Powerpoint Templates and Google slides for Cyber
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Key Factors For Updating Cyber Security Policy
Key Factors For Updating Cyber Security PolicyThis slide covers key reasons for updating cybersecurity policies. The purpose of this template is to serve as a quick reference for stakeholders, outlining the pivotal circumstances that necessitate policy revisions. It includes regulatory changes, technology upgrades, security incidents, and organizational shifts. Introducing our premium set of slides with Key Factors For Updating Cyber Security Policy Ellicudate the Four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Regulatory Changes, Technology Upgrades, Security Incidents. So download instantly and tailor it with your information.
-
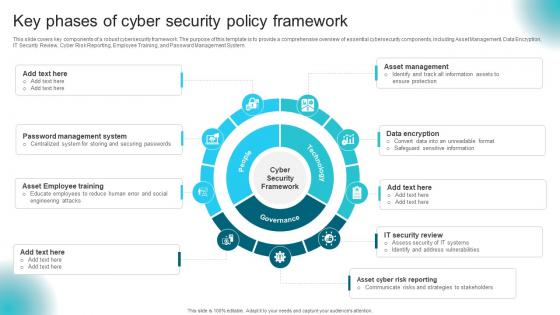 Key Phases Of Cyber Security Policy Framework
Key Phases Of Cyber Security Policy FrameworkThis slide covers key components of a robust cybersecurity framework. The purpose of this template is to provide a comprehensive overview of essential cybersecurity components, including Asset Management, Data Encryption, IT Security Review, Cyber Risk Reporting, Employee Training, and Password Management System. Presenting our set of slides with Key Phases Of Cyber Security Policy Framework This exhibits information on Eight stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cyber Security Framework, Data Encryption
-
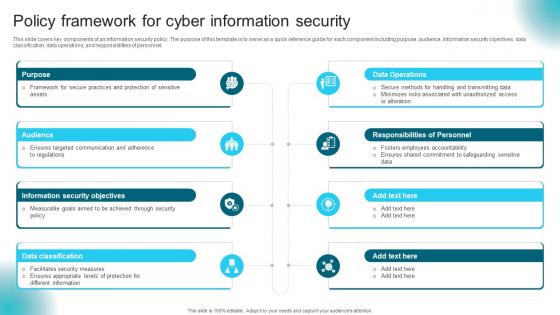 Policy Framework For Cyber Information Security
Policy Framework For Cyber Information SecurityThis slide covers key components of an information security policy. The purpose of this template is to serve as a quick reference guide for each component including purpose, audience, information security objectives, data classification, data operations, and responsibilities of personnel. Presenting our set of slides with Policy Framework For Cyber Information Security This exhibits information on Eight stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Purpose, Audience, Information Security Objectives
-
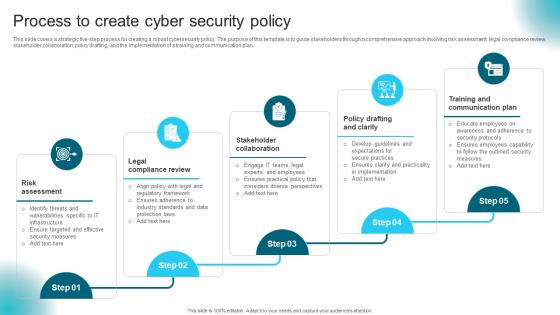 Process To Create Cyber Security Policy
Process To Create Cyber Security PolicyIntroducing our premium set of slides with Process To Create Cyber Security Policy Ellicudate the Five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Risk Assessment, Legal Compliance Review, Stakeholder Collaboration. So download instantly and tailor it with your information.
-
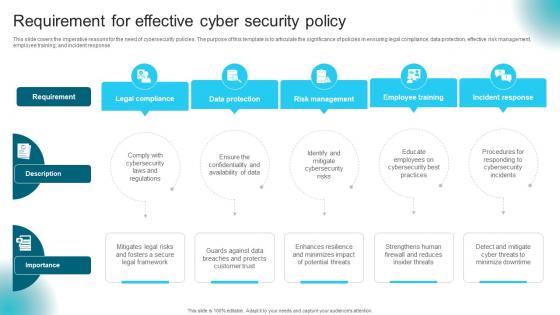 Requirement For Effective Cyber Security Policy
Requirement For Effective Cyber Security PolicyThis slide covers the imperative reasons for the need of cybersecurity policies. The purpose of this template is to articulate the significance of policies in ensuring legal compliance, data protection, effective risk management, employee training, and incident response. Presenting our set of slides with Requirement For Effective Cyber Security Policy This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Legal Compliance, Data Protection, Risk Management
-
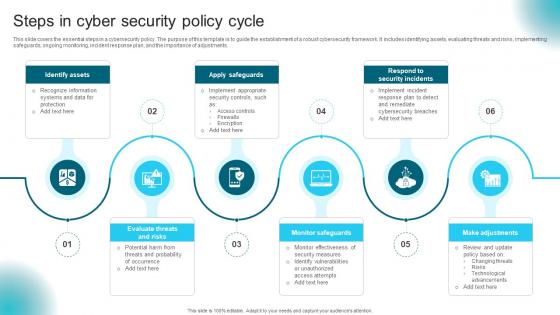 Steps In Cyber Security Policy Cycle
Steps In Cyber Security Policy CycleThis slide covers the essential steps in a cybersecurity policy. The purpose of this template is to guide the establishment of a robust cybersecurity framework. It includes identifying assets, evaluating threats and risks, implementing safeguards, ongoing monitoring, incident response plan, and the importance of adjustments. Presenting our set of slides with Steps In Cyber Security Policy Cycle This exhibits information on Six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Identify Assets, Apply Safeguards, Monitor Safeguards
-
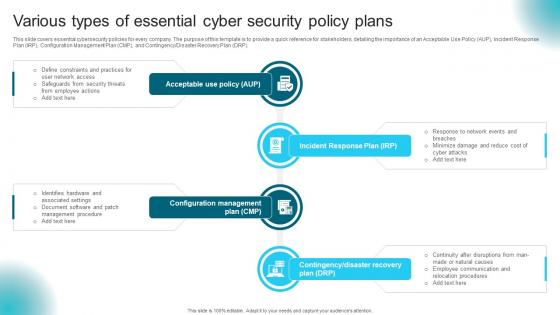 Various Types Of Essential Cyber Security Policy Plans
Various Types Of Essential Cyber Security Policy PlansThis slide covers essential cybersecurity policies for every company. The purpose of this template is to provide a quick reference for stakeholders, detailing the importance of an Acceptable Use Policy AUP, Incident Response Plan IRP, Configuration Management Plan CMP, and ContingencyDisaster Recovery Plan DRP. Introducing our premium set of slides with Various Types Of Essential Cyber Security Policy Plans Ellicudate the Six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Incident Response Plan, Configuration Management, Acceptable Use Policy. So download instantly and tailor it with your information.
-
 Gamification Training Methods In Cyber Security
Gamification Training Methods In Cyber SecurityThis slide showcases the gamification training topics used in cyber security. It include details such as cybersecurity simulations, scavenger hunts, etc. Introducing our Gamification Training Methods In Cyber Security set of slides. The topics discussed in these slides are Cybersecurity Simulations, Scavenger Hunts, Cybersecurity Trivia This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
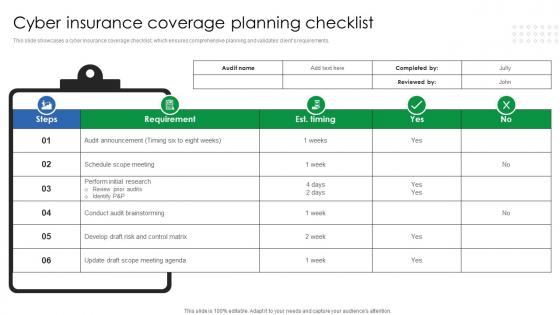 Cyber Insurance Coverage Planning Checklist
Cyber Insurance Coverage Planning ChecklistThis slide showcases a cyber insurance coverage checklist, which ensures comprehensive planning and validates clients requirements. Presenting our well structured Cyber Insurance Coverage Planning Checklist. The topics discussed in this slide are Cyber Insurance, Coverage Planning Checklist. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Cyber Security Insurance Audit Checklist
Cyber Security Insurance Audit ChecklistThis slide showcases cyber security insurance audit checklist which helps in providing coverage to reduce the financial risks associated with cybercrimes. Introducing our Cyber Security Insurance Audit Checklist set of slides. The topics discussed in these slides are Network And Perimeter Security, Password Policy And Authentication, Vulnerability Management, Backups And Disaster Recovery.This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Advantages Of CTI In Enhancing Business Cybersecurity
Advantages Of CTI In Enhancing Business CybersecurityThis slide highlights the advantages of utilizing CTI to improve business cyber security. The purpose of this slide is to help the business utilize cyber threat intelligence in order to identify advanced persistent threats, enhance business cybersecurity, etc. Presenting our set of slides with Advantages Of CTI In Enhancing Business Cybersecurity This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Advantages, Description, Benefit
-
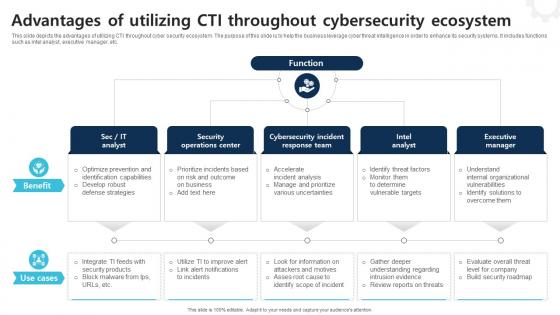 Advantages Of Utilizing CTI Throughout Cybersecurity Ecosystem
Advantages Of Utilizing CTI Throughout Cybersecurity EcosystemThis slide depicts the advantages of utilizing CTI throughout cyber security ecosystem. The purpose of this slide is to help the business leverage cyber threat intelligence in order to enhance its security systems. It includes functions such as intel analyst, executive manager, etc. Introducing our premium set of slides with Advantages Of Utilizing CTI Throughout Cybersecurity Ecosystem Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Security Operations Center, Intel Analyst, Executive Manager So download instantly and tailor it with your information.
-
 Best Practices For Integrating Threat Intelligence With Cybersecurity
Best Practices For Integrating Threat Intelligence With CybersecurityThis slide depicts the best practices for integrating cyber threat intelligence with cybersecurity. The purpose of this slide is to help the business successfully integrate threat intelligence with cybersecurity. It includes automation of data processing,, establishment of threat intelligence sharing policies, etc. Presenting our set of slides with Best Practices For Integrating Threat Intelligence With Cybersecurity This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Ensure Integration, Current System, Automate Data Processing
-
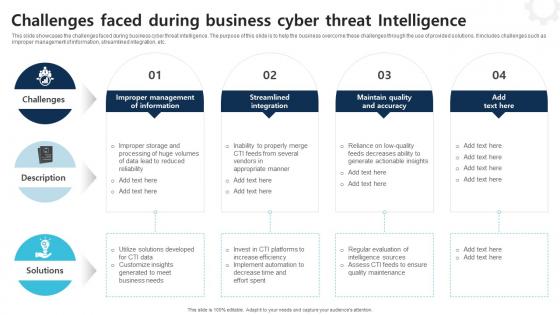 Challenges Faced During Business Cyber Threat Intelligence
Challenges Faced During Business Cyber Threat IntelligenceThis slide showcases the challenges faced during business cyber threat intelligence. The purpose of this slide is to help the business overcome these challenges through the use of provided solutions. It includes challenges such as improper management of information, streamlined integration, etc. Introducing our premium set of slides with Challenges Faced During Business Cyber Threat Intelligence Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Description, Challenges, Solutions So download instantly and tailor it with your information.
-
 CTI Cybersecurity Icon To Prevent Malware Infections And Attacks
CTI Cybersecurity Icon To Prevent Malware Infections And AttacksPresenting our set of slides with CTI Cybersecurity Icon To Prevent Malware Infections And Attacks This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on CTI Cybersecurity Icon, Prevent Malware Infections And Attacks
-
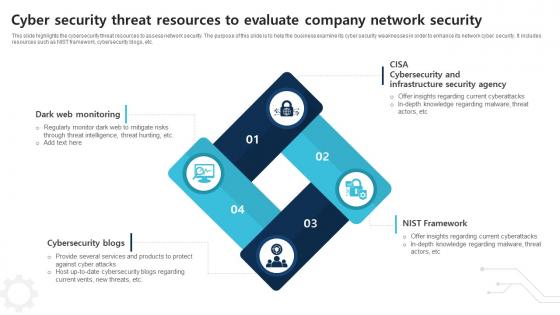 Cyber Security Threat Resources To Evaluate Company Network Security
Cyber Security Threat Resources To Evaluate Company Network SecurityThis slide highlights the cybersecurity threat resources to assess network security. The purpose of this slide is to help the business examine its cyber security weaknesses in order to enhance its network cyber security. It includes resources such as NIST framework, cybersecurity blogs, etc. Introducing our premium set of slides with Cyber Security Threat Resources To Evaluate Company Network Security Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Dark Web Monitoring, Cybersecurity Blogs, Nist Framework So download instantly and tailor it with your information.
-
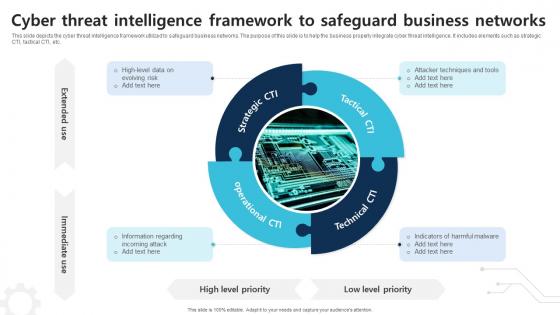 Cyber Threat Intelligence Framework To Safeguard Business Networks
Cyber Threat Intelligence Framework To Safeguard Business NetworksThis slide depicts the cyber threat intelligence framework utilized to safeguard business networks. The purpose of this slide is to help the business properly integrate cyber threat intelligence. It includes elements such as strategic CTI, tactical CTI, etc. Presenting our set of slides with Cyber Threat Intelligence Framework To Safeguard Business Networks This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Operational CTI, Strategic CTI
-
 Cyber Threat Intelligence Icon To Detect Digital Attacks
Cyber Threat Intelligence Icon To Detect Digital AttacksIntroducing our premium set of slides with Cyber Threat Intelligence Icon To Detect Digital Attacks Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cyber Threat Intelligence Icon, Detect Digital Attacks So download instantly and tailor it with your information.
-
 Cyber Threat Intelligence Icon To Enhance Cybersecurity
Cyber Threat Intelligence Icon To Enhance CybersecurityPresenting our set of slides with Cyber Threat Intelligence Icon To Enhance Cybersecurity This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cyber Threat Intelligence Icon, Enhance Cybersecurity
-
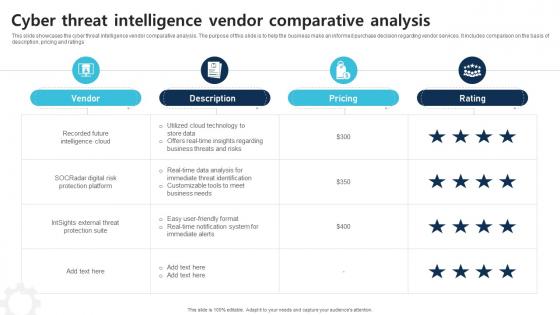 Cyber Threat Intelligence Vendor Comparative Analysis
Cyber Threat Intelligence Vendor Comparative AnalysisThis slide showcases the cyber threat intelligence vendor comparative analysis. The purpose of this slide is to help the business make an informed purchase decision regarding vendor services. It includes comparison on the basis of description, pricing and ratings Introducing our Cyber Threat Intelligence Vendor Comparative Analysis set of slides. The topics discussed in these slides are Vendor, Description, Pricing This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
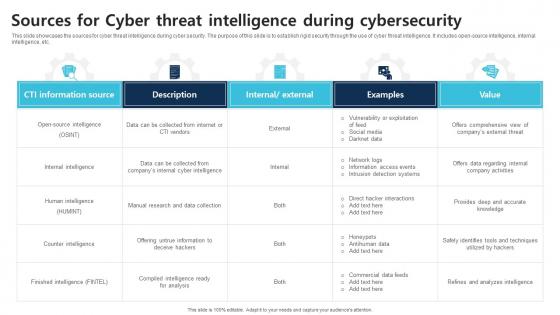 Sources For Cyber Threat Intelligence During Cybersecurity
Sources For Cyber Threat Intelligence During CybersecurityThis slide showcases the sources for cyber threat intelligence during cyber security. The purpose of this slide is to establish rigid security through the use of cyber threat intelligence. It includes open source intelligence, internal intelligence, etc. Presenting our well structured Sources For Cyber Threat Intelligence During Cybersecurity The topics discussed in this slide are CTI Information Source, Description, Examples This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Steps For Cyber Threat Intelligence Lifecycles
Steps For Cyber Threat Intelligence LifecyclesThis slide depicts the steps for cyber threat intelligence lifecycles. The purpose of this slide is to help the business successfully implement cyber threat intelligence practices. It includes steps such as requirements, collection, processing, etc. Introducing our premium set of slides with Steps For Cyber Threat Intelligence Lifecycles Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Requirements, Collection, Processing So download instantly and tailor it with your information.
-
 Types Of Cyber Threat Intelligence To Safeguard Business
Types Of Cyber Threat Intelligence To Safeguard BusinessThis slide depicts the steps for cyber threat intelligence lifecycles. The purpose of this slide is to help the business successfully implement cyber threat intelligence practices. It includes steps such as requirements, collection, processing, etc. Presenting our set of slides with Types Of Cyber Threat Intelligence To Safeguard Business This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Strategic Intelligence, Tactical Intelligence, Operational Intelligence
-
 Use Cases Of Cyber Threat Intelligence Framework To Establish Cybersecurity
Use Cases Of Cyber Threat Intelligence Framework To Establish CybersecurityThis slide depicts the use cases of cyber threat intelligence framework to establish cybersecurity. The purpose of this slide is to help the business appropriately utilize cyber threat intelligence framework in order to enhance its network security. It includes cyber risk management, security operations center, etc. Introducing our premium set of slides with Use Cases Of Cyber Threat Intelligence Framework To Establish Cybersecurity Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cyber Risk Management, Vulnerability Management, Security Operations Center So download instantly and tailor it with your information.
-
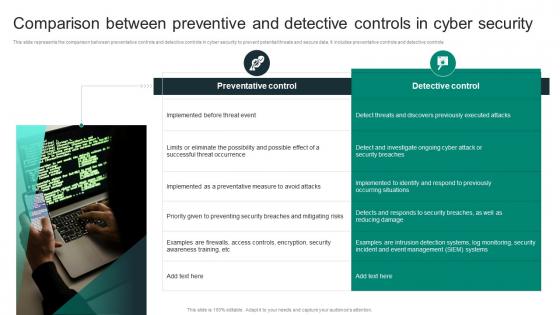 Comparison Between Preventive And Detective Controls In Cyber Security
Comparison Between Preventive And Detective Controls In Cyber SecurityThis slide represents the comparison between preventative controls and detective controls in cyber security to prevent potential threats and secure data. It includes preventative controls and detective controls Presenting our set of slides with Comparison Between Preventive And Detective Controls In Cyber Security This exhibits information on two stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Preventative Control, Detective Control
-
 Cyber Security Attack Control Icon
Cyber Security Attack Control IconIntroducing our premium set of slides with Cyber Security Attack Control Icon Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cyber Security Attack Control Icon So download instantly and tailor it with your information.
-
 Cyber Security Controls Checklist For Business
Cyber Security Controls Checklist For BusinessThis slide highlights the checklist for cyber security controls to prevent business from cyber attacks and protect company confidential data. It includes various KPIs such as password management, privacy and security of sensitive data. Presenting our well structured Cyber Security Controls Checklist For Business The topics discussed in this slide are Password Management, Security Awareness This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
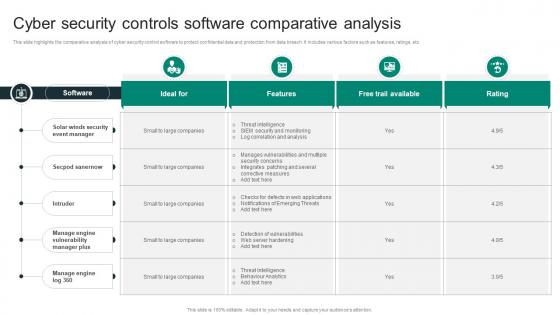 Cyber Security Controls Software Comparative Analysis
Cyber Security Controls Software Comparative AnalysisThis slide highlights the comparative analysis of cyber security control software to protect confidential data and protection from data breach. It includes various factors such as features, ratings, etc Introducing our Cyber Security Controls Software Comparative Analysis set of slides. The topics discussed in these slides are Secpod Sanernow, Intruder, Solar Winds Security Event Manager This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Cyber Security Online Threat Control Icon
Cyber Security Online Threat Control IconPresenting our set of slides with Cyber Security Online Threat Control Icon This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cyber Security Online Threat Control Icon
-
 NIST Cyber Security Control Framework For Business
NIST Cyber Security Control Framework For BusinessThis slide represents cyber security control NIST framework to help business in identifying potential threats of attacks or data breach. It includes various steps such as identify, protect, detect, respond and recover. Introducing our premium set of slides with NIST Cyber Security Control Framework For Business Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Identify, Protect, Detect So download instantly and tailor it with your information.
-
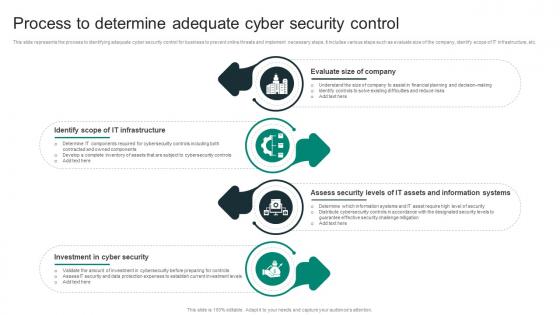 Process To Determine Adequate Cyber Security Control
Process To Determine Adequate Cyber Security ControlThis slide represents the process to identifying adequate cyber security control for business to prevent online threats and implement necessary steps. It includes various steps such as evaluate size of the company, identify scope of IT infrastructure, etc. Presenting our set of slides with Process To Determine Adequate Cyber Security Control This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Identify Scope Of It Infrastructure, Evaluate Size Of Company, Investment In Cyber Security
-
 Types Of Detective Controls Cyber Security
Types Of Detective Controls Cyber SecurityThis slide represents the types of detective controls used in cyber security to prevent data breach by unauthorized access or online attack. It includes various steps such as log monitoring, SIEM, trend analysis, etc. Introducing our premium set of slides with Types Of Detective Controls Cyber Security Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Trend Analysis, Security Audits, Log Monitoring So download instantly and tailor it with your information.
-
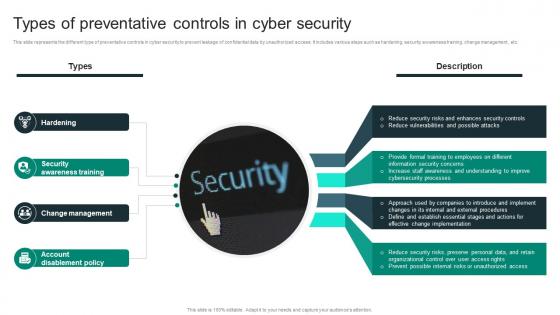 Types Of Preventative Controls In Cyber Security
Types Of Preventative Controls In Cyber SecurityThis slide represents the different type of preventative controls in cyber security to prevent leakage of confidential data by unauthorized access. It includes various steps such as hardening, security awareness training, change management, etc. Presenting our set of slides with Types Of Preventative Controls In Cyber Security This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Security Awareness Training, Hardening, Change Management
-
 Types Of Technical Controls In Cyber Security
Types Of Technical Controls In Cyber SecurityThis slide represents the various types of technical control in cyber security to monitor and track potential threats and prevent data breach. It includes various types such as encryptions, firewalls, antivirus software, etc. Introducing our premium set of slides with Types Of Technical Controls In Cyber Security Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Encryptions, Firewalls, Antivirus Software So download instantly and tailor it with your information.
-
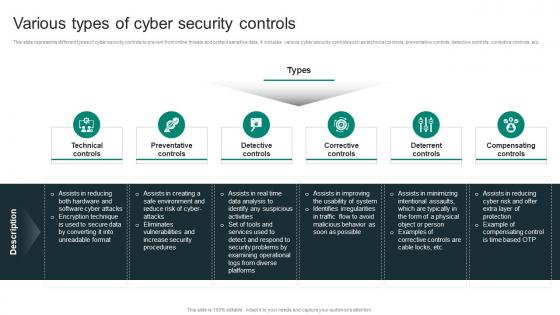 Various Types Of Cyber Security Controls
Various Types Of Cyber Security ControlsThis slide represents different types of cyber security controls to prevent from online threats and protect sensitive data. It includes various cyber security controls such as technical controls, preventative controls, detective controls, corrective controls, etc. Presenting our set of slides with Various Types Of Cyber Security Controls This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Technical Controls, Preventative Controls, Detective Controls
-
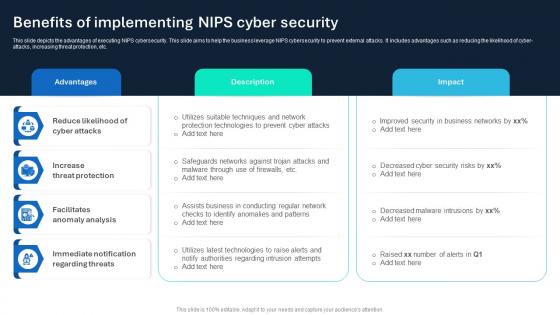 Benefits Of Implementing NIPS Cyber Security
Benefits Of Implementing NIPS Cyber SecurityThis slide depicts the advantages of executing NIPS cybersecurity. This slide aims to help the business leverage NIPS cybersecurity to prevent external attacks. It includes advantages such as reducing the likelihood of cyber attacks, increasing threat protection, etc. Introducing our Benefits Of Implementing NIPS Cyber Security set of slides. The topics discussed in these slides are Advantages, Description, Impact This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
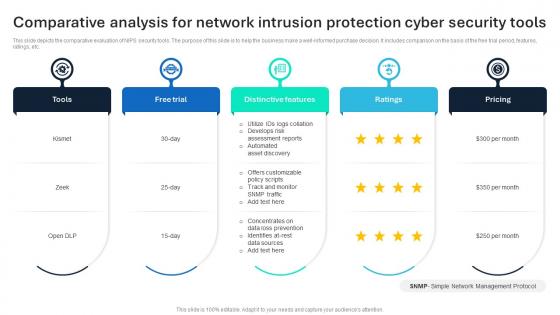 Comparative Analysis For Network Intrusion Protection Cyber Security Tools
Comparative Analysis For Network Intrusion Protection Cyber Security ToolsThis slide depicts the comparative evaluation of NIPS security tools. The purpose of this slide is to help the business make a well informed purchase decision. It includes comparison on the basis of the free trial period, features, ratings, etc. Introducing our premium set of slides with Comparative Analysis For Network Intrusion Protection Cyber Security Tools Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Distinctive Features, Free Trial, Tools So download instantly and tailor it with your information.
-
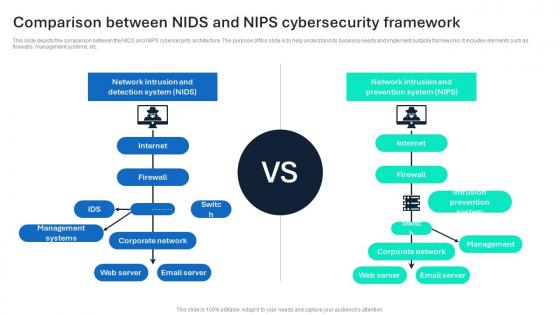 Comparison Between NIDS And NIPS Cybersecurity Framework
Comparison Between NIDS And NIPS Cybersecurity FrameworkThis slide depicts the comparison between the NIDS and NIPS cybersecurity architecture. The purpose of this slide is to help understand its business needs and implement suitable frameworks. It includes elements such as firewalls, management systems, etc. Presenting our set of slides with Comparison Between NIDS And NIPS Cybersecurity Framework This exhibits information on two stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Internet, Firewall, Corporate Network
-
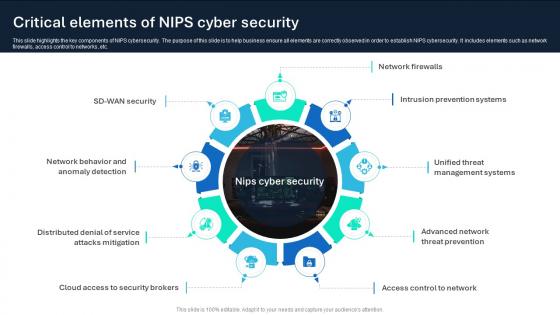 Critical Elements Of NIPS Cyber Security
Critical Elements Of NIPS Cyber SecurityThis slide highlights the key components of NIPS cybersecurity. The purpose of this slide is to help business ensure all elements are correctly observed in order to establish NIPS cybersecurity. It includes elements such as network firewalls, access control to networks, etc. Introducing our premium set of slides with Critical Elements Of NIPS Cyber Security Ellicudate the nine stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Network Firewalls, Intrusion Prevention Systems, Management Systems So download instantly and tailor it with your information.
-
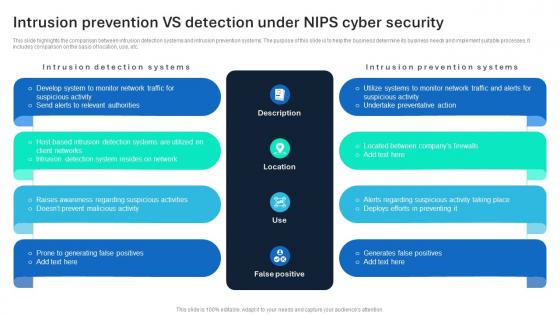 Intrusion Prevention VS Detection Under NIPS Cyber Security
Intrusion Prevention VS Detection Under NIPS Cyber SecurityThis slide highlights the comparison between intrusion detection systems and intrusion prevention systems. The purpose of this slide is to help the business determine its business needs and implement suitable processes. It includes comparison on the basis of location, use, etc. Presenting our well structured Intrusion Prevention VS Detection Under NIPS Cyber Security The topics discussed in this slide are Description, Location, False Positive This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Network Intrusion And Prevention Cyber Security Icon
Network Intrusion And Prevention Cyber Security IconPresenting our set of slides with Network Intrusion And Prevention Cyber Security Icon This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Network Intrusion, Prevention Cyber Security Icon
-
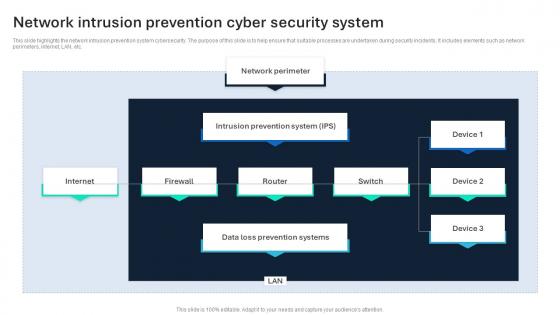 Network Intrusion Prevention Cyber Security System
Network Intrusion Prevention Cyber Security SystemThis slide highlights the network intrusion prevention system cybersecurity. The purpose of this slide is to help ensure that suitable processes are undertaken during security incidents. It includes elements such as network perimeters, internet, LAN, etc. Introducing our Network Intrusion Prevention Cyber Security System set of slides. The topics discussed in these slides are Internet, Network Perimeter, Prevention Systems This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 NIPS Cybersecurity Icon To Safeguard Company Networks
NIPS Cybersecurity Icon To Safeguard Company NetworksIntroducing our premium set of slides with NIPS Cybersecurity Icon To Safeguard Company Networks Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Nips Cybersecurity Icon, Safeguard Company Networks So download instantly and tailor it with your information.
-
 Solutions To Overcome Nips Cybersecurity Challenges
Solutions To Overcome Nips Cybersecurity ChallengesThis slide showcases the challenges faced during Nips cybersecurity implementation. The purpose of this slide is to help the business overcome these challenges through the use of given solutions. It includes challenges such as false positives, evolving threats, etc. Presenting our well structured Solutions To Overcome Nips Cybersecurity Challenges The topics discussed in this slide are Challenge, Description, Solutions This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
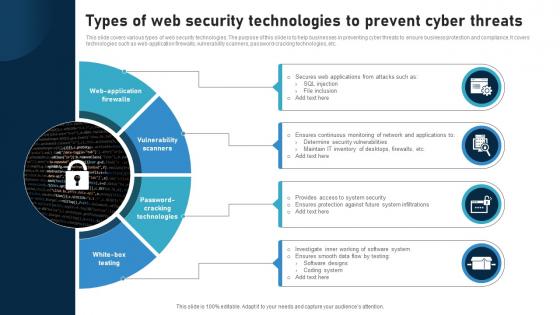 Types Of Web Security Technologies To Prevent Cyber Threats
Types Of Web Security Technologies To Prevent Cyber ThreatsThis slide covers various types of web security technologies. The purpose of this slide is to help businesses in preventing cyber threats to ensure business protection and compliance. It covers technologies such as web application firewalls, vulnerability scanners, password cracking technologies, etc. Presenting our set of slides with Types Of Web Security Technologies To Prevent Cyber Threats This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Web Application Firewalls, Vulnerability Scanners, Password Cracking Technologies
-
 Web Security Icon To Prevent Cyber Attacks
Web Security Icon To Prevent Cyber AttacksPresenting our set of slides with Web Security Icon To Prevent Cyber Attacks This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Web Security Icon, Prevent Cyber Attacks
-
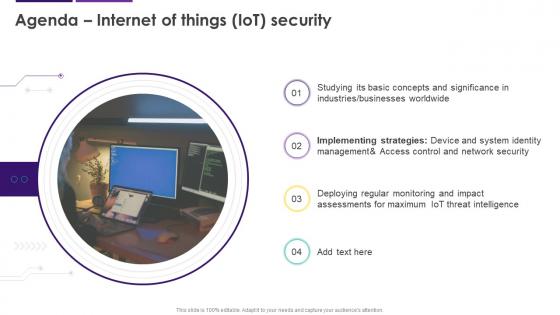 Agenda Internet Of Things IoT Security Ppt Ideas Background Images Cybersecurity SS
Agenda Internet Of Things IoT Security Ppt Ideas Background Images Cybersecurity SSIntroducing Agenda Internet Of Things IoT Security Ppt Ideas Background Images Cybersecurity SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Businesses Worldwide, Implementing Strategies, Threat Intelligence, using this template. Grab it now to reap its full benefits.
-
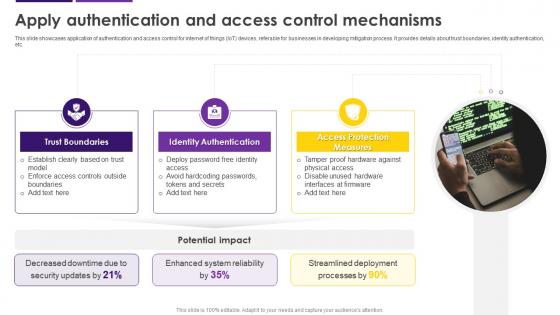 Apply Authentication And Access Control Mechanisms Internet Of Things IoT Security Cybersecurity SS
Apply Authentication And Access Control Mechanisms Internet Of Things IoT Security Cybersecurity SSThis slide showcases application of authentication and access control for internet of things IoT devices, referable for businesses in developing mitigation process. It provides details about trust boundaries, identity authentication, etc. Increase audience engagement and knowledge by dispensing information using Apply Authentication And Access Control Mechanisms Internet Of Things IoT Security Cybersecurity SS. This template helps you present information on three stages. You can also present information on Trust Boundaries, Identity Authentication, Access Protection Measures using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
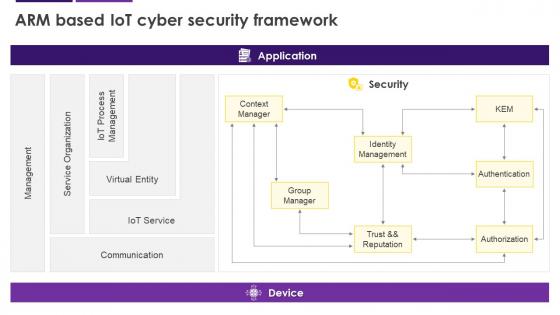 Arm Based IoT Cyber Security Framework Internet Of Things IoT Security Cybersecurity SS
Arm Based IoT Cyber Security Framework Internet Of Things IoT Security Cybersecurity SSPresent the topic in a bit more detail with this Arm Based IoT Cyber Security Framework Internet Of Things IoT Security Cybersecurity SS. Use it as a tool for discussion and navigation on Management, Service Organization, Communication, Cyber Security Framework. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
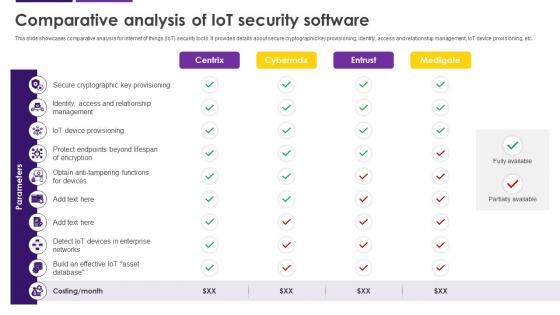 Comparative Analysis Of IoT Security Software Internet Of Things IoT Security Cybersecurity SS
Comparative Analysis Of IoT Security Software Internet Of Things IoT Security Cybersecurity SSThis slide showcases comparative analysis for internet of things IoT security tools. It provides details about secure cryptographic key provisioning, identity, access and relationship management, IoT device provisioning, etc. Deliver an outstanding presentation on the topic using this Comparative Analysis Of IoT Security Software Internet Of Things IoT Security Cybersecurity SS. Dispense information and present a thorough explanation of Comparative Analysis, IoT Security Software, IoT Device Provisioning, Secure Cryptographic using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
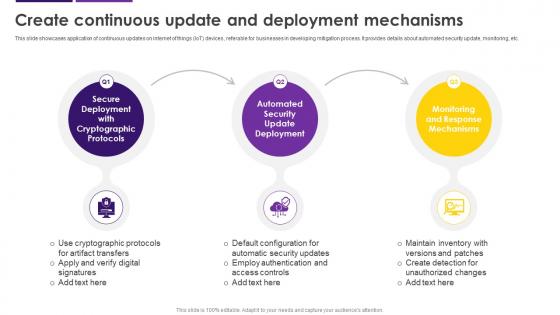 Create Continuous Update And Deployment Mechanisms Internet Of Things IoT Security Cybersecurity SS
Create Continuous Update And Deployment Mechanisms Internet Of Things IoT Security Cybersecurity SSThis slide showcases comparative analysis for internet of things IoT security tools. It provides details about secure cryptographic key provisioning, identity, access and relationship management, IoT device provisioning, etc. Introducing Create Continuous Update And Deployment Mechanisms Internet Of Things IoT Security Cybersecurity SS to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Secure Deployment, Cryptographic Protocols, Automated Security Update Deployment, Monitoring And Response Mechanisms, using this template. Grab it now to reap its full benefits.
-
 Current IoT Security Business Challenges Internet Of Things IoT Security Cybersecurity SS
Current IoT Security Business Challenges Internet Of Things IoT Security Cybersecurity SSThis slide showcases internet of things IoT security challenges faced by businesses. It provides details about IoT malware and ransomware, user privacy risks, insecure interfaces, remove work environments, etc. Deliver an outstanding presentation on the topic using this Current IoT Security Business Challenges Internet Of Things IoT Security Cybersecurity SS. Dispense information and present a thorough explanation of IoT Security Business Challenges, Internet Of Things, IoT Malware And Ransomware, User Privacy Risks using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
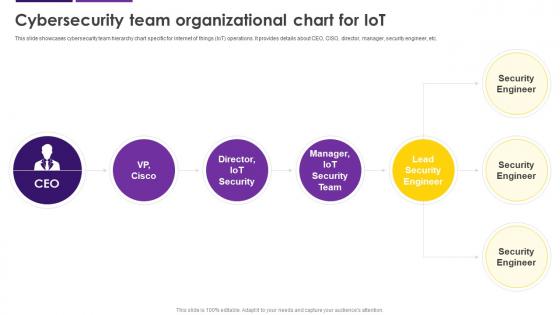 Cybersecurity Team Organizational Chart For IoT Internet Of Things IoT Security Cybersecurity SS
Cybersecurity Team Organizational Chart For IoT Internet Of Things IoT Security Cybersecurity SSThis slide showcases cybersecurity team hierarchy chart specific for internet of things IoT operations. It provides details about CEO, CISO, director, manager, security engineer, etc. Present the topic in a bit more detail with this Cybersecurity Team Organizational Chart For IoT Internet Of Things IoT Security Cybersecurity SS. Use it as a tool for discussion and navigation on Cybersecurity Team, Organizational Chart, Security Engineer, Hierarchy Chart. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
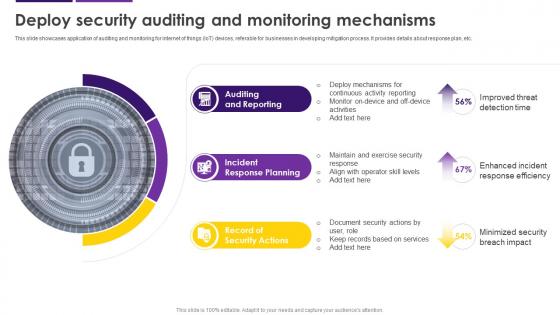 Deploy Security Auditing And Monitoring Mechanisms Internet Of Things IoT Security Cybersecurity SS
Deploy Security Auditing And Monitoring Mechanisms Internet Of Things IoT Security Cybersecurity SSThis slide showcases application of auditing and monitoring for internet of things IoT devices, referable for businesses in developing mitigation process. It provides details about response plan, etc. Increase audience engagement and knowledge by dispensing information using Deploy Security Auditing And Monitoring Mechanisms Internet Of Things IoT Security Cybersecurity SS. This template helps you present information on three stages. You can also present information on Auditing And Reporting, Incident Response Planning, Record Of Security Actions using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Icons Slide For Internet Of Things IoT Security Ppt Ideas Infographic Template Cybersecurity SS
Icons Slide For Internet Of Things IoT Security Ppt Ideas Infographic Template Cybersecurity SSPresenting our well crafted Icons Slide For Internet Of Things IoT Security Ppt Ideas Infographic Template Cybersecurity SS set of slides. The slides include icons that are innovatively designed by our team of experts. The icons are easy to edit so you can conveniently increase or decrease their size without any loss in resolution. Therefore, grab them instantly.
-
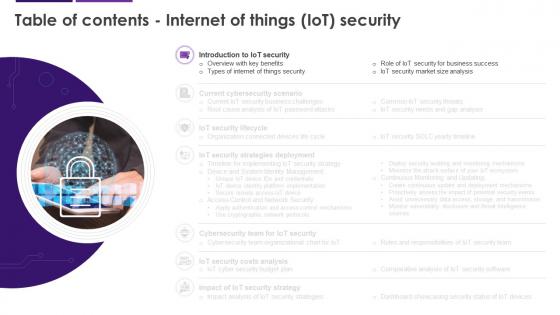 Internet Of Things IoT Security For Table Of Contents Cybersecurity SS
Internet Of Things IoT Security For Table Of Contents Cybersecurity SSIntroducing Internet Of Things IoT Security For Table Of Contents Cybersecurity SS to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Business Success, IoT Security, Market Size Analysis, Overview With Key Benefits, using this template. Grab it now to reap its full benefits.
-
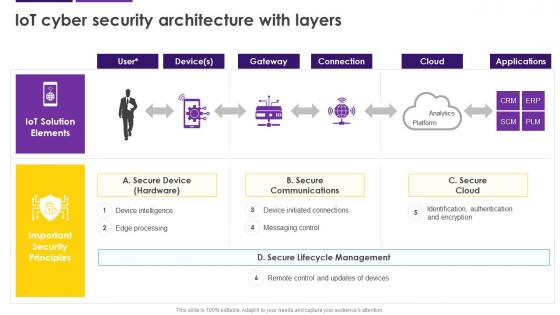 IoT Cyber Security Architecture With Layers Internet Of Things IoT Security Cybersecurity SS
IoT Cyber Security Architecture With Layers Internet Of Things IoT Security Cybersecurity SSDeliver an outstanding presentation on the topic using this IoT Cyber Security Architecture With Layers Internet Of Things IoT Security Cybersecurity SS. Dispense information and present a thorough explanation of Secure Communications, Secure Cloud, Secure Device, Messaging Control using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 IoT Device Identity Platform Implementation Internet Of Things IoT Security Cybersecurity SS
IoT Device Identity Platform Implementation Internet Of Things IoT Security Cybersecurity SSThis slide showcases internet of things IoT device identity platform deployment, referable for businesses in developing mitigation process. It provides details about APIs, architecture, device client, etc. Deliver an outstanding presentation on the topic using this IoT Device Identity Platform Implementation Internet Of Things IoT Security Cybersecurity SS. Dispense information and present a thorough explanation of IoT Device, Platform Deployment, Developing Mitigation Process using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
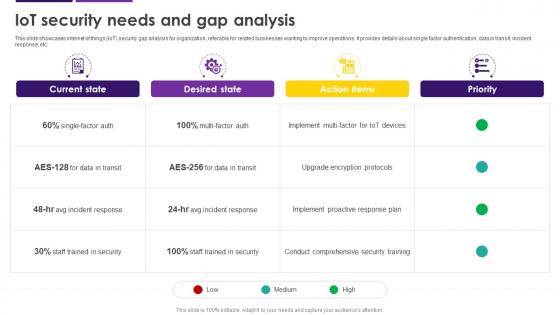 IoT Security Needs And Gap Analysis Internet Of Things IoT Security Cybersecurity SS
IoT Security Needs And Gap Analysis Internet Of Things IoT Security Cybersecurity SSThis slide showcases internet of things IoT security gap analysis for organization, referable for related businesses wanting to improve operations. It provides details about single factor authentication, data in transit, incident response, etc. Deliver an outstanding presentation on the topic using this IoT Security Needs And Gap Analysis Internet Of Things IoT Security Cybersecurity SS. Dispense information and present a thorough explanation of Comprehensive Security Training, Upgrade Encryption Protocols, Gap Analysis using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 IoT Security Overview With Key Benefits Internet Of Things IoT Security Cybersecurity SS
IoT Security Overview With Key Benefits Internet Of Things IoT Security Cybersecurity SSThis slide showcases internet of things IoT security introduction with its major benefits, referable for companies dealing with related vulnerabilities. It provides details about security protocols, device protection, encryption, etc. Increase audience engagement and knowledge by dispensing information using IoT Security Overview With Key Benefits Internet Of Things IoT Security Cybersecurity SS. This template helps you present information on two stages. You can also present information on Protection Of Devices, Encryption Of Networks, Secured Data Handling using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.