Powerpoint Templates and Google slides for Identify System Security Weaknesses
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
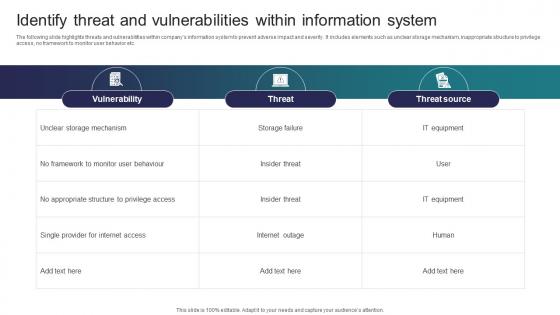 Identify Threat And Vulnerabilities Within Information System Implementing Strategies To Mitigate Cyber Security
Identify Threat And Vulnerabilities Within Information System Implementing Strategies To Mitigate Cyber SecurityThe following slide highlights threats and vulnerabilities within companys information system to prevent adverse impact and severity. It includes elements such as unclear storage mechanism, inappropriate structure to privilege access, no framework to monitor user behavior etc. Deliver an outstanding presentation on the topic using this Identify Threat And Vulnerabilities Within Information System Implementing Strategies To Mitigate Cyber Security Dispense information and present a thorough explanation of Vulnerability, Threat, Threat Source using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
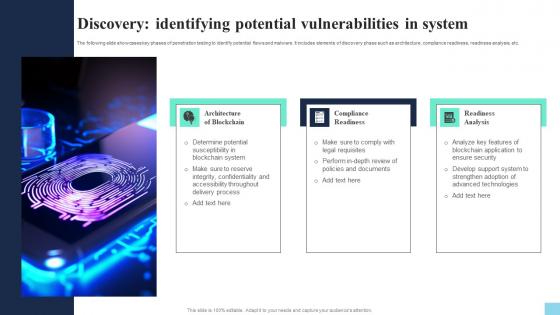 Discovery Identifying Potential Vulnerabilities In System Hands On Blockchain Security Risk BCT SS V
Discovery Identifying Potential Vulnerabilities In System Hands On Blockchain Security Risk BCT SS VThe following slide showcases key phases of penetration testing to identify potential flaws and malware. It includes elements of discovery phase such as architecture, compliance readiness, readiness analysis, etc. Introducing Discovery Identifying Potential Vulnerabilities In System Hands On Blockchain Security Risk BCT SS V to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Architecture Of Blockchain, Compliance Readiness, Readiness Analysis, using this template. Grab it now to reap its full benefits.
-
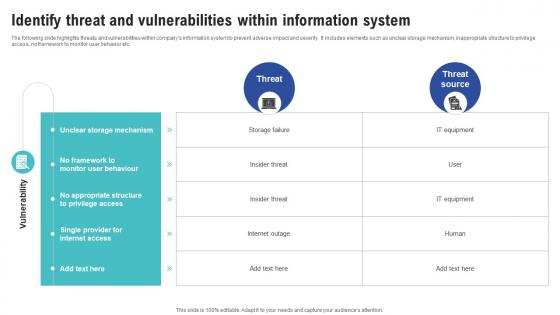 Identify Threat And Vulnerabilities Within Information System Creating Cyber Security Awareness
Identify Threat And Vulnerabilities Within Information System Creating Cyber Security AwarenessThe following slide highlights threats and vulnerabilities within companys information system to prevent adverse impact and severity. It includes elements such as unclear storage mechanism, inappropriate structure to privilege access, no framework to monitor user behavior etc. Deliver an outstanding presentation on the topic using this Identify Threat And Vulnerabilities Within Information System Creating Cyber Security Awareness Dispense information and present a thorough explanation of Unclear Storage Mechanism, Monitor User Behaviour, No Appropriate Structure using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
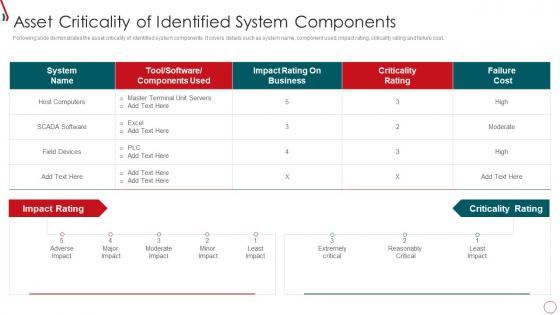 Risk Management Framework For Information Security Asset Criticality Of Identified System
Risk Management Framework For Information Security Asset Criticality Of Identified SystemFollowing slide demonstrates the asset criticality of identified system components. It covers details such as system name, component used, impact rating, criticality rating and failure cost. Present the topic in a bit more detail with this Risk Management Framework For Information Security Asset Criticality Of Identified System. Use it as a tool for discussion and navigation on Host Computers, Impact Rating, Criticality Rating, Failure Cost. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
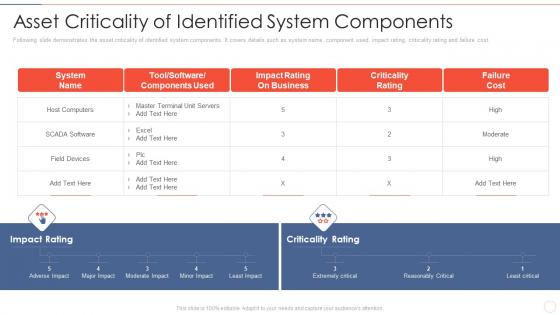 Effective information security asset criticality of identified system components
Effective information security asset criticality of identified system componentsFollowing slide demonstrates the asset criticality of identified system components. It covers details such as system name, component used, impact rating, criticality rating and failure cost. Deliver an outstanding presentation on the topic using this Effective Information Security Asset Criticality Of Identified System Components. Dispense information and present a thorough explanation of Host Computers, Impact Rating, Business, Criticality Rating using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
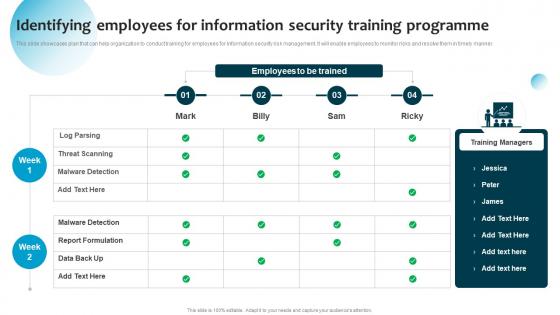 Identifying Employees For Information Security Training Information System Security And Risk Administration
Identifying Employees For Information Security Training Information System Security And Risk AdministrationThis slide showcases plan that can help organization to conduct training for employees for information security risk management. It will enable employees to monitor risks and resolve them in timely manner. Present the topic in a bit more detail with this Identifying Employees For Information Security Training Information System Security And Risk Administration. Use it as a tool for discussion and navigation on Threat Scanning, Malware Detection, Report Formulation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
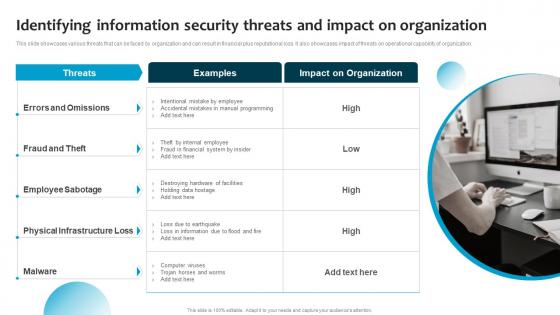 Information System Security And Risk Administration Plan Identifying Information Security Threats And Impact
Information System Security And Risk Administration Plan Identifying Information Security Threats And ImpactThis slide showcases various threats that can be faced by organization and can result in financial plus reputational loss. It also showcases impact of threats on operational capability of organization. Increase audience engagement and knowledge by dispensing information using Information System Security And Risk Administration Plan Identifying Information Security Threats And Impact. This template helps you present information on one stages. You can also present information on Employee Sabotage, Physical Infrastructure Loss, Threats using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Security Incident Response Playbook Asset Criticality Of Identified System Components
Security Incident Response Playbook Asset Criticality Of Identified System ComponentsMentioned slide demonstrates the asset criticality of identified system components. It includes information of system name, component used, impact rating, criticality rating and failure cost. Present the topic in a bit more detail with this Security Incident Response Playbook Asset Criticality Of Identified System Components. Use it as a tool for discussion and navigation on Identified, Components, Information. This template is free to edit as deemed fit for your organization. Therefore download it now.