Powerpoint Templates and Google slides for Security
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Internet Things Security Policy In Powerpoint And Google Slides Cpb
Internet Things Security Policy In Powerpoint And Google Slides CpbPresenting Internet Things Security Policy In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Internet Things Security Policy. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Corporate Fixed Income Securities In Powerpoint And Google Slides Cpb
Corporate Fixed Income Securities In Powerpoint And Google Slides CpbPresenting our Corporate Fixed Income Securities In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases five stages. It is useful to share insightful information on Corporate Fixed Income Securities. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Invest Securities Income Program In Powerpoint And Google Slides Cpb
Invest Securities Income Program In Powerpoint And Google Slides CpbPresenting Invest Securities Income Program In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Invest Securities Income Program. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Cyber Security Analyst Work In Powerpoint And Google Slides Cpb
Cyber Security Analyst Work In Powerpoint And Google Slides CpbPresenting our Cyber Security Analyst Work In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases six stages. It is useful to share insightful information on Cyber Security Analyst Work This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Cyber Security Illustration In Powerpoint And Google Slides Cpb
Cyber Security Illustration In Powerpoint And Google Slides CpbPresenting Cyber Security Illustration In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase five stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Cyber Security Illustration. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Data Breaches Cyber Security In Powerpoint And Google Slides Cpb
Data Breaches Cyber Security In Powerpoint And Google Slides CpbPresenting our Data Breaches Cyber Security In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Data Breaches Cyber Security This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 National Security Database Internship In Powerpoint And Google Slides Cpb
National Security Database Internship In Powerpoint And Google Slides CpbPresenting our National Security Database Internship In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases five stages. It is useful to share insightful information on National Security Database Internship This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Equities Stocks Securities In Powerpoint And Google Slides Cpb
Equities Stocks Securities In Powerpoint And Google Slides CpbPresenting Equities Stocks Securities In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Equities Stocks Securities. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Finance Cyber Security Jobs In Powerpoint And Google Slides Cpb
Finance Cyber Security Jobs In Powerpoint And Google Slides CpbPresenting Finance Cyber Security Jobs In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Finance Cyber Security Jobs. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
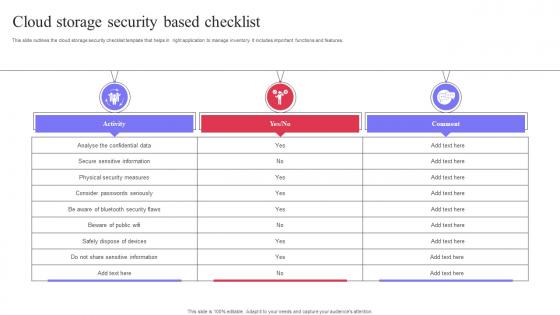 Cloud Storage Security Based Checklist
Cloud Storage Security Based ChecklistThis slide outlines the cloud storage security checklist template that helps in right application to manage inventory. It includes important functions and features. Introducing our Cloud Storage Security Based Checklist set of slides. The topics discussed in these slides are Secure Sensitive Information, Physical Security Measures. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Autonomous Mobile Robots Architecture AMRs In Autonomous Security Robots ASRs
Autonomous Mobile Robots Architecture AMRs In Autonomous Security Robots ASRsThis slide describes the application of autonomous security robots to help security personnel. AMRs are also beneficial for cutting the high personnel costs and a thorough inspection of the incidents if anything suspicious is found. Deliver an outstanding presentation on the topic using this Autonomous Mobile Robots Architecture AMRs In Autonomous Security Robots ASRs. Dispense information and present a thorough explanation of Autonomous Security Robots, Security Personnel, Security Is A Rapidly Expanding, Future Inspection And Analysis using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Security Digital Payments In Powerpoint And Google Slides Cpb
Security Digital Payments In Powerpoint And Google Slides CpbPresenting our Security Digital Payments In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Security Digital Payments This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Security Identity Card Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Security Identity Card Colored Icon In Powerpoint Pptx Png And Editable Eps FormatA coloured powerpoint icon depicting an Identity Card. Perfect for presentations, documents, and websites. Can be used to represent identity, security, and access. Easy to customize and resize. Ideal for business, education, and personal use.
-
 Security Identity Card Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Security Identity Card Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone PowerPoint Icon on Identity Card is a visual representation of a card, perfect for use in presentations related to identity, security, or access control. It is a simple, yet effective design that can easily be customized to fit your presentations theme.
-
 Equity Securities Derivatives In Powerpoint And Google Slides Cpb
Equity Securities Derivatives In Powerpoint And Google Slides CpbPresenting our Equity Securities Derivatives In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Equity Securities Derivatives. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Collateral Security Banking In Powerpoint And Google Slides Cpb
Collateral Security Banking In Powerpoint And Google Slides CpbPresenting our Collateral Security Banking In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Collateral Security Banking This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Features Income Securities In Powerpoint And Google Slides Cpb
Features Income Securities In Powerpoint And Google Slides CpbPresenting our Features Income Securities In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Features Income Securities This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Fixed Income Securities In Powerpoint And Google Slides Cpb
Fixed Income Securities In Powerpoint And Google Slides CpbPresenting Fixed Income Securities In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Fixed Income Securities. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Cash Security Deposit Rental In Powerpoint And Google Slides Cpb
Cash Security Deposit Rental In Powerpoint And Google Slides CpbPresenting our Cash Security Deposit Rental In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases five stages. It is useful to share insightful information on Cash Security Deposit Rental. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Mortgage Backed Security Market In Powerpoint And Google Slides Cpb
Mortgage Backed Security Market In Powerpoint And Google Slides CpbPresenting Mortgage Backed Security Market In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Mortgage Backed Security Market. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Social Security Benefit Calculator In Powerpoint And Google Slides Cpb
Social Security Benefit Calculator In Powerpoint And Google Slides CpbPresenting our Social Security Benefit Calculator In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases seven stages. It is useful to share insightful information on Social Security Benefit Calculator. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Leveraged Loans Securities In Powerpoint And Google Slides Cpb
Leveraged Loans Securities In Powerpoint And Google Slides CpbPresenting our Leveraged Loans Securities In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Leveraged Loans Securities This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Difference Securities Bonds In Powerpoint And Google Slides Cpb
Difference Securities Bonds In Powerpoint And Google Slides CpbPresenting our Difference Securities Bonds In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases six stages. It is useful to share insightful information on Difference Securities Bonds. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Data Breach Prevention Data Breach Prevention Services Provided By Security Tools
Data Breach Prevention Data Breach Prevention Services Provided By Security ToolsThis slide represents the multiple layers of protection provided by security solution providers against data breaches. These include database firewalls, data masking and encryption, Data Loss Prevention DLP, user behavior analytics, alert prioritization, etc. Present the topic in a bit more detail with this Data Breach Prevention Data Breach Prevention Services Provided By Security Tools. Use it as a tool for discussion and navigation on Data Breach Prevention, Services Provided By Security Tools, Obfuscates Sensitive Data. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data Breach Prevention Immediate And Long Term Impact Of Data Security Breach
Data Breach Prevention Immediate And Long Term Impact Of Data Security BreachThis slide outlines the immediate and longstanding expenses associated with data breaches. The direct business costs include government fines, public relations costs, attorney fees, cybersecurity investigations, operational disruption, etc. Present the topic in a bit more detail with this Data Breach Prevention Immediate And Long Term Impact Of Data Security Breach. Use it as a tool for discussion and navigation on Customer Breach Notifications, Damaged Brand Reputation, Public Relations Costs, Operational Disruption. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data Breach Prevention Security Software To Protect Business From Data Breach
Data Breach Prevention Security Software To Protect Business From Data BreachThe purpose of this slide is to highlight the available security tools to stay safe from data breaches. The popular security software are access control solutions, Security Information And Event Management SIEM tools, and antivirus software. Increase audience engagement and knowledge by dispensing information using Data Breach Prevention Security Software To Protect Business From Data Breach. This template helps you present information on three stages. You can also present information on Security Information And Event Management, Amends Permissions As Needed, Security Software To Protect Business using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Data Breach Response Plan Secure Operations Data Breach Prevention And Mitigation
Data Breach Response Plan Secure Operations Data Breach Prevention And MitigationThis slide represents actions to be taken, the responsible team, the deadline, and tasks for securing operations after a data breach. The action items include secure physical areas, assemble expert team, consult with legal counsel, secure website and contact search engines, etc. Present the topic in a bit more detail with this Data Breach Response Plan Secure Operations Data Breach Prevention And Mitigation. Use it as a tool for discussion and navigation on Assemble Expert Team, Consult With Legal Counsel, Secure Physical Areas. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Best Business Security System In Powerpoint And Google Slides Cpb
Best Business Security System In Powerpoint And Google Slides CpbPresenting our Best Business Security System In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Best Business Security System. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Best Business Security Camera System In Powerpoint And Google Slides Cpb
Best Business Security Camera System In Powerpoint And Google Slides CpbPresenting our Best Business Security Camera System In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Best Business Security Camera System This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
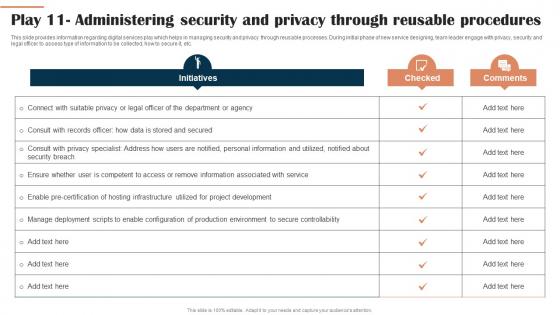 Play 11 Administering Security And Privacy Through Digital Hosting Environment Playbook
Play 11 Administering Security And Privacy Through Digital Hosting Environment PlaybookThis slide provides information regarding digital services play which helps in managing security and privacy through reusable processes. During initial phase of new service designing, team leader engage with privacy, security and legal officer to assess type of information to be collected, how to secure it, etc. Deliver an outstanding presentation on the topic using this Play 11 Administering Security And Privacy Through Digital Hosting Environment Playbook. Dispense information and present a thorough explanation of Deployment, Configuration, Environment using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
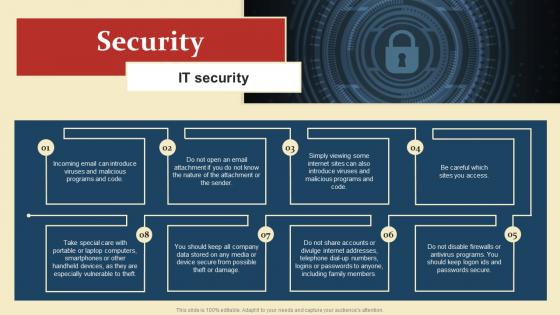 Security Introduction To Human Resource Policy
Security Introduction To Human Resource PolicyIntroducing Security Introduction To Human Resource Policy to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Security, using this template. Grab it now to reap its full benefits.
-
 Agenda Zero Trust Security Model Ppt Slides Background Images
Agenda Zero Trust Security Model Ppt Slides Background ImagesIncrease audience engagement and knowledge by dispensing information using Agenda Zero Trust Security Model Ppt Slides Background Images. This template helps you present information on five stages. You can also present information on Deployment, Approaches, Technologies using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
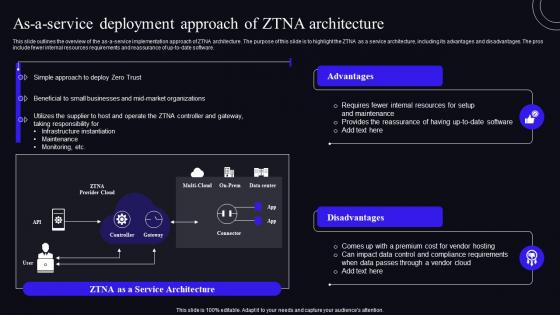 As A Service Deployment Approach Of ZTNA Architecture Zero Trust Security Model
As A Service Deployment Approach Of ZTNA Architecture Zero Trust Security ModelThis slide outlines the overview of the as-a-service implementation approach of ZTNA architecture. The purpose of this slide is to highlight the ZTNA as a service architecture, including its advantages and disadvantages. The pros include fewer internal resources requirements and reassurance of up-to-date software. Present the topic in a bit more detail with this As A Service Deployment Approach Of ZTNA Architecture Zero Trust Security Model. Use it as a tool for discussion and navigation on Architecture, Deployment, Approach. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
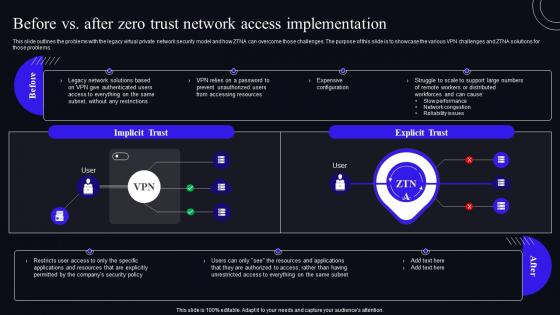 Before Vs After Zero Trust Network Access Implementation Zero Trust Security Model
Before Vs After Zero Trust Network Access Implementation Zero Trust Security ModelThis slide outlines the problems with the legacy virtual private network security model and how ZTNA can overcome those challenges. The purpose of this slide is to showcase the various VPN challenges and ZTNA solutions for those problems. Deliver an outstanding presentation on the topic using this Before Vs After Zero Trust Network Access Implementation Zero Trust Security Model. Dispense information and present a thorough explanation of Implementation, Distributed, Resources using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
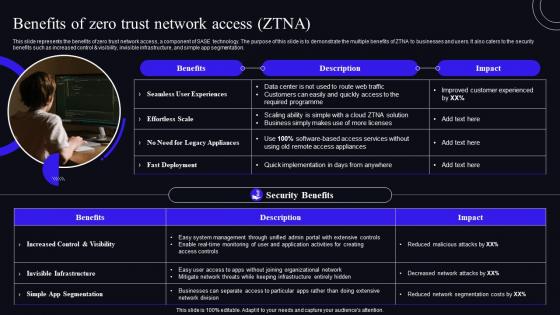 Benefits Of Zero Trust Network Access ZTNA Zero Trust Security Model
Benefits Of Zero Trust Network Access ZTNA Zero Trust Security ModelThis Slide Represents The Benefits Of Zero Trust Network Access, A Component Of SASE Technology. The Purpose Of This Slide Is To Demonstrate The Multiple Benefits Of ZTNA To Businesses And Users. It Also Caters To The Security Benefits Such As Increased Control And Visibility, Invisible Infrastructure, And Simple App Segmentation. Present The Topic In A Bit More Detail With This Benefits Of Zero Trust Network Access ZTNA Zero Trust Security Model. Use It As A Tool For Discussion And Navigation On Deployment, Experiences, Appliances. This Template Is Free To Edit As Deemed Fit For Your Organization. Therefore Download It Now.
-
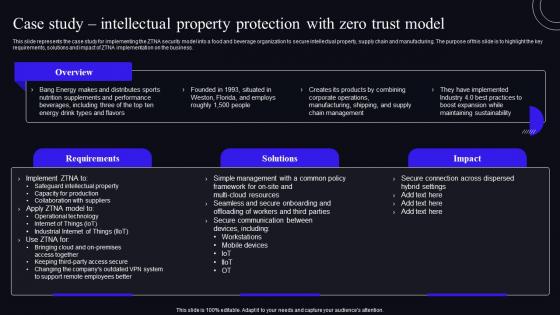 Case Study Intellectual Property Protection With Zero Trust Model Zero Trust Security Model
Case Study Intellectual Property Protection With Zero Trust Model Zero Trust Security ModelThis slide represents the case study for implementing the ZTNA security model into a food and beverage organization to secure intellectual property, supply chain and manufacturing. The purpose of this slide is to highlight the key requirements, solutions and impact of ZTNA implementation on the business. Deliver an outstanding presentation on the topic using this Case Study Intellectual Property Protection With Zero Trust Model Zero Trust Security Model. Dispense information and present a thorough explanation of Protection, Management, Communication using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Challenges Of VPN Based Remote Access Solutions Zero Trust Security Model
Challenges Of VPN Based Remote Access Solutions Zero Trust Security ModelThis slide outlines the limitations of virtual private network-based remote access services. The purpose of this slide is to showcase the various challenges of the VPN network system and how the zero trust network model can overcome those issues. Present the topic in a bit more detail with this Challenges Of VPN Based Remote Access Solutions Zero Trust Security Model. Use it as a tool for discussion and navigation on Extreme Implicit Trust, Performance Problems, Insufficient Granular. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
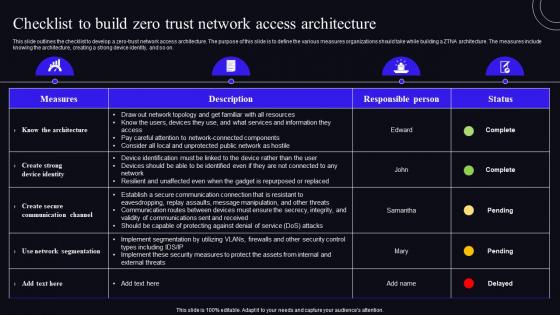 Checklist To Build Zero Trust Network Access Architecture Zero Trust Security Model
Checklist To Build Zero Trust Network Access Architecture Zero Trust Security ModelThis slide outlines the checklist to develop a zero-trust network access architecture. The purpose of this slide is to define the various measures organizations should take while building a ZTNA architecture. The measures include knowing the architecture, creating a strong device identity, and so on. Deliver an outstanding presentation on the topic using this Checklist To Build Zero Trust Network Access Architecture Zero Trust Security Model. Dispense information and present a thorough explanation of Architecture, Measures, Organizations using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
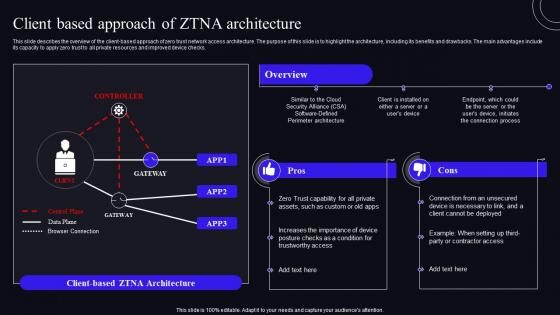 Client Based Approach Of ZTNA Architecture Zero Trust Security Model
Client Based Approach Of ZTNA Architecture Zero Trust Security ModelThis slide describes the overview of the client-based approach of zero trust network access architecture. The purpose of this slide is to highlight the architecture, including its benefits and drawbacks. The main advantages include its capacity to apply zero trust to all private resources and improved device checks. Present the topic in a bit more detail with this Client Based Approach Of ZTNA Architecture Zero Trust Security Model. Use it as a tool for discussion and navigation on Architecture, Process, Approach. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Comparative Assessment Of ZTNA Version 1 0 And 2 0 Zero Trust Security Model
Comparative Assessment Of ZTNA Version 1 0 And 2 0 Zero Trust Security ModelThis Slide Represents The Comparison Between Zero Trust Network Access Versions 1.0 And 2.0. The Purpose Of This Slide Is To Demonstrate The Overview Of Both Versions, Including Differences. It Also Includes The Architecture Of Both Versions Of Zero-Trust Network Access. Deliver An Outstanding Presentation On The Topic Using This Comparative Assessment Of ZTNA Version 1 0 And 2 0 Zero Trust Security Model. Dispense Information And Present A Thorough Explanation Of Comparative, Assessment, Applications Using The Slides Given. This Template Can Be Altered And Personalized To Fit Your Needs. It Is Also Available For Immediate Download. So Grab It Now.
-
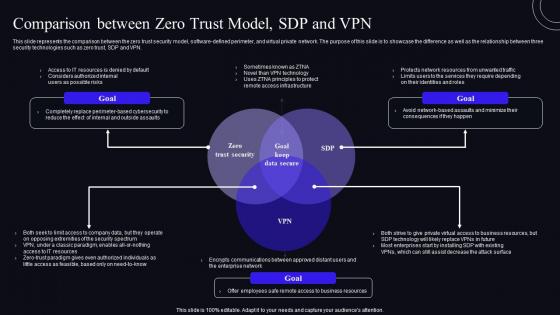 Comparison Between Zero Trust Model SDP And VPN Zero Trust Security Model
Comparison Between Zero Trust Model SDP And VPN Zero Trust Security ModelThis slide represents the comparison between the zero trust security model, software-defined perimeter, and virtual private network. The purpose of this slide is to showcase the difference as well as the relationship between three security technologies such as zero trust, SDP and VPN. Present the topic in a bit more detail with this Comparison Between Zero Trust Model SDP And VPN Zero Trust Security Model. Use it as a tool for discussion and navigation on Comparison, Business, Resources. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
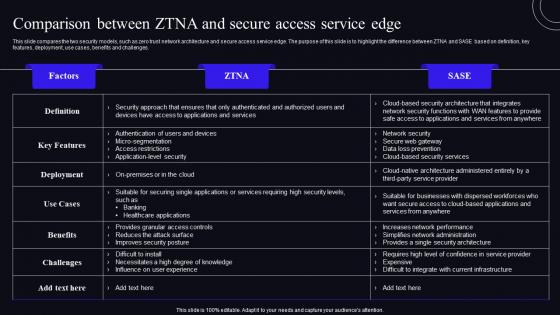 Comparison Between ZTNA And Secure Access Service Edge Zero Trust Security Model
Comparison Between ZTNA And Secure Access Service Edge Zero Trust Security ModelThis slide compares the two security models, such as zero trust network architecture and secure access service edge. The purpose of this slide is to highlight the difference between ZTNA and SASE based on definition, key features, deployment, use cases, benefits and challenges. Deliver an outstanding presentation on the topic using this Comparison Between ZTNA And Secure Access Service Edge Zero Trust Security Model. Dispense information and present a thorough explanation of Comparison, Architecture, Service using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Critical Principles Of Zero Trust Network Access Model Zero Trust Security Model
Critical Principles Of Zero Trust Network Access Model Zero Trust Security ModelThis slide illustrates the key principles of zero trust network access model, including their impact. The purpose of this slide is to highlight the primary principles of the ZTNA model, including least privilege access, micro-segmentation, MFA, device validation, and monitoring everything. Present the topic in a bit more detail with this Critical Principles Of Zero Trust Network Access Model Zero Trust Security Model. Use it as a tool for discussion and navigation on Description, Segmentation, Validation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
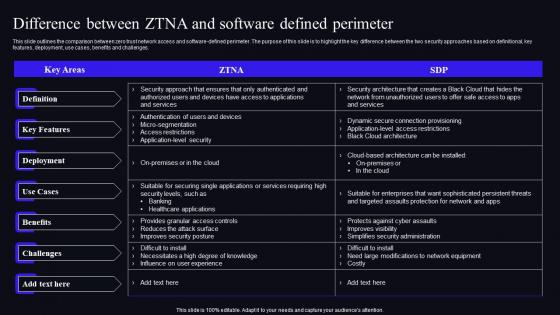 Difference Between ZTNA And Software Defined Perimeter Zero Trust Security Model
Difference Between ZTNA And Software Defined Perimeter Zero Trust Security ModelThis slide outlines the comparison between zero trust network access and software-defined perimeter. The purpose of this slide is to highlight the key difference between the two security approaches based on definitional, key features, deployment, use cases, benefits and challenges. Deliver an outstanding presentation on the topic using this Difference Between ZTNA And Software Defined Perimeter Zero Trust Security Model. Dispense information and present a thorough explanation of Definition, Deployment, Key Features using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Endpoint Initiated Vs Service Initiated Zero Trust Security Model
Endpoint Initiated Vs Service Initiated Zero Trust Security ModelThis Slide Represents The Comparison Between The Two Primary Approaches To Implementing Zero-Trust Network Access For Organizations. The Purpose Of This Slide Is To Showcase The Endpoint-Initiated And Service-Initiated Approach Of Zero-Trust Network Access. Present The Topic In A Bit More Detail With This Endpoint Initiated Vs Service Initiated Zero Trust Security Model. Use It As A Tool For Discussion And Navigation On Enterprise, Environment, Connection. This Template Is Free To Edit As Deemed Fit For Your Organization. Therefore Download It Now.
-
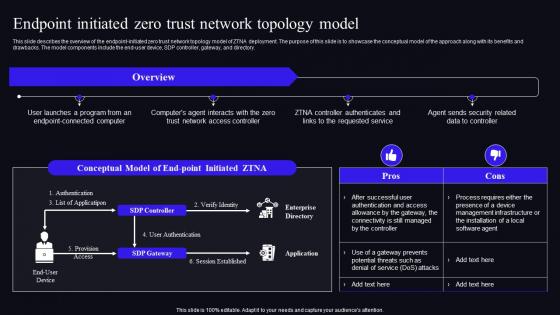 Endpoint Initiated Zero Trust Network Topology Model Zero Trust Security Model
Endpoint Initiated Zero Trust Network Topology Model Zero Trust Security ModelThis slide describes the overview of the endpoint-initiated zero trust network topology model of ZTNA deployment. The purpose of this slide is to showcase the conceptual model of the approach along with its benefits and drawbacks. The model components include the end-user device, SDP controller, gateway, and directory. Deliver an outstanding presentation on the topic using this Endpoint Initiated Zero Trust Network Topology Model Zero Trust Security Model. Dispense information and present a thorough explanation of Management, Infrastructure, Installation using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
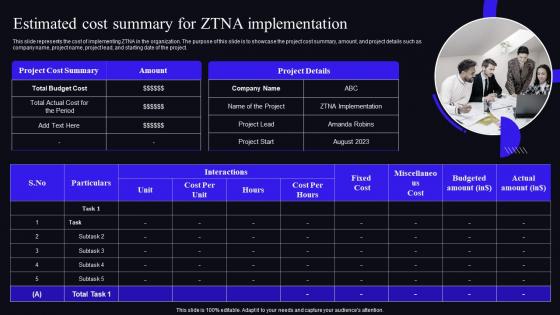 Estimated Cost Summary For ZTNA Implementation Zero Trust Security Model
Estimated Cost Summary For ZTNA Implementation Zero Trust Security ModelThis slide represents the cost of implementing ZTNA in the organization. The purpose of this slide is to showcase the project cost summary, amount, and project details such as company name, project name, project lead, and starting date of the project. Present the topic in a bit more detail with this Estimated Cost Summary For ZTNA Implementation Zero Trust Security Model. Use it as a tool for discussion and navigation on Implementation, Organization, Represents. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
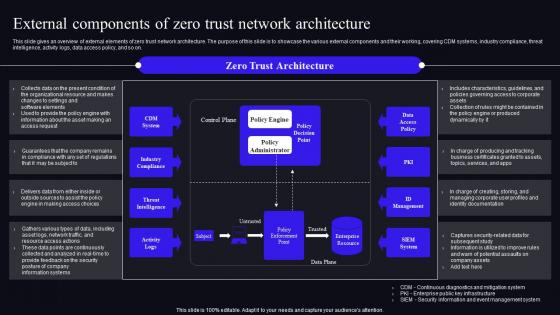 External Components Of Zero Trust Network Architecture Zero Trust Security Model
External Components Of Zero Trust Network Architecture Zero Trust Security ModelThis slide gives an overview of external elements of zero trust network architecture. The purpose of this slide is to showcase the various external components and their working, covering CDM systems, industry compliance, threat intelligence, activity logs, data access policy, and so on. Deliver an outstanding presentation on the topic using this External Components Of Zero Trust Network Architecture Zero Trust Security Model. Dispense information and present a thorough explanation of Architecture, Documentation, Potential using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
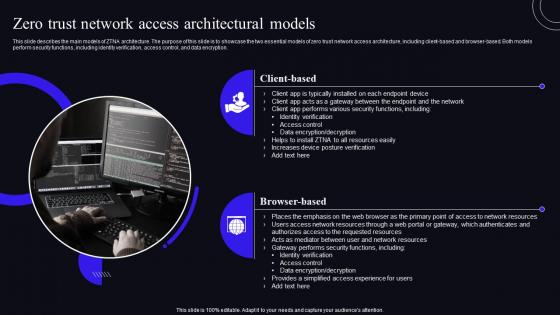 F1585 Zero Trust Network Access Architectural Models Zero Trust Security Model
F1585 Zero Trust Network Access Architectural Models Zero Trust Security ModelThis slide describes the main models of ZTNA architecture. The purpose of this slide is to showcase the two essential models of zero trust network access architecture, including client-based and browser-based. Both models perform security functions, including identity verification, access control, and data encryption. Introducing F1585 Zero Trust Network Access Architectural Models Zero Trust Security Model to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Architectural, Resources, Verification, using this template. Grab it now to reap its full benefits.
-
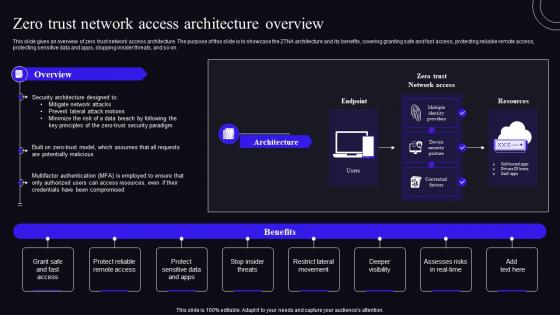 F1586 Zero Trust Network Access Architecture Overview Zero Trust Security Model
F1586 Zero Trust Network Access Architecture Overview Zero Trust Security ModelThis slide gives an overview of zero trust network access architecture. The purpose of this slide is to showcase the ZTNA architecture and its benefits, covering granting safe and fast access, protecting reliable remote access, protecting sensitive data and apps, stopping insider threats, and so on. Present the topic in a bit more detail with this F1586 Zero Trust Network Access Architecture Overview Zero Trust Security Model. Use it as a tool for discussion and navigation on Resources, Architecture, Overview. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
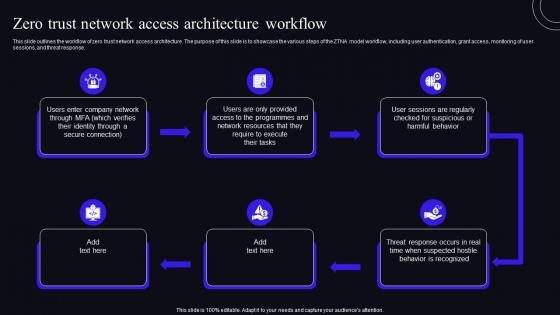 F1587 Zero Trust Network Access Architecture Workflow Zero Trust Security Model
F1587 Zero Trust Network Access Architecture Workflow Zero Trust Security ModelThis slide outlines the workflow of zero trust network access architecture. The purpose of this slide is to showcase the various steps of the ZTNA model workflow, including user authentication, grant access, monitoring of user sessions, and threat response. Increase audience engagement and knowledge by dispensing information using F1587 Zero Trust Network Access Architecture Workflow Zero Trust Security Model. This template helps you present information on six stages. You can also present information on Architecture, Workflow, Resources using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
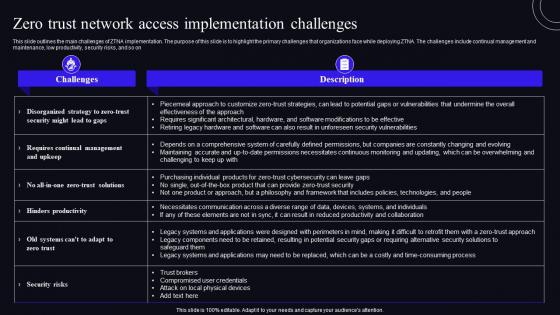 F1588 Zero Trust Network Access Implementation Challenges Zero Trust Security Model
F1588 Zero Trust Network Access Implementation Challenges Zero Trust Security ModelThis slide outlines the main challenges of ZTNA implementation. The purpose of this slide is to highlight the primary challenges that organizations face while deploying ZTNA. The challenges include continual management and maintenance, low productivity, security risks, and so on Present the topic in a bit more detail with this F1588 Zero Trust Network Access Implementation Challenges Zero Trust Security Model. Use it as a tool for discussion and navigation on Implementation, Organizations, Productivity. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
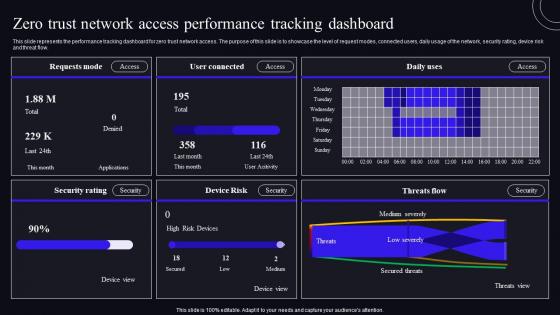 F1589 Zero Trust Network Access Performance Tracking Dashboard Zero Trust Security Model
F1589 Zero Trust Network Access Performance Tracking Dashboard Zero Trust Security ModelThis slide represents the performance tracking dashboard for zero trust network access. The purpose of this slide is to showcase the level of request modes, connected users, daily usage of the network, security rating, device risk and threat flow. Deliver an outstanding presentation on the topic using this F1589 Zero Trust Network Access Performance Tracking Dashboard Zero Trust Security Model. Dispense information and present a thorough explanation of Performance, Dashboard, Represents using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
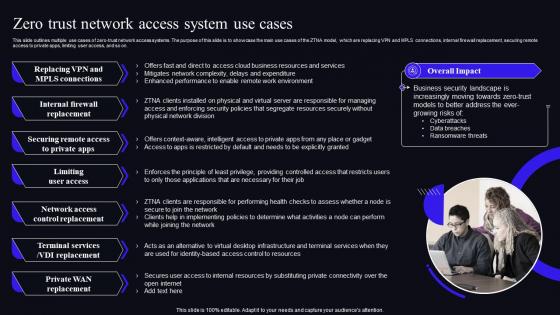 F1590 Zero Trust Network Access System Use Cases Zero Trust Security Model
F1590 Zero Trust Network Access System Use Cases Zero Trust Security ModelThis slide outlines multiple use cases of zero-trust network access systems. The purpose of this slide is to showcase the main use cases of the ZTNA model, which are replacing VPN and MPLS connections, internal firewall replacement, securing remote access to private apps, limiting user access, and so on. Present the topic in a bit more detail with this F1590 Zero Trust Network Access System Use Cases Zero Trust Security Model. Use it as a tool for discussion and navigation on Internal Firewall Replacement, Limiting User Access, Network Access Control Replacement. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
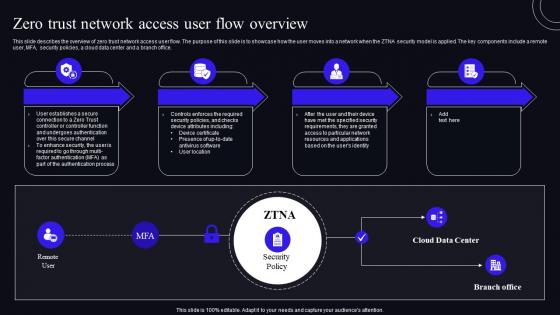 F1591 Zero Trust Network Access User Flow Overview Zero Trust Security Model
F1591 Zero Trust Network Access User Flow Overview Zero Trust Security ModelThis slide describes the overview of zero trust network access user flow. The purpose of this slide is to showcase how the user moves into a network when the ZTNA security model is applied. The key components include a remote user, MFA, security policies, a cloud data center and a branch office. Deliver an outstanding presentation on the topic using this F1591 Zero Trust Network Access User Flow Overview Zero Trust Security Model. Dispense information and present a thorough explanation of Authentication, Process, Resources using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
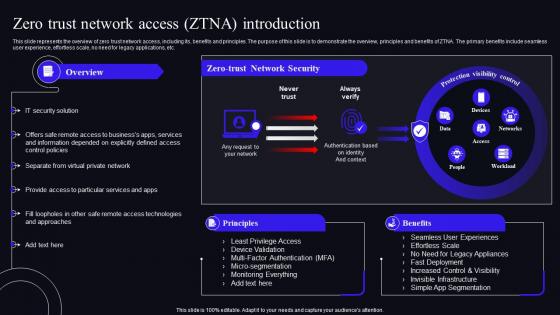 F1592 Zero Trust Network Access ZTNA Introduction Zero Trust Security Model
F1592 Zero Trust Network Access ZTNA Introduction Zero Trust Security ModelThis slide represents the overview of zero trust network access, including its, benefits and principles. The purpose of this slide is to demonstrate the overview, principles and benefits of ZTNA. The primary benefits include seamless user experience, effortless scale, no need for legacy applications, etc. Present the topic in a bit more detail with this F1592 Zero Trust Network Access ZTNA Introduction Zero Trust Security Model. Use it as a tool for discussion and navigation on Introduction, Appliances, Infrastructure. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
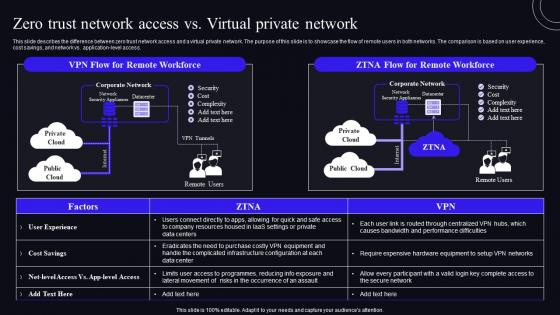 F1593 Zero Trust Network Access Vs Virtual Private Network Zero Trust Security Model
F1593 Zero Trust Network Access Vs Virtual Private Network Zero Trust Security ModelThis slide describes the difference between zero trust network access and a virtual private network. The purpose of this slide is to showcase the flow of remote users in both networks. The comparison is based on user experience, cost savings, and network vs. application-level access. Deliver an outstanding presentation on the topic using this F1593 Zero Trust Network Access Vs Virtual Private Network Zero Trust Security Model. Dispense information and present a thorough explanation of Infrastructure, Configuration, Equipment using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
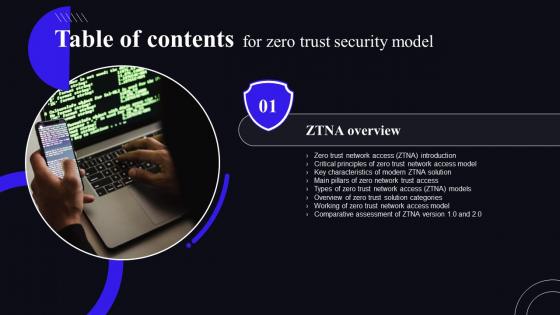 F1594 Zero Trust Security Model For Table Of Contents
F1594 Zero Trust Security Model For Table Of ContentsIntroducing F1594 Zero Trust Security Model For Table Of Contents to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Introduction, Solution, Comparative, using this template. Grab it now to reap its full benefits.
-
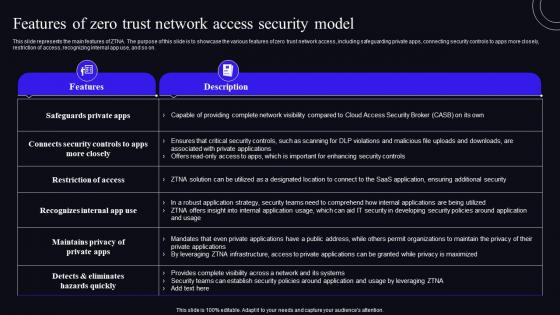 Features Of Zero Trust Network Access Security Model Zero Trust Security Model
Features Of Zero Trust Network Access Security Model Zero Trust Security ModelThis slide represents the main features of ZTNA. The purpose of this slide is to showcase the various features of zero trust network access, including safeguarding private apps, connecting security controls to apps more closely, restriction of access, recognizing internal app use, and so on. Present the topic in a bit more detail with this Features Of Zero Trust Network Access Security Model Zero Trust Security Model. Use it as a tool for discussion and navigation on Organizations, Applications, Infrastructure. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
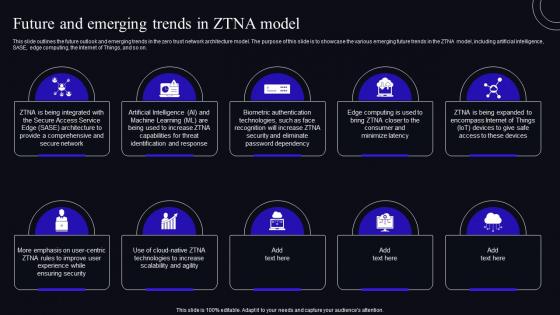 Future And Emerging Trends In ZTNA Model Zero Trust Security Model
Future And Emerging Trends In ZTNA Model Zero Trust Security ModelThis slide outlines the future outlook and emerging trends in the zero trust network architecture model. The purpose of this slide is to showcase the various emerging future trends in the ZTNA model, including artificial intelligence, SASE, edge computing, the Internet of Things, and so on. Increase audience engagement and knowledge by dispensing information using Future And Emerging Trends In ZTNA Model Zero Trust Security Model. This template helps you present information on ten stages. You can also present information on Authentication, Capabilities, Identification using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.



