Powerpoint Templates and Google slides for Security Effectiveness
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Checklist To Conduct Effective Web Security
Checklist To Conduct Effective Web SecurityThis slide showcases actions performed while conducting web security in an organization which include actions, person responsible, status, etc. Presenting our well structured Checklist To Conduct Effective Web Security. The topics discussed in this slide are Authentication And Authorization, Session Management, Connectivity. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Roadmap For Implementing Effective Web Security
Roadmap For Implementing Effective Web SecurityThis slide outlines the steps that an organization should take while conducting web security such as education, infrastructure security, etc. Presenting our set of slides with name Roadmap For Implementing Effective Web Security. This exhibits information on seven stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Monitoring, Application Security, Incident Response, Assessment And Planning.
-
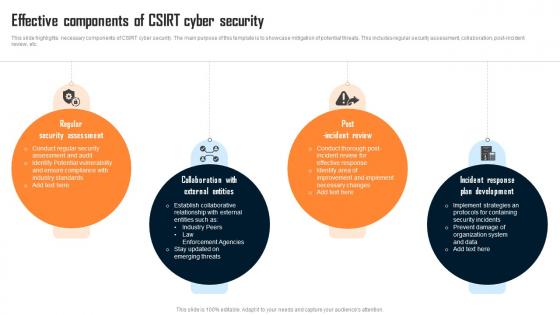 Effective Components Of Csirt Cyber Security
Effective Components Of Csirt Cyber SecurityThis slide highlights necessary components of CSIRT cyber security. The main purpose of this template is to showcase mitigation of potential threats. This includes regular security assessment, collaboration, post incident review, etc. Presenting our set of slides with Effective Components Of Csirt Cyber Security. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Security Assessment, External Entities, Incident Review.
-
 Best Practices For Effective Server Security Management
Best Practices For Effective Server Security ManagementFollowing slide highlights server security management best practices, also including elements such as server management, physical security, update software, etc. Introducing our Best Practices For Effective Server Security Management set of slides. The topics discussed in these slides are Server Management, Physical Security, Update Software. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Securing Food Safety In Online Analyzing Food Delivery App Features For Effective
Securing Food Safety In Online Analyzing Food Delivery App Features For EffectiveThis slide covers application features for restaurant business such as real time order tracking, notification and alerts and enabling promotions and discounts. Introducing Securing Food Safety In Online Analyzing Food Delivery App Features For Effective to increase your presentation threshold. Encompassed with One stages, this template is a great option to educate and entice your audience. Dispence information on Pricing, Features, Personalization, POS Integration, using this template. Grab it now to reap its full benefits.
-
 Securing Food Safety In Online Route Optimization Software For Effective Food
Securing Food Safety In Online Route Optimization Software For Effective FoodThis slide covers utilizing route optimization software to get real time updates. It involves key features such as real time routes updates, temperature control and minimizes food spoilage. Introducing Securing Food Safety In Online Route Optimization Software For Effective Food to increase your presentation threshold. Encompassed with Three stages, this template is a great option to educate and entice your audience. Dispence information on Real Time Updates, Temperature Control, Minimizes Food Spoilage, using this template. Grab it now to reap its full benefits.
-
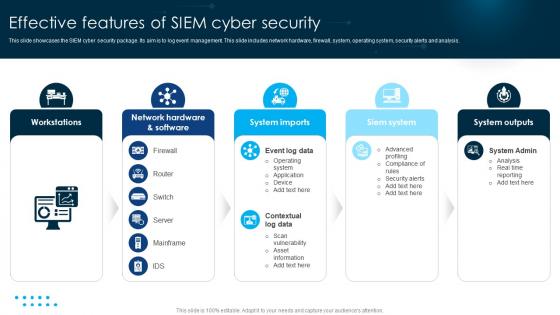 Effective Features Of SIEM Cyber Security
Effective Features Of SIEM Cyber SecurityThis slide showcases the SIEM cyber security package. Its aim is to log event management. This slide includes network hardware, firewall, system, operating system, security alerts and analysis. Introducing our premium set of slides with name Effective Features Of SIEM Cyber Security. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Workstations, System Imports, Siem System. So download instantly and tailor it with your information.
-
 KPI Metrics Dashboard To Effectively Building A Security Awareness Program
KPI Metrics Dashboard To Effectively Building A Security Awareness ProgramThe purpose of this slide is to highlight performance KPI dashboard used to monitor the cyber threat management. The metrics highlighted in the slide are risk score, compliance status, threat level, monitoring and operational status. Present the topic in a bit more detail with this KPI Metrics Dashboard To Effectively Building A Security Awareness Program. Use it as a tool for discussion and navigation on Threat Management, Metrics Dashboard. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
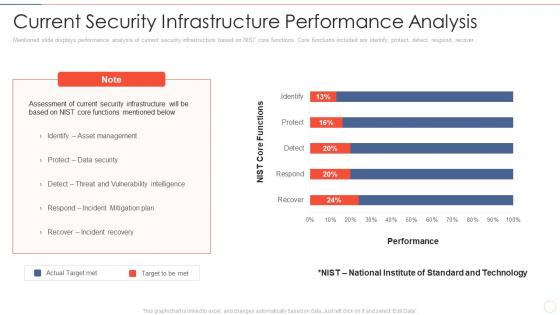 Effective information security current security infrastructure performance analysis
Effective information security current security infrastructure performance analysisMentioned slide displays performance analysis of current security infrastructure based on NIST core functions. Core functions included are identify, protect, detect, respond, recover. Deliver an outstanding presentation on the topic using this Effective Information Security Current Security Infrastructure Performance Analysis. Dispense information and present a thorough explanation of Performance, Actual Target Met, Target To Be Met, Asset Management, Data Security, Incident Recovery using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
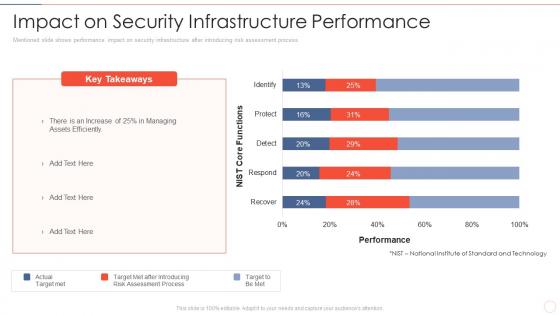 Effective information security impact on security infrastructure performance
Effective information security impact on security infrastructure performanceMentioned slide shows performance impact on security infrastructure after introducing risk assessment process. Deliver an outstanding presentation on the topic using this Effective Information Security Impact On Security Infrastructure Performance. Dispense information and present a thorough explanation of NIST Core Functions, Performance, Actual Target met using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Effective information security information security risk management dashboard
Effective information security information security risk management dashboardFollowing slide covers information security risk management dashboard. It include KPIs such as risk analysis progress, percent risk, response progress for risks and number of risks encountered. Deliver an outstanding presentation on the topic using this Effective Information Security Information Security Risk Management Dashboard. Dispense information and present a thorough explanation of Risk Threshold, Risk Analysis, Progress Response, Progress Risks Threshold using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
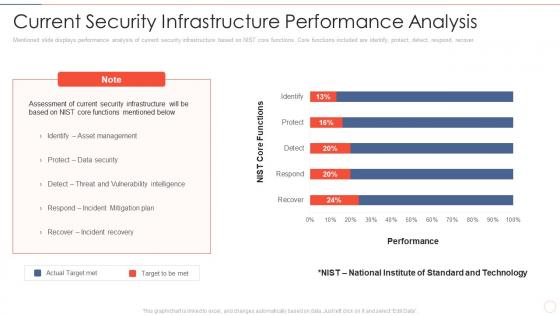 Current security infrastructure effective information security risk management process
Current security infrastructure effective information security risk management processMentioned slide displays performance analysis of current security infrastructure based on NIST core functions. Core functions included are identify, protect, detect, respond, recover. Present the topic in a bit more detail with this Current Security Infrastructure Effective Information Security Risk Management Process. Use it as a tool for discussion and navigation on Asset Management, Incident Mitigation Plan, Incident Recovery. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Information security dashboard effective information security risk management process
Information security dashboard effective information security risk management processFollowing slide covers information security risk management dashboard. It include KPIs such as risk analysis progress, persent risk, response progress for risks and number of risks encountered.Present the topic in a bit more detail with this Information Security Dashboard Effective Information Security Risk Management Process. Use it as a tool for discussion and navigation on Risk Rating Breakdown, Risk Analysis Progress Action Plan Breakdown. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
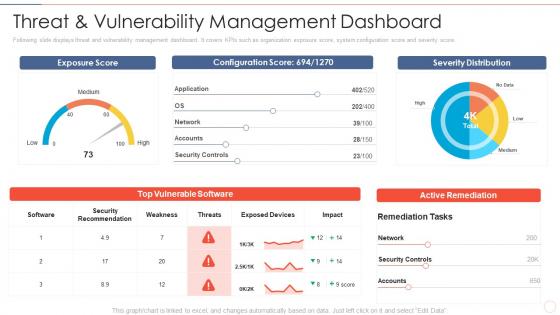 Threat and dashboard effective information security risk management process
Threat and dashboard effective information security risk management processFollowing slide displays threat and vulnerability management dashboard. It covers KPIs such as organization exposure score, system configuration score and severity score. Present the topic in a bit more detail with this Threat And Dashboard Effective Information Security Risk Management Process. Use it as a tool for discussion and navigation on Security Recommendation, Security Controls, Active Remediation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
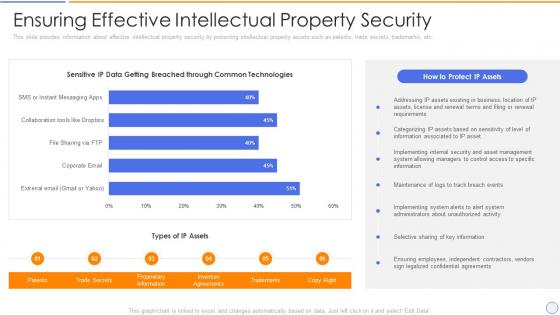 Building organizational security strategy plan ensuring effective intellectual property security
Building organizational security strategy plan ensuring effective intellectual property securityThis slide provides information about effective intellectual property security by protecting intellectual property assets such as patents, trade secrets, trademarks, etc. Present the topic in a bit more detail with this Building Organizational Security Strategy Plan Ensuring Effective Intellectual Property Security. Use it as a tool for discussion and navigation on Information, Intellectual, Trademarks. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
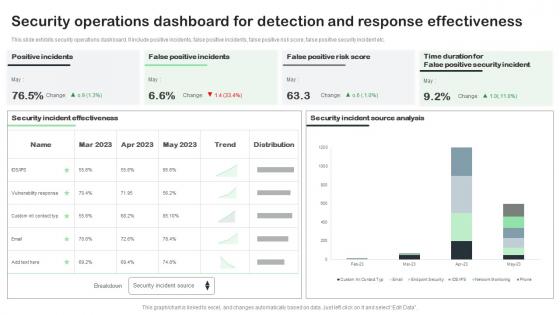 Security Operations Dashboard For Detection And Response Effectiveness
Security Operations Dashboard For Detection And Response EffectivenessThis slide exhibits security operations dashboard. It include positive incidents, false positive incidents, false positive risk score, false positive security incident etc. Introducing our Security Operations Dashboard For Detection And Response Effectiveness set of slides. The topics discussed in these slides are Security Operations Dashboard, Detection, Response Effectiveness. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
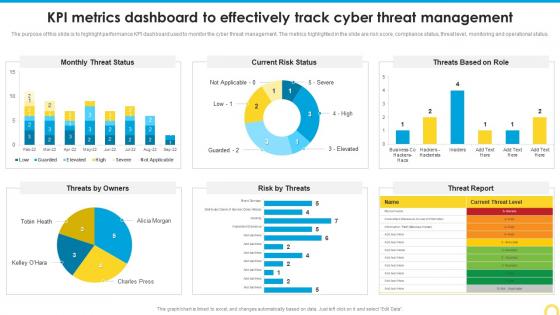
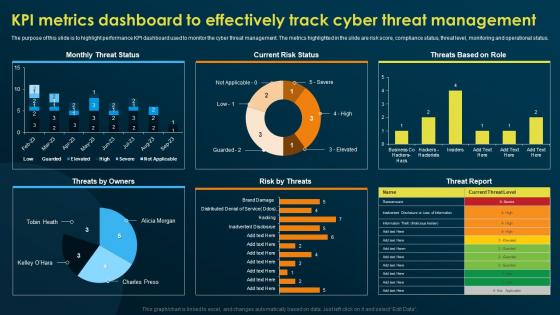 KPI Metrics Dashboard To Effectively Track Cyber Threat Implementing Security Awareness Training
KPI Metrics Dashboard To Effectively Track Cyber Threat Implementing Security Awareness TrainingThe purpose of this slide is to highlight performance KPI dashboard used to monitor the cyber threat management. The metrics highlighted in the slide are risk score, compliance status, threat level, monitoring and operational status. Present the topic in a bit more detail with this KPI Metrics Dashboard To Effectively Track Cyber Threat Implementing Security Awareness Training. Use it as a tool for discussion and navigation on Current Risk Status, Threats By Owners, Risk By Threats. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Kpi Metrics Dashboard To Effectively Track Cyber Threat Preventing Data Breaches Through Cyber Security
Kpi Metrics Dashboard To Effectively Track Cyber Threat Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to highlight performance KPI dashboard used to monitor the cyber threat management. The metrics highlighted in the slide are risk score, compliance status, threat level, monitoring and operational status. Present the topic in a bit more detail with this Kpi Metrics Dashboard To Effectively Track Cyber Threat Preventing Data Breaches Through Cyber Security. Use it as a tool for discussion and navigation on Risk By Threats, Threat Report, Current Risk Status. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
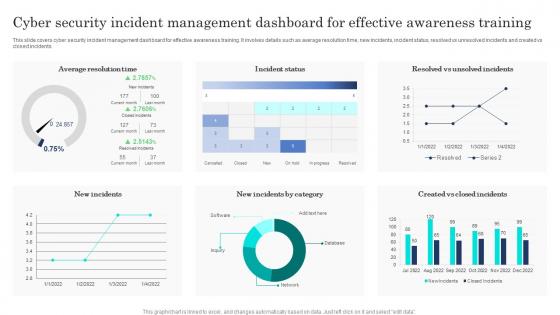 Cyber Security Incident Management Dashboard For Effective Awareness Training
Cyber Security Incident Management Dashboard For Effective Awareness TrainingThis slide covers cyber security incident management dashboard for effective awareness training. It involves details such as average resolution time, new incidents, incident status, resolved vs unresolved incidents and created vs closed incidents. Presenting our well-structured Cyber Security Incident Management Dashboard For Effective Awareness Training. The topics discussed in this slide are Cyber Security, Incident Management Dashboard, Effective Awareness Training. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
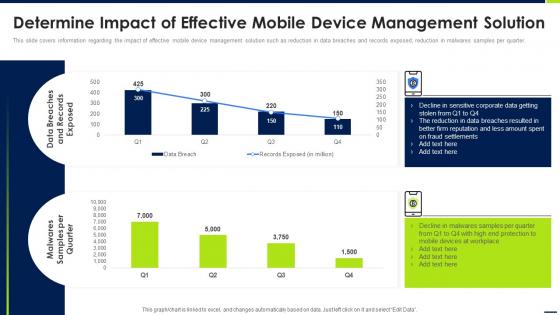 Determine Impact Of Effective Mobile Android Device Security Management
Determine Impact Of Effective Mobile Android Device Security ManagementThis slide covers information regarding the impact of effective mobile device management solution such as reduction in data breaches and records exposed, reduction in malwares samples per quarter. Deliver an outstanding presentation on the topic using this Determine Impact Of Effective Mobile Android Device Security Management. Dispense information and present a thorough explanation of Malwares Samples, Data Breaches, Device Management Solution using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
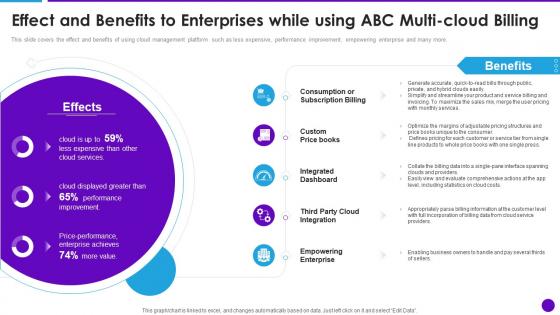 Cloud Architecture And Security Review Effect And Benefits To Enterprises While Using Abc Multi Cloud
Cloud Architecture And Security Review Effect And Benefits To Enterprises While Using Abc Multi CloudThis slide covers the effect and benefits of using cloud management platform such as less expensive, performance improvement, empowering enterprise and many more. Present the topic in a bit more detail with this Cloud Architecture And Security Review Effect And Benefits To Enterprises While Using Abc Multi Cloud. Use it as a tool for discussion and navigation on Consumption Or Subscription Billing, Integrated Dashboard, Empowering Enterprise. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 KPI Metrics Dashboard To Effectively Track Cyber Threat Management Conducting Security Awareness
KPI Metrics Dashboard To Effectively Track Cyber Threat Management Conducting Security AwarenessThe purpose of this slide is to highlight performance KPI dashboard used to monitor the cyber threat management. The metrics highlighted in the slide are risk score, compliance status, threat level, monitoring and operational status. Deliver an outstanding presentation on the topic using this KPI Metrics Dashboard To Effectively Track Cyber Threat Management Conducting Security Awareness. Dispense information and present a thorough explanation of Monthly Threat Status, Current Risk Status, Threats Based Role using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
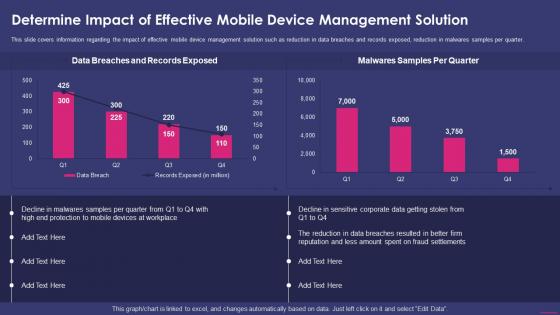 Determine Impact Of Effective Mobile Nterprise Mobile Security For On Device
Determine Impact Of Effective Mobile Nterprise Mobile Security For On DeviceThis slide covers information regarding the impact of effective mobile device management solution such as reduction in data breaches and records exposed, reduction in malwares samples per quarter.Deliver an outstanding presentation on the topic using this Determine Impact Of Effective Mobile Nterprise Mobile Security For On Device. Dispense information and present a thorough explanation of Records Exposed, Malwares Samples, Devices Workplace using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Developing Cyber Security Awareness KPI Metrics Dashboard To Effectively Track Cyber Threat Management
Developing Cyber Security Awareness KPI Metrics Dashboard To Effectively Track Cyber Threat ManagementThe purpose of this slide is to highlight performance KPI dashboard used to monitor the cyber threat management. The metrics highlighted in the slide are risk score, compliance status, threat level, monitoring and operational status. Present the topic in a bit more detail with this Developing Cyber Security Awareness KPI Metrics Dashboard To Effectively Track Cyber Threat Management. Use it as a tool for discussion and navigation on KPI Metrics Dashboard, Effectively Track Cyber, Threat Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 SecOps Effective Implementation Impact On Security Breaches Ppt Elements
SecOps Effective Implementation Impact On Security Breaches Ppt ElementsThis slide outlines the successful implementation impact of SecOps on organizational security breaches. The purpose of this slide is to highlight the number of reduced security breaches inside a company after implementing SecOps. Security breaches include phishing, network intrusion, and so on. Present the topic in a bit more detail with this SecOps Effective Implementation Impact On Security Breaches Ppt Elements. Use it as a tool for discussion and navigation on Security Breaches, Implementing Secops System. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Effective It Cost Optimization Initiatives Strategic Plan To Secure It Infrastructure Strategy SS V
Effective It Cost Optimization Initiatives Strategic Plan To Secure It Infrastructure Strategy SS VThis slide provides information regarding effective IT cost optimization strategies for IT executives such as revamping technology procurement, DevOps deployment, enabling business process reengineering, etc. Increase audience engagement and knowledge by dispensing information using Effective It Cost Optimization Initiatives Strategic Plan To Secure It Infrastructure Strategy SS V. This template helps you present information on four stages. You can also present information on Revamping Technology Procurement, Enabling Business Process Reengineering, Optimization Initiatives using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
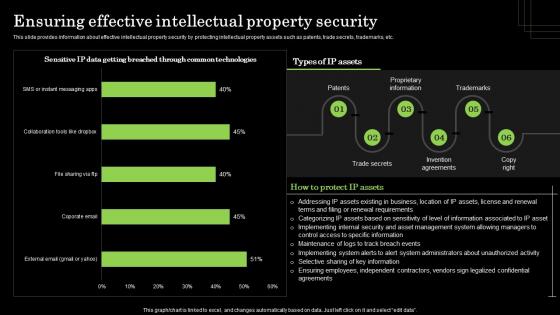 Ensuring Effective Intellectual Property Security Defense Plan To Protect Firm Assets
Ensuring Effective Intellectual Property Security Defense Plan To Protect Firm AssetsThis slide provides information about effective intellectual property security by protecting intellectual property assets such as patents, trade secrets, trademarks, etc. Present the topic in a bit more detail with this Ensuring Effective Intellectual Property Security Defense Plan To Protect Firm Assets. Use it as a tool for discussion and navigation on Proprietary Information, Trademarks, Invention Agreements. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Icons Slide Information Security Program For Effective Cybersecurity Risk Management
Icons Slide Information Security Program For Effective Cybersecurity Risk ManagementIntroducing our well researched set of slides titled Icons Slide Information Security Program For Effective Cybersecurity Risk Management. It displays a hundred percent editable icons. You can use these icons in your presentation to captivate your audiences attention. Download now and use it multiple times.
-
 Checklist For Effectively Managing Asset Security Risk Based Methodology To Cyber
Checklist For Effectively Managing Asset Security Risk Based Methodology To CyberFollowing slide displays system management checklist that company will use for effectively managing asset security. It also includes system management activities and frequency of performing them.Increase audience engagement and knowledge by dispensing information using Checklist For Effectively Managing Asset Security Risk Based Methodology To Cyber This template helps you present information on one stage. You can also present information on System Monitoring, Data Backup, Security Patches using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Checklist For Effectively Managing Asset Security Introducing A Risk Based Approach
Checklist For Effectively Managing Asset Security Introducing A Risk Based ApproachFollowing slide displays system management checklist that company will use for effectively managing asset security. It also includes system management activities and frequency of performing them.Introducing Checklist For Effectively Managing Asset Security Introducing A Risk Based Approach to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispence information on System Monitoring, Virus Scanning, System Monitoring using this template. Grab it now to reap its full benefits.
-
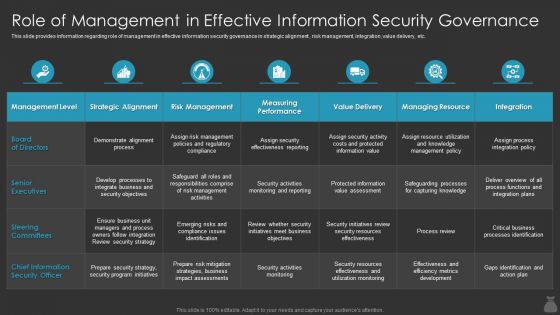 F472 Role Of Management In Effective Information Security It Cost Optimization Priorities By Cios
F472 Role Of Management In Effective Information Security It Cost Optimization Priorities By CiosThis slide provides information regarding role of management in effective information security governance in strategic alignment , risk management, integration, value delivery, etc. Deliver an outstanding presentation on the topic using this F472 Role Of Management In Effective Information Security It Cost Optimization Priorities By Cioss. Dispense information and present a thorough explanation of Information, Security, Governance using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
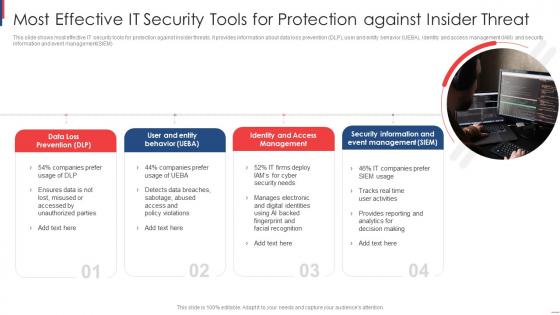 Most Effective It Security Tools For Protection Against Insider Threat
Most Effective It Security Tools For Protection Against Insider ThreatThis slide shows most effective IT security tools for protection against insider threats. It provides information about data loss prevention DLP, user and entity behavior UEBA, identity and access management IAM and security information and event management SIEM Introducing our premium set of slides with Most Effective It Security Tools For Protection Against Insider Threat. Elucidate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Data Loss Prevention, User Entity Behavior, Identity Access Management. So download instantly and tailor it with your information.
-
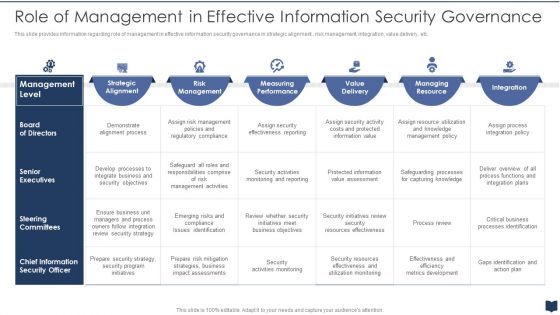 Cios Cost Optimization Playbook Role Of Management Effective Information Security Governance
Cios Cost Optimization Playbook Role Of Management Effective Information Security GovernanceThis slide provides information regarding role of management in effective information security governance in strategic alignment , risk management, integration, value delivery, etc. Deliver an outstanding presentation on the topic using this Cios Cost Optimization Playbook Role Of Management Effective Information Security Governance. Dispense information and present a thorough explanation of Information, Security, Governance using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Effective Mobile Device Management Ensuring Checklist For Mobile Security Deployment
Effective Mobile Device Management Ensuring Checklist For Mobile Security DeploymentThis slide provides information regarding mobile device security deployment checklist in terms of device security, protection against malicious codes. Present the topic in a bit more detail with this Effective Mobile Device Management Ensuring Checklist For Mobile Security Deployment. Use it as a tool for discussion and navigation on Ensuring Checklist For Mobile Security Deployment. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Effective Mobile Device Security Management Ppt Template
Effective Mobile Device Security Management Ppt TemplateThis slide portrays information regarding how firm is successful in handling security issues events and is able in reducing the occurrence of events associated to mobile device. Present the topic in a bit more detail with this Effective Mobile Device Security Management Ppt Template. Use it as a tool for discussion and navigation on Effective Mobile Device Security Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Implementing Mobile Device Security Effective Mobile Device Management Ppt Formats
Implementing Mobile Device Security Effective Mobile Device Management Ppt FormatsThis slide portrays information regarding optimization of current mobile device security framework. The IT department will require to fulfill crucial activities in specific timeframe. Present the topic in a bit more detail with this Implementing Mobile Device Security Effective Mobile Device Management Ppt Formats. Use it as a tool for discussion and navigation on Implement Enterprise Security Program, Implement Control Environment, Implement Security Processes. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Agenda Security Program For Effective Cybersecurity Risk Management
Agenda Security Program For Effective Cybersecurity Risk ManagementIntroducing Agenda Security Program For Effective Cybersecurity Risk Management to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Digitalization, Cybersecurity, Business, using this template. Grab it now to reap its full benefits.
-
 Information Security Program Cybersecurity Checklist Effectively Managing Asset Security
Information Security Program Cybersecurity Checklist Effectively Managing Asset SecurityFollowing slide displays system management checklist that company will use for effectively managing asset security. It also includes system management activities and frequency of performing them. Present the topic in a bit more detail with this Information Security Program Cybersecurity Checklist Effectively Managing Asset Security. Use it as a tool for discussion and navigation on Checklist For Effectively Managing Asset Security. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
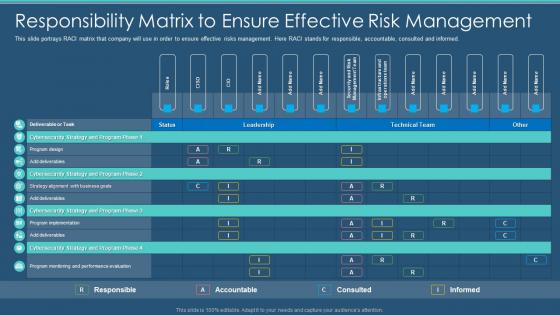 Information Security Program Responsibility Matrix To Ensure Effective Risk Management
Information Security Program Responsibility Matrix To Ensure Effective Risk ManagementThis slide portrays RACI matrix that company will use in order to ensure effective risks management. Here RACI stands for responsible, accountable, consulted and informed. Present the topic in a bit more detail with this Information Security Program Responsibility Matrix To Ensure Effective Risk Management. Use it as a tool for discussion and navigation on Responsibility, Management, Accountable. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
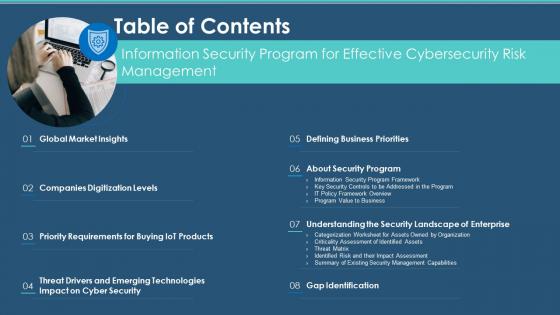 Table Of Contents Information Security Program For Effective Cybersecurity Risk Management
Table Of Contents Information Security Program For Effective Cybersecurity Risk ManagementIncrease audience engagement and knowledge by dispensing information using Table Of Contents Information Security Program For Effective Cybersecurity Risk Management. This template helps you present information on eight stages. You can also present information on Requirements, Technologies, Gap Identification using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
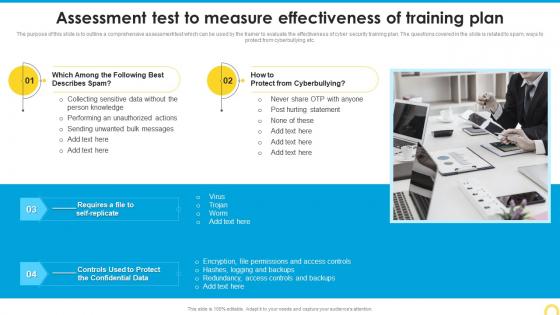 Assessment Test To Measure Effectiveness Building A Security Awareness Program
Assessment Test To Measure Effectiveness Building A Security Awareness ProgramThe purpose of this slide is to outline a comprehensive assessment test which can be used by the trainer to evaluate the effectiveness of cyber security training plan. The questions covered in the slide is related to spam, ways to protect from cyberbullying etc. Increase audience engagement and knowledge by dispensing information using Assessment Test To Measure Effectiveness Building A Security Awareness Program. This template helps you present information on two stages. You can also present information on Protect, Training Plan, Measure Effectiveness using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
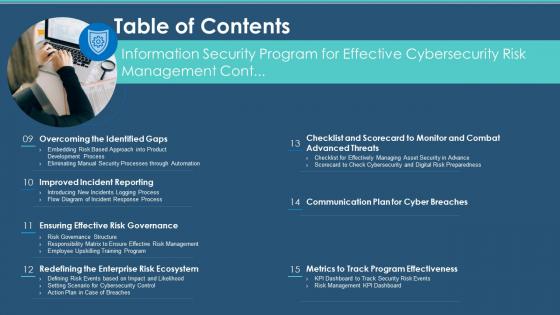 Security Program Effective Cybersecurity Risk Management Table Of Contents
Security Program Effective Cybersecurity Risk Management Table Of ContentsIncrease audience engagement and knowledge by dispensing information using Security Program Effective Cybersecurity Risk Management Table Of Contents. This template helps you present information on seven stages. You can also present information on Risk Governance, Enterprise Risk Ecosystem, Program Effectiveness using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Incident Response Playbook Impact Categories For Effectively Handling Cyber Security Incidents
Incident Response Playbook Impact Categories For Effectively Handling Cyber Security IncidentsMentioned slide provides information about the impact categories which can be used for effectively handling various cyber security incidents. Categories covered are function, information and recoverability impact. Increase audience engagement and knowledge by dispensing information using Incident Response Playbook Impact Categories For Effectively Handling Cyber Security Incidents. This template helps you present information on three stages. You can also present information on Functional Impact, Information Impact, Recoverability Impact using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
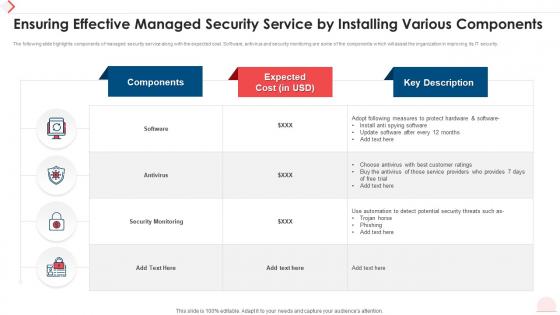 Ensuring Effective Managed Security Service By Installing Various Components
Ensuring Effective Managed Security Service By Installing Various ComponentsThe following slide highlights components of managed security service along with the expected cost. Software, antivirus and security monitoring are some of the components which will assist the organization in improving its IT security. Presenting our well structured Ensuring Effective Managed Security Service By Installing Various Components. The topics discussed in this slide are Expected Cost, Security Monitoring, Best Customer Ratings. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Managed Security Service Strategies For Effective Content Management
Managed Security Service Strategies For Effective Content ManagementPresenting our set of slides with Managed Security Service Strategies For Effective Content Management. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Clean Up Plugins, Scan CMS Platform, Use Latest Version, Strategies.
-
 Defining risk level effective information security
Defining risk level effective information securityFollowing slide defines the incident risk level. It includes details about risk level, risk score and its description. Present the topic in a bit more detail with this Defining Risk Level Effective Information Security. Use it as a tool for discussion and navigation on Risk Level, Score, Extreme, High, Medium, Low. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
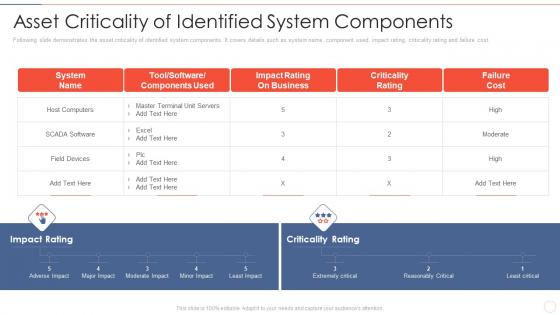 Effective information security asset criticality of identified system components
Effective information security asset criticality of identified system componentsFollowing slide demonstrates the asset criticality of identified system components. It covers details such as system name, component used, impact rating, criticality rating and failure cost. Deliver an outstanding presentation on the topic using this Effective Information Security Asset Criticality Of Identified System Components. Dispense information and present a thorough explanation of Host Computers, Impact Rating, Business, Criticality Rating using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
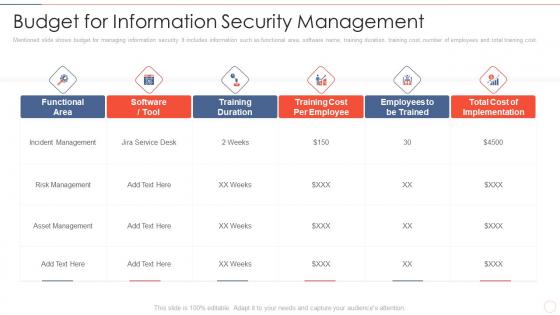 Effective information security budget for information security management
Effective information security budget for information security managementMentioned slide shows budget for managing information security. It includes information such as functional area, software name, training duration, training cost, number of employees and total training cost. Present the topic in a bit more detail with this Effective Information Security Budget For Information Security Management. Use it as a tool for discussion and navigation on Incident Management, Risk Management, Asset Management . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
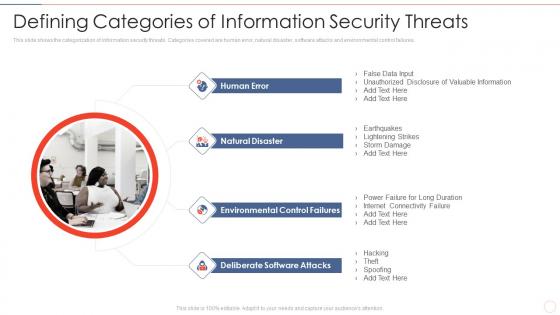 Effective information security defining categories of information security threats
Effective information security defining categories of information security threatsThis slide shows the categorization of information security threats. Categories covered are human error, natural disaster, software attacks and environmental control failures. Increase audience engagement and knowledge by dispensing information using Effective Information Security Defining Categories Of Information Security Threats. This template helps you present information on four stages. You can also present information on Human Error, Natural Disaster, Environmental Control Failures, Deliberate Software Attacks using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
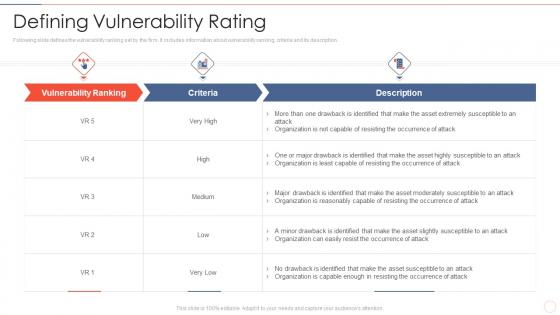 Effective information security defining vulnerability rating
Effective information security defining vulnerability ratingFollowing slide defines the vulnerability ranking set by the firm. It includes information about vulnerability ranking, criteria and its description. Present the topic in a bit more detail with this Effective Information Security Defining Vulnerability Rating. Use it as a tool for discussion and navigation on Vulnerability Ranking, Organization, Occurrence Attack. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
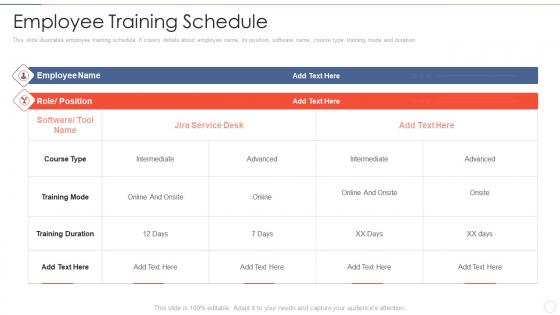 Effective information security employee training schedule
Effective information security employee training scheduleThis slide illustrates employee training schedule. It covers details about employee name, its position, software name, course type, training mode and duration. Deliver an outstanding presentation on the topic using this Effective Information Security Employee Training Schedule. Dispense information and present a thorough explanation of Training Mode, Course Type, Training Duration using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Effective information security impact assessment matrix ppt slides outline
Effective information security impact assessment matrix ppt slides outlinePresent the topic in a bit more detail with this Effective Information Security Impact Assessment Matrix Ppt Slides Outline. Use it as a tool for discussion and navigation on Impact Area, Impact High, Impact Medium, Impact Low. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
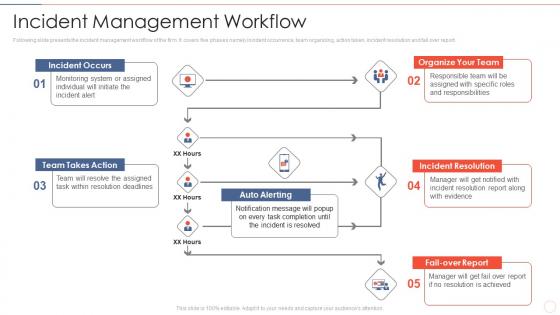 Effective information security incident management workflow
Effective information security incident management workflowFollowing slide presents the incident management workflow of the firm. It covers five phases namely incident occurrence, team organizing, action taken, incident resolution and fail over report. Present the topic in a bit more detail with this Effective Information Security Incident Management Workflow. Use it as a tool for discussion and navigation on Incident Occurs, Team Takes Action, Organize Team, Auto Alerting, Incident Resolution, Fail Over Report. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
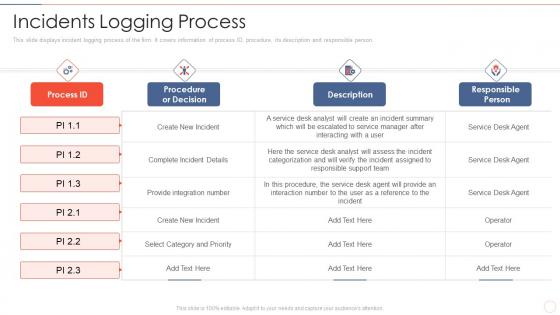 Effective information security incidents logging process
Effective information security incidents logging processThis slide displays incident logging process of the firm. It covers information of process ID, procedure, its description and responsible person. Present the topic in a bit more detail with this Effective Information Security Incidents Logging Process. Use it as a tool for discussion and navigation on Complete Incident Details, Select Category And Priority, Provide Integration Number. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
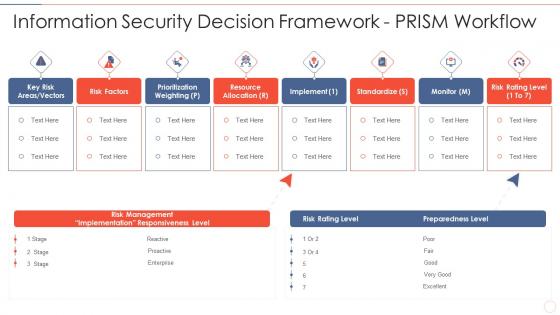 Effective information security information security decision framework prism workflow
Effective information security information security decision framework prism workflowDeliver an outstanding presentation on the topic using this Effective Information Security Information Security Decision Framework Prism Workflow. Dispense information and present a thorough explanation of Key Risk Areas Vectors, Risk Factors, Prioritization Weighting using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
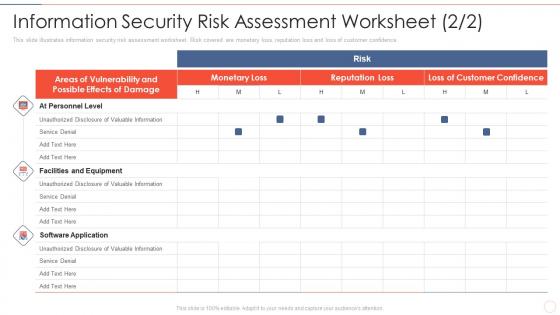 Effective information security information security risk assessment worksheet
Effective information security information security risk assessment worksheetThis slide illustrates information security risk assessment worksheet. Risk covered are monetary loss, reputation loss and loss of customer confidence. Present the topic in a bit more detail with this Effective Information Security Information Security Risk Assessment Worksheet. Use it as a tool for discussion and navigation on Facilities And Equipment, Software Application, At Personnel Level, Risk. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
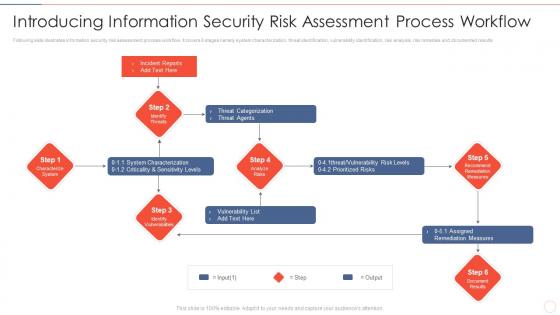 Effective information security introducing information security risk assessment process
Effective information security introducing information security risk assessment processFollowing slide illustrates information security risk assessment process workflow. It covers 6 stages namely system characterization, threat identification, vulnerability identification, risk analysis, risk remedies and documented results Increase audience engagement and knowledge by dispensing information using Effective Information Security Introducing Information Security Risk Assessment Process. This template helps you present information on six stages. You can also present information on Incident Reports, Threat Categorization, Vulnerability List, Assigned Remediation Measures using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
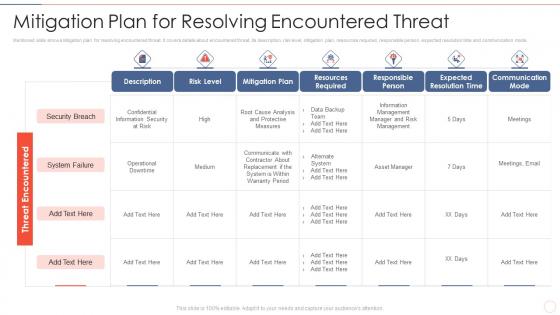 Effective information security mitigation plan for resolving encountered threat
Effective information security mitigation plan for resolving encountered threatMentioned slide shows mitigation plan for resolving encountered threat. It covers details about encountered threat, its description, risk level, mitigation plan, resources required, responsible person, expected resolution time and communication mode. Present the topic in a bit more detail with this Effective Information Security Mitigation Plan For Resolving Encountered Threat. Use it as a tool for discussion and navigation on Security Breach, System Failure, Risk Level, Mitigation Plan. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
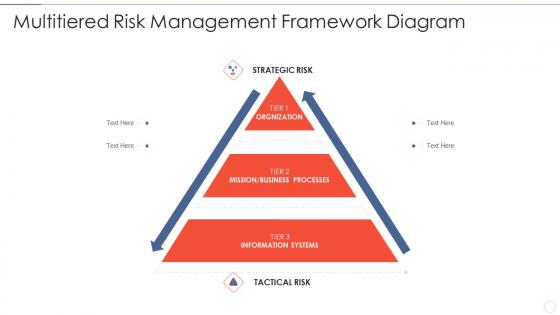 Effective information security multitiered risk management framework diagram
Effective information security multitiered risk management framework diagramIncrease audience engagement and knowledge by dispensing information using Effective Information Security Multitiered Risk Management Framework Diagram. This template helps you present information on three stages. You can also present information on Strategic Risk, Orgnization, Mission, Business Processes, Information Systems using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
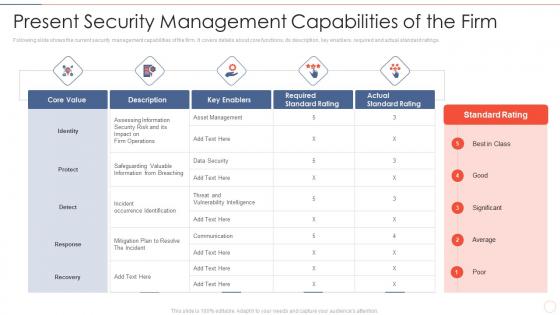 Effective information security present security management capabilities of the firm
Effective information security present security management capabilities of the firmFollowing slide shows the current security management capabilities of the firm. It covers details about core functions, its description, key enablers, required and actual standard ratings. Present the topic in a bit more detail with this Effective Information Security Present Security Management Capabilities Of The Firm. Use it as a tool for discussion and navigation on Core Value, Key Enablers, Required Standard Rating, Actual Standard Rating. This template is free to edit as deemed fit for your organization. Therefore download it now.



