Powerpoint Templates and Google slides for Security Effectiveness
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Effective information security risk reporting and likelihood ppt slides layout
Effective information security risk reporting and likelihood ppt slides layoutMentioned slide shows encountered risk reporting and its likelihood. It includes information about risk encountered, frequency, reported by status, attack scenario, affected asset and likelihood. Deliver an outstanding presentation on the topic using this Effective Information Security Risk Reporting And Likelihood Ppt Slides Layout. Dispense information and present a thorough explanation of Risk Encountered, Frequency, Attack Scenario, Affected Asset using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
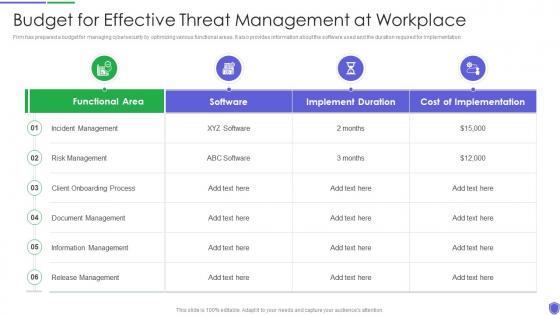 Budget for effective threat managing critical threat vulnerabilities and security threats
Budget for effective threat managing critical threat vulnerabilities and security threatsFirm has prepared a budget for managing cybersecurity by optimizing various functional areas. It also provides information about the software used and the duration required for implementation. Deliver an outstanding presentation on the topic using this Budget For Effective Threat Managing Critical Threat Vulnerabilities And Security Threats. Dispense information and present a thorough explanation of Incident Management, Risk Management, Client Onboarding Process, Document Management using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Impact analysis for effective managing critical threat vulnerabilities and security threats
Impact analysis for effective managing critical threat vulnerabilities and security threatsThis slide portrays information regarding how firm is successful in handling security threats and is able in reducing the occurrence of threats. Introducing Impact Analysis For Effective Managing Critical Threat Vulnerabilities And Security Threats to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Security Requirement, Focus Areas, using this template. Grab it now to reap its full benefits.
-
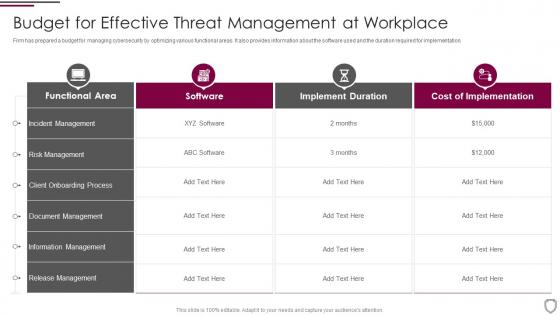 Budget for effective threat management at workplace corporate security management
Budget for effective threat management at workplace corporate security managementFirm has prepared a budget for managing cybersecurity by optimizing various functional areas. It also provides information about the software used and the duration required for implementation. Present the topic in a bit more detail with this Budget For Effective Threat Management At Workplace Corporate Security Management. Use it as a tool for discussion and navigation on Incident Management, Risk Management, Client Onboarding Process, Information Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Impact analysis for effective threat management in corporate security management
Impact analysis for effective threat management in corporate security managementThis slide portrays information regarding how firm is successful in handling security threats and is able in reducing the occurrence of threats. Present the topic in a bit more detail with this Impact Analysis For Effective Threat Management In Corporate Security Management. Use it as a tool for discussion and navigation on Impact Analysis For Effective Threat Management In Securing Workplace. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Agenda of effective information security risk management process
Agenda of effective information security risk management processIncrease audience engagement and knowledge by dispensing information using Agenda Of Effective Information Security Risk Management Process. This template helps you present information on three stages. You can also present information on Agenda using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
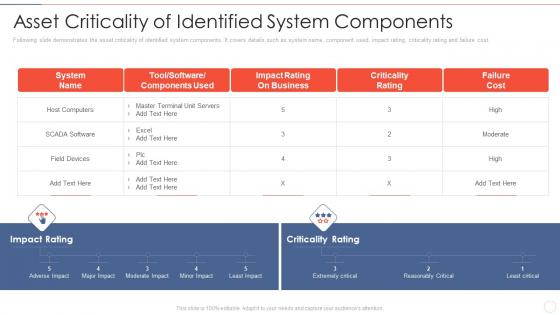 Asset components effective information security risk management process
Asset components effective information security risk management processFollowing slide demonstrates the asset criticality of identified system components. It covers details such as system name, component used, impact rating, criticality rating and failure cost.Present the topic in a bit more detail with this Asset Components Effective Information Security Risk Management Process. Use it as a tool for discussion and navigation on Impact Rating On Business, Criticality Rating, Failure Cost. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
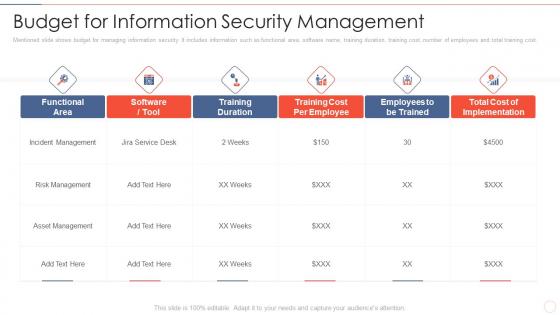 Budget for information effective information security risk management process
Budget for information effective information security risk management processMentioned slide shows budget for managing information security. It includes information such as functional area, software name, training duration, training cost, number of employees and total training cost.Deliver an outstanding presentation on the topic using this Budget For Information Effective Information Security Risk Management Process. Dispense information and present a thorough explanation of Incident Management, Asset Management, Training Duration using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Defining risk level effective information security risk management process
Defining risk level effective information security risk management processFollowing slide defines the incident risk level. It includes details about risk level, risk score and its description. Deliver an outstanding presentation on the topic using this Defining Risk Level Effective Information Security Risk Management Process. Dispense information and present a thorough explanation of Immediate Controlling, Controlling Measures, Offered By The Organization using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
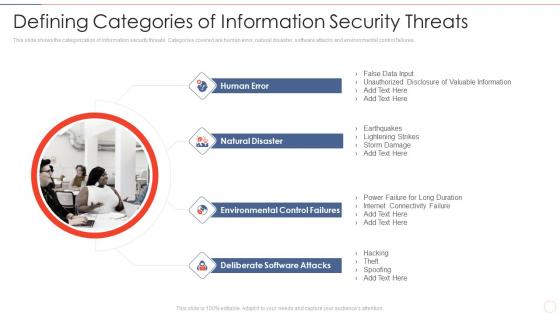 Defining security threats effective information security risk management process
Defining security threats effective information security risk management processThis slide shows the categorization of information security threats. Categories covered are human error, natural disaster, software attacks and environmental control failures.Introducing Defining Security Threats Effective Information Security Risk Management Process to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Natural Disaster, Environmental Control Failures, Deliberate Software Attacks, using this template. Grab it now to reap its full benefits.
-
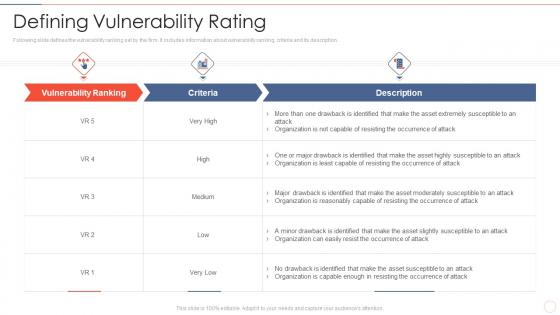 Defining vulnerability rating effective information security risk management process
Defining vulnerability rating effective information security risk management processFollowing slide defines the vulnerability ranking set by the firm. It includes information about vulnerability ranking, criteria and its description.Present the topic in a bit more detail with this Defining Vulnerability Rating Effective Information Security Risk Management Process. Use it as a tool for discussion and navigation on Occurrence Of Attack, Organization Is Reasonably, Organization Is Capable Enough. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
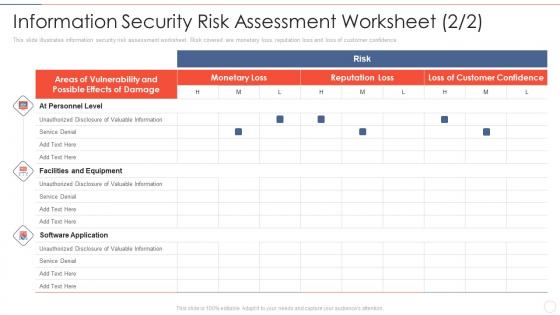 Effective information security management process information security risk assessment
Effective information security management process information security risk assessmentThis slide illustrates information security risk assessment worksheet. Risk covered are monetary loss, reputation loss and loss of customer confidence.Deliver an outstanding presentation on the topic using this Effective Information Security Management Process Information Security Risk Assessment. Dispense information and present a thorough explanation of Facilities And Equipment, Unauthorized Disclosure, Valuable Information using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
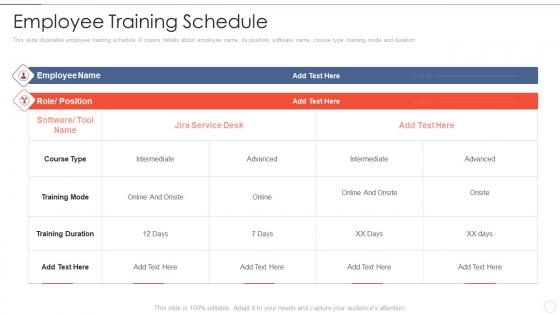 Employee training schedule effective information security risk management process
Employee training schedule effective information security risk management processThis slide illustrates employee training schedule. It covers details about employee name, its position, software name, course type, training mode and duration.Present the topic in a bit more detail with this Employee Training Schedule Effective Information Security Risk Management Process. Use it as a tool for discussion and navigation on Training Duration, Intermediate, Training Mode. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Icons slide for effective information security risk management process
Icons slide for effective information security risk management processPresenting our well crafted Icons Slide For Effective Information Security Risk Management Process set of slides. The slides include icons that are innovatively designed by our team of experts. The icons are easy to edit so you can conveniently increase or decrease their size without any loss in resolution. Therefore, grab them instantly
-
 Impact assessment matrix effective information security risk management process
Impact assessment matrix effective information security risk management processPresent the topic in a bit more detail with this Impact Assessment Matrix Effective Information Security Risk Management Process. Use it as a tool for discussion and navigation on Minor To No Infringement, Suspected Malicious Intent, Impact Medium. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
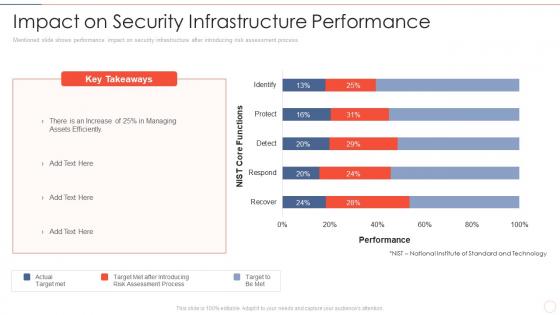 Impact on security performance effective information security risk management process
Impact on security performance effective information security risk management processMentioned slide shows performance impact on security infrastructure after introducing risk assessment process. Deliver an outstanding presentation on the topic using this Impact On Security Performance Effective Information Security Risk Management Process. Dispense information and present a thorough explanation of After Introducing, Risk Assessment Process, Assets Efficiently using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
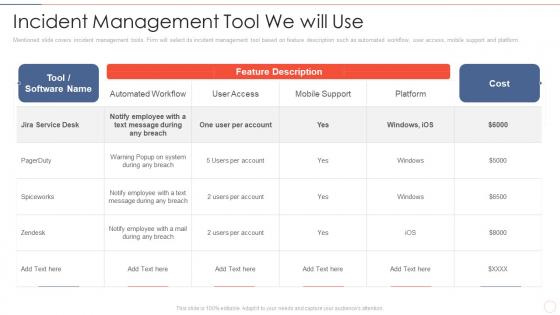 Incident management tool effective information security risk management process
Incident management tool effective information security risk management processMentioned slide covers incident management tools. Firm will select its incident management tool based on feature description such as automated workflow, user access, mobile support and platform.Present the topic in a bit more detail with this Incident Management Tool Effective Information Security Risk Management Process. Use it as a tool for discussion and navigation on Notify Employee, Message During Any Breach, Automated Workflow. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
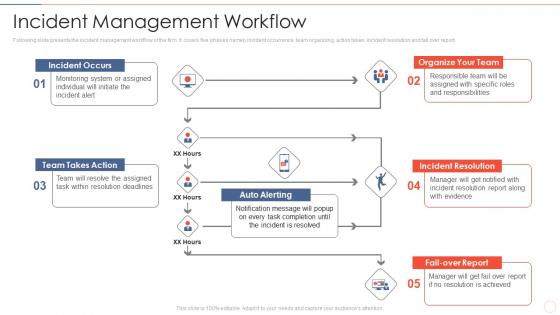 Incident management workflow effective information security risk management process
Incident management workflow effective information security risk management processFollowing slide presents the incident management workflow of the firm. It covers five phases namely incident occurrence, team organizing, action taken, incident resolution and fail over report.Introducing Incident Management Workflow Effective Information Security Risk Management Process to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Organize Your Team, Incident Resolution, Team Takes Action, using this template. Grab it now to reap its full benefits.
-
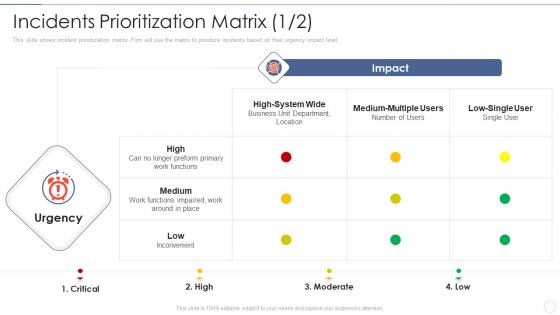 Incidents effective information security risk management process
Incidents effective information security risk management processThis slide shows incident prioritization matrix. Firm will use the matrix to prioritize incidents based on their urgency impact level.Present the topic in a bit more detail with this Incidents Effective Information Security Risk Management Process. Use it as a tool for discussion and navigation on Preform Primary Work Functions, Inconvenient, Medium Multiple. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
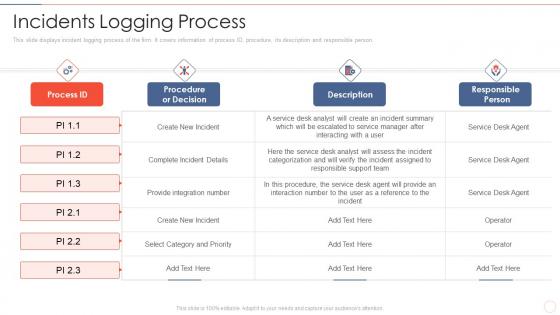 Incidents logging process effective information security risk management process
Incidents logging process effective information security risk management processThis slide displays incident logging process of the firm. It covers information of process ID, procedure, its description and responsible person.Deliver an outstanding presentation on the topic using this Incidents Logging Process Effective Information Security Risk Management Process. Dispense information and present a thorough explanation of Select Category And Priority, Procedure, The Service, Responsible Person using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
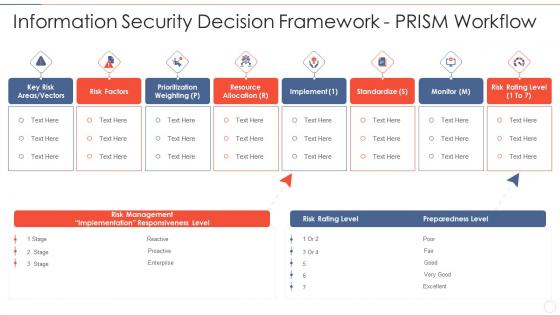 Information security decision effective information security risk management process
Information security decision effective information security risk management processIncrease audience engagement and knowledge by dispensing information using Information Security Decision Effective Information Security Risk Management Process. This template helps you present information on eight stages. You can also present information on Risk Management, Implementation Responsiveness, Prioritization Weighting using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Information security effective information security risk management process
Information security effective information security risk management processMentioned slide illustrates information security risk assessment worksheet. It include information about threat encountered, its vulnerability, asset and consequences and risk to the firm.Present the topic in a bit more detail with this Information Security Effective Information Security Risk Management Process. Use it as a tool for discussion and navigation on Asset And Consequences, Overheating In Server Room, Asset And Consequences. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
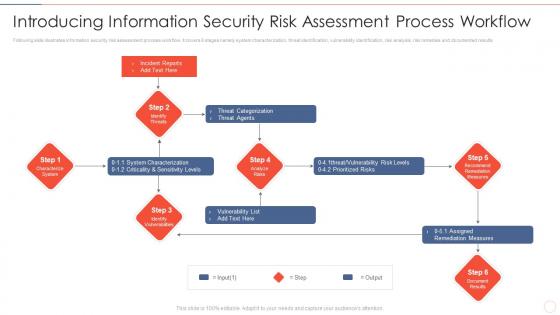 Introducing process workflow effective information security risk management process
Introducing process workflow effective information security risk management processFollowing slide illustrates information security risk assessment process workflow. It covers 6 stages namely system characterization, threat identification, vulnerability identification, risk analysis, risk remedies and documented results Deliver an outstanding presentation on the topic using this Introducing Process Workflow Effective Information Security Risk Management Process. Dispense information and present a thorough explanation of Threat Categorization, System Characterization, Assigned Remediation Measures using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
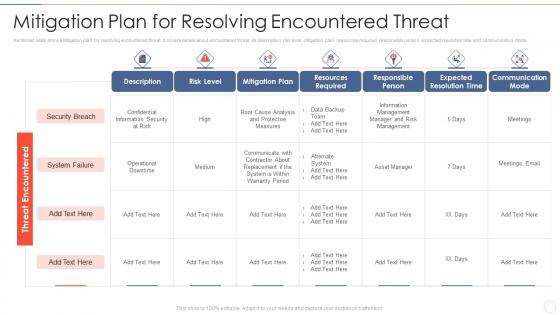 Mitigation plan for threat effective information security risk management process
Mitigation plan for threat effective information security risk management processMentioned slide shows mitigation plan for resolving encountered threat. It covers details about encountered threat, its description, risk level, mitigation plan, resources required, responsible person, expected resolution time and communication mode.Deliver an outstanding presentation on the topic using this Mitigation Plan For Threat Effective Information Security Risk Management Process. Dispense information and present a thorough explanation of Resources Required, Expected Resolution Time, Communication Mode using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
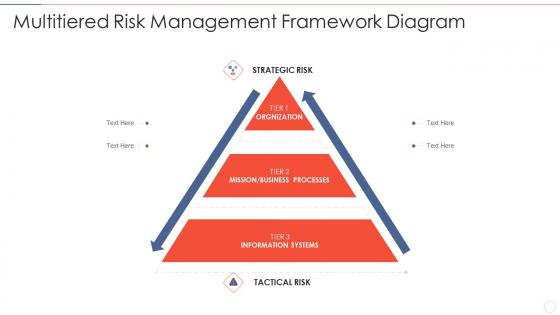 Multitiered risk effective information security risk management process
Multitiered risk effective information security risk management processIntroducing Multitiered Risk Effective Information Security Risk Management Process to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Orgnization, Mission Or Business Processes, Information Systems, using this template. Grab it now to reap its full benefits.
-
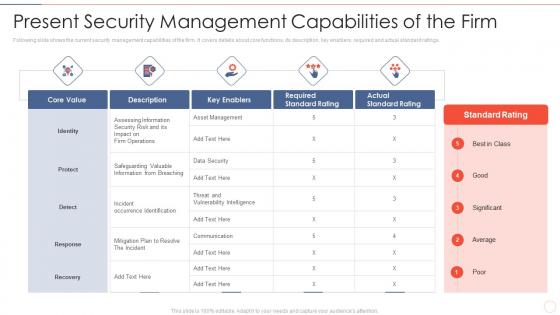 Present security effective information security risk management process
Present security effective information security risk management processFollowing slide shows the current security management capabilities of the firm. It covers details about core functions, its description, key enablers, required and actual standard ratings.Present the topic in a bit more detail with this Present Security Effective Information Security Risk Management Process. Use it as a tool for discussion and navigation on Assessing Information, Incident Occurrence Identification, Vulnerability Intelligence. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Risk reporting and likelihood effective information security risk management process
Risk reporting and likelihood effective information security risk management processMentioned slide shows encountered risk reporting and its likelihood. It includes information about risk encountered, frequency, reported by status, attack scenario, affected asset and likelihood. Deliver an outstanding presentation on the topic using this Risk Reporting And Likelihood Effective Information Security Risk Management Process. Dispense information and present a thorough explanation of Attack Scenario, Risk Encountered, Equipment Failure using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
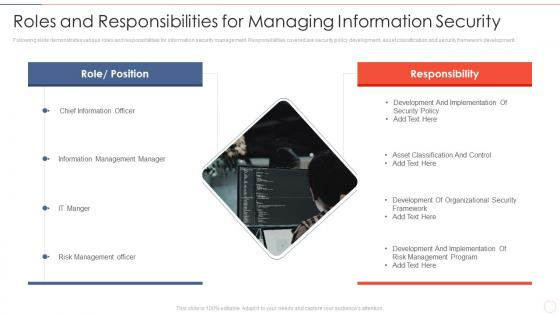 Roles and responsibilities effective information security risk management process
Roles and responsibilities effective information security risk management processFollowing slide demonstrates various roles and responsibilities for information security management. Responsibilities covered are security policy development, asset classification and security framework development.Increase audience engagement and knowledge by dispensing information using Roles And Responsibilities Effective Information Security Risk Management Process. This template helps you present information on one stage. You can also present information on Information Management Manager, Risk Management Officer, Development And Implementation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
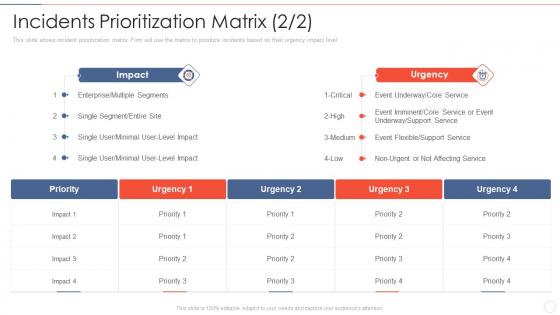 Security risk management process incidents prioritization matrix effective information
Security risk management process incidents prioritization matrix effective informationThis slide shows incident prioritization matrix. Firm will use the matrix to prioritize incidents based on their urgency impact level Present the topic in a bit more detail with this Security Risk Management Process Incidents Prioritization Matrix Effective Information. Use it as a tool for discussion and navigation on Enterprise Or Multiple Segments, Single Segment Or Entire Site, Event Underway. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Setting scenario security control effective information security risk management process
Setting scenario security control effective information security risk management processFollowing slide displays security control scenario setting. It includes scenario detail, category of security controls and controls description.Introducing Setting Scenario Security Control Effective Information Security Risk Management Process to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Management Controls, Operational Controls, Technical Controls, using this template. Grab it now to reap its full benefits.
-
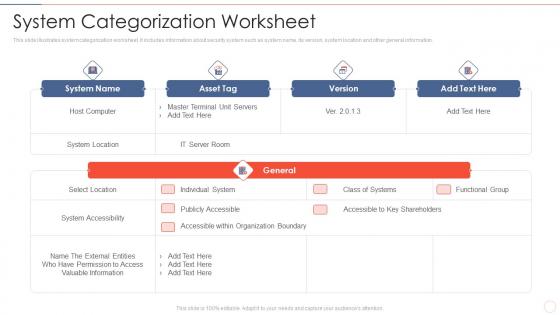 System categorization worksheet effective information security risk management process
System categorization worksheet effective information security risk management processThis slide illustrates system categorization worksheet. It includes information about security system such as system name, its version, system location and other general information.Present the topic in a bit more detail with this System Categorization Worksheet Effective Information Security Risk Management Process. Use it as a tool for discussion and navigation on System Accessibility, Accessible Within Organization Boundary, Valuable Information. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
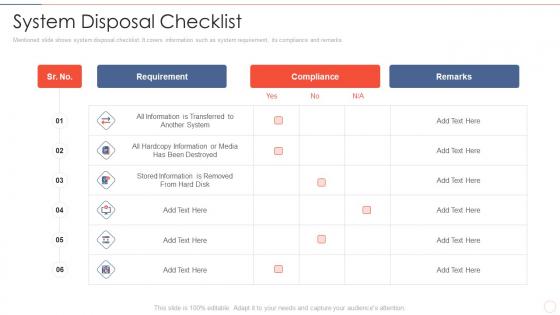 System disposal checklist effective information security risk management process
System disposal checklist effective information security risk management processMentioned slide shows system disposal checklist. It covers information such as system requirement, its compliance and remarks.Deliver an outstanding presentation on the topic using this System Disposal Checklist Effective Information Security Risk Management Process. Dispense information and present a thorough explanation of Stored Information Is Removed, Hardcopy Information, Requirement using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 System management checklist effective information security risk management process
System management checklist effective information security risk management processFollowing slide displays system management checklist. It includes system management activities and frequency of performing them.Present the topic in a bit more detail with this System Management Checklist Effective Information Security Risk Management Process. Use it as a tool for discussion and navigation on System Monitoring, Security Patches, Virus Scanning . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
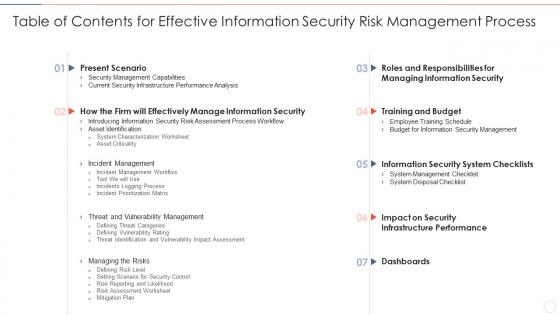 Table of contents for effective information security risk management process
Table of contents for effective information security risk management processDeliver an outstanding presentation on the topic using this Table Of Contents For Effective Information Security Risk Management Process. Dispense information and present a thorough explanation of Present Scenario, Training And Budget, Dashboards using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
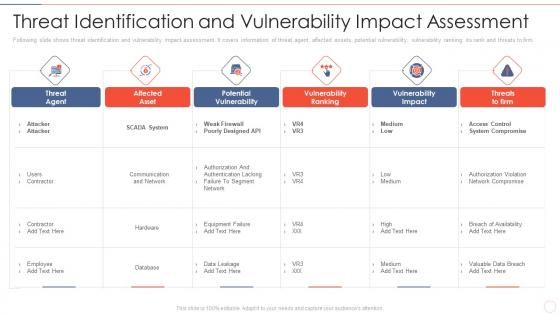 Threat assessment effective information security risk management process
Threat assessment effective information security risk management processFollowing slide shows threat identification and vulnerability impact assessment. It covers information of threat agent, affected assets, potential vulnerability, vulnerability ranking, its rank and threats to firm. Deliver an outstanding presentation on the topic using this Threat Assessment Effective Information Security Risk Management Process. Dispense information and present a thorough explanation of Affected Asset, Potential Vulnerability, Vulnerability Ranking using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Budget for effective threat management workplace cyber security risk management
Budget for effective threat management workplace cyber security risk managementFirm has prepared a budget for managing cybersecurity by optimizing various functional areas. It also provides information about the software used and the duration required for implementation. Present the topic in a bit more detail with this Budget For Effective Threat Management Workplace Cyber Security Risk Management. Use it as a tool for discussion and navigation on Incident Management, Risk Management, Client Onboarding Process, Document Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Impact analysis for effective threat management in cyber security risk management
Impact analysis for effective threat management in cyber security risk managementThis slide portrays information regarding how firm is successful in handling security threats and is able in reducing the occurrence of threats. Introducing Impact Analysis For Effective Threat Management In Cyber Security Risk Management to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Focus Areas, Actual Access Violations, Access Rights Authorized, using this template. Grab it now to reap its full benefits.
-
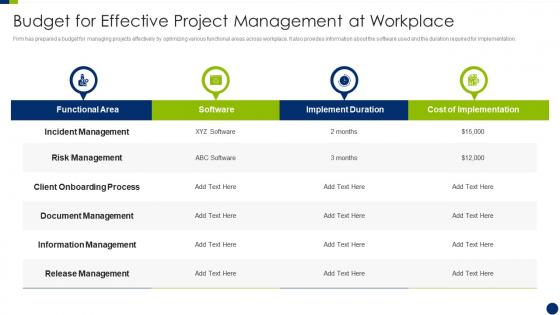 Enhancing overall project security it budget for effective project management at workplace
Enhancing overall project security it budget for effective project management at workplaceFirm has prepared a budget for managing projects effectively by optimizing various functional areas across workplace. It also provides information about the software used and the duration required for implementation. Present the topic in a bit more detail with this Enhancing Overall Project Security It Budget For Effective Project Management At Workplace. Use it as a tool for discussion and navigation on Management, Workplace, Process. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Building organizational security strategy plan budget analysis for effective security management
Building organizational security strategy plan budget analysis for effective security managementPresent the topic in a bit more detail with this Building Organizational Security Strategy Plan Budget Analysis For Effective Security Management. Use it as a tool for discussion and navigation on Analysis, Management, Workplace. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Building organizational security strategy plan effective security management at workplace
Building organizational security strategy plan effective security management at workplaceThis slide portrays information regarding how firm is successful in handling security issues or events and is able in reducing the occurrence of events. Present the topic in a bit more detail with this Building Organizational Security Strategy Plan Effective Security Management At Workplace. Use it as a tool for discussion and navigation on Management, Workplace, Information. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Building organizational security strategy plan role of management in effective corporate
Building organizational security strategy plan role of management in effective corporateThis slide portrays information regarding the responsibilities that are to be performed by board of directors, senior executives, steering committees and chief security office in order to ensure the effective corporate security governance. Deliver an outstanding presentation on the topic using this Building Organizational Security Strategy Plan Role Of Management In Effective Corporate. Dispense information and present a thorough explanation of Management, Corporate, Governance using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cybersecurity and digital business risk management checklist for effectively managing asset security
Cybersecurity and digital business risk management checklist for effectively managing asset securityFollowing slide displays system management checklist that company will use for effectively managing asset security. It also includes system management activities and frequency of performing them. Present the topic in a bit more detail with this Cybersecurity And Digital Business Risk Management Checklist For Effectively Managing Asset Security. Use it as a tool for discussion and navigation on System Monitoring, Data Backup, Security Patches . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Effective IT Security Service Excellence For Risk Mitigation
Effective IT Security Service Excellence For Risk MitigationThis slide signifies the types of security provided through information technology services. It includes surveillance like network, internet, cloud and application for mitigating risk. Introducing our Effective IT Security Service Excellence For Risk Mitigation set of slides. The topics discussed in these slides are Automated Workflows, Customization Option, Multi Channel Deployment. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Analyzing Multiple Sales Tactics For Securing New Leads Boosting Profits With New And Effective Sales
Analyzing Multiple Sales Tactics For Securing New Leads Boosting Profits With New And Effective SalesThis slide provides glimpse about employing different techniques that can help the business in new lead generation. It includes techniques such as social media marketing, cold calling, email marketing, their impact, etc. Introducing Analyzing Multiple Sales Tactics For Securing New Leads Boosting Profits With New And Effective Sales to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Email Marketing, Cold Calling, Social Media Marketing, Multiple Sales, using this template. Grab it now to reap its full benefits.
-
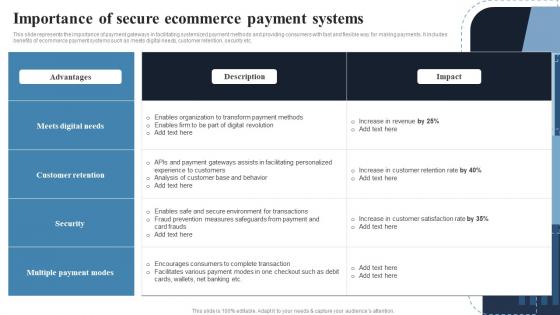 Importance Of Secure Ecommerce Payment Deploying Effective Ecommerce Management
Importance Of Secure Ecommerce Payment Deploying Effective Ecommerce ManagementThis slide represents the importance of payment gateways in facilitating systemized payment methods and providing consumers with fast and flexible way for making payments. It includes benefits of ecommerce payment systems such as meets digital needs, customer retention, security etc. Present the topic in a bit more detail with this Importance Of Secure Ecommerce Payment Deploying Effective Ecommerce Management. Use it as a tool for discussion and navigation on Meets Digital Needs, Customer Retention, Multiple Payment Modes. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Assessment Test To Measure Effectiveness Of Training Implementing Security Awareness Training
Assessment Test To Measure Effectiveness Of Training Implementing Security Awareness TrainingThe purpose of this slide is to outline a comprehensive assessment test which can be used by the trainer to evaluate the effectiveness of cyber security training plan. The questions covered in the slide is related to spam, ways to protect from cyberbullying etc. Increase audience engagement and knowledge by dispensing information using Assessment Test To Measure Effectiveness Of Training Implementing Security Awareness Training. This template helps you present information on four stages. You can also present information on Describes Spam, Cyberbullying, Protect The Confidential Data using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Strategic Plan Timeline To Develop Effective Cyber Security Strategy
Strategic Plan Timeline To Develop Effective Cyber Security StrategyThis slide signifies the strategic plan timeline to create effective cyber security project. It covers information about steps like identify, analyse, evaluate, prioritise, treat and monitor Presenting our set of slides with name Strategic Plan Timeline To Develop Effective Cyber Security Strategy. This exhibits information on six stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Identify, Evaluate, Prioritise.
-
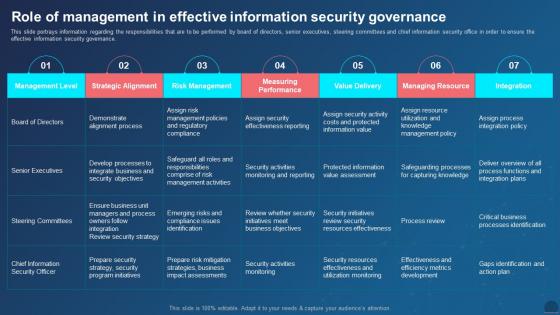 Managing Mobile Devices Role Of Management In Effective Information Security Governance
Managing Mobile Devices Role Of Management In Effective Information Security GovernanceThis slide portrays information regarding the responsibilities that are to be performed by board of directors, senior executives, steering committees and chief information security office in order to ensure the effective information security governance. Present the topic in a bit more detail with this Managing Mobile Devices Role Of Management In Effective Information Security Governance. Use it as a tool for discussion and navigation on Demonstrate Alignment Process, Critical Business Processes Identification, Steering Committees. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
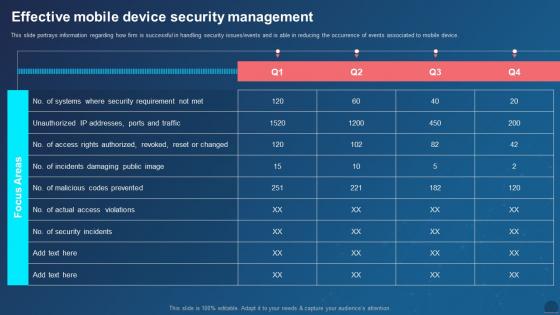 Managing Mobile Devices For Optimizing Effective Mobile Device Security Management
Managing Mobile Devices For Optimizing Effective Mobile Device Security ManagementThis slide portrays information regarding how firm is successful in handling security issues or events and is able in reducing the occurrence of events associated to mobile device. Deliver an outstanding presentation on the topic using this Managing Mobile Devices For Optimizing Effective Mobile Device Security Management. Dispense information and present a thorough explanation of Mobile Device, Security Management, Security Requirement, Codes Prevented using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
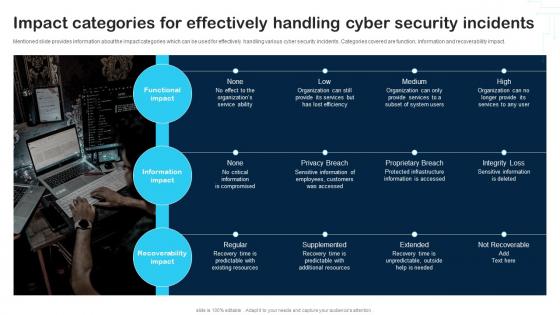 Impact Categories For Effectively Handling Cyber Security Incidents Cybersecurity Incident And Vulnerability
Impact Categories For Effectively Handling Cyber Security Incidents Cybersecurity Incident And VulnerabilityMentioned slide provides information about the impact categories which can be used for effectively handling various cyber security incidents. Categories covered are function, information and recoverability impact. Increase audience engagement and knowledge by dispensing information using Impact Categories For Effectively Handling Cyber Security Incidents Cybersecurity Incident And Vulnerability. This template helps you present information on three stages. You can also present information on Functional Impact, Information Impact, Recoverability Impact using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
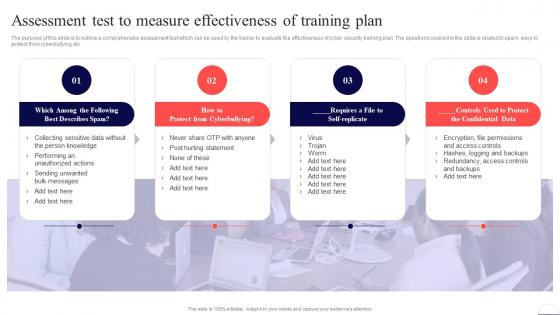 Assessment Test To Measure Effectiveness Of Training Preventing Data Breaches Through Cyber Security
Assessment Test To Measure Effectiveness Of Training Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to outline a comprehensive assessment test which can be used by the trainer to evaluate the effectiveness of cyber security training plan. The questions covered in the slide is related to spam, ways to protect from cyberbullying etc. Increase audience engagement and knowledge by dispensing information using Assessment Test To Measure Effectiveness Of Training Preventing Data Breaches Through Cyber Security. This template helps you present information on four stages. You can also present information on Cyberbullying, Confidential Data, Training Plan using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Effective Mobile Device Security Management Management And Monitoring
Effective Mobile Device Security Management Management And MonitoringThis slide portrays information regarding how firm is successful in handling security issues events and is able in reducing the occurrence of events associated to mobile device. Present the topic in a bit more detail with this Effective Mobile Device Security Management Management And Monitoring. Use it as a tool for discussion and navigation on Effective Mobile Device, Security Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
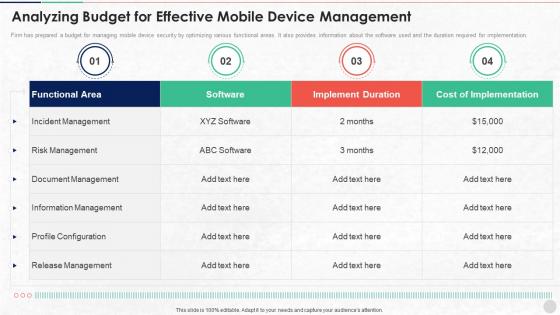 Analyzing Budget For Effective Mobile Device Management Unified Endpoint Security
Analyzing Budget For Effective Mobile Device Management Unified Endpoint SecurityFirm has prepared a budget for managing mobile device security by optimizing various functional areas. It also provides information about the software used and the duration required for implementation. Present the topic in a bit more detail with this Analyzing Budget For Effective Mobile Device Management Unified Endpoint Security. Use it as a tool for discussion and navigation on Incident Management, Risk Management, Information Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
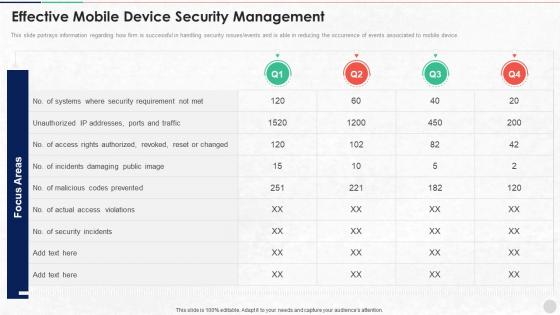 Effective Mobile Device Security Management Unified Endpoint Security
Effective Mobile Device Security Management Unified Endpoint SecurityThis slide portrays information regarding how firm is successful in handling security issues or events and is able in reducing the occurrence of events associated to mobile device. Present the topic in a bit more detail with this Effective Mobile Device Security Management Unified Endpoint Security. Use it as a tool for discussion and navigation on Security Requirement, Rights Authorized, Actual Access . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
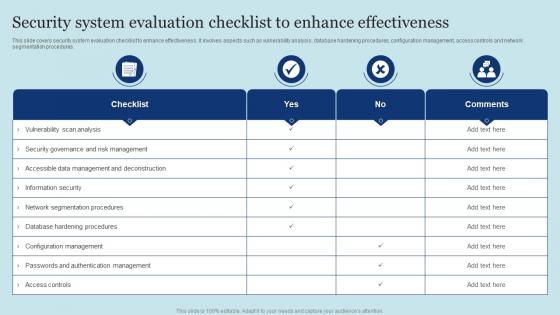 Security System Evaluation Checklist To Enhance Effectiveness
Security System Evaluation Checklist To Enhance EffectivenessThis slide covers security system evaluation checklist to enhance effectiveness. It involves aspects such as vulnerability analysis, database hardening procedures, configuration management, access controls and network segmentation procedures. Introducing our Security System Evaluation Checklist To Enhance Effectiveness set of slides. The topics discussed in these slides are Security System Evaluation, Checklist, Enhance Effectiveness. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Managing Mobile Device Solutions For Workforce Effective Mobile Device Security Management
Managing Mobile Device Solutions For Workforce Effective Mobile Device Security ManagementThis slide portrays information regarding how firm is successful in handling security issues or events and is able in reducing the occurrence of events associated to mobile device. Deliver an outstanding presentation on the topic using this Managing Mobile Device Solutions For Workforce Effective Mobile Device Security Management. Dispense information and present a thorough explanation of Mobile Device, Security Management, Codes Prevented using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
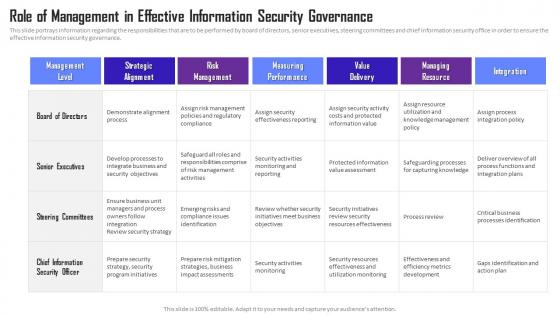 Managing Mobile Device Solutions Role Of Management In Effective Information Security Governance
Managing Mobile Device Solutions Role Of Management In Effective Information Security GovernanceThis slide portrays information regarding the responsibilities that are to be performed by board of directors, senior executives, steering committees and chief information security office in order to ensure the effective information security governance. Present the topic in a bit more detail with this Managing Mobile Device Solutions Role Of Management In Effective Information Security Governance. Use it as a tool for discussion and navigation on Role Of Management, Effective Information, Security Governance. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Communication Plan For Effective Incident Management Security Incident Response Playbook
Communication Plan For Effective Incident Management Security Incident Response PlaybookThis slide portrays communication plan for successfully managing cyber incidents. Sections covered are deliverable info, recipient, delivery method, schedule and responsible person. Deliver an outstanding presentation on the topic using this Communication Plan For Effective Incident Management Security Incident Response Playbook. Dispense information and present a thorough explanation of Management, Communication, Successfully using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
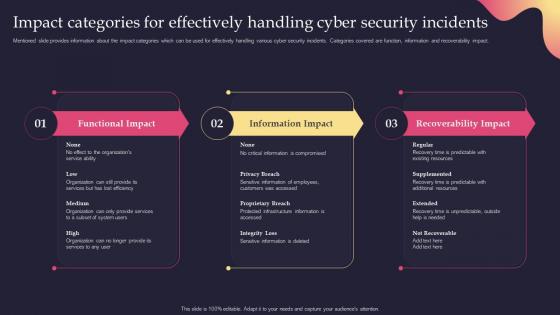 Security Incident Response Playbook Impact Categories For Effectively Handling Cyber Security Incidents
Security Incident Response Playbook Impact Categories For Effectively Handling Cyber Security IncidentsMentioned slide provides information about the impact categories which can be used for effectively handling various cyber security incidents. Categories covered are function, information and recoverability impact. Present the topic in a bit more detail with this Security Incident Response Playbook Impact Categories For Effectively Handling Cyber Security Incidents. Use it as a tool for discussion and navigation on Categories, Effectively, Information Impact. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
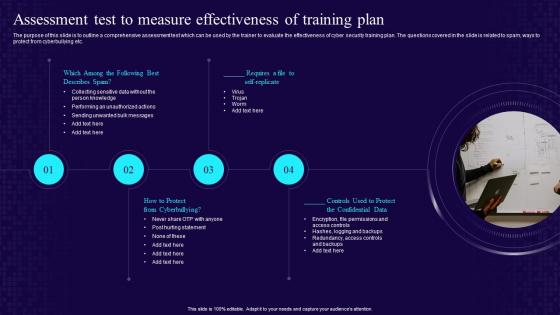 Assessment Test To Measure Effectiveness Of Training Plan Developing Cyber Security Awareness
Assessment Test To Measure Effectiveness Of Training Plan Developing Cyber Security AwarenessThe purpose of this slide is to outline a comprehensive assessment test which can be used by the trainer to evaluate the effectiveness of cyber security training plan. The questions covered in the slide is related to spam, ways to protect from cyberbullying etc. Increase audience engagement and knowledge by dispensing information using Assessment Test To Measure Effectiveness Of Training Plan Developing Cyber Security Awareness. This template helps you present information on four stages. You can also present information on Self Replicate, Confidential Data, Cyberbullying, Training Plan using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.



