Powerpoint Templates and Google slides for Cyber
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
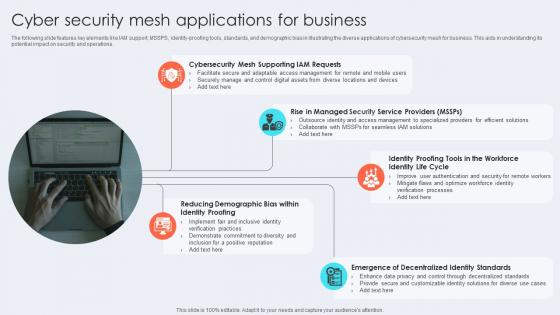 Cyber Security Mesh Applications For Business
Cyber Security Mesh Applications For BusinessThe following slide features key elements like IAM support, MSSPS, identity-proofing tools, standards, and demographic bias in illustrating the diverse applications of cybersecurity mesh for business. This aids in understanding its potential impact on security and operations. Presenting our set of slides with Cyber Security Mesh Applications For Business This exhibits information on Five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Mesh Supporting Iam Requests, Identity Life Cycle, Decentralized Identity Standards
-
 Cyber Security Mesh Architecture
Cyber Security Mesh ArchitectureThe following slide highlights components like centralized dashboard, alerting, investigation, reporting, users, robotics, and processes in the cybersecurity mesh architecture. It aids in illustrating the structure and functionalities of the system. Presenting our well structured Cyber Security Mesh Architecture The topics discussed in this slide are Centralized Dashboard, Centralized Alerting, Centralized Reporting This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
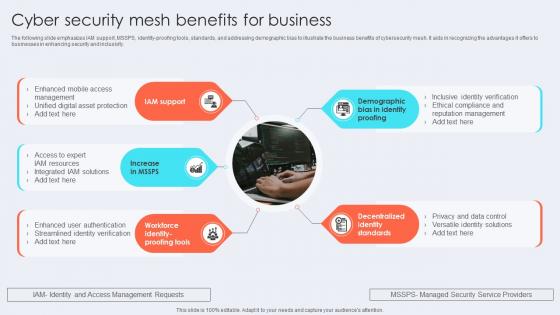 Cyber Security Mesh Benefits For Business
Cyber Security Mesh Benefits For BusinessThe following slide emphasizes IAM support, MSSPS, identity-proofing tools, standards, and addressing demographic bias to illustrate the business benefits of cybersecurity mesh. It aids in recognizing the advantages it offers to businesses in enhancing security and inclusivity. Presenting our set of slides with Cyber Security Mesh Benefits For Business This exhibits information on Five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Iam Support, Identity Standards, Identity Proofing
-
 Cyber Security Mesh Improved Scalability
Cyber Security Mesh Improved ScalabilityIntroducing our Cyber Security Mesh Improved Scalability set of slides. The topics discussed in these slides are Cyber Security Mesh, Improved Scalability. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Four Layers Of Cyber Security Mesh
Four Layers Of Cyber Security MeshThe following slide features essential elements such as security analytics, consolidated policy management, Distributed identity fabric, and unified dashboards to depict the four layers of cybersecurity mesh. This aids in understanding the comprehensive structure and capabilities of cyber mesh. Presenting our set of slides with Four Layers Of Cyber Security Mesh This exhibits information on Four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Posture Management, Distributed Identity Fabric, Consolidated Dashboards
-
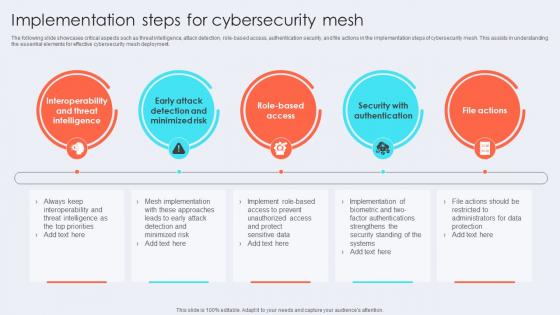 Implementation Steps For Cybersecurity Mesh
Implementation Steps For Cybersecurity MeshThe following slide showcases critical aspects such as threat intelligence, attack detection, role-based access, authentication security, and file actions in the implementation steps of cybersecurity mesh. This assists in understanding the essential elements for effective cybersecurity mesh deployment. Introducing our premium set of slides with Implementation Steps For Cybersecurity Mesh Ellicudate the Five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Threat Intelligence, Minimized Risk, Security With Authentication. So download instantly and tailor it with your information.
-
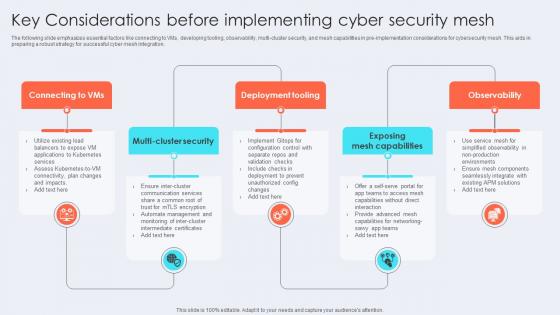 Key Considerations Before Implementing Cyber Security Mesh
Key Considerations Before Implementing Cyber Security MeshThe following slide emphasizes essential factors like connecting to VMs, developing tooling, observability, multi-cluster security, and mesh capabilities in pre-implementation considerations for cybersecurity mesh. This aids in preparing a robust strategy for successful cyber mesh integration. Presenting our set of slides with Key Considerations Before Implementing Cyber Security Mesh This exhibits information on Five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Deployment Tooling, Exposing Mesh Capabilities, Observability
-
 Reducing Attack Surface By Cyber Security Mesh Icon
Reducing Attack Surface By Cyber Security Mesh IconIntroducing our premium set of slides with Reducing Attack Surface By Cyber Security Mesh Icon Ellicudate the Three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Reducing Attack Surface, Cyber Security Mesh Icon. So download instantly and tailor it with your information.
-
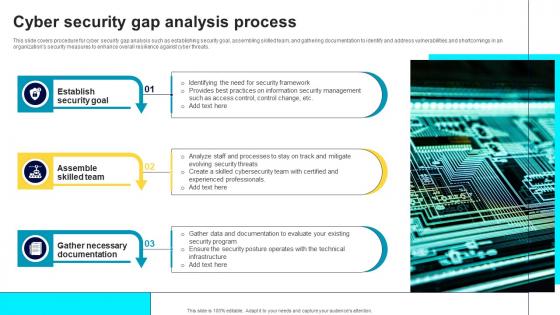 Cyber Security Gap Analysis Process
Cyber Security Gap Analysis ProcessThis slide covers procedure for cyber security gap analysis such as establishing security goal, assembling skilled team, and gathering documentation to identify and address vulnerabilities and shortcomings in an organizations security measures to enhance overall resilience against cyber threats. Presenting our set of slides with name Cyber Security Gap Analysis Process. This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Establish Security Goal, Assemble Skilled Team, Gather Necessary Documentation.
-
 Cyber Security Threat Icon To Prevent Gap
Cyber Security Threat Icon To Prevent GapPresenting our set of slides with name Cyber Security Threat Icon To Prevent Gap. This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cyber Security Threat, Icon Prevent Gap.
-
 BCP Cybersecurity Icon To Address Information Threats Effectively
BCP Cybersecurity Icon To Address Information Threats EffectivelyPresenting our set of slides with BCP Cybersecurity Icon To Address Information Threats Effectively This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on BCP Cybersecurity, Address Information, Threats Effectively
-
 BCP For Addressing Data Loss Incidents To Enhance Cybersecurity
BCP For Addressing Data Loss Incidents To Enhance CybersecurityThis slide represents business continuity plan BCP that assist companies in addressing multiple cybersecurity issues to enhance data protection and operational efficiency. It includes various components such as potential disasters, probability rating, impact, etc. Introducing our BCP For Addressing Data Loss Incidents To Enhance Cybersecurity set of slides. The topics discussed in these slides are Potential Disaster, Probability Rating, Risk Rating This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 BCP Icon For Enhancing Data Protection And Cybersecurity
BCP Icon For Enhancing Data Protection And CybersecurityPresenting our set of slides with BCP Icon For Enhancing Data Protection And Cybersecurity This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on BCP Icon For Enhancing, Data Protection, Cybersecurity
-
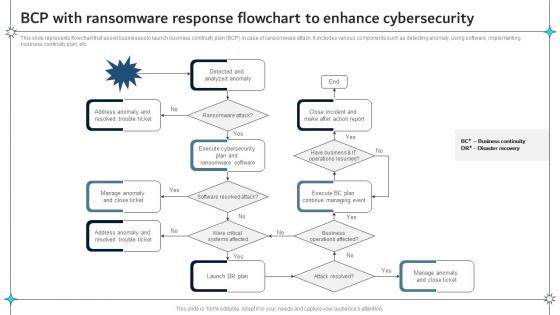 BCP With Ransomware Response Flowchart To Enhance Cybersecurity
BCP With Ransomware Response Flowchart To Enhance CybersecurityThis slide represents flowchart that assist businesses to launch business continuity plan BCP in case of ransomware attack. It includes various components such as detecting anomaly, using software, implementing business continuity plan, etc. Introducing our BCP With Ransomware Response Flowchart To Enhance Cybersecurity set of slides. The topics discussed in these slides are Business Continuity, Ransomware Response, Flowchart This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Best Practices To Improve Cybersecurity In BCP For Data Protection
Best Practices To Improve Cybersecurity In BCP For Data ProtectionThis slide represents various best practices that helps businesses in improving cybersecurity against online data threats affecting business continuity. It includes practices such as using VPN, Training employees, backing up companies data, etc. Presenting our set of slides with Best Practices To Improve Cybersecurity In BCP For Data Protection This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Continuity Software, Backup Company, Train Employees
-
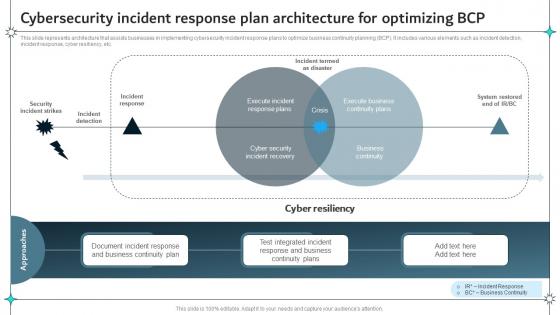 Cybersecurity Incident Response Plan Architecture For Optimizing BCP
Cybersecurity Incident Response Plan Architecture For Optimizing BCPThis slide represents architecture that assists businesses in implementing cybersecurity incident response plans to optimize business continuity planning BCP. It includes various elements such as incident detection, incident response, cyber resiliency, etc. Introducing our Cybersecurity Incident Response Plan Architecture For Optimizing BCP set of slides. The topics discussed in these slides are Cyber Resiliency, Incident Detection, System Restored This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
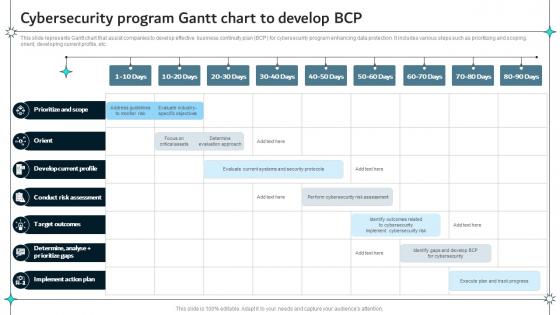 Cybersecurity Program Gantt Chart To Develop BCP
Cybersecurity Program Gantt Chart To Develop BCPThis slide represents Gantt chart that assist companies to develop effective business continuity plan BCP for cybersecurity program enhancing data protection. It includes various steps such as prioritizing and scoping, orient, developing current profile, etc. Presenting our well structured Cybersecurity Program Gantt Chart To Develop BCP The topics discussed in this slide are Develop Current Profile, Conduct Risk Assessment This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Cybersecurity Training Schedule For Enhancing BCP
Cybersecurity Training Schedule For Enhancing BCPThis slide represents an action plan that assists companies in providing effective training to their employees on cybersecurity for enhancing business continuity. It includes various components such as courses, details, hours, deadlines, platform, cost, etc. Introducing our Cybersecurity Training Schedule For Enhancing BCP set of slides. The topics discussed in these slides are Cybersecurity Training, Schedule For Enhancing This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Implementing Cybersecurity In BCP For Enhancing Risk Protection
Implementing Cybersecurity In BCP For Enhancing Risk ProtectionThis slide represents process to implement cybersecurity in business continuity planning BCP for improving company data protection from cyber risks. It includes steps such as conducting business impact analysis, developing risk assessment, maintaining total vison, etc. Presenting our set of slides with Implementing Cybersecurity In BCP For Enhancing Risk Protection This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Maintain Total Vision, Risk Management, Implement Controls
-
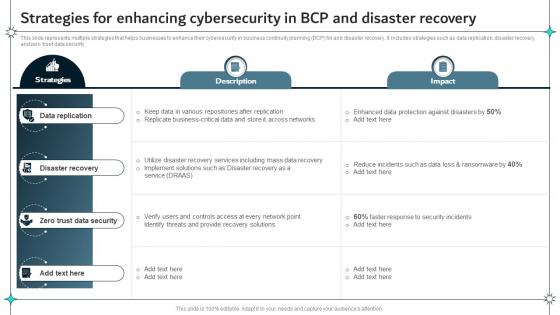 Strategies For Enhancing Cybersecurity In BCP And Disaster Recovery
Strategies For Enhancing Cybersecurity In BCP And Disaster RecoveryThis slide represents multiple strategies that helps businesses to enhance their cybersecurity in business continuity planning BCP for and disaster recovery. It includes strategies such as data replication, disaster recovery, and zero trust data security. Introducing our Strategies For Enhancing Cybersecurity In BCP And Disaster Recovery set of slides. The topics discussed in these slides are Data Replication, Disaster Recovery, Trust Data Security This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Future Application Of AI In Cybersecurity Icon
Future Application Of AI In Cybersecurity IconPresenting our set of slides with name Future Application Of AI In Cybersecurity Icon. This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Future Application, AI In Cybersecurity Icon.
-
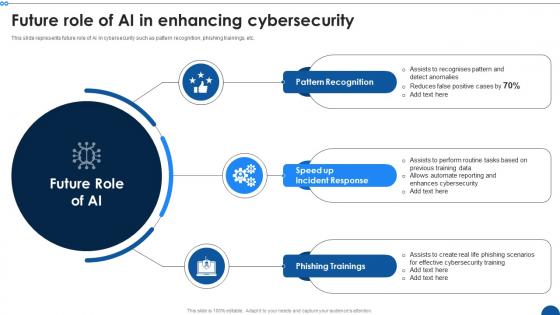 Future Role Of AI In Enhancing Cybersecurity
Future Role Of AI In Enhancing CybersecurityThis slide represents future role of Ai in cybersecurity such as pattern recognition, phishing trainings, etc. Presenting our set of slides with name Future Role Of AI In Enhancing Cybersecurity. This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Pattern Recognition, Speed Up Incident Response, Phishing Trainings.
-
 Addressing Challenges For Enhancing SCADA System Cybersecurity
Addressing Challenges For Enhancing SCADA System CybersecurityThis slide represents various strategies that assist IT companies in mitigating challenges related to SCADA system cybersecurity and enhancing operational efficiency. It includes challenges such as monitoring issues, poor training, etc. Presenting our set of slides with Addressing Challenges For Enhancing SCADA System Cybersecurity This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on This slide represents various strategies that assist IT companies in mitigating challenges related to SCADA system cybersecurity and enhancing operational efficiency. It includes challenges such as monitoring issues, poor training, etc.
-
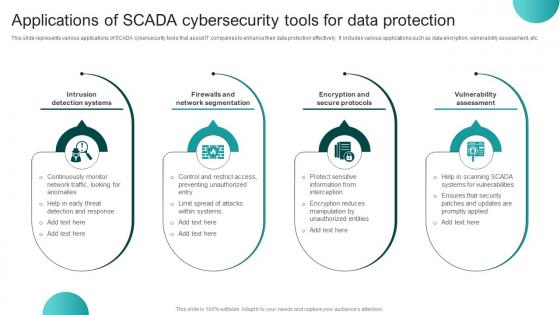 Applications Of SCADA Cybersecurity Tools For Data Protection
Applications Of SCADA Cybersecurity Tools For Data ProtectionThis slide represents various applications of SCADA cybersecurity tools that assist IT companies to enhance their data protection effectively. It includes various applications such as data encryption, vulnerability assessment, etc. Introducing our premium set of slides with Applications Of SCADA Cybersecurity Tools For Data Protection Ellicudate the Four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Intrusion Detection Systems, Firewalls And Network Segmentation, Encryption And Secure Protocols. So download instantly and tailor it with your information.
-
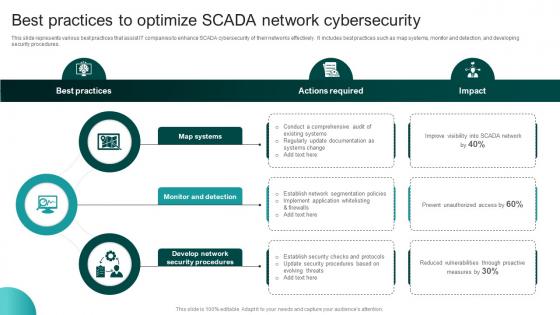 Best Practices To Optimize SCADA Network Cybersecurity
Best Practices To Optimize SCADA Network CybersecurityThis slide represents various best practices that assist IT companies to enhance SCADA cybersecurity of their networks effectively. It includes best practices such as map systems, monitor and detection, and developing security procedures. Presenting our set of slides with Best Practices To Optimize SCADA Network Cybersecurity This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Security Procedures, Monitor And Detection, Map Systems
-
 Checklist To Enhance Cyber Security Of SCADA Networks
Checklist To Enhance Cyber Security Of SCADA NetworksThis slide represents checklist that assist IT companies to enhance their SCADA networks cyber security for improving data protection. It includes various elements such as recognizing connections, disconnecting irrelevant networks, etc. Introducing our Checklist To Enhance Cyber Security Of SCADA Networks set of slides. The topics discussed in these slides are Essential Connections, Inadvertent Disclosure, SCADA Network This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
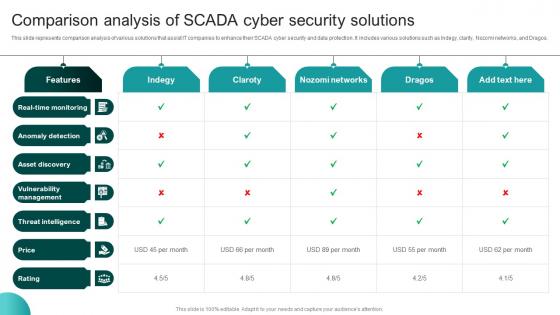 Comparison Analysis Of SCADA Cyber Security Solutions
Comparison Analysis Of SCADA Cyber Security SolutionsThis slide represents comparison analysis of various solutions that assist IT companies to enhance their SCADA cyber security and data protection. It includes various solutions such as Indegy, clarity, Nozomi networks, and Dragos. Presenting our well structured Comparison Analysis Of SCADA Cyber Security Solutions The topics discussed in this slide are Anomaly Detection, Asset Discovery, Vulnerability Management. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Data Encryption Icon For Enhancing SCADA Cybersecurity
Data Encryption Icon For Enhancing SCADA CybersecurityIntroducing our Data Encryption Icon For Enhancing SCADA Cybersecurity set of slides. The topics discussed in these slides are Data Encryption Icon For Enhancing, SCADA Cybersecurity This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Focus Areas To Optimize Cybersecurity Of SCADA Networks
Focus Areas To Optimize Cybersecurity Of SCADA NetworksThis slide represents various focus areas that assist IT companies to enhance their SCADA network cybersecurity and improve information protection. It includes various areas such as network connection, software security, etc. Presenting our well structured Focus Areas To Optimize Cybersecurity Of SCADA Networks The topics discussed in this slide are Network Connections, Security Measure, Area Of Focus. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Framework For SCADA Cyber Security Policy
Framework For SCADA Cyber Security PolicyThis slide represents framework of various policies that assist IT companies to optimize their SCADA cyber security for effective data protection. It includes policies related to data security, platform security, communication security, audit, etc. Introducing our Framework For SCADA Cyber Security Policy set of slides. The topics discussed in these slides are System Security Program, Cyber Security Policy This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
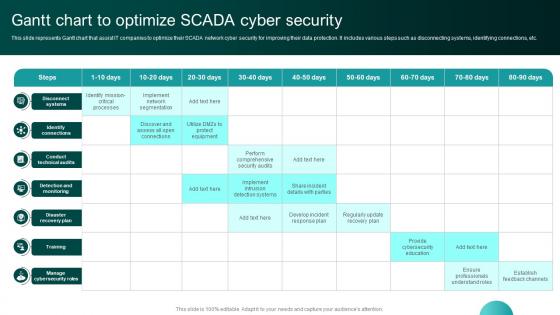 Gantt Chart To Optimize SCADA Cyber Security
Gantt Chart To Optimize SCADA Cyber SecurityThis slide represents Gantt chart that assist IT companies to optimize their SCADA network cyber security for improving their data protection. It includes various steps such as disconnecting systems, identifying connections, etc. Presenting our well structured Gantt Chart To Optimize SCADA Cyber Security The topics discussed in this slide are Identify Connections, Conduct Technical Audits. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
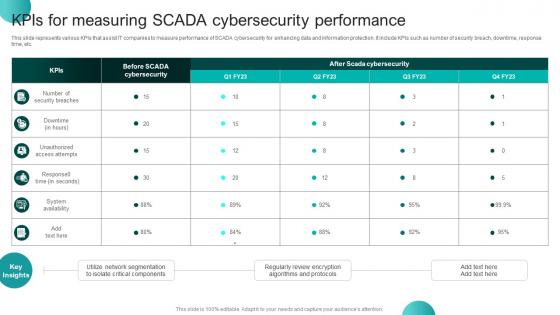 Kpis For Measuring SCADA Cybersecurity Performance
Kpis For Measuring SCADA Cybersecurity PerformanceThis slide represents various KPIs that assist IT companies to measure performance of SCADA cybersecurity for enhancing data and information protection. It include KPIs such as number of security breach, downtime, response time, etc. Introducing our Kpis For Measuring SCADA Cybersecurity Performance set of slides. The topics discussed in these slides are Algorithms And Protocols, Isolate Critical Components This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
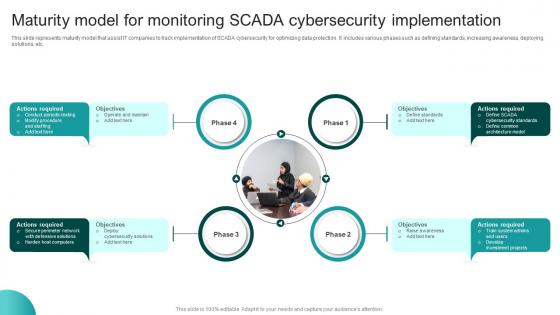 Maturity Model For Monitoring SCADA Cybersecurity Implementation
Maturity Model For Monitoring SCADA Cybersecurity ImplementationThis slide represents maturity model that assist IT companies to track implementation of SCADA cybersecurity for optimizing data protection. It includes various phases such as defining standards, increasing awareness, deploying solutions, etc. Introducing our premium set of slides with Maturity Model For Monitoring SCADA Cybersecurity Implementation Ellicudate the Four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Objectives, Operate And Maintain, Actions Required, Cybersecurity Implementation. So download instantly and tailor it with your information.
-
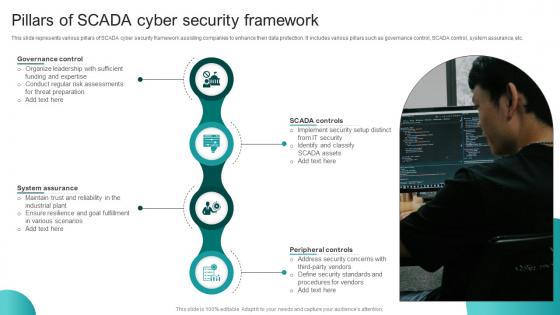 Pillars Of SCADA Cyber Security Framework
Pillars Of SCADA Cyber Security FrameworkThis slide represents various pillars of SCADA cyber security framework assisting companies to enhance their data protection. It includes various pillars such as governance control, SCADA control, system assurance, etc. Presenting our set of slides with Pillars Of SCADA Cyber Security Framework This exhibits information on Four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Governance Control, SCADA Controls, Peripheral Controls
-
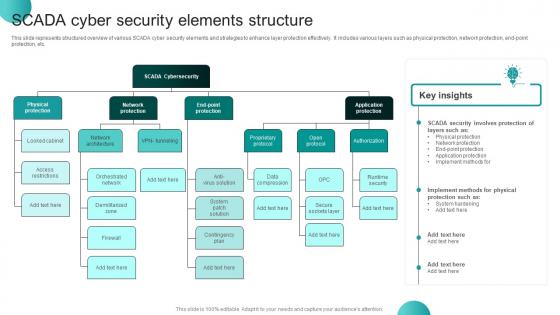 SCADA Cyber Security Elements Structure
SCADA Cyber Security Elements StructureThis slide represents structured overview of various SCADA cyber security elements and strategies to enhance layer protection effectively. It includes various layers such as physical protection, network protection, end-point protection, etc. Presenting our well structured SCADA Cyber Security Elements Structure The topics discussed in this slide are SCADA Security, SCADA Cybersecurity, Application Protection. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 SCADA Cybersecurity Icon For Network Breach Protection
SCADA Cybersecurity Icon For Network Breach ProtectionIntroducing our SCADA Cybersecurity Icon For Network Breach Protection set of slides. The topics discussed in these slides are SCADA Cybersecurity Icon, Network Breach Protection This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 SCADA Cybersecurity Icon For Protecting Digital Infrastructure
SCADA Cybersecurity Icon For Protecting Digital InfrastructureIntroducing our SCADA Cybersecurity Icon For Protecting Digital Infrastructure set of slides. The topics discussed in these slides are SCADA Cybersecurity Icon, Protecting Digital Infrastructure This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Strategies To Mitigate SCADA Network Cybersecurity Threats
Strategies To Mitigate SCADA Network Cybersecurity ThreatsThis slide represents various strategies that assist companies to mitigate various SCADA network threats for enhancing data cybersecurity. It includes various threats such as hackers, malware, and employees. In Presenting our well structured Strategies To Mitigate SCADA Network Cybersecurity Threats The topics discussed in this slide are Hackers, Malware, Employees. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Training Schedule For Enhancing SCADA Cyber Security
Training Schedule For Enhancing SCADA Cyber SecurityThis slide represents training schedule that helps IT companies to plan education sessions on SCADA cyber security for their IT employees effectively. It includes various components such as course, details, duration, etc. Introducing our Training Schedule For Enhancing SCADA Cyber Security set of slides. The topics discussed in these slides are Duration, Platform, Deadline This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Working Model Of SCADA Cybersecurity For Data Protection
Working Model Of SCADA Cybersecurity For Data ProtectionThis slide represents working model of SCADA cybersecurity that assists IT companies to secure their data from vulnerable attacks. It includes various components such as impact analysis, mitigation strategies, etc. Presenting our well structured Working Model Of SCADA Cybersecurity For Data Protection The topics discussed in this slide are Remedial, Prevention, Decision Making. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Simulation Based Cyber Security Training Program
Simulation Based Cyber Security Training ProgramThis slide represents simulation based training program for cyber security awareness including components such as session name, expected impact, duration, etc. Introducing our premium set of slides with Simulation Based Cyber Security Training Program Ellicudate the Four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Customer Data Protection, Attack Mitigation, Duration. So download instantly and tailor it with your information.
-
 Cyber Security Technology Stack Icon
Cyber Security Technology Stack IconIntroducing our Cyber Security Technology Stack Icon set of slides. The topics discussed in these slides are Cyber Security Technology Stack Icon. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Technological Stacks Enhancing Cyber Security
Technological Stacks Enhancing Cyber SecurityThis slide showcases the technological stacks accelerating cyber security which helps an organization to ensure maintaining and setting powerful password and email filtering. It include details such as endpoint detection and response, mobile threat defense, etc. Presenting our set of slides with name Technological Stacks Enhancing Cyber Security This exhibits information on Four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Endpoint Protection Platform, Endpoint Detection And Response
-
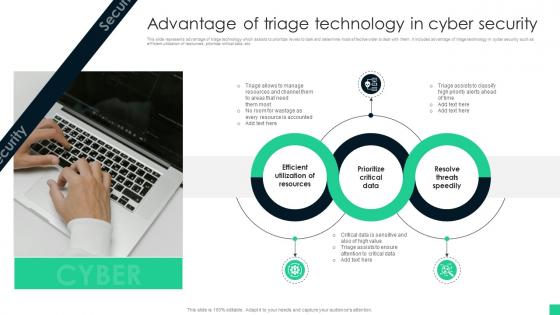 Advantage Of Triage Technology In Cyber Security
Advantage Of Triage Technology In Cyber SecurityThis slide represents advantage of triage technology which assists to prioritize levels to task and determine most effective order to deal with them. It includes advantage of triage technology in cyber security such as efficient utilization of resources, prioritize critical data, etc Presenting our set of slides with name Advantage Of Triage Technology In Cyber Security This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Utilization Of Resources, Prioritize Critical Data, Resolve Threats Speedily
-
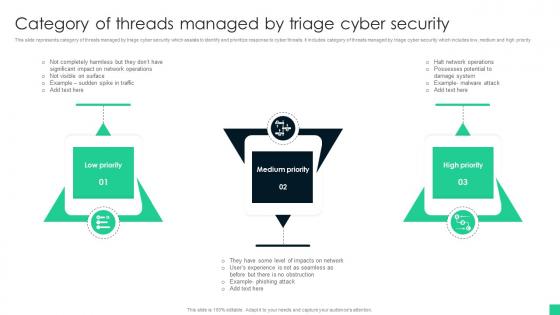 Category Of Threads Managed By Triage Cyber Security
Category Of Threads Managed By Triage Cyber SecurityThis slide represents category of threats managed by triage cyber security which assists to identify and prioritize response to cyber threats. It includes category of threats managed by triage cyber security which includes low, medium and high priority Introducing our premium set of slides with name Category Of Threads Managed By Triage Cyber Security Ellicudate the Three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Low Priority, Medium Priority, High Priority . So download instantly and tailor it with your information.
-
 Checklist To Establish Triage Capability In Cyber Security
Checklist To Establish Triage Capability In Cyber SecurityThis slide represents checklist to establish triage capability in cyber security which assists to analyse threat alerts and effectively response cyber threats. It includes checklist to establish triage capability in cyber security which includes steps such as type of events, skill levels, etc Introducing our Checklist To Establish Triage Capability In Cyber Security set of slides. The topics discussed in these slides are Types Of Events, Skills Levels, Channels Of Support. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
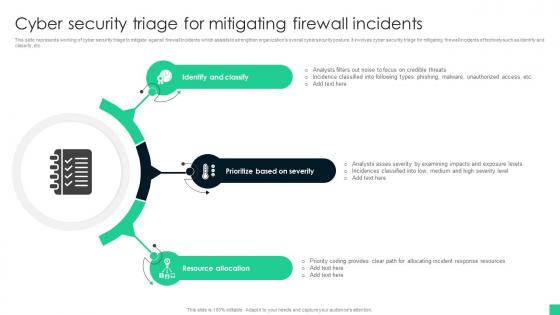 Cyber Security Triage For Mitigating Firewall Incidents
Cyber Security Triage For Mitigating Firewall IncidentsThis slide represents working of cyber security triage to mitigate against firewall incidents which assists to strengthen organizations overall cybersecurity posture. It involves cyber security triage for mitigating firewall incidents effectively such as identify and classify, etc Presenting our set of slides with name Cyber Security Triage For Mitigating Firewall Incidents This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Identify And Classify, Prioritize Based On Severity, Resource Allocation
-
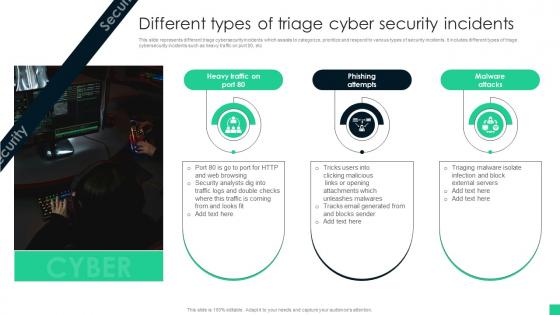 Different Types Of Triage Cyber Security Incidents
Different Types Of Triage Cyber Security IncidentsThis slide represents different triage cybersecurity incidents which assists to categorize, prioritize and respond to various types of security incidents. It includes different types of triage cybersecurity incidents such as heavy traffic on port 80, etc Introducing our premium set of slides with name Different Types Of Triage Cyber Security Incidents Ellicudate the Three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Phishing Attempts, Malware Attacks. So download instantly and tailor it with your information.
-
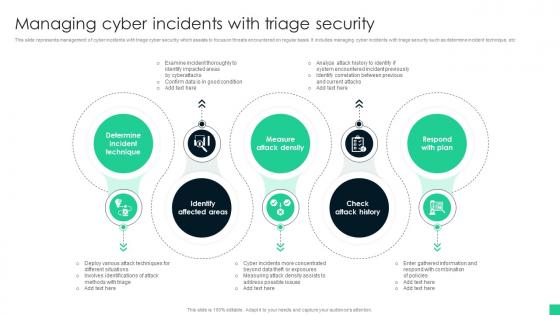 Managing Cyber Incidents With Triage Security
Managing Cyber Incidents With Triage SecurityThis slide represents management of cyber incidents with triage cyber security which assists to focus on threats encountered on regular basis. It includes managing cyber incidents with triage security such as determine incident technique, etc Presenting our set of slides with name Managing Cyber Incidents With Triage Security This exhibits information on Five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Determine Incident Technique, Identify Affected Areas, Measure Attack Density
-
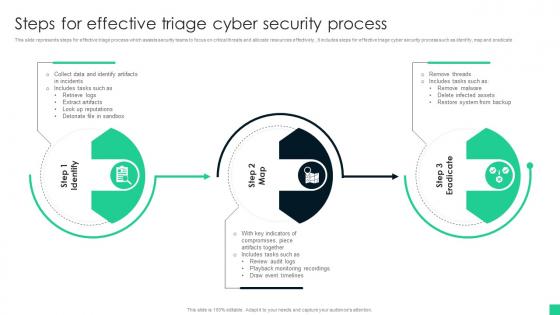 Steps For Effective Triage Cyber Security Process
Steps For Effective Triage Cyber Security ProcessThis slide represents steps for effective triage process which assists security teams to focus on critical threats and allocate resources effectively., It includes steps for effective triage cyber security process such as identify, map and eradicate Introducing our premium set of slides with name Steps For Effective Triage Cyber Security Process Ellicudate the Three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Identify Artifacts, Draw Event Timelines, System From Backup. So download instantly and tailor it with your information.
-
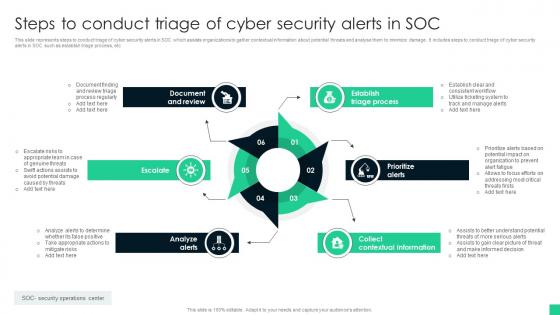 Steps To Conduct Triage Of Cyber Security Alerts In Soc
Steps To Conduct Triage Of Cyber Security Alerts In SocThis slide represents steps to conduct triage of cyber security alerts in SOC which assists organizations to gather contextual information about potential threats and analyse them to minimize damage. It includes steps to conduct triage of cyber security alerts in SOC such as establish triage process, etc Presenting our set of slides with name Steps To Conduct Triage Of Cyber Security Alerts In Soc This exhibits information on Six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Establish Triage Process, Prioritize Alerts, Collect Contextual Information
-
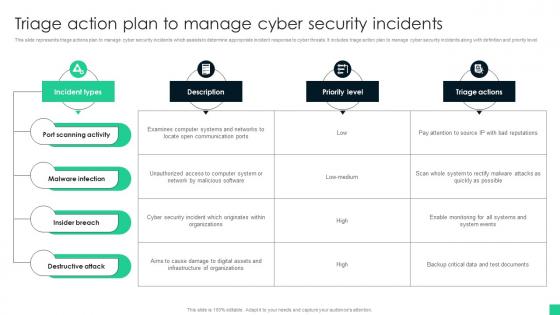 Triage Action Plan To Manage Cyber Security Incidents
Triage Action Plan To Manage Cyber Security IncidentsThis slide represents triage actions plan to manage cyber security incidents which assists to determine appropriate incident response to cyber threats. It includes triage action plan to manage cyber security incidents along with definition and priority level. Introducing our Triage Action Plan To Manage Cyber Security Incidents set of slides. The topics discussed in these slides are Port Scanning Activity, Malware Infection, Insider Breach. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Triage Cyber Security For System Protection Icon
Triage Cyber Security For System Protection IconPresenting our set of slides with name Triage Cyber Security For System Protection Icon This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Triage Cyber Security, System Protection Icon
-
 Triage Cyber Security To Identify Cyber Threats Icon
Triage Cyber Security To Identify Cyber Threats IconIntroducing our premium set of slides with name Triage Cyber Security To Identify Cyber Threats Icon Ellicudate the Three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Triage Cyber Security, Identify Cyber Threats Icon. So download instantly and tailor it with your information.
-
 Triage Process For Cyber Security Icon
Triage Process For Cyber Security IconPresenting our set of slides with name Triage Process For Cyber Security Icon This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Triage Process, Cyber Security Icon
-
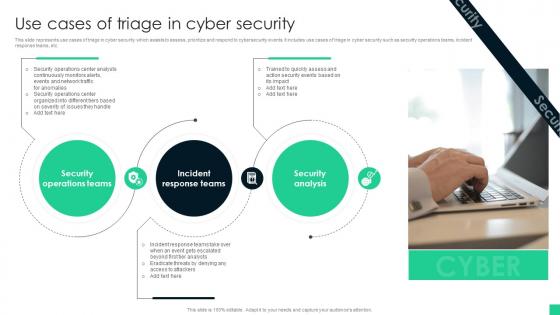 Use Cases Of Triage In Cyber Security
Use Cases Of Triage In Cyber SecurityThis slide represents use cases of triage in cyber security which assists to assess, prioritize and respond to cybersecurity events. It includes use cases of triage in cyber security such as security operations teams, incident response teams, etc. Introducing our premium set of slides with name Use Cases Of Triage In Cyber Security Ellicudate the Three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Security Operations Teams, Incident Response Teams, Security Analysis. So download instantly and tailor it with your information.
-
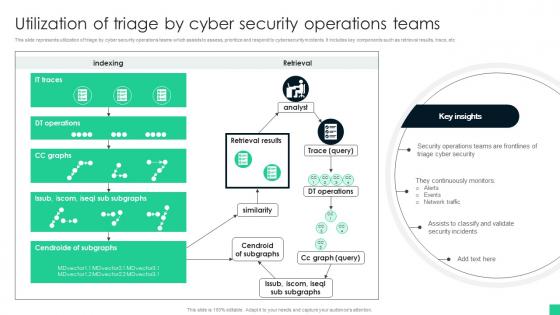 Utilization Of Triage By Cyber Security Operations Teams
Utilization Of Triage By Cyber Security Operations TeamsThis slide represents utilization of triage by cyber security operations teams which assists to assess, prioritize and respond to cybersecurity incidents. It includes key components such as retrieval results, trace, etc Introducing our Utilization Of Triage By Cyber Security Operations Teams set of slides. The topics discussed in these slides are Triage Cyber Security, Network Traffic, Security Incidents. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
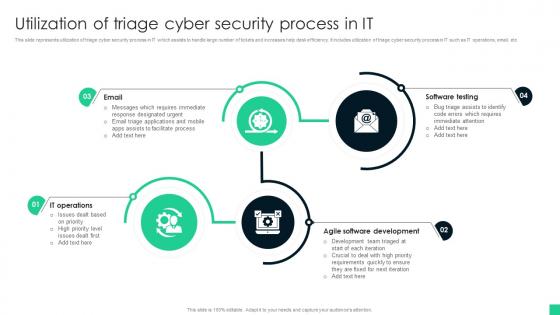 Utilization Of Triage Cyber Security Process In It
Utilization Of Triage Cyber Security Process In ItThis slide represents utilization of triage cyber security process in IT which assists to handle large number of tickets and increases help desk efficiency. It includes utilization of triage cyber security process in IT such as IT operations, email, etc Presenting our set of slides with name Utilization Of Triage Cyber Security Process In It This exhibits information on Four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Software Testing, Agile Software Development, IT Operations
-
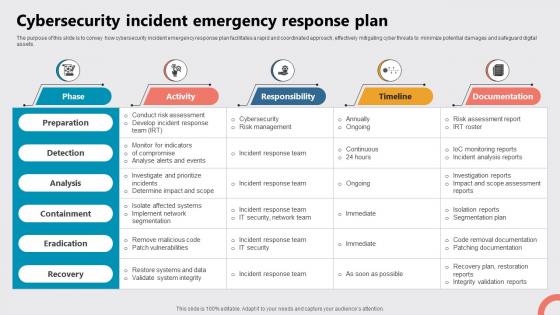 Cybersecurity Incident Emergency Response Plan
Cybersecurity Incident Emergency Response PlanThe purpose of this slide is to convey how cybersecurity incident emergency response plan facilitates a rapid and coordinated approach, effectively mitigating cyber threats to minimize potential damages and safeguard digital assets. Presenting our well structured Cybersecurity Incident Emergency Response Plan. The topics discussed in this slide are Cybersecurity, Risk Management, Incident Response Team, Segmentation Plan. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Emergency Response Plan Icon For Cybersecurity Incidents
Emergency Response Plan Icon For Cybersecurity IncidentsPresenting our set of slides with name Emergency Response Plan Icon For Cybersecurity Incidents. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Emergency Response Plan, Icon For Cybersecurity Incidents.



