Powerpoint Templates and Google slides for Secure Programming
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
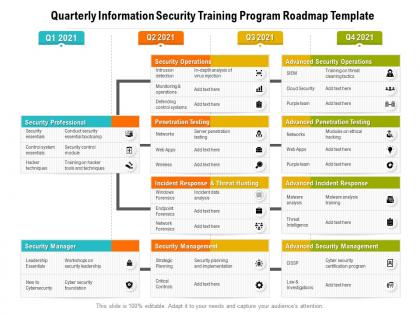 Quarterly information security training program roadmap template
Quarterly information security training program roadmap templatePresenting Quarterly Information Security Training Program Roadmap Template PowerPoint slide which is percent editable. You can change the color, font size, font type, and shapes of this PPT layout according to your needs. This PPT template is compatible with Google Slides and is available in both 4,3 and 16,9 aspect ratios. This ready to use PowerPoint presentation can be downloaded in various formats like PDF, JPG, and PNG.
-
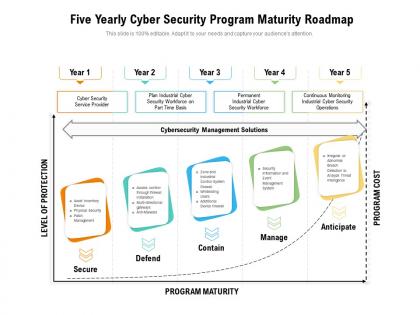 Five yearly cyber security program maturity roadmap
Five yearly cyber security program maturity roadmapPresenting Five Yearly Cyber Security Program Maturity Roadmap PowerPoint slide which is percent editable. You can change the color, font size, font type, and shapes of this PPT layout according to your needs. This PPT template is compatible with Google Slides and is available in both 4,3 and 16,9 aspect ratios. This ready to use PowerPoint presentation can be downloaded in various formats like PDF, JPG, and PNG.
-
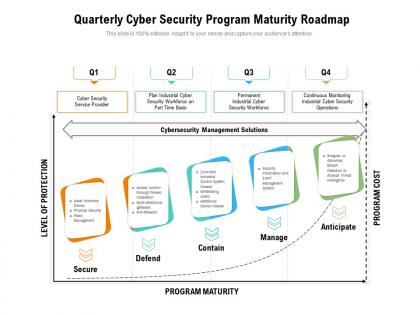 Quarterly cyber security program maturity roadmap
Quarterly cyber security program maturity roadmapPresenting Quarterly Cyber Security Program Maturity Roadmap PowerPoint Template. This PPT presentation is Google Slides compatible hence it is easily accessible. You can download and save this PowerPoint layout in different formats like PDF, PNG, and JPG. This PPT theme is available in both 4,3 and 16,9 aspect ratios. This PowerPoint template is customizable so you can modify the font size, font type, color, and shapes as per your requirements.
-
 Best Practices For Information Security Program
Best Practices For Information Security ProgramThis slide shows information security program best practices tofocus on conducting comprehensive scans andassessing vulnerabilities .It further includes practices such as conduct comprehensive scans , continually assess vulnerabilities etc. Presenting our set of slides with Best Practices For Information Security Program This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Conduct Comprehensive Scans, Continually Assess Vulnerabilities, Accelerate Processes
-
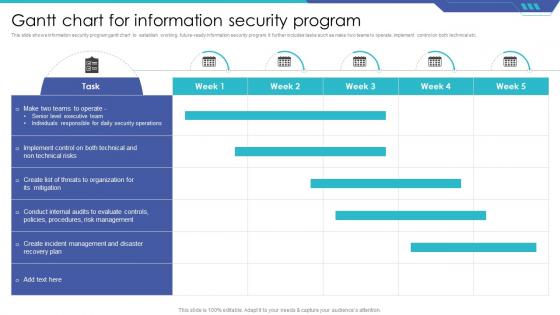 Gantt Chart For Information Security Program
Gantt Chart For Information Security ProgramThis slide shows information security program gantt chart to establish working, future-ready information security program. It further includes tasks such as make two teams to operate ,implement control on both technical etc. Introducing our Gantt Chart For Information Security Program set of slides. The topics discussed in these slides are This slide shows information security program gantt chart to establish working, future-ready information security program. It further includes tasks such as make two teams to operate ,implement control on both technical etc.. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
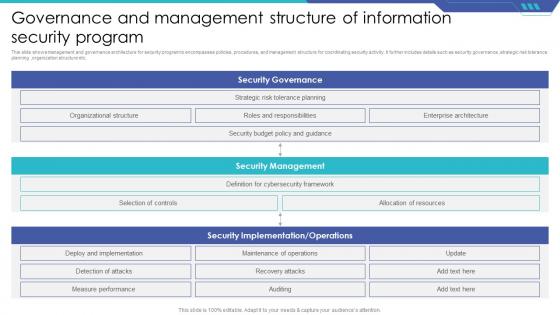 Governance And Management Structure Of Information Security Program
Governance And Management Structure Of Information Security ProgramThis slide shows management and governance architecture for security program to encompasses policies, procedures, and management structure for coordinating security activity. It further includes details such as security governance ,strategic risk tolerance planning ,organization structure etc. Presenting our well structured Governance And Management Structure Of Information Security Program The topics discussed in this slide are Security Governance, Security Management. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Information Network Security Program Icon
Information Network Security Program IconIntroducing our Information Network Security Program Icon set of slides. The topics discussed in these slides are Information Network Security Program Icon. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Information Security Awareness Training Program
Information Security Awareness Training ProgramThis slide shows program campaign for information security which helps keep individuals informed about the latest cybersecurity threats. It further includes details such as overview of campaign ,languages used ,target group ,product included etc. Presenting our set of slides with Information Security Awareness Training Program This exhibits information on Five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Overview, Target Group, Product Included
-
 Information Security Management Program To Protect Data
Information Security Management Program To Protect DataThis slide shows information security program checklist that helps toidentify potential weaknesses or vulnerabilities in system. It further includes metrics such as risk management, information security policy ,information security responsibility etc. Presenting our well structured Information Security Management Program To Protect Data The topics discussed in this slide are Risk Management, Information Security Policy. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Information Security Program Icon For Data Protection
Information Security Program Icon For Data ProtectionIntroducing our Information Security Program Icon For Data Protection set of slides. The topics discussed in these slides are Information Security Program, Icon For Data Protection. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Information Security Program Icon For Internet Encryption
Information Security Program Icon For Internet EncryptionIntroducing our premium set of slides with Information Security Program Icon For Internet Encryption Ellicudate the Three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Information Security Program, Icon For Internet Encryption. So download instantly and tailor it with your information.
-
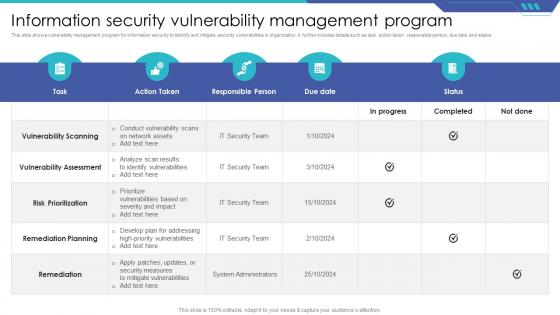 Information Security Vulnerability Management Program
Information Security Vulnerability Management ProgramThis slide shows vulnerability management program for information security to identify and mitigate security vulnerabilities in organization. It further includes details such as task, action taken, responsible person, due date and status. Presenting our well structured Information Security Vulnerability Management Program The topics discussed in this slide are Vulnerability Scanning, Remediation Planning, Remediation. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
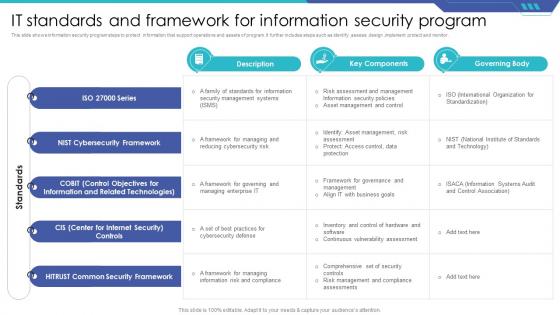 IT Standards And Framework For Information Security Program
IT Standards And Framework For Information Security ProgramThis slide shows information security program steps to protect information that support operations and assets of program. It further includes steps such as identify ,assess ,design ,implement protect and monitor. Introducing our IT Standards And Framework For Information Security Program set of slides. The topics discussed in these slides are Governing Body, Cybersecurity Framework, Common Security Framework. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
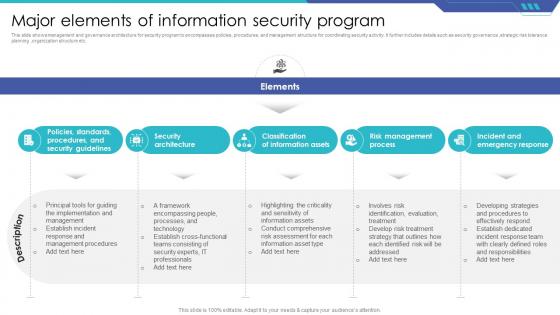 Major Elements Of Information Security Program
Major Elements Of Information Security ProgramIntroducing our premium set of slides with Major Elements Of Information Security Program Ellicudate the Five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Security Architecture, Classification Of Information Assets, Risk Management Process. So download instantly and tailor it with your information.
-
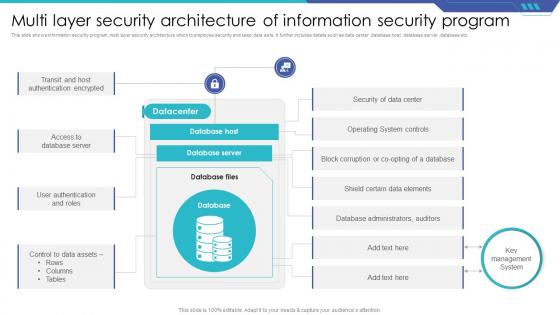 Multi Layer Security Architecture Of Information Security Program
Multi Layer Security Architecture Of Information Security ProgramThis slide shows information security program ,multi layer security architecture which to employee security and keep data safe. It further includes details such as data center ,database host ,database server ,database etc. Introducing our Multi Layer Security Architecture Of Information Security Program set of slides. The topics discussed in these slides are Datacenter, Database Host, Database Server. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
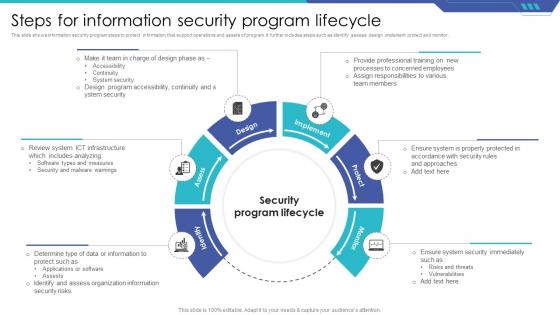 Steps For Information Security Program Lifecycle
Steps For Information Security Program LifecycleThis slide shows information security program steps to protect information that support operations and assets of program. It further includes steps such as identify, assess, design, implement protect and monitor. Presenting our set of slides with Steps For Information Security Program Lifecycle This exhibits information on Six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Malware Warnings, Security Program Lifecycle.
-
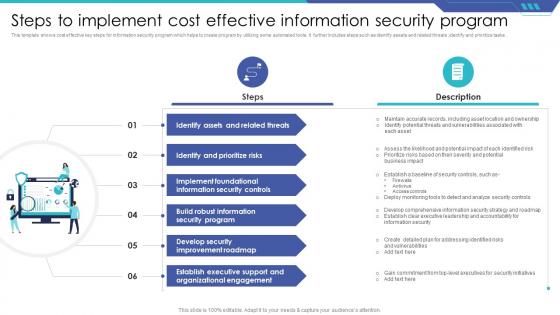 Steps To Implement Cost Effective Information Security Program
Steps To Implement Cost Effective Information Security ProgramThis template shows cost effective key steps for information security program which helps to create program by utilizing some automated tools. It further includes steps such as identify assets and related threats ,identify and prioritize tasks . Introducing our premium set of slides with Steps To Implement Cost Effective Information Security Program Ellicudate the Six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Identify Assets And Related Threats, Identify And Prioritize Risks, Information Security Controls. So download instantly and tailor it with your information.
-
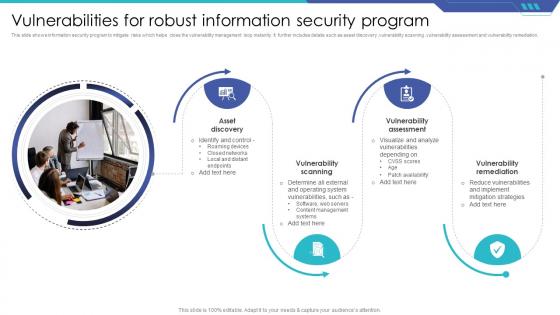 Vulnerabilities For Robust Information Security Program
Vulnerabilities For Robust Information Security ProgramThis slide shows information security program to mitigate risks which helps close the vulnerability management loop instantly. It further includes details such as asset discovery ,vulnerability scanning ,vulnerability assessment and vulnerability remediation. Presenting our set of slides with Vulnerabilities For Robust Information Security Program This exhibits information on Four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Asset Discovery, Vulnerability Scanning, Vulnerability Assessment


