Powerpoint Templates and Google slides for Cybersecurity assetment
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Formulating Cybersecurity Plan To Safeguard Information Assets Powerpoint Presentation Slides
Formulating Cybersecurity Plan To Safeguard Information Assets Powerpoint Presentation SlidesEnthrall your audience with this Formulating Cybersecurity Plan To Safeguard Information Assets Powerpoint Presentation Slides. Increase your presentation threshold by deploying this well-crafted template. It acts as a great communication tool due to its well-researched content. It also contains stylized icons, graphics, visuals etc, which make it an immediate attention-grabber. Comprising seventy one slides, this complete deck is all you need to get noticed. All the slides and their content can be altered to suit your unique business setting. Not only that, other components and graphics can also be modified to add personal touches to this prefabricated set.
-
 Identifying Assets As A Step For Cybersecurity Risk Identification Training Ppt
Identifying Assets As A Step For Cybersecurity Risk Identification Training PptPresenting Identifying Assets as a Step for Cybersecurity Risk Identification. This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizable alter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
 Cybersecurity Crisis Leadership To Safeguard Digital Assets
Cybersecurity Crisis Leadership To Safeguard Digital AssetsThe purpose of this slide is to highlight how cybersecurity crisis leadership safeguards digital assets with proactive strategies, incident response protocols, and fostering organizational resilience against cyber threats. Deliver an outstanding presentation on the topic using this Cybersecurity Crisis Leadership To Safeguard Digital Assets. Dispense information and present a thorough explanation of Tone For Preparedness, Culture Of Vigilance, Adequate Resources using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cybersecurity Risk Assessment Program Comprehensive Overview Of Organization IT Assets
Cybersecurity Risk Assessment Program Comprehensive Overview Of Organization IT AssetsThe purpose this slide is to showcase the comprehensive overview of organization IT assets. The dashboards provide information regarding the IT devices count, distribution in terms of operating system, and location. It also contains details of endpoint by hardware, department and cyber attack visibility. Deliver an outstanding presentation on the topic using this Cybersecurity Risk Assessment Program Comprehensive Overview Of Organization IT Assets. Dispense information and present a thorough explanation of Comprehensive Overview, Organization IT Assets, Dashboards, Operating System using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Information Security Program Cybersecurity Checklist Effectively Managing Asset Security
Information Security Program Cybersecurity Checklist Effectively Managing Asset SecurityFollowing slide displays system management checklist that company will use for effectively managing asset security. It also includes system management activities and frequency of performing them. Present the topic in a bit more detail with this Information Security Program Cybersecurity Checklist Effectively Managing Asset Security. Use it as a tool for discussion and navigation on Checklist For Effectively Managing Asset Security. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Information Security Program Cybersecurity Management Threat Vulnerability Asset Matrix
Information Security Program Cybersecurity Management Threat Vulnerability Asset MatrixMentioned slide displays the threat vulnerability asset matrix covering sections namely ranked threat agent and details about critical resources ranked from most critical to least. Deliver an outstanding presentation on the topic using this Information Security Program Cybersecurity Management Threat Vulnerability Asset Matrix. Dispense information and present a thorough explanation of Threat Vulnerability Asset Matrix using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
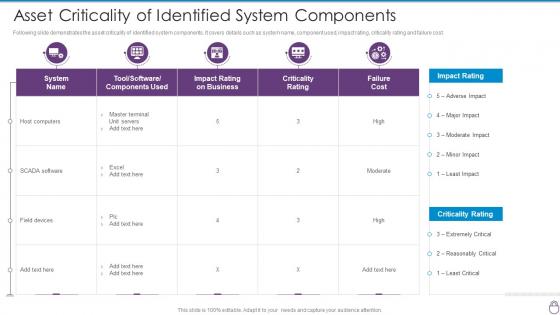 Cybersecurity Risk Management Framework Asset Criticality Of Identified System
Cybersecurity Risk Management Framework Asset Criticality Of Identified SystemFollowing slide demonstrates the asset criticality of identified system components. It covers details such as system name, component used, impact rating, criticality rating and failure cost. Present the topic in a bit more detail with this Cybersecurity Risk Management Framework Asset Criticality Of Identified System. Use it as a tool for discussion and navigation on Criticality Rating, Failure Cost, Moderate, High. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
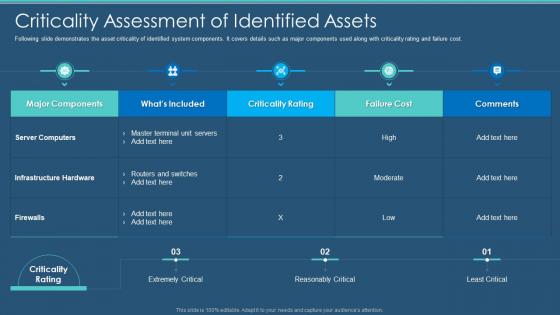 Cybersecurity Criticality Assessment Of Identified Assets Information Security Program
Cybersecurity Criticality Assessment Of Identified Assets Information Security ProgramFollowing slide demonstrates the asset criticality of identified system components. It covers details such as major components used along with criticality rating and failure cost. Present the topic in a bit more detail with this Cybersecurity Criticality Assessment Of Identified Assets Information Security Program. Use it as a tool for discussion and navigation on Criticality Assessment Of Identified Assets. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
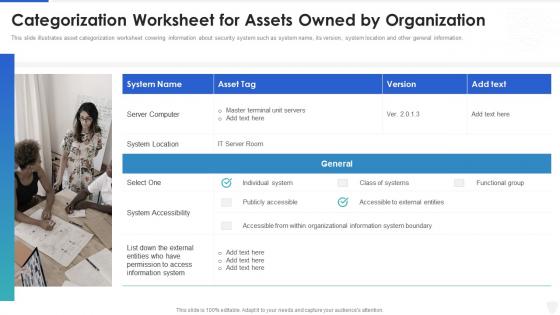 Cybersecurity and digital business risk management categorization worksheet for assets
Cybersecurity and digital business risk management categorization worksheet for assetsThis slide illustrates asset categorization worksheet covering information about security system such as system name, its version, system location and other general information. Increase audience engagement and knowledge by dispensing information using Cybersecurity And Digital Business Risk Management Categorization Worksheet For Assets. This template helps you present information on one stages. You can also present information on Organization, Information, Location using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cybersecurity and digital business risk management checklist for effectively managing asset security
Cybersecurity and digital business risk management checklist for effectively managing asset securityFollowing slide displays system management checklist that company will use for effectively managing asset security. It also includes system management activities and frequency of performing them. Present the topic in a bit more detail with this Cybersecurity And Digital Business Risk Management Checklist For Effectively Managing Asset Security. Use it as a tool for discussion and navigation on System Monitoring, Data Backup, Security Patches . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cybersecurity and digital business risk management criticality assessment of identified assets
Cybersecurity and digital business risk management criticality assessment of identified assetsFollowing slide demonstrates the asset criticality of identified system components. It covers details such as major components used along with criticality rating and failure cost. Present the topic in a bit more detail with this Cybersecurity And Digital Business Risk Management Criticality Assessment Of Identified Assets. Use it as a tool for discussion and navigation on Assessment, Infrastructure, Components. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
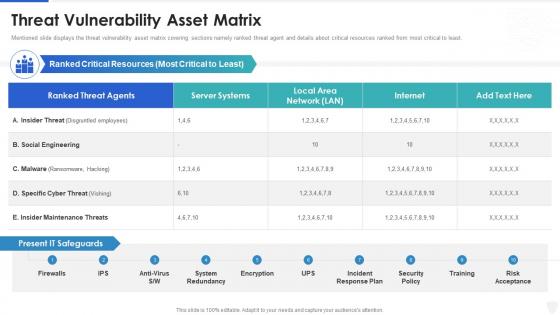 Cybersecurity and digital business risk management threat vulnerability asset matrix
Cybersecurity and digital business risk management threat vulnerability asset matrixMentioned slide displays the threat vulnerability asset matrix covering sections namely ranked threat agent and details about critical resources ranked from most critical to least. Deliver an outstanding presentation on the topic using this Cybersecurity And Digital Business Risk Management Threat Vulnerability Asset Matrix. Dispense information and present a thorough explanation of Threat Vulnerability Asset Matrix using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Analysing The Impact On Assets Due To Cybersecurity Risk Analysis And Management Plan
Analysing The Impact On Assets Due To Cybersecurity Risk Analysis And Management PlanThis slide showcases impact of information breach on different assets which can help organization in formulating risk monitoring policy. Its key components are criterion, criterion weight and information assets Deliver an outstanding presentation on the topic using this Analysing The Impact On Assets Due To Cybersecurity Risk Analysis And Management Plan. Dispense information and present a thorough explanation of Information, Analysing, Organization using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Asset Identification For Information Security Cybersecurity Risk Analysis And Management Plan
Asset Identification For Information Security Cybersecurity Risk Analysis And Management PlanThis slide showcases identification of asset which can help organization to formulate risk monitoring plan. It can help form to monitor the asset in real time for any data breach or cyber attack Introducing Asset Identification For Information Security Cybersecurity Risk Analysis And Management Plan to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Identification, Information, Management, using this template. Grab it now to reap its full benefits.
-
 Assigning Criticality Rating To Information Assets Cybersecurity Risk Analysis And Management Plan
Assigning Criticality Rating To Information Assets Cybersecurity Risk Analysis And Management PlanThis slide showcases criticality rating that can be allocation to assets for identifying critical assets. Its key elements are asst, failure cost, failure impact and criticality rating Present the topic in a bit more detail with this Assigning Criticality Rating To Information Assets Cybersecurity Risk Analysis And Management Plan. Use it as a tool for discussion and navigation on Information, Extremely Critical, Reasonably Critical. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Agenda Formulating Cybersecurity Plan To Safeguard Information Assets
Agenda Formulating Cybersecurity Plan To Safeguard Information AssetsIntroducing Agenda Formulating Cybersecurity Plan To Safeguard Information Assets to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Current Information, Organization, Formulating Cybersecurity, using this template. Grab it now to reap its full benefits.
-
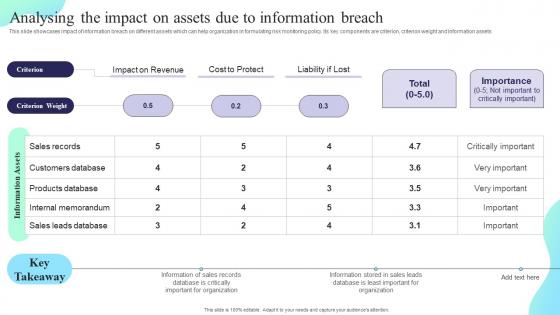 Analysing The Impact On Assets Due To Information Breach Formulating Cybersecurity Plan
Analysing The Impact On Assets Due To Information Breach Formulating Cybersecurity PlanThis slide showcases impact of information breach on different assets which can help organization in formulating risk monitoring policy. Its key components are criterion, criterion weight and information assets. Deliver an outstanding presentation on the topic using this Analysing The Impact On Assets Due To Information Breach Formulating Cybersecurity Plan. Dispense information and present a thorough explanation of Sales Records, Customers Database, Products Database using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
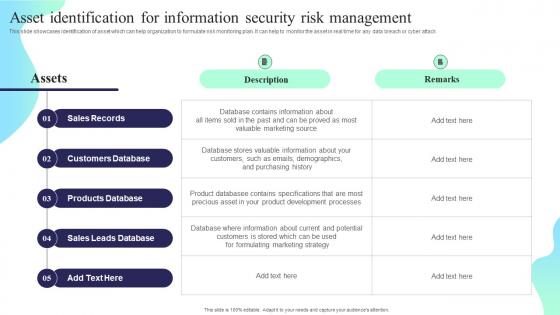 Asset Identification For Information Security Risk Management Formulating Cybersecurity Plan
Asset Identification For Information Security Risk Management Formulating Cybersecurity PlanThis slide showcases identification of asset which can help organization to formulate risk monitoring plan. It can help to monitor the asset in real time for any data breach or cyber attack. Deliver an outstanding presentation on the topic using this Asset Identification For Information Security Risk Management Formulating Cybersecurity Plan. Dispense information and present a thorough explanation of Sales Records, Customers Database, Products Database using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Assigning Criticality Rating To Information Assets Formulating Cybersecurity Plan
Assigning Criticality Rating To Information Assets Formulating Cybersecurity PlanThis slide showcases criticality rating that can be allocated to assets for identifying critical assets. Its key elements are asset, failure cost, failure impact and criticality rating. Present the topic in a bit more detail with this Assigning Criticality Rating To Information Assets Formulating Cybersecurity Plan. Use it as a tool for discussion and navigation on Sales Records, Customers Database, Products Database. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 G14 Table Of Contents Formulating Cybersecurity Plan To Safeguard Information Assets
G14 Table Of Contents Formulating Cybersecurity Plan To Safeguard Information AssetsIntroducing G14 Table Of Contents Formulating Cybersecurity Plan To Safeguard Information Assets to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispence information on Process, Risk Management Plan, Formulate Information, using this template. Grab it now to reap its full benefits.
-
 Icons Slide For Formulating Cybersecurity Plan To Safeguard Information Assets
Icons Slide For Formulating Cybersecurity Plan To Safeguard Information AssetsIntroducing our well researched set of slides titled Icons Slide For Formulating Cybersecurity Plan To Safeguard Information Assets. It displays a hundred percent editable icons. You can use these icons in your presentation to captivate your audiences attention. Download now and use it multiple times.
-
 Table Of Contents Formulating Cybersecurity Plan To Safeguard Information Assets
Table Of Contents Formulating Cybersecurity Plan To Safeguard Information AssetsIntroducing Table Of Contents Formulating Cybersecurity Plan To Safeguard Information Assets to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Current Scenario Assessment, Security Capabilities, Management Plan, using this template. Grab it now to reap its full benefits.
-
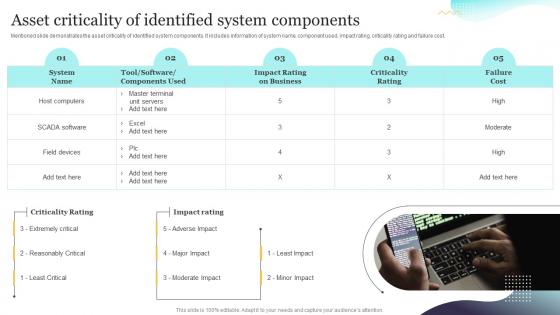 Asset Criticality Of Identified System Components Upgrading Cybersecurity With Incident Response Playbook
Asset Criticality Of Identified System Components Upgrading Cybersecurity With Incident Response PlaybookMentioned slide demonstrates the asset criticality of identified system components. It includes information of system name, component used, impact rating, criticality rating and failure cost. Present the topic in a bit more detail with this Asset Criticality Of Identified System Components Upgrading Cybersecurity With Incident Response Playbook. Use it as a tool for discussion and navigation on Criticality, Information, Demonstrates. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
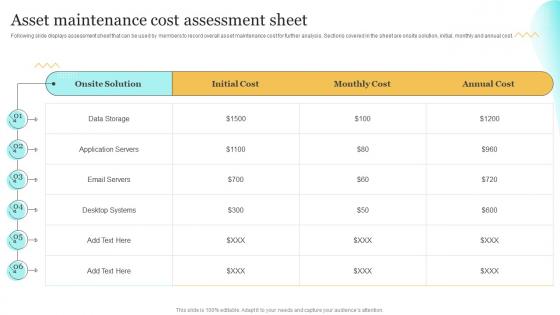 Asset Maintenance Cost Assessment Sheet Upgrading Cybersecurity With Incident Response Playbook
Asset Maintenance Cost Assessment Sheet Upgrading Cybersecurity With Incident Response PlaybookFollowing slide displays assessment sheet that can be used by members to record overall asset maintenance cost for further analysis. Sections covered in the sheet are onsite solution, initial, monthly and annual cost. Deliver an outstanding presentation on the topic using this Asset Maintenance Cost Assessment Sheet Upgrading Cybersecurity With Incident Response Playbook. Dispense information and present a thorough explanation of Assessment, Maintenance, Solution using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Checklist To Ensure Asset Protection From Internal Upgrading Cybersecurity With Incident Response Playbook
Checklist To Ensure Asset Protection From Internal Upgrading Cybersecurity With Incident Response PlaybookFollowing slide displays checklist having security control measures that can be used by members to ensure the safety of companys assets from any insider threat. Present the topic in a bit more detail with this Checklist To Ensure Asset Protection From Internal Upgrading Cybersecurity With Incident Response Playbook. Use it as a tool for discussion and navigation on Protection, Measures, Ensure. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
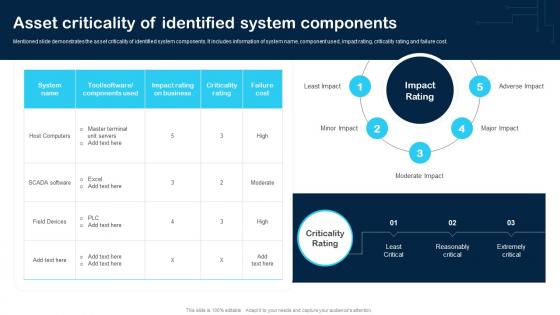 Asset Criticality Of Identified System Components Cybersecurity Incident And Vulnerability
Asset Criticality Of Identified System Components Cybersecurity Incident And VulnerabilityMentioned slide demonstrates the asset criticality of identified system components. It includes information of system name, component used, impact rating, criticality rating and failure cost. Deliver an outstanding presentation on the topic using this Asset Criticality Of Identified System Components Cybersecurity Incident And Vulnerability. Dispense information and present a thorough explanation of Host Computers, SCADA Software, Field Devices using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
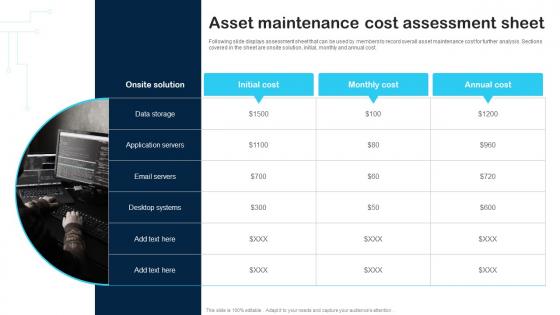 Asset Maintenance Cost Assessment Sheet Cybersecurity Incident And Vulnerability
Asset Maintenance Cost Assessment Sheet Cybersecurity Incident And VulnerabilityFollowing slide displays assessment sheet that can be used by members to record overall asset maintenance cost for further analysis. Sections covered in the sheet are onsite solution, initial, monthly and annual cost. Introducing Asset Maintenance Cost Assessment Sheet Cybersecurity Incident And Vulnerability to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Data Storage, Application Servers, Email Servers, using this template. Grab it now to reap its full benefits.
-
 Checklist To Ensure Asset Protection From Internal Threats Cybersecurity Incident And Vulnerability
Checklist To Ensure Asset Protection From Internal Threats Cybersecurity Incident And VulnerabilityFollowing slide displays checklist having security control measures that can be used by members to ensure the safety of companys assets from any insider threat. Introducing Checklist To Ensure Asset Protection From Internal Threats Cybersecurity Incident And Vulnerability to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Employees, Email, Mobile Devices, using this template. Grab it now to reap its full benefits.
-
 Performing Cyber Training Exercises For Securing The Assets Cybersecurity Incident And Vulnerability
Performing Cyber Training Exercises For Securing The Assets Cybersecurity Incident And VulnerabilityPurpose of this slide is to address and perform various cyber training exercises in order to secure companys assets. Exercises covered are defense in depth, capture the flag etc. Deliver an outstanding presentation on the topic using this Performing Cyber Training Exercises For Securing The Assets Cybersecurity Incident And Vulnerability. Dispense information and present a thorough explanation of Capture The Flag Event, Training, System Administrator using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
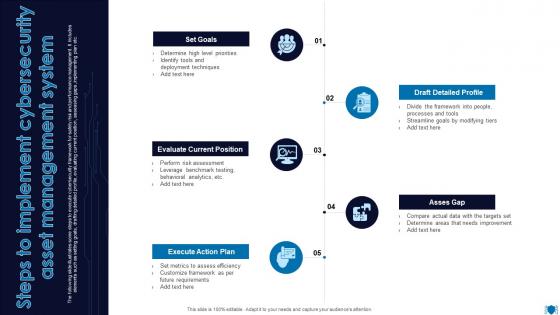 Steps To Implement Cybersecurity Asset Management System
Steps To Implement Cybersecurity Asset Management SystemThe following slide illustrates some steps to execute cybersecurity framework for safety risk and performance management. It includes elements such as setting goals, drafting detailed profile, evaluating current position, assessing gaps, implementing plan etc. Presenting our set of slides with Steps To Implement Cybersecurity Asset Management System. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Evaluate Current Position, Execute Action Plan, Asses Gap.

