Powerpoint Templates and Google slides for Identification Cyber
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Identifying Assets As A Step For Cybersecurity Risk Identification Training Ppt
Identifying Assets As A Step For Cybersecurity Risk Identification Training PptPresenting Identifying Assets as a Step for Cybersecurity Risk Identification. This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizable alter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
 Identifying Threats As A Step For Cybersecurity Risk Identification Training Ppt
Identifying Threats As A Step For Cybersecurity Risk Identification Training PptPresenting Identifying Threats as a Step for Cybersecurity Risk Identification. This PPT presentation is meticulously researched and each slide consists of relevant content. Designed by SlideTeams PowerPoint experts, this PPT is fully customizable alter the colors, text, icons, and font size to meet your requirements. Compatible with Google Slides and backed by excellent customer support. Download to present with poise and assurance.
-
 Identifying Vulnerabilities As A Step For Cybersecurity Risk Identification Training Ppt
Identifying Vulnerabilities As A Step For Cybersecurity Risk Identification Training PptPresenting Identifying Vulnerabilities as a Step for Cybersecurity Risk Identification. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. It is well crafted and designed by our PowerPoint specialists. Suitable for use by managers, employees, and organizations. You can edit the color, text, icon, and font size to suit your requirements. The PPT also supports Google Slides. Even Premium Customer Support is also available. Download now and present with confidence.
-
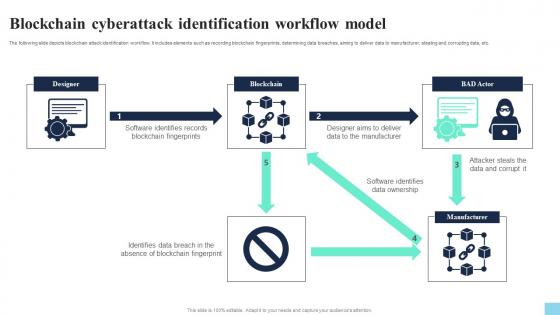 Blockchain Cyberattack Identification Workflow Model Hands On Blockchain Security Risk BCT SS V
Blockchain Cyberattack Identification Workflow Model Hands On Blockchain Security Risk BCT SS VThe following slide depicts blockchain attack identification workflow. It includes elements such as recording blockchain fingerprints, determining data breaches, aiming to deliver data to manufacturer, stealing and corrupting data, etc. Present the topic in a bit more detail with this Blockchain Cyberattack Identification Workflow Model Hands On Blockchain Security Risk BCT SS V. Use it as a tool for discussion and navigation on Blockchain Fingerprints, Data Ownership, Data And Corrupt. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Security Icon For Threat Identification
Cyber Security Icon For Threat IdentificationIntroducing our premium set of slides with Cyber Security Icon For Threat Identification. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cyber Security Icon, Threat Identification. So download instantly and tailor it with your information.
-
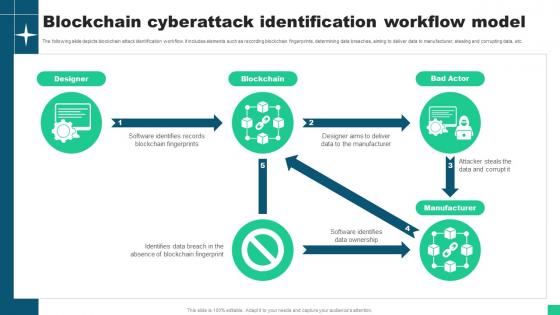 Blockchain Cyberattack Identification Workflow Model Guide For Blockchain BCT SS V
Blockchain Cyberattack Identification Workflow Model Guide For Blockchain BCT SS VThe following slide depicts blockchain attack identification workflow. It includes elements such as recording blockchain fingerprints, determining data breaches, aiming to deliver data to manufacturer, stealing and corrupting data, etc. Present the topic in a bit more detail with this Blockchain Cyberattack Identification Workflow Model Guide For Blockchain BCT SS V Use it as a tool for discussion and navigation on Designer, Blockchain, Manufacturer This template is free to edit as deemed fit for your organization. Therefore download it now.
-
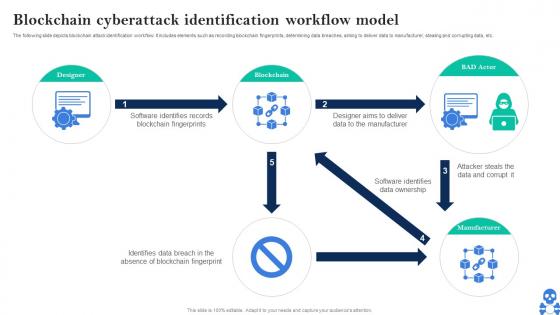 Cyber Threats In Blockchain Blockchain Cyberattack Identification Workflow Model BCT SS V
Cyber Threats In Blockchain Blockchain Cyberattack Identification Workflow Model BCT SS VThe following slide depicts blockchain attack identification workflow. It includes elements such as recording blockchain fingerprints, determining data breaches, aiming to deliver data to manufacturer, stealing and corrupting data, etc. Present the topic in a bit more detail with this Cyber Threats In Blockchain Blockchain Cyberattack Identification Workflow Model BCT SS V Use it as a tool for discussion and navigation on Designer, Blockchain, BAD Actor This template is free to edit as deemed fit for your organization. Therefore download it now.
-
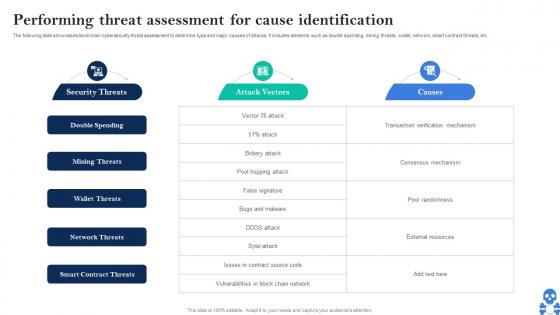 Cyber Threats In Blockchain Performing Threat Assessment For Cause Identification BCT SS V
Cyber Threats In Blockchain Performing Threat Assessment For Cause Identification BCT SS VThe following slide showcases blockchain cybersecurity threat assessment to determine type and major causes of attacks. It includes elements such as double spending, mining threats, wallet, network, smart contract threats, etc. Deliver an outstanding presentation on the topic using this Cyber Threats In Blockchain Major Cybersecurity Challenges In Blockchain Technology BCT SS V Dispense information and present a thorough explanation of Double Spending, Mining Threats, Wallet Threats using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
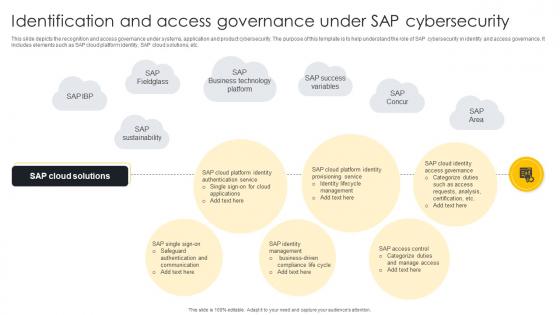 Identification And Access Governance Under SAP Cybersecurity
Identification And Access Governance Under SAP CybersecurityThis slide depicts the recognition and access governance under systems, application and product cybersecurity. The purpose of this template is to help understand the role of SAP cybersecurity in identity and access governance. It includes elements such as SAP cloud platform identity, SAP cloud solutions, etc. Introducing our Identification And Access Governance Under SAP Cybersecurity set of slides. The topics discussed in these slides are SAP Fieldglass, Identity Lifecycle Management, SAP Success Variables. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
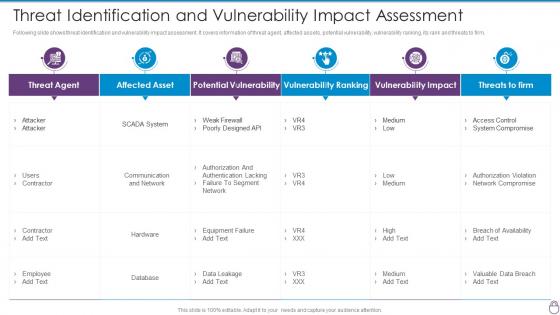 Cybersecurity Risk Management Framework Threat Identification And Vulnerability Impact
Cybersecurity Risk Management Framework Threat Identification And Vulnerability ImpactFollowing slide shows threat identification and vulnerability impact assessment. It covers information of threat agent, affected assets, potential vulnerability, vulnerability ranking, its rank and threats to firm. Deliver an outstanding presentation on the topic using this Cybersecurity Risk Management Framework Threat Identification And Vulnerability Impact. Dispense information and present a thorough explanation of Threat Agent, Affected Asset, Potential Vulnerability, Vulnerability Ranking, Vulnerability Impact using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
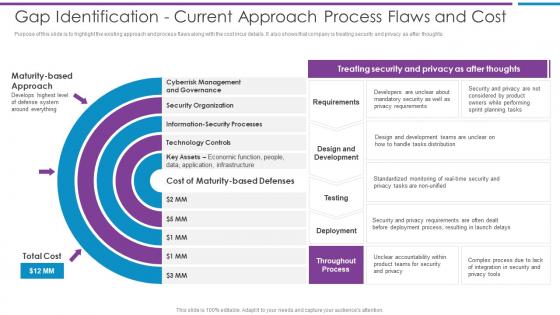
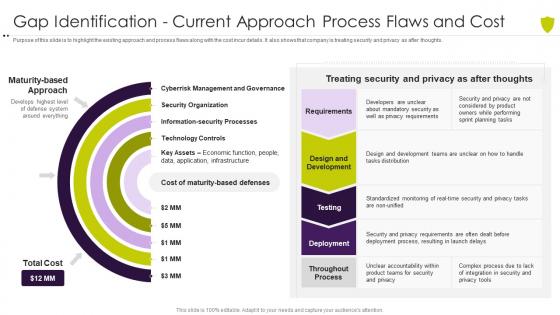 Gap identification current approach process flaws managing cyber risk in a digital age
Gap identification current approach process flaws managing cyber risk in a digital agePurpose of this slide is to highlight the existing approach and process flaws along with the cost incur details. It also shows that company is treating security and privacy as after thoughts. Present the topic in a bit more detail with this Gap Identification Current Approach Process Flaws Managing Cyber Risk In A Digital Age. Use it as a tool for discussion and navigation on Gap Identification Current Approach Process Flaws And Cost. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Gap Identification Current Approach Process Flaws And Cost Risk Based Methodology To Cyber
Gap Identification Current Approach Process Flaws And Cost Risk Based Methodology To CyberPurpose of this slide is to highlight the existing approach and process flaws along with the cost incur details. It also shows that company is treating security and privacy as after thoughts.Introducing Gap Identification Current Approach Process Flaws And Cost Risk Based Methodology To Cyber to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Design And Development, Requirements, Deployment using this template. Grab it now to reap its full benefits.
-
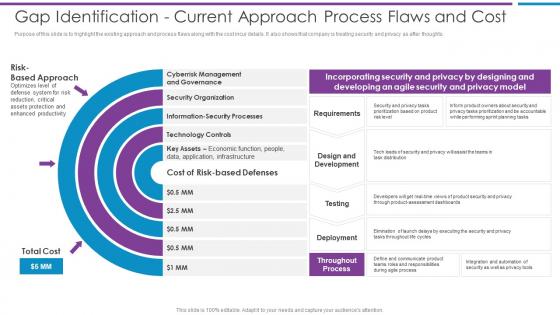 Gap Identification Current Approach Process Flaws And Risk Based Methodology To Cyber
Gap Identification Current Approach Process Flaws And Risk Based Methodology To CyberPurpose of this slide is to highlight the existing approach and process flaws along with the cost incur details. It also shows that company is treating security and privacy as after thoughts.Increase audience engagement and knowledge by dispensing information using Gap Identification Current Approach Process Flaws And Risk Based Methodology To Cyber This template helps you present information on three stages. You can also present information on Security Organization, Information Security Processes, Technology Controls using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cybersecurity and digital business risk management gap identification current approach process
Cybersecurity and digital business risk management gap identification current approach processPurpose of this slide is to highlight the existing approach and process flaws along with the cost incur details. It also shows that company is treating security and privacy as after thoughts. Increase audience engagement and knowledge by dispensing information using Cybersecurity And Digital Business Risk Management Gap Identification Current Approach Process. This template helps you present information on four stages. You can also present information on Approach, Process, Development using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Asset Identification For Information Security Cybersecurity Risk Analysis And Management Plan
Asset Identification For Information Security Cybersecurity Risk Analysis And Management PlanThis slide showcases identification of asset which can help organization to formulate risk monitoring plan. It can help form to monitor the asset in real time for any data breach or cyber attack Introducing Asset Identification For Information Security Cybersecurity Risk Analysis And Management Plan to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Identification, Information, Management, using this template. Grab it now to reap its full benefits.
-
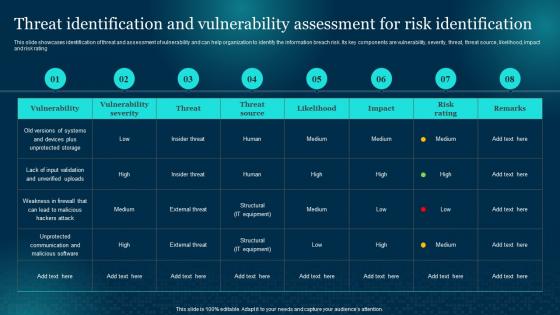 Threat Identification And Vulnerability Assessment For Cybersecurity Risk Analysis And Management Plan
Threat Identification And Vulnerability Assessment For Cybersecurity Risk Analysis And Management PlanThis slide showcases identification of threat and assessment of vulnerability and can help organization to identify the information breach risk. Its key components are vulnerability, severity, threat, threat source, likelihood, impact and risk rating Deliver an outstanding presentation on the topic using this Threat Identification And Vulnerability Assessment For Cybersecurity Risk Analysis And Management Plan. Dispense information and present a thorough explanation of Identification, Assessment, Vulnerability using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
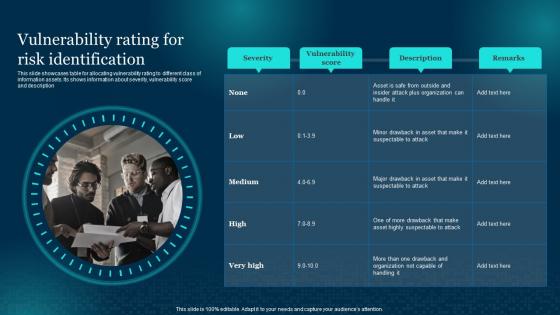 Vulnerability Rating For Risk Identification Cybersecurity Risk Analysis And Management Plan
Vulnerability Rating For Risk Identification Cybersecurity Risk Analysis And Management PlanThis slide showcases table for allocating vulnerability rating to different class of information assets. Its shows information about severity, vulnerability score and description Deliver an outstanding presentation on the topic using this Vulnerability Rating For Risk Identification Cybersecurity Risk Analysis And Management Plan. Dispense information and present a thorough explanation of Vulnerability, Identification, Information using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
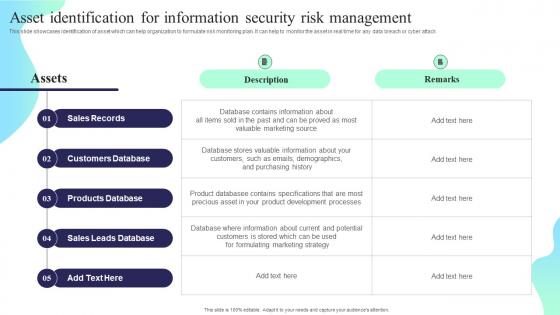 Asset Identification For Information Security Risk Management Formulating Cybersecurity Plan
Asset Identification For Information Security Risk Management Formulating Cybersecurity PlanThis slide showcases identification of asset which can help organization to formulate risk monitoring plan. It can help to monitor the asset in real time for any data breach or cyber attack. Deliver an outstanding presentation on the topic using this Asset Identification For Information Security Risk Management Formulating Cybersecurity Plan. Dispense information and present a thorough explanation of Sales Records, Customers Database, Products Database using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
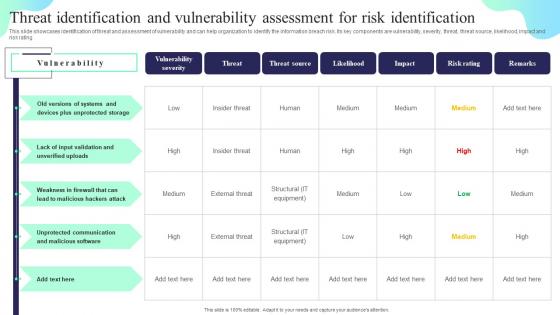 Threat Identification And Vulnerability Assessment Formulating Cybersecurity Plan
Threat Identification And Vulnerability Assessment Formulating Cybersecurity PlanThis slide showcases identification of threat and assessment of vulnerability and can help organization to identify the information breach risk. Its key components are vulnerability, severity, threat, threat source, likelihood, impact and risk rating. Present the topic in a bit more detail with this Threat Identification And Vulnerability Assessment Formulating Cybersecurity Plan. Use it as a tool for discussion and navigation on Vulnerability Severity, Threat Source, Likelihood. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Vulnerability Rating For Risk Identification Formulating Cybersecurity Plan
Vulnerability Rating For Risk Identification Formulating Cybersecurity PlanThis slide showcases table for allocating vulnerability rating to different class of information assets. It shows information about severity, vulnerability score and description. Introducing Vulnerability Rating For Risk Identification Formulating Cybersecurity Plan to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Vulnerability Score, Risk Identification, using this template. Grab it now to reap its full benefits.
-
 Cyber Security Strategy Icon Depicting Biometric Identification
Cyber Security Strategy Icon Depicting Biometric IdentificationIntroducing our Cyber Security Strategy Icon Depicting Biometric Identification set of slides. The topics discussed in these slides are Cyber Security, Strategy Icon, Depicting Biometric, Identification. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
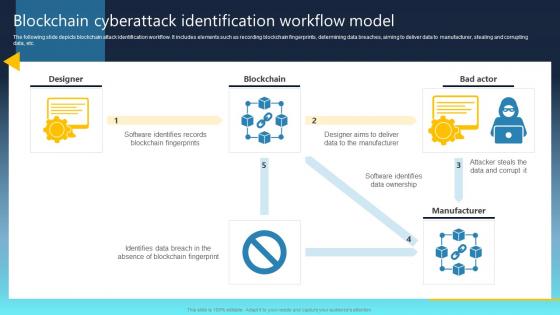 Ultimate Guide For Blockchain Blockchain Cyberattack Identification Workflow Model BCT SS
Ultimate Guide For Blockchain Blockchain Cyberattack Identification Workflow Model BCT SSThe following slide depicts blockchain attack identification workflow. It includes elements such as recording blockchain fingerprints, determining data breaches, aiming to deliver data to manufacturer, stealing and corrupting data, etc. Present the topic in a bit more detail with this Ultimate Guide For Blockchain Blockchain Cyberattack Identification Workflow Model BCT SS Use it as a tool for discussion and navigation on Blockchain Fingerprint, Data Ownership This template is free to edit as deemed fit for your organization. Therefore download it now.
-
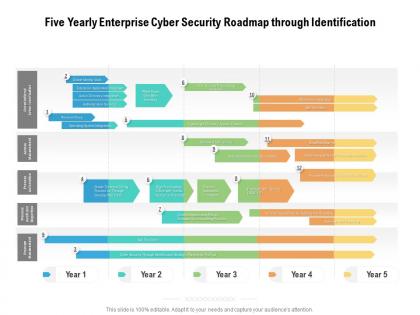 Five yearly enterprise cyber security roadmap through identification
Five yearly enterprise cyber security roadmap through identificationPresenting Five Yearly Enterprise Cyber Security Roadmap Through Identification PowerPoint slide. This PPT presentation is Google Slides compatible hence it is easily accessible. This PPT theme is available in both 4,3 and 16,9 aspect ratios. This PowerPoint template is customizable so you can modify the font size, font type, color, and shapes as per your requirements. You can download and save this PowerPoint layout in different formats like PDF, PNG, and JPG.
-
 Half yearly enterprise cyber security roadmap through identification
Half yearly enterprise cyber security roadmap through identificationPresenting Half Yearly Enterprise Cyber Security Roadmap Through Identification PowerPoint slide. This PPT presentation is Google Slides compatible hence it is easily accessible. This PPT theme is available in both 4,3 and 16,9 aspect ratios. This PowerPoint template is customizable so you can modify the font size, font type, color, and shapes as per your requirements. You can download and save this PowerPoint layout in different formats like PDF, PNG, and JPG.
-
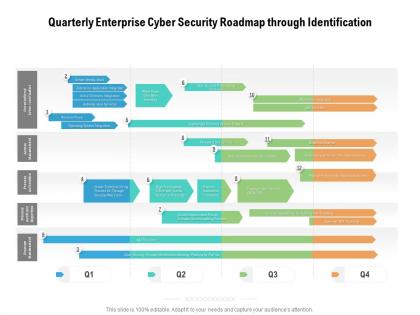 Quarterly enterprise cyber security roadmap through identification
Quarterly enterprise cyber security roadmap through identificationPresenting Quarterly Enterprise Cyber Security Roadmap Through Identification PowerPoint slide. This PPT presentation is Google Slides compatible hence it is easily accessible. This PPT theme is available in both 4,3 and 16,9 aspect ratios. This PowerPoint template is customizable so you can modify the font size, font type, color, and shapes as per your requirements. You can download and save this PowerPoint layout in different formats like PDF, PNG, and JPG.
-
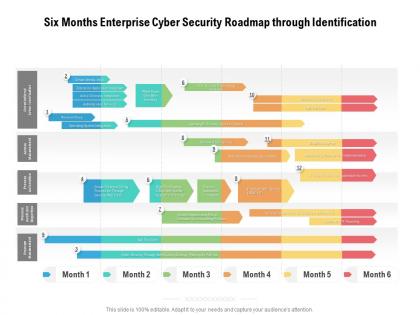 Six months enterprise cyber security roadmap through identification
Six months enterprise cyber security roadmap through identificationPresenting Six Months Enterprise Cyber Security Roadmap Through Identification PowerPoint slide. This PPT presentation is Google Slides compatible hence it is easily accessible. This PPT theme is available in both 4,3 and 16,9 aspect ratios. This PowerPoint template is customizable so you can modify the font size, font type, color, and shapes as per your requirements. You can download and save this PowerPoint layout in different formats like PDF, PNG, and JPG.
-
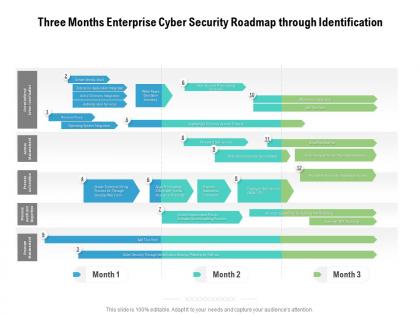 Three months enterprise cyber security roadmap through identification
Three months enterprise cyber security roadmap through identificationPresenting Three Months Enterprise Cyber Security Roadmap Through Identification PowerPoint slide. This PPT presentation is Google Slides compatible hence it is easily accessible. This PPT theme is available in both 4,3 and 16,9 aspect ratios. This PowerPoint template is customizable so you can modify the font size, font type, color, and shapes as per your requirements. You can download and save this PowerPoint layout in different formats like PDF, PNG, and JPG.
-
 Cyber monitoring of system using biometric security identification icon
Cyber monitoring of system using biometric security identification iconPresenting this set of slides with name Cyber Monitoring Of System Using Biometric Security Identification Icon. This is a three stage process. The stages in this process are Cyber Monitoring Of System Using Biometric Security Identification Icon. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
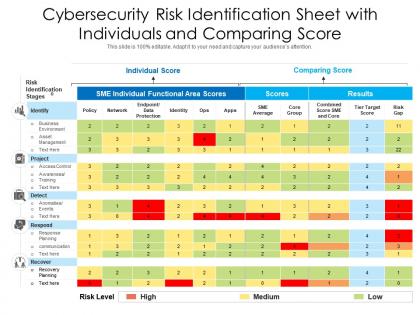 Cybersecurity risk identification sheet with individuals and comparing score
Cybersecurity risk identification sheet with individuals and comparing scoreIntroducing our Cybersecurity Risk Identification Sheet With Individuals And Comparing Score set of slides. The topics discussed in these slides are Individual Score, Comparing Score. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
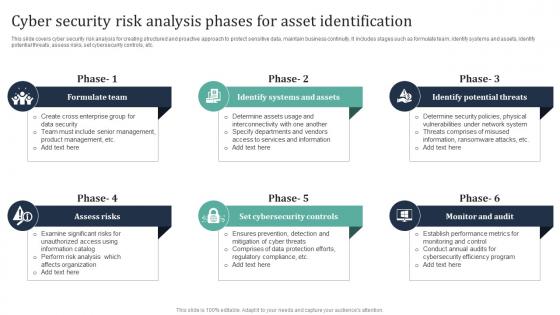 Cyber Security Risk Analysis Phases For Asset Identification
Cyber Security Risk Analysis Phases For Asset IdentificationThis slide covers cyber security risk analysis for creating structured and proactive approach to protect sensitive data, maintain business continuity. It includes stages such as formulate team, identify systems and assets, identify potential threats, assess risks, set cybersecurity controls, etc. Introducing our premium set of slides with Cyber Security Risk Analysis Phases For Asset Identification. Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Team, Assess, Cybersecurity. So download instantly and tailor it with your information.

