Powerpoint Templates and Google slides for Cyber
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Cyber Security Denial Service In Powerpoint And Google Slides Cpb
Cyber Security Denial Service In Powerpoint And Google Slides CpbPresenting Cyber Security Denial Service In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase five stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Cyber Security Denial Service. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Cybers Security Business In Powerpoint And Google Slides Cpb
Cybers Security Business In Powerpoint And Google Slides CpbPresenting Cybers Security Business In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Cybers Security Business. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Largest Cybersecurity Companies Revenue In Powerpoint And Google Slides Cpb
Largest Cybersecurity Companies Revenue In Powerpoint And Google Slides CpbPresenting our Largest Cybersecurity Companies Revenue In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Largest Cybersecurity Companies Revenue. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Cyber Security Awareness In Powerpoint And Google Slides Cpb
Cyber Security Awareness In Powerpoint And Google Slides CpbPresenting Cyber Security Awareness In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Cyber Security Awareness. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Cyber Security Business Network Security In Powerpoint And Google Slides Cpb
Cyber Security Business Network Security In Powerpoint And Google Slides CpbPresenting Cyber Security Business Network Security In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Cyber Security Business Network Security. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Extensive Business Strategy Cyber Strategies For KPMG For Client Data Protection Strategy SS V
Extensive Business Strategy Cyber Strategies For KPMG For Client Data Protection Strategy SS VThis slide covers techniques to secure customers confidential data through several cyber security strategies. The purpose for this template is to provide an overview on important elements of top techniques deployed by the company . It includes strategies such as people, process, data and technology and regulatory. Introducing Extensive Business Strategy Cyber Strategies For KPMG For Client Data Protection Strategy SS V to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on People, Process, Regulatory, using this template. Grab it now to reap its full benefits.
-
 Extensive Business Strategy Other Cyber Strategies Of KPMG For Client Data Protection Strategy SS V
Extensive Business Strategy Other Cyber Strategies Of KPMG For Client Data Protection Strategy SS VThis slide covers cyber strategies to protect KPMG customer data protection. The purpose of this template is to provide an overview on top techniques to be implemented to save clients data. It includes strategies such as developing comprehensive understanding of cyber threat landscape, implementing risk based approach, establishing robust security governance framework, etc. Increase audience engagement and knowledge by dispensing information using Extensive Business Strategy Other Cyber Strategies Of KPMG For Client Data Protection Strategy SS V. This template helps you present information on five stages. You can also present information on Threat Landscape, Cyber Security, Governance Framework using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
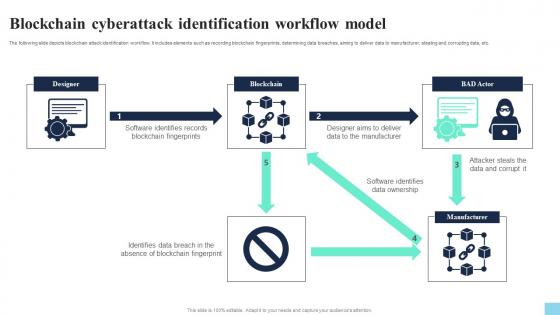 Blockchain Cyberattack Identification Workflow Model Hands On Blockchain Security Risk BCT SS V
Blockchain Cyberattack Identification Workflow Model Hands On Blockchain Security Risk BCT SS VThe following slide depicts blockchain attack identification workflow. It includes elements such as recording blockchain fingerprints, determining data breaches, aiming to deliver data to manufacturer, stealing and corrupting data, etc. Present the topic in a bit more detail with this Blockchain Cyberattack Identification Workflow Model Hands On Blockchain Security Risk BCT SS V. Use it as a tool for discussion and navigation on Blockchain Fingerprints, Data Ownership, Data And Corrupt. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Conducting Blockchain Cybersecurity Training For Users Hands On Blockchain Security Risk BCT SS V
Conducting Blockchain Cybersecurity Training For Users Hands On Blockchain Security Risk BCT SS VThe following slide showcases blockchain cybersecurity training plan to reduce insider threats. It includes elements such as introduction ,blockchain security risks, smart contracts development, network security, data encryption, incidence response management, etc. Deliver an outstanding presentation on the topic using this Conducting Blockchain Cybersecurity Training For Users Hands On Blockchain Security Risk BCT SS V. Dispense information and present a thorough explanation of Trainer Name, Mode, Proposed Date using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
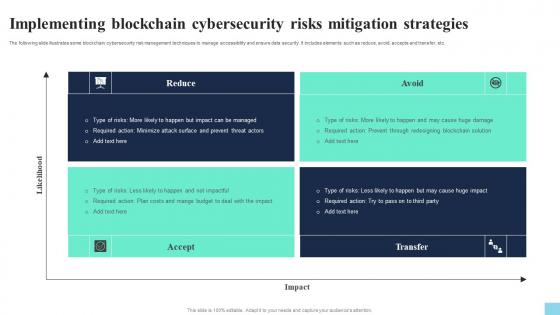 Implementing Blockchain Cybersecurity Risks Mitigation Hands On Blockchain Security Risk BCT SS V
Implementing Blockchain Cybersecurity Risks Mitigation Hands On Blockchain Security Risk BCT SS VThe following slide illustrates some blockchain cybersecurity risk management techniques to manage accessibility and ensure data security. It includes elements such as reduce, avoid, accepts and transfer, etc. Present the topic in a bit more detail with this Implementing Blockchain Cybersecurity Risks Mitigation Hands On Blockchain Security Risk BCT SS V. Use it as a tool for discussion and navigation on Reduce, Accept, Avoid. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Importance Of Cybersecurity In Blockchain Technology Hands On Blockchain Security Risk BCT SS V
Importance Of Cybersecurity In Blockchain Technology Hands On Blockchain Security Risk BCT SS VThe following slide highlights how blockchain cybersecurity is important to boost security and prevent cyberattacks. It includes elements such as decentralized architecture, immutable records, public key cryptography, smart contracts, etc. Introducing Importance Of Cybersecurity In Blockchain Technology Hands On Blockchain Security Risk BCT SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Decentralized Architecture, Public Key Cryptography, Smart Contracts, using this template. Grab it now to reap its full benefits.
-
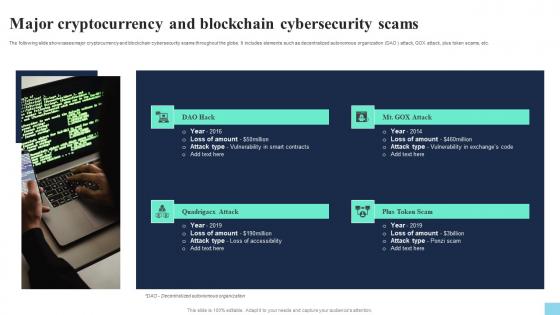 Major Cryptocurrency And Blockchain Cybersecurity Scams Hands On Blockchain Security Risk BCT SS V
Major Cryptocurrency And Blockchain Cybersecurity Scams Hands On Blockchain Security Risk BCT SS VThe following slide showcases major cryptocurrency and blockchain cybersecurity scams throughout the globe. It includes elements such as decentralized autonomous organization DAO attack, GOX attack, plus token scams, etc. Increase audience engagement and knowledge by dispensing information using Major Cryptocurrency And Blockchain Cybersecurity Scams Hands On Blockchain Security Risk BCT SS V. This template helps you present information on four stages. You can also present information on Attack Hack, Attack, Plus Token Scam using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
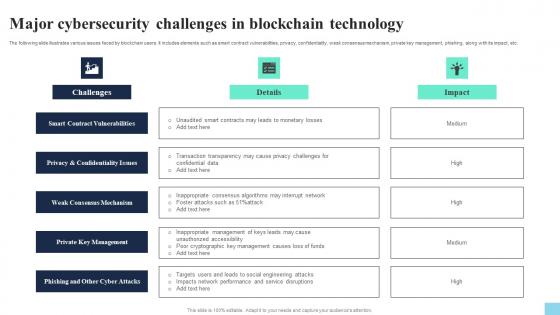 Major Cybersecurity Challenges In Blockchain Technology Hands On Blockchain Security Risk BCT SS V
Major Cybersecurity Challenges In Blockchain Technology Hands On Blockchain Security Risk BCT SS VThe following slide illustrates various issues faced by blockchain users. It includes elements such as smart contract vulnerabilities, privacy, confidentiality, weak consensus mechanism, private key management, phishing, along with its impact, etc. Introducing Major Cybersecurity Challenges In Blockchain Technology Hands On Blockchain Security Risk BCT SS V to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Smart Contract Vulnerabilities, Weak Consensus Mechanism, Private Key Management, using this template. Grab it now to reap its full benefits.
-
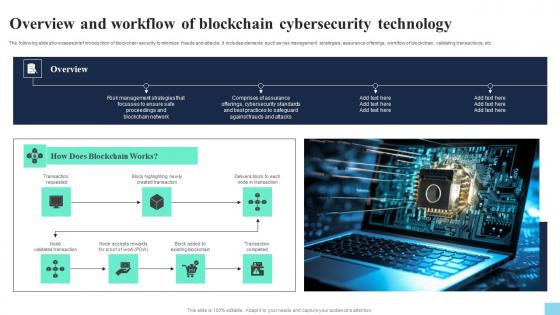 Overview And Workflow Of Blockchain Cybersecurity Technology Hands On Blockchain Security Risk BCT SS V
Overview And Workflow Of Blockchain Cybersecurity Technology Hands On Blockchain Security Risk BCT SS VThe following slide showcases brief introduction of blockchain security to minimize frauds and attacks. It includes elements such as risk management strategies, assurance offerings, workflow of blockchain, validating transactions, etc. Increase audience engagement and knowledge by dispensing information using Overview And Workflow Of Blockchain Cybersecurity Technology Hands On Blockchain Security Risk BCT SS V. This template helps you present information on seven stages. You can also present information on Transaction Requested, Created Transaction, Existing Blockchain using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
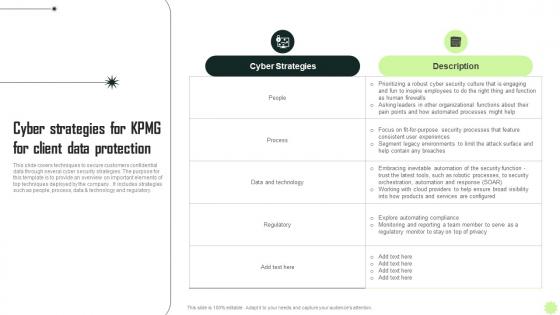 Cyber Strategies For KPMG For Client KPMG Operational And Marketing Strategy SS V
Cyber Strategies For KPMG For Client KPMG Operational And Marketing Strategy SS VThis slide covers techniques to secure customers confidential data through several cyber security strategies. The purpose for this template is to provide an overview on important elements of top techniques deployed by the company. It includes strategies such as people, process, data and technology and regulatory. Present the topic in a bit more detail with this Cyber Strategies For KPMG For Client KPMG Operational And Marketing Strategy SS V. Use it as a tool for discussion and navigation on Strategies, Protection, Data. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Other Cyber Strategies Of KPMG For Client KPMG Operational And Marketing Strategy SS V
Other Cyber Strategies Of KPMG For Client KPMG Operational And Marketing Strategy SS VThis slide covers cyber strategies to protect KPMG customer data protection. The purpose of this template is to provide an overview on top techniques to be implemented to save clients data. It includes strategies such as developing comprehensive understanding of cyber threat landscape, implementing risk based approach, establishing robust security governance framework, etc. Increase audience engagement and knowledge by dispensing information using Other Cyber Strategies Of KPMG For Client KPMG Operational And Marketing Strategy SS V. This template helps you present information on five stages. You can also present information on Developing, Implementing, Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyberbullying Online Harassment In Powerpoint And Google Slides Cpb
Cyberbullying Online Harassment In Powerpoint And Google Slides CpbPresenting our Cyberbullying Online Harassment In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases six stages. It is useful to share insightful information on Cyberbullying Online Harassment This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Assessing Multiple Platforms For Cyber Security Digital Transformation Strategies To Integrate DT SS
Assessing Multiple Platforms For Cyber Security Digital Transformation Strategies To Integrate DT SSThis slide provides glimpse about comparative analysis of cyber security and risk management tools that can help the business in mitigating cyber threats. It includes key features, pricing, deployment, etc. Deliver an outstanding presentation on the topic using this Assessing Multiple Platforms For Cyber Security Digital Transformation Strategies To Integrate DT SS. Dispense information and present a thorough explanation of Management Software, Cybersecurity, Supported Platforms using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cybersecurity And Risk Management Overview Digital Transformation Strategies To Integrate DT SS
Cybersecurity And Risk Management Overview Digital Transformation Strategies To Integrate DT SSThis slide provides glimpse about summary of cybersecurity and risk management that can help businesses to handle any such incidents. It includes key considerations such as risk assessment, threat intelligence, etc. Increase audience engagement and knowledge by dispensing information using Cybersecurity And Risk Management Overview Digital Transformation Strategies To Integrate DT SS. This template helps you present information on seven stages. You can also present information on Overview, Digital Transformation, Key Considerations using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
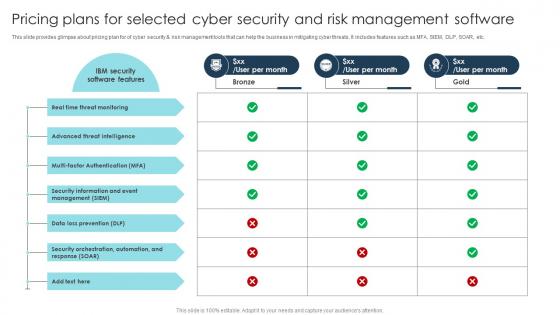 Pricing Plans For Selected Cyber Security Digital Transformation Strategies To Integrate DT SS
Pricing Plans For Selected Cyber Security Digital Transformation Strategies To Integrate DT SSPresent the topic in a bit more detail with this Pricing Plans For Selected Cyber Security Digital Transformation Strategies To Integrate DT SS. Use it as a tool for discussion and navigation on Software Features, Real Time, Threat Intelligence. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Use Case Cybersecurity And Risk Management Digital Transformation Strategies To Integrate DT SS
Use Case Cybersecurity And Risk Management Digital Transformation Strategies To Integrate DT SSThis slide provides glimpse about business case that help businesses take various cybersecurity measures and mitigate risks. It includes introduction, challenges, initiatives, etc. Introducing Use Case Cybersecurity And Risk Management Digital Transformation Strategies To Integrate DT SS to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Data Protection, Industry Standards, Global Technology, using this template. Grab it now to reap its full benefits.
-
 Classify Incident Report Template For Cyber Security Analysis
Classify Incident Report Template For Cyber Security AnalysisThis slide exhibits cyber report template categorization for ensuring quick and effective understanding of incident nature, impact and implication. It includes elements such as Michigan, sysnets security, techtargets and thycotics template. Presenting our set of slides with Classify Incident Report Template For Cyber Security Analysis. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Michigan Template, Sysnets Security Template, Thycotics Template.
-
 Cyber Incident Icon For Process Improvement Report Template
Cyber Incident Icon For Process Improvement Report TemplateIntroducing our premium set of slides with Cyber Incident Icon For Process Improvement Report Template. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cyber Incident, Process, Improvement. So download instantly and tailor it with your information.
-
 Cyber Incident Report Checklist Template For Decision Making
Cyber Incident Report Checklist Template For Decision MakingThis slide covers cyber report checklist for providing structured and standardized framework for documenting cybersecurity incidents. It includes aspects such as tasks, authorized head, relevant, irrelevant and notes. Presenting our well structured Cyber Incident Report Checklist Template For Decision Making. The topics discussed in this slide are Authorized Head, Irrelevant, Relevant. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Cyber Incident Report Icon For Documentation And Template
Cyber Incident Report Icon For Documentation And TemplateIntroducing our Cyber Incident Report Icon For Documentation And Template set of slides. The topics discussed in these slides are Documentation, Cyber Incident Report. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
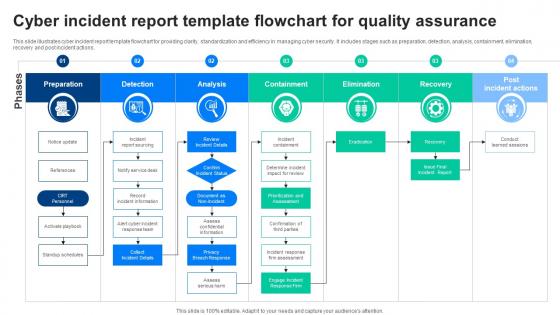 Cyber Incident Report Template Flowchart For Quality Assurance
Cyber Incident Report Template Flowchart For Quality AssuranceThis slide illustrates cyber incident report template flowchart for providing clarity, standardization and efficiency in managing cyber security. It includes stages such as preparation, detection, analysis, containment, elimination, recovery and post incident actions. Introducing our Cyber Incident Report Template Flowchart For Quality Assurance set of slides. The topics discussed in these slides are Assurance, Containment, Elimination. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
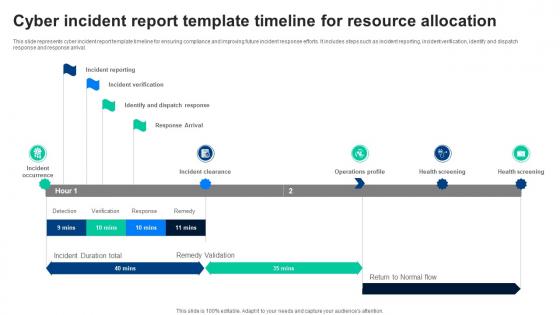 Cyber Incident Report Template Timeline For Resource Allocation
Cyber Incident Report Template Timeline For Resource AllocationThis slide represents cyber incident report template timeline for ensuring compliance and improving future incident response efforts. It includes steps such as incident reporting, incident verification, identify and dispatch response and response arrival. Presenting our well structured Cyber Incident Report Template Timeline For Resource Allocation. The topics discussed in this slide are Timeline, Resource, Allocation. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Essential Steps For Automated Cyber Incident Report Template
Essential Steps For Automated Cyber Incident Report TemplateThis slide highlights steps of cyber incident report template providing necessary information to handle cyber attacks better and efficiently. It includes phases such as record, remediate and report. Presenting our set of slides with Essential Steps For Automated Cyber Incident Report Template. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Record, Remediate, Essential.
-
 Gather Information Template Icon For Cyber Incident Report
Gather Information Template Icon For Cyber Incident ReportIntroducing our premium set of slides with Gather Information Template Icon For Cyber Incident Report. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Information, Cyber Incident Report. So download instantly and tailor it with your information.
-
 Implement Cyber Incident Report Template Phases For Risk Mitigation
Implement Cyber Incident Report Template Phases For Risk MitigationThis slide demonstrates cyber report template phases for supporting incidents systematically by using appropriate actions to follow consistent process. It includes stages such as preparation, detection and analysis, containment, elimination, recovery, etc. Presenting our set of slides with Implement Cyber Incident Report Template Phases For Risk Mitigation. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Detection And Analysis, Containment, Elimination.
-
 Key Constituents Of Cyber Incident Report Template
Key Constituents Of Cyber Incident Report TemplateThis slide represents cyber incident purpose to detect, respond, mitigate effectively while promoting culture of security. It includes basis such as maintain regulatory compliance, improve risk and threat awareness, build trust with stakeholders, protect business relationships, etc. Introducing our premium set of slides with Key Constituents Of Cyber Incident Report Template. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Maintain Regulatory Compliance, Improve Risk And Threat Awareness, Protect Business Relationships. So download instantly and tailor it with your information.
-
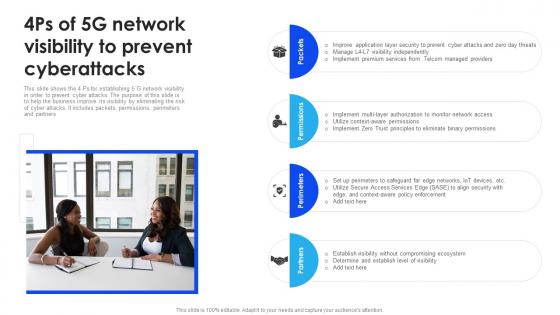 4Ps Of 5G Network Visibility To Prevent Cyberattacks
4Ps Of 5G Network Visibility To Prevent CyberattacksThis slide shows the 4 Ps for establishing 5 G network visibility in order to prevent cyber attacks. The purpose of this slide is to help the business improve its visibility by eliminating the risk of cyber attacks. It includes packets, permissions, perimeters and partners Presenting our set of slides with 4Ps Of 5G Network Visibility To Prevent Cyberattacks. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Application, Services, Network.
-
 5G Cybersecurity Icon For Preventing Digital Attacks
5G Cybersecurity Icon For Preventing Digital AttacksIntroducing our 5G Cybersecurity Icon For Preventing Digital Attacks set of slides. The topics discussed in these slides are Preventing, Digital, Cybersecurity. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 5G Cybersecurity Icon For Safeguarding Network
5G Cybersecurity Icon For Safeguarding NetworkPresenting our well structured 5G Cybersecurity Icon For Safeguarding Network. The topics discussed in this slide are Safeguarding, Network, Cybersecurity. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
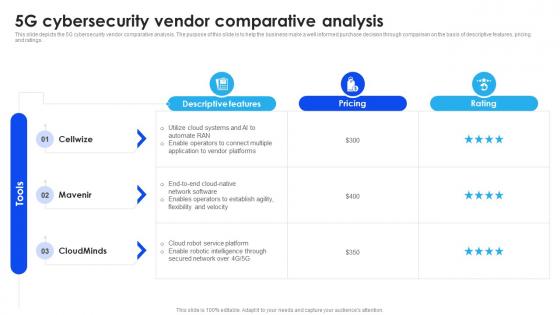 5G Cybersecurity Vendor Comparative Analysis
5G Cybersecurity Vendor Comparative AnalysisThis slide depicts the 5G cybersecurity vendor comparative analysis. The purpose of this slide is to help the business make a well informed purchase decision through comparison on the basis of descriptive features, pricing and ratings. Presenting our well structured 5G Cybersecurity Vendor Comparative Analysis. The topics discussed in this slide are Purchase, Business, Comparative. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
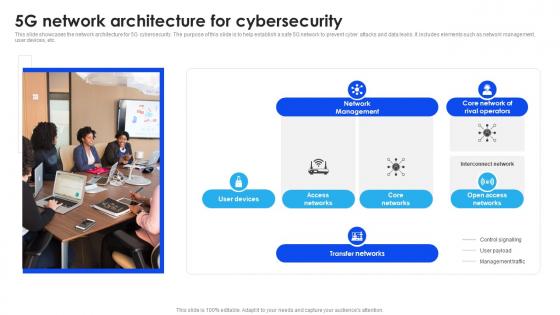 5G Network Architecture For Cybersecurity
5G Network Architecture For CybersecurityThis slide showcases the network architecture for 5G cybersecurity. The purpose of this slide is to help establish a safe 5G network to prevent cyber attacks and data leaks. It includes elements such as network management, user devices, etc. Introducing our premium set of slides with 5G Network Architecture For Cybersecurity. Ellicudate the one stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics likeManagement, Operators, Access. So download instantly and tailor it with your information.
-
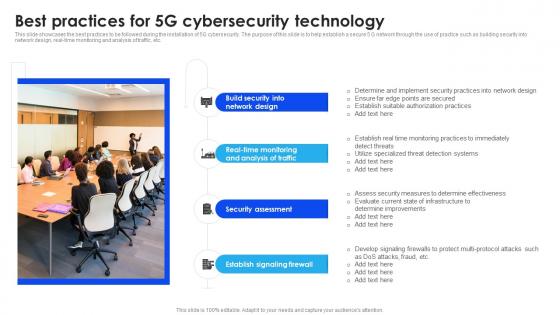 Best Practices For 5G Cybersecurity Technology
Best Practices For 5G Cybersecurity TechnologyThis slide showcases the best practices to be followed during the installation of 5G cybersecurity. The purpose of this slide is to help establish a secure 5 G network through the use of practice such as building security into network design, real time monitoring and analysis of traffic, etc. Presenting our set of slides with Best Practices For 5G Cybersecurity Technology. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Network, Monitoring, Assessment.
-
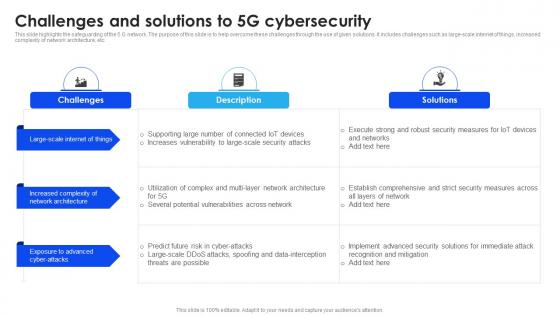 Challenges And Solutions To 5G Cybersecurity
Challenges And Solutions To 5G CybersecurityThis slide highlights the safeguarding of the 5 G network. The purpose of this slide is to help overcome these challenges through the use of given solutions. It includes challenges such as large scale internet of things, increased complexity of network architecture, etc. Introducing our Challenges And Solutions To 5G Cybersecurity set of slides. The topics discussed in these slides are Internet, Architecture, Advanced. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
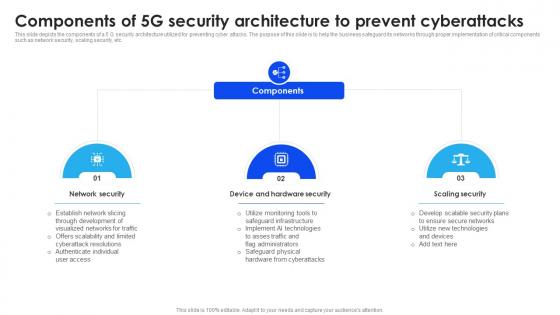 Components Of 5G Security Architecture To Prevent Cyberattacks
Components Of 5G Security Architecture To Prevent CyberattacksThis slide depicts the components of a 5 G security architecture utilized for preventing cyber attacks. The purpose of this slide is to help the business safeguard its networks through proper implementation of critical components such as network security, scaling security, etc. Presenting our set of slides with Components Of 5G Security Architecture To Prevent Cyberattacks. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Network, Hardware, Security.
-
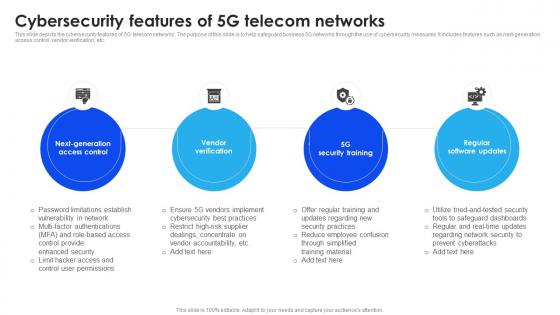 Cybersecurity Features Of 5G Telecom Networks
Cybersecurity Features Of 5G Telecom NetworksThis slide depicts the cybersecurity features of 5G telecom networks. The purpose of this slide is to help safeguard business 5G networks through the use of cybersecurity measures. It includes features such as next generation access control, vendor verification, etc. Introducing our premium set of slides with Cybersecurity Features Of 5G Telecom Networks. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Access, Verification, Training. So download instantly and tailor it with your information.
-
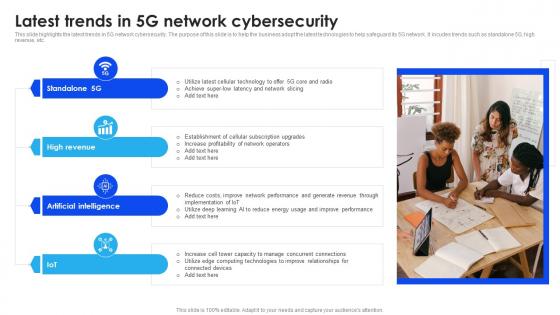 Latest Trends In 5G Network Cybersecurity
Latest Trends In 5G Network CybersecurityThis slide highlights the latest trends in 5G network cybersecurity. The purpose of this slide is to help the business adopt the latest technologies to help safeguard its 5G network. It incudes trends such as standalone 5G, high revenue, etc. Introducing our premium set of slides with Latest Trends In 5G Network Cybersecurity. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Technology, Network, Operators. So download instantly and tailor it with your information.
-
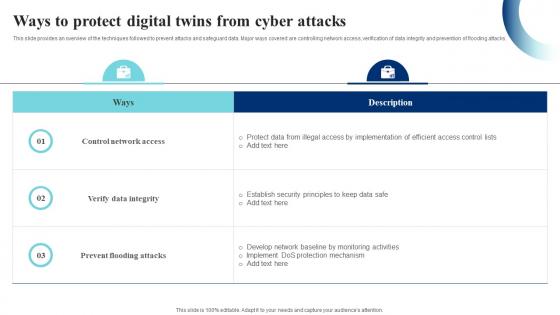 Ways To Protect Digital Twins From Cyber Attacks IoT Digital Twin Technology IOT SS
Ways To Protect Digital Twins From Cyber Attacks IoT Digital Twin Technology IOT SSThis slide provides an overview of the techniques followed to prevent attacks and safeguard data. Major ways covered are controlling network access, verification of data integrity and prevention of flooding attacks. Present the topic in a bit more detail with this Ways To Protect Digital Twins From Cyber Attacks IoT Digital Twin Technology IOT SS. Use it as a tool for discussion and navigation on Control Network Access, Prevent Flooding Attacks, Verify Data Integrity. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Security Internship In Powerpoint And Google Slides Cpb
Cyber Security Internship In Powerpoint And Google Slides CpbPresenting our Cyber Security Internship In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Cyber Security Internship This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Cyber Security Banking Industry In Powerpoint And Google Slides Cpb
Cyber Security Banking Industry In Powerpoint And Google Slides CpbPresenting Cyber Security Banking Industry In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Cyber Security Banking Industry. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Current Trending Technologies Cyber Security Technology Market Overview
Current Trending Technologies Cyber Security Technology Market OverviewThis slide explains Cyber security technology market overview with top players in the year 2021. It also predicts market growth and compound annual growth rate from year 2021 till 2028. Deliver an outstanding presentation on the topic using this Current Trending Technologies Cyber Security Technology Market Overview. Dispense information and present a thorough explanation of Cyber Security Technology, Market Growth, Compound Annual Growth Rate, Business Continuity using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Current Trending Technologies Need For Cyber Security Technology
Current Trending Technologies Need For Cyber Security TechnologyThis slide gives an overview of cyber security technology. It also gives an idea about which industries are most venerable for a cyber attack and why cyber security is needed. Increase audience engagement and knowledge by dispensing information using Current Trending Technologies Need For Cyber Security Technology. This template helps you present information on three stages. You can also present information on Cyber Security Technology, Prevention Of Cybercrime, Protection Of Sensitive Information using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Current Trending Technologies Objectives Of Cyber Security Technology
Current Trending Technologies Objectives Of Cyber Security TechnologyThis slide explains the objectives of cyber security technology such as confidentiality, integrity and availability. It also talks about the three goals and how they collectively ensures the data protection. Introducing Current Trending Technologies Objectives Of Cyber Security Technology to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Confidentiality, Cyber Security Technology, Data Protection, Integrity And Availability, using this template. Grab it now to reap its full benefits.
-
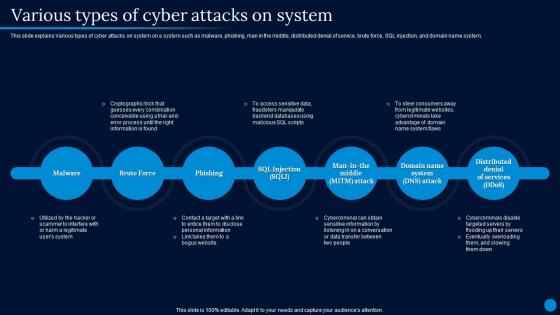 Current Trending Technologies Various Types Of Cyber Attacks On System
Current Trending Technologies Various Types Of Cyber Attacks On SystemThis slide explains Various types of cyber attacks on system on a system such as malware, phishing, man in the middle, distributed denial of service, brute force, SQL injection, and domain name system. Introducing Current Trending Technologies Various Types Of Cyber Attacks On System to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Cyber Attacks On System, Distributed Denial Of Service, Cryptographic Trick, Cybercriminals Disable Targeted Servers, using this template. Grab it now to reap its full benefits.
-
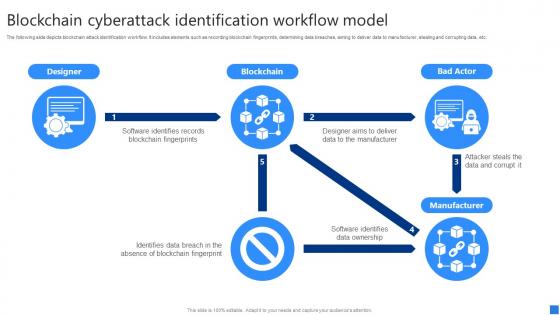 Blockchain Cyberattack Securing Blockchain Transactions A Beginners Guide BCT SS V
Blockchain Cyberattack Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide depicts blockchain attack identification workflow. It includes elements such as recording blockchain fingerprints, determining data breaches, aiming to deliver data to manufacturer, stealing and corrupting data, etc. Present the topic in a bit more detail with this Blockchain Cyberattack Securing Blockchain Transactions A Beginners Guide BCT SS V. Use it as a tool for discussion and navigation on Designer, Blockchain, Bad Actor. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Conducting Blockchain Cybersecurity Securing Blockchain Transactions A Beginners Guide BCT SS V
Conducting Blockchain Cybersecurity Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide showcases blockchain cybersecurity training plan to reduce insider threats. It includes elements such as introduction ,blockchain security risks, smart contracts development, network security, data encryption, incidence response management, etc. Deliver an outstanding presentation on the topic using this Conducting Blockchain Cybersecurity Securing Blockchain Transactions A Beginners Guide BCT SS V. Dispense information and present a thorough explanation of Introduction Blockchain, Blockchain Security Risks, Smart Contracts Development using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Implementing Blockchain Cybersecurity Securing Blockchain Transactions A Beginners Guide BCT SS V
Implementing Blockchain Cybersecurity Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide showcases blockchain cybersecurity threat assessment to determine type and major causes of attacks. It includes elements such as double spending, mining threats, wallet, network, smart contract threats, etc. Introducing Implementing Blockchain Cybersecurity Securing Blockchain Transactions A Beginners Guide BCT SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Reduce, Accept, Transfer, using this template. Grab it now to reap its full benefits.
-
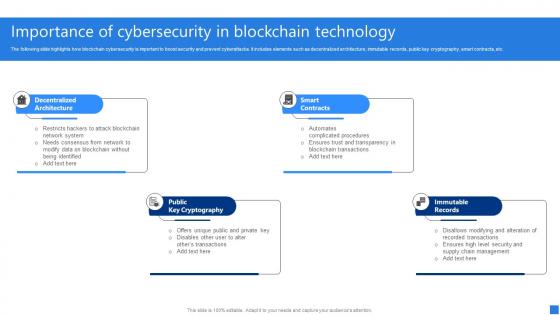 Importance Of Cybersecurity Securing Blockchain Transactions A Beginners Guide BCT SS V
Importance Of Cybersecurity Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide highlights how blockchain cybersecurity is important to boost security and prevent cyberattacks. It includes elements such as decentralized architecture, immutable records, public key cryptography, smart contracts, etc. Increase audience engagement and knowledge by dispensing information using Importance Of Cybersecurity Securing Blockchain Transactions A Beginners Guide BCT SS V. This template helps you present information on four stages. You can also present information on Decentralized Architecture, Public Key Cryptography, Smart Contracts, Immutable Records using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Major Cybersecurity Challenges Securing Blockchain Transactions A Beginners Guide BCT SS V
Major Cybersecurity Challenges Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide illustrates various issues faced by blockchain users. It includes elements such as smart contract vulnerabilities, privacy, confidentiality, weak consensus mechanism, private key management, phishing, along with its impact, etc. Increase audience engagement and knowledge by dispensing information using Major Cybersecurity Challenges Securing Blockchain Transactions A Beginners Guide BCT SS V. This template helps you present information on one stages. You can also present information on Smart Contract Vulnerabilities, Weak Consensus Mechanism, Private Key Management using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
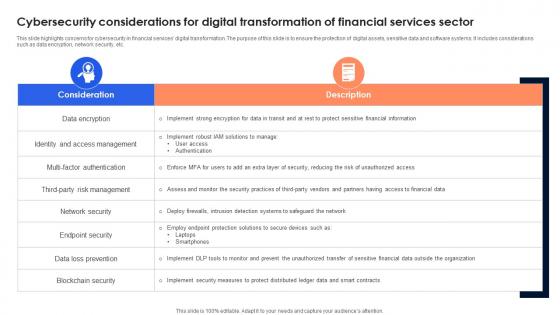 Cybersecurity Considerations For Digital Transformation Of Financial Services Sector
Cybersecurity Considerations For Digital Transformation Of Financial Services SectorThis slide highlights concerns for cybersecurity in financial services digital transformation. The purpose of this slide is to ensure the protection of digital assets, sensitive data and software systems. It includes considerations such as data encryption, network security, etc. Introducing our Cybersecurity Considerations For Digital Transformation Of Financial Services Sector set of slides. The topics discussed in these slides are Consideration, Description. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Coalition Cyber Insurance Review In Powerpoint And Google Slides Cpb
Coalition Cyber Insurance Review In Powerpoint And Google Slides CpbPresenting our Coalition Cyber Insurance Review In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Coalition Cyber Insurance Review This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Agenda Creating Cyber Security Awareness Among Employees
Agenda Creating Cyber Security Awareness Among EmployeesIntroducing Agenda Creating Cyber Security Awareness Among Employees to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Agenda using this template. Grab it now to reap its full benefits.
-
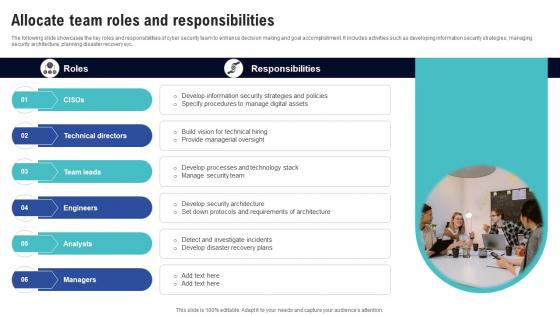 Allocate Team Roles And Responsibilities Creating Cyber Security Awareness
Allocate Team Roles And Responsibilities Creating Cyber Security AwarenessThe following slide showcases the key roles and responsibilities of cyber security team to enhance decision making and goal accomplishment. It includes activities such as developing information security strategies, managing security architecture, planning disaster recovery eyc. Increase audience engagement and knowledge by dispensing information using Allocate Team Roles And Responsibilities Creating Cyber Security Awareness This template helps you present information on Five stages. You can also present information on Technical Directors, Team Leads, Engineers using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
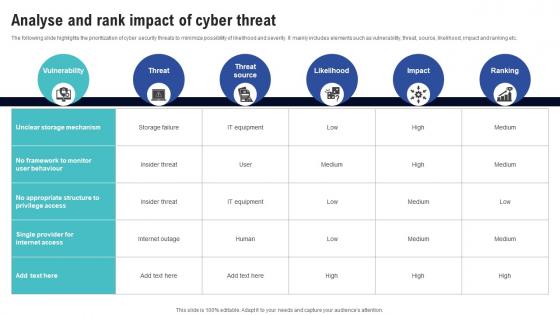 Analyse And Rank Impact Of Cyber Threat Creating Cyber Security Awareness
Analyse And Rank Impact Of Cyber Threat Creating Cyber Security AwarenessThe following slide highlights the prioritization of cyber security threats to minimize possibility of likelihood and severity. It mainly includes elements such as vulnerability, threat, source, likelihood, impact and ranking etc. Present the topic in a bit more detail with this Analyse And Rank Impact Of Cyber Threat Creating Cyber Security Awareness Use it as a tool for discussion and navigation on Likelihood, Impact, Ranking This template is free to edit as deemed fit for your organization. Therefore download it now.
-
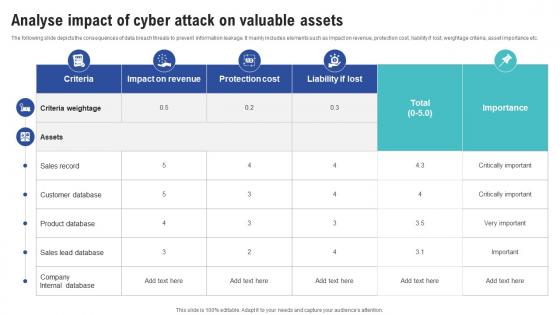 Analyse Impact Of Cyber Attack On Valuable Assets Creating Cyber Security Awareness
Analyse Impact Of Cyber Attack On Valuable Assets Creating Cyber Security AwarenessThe following slide depicts the consequences of data breach threats to prevent information leakage. It mainly includes elements such as impact on revenue, protection cost, liability if lost, weightage criteria, asset importance etc. Deliver an outstanding presentation on the topic using this Analyse Impact Of Cyber Attack On Valuable Assets Creating Cyber Security Awareness Dispense information and present a thorough explanation of Impact On Revenue, Protection Cost using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
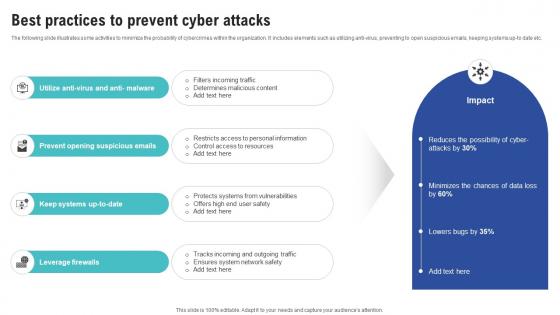 Best Practices To Prevent Cyber Attacks Creating Cyber Security Awareness
Best Practices To Prevent Cyber Attacks Creating Cyber Security AwarenessThe following slide illustrates some activities to minimize the probability of cybercrimes within the organization. It includes elements such as utilizing anti-virus, preventing to open suspicious emails, keeping systems up-to date etc. Introducing Best Practices To Prevent Cyber Attacks Creating Cyber Security Awareness to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Opening Suspicious Emails, Leverage Firewalls using this template. Grab it now to reap its full benefits.