Powerpoint Templates and Google slides for Security Compliance
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Security Compliance Powerpoint Ppt Template Bundles
Security Compliance Powerpoint Ppt Template BundlesDeliver a lucid presentation by utilizing this Security Compliance Powerpoint Ppt Template Bundles. Use it to present an overview of the topic with the right visuals, themes, shapes, and graphics. This is an expertly designed complete deck that reinforces positive thoughts and actions. Use it to provide visual cues to your audience and help them make informed decisions. A wide variety of discussion topics can be covered with this creative bundle such as Compliance With Security Standards, Security Compliance Best Practices, Compliance Monitoring For Security, Network Security Standards Compliance, IT Security Compliance Measures. All the seventeen slides are available for immediate download and use. They can be edited and modified to add a personal touch to the presentation. This helps in creating a unique presentation every time. Not only that, with a host of editable features, this presentation can be used by any industry or business vertical depending on their needs and requirements. The compatibility with Google Slides is another feature to look out for in the PPT slideshow.
-
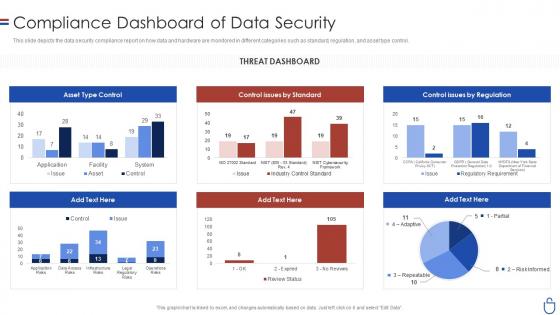 Data security it compliance dashboard snapshot of data security
Data security it compliance dashboard snapshot of data securityThis slide depicts the data security compliance report on how data and hardware are monitored in different categories such as standard, regulation, and asset type control. Present the topic in a bit more detail with this Data Security IT Compliance Dashboard Snapshot Of Data Security. Use it as a tool for discussion and navigation on Asset Type Control, Control Issues By Standard, Control Issues By Regulation, Threat Dashboard. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
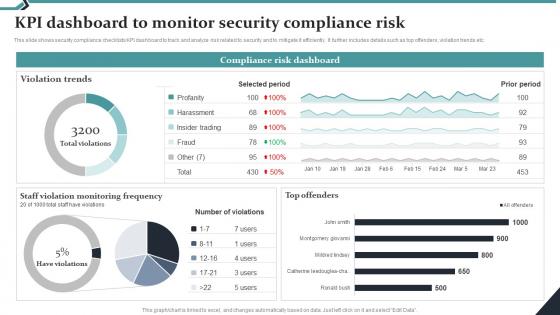 Kpi Dashboard To Monitor Security Compliance Risk
Kpi Dashboard To Monitor Security Compliance RiskThis slide shows security compliance checklists KPI dashboard to track and analyze risk related to security and to mitigate it efficiently. It further includes details such as top offenders, violation trends etc. Presenting our well structured Kpi Dashboard To Monitor Security Compliance Risk. The topics discussed in this slide are Violation Trends, Selected Period.This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Automated Saas Compliance Audit Framework For Data Security
Automated Saas Compliance Audit Framework For Data SecurityThis slide shows automated compliance audit framework for building scalable security practices in SaaS businesses. The purpose of this slide is to assist businesses in gaining competitive advantage by simplifying SaaS compliance processes. It covers components such as deadline, controls implemented, compliance status, etc. Introducing our Automated Saas Compliance Audit Framework For Data Security set of slides. The topics discussed in these slides are Automated Saas Compliance, Audit Framework For Data Security. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
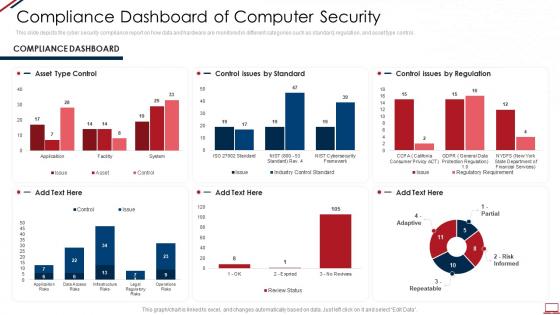 Computer system security compliance dashboard Snapshot of computer security
Computer system security compliance dashboard Snapshot of computer securityThis slide depicts the cyber security compliance report on how data and hardware are monitored in different categories such as standard, regulation, and asset type control. Present the topic in a bit more detail with this Computer System Security Compliance Dashboard Snapshot Of Computer Security. Use it as a tool for discussion and navigation on Asset Type Control, Control Issues By Standard, Control Issues By Regulation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
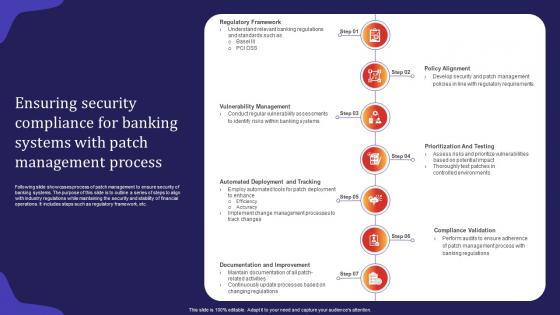 Ensuring Security Compliance For Banking Systems With Patch Management Process
Ensuring Security Compliance For Banking Systems With Patch Management ProcessFollowing slide showcases process of patch management to ensure security of banking systems. The purpose of this slide is to outline a series of steps to align with industry regulations while maintaining the security and stability of financial operations. It includes steps such as regulatory framework, etc.Presenting our set of slides with Ensuring Security Compliance For Banking Systems With Patch Management Process. This exhibits information on seven stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Vulnerability Management, Compliance Validation, Documentation Improvement
-
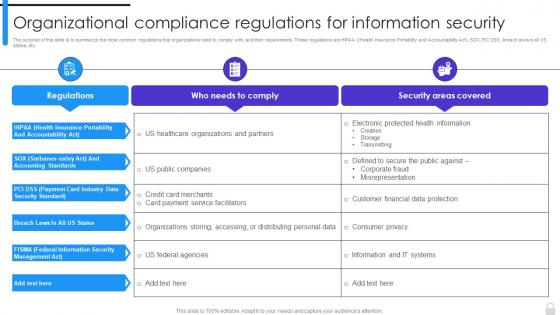 Encryption Implementation Strategies Organizational Compliance Regulations For Information Security
Encryption Implementation Strategies Organizational Compliance Regulations For Information SecurityThe purpose of this slide is to summarize the most common regulations that organizations need to comply with, and their requirements. These regulations are HIPAA Health Insurance Portability and Accountability Act, SOX, PCI DSS, breach laws in all US states, etc. Present the topic in a bit more detail with this Encryption Implementation Strategies Organizational Compliance Regulations For Information Security. Use it as a tool for discussion and navigation on Health Insurance Portability, Accountability Act, Payment Card Industry, Data Security Standard. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Digital Transformation Ensuring Erp Data Security And Compliance DT SS
Digital Transformation Ensuring Erp Data Security And Compliance DT SSPresent the topic in a bit more detail with this Digital Transformation Ensuring Erp Data Security And Compliance DT SS Use it as a tool for discussion and navigation on Robust Access Controls, Data Encryption, Compliance With Regulations This template is free to edit as deemed fit for your organization. Therefore download it now.
-
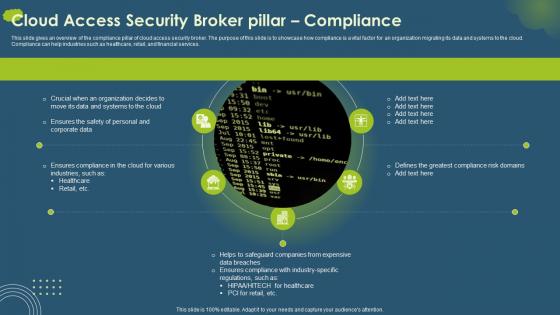 Cloud Access Security Broker CASB V2 Pillar Compliance Ppt Icon Background Images
Cloud Access Security Broker CASB V2 Pillar Compliance Ppt Icon Background ImagesThis slide gives an overview of the compliance pillar of cloud access security broker. The purpose of this slide is to showcase how compliance is a vital factor for an organization migrating its data and systems to the cloud. Compliance can help industries such as healthcare, retail, and financial services. Introducing Cloud Access Security Broker CASB V2 Pillar Compliance Ppt Icon Background Images to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Compliance Pillar, Cloud Access Security Broker, Financial Services, Compliance Risk Domains, using this template. Grab it now to reap its full benefits.
-
 Best Practices For Security Compliance Management
Best Practices For Security Compliance ManagementThis slide shows best practices for security compliance helps to improve security posture, minimize exposure to non compliance risks. It further includes practices such as develop risk assessment plan, promote team communication etc. Presenting our set of slides with Best Practices For Security Compliance Management. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Develop Risk Assessment Plan, Promote Team Communication.
-
 Comparative Analysis Of It Security And Compliance
Comparative Analysis Of It Security And ComplianceThis slide shows It security and compliance comparative analysis to implement effective technical controls to protect company assets. It further includes details such as it security Practiced by business for personal gain etc. Introducing our premium set of slides with Comparative Analysis Of It Security And Compliance. Ellicudate the two stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like It Security, It Compliance. So download instantly and tailor it with your information.
-
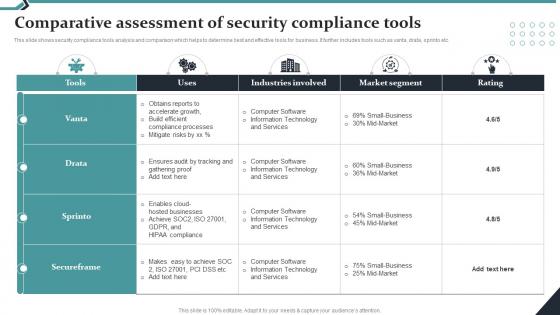 Comparative Assessment Of Security Compliance Tools
Comparative Assessment Of Security Compliance ToolsThis slide shows security compliance tools analysis and comparison which helps to determine best and effective tools for business. It further includes tools such as vanta, drata, sprinto etc. Presenting our well structured Comparative Assessment Of Security Compliance Tools. The topics discussed in this slide are Industries Involved, Market Segment.This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Employee Data Security Compliance Icon
Employee Data Security Compliance IconPresenting our set of slides with Employee Data Security Compliance Icon. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Employee Data, Security Compliance.
-
 Healthcare And Medical Security Compliance Checklist Icon
Healthcare And Medical Security Compliance Checklist IconIntroducing our premium set of slides with Healthcare And Medical Security Compliance Checklist Icon. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Healthcare Medical Security, Compliance Checklist. So download instantly and tailor it with your information.
-
 Information Security Compliance Laws And Standards
Information Security Compliance Laws And StandardsThis slide shows types of security compliance helps to differentiate between security standards and outline their uses with industry focus. It further includes types such as ISO 27000, NIST, PCI DSS etc. Introducing our premium set of slides with Information Security Compliance Laws And Standards. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Compliance Standard, Description. So download instantly and tailor it with your information.
-
 Laws And Standards For Security Compliance Management
Laws And Standards For Security Compliance ManagementThis slide shows laws and standards for security compliance management helps in allow businesses to build a cyber security program. It further includes details as GDPR, CCPA and CPRA, soc, hipaa etc. Presenting our set of slides with Laws And Standards For Security Compliance Management. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Laws And Standards, Description.
-
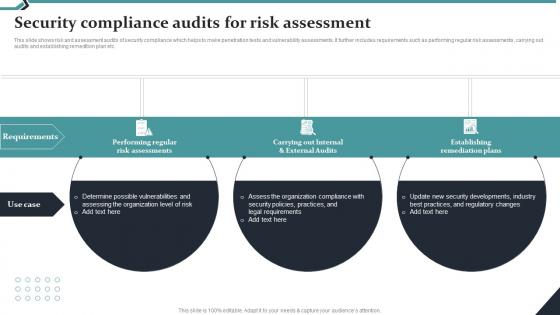 Security Compliance Audits For Risk Assessment
Security Compliance Audits For Risk AssessmentThis slide shows risk and assessment audits of security compliance which helps to make penetration tests and vulnerability assessments. It further includes requirements such as performing regular risk assessments, carrying out audits and establishing remedition plan etc. Introducing our premium set of slides with Security Compliance Audits For Risk Assessment. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Performing Regular, Carrying Out Internal. So download instantly and tailor it with your information.
-
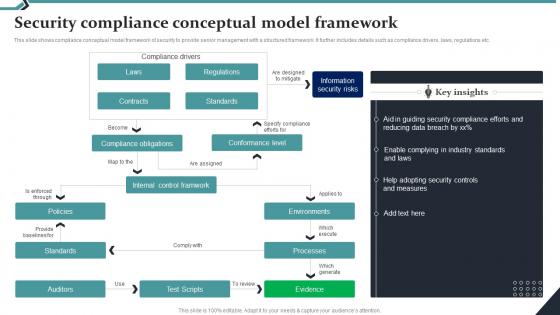 Security Compliance Conceptual Model Framework
Security Compliance Conceptual Model FrameworkThis slide shows compliance conceptual model framework of security to provide senior management with a structured framework. It further includes details such as compliance drivers, laws, regulations etc. Introducing our Security Compliance Conceptual Model Framework set of slides. The topics discussed in these slides are Contracts, Standards. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
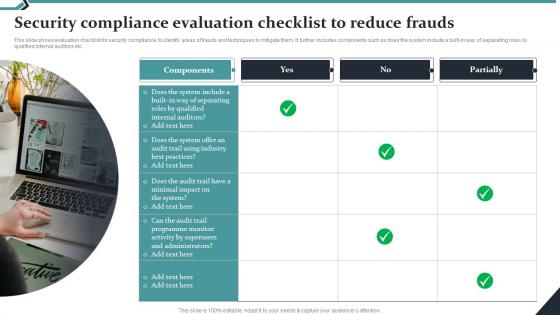 Security Compliance Evaluation Checklist To Reduce Frauds
Security Compliance Evaluation Checklist To Reduce FraudsThis slide shows evaluation checklist for security compliance to identify areas of frauds and techniques to mitigate them. It further includes components such as does the system include a built in way of separating roles by qualified internal auditors etc. Presenting our set of slides with Security Compliance Evaluation Checklist To Reduce Frauds. This exhibits information on one stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Components, Partially.
-
 Security Compliance Icon For Network Protection
Security Compliance Icon For Network ProtectionPresenting our well structured Security Compliance Icon For Network Protection. The topics discussed in this slide are Security Compliance, Network Protection.This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
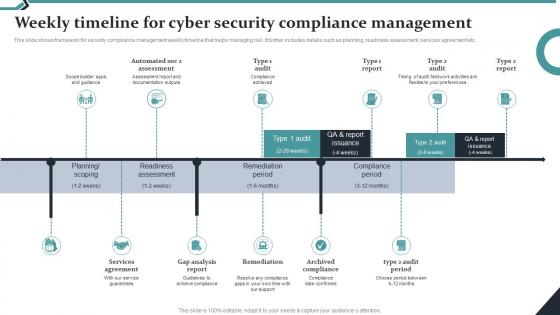 Weekly Timeline For Cyber Security Compliance Management
Weekly Timeline For Cyber Security Compliance ManagementThis slide shows framework for security compliance management weekly timeline that helps managing risk. It further includes details such as planning, readiness assessment, services agreement etc. Introducing our Weekly Timeline For Cyber Security Compliance Management set of slides. The topics discussed in these slides are Compliance Period, Remediation Period. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Impacts Of Cyber Security Data Compliance
Impacts Of Cyber Security Data ComplianceThis slide shows benefits of cyber security compliance which helps in aiming to protect sensitive data and maintain the integrity of information systems. It further includes benefits such as strengthening data protection etc. Presenting our set of slides with Impacts Of Cyber Security Data Compliance. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Strengthening Data Protection, Regulatory Compliance.
-
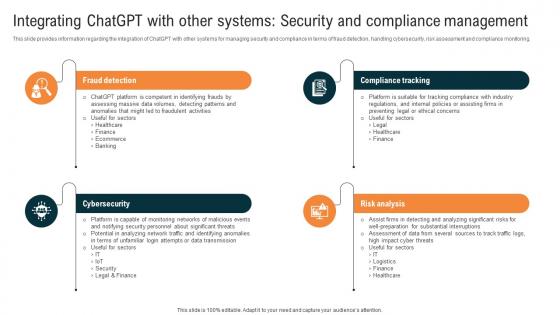 Integrating ChatGPT With Other Systems Security And Compliance Glimpse About ChatGPT As AI ChatGPT SS V
Integrating ChatGPT With Other Systems Security And Compliance Glimpse About ChatGPT As AI ChatGPT SS VThis slide provides information regarding the integration of ChatGPT with other systems for managing security and compliance in terms of fraud detection, handling cybersecurity, risk assessment and compliance monitoring. Introducing Integrating ChatGPT With Other Systems Security And Compliance Glimpse About ChatGPT As AI ChatGPT SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Fraud Detection, Compliance Tracking, Risk Analysis, Cybersecurity, Security And Compliance Management, using this template. Grab it now to reap its full benefits.
-
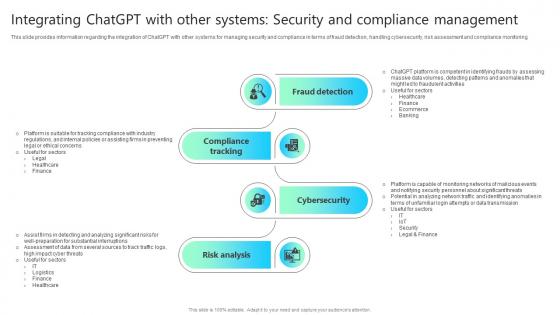 Integrating Chatgpt With Other Systems Security And Compliance Chatgpt Impact How ChatGPT SS V
Integrating Chatgpt With Other Systems Security And Compliance Chatgpt Impact How ChatGPT SS VThis slide provides information regarding the integration of ChatGPT with other systems for managing security and compliance in terms of fraud detection, handling cybersecurity, risk assessment and compliance monitoring. Increase audience engagement and knowledge by dispensing information using Integrating Chatgpt With Other Systems Security And Compliance Chatgpt Impact How ChatGPT SS V This template helps you present information on Four stages. You can also present information on Consumer Assistance, Sales Support, Customization, Consumer Feedback Assessment using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
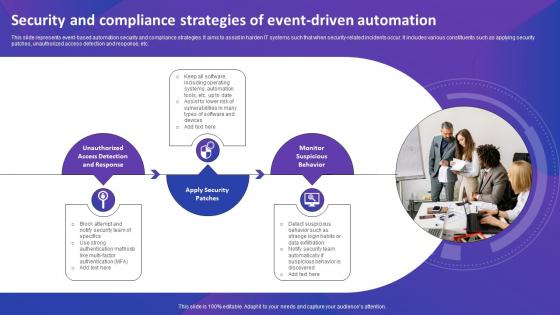 Security And Compliance Strategies Of Event Driven Automation
Security And Compliance Strategies Of Event Driven AutomationThis slide represents event-based automation security and compliance strategies. It aims to assist in harden IT systems such that when security-related incidents occur. It includes various constituents such as applying security patches, unauthorized access detection and response, etc. Presenting our set of slides with Security And Compliance Strategies Of Event Driven Automation. This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Enhance Success Of Events, Attendee Satisfaction, Meet Event Goals
-
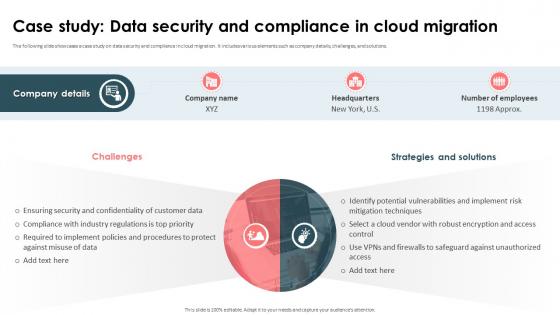 Strategic Approach For Effective Data Migration Case Study Data Security And Compliance In Cloud Migration
Strategic Approach For Effective Data Migration Case Study Data Security And Compliance In Cloud MigrationThe following slide showcases a case study on data security and compliance in cloud migration. It includes various elements such as company details, challenges, and solutions. Increase audience engagement and knowledge by dispensing information using Strategic Approach For Effective Data Migration Case Study Data Security And Compliance In Cloud Migration. This template helps you present information on three stages. You can also present information on Data Security, Cloud Migration, Security And Confidentiality, Customer Data using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
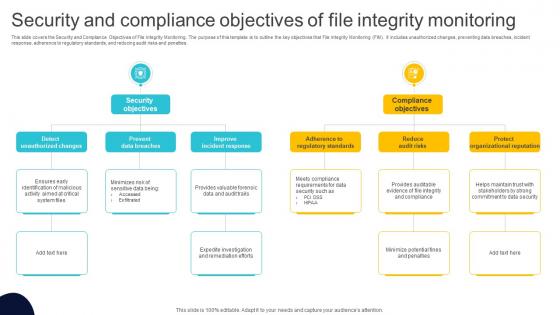 Security And Compliance Objectives Of File Integrity Monitoring
Security And Compliance Objectives Of File Integrity MonitoringThis slide covers the Security and Compliance Objectives of File Integrity Monitoring. The purpose of this template is to outline the key objectives that File Integrity Monitoring FIM. It includes unauthorized changes, preventing data breaches, incident response, adherence to regulatory standards, and reducing audit risks and penalties. Presenting our set of slides with Security And Compliance Objectives Of File Integrity Monitoring This exhibits information on Two stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Security Objectives, Compliance Objectives
-
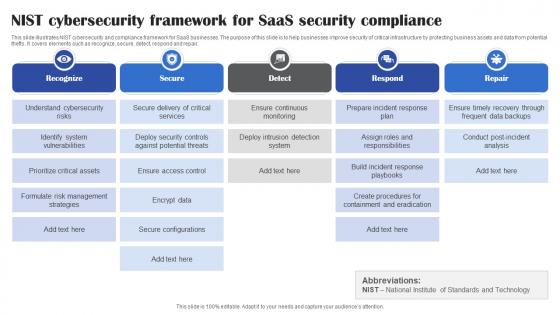 Nist Cybersecurity Framework For Saas Security Compliance
Nist Cybersecurity Framework For Saas Security ComplianceThis slide illustrates NIST cybersecurity and compliance framework for SaaS businesses. The purpose of this slide is to help businesses improve security of critical infrastructure by protecting business assets and data from potential thefts. It covers elements such as recognize, secure, detect, respond and repair. Presenting our set of slides with Nist Cybersecurity Framework For Saas Security Compliance. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Recognize, Secure, Detect, Respond.
-
 Saas Compliance Checklist For Organizational Security
Saas Compliance Checklist For Organizational SecurityThis slide presents organizational security checklist to manage governance and compliance requirements for SaaS businesses. It aims to provide assistance during the SaaS compliance journey for securing cloud-based applications. It covers elements such as determining compliance requirements, evaluating risks, assessing compliance level, formulating strategy, implementing controls, etc. Introducing our Saas Compliance Checklist For Organizational Security set of slides. The topics discussed in these slides are Data Handling Processes, Security Risks, Resource Requirements. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
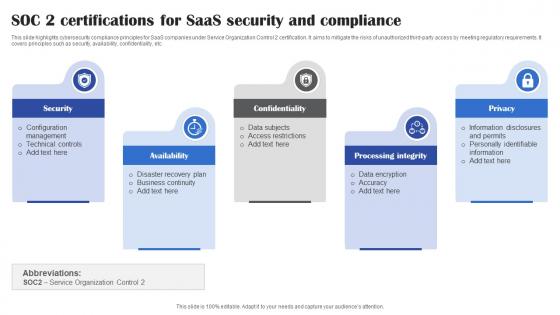 SOC 2 Certifications For Saas Security And Compliance
SOC 2 Certifications For Saas Security And ComplianceThis slide highlights cybersecurity compliance principles for SaaS companies under Service Organization Control 2 certification. It aims to mitigate the risks of unauthorized third-party access by meeting regulatory requirements. It covers principles such as security, availability, confidentiality, etc. Presenting our set of slides with SOC 2 Certifications For Saas Security And Compliance. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Security, Availability, Confidentiality.
-
 Factors Affecting Security Compliance In It Audit
Factors Affecting Security Compliance In It AuditFollowing slide showcases factors in IT audit that affect security compliance for risk mitigation. It further covers factors such as logical and physical security, regulatory compliance and hardware. Introducing our premium set of slides with Factors Affecting Security Compliance In It Audit. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Physical Security, Regulatory Compliance, Management System. So download instantly and tailor it with your information.
-
 Firewall Audit Software Solutions For Security Compliance
Firewall Audit Software Solutions For Security ComplianceThis slide shows major features offered by firewall audit software that helps in maintaining a strong network security posture by complying with organizational regulatory standards. It covers solutions such as rule analysis, workflow automation and configuration management.Presenting our set of slides with Firewall Audit Software Solutions For Security Compliance. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Workflow Automation, Configuration Management, Firewall Rule Analysis.
-
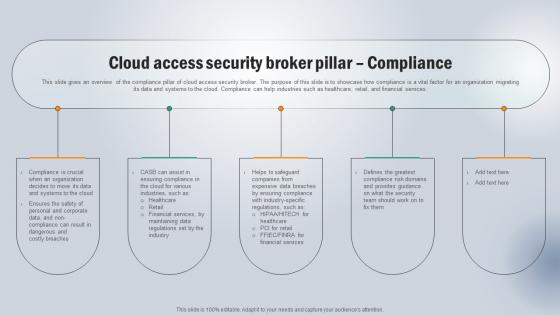 Cloud Access Security Broker Pillar Compliance Next Generation CASB
Cloud Access Security Broker Pillar Compliance Next Generation CASBThis slide gives an overview of the compliance pillar of cloud access security broker. The purpose of this slide is to showcase how compliance is a vital factor for an organization migrating its data and systems to the cloud. Compliance can help industries such as healthcare, retail, and financial services. Introducing Cloud Access Security Broker Pillar Compliance Next Generation CASB to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Financial Services, Risk Domains, Costly Breaches using this template. Grab it now to reap its full benefits.
-
 Cloud Automation Strategies To Enhance Security And Compliance
Cloud Automation Strategies To Enhance Security And ComplianceThis slide represents cloud automation strategies to enhance security and compliance which assists organizations to streamline operations and minimizes manual intervention. It includes cloud automation strategies to enhance security and compliances such as utilize infrastructure as code, etc. Introducing our premium set of slides with name Cloud Automation Strategies To Enhance Security And Compliance. Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cloud Consulting Partner, Leverage Automation, Enhance Compliance, Utilize Policy As Tools. So download instantly and tailor it with your information.
-
 Stages Of Cyber Security And Compliance Automation
Stages Of Cyber Security And Compliance AutomationThis slide represents stages of cyber security and compliance automation which assists in cyber risk and policy adherence. It includes stages of cyber security and compliance automation such as initial, developing, define, etc. Presenting our set of slides with name Stages Of Cyber Security And Compliance Automation. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Stages Of Cyber Security, Compliance Automation, Developing, Risk And Policy Adherence.
-
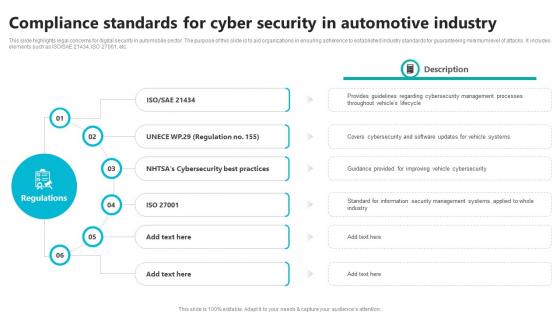 Compliance Standards For Cyber Security In Automotive Industry
Compliance Standards For Cyber Security In Automotive IndustryThis slide highlights legal concerns for digital security in automobile sector. The purpose of this slide is to aid organizations in ensuring adherence to established industry standards for guaranteeing minimum level of attacks. It includes elements such as ISO SAE 21434, ISO 27001, etc. Presenting our set of slides with Compliance Standards For Cyber Security In Automotive Industry This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cybersecurity Best Practices, Management Processes.
-
 Cloud Access Security Broker Pillar Compliance CASB Cloud Security
Cloud Access Security Broker Pillar Compliance CASB Cloud SecurityThis slide gives an overview of the compliance pillar of cloud access security broker. The purpose of this slide is to showcase how compliance is a vital factor for an organization migrating its data and systems to the cloud. Compliance can help industries such as healthcare, retail, and financial services. Present the topic in a bit more detail with this Cloud Access Security Broker Pillar Compliance CASB Cloud Security. Use it as a tool for discussion and navigation on Cloud Access Security Broker Pillar, Financial Services, Compliance Is Crucial. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
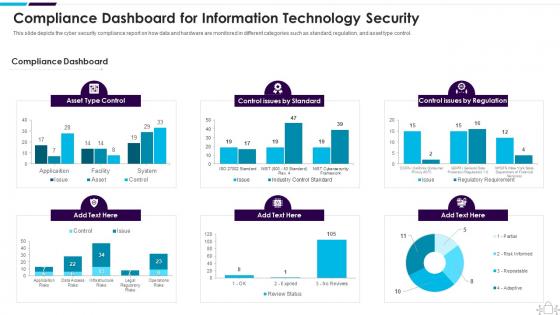 Information Technology Security Compliance Dashboard Snapshot For Information Technology Security
Information Technology Security Compliance Dashboard Snapshot For Information Technology SecurityThis slide depicts the cyber security compliance report on how data and hardware are monitored in different categories such as standard, regulation, and asset type control. Present the topic in a bit more detail with this Information Technology Security Compliance Dashboard Snapshot For Information Technology Security. Use it as a tool for discussion and navigation on Dashboard, Information, Technology. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
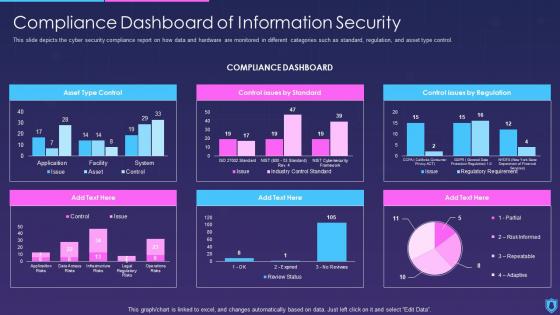 Information Security Compliance Dashboard Snapshot Of Information Security
Information Security Compliance Dashboard Snapshot Of Information SecurityThis slide depicts the cyber security compliance report on how data and hardware are monitored in different categories such as standard, regulation, and asset type control. Deliver an outstanding presentation on the topic using this Information Security Compliance Dashboard snapshot Of Information Security. Dispense information and present a thorough explanation of Compliance, Dashboard, Information using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Security information and event management successful siem strategies for audit compliance
Security information and event management successful siem strategies for audit complianceThis slide covers the SIEM dashboard which focuses on security events, event categories, data sources, logger event, multiple events, etc. Present the topic in a bit more detail with this Security Information And Event Management Successful Siem Strategies For Audit Compliance. Use it as a tool for discussion and navigation on Information, Management, Dashboard. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
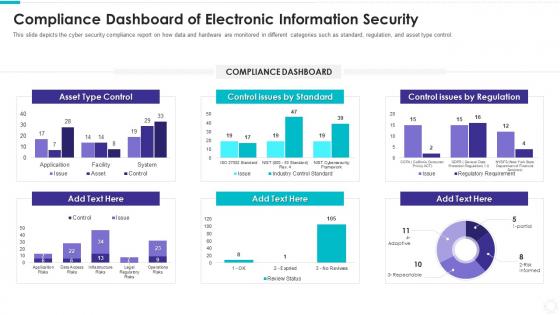 Compliance dashboard snapshot of electronic information security
Compliance dashboard snapshot of electronic information securityThis slide depicts the cyber security compliance report on how data and hardware are monitored in different categories such as standard, regulation, and asset type control. Present the topic in a bit more detail with this Compliance Dashboard Snapshot Of Electronic Information Security. Use it as a tool for discussion and navigation on Asset Type Control, Compliance Dashboard, Control Issues By Regulation, Control Issues By Standard. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
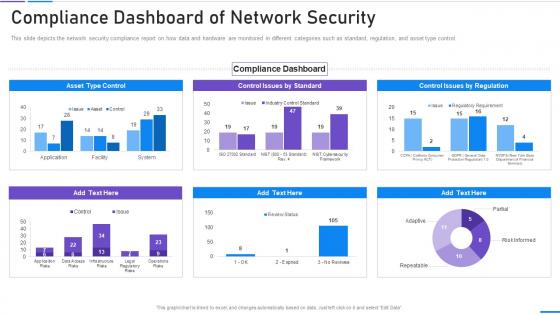 Network Security Compliance Dashboard Snapshot Of Network Security
Network Security Compliance Dashboard Snapshot Of Network SecurityThis slide depicts the network security compliance report on how data and hardware are monitored in different categories such as standard, regulation, and asset type control. Present the topic in a bit more detail with this Network Security Compliance Dashboard Snapshot Of Network Security. Use it as a tool for discussion and navigation on Compliance Dashboard Of Network Security. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cloud Security Threats Compliance Violations Cloud Data Protection
Cloud Security Threats Compliance Violations Cloud Data ProtectionThis slide depicts the value of compliance violations threat of cloud security in a business and how fast an organization can switch to a non-compliance state. Introducing Cloud Security Threats Compliance Violations Cloud Data Protection to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispense information on Authentication Procedures, Business, Organizations, using this template. Grab it now to reap its full benefits.
-
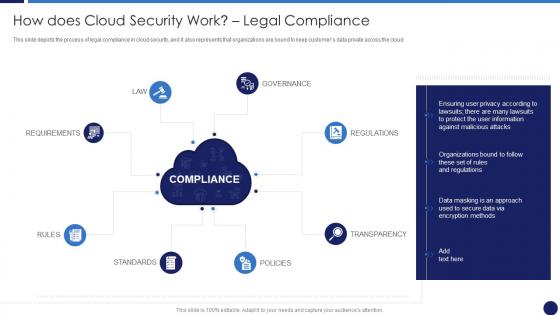 How Does Cloud Security Work Legal Compliance Cloud Data Protection
How Does Cloud Security Work Legal Compliance Cloud Data ProtectionThis slide depicts the process of legal compliance in cloud security, and it also represents that organizations are bound to keep customers data private across the cloud. Increase audience engagement and knowledge by dispensing information using How Does Cloud Security Work Legal Compliance Cloud Data Protection. This template helps you present information on eight stages. You can also present information on Secure Data, Organizations, Compliance using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
 Cloud Computing Security How Does Cloud Security Work Legal Compliance
Cloud Computing Security How Does Cloud Security Work Legal ComplianceThis slide depicts the process of legal compliance in cloud security, and it also represents that organizations are bound to keep customers data private across the cloud. Increase audience engagement and knowledge by dispensing information using Cloud Computing Security How Does Cloud Security Work Legal Compliance. This template helps you present information on eight stages. You can also present information on Transparency, Regulations, Governance, Compliance, Policies using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cloud Security Threats Compliance Violations Cloud Computing Security
Cloud Security Threats Compliance Violations Cloud Computing SecurityThis slide depicts the value of compliance violations threat of cloud security in a business and how fast an organization can switch to a non compliance state. Introducing Cloud Security Threats Compliance Violations Cloud Computing Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Organizations, Authentication Procedures, Businesses, using this template. Grab it now to reap its full benefits.
-
 Cloud Security Threats Compliance Violations Cloud Information Security
Cloud Security Threats Compliance Violations Cloud Information SecurityThis slide depicts the value of compliance violations threat of cloud security in a business and how fast an organization can switch to a non compliance state.Introducing Cloud Security Threats Compliance Violations Cloud Information Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Needed Information, Against Organization, Business Partners using this template. Grab it now to reap its full benefits.
-
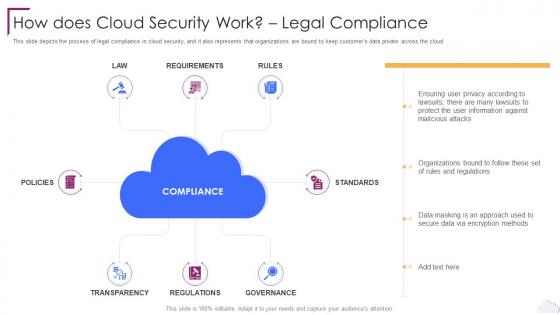
 How Does Cloud Security Work Legal Compliance Cloud Information Security
How Does Cloud Security Work Legal Compliance Cloud Information SecurityThis slide depicts the process of legal compliance in cloud security, and it also represents that organizations are bound to keep customers data private across the cloud.Increase audience engagement and knowledge by dispensing information using How Does Cloud Security Work Legal Compliance Cloud Information Security This template helps you present information on eight stages. You can also present information on Firewalls Ensure, Organization Security, Permitting Limited using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Successful siem strategies audit compliance benchmarking security operations maturity
Successful siem strategies audit compliance benchmarking security operations maturityThis slide focuses on the SOMM which measures the current security posture and understand the progress of operations readiness by visibility improvement, threats identification, etc. Increase audience engagement and knowledge by dispensing information using Successful Siem Strategies Audit Compliance Benchmarking Security Operations Maturity. This template helps you present information on three stages. You can also present information on Improve Visibility, Quickly Identify Threats, Decrease Response Time using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Successful siem strategies audit compliance security information event management services
Successful siem strategies audit compliance security information event management servicesThis slide covers the SIEM services offered by our company such as data aggregation, correlation, security alerts, dashboards, retention, forensic analysis, IT compliance, threat detection, etc. Introducing Successful Siem Strategies Audit Compliance Security Information Event Management Services to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Data Aggregation, Data Correlation, Dashboards, using this template. Grab it now to reap its full benefits.
-
 Cloud Security Governance Risk And Compliance Model
Cloud Security Governance Risk And Compliance ModelThe following slide presents a GRC model to manage and control cloud cyber security operations and reduce the impact of risk events. It includes key components such as governance, risk and compliance. Introducing our Cloud Security Governance Risk And Compliance Model set of slides. The topics discussed in these slides are Governance, Compliance, Update And Publish Policies. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
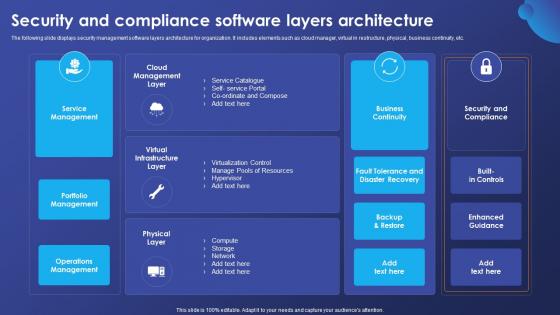 Security And Compliance Software Layers Architecture
Security And Compliance Software Layers ArchitectureThe following slide displays security management software layers architecture for organization. It includes elements such as cloud manager, virtual in restructure, physical, business continuity, etc. Introducing our Security And Compliance Software Layers Architecture set of slides. The topics discussed in these slides are Service Management, Portfolio Management, Operations Management. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Cyber Security Compliance Matrix Icon
Cyber Security Compliance Matrix IconPresenting our set of slides with name Cyber Security Compliance Matrix Icon. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cyber Security, Compliance Matrix Icon.
-
 Cyber Security Standards Compliance Matrix
Cyber Security Standards Compliance MatrixThis slide represents the cyber security standards compliance matrix. The purpose of this slide is to demonstrate the various cybersecurity standards and their compliance requirements for businesses. The primary standards include ISO27001, PCI DSS, HIPPA, FINRA and GDPR. Presenting our well structured Cyber Security Standards Compliance Matrix. The topics discussed in this slide are Standards, Requirements, Compliance Status, Risk Level, Comments. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
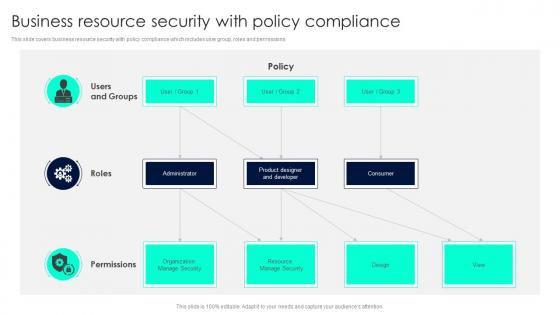 Business Resource Security With Policy Compliance
Business Resource Security With Policy ComplianceThis slide covers business resource security with policy compliance which includes user group, roles and permissions. Introducing our Business Resource Security With Policy Compliance set of slides. The topics discussed in these slides are Users Groups, Roles, Permissions. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
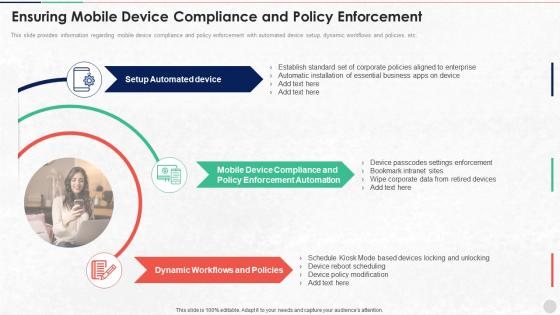 Ensuring Mobile Device Compliance And Policy Enforcement Unified Endpoint Security
Ensuring Mobile Device Compliance And Policy Enforcement Unified Endpoint SecurityThis slide provides information regarding mobile device compliance and policy enforcement with automated device setup, dynamic workflows and policies, etc.Increase audience engagement and knowledge by dispensing information using Ensuring Mobile Device Compliance And Policy Enforcement Unified Endpoint Security. This template helps you present information on three stages. You can also present information on Enforcement Automation, Dynamic Workflows, Device Compliance using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
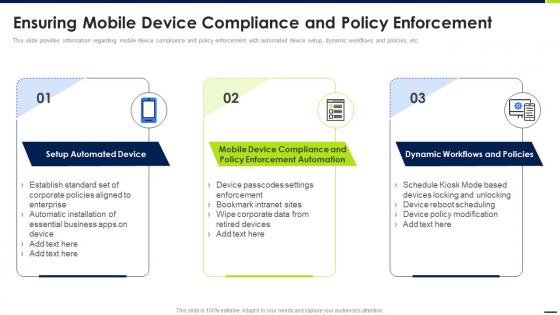 Ensuring Mobile Device Compliance And Policy Enforcement Android Device Security Management
Ensuring Mobile Device Compliance And Policy Enforcement Android Device Security ManagementThis slide provides information regarding mobile device compliance and policy enforcement with automated device setup, dynamic workflows and policies, etc. Increase audience engagement and knowledge by dispensing information using Ensuring Mobile Device Compliance And Policy Enforcement Android Device Security Management. This template helps you present information on three stages. You can also present information on Setup Automated Device, Mobile Device Compliance, Dynamic Workflows using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
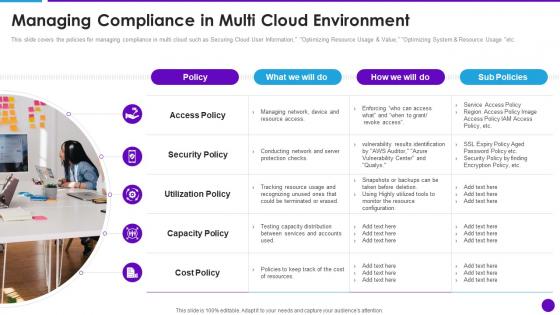 Cloud Architecture And Security Review Managing Compliance In Multi Cloud Environment
Cloud Architecture And Security Review Managing Compliance In Multi Cloud EnvironmentThis slide covers the policies for managing compliance in multi cloud such as Securing Cloud User Information, Optimizing Resource Usage and Value, Optimizing System and Resource Usage etc. Increase audience engagement and knowledge by dispensing information using Cloud Architecture And Security Review Managing Compliance In Multi Cloud Environment. This template helps you present information on five stages. You can also present information on Utilization Policy, Capacity Policy, Security Policy using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Ensuring Mobile Device Compliance Enforcement Enterprise Mobile Security For On Device
Ensuring Mobile Device Compliance Enforcement Enterprise Mobile Security For On DeviceThis slide provides information regarding mobile device compliance and policy enforcement with automated device setup, dynamic workflows and policies, etc.Present the topic in a bit more detail with this Ensuring Mobile Device Compliance Enforcement Enterprise Mobile Security For On Device. Use it as a tool for discussion and navigation on Automated Device, Corporate Policies, Essential Business. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Security Policies Compliance Regulations Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Security Policies Compliance Regulations Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis coloured powerpoint icon is perfect for Employee Security Business presentations. It features a shield with a padlock, representing a secure environment for employees. The icon is bright and eye-catching, making it easy to spot in any presentation. Use it to illustrate the importance of keeping employees safe and secure.


