Powerpoint Templates and Google slides for Comparison Security
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
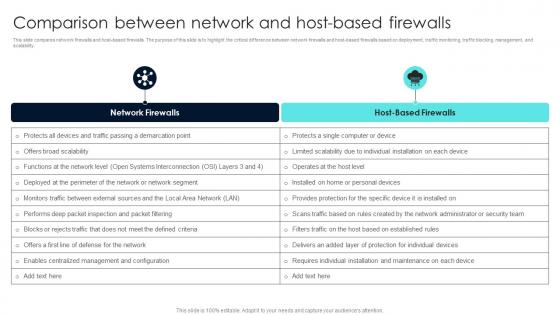 Firewall Network Security Comparison Between Network And Host Based Firewalls
Firewall Network Security Comparison Between Network And Host Based FirewallsThis slide compares network firewalls and host-based firewalls. The purpose of this slide is to highlight the critical difference between network firewalls and host-based firewalls based on deployment, traffic monitoring, traffic blocking, management, and scalability. Deliver an outstanding presentation on the topic using this Firewall Network Security Comparison Between Network And Host Based Firewalls Dispense information and present a thorough explanation of Network Firewalls, Host-Based Firewalls using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
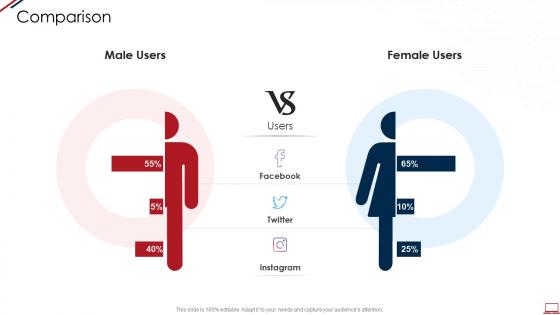 Computer system security comparison ppt powerpoint presentation slides visuals
Computer system security comparison ppt powerpoint presentation slides visualsIntroducing Computer System Security Comparison Ppt Powerpoint Presentation Slides Visuals to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Male Users, Female Users, using this template. Grab it now to reap its full benefits.
-
 Secured Loan Comparison In Powerpoint And Google Slides Cpb
Secured Loan Comparison In Powerpoint And Google Slides CpbPresenting our Secured Loan Comparison In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases Four stages. It is useful to share insightful information on Secured Loan Comparison This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
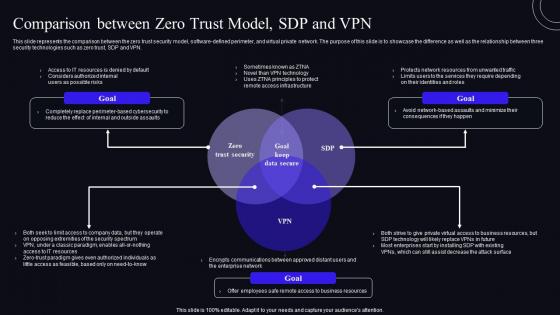 Comparison Between Zero Trust Model SDP And VPN Zero Trust Security Model
Comparison Between Zero Trust Model SDP And VPN Zero Trust Security ModelThis slide represents the comparison between the zero trust security model, software-defined perimeter, and virtual private network. The purpose of this slide is to showcase the difference as well as the relationship between three security technologies such as zero trust, SDP and VPN. Present the topic in a bit more detail with this Comparison Between Zero Trust Model SDP And VPN Zero Trust Security Model. Use it as a tool for discussion and navigation on Comparison, Business, Resources. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
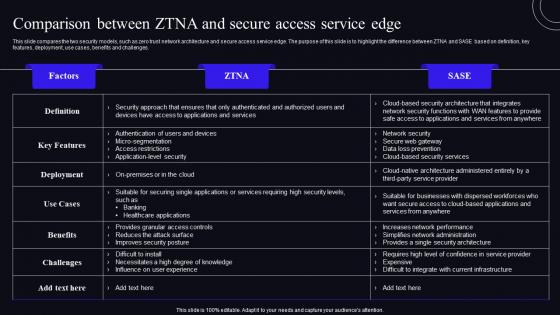 Comparison Between ZTNA And Secure Access Service Edge Zero Trust Security Model
Comparison Between ZTNA And Secure Access Service Edge Zero Trust Security ModelThis slide compares the two security models, such as zero trust network architecture and secure access service edge. The purpose of this slide is to highlight the difference between ZTNA and SASE based on definition, key features, deployment, use cases, benefits and challenges. Deliver an outstanding presentation on the topic using this Comparison Between ZTNA And Secure Access Service Edge Zero Trust Security Model. Dispense information and present a thorough explanation of Comparison, Architecture, Service using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
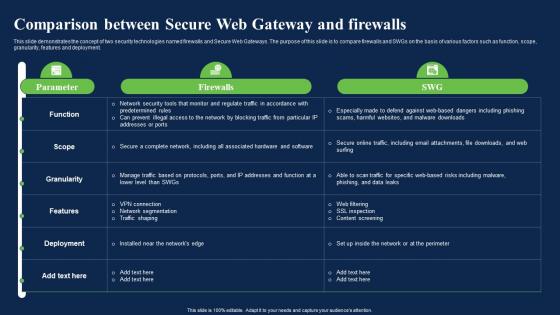 Comparison Between Secure Web Gateway And Firewalls Network Security Using Secure Web Gateway
Comparison Between Secure Web Gateway And Firewalls Network Security Using Secure Web GatewayThis slide demonstrates the concept of two security technologies named firewalls and Secure Web Gateways. The purpose of this slide is to compare firewalls and SWGs on the basis of various factors such as function, scope, granularity, features and deployment. Present the topic in a bit more detail with this Comparison Between Secure Web Gateway And Firewalls Network Security Using Secure Web Gateway. Use it as a tool for discussion and navigation on Comparison, Deployment, Technologies. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Comparison Secure Web Gateway And Cloud Network Security Using Secure Web Gateway
Comparison Secure Web Gateway And Cloud Network Security Using Secure Web GatewayThis slide demonstrates the concept of cloud security gateways and Secure Web Gateways. The purpose of this slide is to compare cloud security gateways and SWGs on the basis of various factors such as scope, deployment, architecture, features and cost. Deliver an outstanding presentation on the topic using this Comparison Secure Web Gateway And Cloud Network Security Using Secure Web Gateway. Dispense information and present a thorough explanation of Deployment, Architecture, Comparison using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
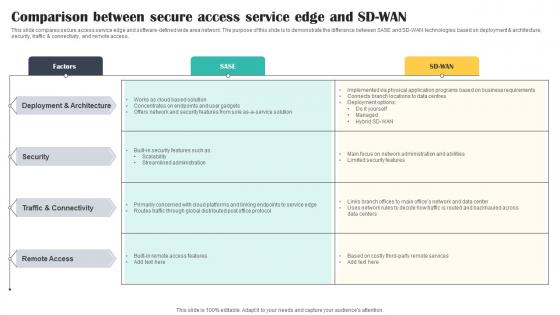 Comparison Between Secure Access Service Edge And SD WAN Cloud Security Model
Comparison Between Secure Access Service Edge And SD WAN Cloud Security ModelThis slide compares secure access service edge and software defined wide area network. The purpose of this slide is to demonstrate the difference between SASE and SD WAN technologies based on deployment and architecture, security, traffic and connectivity, and remote access. Present the topic in a bit more detail with this Comparison Between Secure Access Service Edge And SD WAN Cloud Security Model. Use it as a tool for discussion and navigation on Deployment, Architecture, Security. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
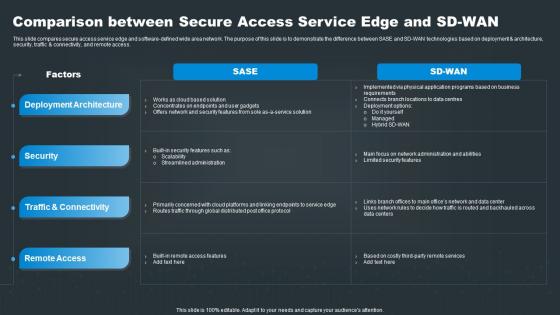 SASE Network Security Comparison Between Secure Access Service Edge And SD WAN
SASE Network Security Comparison Between Secure Access Service Edge And SD WANThis slide compares secure access service edge and software defined wide area network. The purpose of this slide is to demonstrate the difference between SASE and SD WAN technologies based on deployment and architecture, security, traffic and connectivity, and remote access. Present the topic in a bit more detail with this SASE Network Security Comparison Between Secure Access Service Edge And SD WAN. Use it as a tool for discussion and navigation on Deployment, Security, Connectivity. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
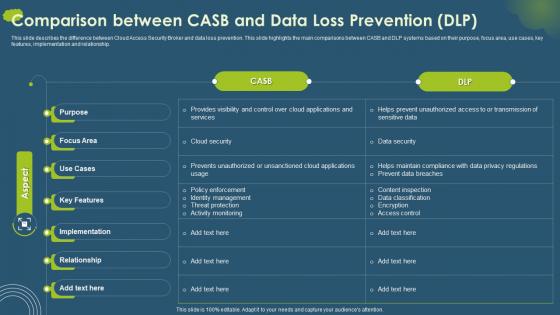 Cloud Access Security Broker CASB V2 Comparison Between CASB And Data Loss Prevention DLP
Cloud Access Security Broker CASB V2 Comparison Between CASB And Data Loss Prevention DLPThis slide describes the difference between Cloud Access Security Broker and data loss prevention. This slide highlights the main comparisons between CASB and DLP systems based on their purpose, focus area, use cases, key features, implementation and relationship. Deliver an outstanding presentation on the topic using this Cloud Access Security Broker CASB V2 Comparison Between CASB And Data Loss Prevention DLP. Dispense information and present a thorough explanation of Content Inspection, Data Classification, Encryption, Access Control using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
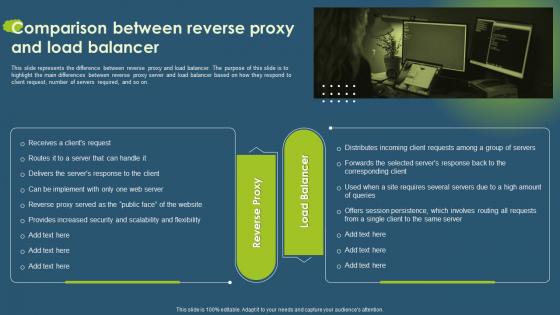 Cloud Access Security Broker CASB V2 Comparison Between Reverse Proxy And Load Balancer
Cloud Access Security Broker CASB V2 Comparison Between Reverse Proxy And Load BalancerThis slide represents the difference between reverse proxy and load balancer. The purpose of this slide is to highlight the main differences between reverse proxy server and load balancer based on how they respond to client request, number of servers required, and so on. Increase audience engagement and knowledge by dispensing information using Cloud Access Security Broker CASB V2 Comparison Between Reverse Proxy And Load Balancer. This template helps you present information on one stages. You can also present information on Reverse Proxy And Load Balancer, Reverse Proxy, Site Requires Several Servers, Scalability And Flexibility using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
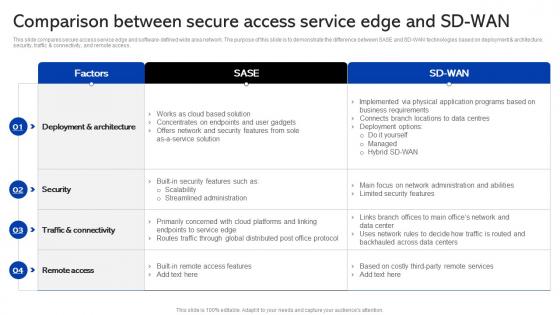 Sase Security Comparison Between Secure Access Service Edge And Sd Wan
Sase Security Comparison Between Secure Access Service Edge And Sd WanThis slide compares secure access service edge and software-defined wide area network. The purpose of this slide is to demonstrate the difference between SASE and SD-WAN technologies based on deployment and architecture, security, traffic and connectivity, and remote access. Present the topic in a bit more detail with this Sase Security Comparison Between Secure Access Service Edge And Sd Wan. Use it as a tool for discussion and navigation on Service, Comparison, Demonstrate. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
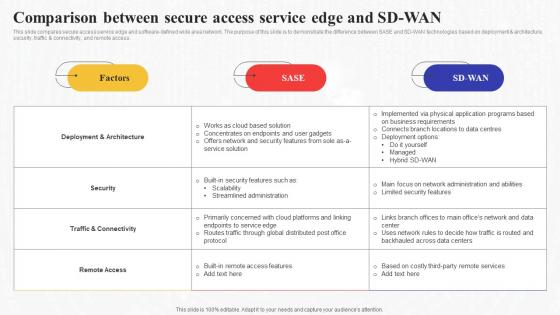 Comparison Between Secure Access Service Edge And Sd Wan Secure Access Service Edge Sase
Comparison Between Secure Access Service Edge And Sd Wan Secure Access Service Edge SaseThis slide compares secure access service edge and software-defined wide area network. The purpose of this slide is to demonstrate the difference between SASE and SD-WAN technologies based on deployment and architecture, security, traffic and connectivity, and remote access. Deliver an outstanding presentation on the topic using this Comparison Between Secure Access Service Edge And Sd Wan Secure Access Service Edge Sase. Dispense information and present a thorough explanation of Comparison, Service, Architecture using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
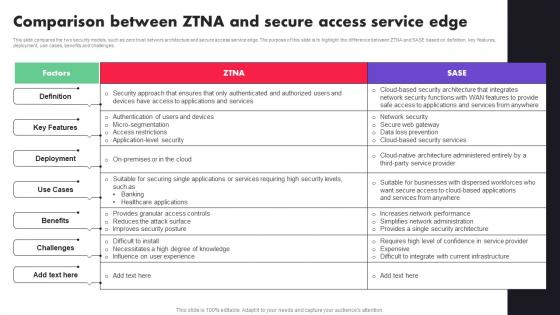 Comparison Between ZTNA And Secure Access Service Edge Ppt File Diagrams
Comparison Between ZTNA And Secure Access Service Edge Ppt File DiagramsThis slide compares the two security models, such as zero trust network architecture and secure access service edge. The purpose of this slide is to highlight the difference between ZTNA and SASE based on definition, key features, deployment, use cases, benefits and challenges. Present the topic in a bit more detail with this Comparison Between ZTNA And Secure Access Service Edge Ppt File Diagrams. Use it as a tool for discussion and navigation on Key Features, Deployment, Benefits. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
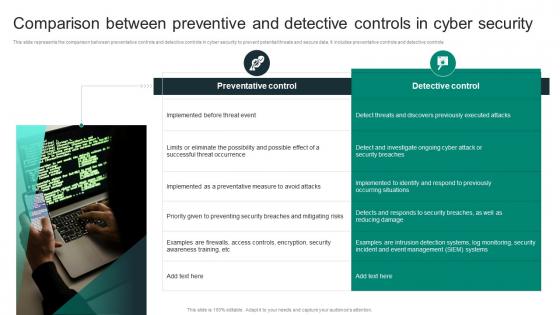 Comparison Between Preventive And Detective Controls In Cyber Security
Comparison Between Preventive And Detective Controls In Cyber SecurityThis slide represents the comparison between preventative controls and detective controls in cyber security to prevent potential threats and secure data. It includes preventative controls and detective controls Presenting our set of slides with Comparison Between Preventive And Detective Controls In Cyber Security This exhibits information on two stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Preventative Control, Detective Control
-
 Devsecops Best Practices For Secure Comparison Between Devops And Devsecops Models
Devsecops Best Practices For Secure Comparison Between Devops And Devsecops ModelsThis slide showcases the comparison between DevOps and DevSecOps models. The purpose of this slide is to highlight the key differences in terms of definition, objective, benefits, attack surface, tool and methods, collaboration and continuous improvement. Deliver an outstanding presentation on the topic using this Devsecops Best Practices For Secure Comparison Between Devops And Devsecops Models. Dispense information and present a thorough explanation of Benefits, Attack Surface, Tool And Methods, Collaboration And Continuous Improvement using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Secure Messaging Apps Comparison In Powerpoint And Google Slides Cpb
Secure Messaging Apps Comparison In Powerpoint And Google Slides CpbPresenting our Secure Messaging Apps Comparison In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases six stages. It is useful to share insightful information on Secure Messaging Apps Comparison This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Sase Model Comparison Between Secure Access Service Edge And Sd Wan
Sase Model Comparison Between Secure Access Service Edge And Sd WanThis slide compares secure access service edge and software-defined wide area network. The purpose of this slide is to demonstrate the difference between SASE and SD-WAN technologies based on deployment and architecture, security, traffic and connectivity, and remote access. Deliver an outstanding presentation on the topic using this Sase Model Comparison Between Secure Access Service Edge And Sd Wan. Dispense information and present a thorough explanation of Factors, Sd Wan, Sase using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
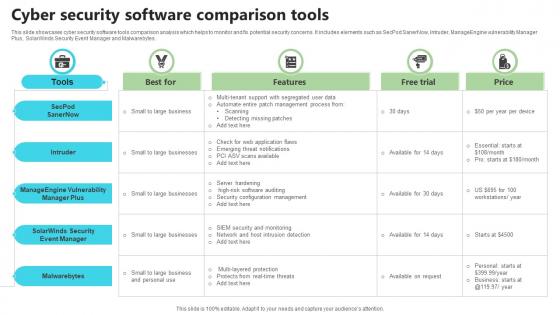 Cyber Security Software Comparison Tools
Cyber Security Software Comparison ToolsThis slide showcases cyber security software tools comparison analysis which helps to monitor and fix potential security concerns. It includes elements such as SecPod SanerNow, Intruder, ManageEngine vulnerability Manager Plus, SolarWinds Security Event Manager and Malwarebytes. Presenting our well structured Cyber Security Software Comparison Tools. The topics discussed in this slide are Best For Features, Free Trial. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
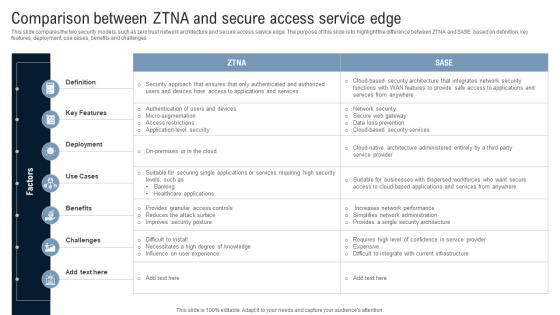 Comparison Between ZTNA And Secure Access Service Edge Identity Defined Networking
Comparison Between ZTNA And Secure Access Service Edge Identity Defined NetworkingThis slide compares the two security models, such as zero trust network architecture and secure access service edge. The purpose of this slide is to highlight the difference between ZTNA and SASE based on definition, key features, deployment, use cases, benefits and challenges. Present the topic in a bit more detail with this Comparison Between ZTNA And Secure Access Service Edge Identity Defined Networking Use it as a tool for discussion and navigation on Key Features, Deployment, Benefits, Challenges This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 IoT Device Management Platforms Comparison IoT Security And Privacy Safeguarding IoT SS
IoT Device Management Platforms Comparison IoT Security And Privacy Safeguarding IoT SSThis slide displays the most popular IoT device management platforms that help to automate connected device monitoring. It includes platforms such as Bytebeam, Cico IoT, Azure IoT Hub, and AWS IoT Core. Deliver an outstanding presentation on the topic using this IoT Device Management Platforms Comparison IoT Security And Privacy Safeguarding IoT SS. Dispense information and present a thorough explanation of Cloud Integration, Device Connectivity, Pricing Flexibility using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
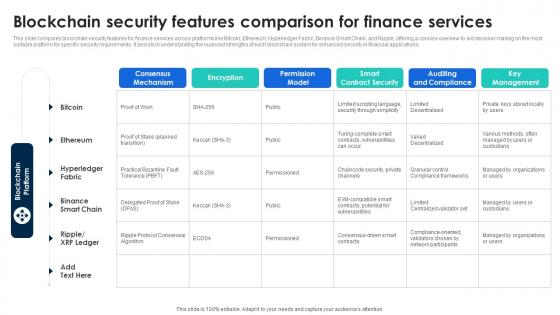 Blockchain Security Features Comparison For Finance Services
Blockchain Security Features Comparison For Finance ServicesThis slide compares blockchain security features for finance services across platforms like Bitcoin, Ethereum, Hyperledger Fabric, Binance Smart Chain, and Ripple, offering a concise overview to aid decision making on the most suitable platform for specific security requirements. It assists in understanding the nuanced strengths of each blockchain system for enhanced security in financial applications. Introducing our Blockchain Security Features Comparison For Finance Services set of slides. The topics discussed in these slides are Encryption, Permission, Security. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
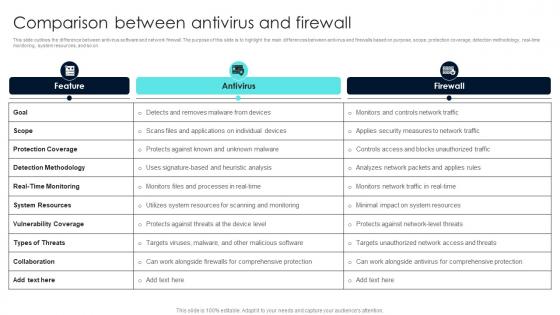 Firewall Network Security Comparison Between Antivirus And Firewall
Firewall Network Security Comparison Between Antivirus And FirewallThis slide outlines the difference between antivirus software and network firewall. The purpose of this slide is to highlight the main differences between antivirus and firewalls based on purpose, scope, protection coverage, detection methodology, real-time monitoring, system resources, and so on. Present the topic in a bit more detail with this Firewall Network Security Comparison Between Antivirus And Firewall Use it as a tool for discussion and navigation on Antivirus, Firewall This template is free to edit as deemed fit for your organization. Therefore download it now.
-
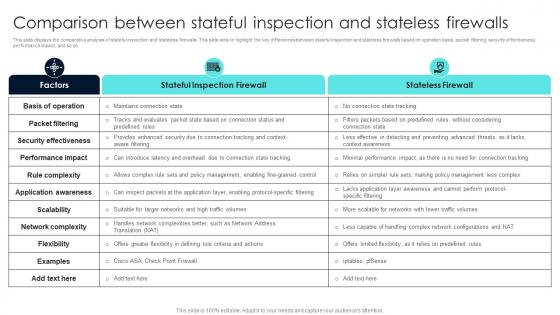 Firewall Network Security Comparison Between Stateful Inspection And Stateless Firewalls
Firewall Network Security Comparison Between Stateful Inspection And Stateless FirewallsThis slide displays the comparative analysis of stateful inspection and stateless firewalls. This slide aims to highlight the key differences between stateful inspection and stateless firewalls based on operation basis, packet filtering, security effectiveness, performance impact, and so on. Present the topic in a bit more detail with this Firewall Network Security Comparison Between Stateful Inspection And Stateless Firewalls Use it as a tool for discussion and navigation on Stateful Inspection Firewall, Stateless Firewall This template is free to edit as deemed fit for your organization. Therefore download it now.
-
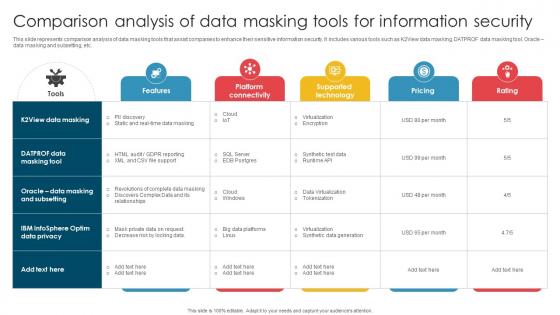 Comparison Analysis Of Data Masking Tools For Information Security
Comparison Analysis Of Data Masking Tools For Information SecurityThis slide represents comparison analysis of data masking tools that assist companies to enhance their sensitive information security. It includes various tools such as K2View data masking, DATPROF data masking tool, Oracle data masking and subsetting, etc. Presenting our well structured Comparison Analysis Of Data Masking Tools For Information Security. The topics discussed in this slide are Virtualization, Synthetic Data Generation, Tokenization. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
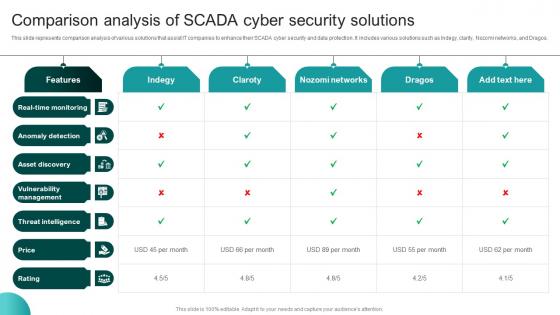 Comparison Analysis Of SCADA Cyber Security Solutions
Comparison Analysis Of SCADA Cyber Security SolutionsThis slide represents comparison analysis of various solutions that assist IT companies to enhance their SCADA cyber security and data protection. It includes various solutions such as Indegy, clarity, Nozomi networks, and Dragos. Presenting our well structured Comparison Analysis Of SCADA Cyber Security Solutions The topics discussed in this slide are Anomaly Detection, Asset Discovery, Vulnerability Management. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Comparison Of Mobile Security Solution Capabilities
Comparison Of Mobile Security Solution CapabilitiesThis slide highlights mobile security solutions comparative assessment and includes core expertise, mobile threat detection and response. Presenting our set of slides with name Comparison Of Mobile Security Solution Capabilities. This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Unified Device Management, Threat Detection And Response, Mobile Security Solutions.
-
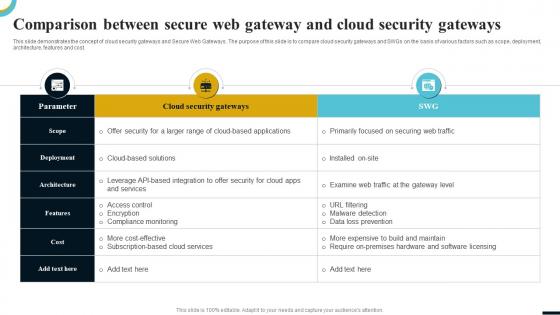 Comparison Between Secure Web Internet Gateway Security IT
Comparison Between Secure Web Internet Gateway Security ITThis slide demonstrates the concept of cloud security gateways and Secure Web Gateways. The purpose of this slide is to compare cloud security gateways and SWGs on the basis of various factors such as scope, deployment, architecture, features and cost. Present the topic in a bit more detail with this Comparison Between Secure Web Internet Gateway Security IT. Use it as a tool for discussion and navigation on Parameter, Scope, Deployment, Architecture, Features, Cost. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
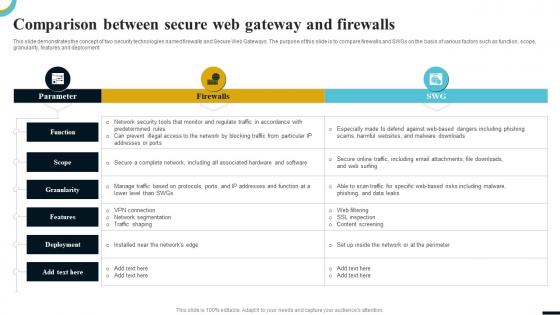 Internet Gateway Security IT Comparison Between Secure Web Gateway
Internet Gateway Security IT Comparison Between Secure Web GatewayThis slide demonstrates the concept of two security technologies named firewalls and Secure Web Gateways. The purpose of this slide is to compare firewalls and SWGs on the basis of various factors such as function, scope, granularity, features and deployment. Present the topic in a bit more detail with this Internet Gateway Security IT Comparison Between Secure Web Gateway. Use it as a tool for discussion and navigation on Function, Scope, Granularity, Features, Deployment. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
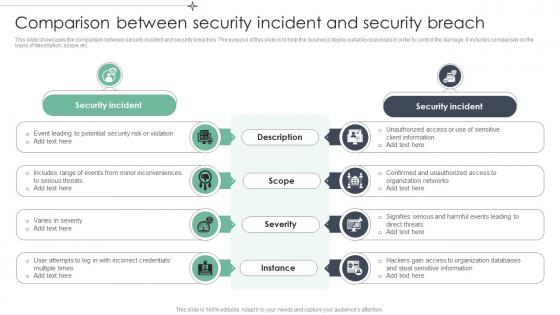 Comparison Between Security Incident And Security Breach
Comparison Between Security Incident And Security BreachThis slide showcases the comparison between security incident and security breaches. The purpose of this slide is to help the business deploy suitable responses in order to control the damage. It includes comparison on the basis of description, scope, etc. Introducing our premium set of slides with Comparison Between Security Incident And Security Breach. Ellicudate the eight stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Security Risk, Minor Inconveniences, Organization Networks. So download instantly and tailor it with your information.
-
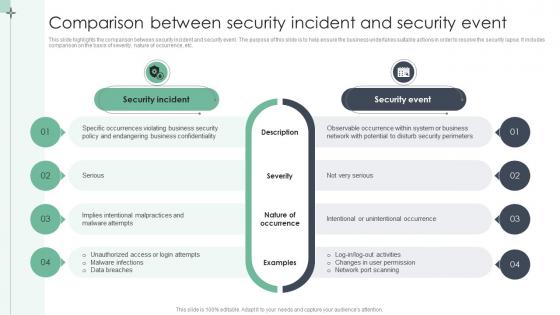 Comparison Between Security Incident And Security Event
Comparison Between Security Incident And Security EventThis slide highlights the comparison between security incident and security event. The purpose of this slide is to help ensure the business undertakes suitable actions in order to resolve the security lapse. It includes comparison on the basis of severity, nature of occurrence, etc. Presenting our set of slides with Comparison Between Security Incident And Security Event. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Business Confidentiality, Malware Attempts, Unintentional Occurrence.
-
 Comparison Between CASB And Data Loss Prevention DLP CASB Cloud Security
Comparison Between CASB And Data Loss Prevention DLP CASB Cloud SecurityThis slide describes the difference between cloud access security broker and data loss prevention. This slide highlights the main comparisons between CASB and DLP systems based on their purpose, focus area, use cases, key features, implementation and relationship. Present the topic in a bit more detail with this Comparison Between CASB And Data Loss Prevention DLP CASB Cloud Security. Use it as a tool for discussion and navigation on Cloud Access Security Broker, Data Loss Prevention, Focus Area, Implementation And Relationship. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Comparison Between Reverse Proxy And Load Balancer CASB Cloud Security
Comparison Between Reverse Proxy And Load Balancer CASB Cloud SecurityThis slide represents the difference between reverse proxy and load balancer. The purpose of this slide is to highlight the main differences between reverse proxy server and load balancer based on how they respond to client request, number of servers required, and so on. Introducing Comparison Between Reverse Proxy And Load Balancer CASB Cloud Security to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Reverse Proxy And Load Balancer, Reverse Proxy Server, Site Requires Several Servers, using this template. Grab it now to reap its full benefits.
-
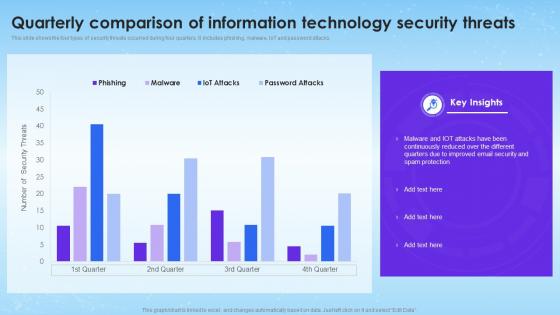 Quarterly Comparison Of Information Technology Security Threats
Quarterly Comparison Of Information Technology Security ThreatsThis slide shows the four types of security threats occurred during four quarters. It includes phishing, malware, IoT and password attacks. Introducing our Quarterly Comparison Of Information Technology Security Threats set of slides. The topics discussed in these slides are Quarterly Comparison, Information Technology, Security Threats. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
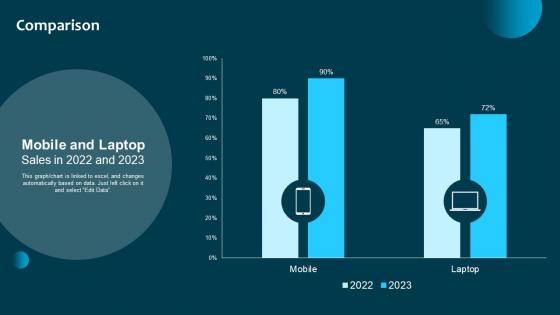 Comparison Information System Security And Risk Administration Plan Ppt Styles Show
Comparison Information System Security And Risk Administration Plan Ppt Styles ShowThis graph chart is linked to excel, and changes automatically based on data. Just left click on it and select Edit Data. Present the topic in a bit more detail with this Comparison Information System Security And Risk Administration Plan Ppt Styles Show. Use it as a tool for discussion and navigation on Mobile, Laptop, Sales. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
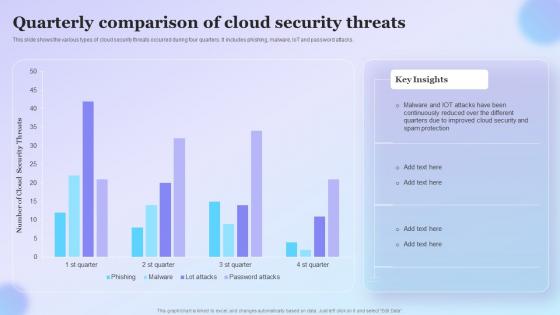 Quarterly Comparison Of Cloud Security Threats
Quarterly Comparison Of Cloud Security ThreatsThis slide shows the various types of cloud security threats occurred during four quarters. It includes phishing, malware, IoT and password attacks. Presenting our well structured Quarterly Comparison Of Cloud Security Threats. The topics discussed in this slide are Quarterly, Comparison Of Cloud Security, Threats. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
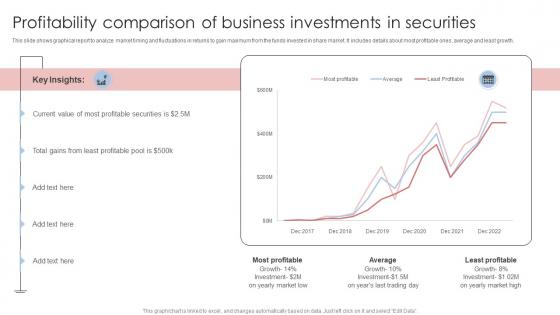 Profitability Comparison Of Business Investments In Securities
Profitability Comparison Of Business Investments In SecuritiesThis slide shows graphical report to analyze market timing and fluctuations in returns to gain maximum from the funds invested in share market. It includes details about most profitable ones, average and least growth. Presenting our well-structured Profitability Comparison Of Business Investments In Securities. The topics discussed in this slide are Profitability Comparison, Business Investments, Securities. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
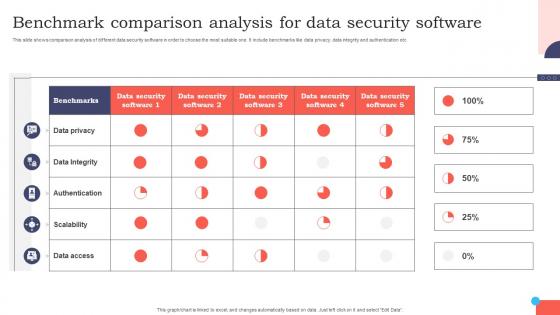 Benchmark Comparison Analysis For Data Security Software
Benchmark Comparison Analysis For Data Security SoftwareThis slide shows comparison analysis of different data security software in order to choose the most suitable one. It include benchmarks like data privacy, data integrity and authentication etc. Introducing our Benchmark Comparison Analysis For Data Security Software set of slides. The topics discussed in these slides are Research And Development, Marketing, Human Resources. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
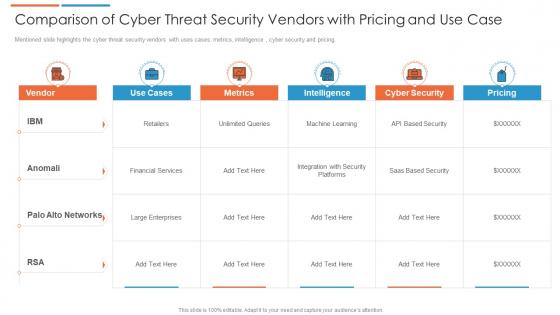 Comparison of cyber threat security vendors with pricing and use case
Comparison of cyber threat security vendors with pricing and use caseMentioned slide highlights the cyber threat security vendors with uses cases, metrics, intelligence , cyber security and pricing. Presenting our well structured Comparison Of Cyber Threat Security Vendors With Pricing And Use Case. The topics discussed in this slide are Financial Services, Cyber Security, Intelligence. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
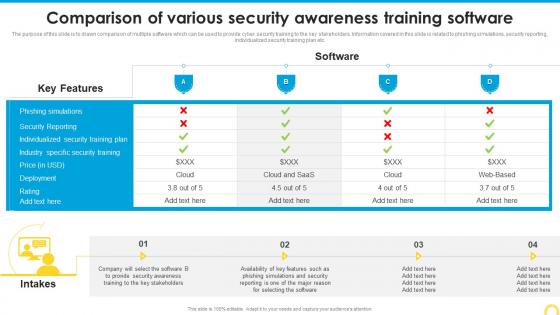 Comparison Of Various Security Building A Security Awareness Program
Comparison Of Various Security Building A Security Awareness ProgramThe purpose of this slide is to drawn comparison of multiple software which can be used to provide cyber security training to the key stakeholders. Information covered in this slide is related to phishing simulations, security reporting, individualized security training plan etc. Deliver an outstanding presentation on the topic using this Comparison Of Various Security Building A Security Awareness Program. Dispense information and present a thorough explanation of Software, Comparison, Various Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
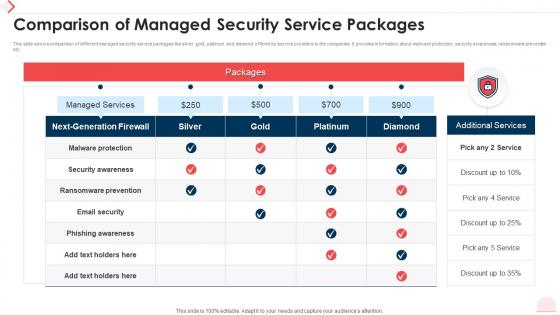 Comparison Of Managed Security Service Packages
Comparison Of Managed Security Service PackagesThis slide shows comparison of different managed security service packages like silver, gold, platinum and diamond offered by service providers to the companies. It provides information about malware protection, security awareness, ransomware prevention etc. Introducing our Comparison Of Managed Security Service Packages set of slides. The topics discussed in these slides are Managed Services, Next Generation Firewall, Security Awareness. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Security system cost comparison ppt powerpoint presentation styles example topics cpb
Security system cost comparison ppt powerpoint presentation styles example topics cpbPresenting Security System Cost Comparison Ppt Powerpoint Presentation Styles Example Topics Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Security System Cost Comparison. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Comparison Of Various Security Awareness Training Implementing Security Awareness Training
Comparison Of Various Security Awareness Training Implementing Security Awareness TrainingThe purpose of this slide is to drawn comparison of multiple software which can be used to provide cyber security training to the key stakeholders. Information covered in this slide is related to phishing simulations, security reporting, individualized security training plan etc. Deliver an outstanding presentation on the topic using this Comparison Of Various Security Awareness Training Implementing Security Awareness Training. Dispense information and present a thorough explanation of Phishing Simulations, Security Reporting, Deployment using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
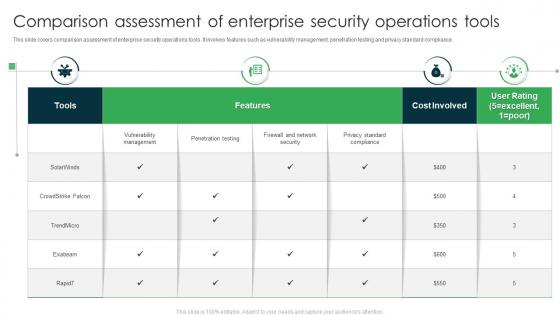 Comparison Assessment Of Enterprise Security Operations Tools
Comparison Assessment Of Enterprise Security Operations ToolsThis slide covers comparison assessment of enterprise security operations tools. It involves features such as vulnerability management, penetration testing and privacy standard compliance. Introducing our Comparison Assessment Of Enterprise Security Operations Tools set of slides. The topics discussed in these slides are Features, Cost Involved, User Rating. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Comparison Of Various Security Awareness Training Software Preventing Data Breaches Through Cyber Security
Comparison Of Various Security Awareness Training Software Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to drawn comparison of multiple software which can be used to provide cyber security training to the key stakeholders. Information covered in this slide is related to phishing simulations, security reporting, individualized security training plan etc. Deliver an outstanding presentation on the topic using this Comparison Of Various Security Awareness Training Software Preventing Data Breaches Through Cyber Security. Dispense information and present a thorough explanation of Security Reporting, Phishing Simulations, Deployment using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Comparison Security Incident Response Playbook Ppt Slides Background Designs
Comparison Security Incident Response Playbook Ppt Slides Background DesignsIntroducing Comparison Security Incident Response Playbook Ppt Slides Background Designs to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Comparison, using this template. Grab it now to reap its full benefits.
-
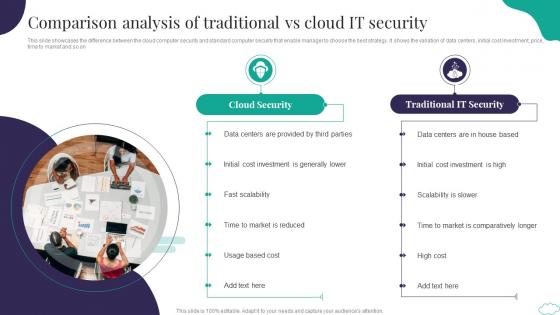 Comparison Analysis Of Traditional Vs Cloud It Security
Comparison Analysis Of Traditional Vs Cloud It SecurityThis slide showcases the difference between the cloud computer security and standard computer security that enable manager to choose the best strategy. It shows the variation of data centers, initial cost investment, price, time to market and so on Introducing our premium set of slides with Comparison Analysis Of Traditional Vs Cloud It Security. Elucidate the two stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cloud Security, Traditional IT Security. So download instantly and tailor it with your information.
-
 Comparison Of Various Security Awareness Training Software Developing Cyber Security Awareness
Comparison Of Various Security Awareness Training Software Developing Cyber Security AwarenessThe purpose of this slide is to drawn comparison of multiple software which can be used to provide cyber security training to the key stakeholders. Information covered in this slide is related to phishing simulations, security reporting, individualized security training plan etc. Deliver an outstanding presentation on the topic using this Comparison Of Various Security Awareness Training Software Developing Cyber Security Awareness. Dispense information and present a thorough explanation of Comparison Of Various, Security Awareness, Training Software using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Comparison Of Various Cyber Security Software
Comparison Of Various Cyber Security SoftwareThis slide shows comparative analysis of various cyber security tools which can be used by organizations for IT safety. It includes features, compatibility, price and ratings. Presenting our well structured Comparison Of Various Cyber Security Software. The topics discussed in this slide are Software, Features, Compatibility, Price, Ratings. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
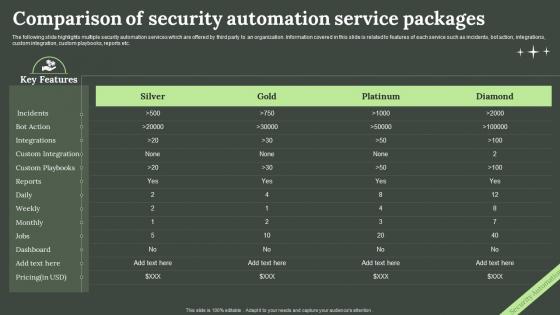 Comparison Of Security Automation Service Packages
Comparison Of Security Automation Service PackagesThe following slide highlights multiple security automation services which are offered by third party to an organization. Information covered in this slide is related to features of each service such as incidents, bot action, integrations, custom integration, custom playbooks, reports etc. Introducing our Comparison Of Security Automation Service Packages set of slides. The topics discussed in these slides are Comparison, Security Automation Service, Packages. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
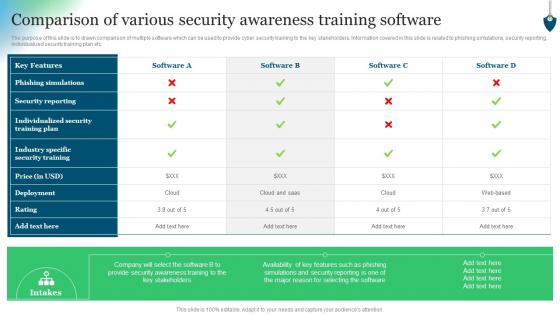 Comparison Of Various Security Awareness Training Software Conducting Security Awareness
Comparison Of Various Security Awareness Training Software Conducting Security AwarenessThe purpose of this slide is to drawn comparison of multiple software which can be used to provide cyber security training to the key stakeholders. Information covered in this slide is related to phishing simulations, security reporting, individualized security training plan etc. Deliver an outstanding presentation on the topic using this Comparison Of Various Security Awareness Training Software Conducting Security Awareness. Dispense information and present a thorough explanation of Key Features, Phishing Simulations, Security Reporting using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
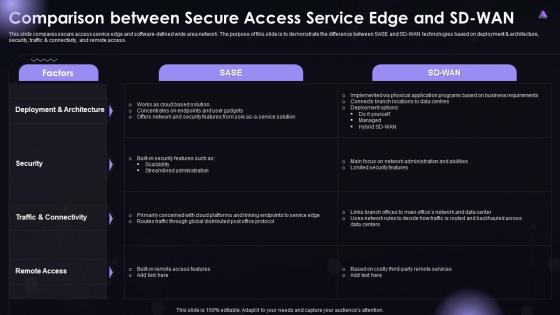 SASE IT Comparison Between Secure Access Service Edge And SD WAN Ppt Download
SASE IT Comparison Between Secure Access Service Edge And SD WAN Ppt DownloadThis slide compares secure access service edge and software-defined wide area network. The purpose of this slide is to demonstrate the difference between SASE and SD-WAN technologies based on deployment and architecture, security, traffic and connectivity, and remote access. Deliver an outstanding presentation on the topic using this SASE IT Comparison Between Secure Access Service Edge And SD WAN Ppt Download. Dispense information and present a thorough explanation of Deployment And Architecture, Traffic And Connectivity, Security, Remote Access using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
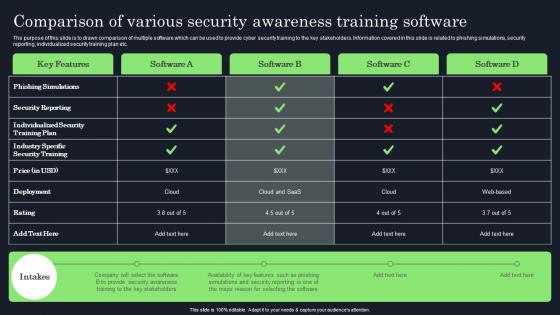 Comparison Of Various Security Awareness Raising Cyber Security Awareness In Organizations
Comparison Of Various Security Awareness Raising Cyber Security Awareness In OrganizationsThe purpose of this slide is to drawn comparison of multiple software which can be used to provide cyber security training to the key stakeholders. Information covered in this slide is related to phishing simulations, security reporting, individualized security training plan etc. Present the topic in a bit more detail with this Comparison Of Various Security Awareness Raising Cyber Security Awareness In Organizations. Use it as a tool for discussion and navigation on Phishing Simulations, Security Reporting, Individualized Security. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Comparison Traditional Digital Globally Mobile Banking For Convenient And Secure Online Payments Fin SS
Comparison Traditional Digital Globally Mobile Banking For Convenient And Secure Online Payments Fin SSThis slide shows data related to different types of banking users with different age groups. It includes percentage of population uses traditional, digital and mobile banking services. Deliver an outstanding presentation on the topic using this Comparison Traditional Digital Globally Mobile Banking For Convenient And Secure Online Payments Fin SS. Dispense information and present a thorough explanation of Comparison, Traditional, Services using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
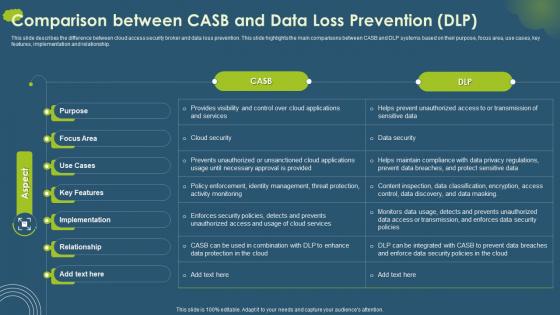 Cloud Access Security Broker CASB Comparison Between CASB And Data Loss Prevention
Cloud Access Security Broker CASB Comparison Between CASB And Data Loss PreventionThis slide describes the difference between cloud access security broker and data loss prevention. This slide highlights the main comparisons between CASB and DLP systems based on their purpose, focus area, use cases, key features, implementation and relationship. Deliver an outstanding presentation on the topic using this Cloud Access Security Broker CASB Comparison Between CASB And Data Loss Prevention. Dispense information and present a thorough explanation of Purpose, Focus Area, Use Cases using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
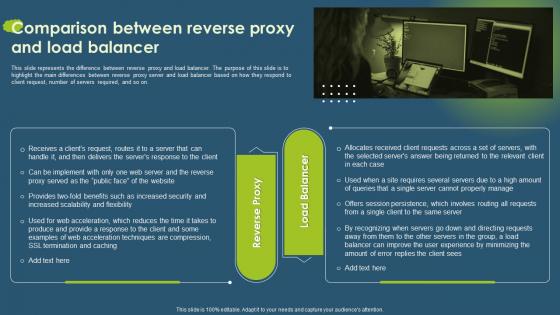 Cloud Access Security Broker CASB Comparison Between Reverse Proxy And Load Balancer
Cloud Access Security Broker CASB Comparison Between Reverse Proxy And Load BalancerThis slide represents the difference between reverse proxy and load balancer. The purpose of this slide is to highlight the main differences between reverse proxy server and load balancer based on how they respond to client request, number of servers required, and so on. Increase audience engagement and knowledge by dispensing information using Cloud Access Security Broker CASB Comparison Between Reverse Proxy And Load Balancer. This template helps you present information on two stages. You can also present information on Reverse Proxy, Load Balancer, Comparison using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 ZTNA Comparison Between ZTNA And Secure Access Service Edge
ZTNA Comparison Between ZTNA And Secure Access Service EdgeThis slide compares the two security models, such as zero trust network architecture and secure access service edge. The purpose of this slide is to highlight the difference between ZTNA and SASE based on definition, key features, deployment, use cases, benefits and challenges. Present the topic in a bit more detail with this ZTNA Comparison Between ZTNA And Secure Access Service Edge. Use it as a tool for discussion and navigation on Deployment, Benefits, Applications. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
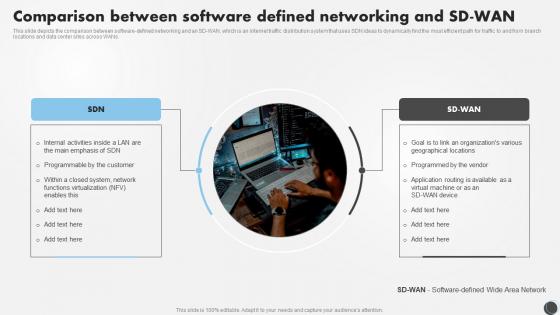 SDN Security IT Comparison Between Software Defined Networking And SD WAN
SDN Security IT Comparison Between Software Defined Networking And SD WANThis slide depicts the comparison between software defined networking and an SD WAN, which is an internet traffic distribution system that uses SDN ideas to dynamically find the most efficient path for traffic to and from branch locations and data center sites across WANs. Introducing SDN Security IT Comparison Between Software Defined Networking And SD WAN to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Comparison, Software, Networking, using this template. Grab it now to reap its full benefits.
-
 Information Security Frameworks Comparison In Powerpoint And Google Slides Cpb
Information Security Frameworks Comparison In Powerpoint And Google Slides CpbPresenting our Information Security Frameworks Comparison In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Information Security Frameworks Comparison. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Cyber security products comparison ppt powerpoint presentation file diagrams cpb
Cyber security products comparison ppt powerpoint presentation file diagrams cpbPresenting this set of slides with name Cyber Security Products Comparison Ppt Powerpoint Presentation File Diagrams Cpb. This is an editable Powerpoint five stages graphic that deals with topics like Cyber Security Products Comparison to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.


