Powerpoint Templates and Google slides for Attack Prevention Techniques
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
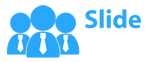
 Attack Prevention Layers Uses In DOS Network
Attack Prevention Layers Uses In DOS NetworkFollowing slide showcases DOS network attack prevention layers uses for reduced network congestion. It further covers attacks and exploits, functions and layers such as physical, data link, network, transport and session. Introducing our Attack Prevention Layers Uses In DOS Network set of slides. The topics discussed in these slides are Attacks And Exploits, Functions, Layers . This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
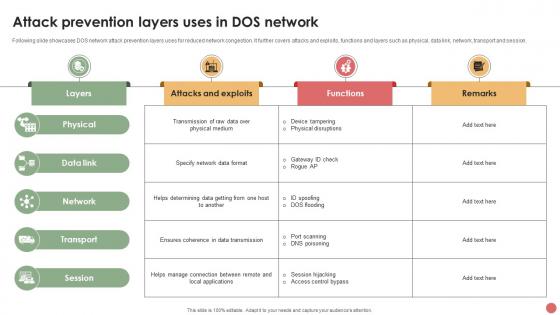
 Checklists To Plan DOS Attack Prevention
Checklists To Plan DOS Attack PreventionThis slide shows a checklist that can be used by organizations to prevent their computer systems from cyber-attacks and enhance cyber security. It includes elements such as tasks, responsible person, priority level, and status. Presenting our well structured Checklists To Plan DOS Attack Prevention. The topics discussed in this slide are Responsible Person, Priority, High. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
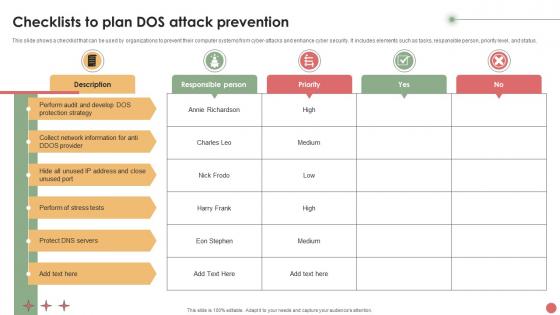
 Cloud Mitigation Strategies For DOS Attack Prevention
Cloud Mitigation Strategies For DOS Attack PreventionFollowing slide showcases DOS attack prevention cloud mitigation strategies for early threat detection and resolving it. It further covers paths for business as usual and when DOS attacks are detected. Introducing our premium set of slides with name Cloud Mitigation Strategies For DOS Attack Prevention. Ellicudate the one stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Internet, Service Provider, Cloud Mitigation Strategies. So download instantly and tailor it with your information.
-
 Malware Threat Attack Icon For DOS Attack Prevention
Malware Threat Attack Icon For DOS Attack PreventionPresenting our set of slides with name Malware Threat Attack Icon For DOS Attack Prevention. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Malware Threat ,Attack Icon, DOS Attack Prevention.
-
 Security Incident Icon To Prevent Cyber Attacks
Security Incident Icon To Prevent Cyber AttacksPresenting our set of slides with Security Incident Icon To Prevent Cyber Attacks. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Security Incident, Prevent Cyber Attacks.
-
 Biometric Authentication Trend Icon To Prevent Cybersecurity Attacks
Biometric Authentication Trend Icon To Prevent Cybersecurity AttacksIntroducing our premium set of slides with Biometric Authentication Trend Icon To Prevent Cybersecurity Attacks. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Biometric Authentication Trend, Icon To Prevent, Cybersecurity Attacks. So download instantly and tailor it with your information.
-
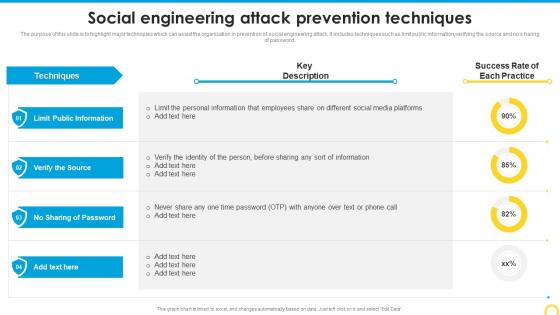 Social Engineering Attack Prevention Techniques Building A Security Awareness Program
Social Engineering Attack Prevention Techniques Building A Security Awareness ProgramThe purpose of this slide is to highlight major techniques which can assist the organization in prevention of social engineering attack. It includes techniques such as limit public information, verifying the source and no s haring of password. Deliver an outstanding presentation on the topic using this Social Engineering Attack Prevention Techniques Building A Security Awareness Program. Dispense information and present a thorough explanation of Public Information, Prevention Techniques, Social Engineering Attack using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Social Engineering Attack Prevention Techniques Implementing Security Awareness Training
Social Engineering Attack Prevention Techniques Implementing Security Awareness TrainingThe purpose of this slide is to highlight major techniques which can assist the organization in prevention of social engineering attack. It includes techniques such as limit public information, verifying the source and no s haring of password. Present the topic in a bit more detail with this Social Engineering Attack Prevention Techniques Implementing Security Awareness Training. Use it as a tool for discussion and navigation on Limit Public Information, Verify The Source, No Sharing Of Password. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Table Of Contents Implementing Security Awareness Training To Prevent Cyber Attacks
Table Of Contents Implementing Security Awareness Training To Prevent Cyber AttacksPresent the topic in a bit more detail with this Table Of Contents Implementing Security Awareness Training To Prevent Cyber Attacks. Use it as a tool for discussion and navigation on Security Awareness, Current Assessment, Organization. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
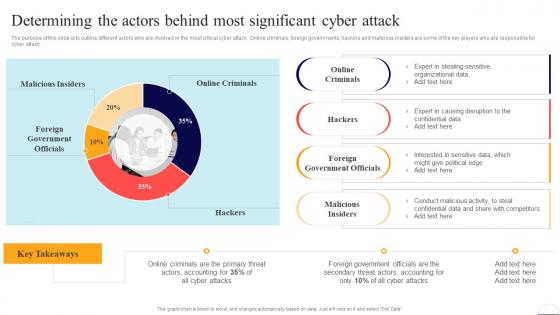 Determining The Actors Behind Most Significant Cyber Attack Preventing Data Breaches Through Cyber Security
Determining The Actors Behind Most Significant Cyber Attack Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to outline different actors who are involved in the most critical cyber attack. Online criminals, foreign governments, hackers and malicious insiders are some of the key players who are responsible for cyber attack. Present the topic in a bit more detail with this Determining The Actors Behind Most Significant Cyber Attack Preventing Data Breaches Through Cyber Security. Use it as a tool for discussion and navigation on Online Criminals, Foreign Government Officials, Malicious Insiders. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
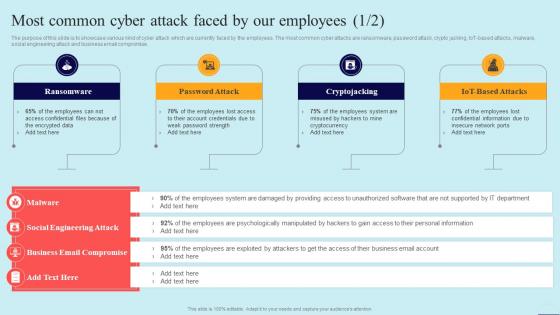 Most Common Cyber Attack Faced By Our Employees Preventing Data Breaches Through Cyber Security
Most Common Cyber Attack Faced By Our Employees Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to showcase various kind of cyber attack which are currently faced by the employees. The most common cyber attacks are ransomware, password attack, crypto jacking, IoT-based attacks, malware, social engineering attack and business email compromise. Introducing Most Common Cyber Attack Faced By Our Employees Preventing Data Breaches Through Cyber Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Ransomware, Password Attack, Cryptojacking, using this template. Grab it now to reap its full benefits.
-
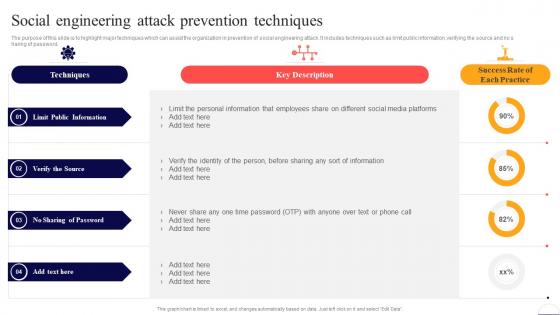 Social Engineering Attack Prevention Techniques Preventing Data Breaches Through Cyber Security
Social Engineering Attack Prevention Techniques Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to highlight major techniques which can assist the organization in prevention of social engineering attack. It includes techniques such as limit public information, verifying the source and no sharing of password. Present the topic in a bit more detail with this Social Engineering Attack Prevention Techniques Preventing Data Breaches Through Cyber Security. Use it as a tool for discussion and navigation on Limit Public Information, Verify The Source, No Sharing Of Password. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
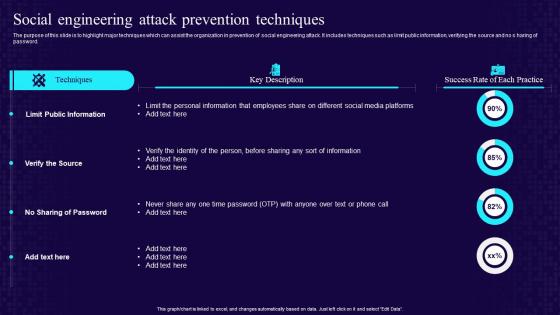 Social Engineering Attack Prevention Techniques Developing Cyber Security Awareness Training
Social Engineering Attack Prevention Techniques Developing Cyber Security Awareness TrainingThe purpose of this slide is to highlight major techniques which can assist the organization in prevention of social engineering attack. It includes techniques such as limit public information, verifying the source and no s haring of password. Deliver an outstanding presentation on the topic using this Social Engineering Attack Prevention Techniques Developing Cyber Security Awareness Training. Dispense information and present a thorough explanation of Limit Public Information, Verify The Source, No Sharing Of Password using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
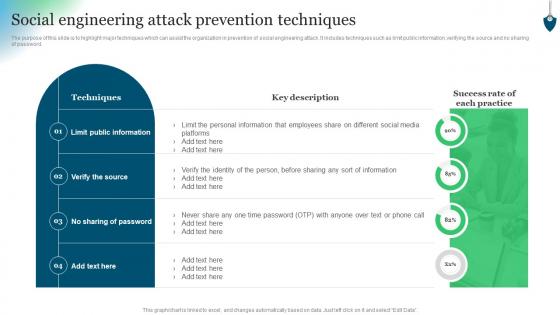 Social Engineering Attack Prevention Techniques Conducting Security Awareness
Social Engineering Attack Prevention Techniques Conducting Security AwarenessThe purpose of this slide is to highlight major techniques which can assist the organization in prevention of social engineering attack. It includes techniques such as limit public information, verifying the source and no sharing of password. Present the topic in a bit more detail with this Social Engineering Attack Prevention Techniques Conducting Security Awareness. Use it as a tool for discussion and navigation on Techniques, Limit Public Information, Verify Source. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
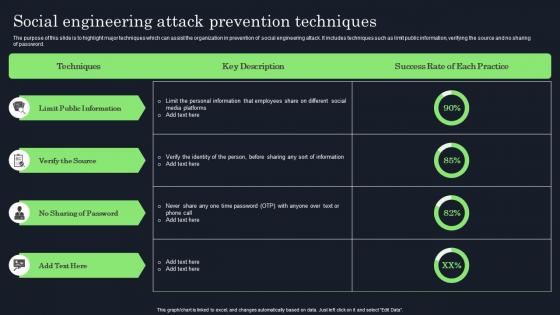 Social Engineering Attack Prevention Techniques Raising Cyber Security Awareness In Organizations
Social Engineering Attack Prevention Techniques Raising Cyber Security Awareness In OrganizationsThe purpose of this slide is to highlight major techniques which can assist the organization in prevention of social engineering attack. It includes techniques such as limit public information, verifying the source and no sharing of password. Present the topic in a bit more detail with this Social Engineering Attack Prevention Techniques Raising Cyber Security Awareness In Organizations. Use it as a tool for discussion and navigation on Verify The Source, Sharing Of Password, Public Information. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
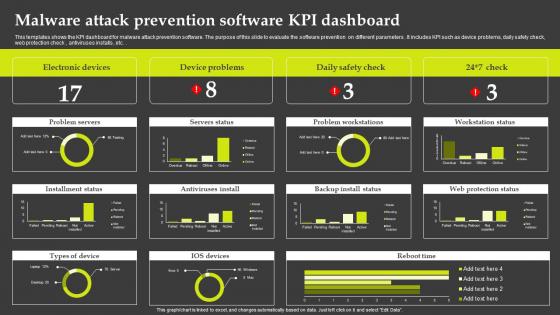 Malware Attack Prevention Software KPI Dashboard
Malware Attack Prevention Software KPI DashboardThis templates shows the KPI dashboard for malware attack prevention software. The purpose of this slide to evaluate the software prevention on different parameters . It includes KPI such as device problems, daily safety check, web protection check , antiviruses installs , etc.Introducing our Malware Attack Prevention Software KPI Dashboard set of slides. The topics discussed in these slides are Electronic Devices, Device Problems, Problem Workstations. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 5 Key Practices To Prevent Cyber Phishing Attack
5 Key Practices To Prevent Cyber Phishing AttackMentioned slide showcases best practices which can be implemented to prevent cyber phishing. The practices are recognizing hyperlinks attached in an email, backup system copies, secure robust HTTPs connections, installing a firewall and using anti spam tools. Presenting our set of slides with name 5 Key Practices To Prevent Cyber Phishing Attack. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Recognize Hyperlinks Attached In An Email, Secure HTTP Connections, Backup Copy.
-
 How To Prevent Ddos Attacks In The Company Cyber Terrorism Attacks
How To Prevent Ddos Attacks In The Company Cyber Terrorism AttacksThis slide represents the ways to prevent DDoS attacks in the company, which include network monitoring, updating security elements, etc. Introducing How To Prevent Ddos Attacks In The Company Cyber Terrorism Attacks to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Service, Bandwidth, Capacity, Network Monitoring, Mitigation Technologies, using this template. Grab it now to reap its full benefits.
-
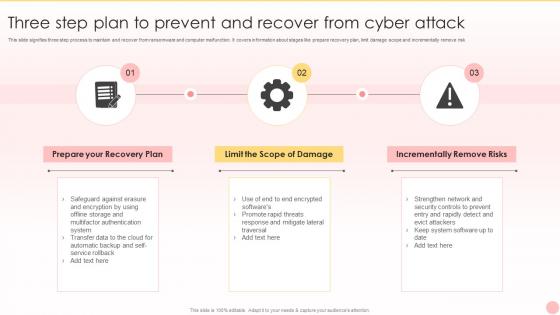 Three Step Plan To Prevent And Recover From Cyber Attack
Three Step Plan To Prevent And Recover From Cyber AttackThis slide signifies three step process to maintain and recover from ransomware and computer malfunction. It covers information about stages like prepare recovery plan, limit damage scope and incrementally remove risk. Introducing our premium set of slides with Three Step Plan To Prevent And Recover From Cyber Attack. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Prepare your Recovery Plan, Limit Scope Damage, Incrementally Remove Risks. So download instantly and tailor it with your information.
-
 Security measures to prevent phishing attacks ppt powerpoint presentation pictures display
Security measures to prevent phishing attacks ppt powerpoint presentation pictures displayThis slide represents the security measures to prevent phishing attacks, such as using the spam filter, updating security software regularly, utilization of multi factor authentication, and so on. Increase audience engagement and knowledge by dispensing information using Security Measures To Prevent Phishing Attacks Ppt Powerpoint Presentation Pictures Display. This template helps you present information on six stages. You can also present information on Security Measures To Prevent Phishing Attacks using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyberterrorism it how to prevent ddos attacks in the company
Cyberterrorism it how to prevent ddos attacks in the companyThis slide represents the ways to prevent DDoS attacks in the company, which include network monitoring, updating security elements, etc. Introducing Cyberterrorism IT How To Prevent Ddos Attacks In The Company to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Service Providers, Cloud Services, Network Monitoring, Combat Cybercrime, using this template. Grab it now to reap its full benefits.
-
 Agenda For Implementing Security Awareness Training To Prevent Cyber Attacks
Agenda For Implementing Security Awareness Training To Prevent Cyber AttacksIntroducing Agenda For Implementing Security Awareness Training To Prevent Cyber Attacks to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Awareness Campaign, Cyber Security, Awareness Training, using this template. Grab it now to reap its full benefits.
-
 Dos And Donts Of Prevention From Ransomware Attack Implementing Security Awareness Training
Dos And Donts Of Prevention From Ransomware Attack Implementing Security Awareness TrainingThe purpose of this slide is to showcase the Dos and donts of ransomware prevention attack. The slide covers information about updating the software, installing a firewall software, using reliable website and sources etc. Introducing Dos And Donts Of Prevention From Ransomware Attack Implementing Security Awareness Training to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Prevention, Ransomware Attack, using this template. Grab it now to reap its full benefits.
-
 G33 Table Of Contents Implementing Security Awareness Training To Prevent Cyber Attacks
G33 Table Of Contents Implementing Security Awareness Training To Prevent Cyber AttacksIntroducing G33 Table Of Contents Implementing Security Awareness Training To Prevent Cyber Attacks to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispence information on Current Assessment, Organization, Cyber Security, using this template. Grab it now to reap its full benefits.
-
 Icons Slide For Implementing Security Awareness Training To Prevent Cyber Attacks
Icons Slide For Implementing Security Awareness Training To Prevent Cyber AttacksIntroducing our well researched set of slides titled Icons Slide For Implementing Security Awareness Training To Prevent Cyber Attacks. It displays a hundred percent editable icons. You can use these icons in your presentation to captivate your audiences attention. Download now and use it multiple times.
-
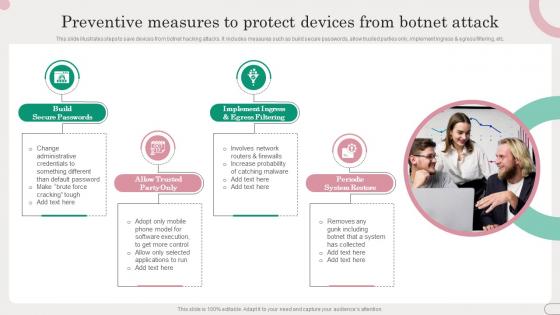 Preventive Measures To Protect Devices From Botnet Attack
Preventive Measures To Protect Devices From Botnet AttackThis slide illustrates steps to save devices from botnet hacking attacks. It includes measures such as build secure passwords, allow trusted parties only, implement ingress and egress filtering, etc. Introducing our premium set of slides with Preventive Measures To Protect Devices From Botnet Attack. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Build Secure Passwords, Periodic System Restore. So download instantly and tailor it with your information.
-
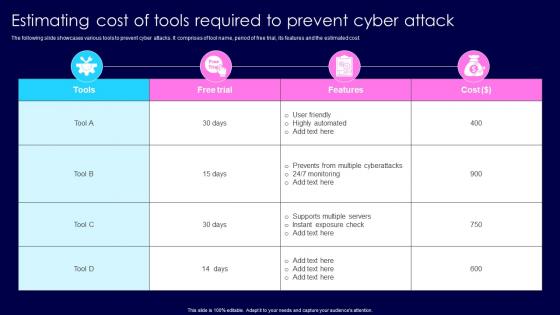 Estimating Cost Of Tools Required To Prevent Cyber Attack
Estimating Cost Of Tools Required To Prevent Cyber AttackThe following slide showcases various tools to prevent cyber attacks. It comprises of tool name, period of free trial, its features and the estimated cost. Introducing our Estimating Cost Of Tools Required To Prevent Cyber Attack set of slides. The topics discussed in these slides are Highly Automated, Supports Multiple Servers. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
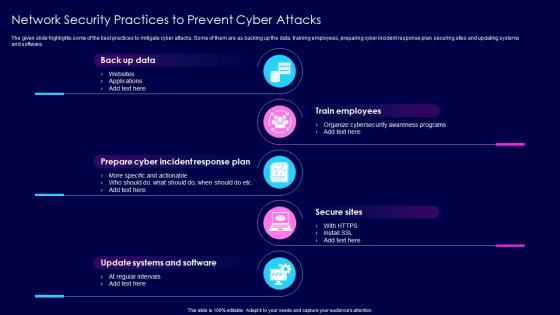 Network Security Practices To Prevent Cyber Attacks
Network Security Practices To Prevent Cyber AttacksThe given slide highlights some of the best practices to mitigate cyber attacks. Some of them are as backing up the data, training employees, preparing cyber incident response plan, securing sites and updating systems and software. Presenting our set of slides with Network Security Practices To Prevent Cyber Attacks. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Train Employees, Secure Sites.
-
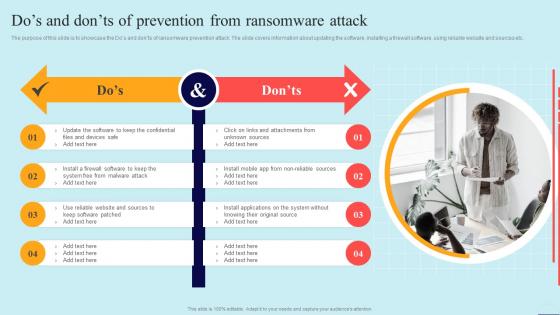 Dos And Donts Of Prevention From Ransomware Attack Preventing Data Breaches Through Cyber Security
Dos And Donts Of Prevention From Ransomware Attack Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to showcase the Dos and donts of ransomware prevention attack. The slide covers information about updating the software, installing a firewall software, using reliable website and sources etc. Introducing Dos And Donts Of Prevention From Ransomware Attack Preventing Data Breaches Through Cyber Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Online Criminals, Foreign Government Officials, Malicious Insiders, using this template. Grab it now to reap its full benefits.
-
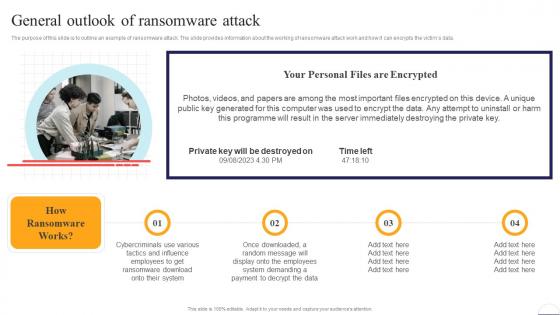 General Outlook Of Ransomware Attack Preventing Data Breaches Through Cyber Security
General Outlook Of Ransomware Attack Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to outline an example of ransomware attack. The slide provides information about the working of ransomware attack work and how it can encrypts the victims data. Introducing General Outlook Of Ransomware Attack Preventing Data Breaches Through Cyber Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on System, Data, Employees, using this template. Grab it now to reap its full benefits.
-
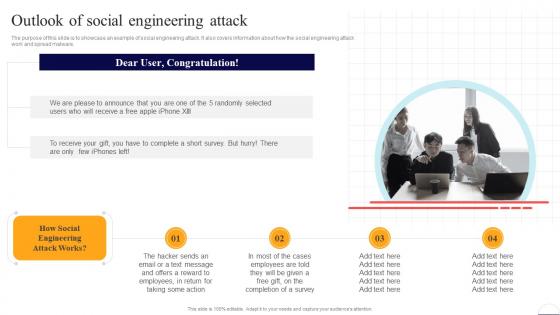 Outlook Of Social Engineering Attack Preventing Data Breaches Through Cyber Security
Outlook Of Social Engineering Attack Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to showcase an example of social engineering attack. It also covers information about how the social engineering attack work and spread malware. Introducing Outlook Of Social Engineering Attack Preventing Data Breaches Through Cyber Security to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Social Engineering, Employees, using this template. Grab it now to reap its full benefits.
-
 Overview Of Business Email Compromise Attack Preventing Data Breaches Through Cyber Security
Overview Of Business Email Compromise Attack Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to delineate an example of business email compromise attack. Information covered in this slide is related to the working of this attack and how it can result in loss of company reputation. Increase audience engagement and knowledge by dispensing information using Overview Of Business Email Compromise Attack Preventing Data Breaches Through Cyber Security. This template helps you present information on four stages. You can also present information on Email, Services, Account using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Dos And Donts Of Prevention From Ransomware Attack Developing Cyber Security Awareness Training
Dos And Donts Of Prevention From Ransomware Attack Developing Cyber Security Awareness TrainingThe purpose of this slide is to showcase the Dos and donts of ransomware prevention attack. The slide covers information about updating the software, installing a firewall software, using reliable website and sources etc. Increase audience engagement and knowledge by dispensing information using Dos And Donts Of Prevention From Ransomware Attack Developing Cyber Security Awareness Training. This template helps you present information on two stages. You can also present information on Confidential Files, Devices Safe, Firewall Software, Malware Attack using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
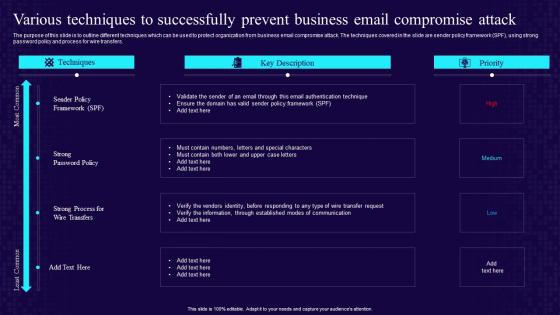 Various Techniques To Successfully Prevent Business Email Compromise Attack Developing Cyber Security Awareness
Various Techniques To Successfully Prevent Business Email Compromise Attack Developing Cyber Security AwarenessThe purpose of this slide is to outline different techniques which can be used to protect organization from business email compromise attack. The techniques covered in the slide are sender policy framework SPF, using strong password policy and process for wire transfers. Present the topic in a bit more detail with this Various Techniques To Successfully Prevent Business Email Compromise Attack Developing Cyber Security Awareness. Use it as a tool for discussion and navigation on Various Techniques, Successfully Prevent, Business Email, Compromise Attack. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
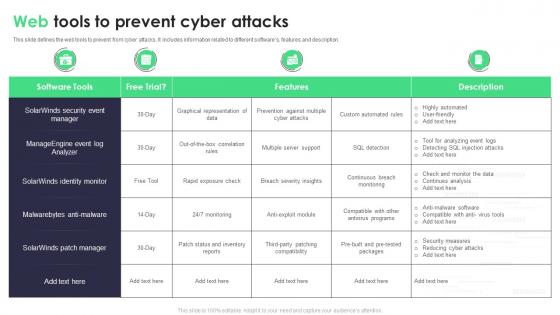 Web Tools To Prevent Cyber Attacks
Web Tools To Prevent Cyber AttacksThis slide defines the web tools to prevent from cyber attacks. It includes information related to different softwares, features and description. Introducing our Web Tools To Prevent Cyber Attacks set of slides. The topics discussed in these slides are Web Tools, Prevent, Cyber Attacks. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Dos And Donts Of Prevention From Ransomware Attack Conducting Security Awareness
Dos And Donts Of Prevention From Ransomware Attack Conducting Security AwarenessThe purpose of this slide is to showcase the dos and donts of ransomware prevention attack. The slide covers information about updating the software, installing a firewall software, using reliable website and sources etc. Increase audience engagement and knowledge by dispensing information using Dos And Donts Of Prevention From Ransomware Attack Conducting Security Awareness. This template helps you present information on one stages. You can also present information on Devices Safe, Malware Attack Patched, Keep Confidential using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Prevent Cyber Attacks In Powerpoint And Google Slides Cpb
Prevent Cyber Attacks In Powerpoint And Google Slides CpbPresenting our Prevent Cyber Attacks In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Prevent Cyber Attacks This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Cyber Security Attacks Response User Awareness Training Program To Prevent Cyber Security Incidents
Cyber Security Attacks Response User Awareness Training Program To Prevent Cyber Security IncidentsThis slide represents the training program conducted by the incident management team for end users to help them identify and mitigate the cyber security incidents before they occur. It includes details related to training topic, method, date, trainer and budget. Deliver an outstanding presentation on the topic using this Cyber Security Attacks Response User Awareness Training Program To Prevent Cyber Security Incidents. Dispense information and present a thorough explanation of User Awareness, Training Program, Prevent Cyber Security Incidents using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
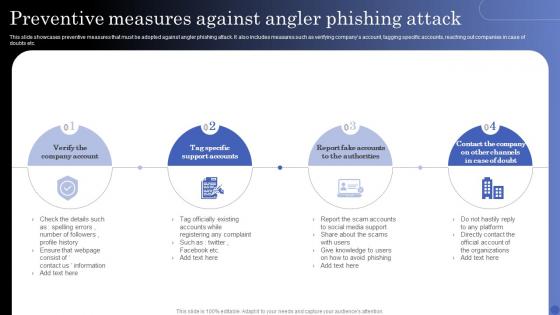 Preventive Measures Against Angler Phishing Attack
Preventive Measures Against Angler Phishing AttackThis slide showcases preventive measures that must be adopted against angler phishing attack. It also includes measures such as verifying companys account, tagging specific accounts, reaching out companies in case of doubts etc. Presenting our set of slides with Preventive Measures Against Angler Phishing Attack. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Company Account, Support Accounts, Fake Accounts.
-
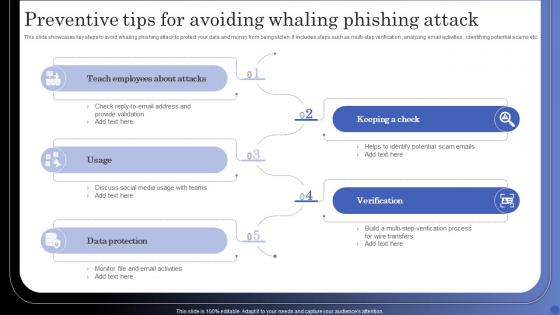 Preventive Tips For Avoiding Whaling Phishing Attack
Preventive Tips For Avoiding Whaling Phishing AttackThis slide showcases key steps to avoid whaling phishing attack to protect your data and money from being stolen. It includes steps such as multi step verification, analyzing email activities , identifying potential scams etc. Introducing our premium set of slides with Preventive Tips For Avoiding Whaling Phishing Attack. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Teach Employees, Verification, Data Protection. So download instantly and tailor it with your information.
-
 Prevent Ransomware Attacks In Powerpoint And Google Slides Cpb
Prevent Ransomware Attacks In Powerpoint And Google Slides CpbPresenting Prevent Ransomware Attacks In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Prevent Ransomware Attacks. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Preventing DDOS Attacks In Powerpoint And Google Slides Cpb
Preventing DDOS Attacks In Powerpoint And Google Slides CpbPresenting Preventing DDOS Attacks In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase six stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Preventing DDOS Attacks. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Ultimate Guide For Blockchain Techniques To Prevent Eclipse Attack And Secure Funds BCT SS
Ultimate Guide For Blockchain Techniques To Prevent Eclipse Attack And Secure Funds BCT SSThe following slide highlights major issues faced by users due to Sybil frauds to reduce fake account creations. It includes elements such as block users from network, breach of privacy, fosters 51 Percent attack, etc. Increase audience engagement and knowledge by dispensing information using Ultimate Guide For Blockchain Techniques To Prevent Eclipse Attack And Secure Funds BCT SS This template helps you present information on Three stages. You can also present information on Random Node Selection, Deterministic Node Selection using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
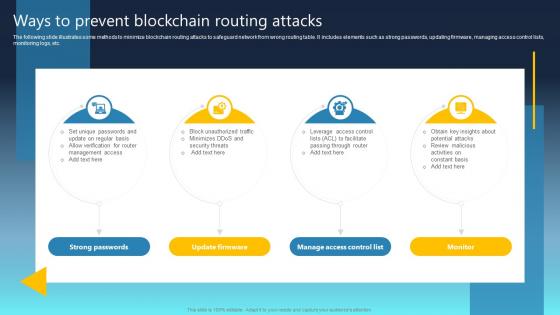 Ultimate Guide For Blockchain Ways To Prevent Blockchain Routing Attacks BCT SS
Ultimate Guide For Blockchain Ways To Prevent Blockchain Routing Attacks BCT SSThe following slide illustrates some methods to minimize blockchain routing attacks to safeguard network from wrong routing table. It includes elements such as strong passwords, updating firmware, managing access control lists, monitoring logs, etc. Increase audience engagement and knowledge by dispensing information using Ultimate Guide For Blockchain Ways To Prevent Blockchain Routing Attacks BCT SS This template helps you present information on Four stages. You can also present information on Strong Passwords, Update Firmware using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
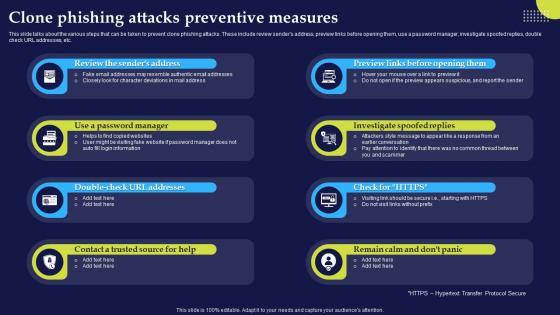 Clone Phishing Attacks Preventive Measures Phishing Attacks And Strategies
Clone Phishing Attacks Preventive Measures Phishing Attacks And StrategiesThis slide talks about the various steps that can be taken to prevent clone phishing attacks. These include review senders address, preview links before opening them, use a password manager, investigate spoofed replies, double check URL addresses, etc.Introducing Clone Phishing Attacks Preventive Measures Phishing Attacks And Strategies to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Investigate Spoofed, Password Manager, Contact Trusted, using this template. Grab it now to reap its full benefits.
-
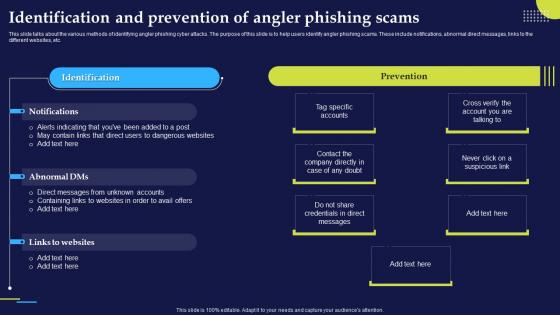 Identification And Prevention Of Angler Phishing Attacks And Strategies
Identification And Prevention Of Angler Phishing Attacks And StrategiesThis slide talks about the various methods of identifying angler phishing cyber attacks. The purpose of this slide is to help users identify angler phishing scams. These include notifications, abnormal direct messages, links to the different websites, etc.Present the topic in a bit more detail with this Identification And Prevention Of Angler Phishing Attacks And Strategies. Use it as a tool for discussion and navigation on Credentials Direct, Direct Messages, Unknown Accounts. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Identification And Prevention Of Spear Phishing Attacks And Strategies
Identification And Prevention Of Spear Phishing Attacks And StrategiesThis slide talks about the various methods of identifying spear phishing cyber attacks. The purpose of this slide is to help users prevent spear phishing scams. The key signs include unusual request, shared drive links and documents with password protection.Introducing Identification And Prevention Of Spear Phishing Attacks And Strategies to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispence information on Password Protection, Unusual Request, Appears Strange, using this template. Grab it now to reap its full benefits.
-
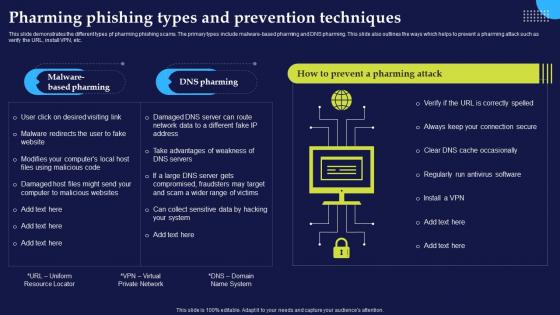 Pharming Phishing Types And Prevention Phishing Attacks And Strategies
Pharming Phishing Types And Prevention Phishing Attacks And StrategiesThis slide demonstrates the different types pf pharming phishing scams. The primary types include malware based pharming and DNS pharming. This slide also outlines the ways which helps to prevent a pharming attack such as verify the URL, install VPN, etc.Introducing Pharming Phishing Types And Prevention Phishing Attacks And Strategies to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Regularly Run, Antivirus Software, Malware Redirects, using this template. Grab it now to reap its full benefits.
-
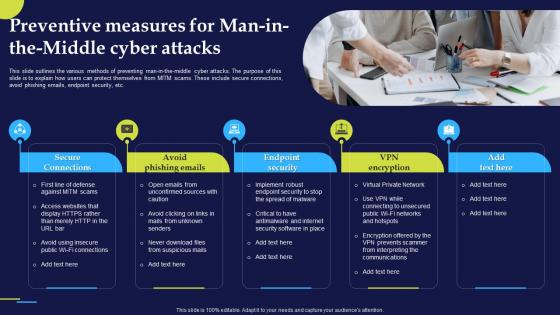 Preventive Measures For Man In The Middle Phishing Attacks And Strategies
Preventive Measures For Man In The Middle Phishing Attacks And StrategiesThis slide outlines the various methods of preventing man in the middle cyber attacks. The purpose of this slide is to explain how users can protect themselves from MITM scams. These include secure connections, avoid phishing emails, endpoint security, etc.Introducing Preventive Measures For Man In The Middle Phishing Attacks And Strategies to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Secure Connections, Avoid Phishing Emails, Endpoint Security, using this template. Grab it now to reap its full benefits.
-
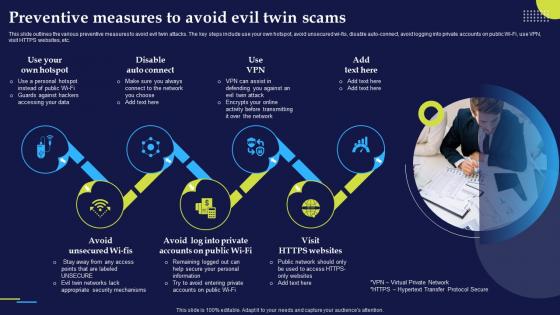 Preventive Measures To Avoid Evil Twin Scams Phishing Attacks And Strategies
Preventive Measures To Avoid Evil Twin Scams Phishing Attacks And StrategiesThis slide outlines the various preventive measures to avoid evil twin attacks. The key steps include use your own hotspot, avoid unsecured wi fis, disable auto connect, avoid logging into private accounts on public Wi Fi, use VPN, visit HTTPS websites, etc.Increase audience engagement and knowledge by dispensing information using Preventive Measures To Avoid Evil Twin Scams Phishing Attacks And Strategies. This template helps you present information on seven stages. You can also present information on Appropriate Security Mechanisms, Transfer Protocol Secure, Accessing Data using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
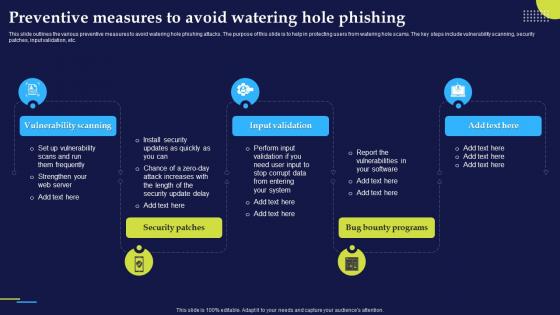 Preventive Measures To Avoid Watering Hole Phishing Attacks And Strategies
Preventive Measures To Avoid Watering Hole Phishing Attacks And StrategiesThis slide outlines the various preventive measures to avoid watering hole phishing attacks. The purpose of this slide is to help in protecting users from watering hole scams. The key steps include vulnerability scanning, security patches, input validation, etc.Introducing Preventive Measures To Avoid Watering Hole Phishing Attacks And Strategies to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Vulnerability Scanning, Input Validation, Security Patches, using this template. Grab it now to reap its full benefits.
-
 Tools Provided By Google To Prevent Phishing Attacks And Strategies
Tools Provided By Google To Prevent Phishing Attacks And StrategiesThis slide demonstrates the different tools provided by Google to prevent and report cyber phishing scams. These include to spot phishing mails with the help of Gmail, utilize safe browsing in chrome, look for unsafe saved passwords, password alert for chrome, etc.Deliver an outstanding presentation on the topic using this Tools Provided By Google To Prevent Phishing Attacks And Strategies. Dispense information and present a thorough explanation of Saved Passwords, Notifications Concerning, Ever Compromised using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Vishing Attacks Prevention Email Signing phishing Attacks And Strategies
Vishing Attacks Prevention Email Signing phishing Attacks And StrategiesThis slide talks about the techniques which can help in protecting organizations from phishing and vishing attacks. The purpose of this slide is to explain two important methods of preventing cyber scams. These techniques are email signing and code signing.Deliver an outstanding presentation on the topic using this Vishing Attacks Prevention Email Signing phishing Attacks And Strategies. Dispense information and present a thorough explanation of Malicious Software, Code Signing, Code Signing using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
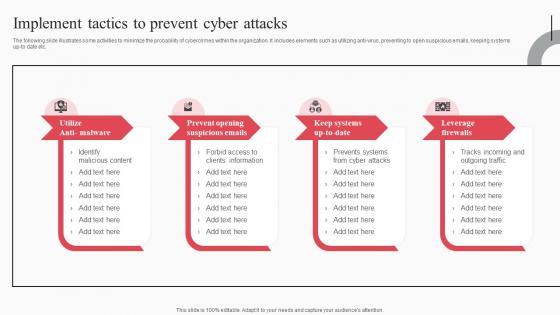 Implement Tactics To Prevent Cyber Attacks Cyber Attack Risks Mitigation
Implement Tactics To Prevent Cyber Attacks Cyber Attack Risks MitigationThe following slide illustrates some activities to minimize the probability of cybercrimes within the organization. It includes elements such as utilizing anti virus, preventing to open suspicious emails, keeping systems up to date etc. Introducing Implement Tactics To Prevent Cyber Attacks Cyber Attack Risks Mitigation to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Prevent Opening Suspicious Emails, Keep Systems Up To Date, Leverage Firewalls, using this template. Grab it now to reap its full benefits.
-
 Malware Attack Icon To Prevent Threat
Malware Attack Icon To Prevent ThreatPresenting our well structured Malware Attack Icon To Prevent Threat. The topics discussed in this slide are Malware Attack Icon, Prevent Threat. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Malware Device Icon To Prevent Form Malicious Attacks
Malware Device Icon To Prevent Form Malicious AttacksPresenting our well structured Malware Device Icon To Prevent Form Malicious Attacks. The topics discussed in this slide are Malware Device Icon, Prevent Form Malicious Attacks. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
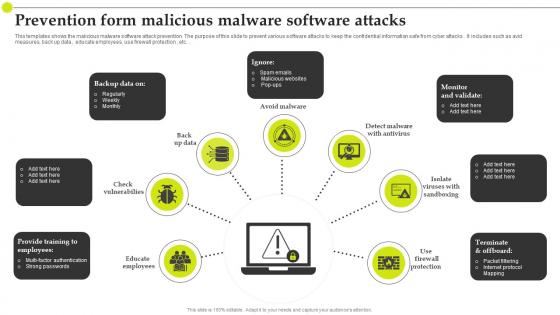 Prevention Form Malicious Malware Software Attacks
Prevention Form Malicious Malware Software AttacksThis templates shows the malicious malware software attack prevention. The purpose of this slide to prevent various software attacks to keep the confidential information safe from cyber attacks . It includes such as avid measures, back up data , educate employees, use firewall protection , etc.Introducing our premium set of slides with Prevention Form Malicious Malware Software Attacks. Ellicudate the seven stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Packet Filtering, Internet Protocol, Educate Employees. So download instantly and tailor it with your information.
-
 Email Based Phishing Attacks Prevention IT Illustration
Email Based Phishing Attacks Prevention IT IllustrationThis colored PowerPoint Illustration provides a comprehensive overview of email-based phishing attacks and how to prevent them. It covers topics such as identifying suspicious emails, understanding phishing tactics, and implementing security measures.
-
 Different ways to prevent social engineering attacks
Different ways to prevent social engineering attacksPresenting this set of slides with name Different Ways To Prevent Social Engineering Attacks. This is a four process. The stages in this process are stages Social Engineering, Technology, Social, Network. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
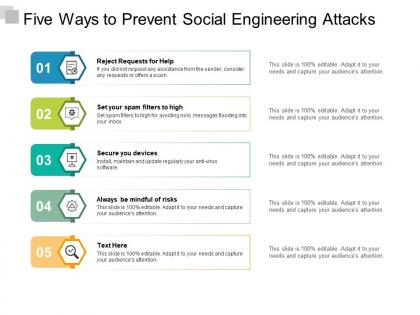 Five ways to prevent social engineering attacks
Five ways to prevent social engineering attacksPresenting this set of slides with name Five Ways To Prevent Social Engineering Attacks. This is a five process. The stages in this process are stages Social Engineering, Technology, Social, Network. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.