Powerpoint Templates and Google slides for Securing Operations Of Logistics
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Operational Security As A Component Of Cybersecurity Training Ppt
Operational Security As A Component Of Cybersecurity Training PptPresenting Operational Security as a Component of Cybersecurity. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. It is well crafted and designed by our PowerPoint specialists. Suitable for use by managers, employees, and organizations. You can edit the color, text, icon, and font size to suit your requirements. The PPT also supports Google Slides. Even Premium Customer Support is also available. Download now and present with confidence.
-
 Overview Of Importance Of Operational Security Training Ppt
Overview Of Importance Of Operational Security Training PptPresenting Overview of Importance of Operational Security. This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizable alter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
 Mitigation As A Part Of An Operational Security Plan Training Ppt
Mitigation As A Part Of An Operational Security Plan Training PptPresenting Mitigation as a Part of an Operational Security Plan. This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizable alter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
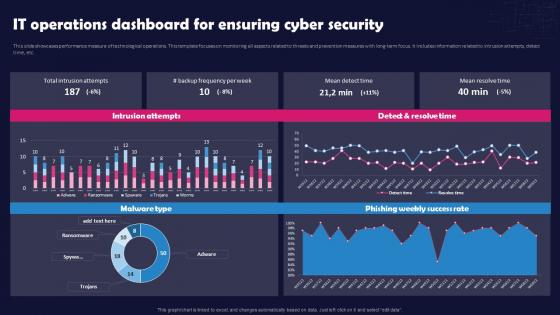 Unlocking The Impact Of Technology It Operations Dashboard For Ensuring Cyber Security
Unlocking The Impact Of Technology It Operations Dashboard For Ensuring Cyber SecurityThis slide showcases performance measure of technological operations. This template focuses on monitoring all aspects related to threats and prevention measures with long-term focus. It includes information related to intrusion attempts, detect time, etc. Present the topic in a bit more detail with this Unlocking The Impact Of Technology It Operations Dashboard For Ensuring Cyber Security. Use it as a tool for discussion and navigation on IT Operations Dashboard, Ensuring Cyber Security, Threats And Prevention, Technological Operations. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
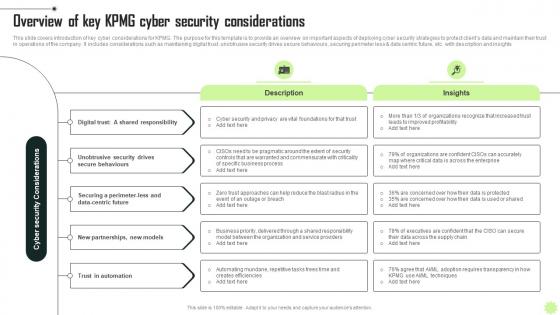 Overview Of Key KPMG Cyber Security KPMG Operational And Marketing Strategy SS V
Overview Of Key KPMG Cyber Security KPMG Operational And Marketing Strategy SS VThis slide covers introduction of key cyber considerations for KPMG. The purpose for this template is to provide an overview on important aspects of deploying cyber security strategies to protect clients data and maintain their trust in operations of the company. It includes considerations such as maintaining digital trust, unobtrusive security drives secure behaviours, securing perimeter less and data centric future, etc. with description and insights Increase audience engagement and knowledge by dispensing information using Overview Of Key KPMG Cyber Security KPMG Operational And Marketing Strategy SS V. This template helps you present information on five stages. You can also present information on Digital, Security, Automation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Elements of computer security operational security computer system security
Elements of computer security operational security computer system securityThis slide defines the operational security element of cyber security. It also shows the best practices for operational security such as change management processes, deploys automation, etc. Increase audience engagement and knowledge by dispensing information using Elements Of Computer Security Operational Security Computer System Security. This template helps you present information on five stages. You can also present information on Change Management Processes, Deploy Automation, Plan For Disaster, Restrict Device Access, Implement Dual Control using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Computer system security main steps of operational security
Computer system security main steps of operational securityThis slide depicts the main steps of operational security, such as describing sensitive information, identifying potential risks, and so on, by showing how these steps are operating. Introducing Computer System Security Main Steps Of Operational Security to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Assessment Of Risks, Analyze Security Holes And Vulnerabilities, Potential Threats, Sensitive Information, Implementation Of Appropriate Countermeasures, using this template. Grab it now to reap its full benefits.
-
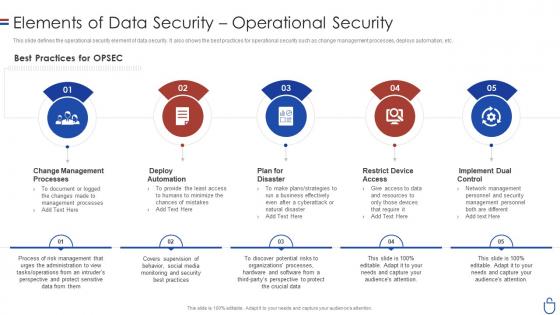 Data security it elements of data security operational security
Data security it elements of data security operational securityThis slide defines the operational security element of data security. It also shows the best practices for operational security such as change management processes, deploys automation, etc. Introducing Data Security IT Elements Of Data Security Operational Security to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Best Practices, OPSEC, Change Management Processes, Deploy Automation, Plan For Disaster, Restrict Device Access, Implement Dual Control, using this template. Grab it now to reap its full benefits.
-
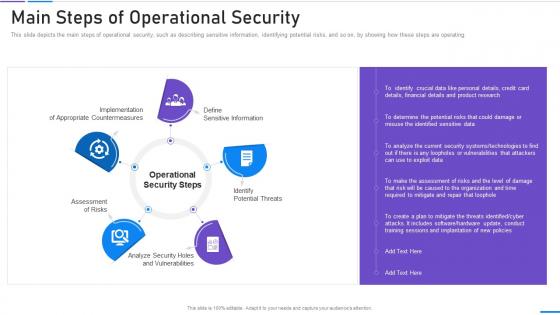
 Data security it main steps of operational security
Data security it main steps of operational securityThis slide depicts the main steps of operational security, such as describing sensitive information, identifying potential risks, and so on, by showing how these steps are operating. Increase audience engagement and knowledge by dispensing information using Data Security IT Main Steps Of Operational Security. This template helps you present information on one stages. You can also present information on Financial Details, Product Research, Exploit Data, Plan using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Application Of Digital Security In Operational Technology
Application Of Digital Security In Operational TechnologyThis slide showcase operational technology cyber risk strategy mapping to different project lifecycles from strategy, architecture, implementation, and operations phases to prevent, predict, detect and response adaptative security model Presenting our well structured Application Of Digital Security In Operational Technology. The topics discussed in this slide are Digital, Priorities, Scenarios. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
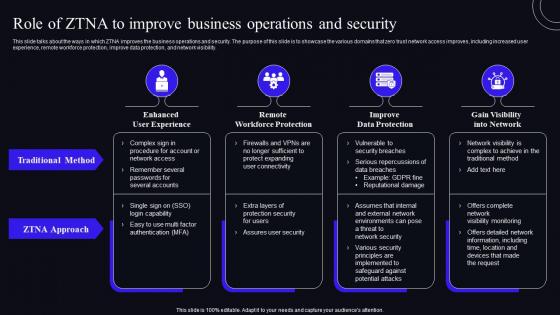 Role Of ZTNA To Improve Business Operations And Security Zero Trust Security Model
Role Of ZTNA To Improve Business Operations And Security Zero Trust Security ModelThis slide talks about the ways in which ZTNA improves the business operations and security. The purpose of this slide is to showcase the various domains that zero trust network access improves, including increased user experience, remote workforce protection, improve data protection, and network visibility. Deliver an outstanding presentation on the topic using this Role Of ZTNA To Improve Business Operations And Security Zero Trust Security Model. Dispense information and present a thorough explanation of Enhanced User Experience, Remote Workforce Protection, Improve Data Protection using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Secops V2 Challenges And Solutions Of Security Operations Centres
Secops V2 Challenges And Solutions Of Security Operations CentresThis slide outlines the key challenges and solutions of security operations centers. The purpose of this slide is to highlight the problems faced by SOC teams and methods to overcome those problems. The main challenges include talent gaps, sophisticated attackers, increased data and network traffic, etc. Present the topic in a bit more detail with this Secops V2 Challenges And Solutions Of Security Operations Centres. Use it as a tool for discussion and navigation on Challenges And Solutions, Security Operations Centres, Sophisticated Attackers, Data And Network Traffic. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
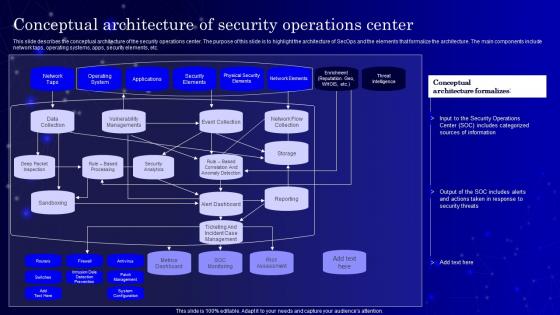 Secops V2 Conceptual Architecture Of Security Operations Center
Secops V2 Conceptual Architecture Of Security Operations CenterThis slide describes the conceptual architecture of the security operations center. The purpose of this slide is to highlight the architecture of SecOps and the elements that formalize the architecture. The main components include network taps, operating systems, apps, security elements, etc. Deliver an outstanding presentation on the topic using this Secops V2 Conceptual Architecture Of Security Operations Center. Dispense information and present a thorough explanation of Conceptual Architecture, Security Operations Center, Network Taps, Operating Systems, Security Elements using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
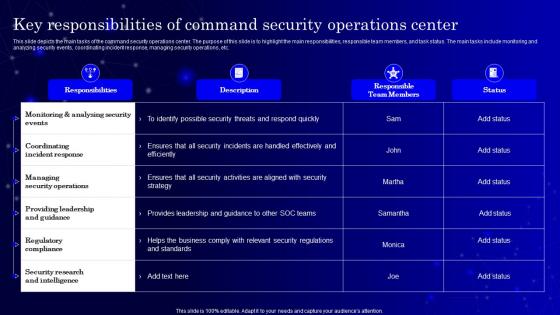 Secops V2 Key Responsibilities Of Command Security Operations Center
Secops V2 Key Responsibilities Of Command Security Operations CenterThis slide depicts the main tasks of the command security operations center. The purpose of this slide is to highlight the main responsibilities, responsible team members, and task status. The main tasks include monitoring and analyzing security events, coordinating incident response, managing security operations, etc. Present the topic in a bit more detail with this Secops V2 Key Responsibilities Of Command Security Operations Center. Use it as a tool for discussion and navigation on Monitoring And Analysing Security Events, Coordinating Incident Response, Regulatory Compliance. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Secops V2 Main Responsibilities Of Security Operations Center Soc
Secops V2 Main Responsibilities Of Security Operations Center SocThis slide describes the different responsibilities of a secure operations center. The purpose of this slide is to showcase the multiple functions SOC teams perform, including communication with DevOps teams, coordinating incident response process, incident investigation, and prioritization of threats. Introducing Secops V2 Main Responsibilities Of Security Operations Center Soc to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Coordinating Incident Response Process, Incident Investigation, Prioritization, using this template. Grab it now to reap its full benefits.
-
 Secops V2 Roles And Responsibilities Of Security Operations Center Team
Secops V2 Roles And Responsibilities Of Security Operations Center TeamThis slide outlines the roles and responsibilities of the security operations center team. The purpose of this slide is to showcase the roles as well as duties of the SOC team. The prominent roles include incident responder, security investigator, advanced security analyst, SOC manager, and security engineer. Introducing Secops V2 Roles And Responsibilities Of Security Operations Center Team to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Incident Responder, Security Investigator, Advanced Security Analyst, Security Engineer Or Architect, using this template. Grab it now to reap its full benefits.
-
 Zero Trust Architecture ZTA Role Of ZTNA To Improve Business Operations And Security
Zero Trust Architecture ZTA Role Of ZTNA To Improve Business Operations And SecurityThis slide talks about the ways in which ZTNA improves the business operations and security. The purpose of this slide is to showcase the various domains that zero trust network access improves, including increased user experience, remote workforce protection, improve data protection, and network visibility. Introducing Zero Trust Architecture ZTA Role Of ZTNA To Improve Business Operations And Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Traditional Method, ZTNA Approach, Login Capability, using this template. Grab it now to reap its full benefits.
-
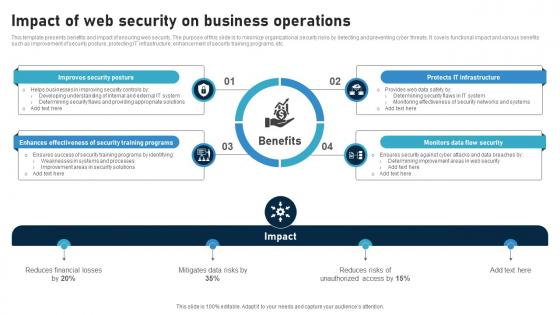 Impact Of Web Security On Business Operations
Impact Of Web Security On Business OperationsThis template presents benefits and impact of ensuring web security. The purpose of this slide is to minimize organizational security risks by detecting and preventing cyber threats. It covers functional impact and various benefits such as improvement of security posture, protecting IT infrastructure, enhancement of security training programs, etc. Introducing our Impact Of Web Security On Business Operations set of slides. The topics discussed in these slides are Monitors Data Flow Security, Protects IT Infrastructure, Improves Security Posture This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Role Of ZTNA To Improve Business Operations And Security Identity Defined Networking
Role Of ZTNA To Improve Business Operations And Security Identity Defined NetworkingThis slide talks about the ways in which ZTNA improves the business operations and security. The purpose of this slide is to showcase the various domains that zero trust network access improves, including increased user experience, remote workforce protection, improve data protection, and network visibility. Present the topic in a bit more detail with this Role Of ZTNA To Improve Business Operations And Security Identity Defined Networking. Use it as a tool for discussion and navigation on Traditional Method, Workforce Protection, Data Protection. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
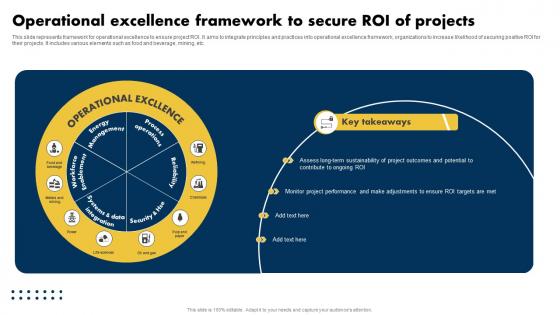 Operational Excellence Framework To Secure Roi Of Projects
Operational Excellence Framework To Secure Roi Of ProjectsThis slide represents framework for operational excellence to ensure project ROI. It aims to integrate principles and practices into operational excellence framework, organizations to increase likelihood of securing positive ROI for their projects. It includes various elements such as food and beverage, mining, etc. Presenting our well structured Operational Excellence Framework To Secure Roi Of Projects. The topics discussed in this slide are Excellence, Secure, Projects. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 ChatGPT Use Cases For Streamlining Security Operations Impact Of Generative AI SS V
ChatGPT Use Cases For Streamlining Security Operations Impact Of Generative AI SS VThis slide showcases various ChatGPT use cases for streamlining and automating the cybersecurity operations of organization. Its key elements are establish security policies, automate repetitive tasks and identification of vulnerabilities. Increase audience engagement and knowledge by dispensing information using ChatGPT Use Cases For Streamlining Security Operations Impact Of Generative AI SS V. This template helps you present information on three stages. You can also present information on Establish Security, Automate Repetitive Tasks, Identify Vulnerabilities using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
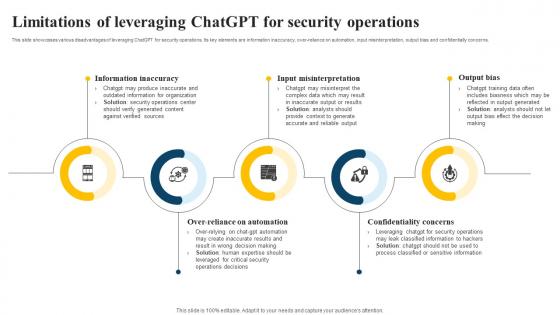 Limitations Of Leveraging ChatGPT For Security Operations Impact Of Generative AI SS V
Limitations Of Leveraging ChatGPT For Security Operations Impact Of Generative AI SS VThis slide showcases various disadvantages of leveraging ChatGPT for security operations. Its key elements are information inaccuracy, over-reliance on automation, input misinterpretation, output bias and confidentially concerns. Increase audience engagement and knowledge by dispensing information using Limitations Of Leveraging ChatGPT For Security Operations Impact Of Generative AI SS V. This template helps you present information on five stages. You can also present information on Information Inaccuracy, Input Misinterpretation, Confidentiality Concerns using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
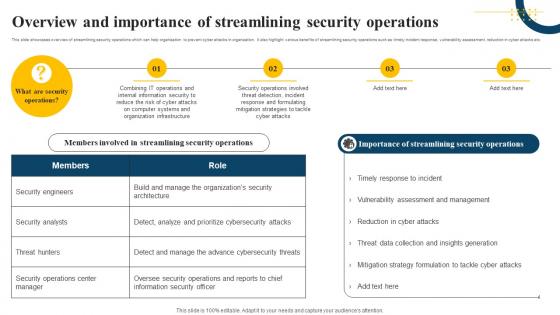 Overview And Importance Of Streamlining Security Operations Impact Of Generative AI SS V
Overview And Importance Of Streamlining Security Operations Impact Of Generative AI SS VThis slide showcases overview of streamlining security operations which can help organization to prevent cyber attacks in organization. It also highlight various benefits of streamlining security operations such as timely incident response, vulnerability assessment, reduction in cyber attacks etc. Increase audience engagement and knowledge by dispensing information using Overview And Importance Of Streamlining Security Operations Impact Of Generative AI SS V. This template helps you present information on four stages. You can also present information on Organization Infrastructure, Cyber Attacks using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
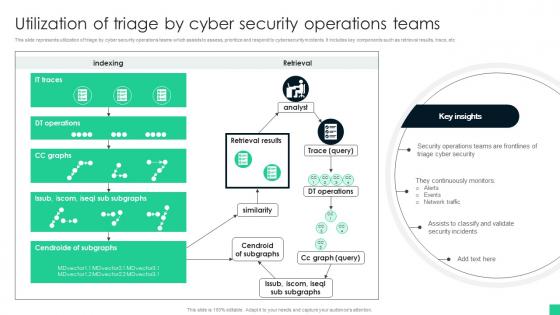 Utilization Of Triage By Cyber Security Operations Teams
Utilization Of Triage By Cyber Security Operations TeamsThis slide represents utilization of triage by cyber security operations teams which assists to assess, prioritize and respond to cybersecurity incidents. It includes key components such as retrieval results, trace, etc Introducing our Utilization Of Triage By Cyber Security Operations Teams set of slides. The topics discussed in these slides are Triage Cyber Security, Network Traffic, Security Incidents. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Maintained security of operations powerpoint ideas
Maintained security of operations powerpoint ideasPresenting maintained security of operations powerpoint ideas. This is a maintained security of operations powerpoint ideas. This is a five stage process. The stages in this process are improved operational performance and efficiency, enhanced ability to strategically plan, enhanced brand recognition, maintained security of operations, value creation.
-
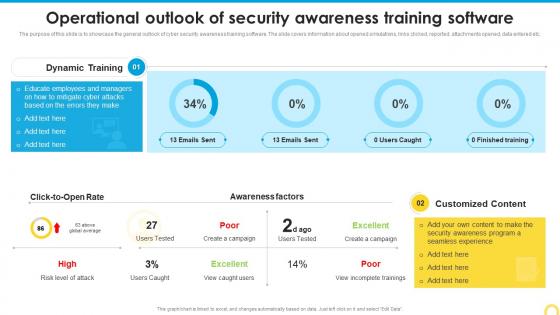 Operational Outlook Of Security Building A Security Awareness Program
Operational Outlook Of Security Building A Security Awareness ProgramThe purpose of this slide is to showcase the general outlook of cyber security awareness training software. The slide covers information about opened simulations, links clicked, reported, attachments opened, data entered etc. Present the topic in a bit more detail with this Operational Outlook Of Security Building A Security Awareness Program. Use it as a tool for discussion and navigation on Customized Content, Awareness Factors, Training Software. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Operational Outlook Of Security Awareness Training Implementing Security Awareness Training
Operational Outlook Of Security Awareness Training Implementing Security Awareness TrainingThe purpose of this slide is to showcase the general outlook of cyber security awareness training software. The slide covers information about opened simulations, links clicked, reported, attachments opened, data entered etc. Present the topic in a bit more detail with this Operational Outlook Of Security Awareness Training Implementing Security Awareness Training. Use it as a tool for discussion and navigation on Operational Outlook, Security Awareness, Training Software. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
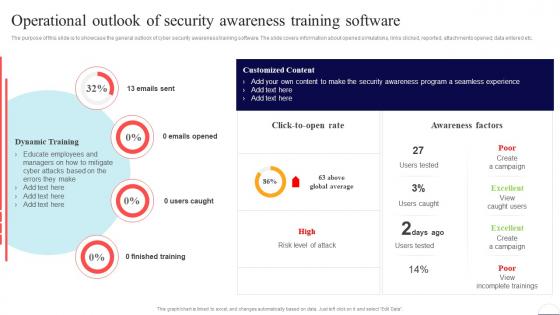 Operational Outlook Of Security Awareness Training Software Preventing Data Breaches Through Cyber Security
Operational Outlook Of Security Awareness Training Software Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to showcase the general outlook of cyber security awareness training software. The slide covers information about opened simulations, links clicked, reported, attachments opened, data entered etc. Present the topic in a bit more detail with this Operational Outlook Of Security Awareness Training Software Preventing Data Breaches Through Cyber Security. Use it as a tool for discussion and navigation on Finished Training, Awareness Factors, Training Software. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Operational Outlook Of Security Awareness Training Software Developing Cyber Security Awareness Training
Operational Outlook Of Security Awareness Training Software Developing Cyber Security Awareness TrainingThe purpose of this slide is to showcase the general outlook of cyber security awareness training software. The slide covers information about opened simulations, links clicked, reported, attachments opened, data entered etc. Deliver an outstanding presentation on the topic using this Operational Outlook Of Security Awareness Training Software Developing Cyber Security Awareness Training. Dispense information and present a thorough explanation of Operational Outlook, Security Awareness, Training Software using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Operational Outlook Of Security Awareness Training Software Conducting Security Awareness
Operational Outlook Of Security Awareness Training Software Conducting Security AwarenessThe purpose of this slide is to showcase the general outlook of cyber security awareness training software. The slide covers information about opened simulations, links clicked, reported, attachments opened, data entered etc. Present the topic in a bit more detail with this Operational Outlook Of Security Awareness Training Software Conducting Security Awareness. Use it as a tool for discussion and navigation on Dynamic Training, Emails Opened, Users Caught. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
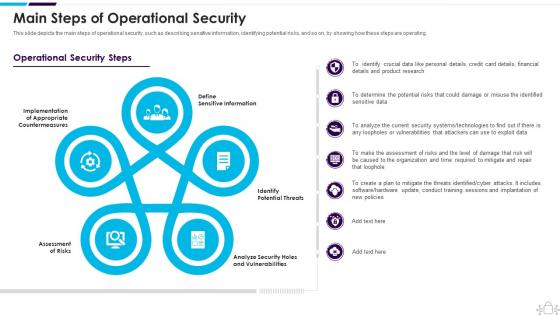 Information Technology Security Main Steps Of Operational Security
Information Technology Security Main Steps Of Operational SecurityThis slide depicts the main steps of operational security, such as describing sensitive information, identifying potential risks, and so on, by showing how these steps are operating. Present the topic in a bit more detail with this Information Technology Security Main Steps Of Operational Security. Use it as a tool for discussion and navigation on Assessment Of Risks, Define Sensitive Information, Identify Potential Threats This template is free to edit as deemed fit for your organization. Therefore download it now.
-
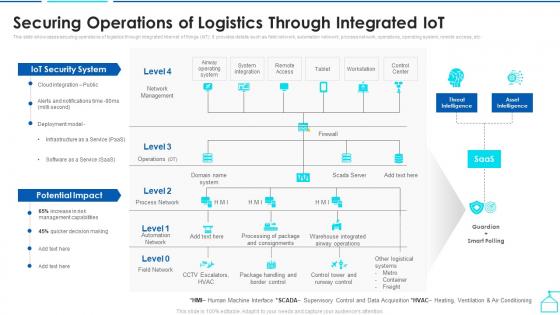 Securing Operations Of Logistics Through Integrated Enabling Smart Shipping And Logistics Through Iot
Securing Operations Of Logistics Through Integrated Enabling Smart Shipping And Logistics Through IotThis slide showcases securing operations of logistics through integrated internet of things IoT. It provides details such as field network, automation network, process network, operations, operating system, remote access, etc. Deliver an outstanding presentation on the topic using this Securing Operations Of Logistics Through Integrated Enabling Smart Shipping And Logistics Through Iot. Dispense information and present a thorough explanation of Potential Impact, Iot Security System, Securing Operations using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
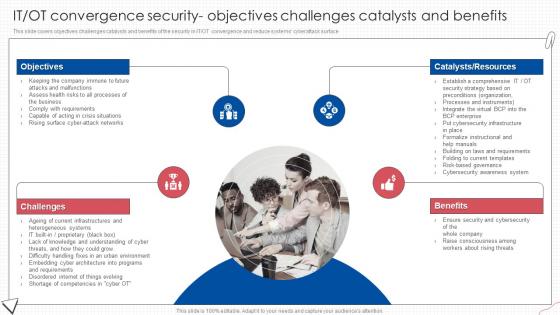 IT OT Convergence Security Objectives Digital Transformation Of Operational Industries
IT OT Convergence Security Objectives Digital Transformation Of Operational IndustriesThis slide covers objectives challenges catalysts and benefits of the security in IT OT convergence and reduce systems cyberattack surface.Introducing IT OT Convergence Security Objectives Digital Transformation Of Operational Industries to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Objectives, Benefits, Consciousness Among, using this template. Grab it now to reap its full benefits.
-
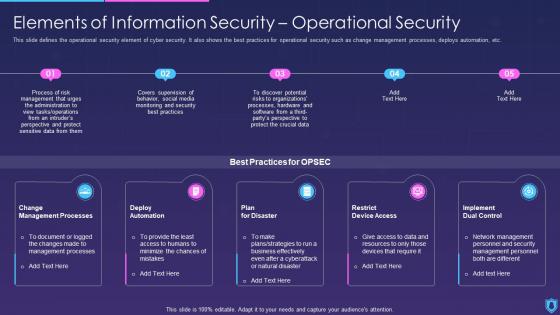 Information Security Elements Of Information Security Operational Security
Information Security Elements Of Information Security Operational SecurityThis slide defines the operational security element of cyber security. It also shows the best practices for operational security such as change management processes, deploys automation, etc. Present the topic in a bit more detail with this Information Security Elements Of Information Security Operational Security. Use it as a tool for discussion and navigation on Operational, Security, Elements. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Steps Of Operational Security Information Security
Steps Of Operational Security Information SecurityThis slide depicts the main steps of operational security, such as describing sensitive information, identifying potential risks, and so on, by showing how these steps are operating. Increase audience engagement and knowledge by dispensing information using Steps Of Operational Security Information Security. This template helps you present information on five stages. You can also present information on Main Steps Of Operational Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
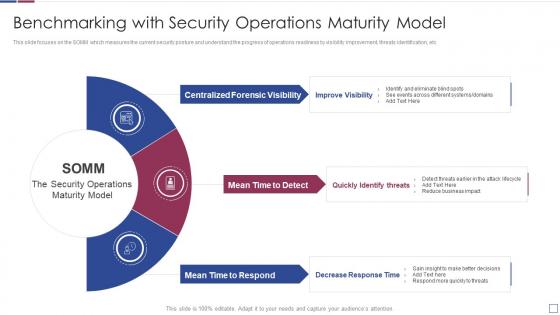 Real time analysis of security alerts benchmarking with security operations maturity model
Real time analysis of security alerts benchmarking with security operations maturity modelThis slide focuses on the SOMM which measures the current security posture and understand the progress of operations readiness by visibility improvement, threats identification, etc. Introducing Real Time Analysis Of Security Alerts Benchmarking With Security Operations Maturity Model to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Centralized Forensic Visibility, Mean Time To Detect, Mean Time To Respond, using this template. Grab it now to reap its full benefits.
-
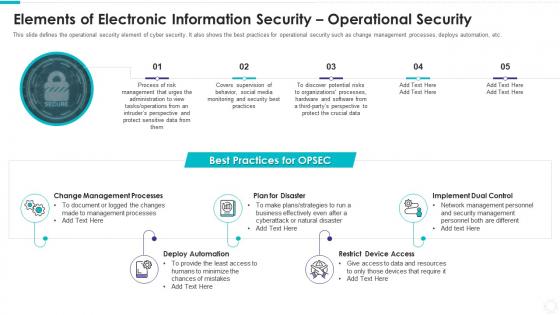 Elements of electronic information security operational security
Elements of electronic information security operational securityThis slide defines the operational security element of cyber security. It also shows the best practices for operational security such as change management processes, deploys automation, etc. Increase audience engagement and knowledge by dispensing information using Elements Of Electronic Information Security Operational Security. This template helps you present information on five stages. You can also present information on Change Management Processes, Plan Disaster, Deploy Automation, Restrict Device Access, Implement Dual Control using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
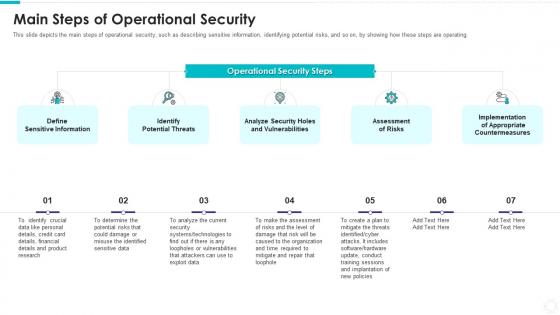 Electronic information security main steps of operational security
Electronic information security main steps of operational securityThis slide depicts the main steps of operational security, such as describing sensitive information, identifying potential risks, and so on, by showing how these steps are operating. Introducing Electronic Information Security Main Steps Of Operational Security to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Define Sensitive Information, Identify Potential Threats, Analyze Security Holes And Vulnerabilities, Assessment Risks, Implementation Appropriate Countermeasures, using this template. Grab it now to reap its full benefits.
-
 Elements Of Network Security Operational Security Ppt Styles Example File
Elements Of Network Security Operational Security Ppt Styles Example FileThis slide defines the operational security element of cyber security. It also shows the best practices for operational security such as change management processes, deploys automation, etc. Introducing Elements Of Network Security Operational Security Ppt Styles Example File to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Management, Sensitive, Administration, Operations, using this template. Grab it now to reap its full benefits.
-
 Network Security Main Steps Of Operational Security
Network Security Main Steps Of Operational SecurityThis slide depicts the main steps of operational security, such as describing sensitive information, identifying potential risks, and so on, by showing how these steps are operating. Increase audience engagement and knowledge by dispensing information using Network Security Main Steps Of Operational Security. This template helps you present information on five stages. You can also present information on Sensitive Information, Potential Threats, Vulnerabilities, Implementation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
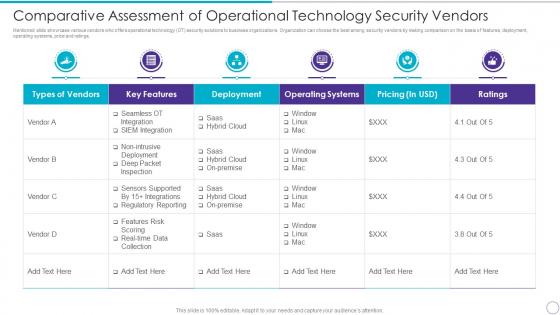 Comparative Assessment Of Operational Technology Security Vendors
Comparative Assessment Of Operational Technology Security VendorsMentioned slide showcase various vendors who offers operational technology OT security solutions to business organizations. Organization can choose the best among security vendors by making comparison on the basis of features, deployment, operating systems, price and ratings. Present the topic in a bit more detail with this Comparative Assessment Of Operational Technology Security Vendors. Use it as a tool for discussion and navigation on Types Vendors, Key Features, Deployment, Operating Systems, Pricing In USD, Ratings. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
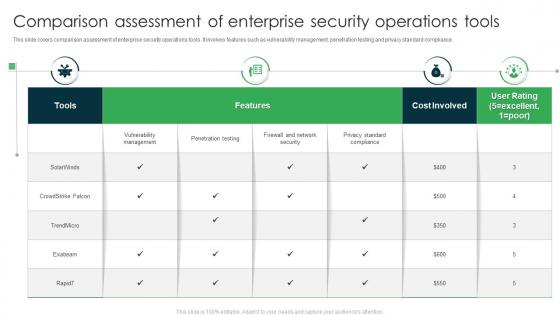 Comparison Assessment Of Enterprise Security Operations Tools
Comparison Assessment Of Enterprise Security Operations ToolsThis slide covers comparison assessment of enterprise security operations tools. It involves features such as vulnerability management, penetration testing and privacy standard compliance. Introducing our Comparison Assessment Of Enterprise Security Operations Tools set of slides. The topics discussed in these slides are Features, Cost Involved, User Rating. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
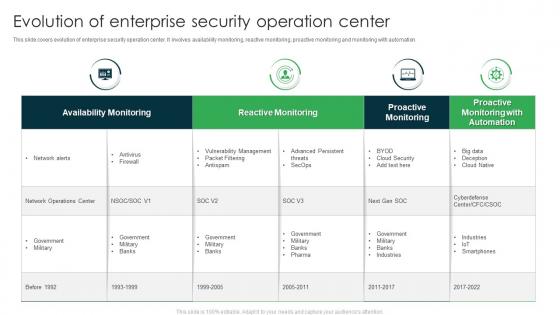 Evolution Of Enterprise Security Operation Center
Evolution Of Enterprise Security Operation CenterThis slide covers evolution of enterprise security operation center. It involves availability monitoring, reactive monitoring, proactive monitoring and monitoring with automation. Introducing our Evolution Of Enterprise Security Operation Center set of slides. The topics discussed in these slides are Reactive Monitoring, Availability Monitoring, Proactive Monitoring. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
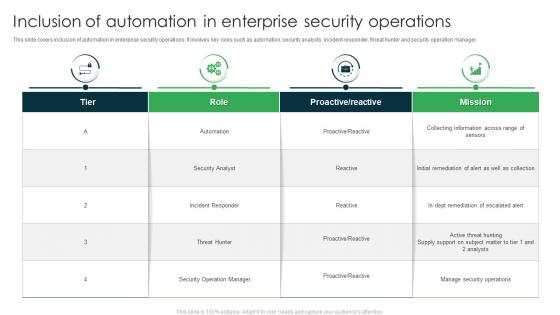 Inclusion Of Automation In Enterprise Security Operations
Inclusion Of Automation In Enterprise Security OperationsThis slide covers inclusion of automation in enterprise security operations. It involves key roles such as automation, security analysts, incident responder, threat hunter and security operation manager. Presenting our well structured Inclusion Of Automation In Enterprise Security Operations. The topics discussed in this slide are Security Analyst, Incident Responder, Security Operation Manager. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
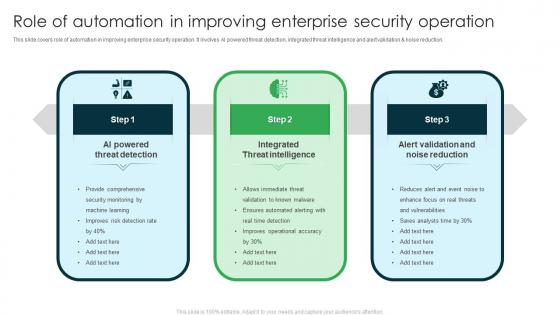 Role Of Automation In Improving Enterprise Security Operation
Role Of Automation In Improving Enterprise Security OperationThis slide covers role of automation in improving enterprise security operation. It involves AI powered threat detection, integrated threat intelligence and alert validation and noise reduction. Presenting our set of slides with Role Of Automation In Improving Enterprise Security Operation. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on AI Powered Threat Detection, Integrated Threat Intelligence, Alert Validation And Noise Reduction.
-
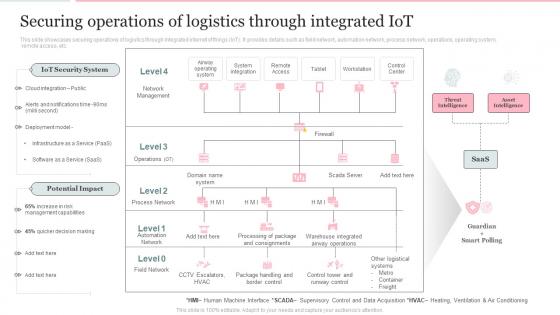 Deploying Internet Logistics Efficient Operations Securing Operations Of Logistics Through Integrated Iot
Deploying Internet Logistics Efficient Operations Securing Operations Of Logistics Through Integrated IotThis slide showcases securing operations of logistics through integrated internet of things IoT. It provides details such as field network, automation network, process network, operations, operating system, remote access, etc. Present the topic in a bit more detail with this Deploying Internet Logistics Efficient Operations Securing Operations Of Logistics Through Integrated Iot. Use it as a tool for discussion and navigation on Operations, Logistics, Potential Impact. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
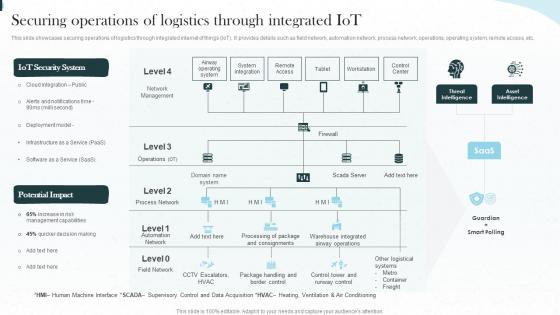 Implementing Iot Architecture In Shipping Business Securing Operations Of Logistics Through Integrated Iot
Implementing Iot Architecture In Shipping Business Securing Operations Of Logistics Through Integrated IotThis slide showcases securing operations of logistics through integrated internet of things IoT. It provides details such as field network, automation network, process network, operations, operating system, remote access, etc. Present the topic in a bit more detail with this Implementing Iot Architecture In Shipping Business Securing Operations Of Logistics Through Integrated Iot. Use it as a tool for discussion and navigation on Operations, Integrated, Workstation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Security Elements IT Operational Security Element Of Cyber Security Ppt Introduction
Cyber Security Elements IT Operational Security Element Of Cyber Security Ppt IntroductionThis slide defines the operational security element of cyber security. It also shows the best practices for operational security, such as changing management processes, deploying automation, planning for disasters, restricting device access, and implementing dual control. Increase audience engagement and knowledge by dispensing information using Cyber Security Elements IT Operational Security Element Of Cyber Security Ppt Introduction. This template helps you present information on five stages. You can also present information on Deploy Automation, Restrict Device Access, Change Management Processes using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Strategies To Enhance Retail Store Security Analysis Of Retail Store Operations Efficiency
Strategies To Enhance Retail Store Security Analysis Of Retail Store Operations EfficiencyThis slide provides information regarding the strategies to enhance retail store security such as integrate access control technology, deploy video surveillance, utilizes electronic article surveillance, install monitored alarms. Increase audience engagement and knowledge by dispensing information using Strategies To Enhance Retail Store Security Analysis Of Retail Store Operations Efficiency. This template helps you present information on four stages. You can also present information on Integrate Access Control Technology, Utilizes Electronic Article Surveillance, Install Monitored Alarm using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Enabling Automation In Cyber Security Operations Table Of Contents Ppt Slides Infographic Template
Enabling Automation In Cyber Security Operations Table Of Contents Ppt Slides Infographic TemplateDeliver an outstanding presentation on the topic using this Enabling Automation In Cyber Security Operations Table Of Contents Ppt Slides Infographic Template. Dispense information and present a thorough explanation of Protection Platform, Security Automation, Processes using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Table Of Contents Enabling Automation In Cyber Security Operations Ppt Slides Background Image
Table Of Contents Enabling Automation In Cyber Security Operations Ppt Slides Background ImageIntroducing Table Of Contents Enabling Automation In Cyber Security Operations Ppt Slides Background Image to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Security Automation, Architecture And Importance, Security Automation Dashboards, using this template. Grab it now to reap its full benefits.
-
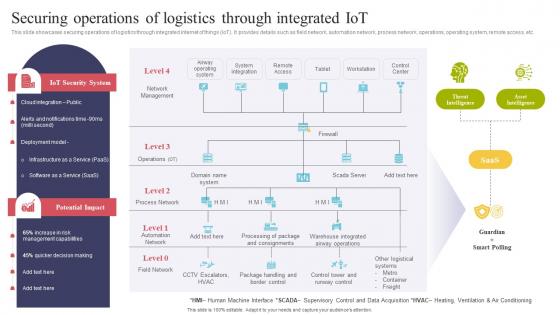 Securing Operations Of Logistics Through Integrated IOT Using IOT Technologies For Better Logistics
Securing Operations Of Logistics Through Integrated IOT Using IOT Technologies For Better LogisticsThis slide showcases securing operations of logistics through integrated internet of things IoT. It provides details such as field network, automation network, process network, operations, operating system, remote access, etc.Deliver an outstanding presentation on the topic using this Securing Operations Of Logistics Through Integrated IOT Using IOT Technologies For Better Logistics. Dispense information and present a thorough explanation of System Integration, Management Capabilities, Quicker Decision using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Roles And Responsibilities Of Security Operations Center Team Ppt Professional
Roles And Responsibilities Of Security Operations Center Team Ppt ProfessionalThis slide outlines the roles and responsibilities of the security operations center team. The purpose of this slide is to showcase the roles as well as duties of the SOC team. The prominent roles include incident responder, security investigator, advanced security analyst, SOC manager, and security engineer. Increase audience engagement and knowledge by dispensing information using Roles And Responsibilities Of Security Operations Center Team Ppt Professional. This template helps you present information on five stages. You can also present information on Incident Responder, Security Investigator using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
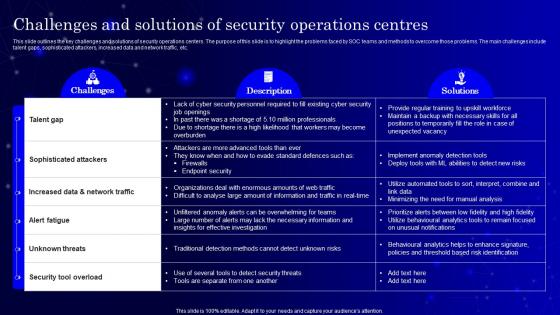 SecOps Challenges And Solutions Of Security Operations Centres Ppt Download
SecOps Challenges And Solutions Of Security Operations Centres Ppt DownloadThis slide outlines the key challenges and solutions of security operations centers. The purpose of this slide is to highlight the problems faced by SOC teams and methods to overcome those problems. The main challenges include talent gaps, sophisticated attackers, increased data and network traffic, etc. Deliver an outstanding presentation on the topic using this SecOps Challenges And Solutions Of Security Operations Centres Ppt Download. Dispense information and present a thorough explanation of Talent Gap, Sophisticated Attackers using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
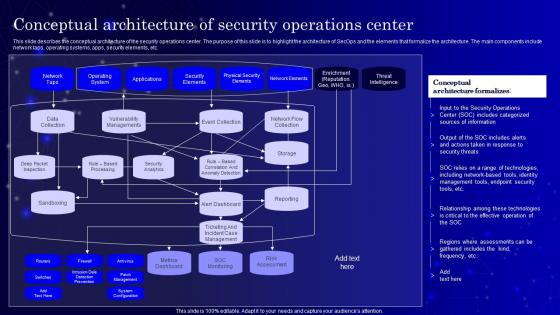 SecOps Conceptual Architecture Of Security Operations Center Ppt Brochure
SecOps Conceptual Architecture Of Security Operations Center Ppt BrochureThis slide describes the conceptual architecture of the security operations center. The purpose of this slide is to highlight the architecture of SecOps and the elements that formalize the architecture. The main components include network taps, operating systems, apps, security elements, etc. Deliver an outstanding presentation on the topic using this SecOps Conceptual Architecture Of Security Operations Center Ppt Brochure. Dispense information and present a thorough explanation of Network Taps, Operating System using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
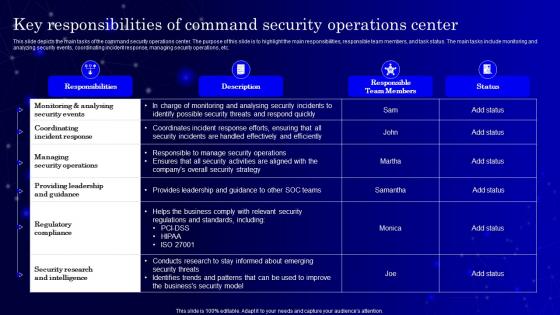 SecOps Key Responsibilities Of Command Security Operations Center Ppt Slides
SecOps Key Responsibilities Of Command Security Operations Center Ppt SlidesThis slide depicts the main tasks of the command security operations center. The purpose of this slide is to highlight the main responsibilities, responsible team members, and task status. The main tasks include monitoring and analyzing security events, coordinating incident response, managing security operations, etc. Present the topic in a bit more detail with this SecOps Key Responsibilities Of Command Security Operations Center Ppt Slides. Use it as a tool for discussion and navigation on Coordinating Incident Response, Responsible Team Members. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 SecOps Main Responsibilities Of Security Operations Center Soc
SecOps Main Responsibilities Of Security Operations Center SocThis slide describes the different responsibilities of a secure operations center. The purpose of this slide is to showcase the multiple functions SOC teams perform, including communication with DevOps teams, coordinating incident response process, incident investigation, and prioritization of threats. Introducing SecOps Main Responsibilities Of Security Operations Center Soc to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Communication, Incident Investigation, using this template. Grab it now to reap its full benefits.
-
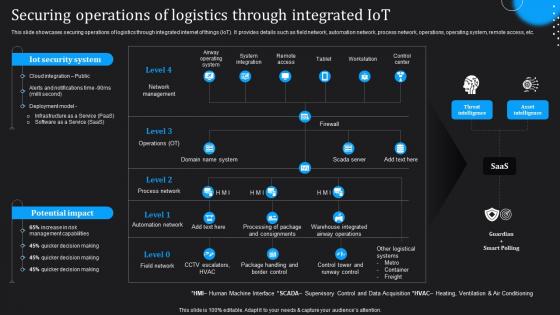 IoT Technologies For Logistics Securing Operations Of Logistics Through Integrated IoT
IoT Technologies For Logistics Securing Operations Of Logistics Through Integrated IoTThis slide showcases securing operations of logistics through integrated internet of things IoT. It provides details such as field network, automation network, process network, operations, operating system, remote access, etc. Deliver an outstanding presentation on the topic using this IoT Technologies For Logistics Securing Operations Of Logistics Through Integrated IoT. Dispense information and present a thorough explanation of Securing Operations Of Logistics, Threat Intelligence, Asset Intelligence using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 ZTNA Role Of ZTNA To Improve Business Operations And Security
ZTNA Role Of ZTNA To Improve Business Operations And SecurityThis slide talks about the ways in which ZTNA improves the business operations and security. The purpose of this slide is to showcase the various domains that zero trust network access improves, including increased user experience, remote workforce protection, improve data protection, and network visibility. Increase audience engagement and knowledge by dispensing information using ZTNA Role Of ZTNA To Improve Business Operations And Security. This template helps you present information on four stages. You can also present information on Traditional Method, Ztna Approach, Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
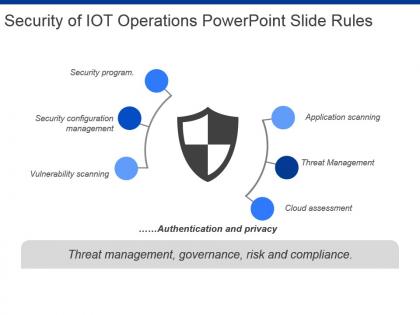 Security of iot operations powerpoint slide rules
Security of iot operations powerpoint slide rulesPresenting security of iot operations powerpoint slide rules. This is a security of iot operations powerpoint slide rules. This is a one stage process. The stages in this process are security program, security configuration management, vulnerability scanning, application scanning, threat management, cloud assessment, authentication and privacy.


