing Example. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Phishing Security Training Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Phishing Security Training Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Phishing security training colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Phishing Security Training Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Phishing Security Training Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Phishing security training monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
 Phishing Training And Employee Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Phishing Training And Employee Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Phishing training and employee colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Phishing Training And Employee Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Phishing Training And Employee Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Phishing training and employee monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
 Phishing Training Degree Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Phishing Training Degree Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Phishing training degree colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Phishing Training Degree Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Phishing Training Degree Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Phishing training degree monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
 Insider Threat Icon For Financial Information Phishing
Insider Threat Icon For Financial Information PhishingIntroducing our premium set of slides with Insider Threat Icon For Financial Information Phishing. Elucidate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Insider Threat Icon, Financial Information Phishing. So download instantly and tailor it with your information.
-
 Cyber Phishing On Laptop Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Cyber Phishing On Laptop Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Cyber phishing on laptop colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Cyber Phishing On Laptop Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Cyber Phishing On Laptop Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Cyber phishing on laptop monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
 Email Phishing Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Email Phishing Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Email phishing colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Email Phishing Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Email Phishing Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Email phishing monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
 Information Phishing Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Information Phishing Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Information phishing colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Information Phishing Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Information Phishing Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Information phishing monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
 5 Key Practices To Prevent Cyber Phishing Attack
5 Key Practices To Prevent Cyber Phishing AttackMentioned slide showcases best practices which can be implemented to prevent cyber phishing. The practices are recognizing hyperlinks attached in an email, backup system copies, secure robust HTTPs connections, installing a firewall and using anti spam tools. Presenting our set of slides with name 5 Key Practices To Prevent Cyber Phishing Attack. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Recognize Hyperlinks Attached In An Email, Secure HTTP Connections, Backup Copy.
-
 7 Step Model Of Spear Phishing Attack
7 Step Model Of Spear Phishing AttackMentioned slide showcases multistep model of cyber phishing attack. The model include points such as attacker sends the email, user opens the email, target system exploitation, installation of RAT etc. Introducing our premium set of slides with name 7 Step Model Of Spear Phishing Attack. Ellicudate the seven stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Attacker, Phishing Email, Targeted Users. So download instantly and tailor it with your information.
-
 Cyber Phishing Attack Icon To Steal Confidential Data
Cyber Phishing Attack Icon To Steal Confidential DataPresenting our well structured Cyber Phishing Attack Icon To Steal Confidential Data. The topics discussed in this slide are Cyber Phishing Attack Icon To Steal Confidential Data. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
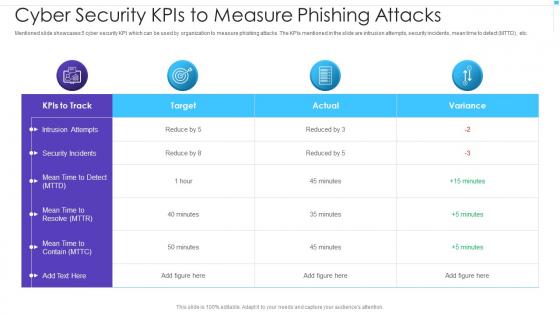 Cyber Security Kpis To Measure Phishing Attacks
Cyber Security Kpis To Measure Phishing AttacksMentioned slide showcases 5 cyber security KPI which can be used by organization to measure phishing attacks. The KPIs mentioned in the slide are intrusion attempts, security incidents, mean time to detect MTTD, etc. Presenting our well structured Cyber Security Kpis To Measure Phishing Attacks. The topics discussed in this slide are Intrusion Attempts, Security Incidents, Mean Time to Resolve. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Icon Of Hacker Launching Cyber Phishing Attack
Icon Of Hacker Launching Cyber Phishing AttackPresenting our set of slides with name Icon Of Hacker Launching Cyber Phishing Attack. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Icon Of Hacker Launching Cyber Phishing Attack.
-
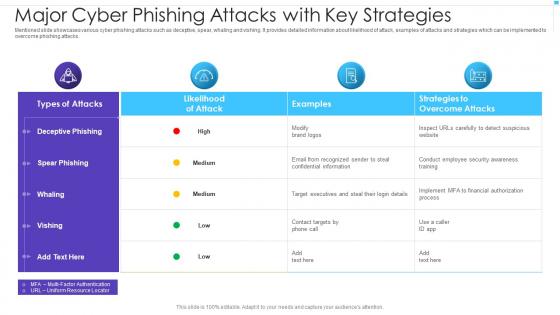 Major Cyber Phishing Attacks With Key Strategies
Major Cyber Phishing Attacks With Key StrategiesMentioned slide showcases various cyber phishing attacks such as deceptive, spear, whaling and vishing. It provides detailed information about likelihood of attack, examples of attacks and strategies which can be implemented to overcome phishing attacks. Introducing our Major Cyber Phishing Attacks With Key Strategies set of slides. The topics discussed in these slides are Spear Phishing, Deceptive Phishing, Whaling. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Phishing Assessment And Cyber Security Training
Phishing Assessment And Cyber Security TrainingMentioned slide showcases phishing awareness training program used to prevent cyber attacks. It provides detailed information about deploying phishing program within the organization, analyzing and preparing reports, developing training and education etc. Introducing our premium set of slides with name Phishing Assessment And Cyber Security Training. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Deploy Phishing Program, Develop Training And Education, Analyze And Report Findings. So download instantly and tailor it with your information.
-
 Phishing Cyber Terrorism Tool Cyber Terrorism Attacks
Phishing Cyber Terrorism Tool Cyber Terrorism AttacksThis slide describes phishing in which an attacker tricks a victim to open an email, provide card credentials or any sensitive information. Increase audience engagement and knowledge by dispensing information using Phishing Cyber Terrorism Tool Cyber Terrorism Attacks. This template helps you present information on five stages. You can also present information on Obtain, Sensitive, Information, Trustworthy, Convinces using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
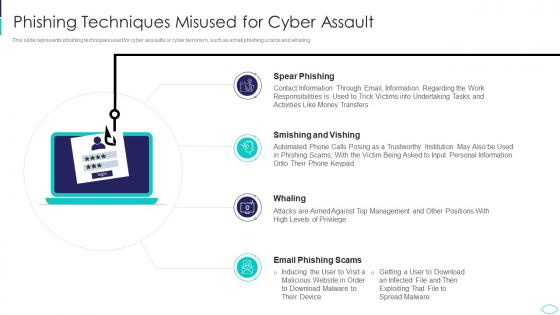 Phishing Techniques Misused For Cyber Assault Cyber Terrorism Attacks
Phishing Techniques Misused For Cyber Assault Cyber Terrorism AttacksThis slide represents phishing techniques used for cyber assaults or cyber terrorism, such as email phishing scams and whaling. Introducing Phishing Techniques Misused For Cyber Assault Cyber Terrorism Attacks to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Phishing Techniques Misused For Cyber Assault, using this template. Grab it now to reap its full benefits.
-
 Security measures to prevent phishing attacks ppt powerpoint presentation pictures display
Security measures to prevent phishing attacks ppt powerpoint presentation pictures displayThis slide represents the security measures to prevent phishing attacks, such as using the spam filter, updating security software regularly, utilization of multi factor authentication, and so on. Increase audience engagement and knowledge by dispensing information using Security Measures To Prevent Phishing Attacks Ppt Powerpoint Presentation Pictures Display. This template helps you present information on six stages. You can also present information on Security Measures To Prevent Phishing Attacks using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Types of phishing attack ppt powerpoint presentation styles format ideas
Types of phishing attack ppt powerpoint presentation styles format ideasThis slide represents the types of phishing attacks such a spear phishing, clone phishing, whaling, BEC, vishing, and snowshoeing phishing. Increase audience engagement and knowledge by dispensing information using Types Of Phishing Attack Ppt Powerpoint Presentation Styles Format Ideas. This template helps you present information on three stages. You can also present information on Spear Phishing, Whaling, Clone Phishing using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 What is phishing attack ppt powerpoint presentation model graphics pictures
What is phishing attack ppt powerpoint presentation model graphics picturesThis slide represents what phishing attacks are and how phishers hoax people through emails, SMS, phone calls, and social media platforms. Present the topic in a bit more detail with this What Is Phishing Attack Ppt Powerpoint Presentation Model Graphics Pictures. Use it as a tool for discussion and navigation on Phishing Attack. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyberterrorism it phishing cyber terrorism tool ppt slides graphics
Cyberterrorism it phishing cyber terrorism tool ppt slides graphicsThis slide describes phishing in which an attacker tricks a victim to open an email, provide card credentials or any sensitive information. Introducing Cyberterrorism IT Phishing Cyber Terrorism Tool Ppt Slides Graphics to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Obtain Sensitive Information, Credit Card Details, Business, Consumer Confidence, using this template. Grab it now to reap its full benefits.
-
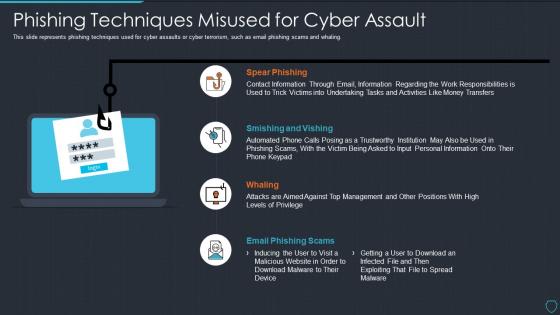 Cyberterrorism it phishing techniques misused for cyber assault
Cyberterrorism it phishing techniques misused for cyber assaultThis slide represents phishing techniques used for cyber assaults or cyber terrorism, such as email phishing scams and whaling. Increase audience engagement and knowledge by dispensing information using Cyberterrorism IT Phishing Techniques Misused For Cyber Assault. This template helps you present information on four stages. You can also present information on Spear Phishing, Smishing And Vishing, Whaling, Email Phishing Scams using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Phishing Emails Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Phishing Emails Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Phishing emails colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Phishing Emails Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Phishing Emails Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Phishing emails monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
 Report Phishing In Powerpoint And Google Slides Cpb
Report Phishing In Powerpoint And Google Slides CpbPresenting Report Phishing In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase five stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Report Phishing. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Phishing Testing Training In Powerpoint And Google Slides Cpb
Phishing Testing Training In Powerpoint And Google Slides CpbPresenting Phishing Testing Training In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Phishing Testing Training. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Social Engineering Phishing Attacks Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Social Engineering Phishing Attacks Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Social engineering phishing attacks colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Social Engineering Phishing Attacks Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Social Engineering Phishing Attacks Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Social engineering phishing attacks monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
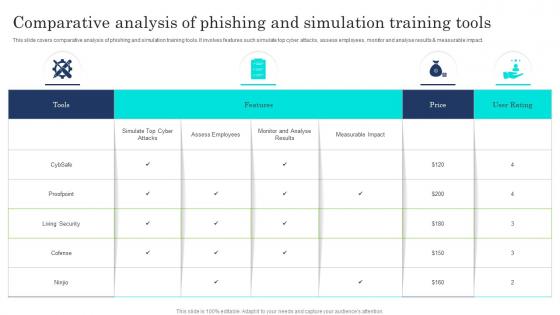 Comparative Analysis Of Phishing And Simulation Training Tools
Comparative Analysis Of Phishing And Simulation Training ToolsThis slide covers comparative analysis of phishing and simulation training tools. It involves features such simulate top cyber attacks, assess employees, monitor and analyse results and measurable impact. Introducing our Comparative Analysis Of Phishing And Simulation Training Tools set of slides. The topics discussed in these slides are Features, Price, User Rating, Tools. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Best Practices For Phishing Awareness Training Program
Best Practices For Phishing Awareness Training ProgramThis slide covers best practices for phishing awareness training plan for successful implementation. It involves best practices such as getting into compliance, including everyone, establishing basics and making training engaging and entertaining. Presenting our set of slides with name Best Practices For Phishing Awareness Training Program. This exhibits information on four stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Including Everyone, Getting Into Compliance, Establishing Basics, Training Engaging, Entertaining.



