Powerpoint Templates and Google slides for Cyber Risk Profiling
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Implementation Of Cyber Security Risk Management Action Plan
Implementation Of Cyber Security Risk Management Action PlanThis slide represents implementation process of cyber security risk management action plan. It further includes steps such as evaluate cyber security risks, prioritize cyber risks Presenting our well structured Implementation Of Cyber Security Risk Management Action Plan. The topics discussed in this slide are Security, Management, Plan. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Agenda For Strategy To Minimize Cyber Attacks Risks Ppt Icon Clipart Images
Agenda For Strategy To Minimize Cyber Attacks Risks Ppt Icon Clipart ImagesIntroducing Agenda For Strategy To Minimize Cyber Attacks Risks Ppt Icon Clipart Images to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Risk Assessment, Cyber Attacks Risks, Attacks Frequency, Cybersecurity Risk, using this template. Grab it now to reap its full benefits.
-
 Icons Slide For Strategy To Minimize Cyber Attacks Risks Ppt Icon Templates
Icons Slide For Strategy To Minimize Cyber Attacks Risks Ppt Icon TemplatesPresenting our premium Icons Slide For Strategy To Minimize Cyber Attacks Risks Ppt Icon Templates set of slides with flexible icons. The icons are designed by our group of professionals. Add these Icons Slide For Strategy To Minimize Cyber Attacks Risks Ppt Icon Templates to your presentation to make it visually appealing. Also, edit them according to your requirement. Download it and captive your audience.
-
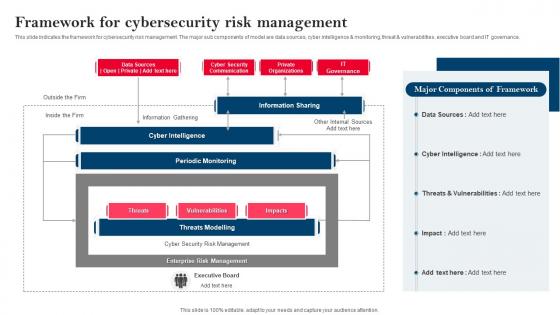 Strategy To Minimize Cyber Attacks Framework For Cybersecurity Risk Management
Strategy To Minimize Cyber Attacks Framework For Cybersecurity Risk ManagementThis slide indicates the framework for cybersecurity risk management. The major sub components of model are data sources, cyber intelligence and monitoring, threat and vulnerabilities, executive board and IT governance. Present the topic in a bit more detail with this Strategy To Minimize Cyber Attacks Framework For Cybersecurity Risk Management. Use it as a tool for discussion and navigation on Information Sharing, Components Of Framework, Framework For Cybersecurity, Risk Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
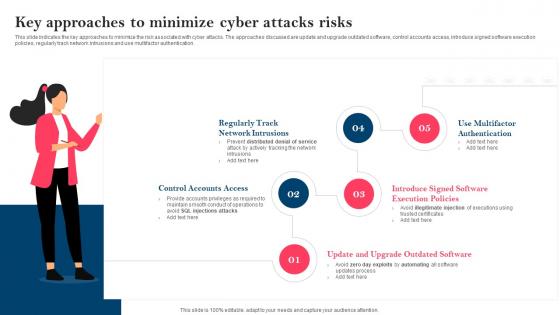 Strategy To Minimize Cyber Attacks Key Approaches To Minimize Cyber Attacks Risks
Strategy To Minimize Cyber Attacks Key Approaches To Minimize Cyber Attacks RisksThis slide indicates the key approaches to minimize the risk associated with cyber attacks. The approaches discussed are update and upgrade outdated software, control accounts access, introduce signed software execution policies, regularly track network intrusions and use multifactor authentication. Increase audience engagement and knowledge by dispensing information using Strategy To Minimize Cyber Attacks Key Approaches To Minimize Cyber Attacks Risks. This template helps you present information on five stages. You can also present information on Control Accounts Access, Software Execution Policies, Multifactor Authentication, Regularly Track Network Intrusions using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
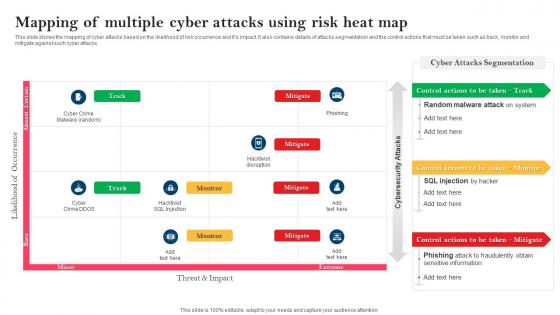 Strategy To Minimize Cyber Attacks Mapping Of Multiple Cyber Attacks Using Risk Heat Map
Strategy To Minimize Cyber Attacks Mapping Of Multiple Cyber Attacks Using Risk Heat MapThis slide shows the mapping of cyber attacks based on the likelihood of risk occurrence and its impact. It also contains details of attacks segmentation and the control actions that must be taken such as track, monitor and mitigate against such cyber attacks. Present the topic in a bit more detail with this Strategy To Minimize Cyber Attacks Mapping Of Multiple Cyber Attacks Using Risk Heat Map. Use it as a tool for discussion and navigation on Random Malware Attack, Phishing Attack, Fraudulently Obtain, Sensitive Information. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
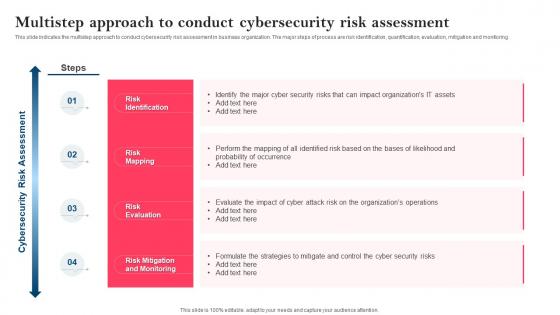 Strategy To Minimize Cyber Attacks Multistep Approach To Conduct Cybersecurity Risk Assessment
Strategy To Minimize Cyber Attacks Multistep Approach To Conduct Cybersecurity Risk AssessmentThis slide indicates the multistep approach to conduct cybersecurity risk assessment in business organization. The major steps of process are risk identification, quantification, evaluation, mitigation and monitoring. Introducing Strategy To Minimize Cyber Attacks Multistep Approach To Conduct Cybersecurity Risk Assessment to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Risk Identification, Risk Mapping, Risk Evaluation, Risk Mitigation And Monitoring, using this template. Grab it now to reap its full benefits.
-
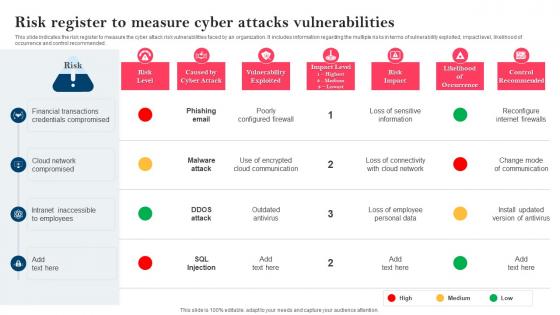 Strategy To Minimize Cyber Attacks Risk Register To Measure Cyber Attacks Vulnerabilities
Strategy To Minimize Cyber Attacks Risk Register To Measure Cyber Attacks VulnerabilitiesThis slide indicates the risk register to measure the cyber attack risk vulnerabilities faced by an organization. It includes information regarding the multiple risks in terms of vulnerability exploited, impact level, likelihood of occurrence and control recommended. Deliver an outstanding presentation on the topic using this Strategy To Minimize Cyber Attacks Risk Register To Measure Cyber Attacks Vulnerabilities. Dispense information and present a thorough explanation of Financial Transactions, Credentials Compromised, Cloud Network Compromised using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
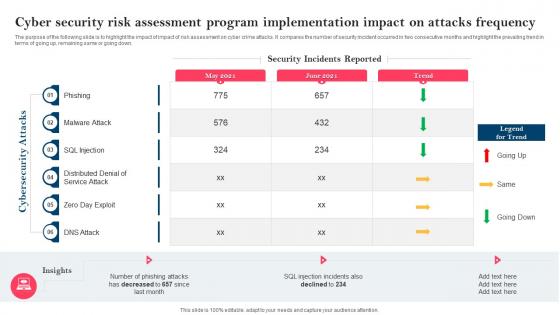 Strategy To Minimize Cyber Attacks Risks Cyber Security Risk Assessment Program Implementation
Strategy To Minimize Cyber Attacks Risks Cyber Security Risk Assessment Program ImplementationThe purpose of the following slide is to highlight the impact of impact of risk assessment on cyber crime attacks. It compares the number of security incident occurred in two consecutive months and highlight the prevailing trend in terms of going up, remaining same or going down. Present the topic in a bit more detail with this Strategy To Minimize Cyber Attacks Risks Cyber Security Risk Assessment Program Implementation. Use it as a tool for discussion and navigation on Cyber Security, Risk Assessment, Program Implementation, Impact On Attacks Frequency. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Strategy To Minimize Cyber Attacks Risks For Table Of Content Ppt Icon Elements
Strategy To Minimize Cyber Attacks Risks For Table Of Content Ppt Icon ElementsIncrease audience engagement and knowledge by dispensing information using Strategy To Minimize Cyber Attacks Risks For Table Of Content Ppt Icon Elements. This template helps you present information on one stages. You can also present information on Cyber Attacks Risks, Cyber Attacks Risk Mitigation, Mitigation Plan using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Table Of Contents For Strategy To Minimize Cyber Attacks Risks
Table Of Contents For Strategy To Minimize Cyber Attacks RisksIntroducing Table Of Contents For Strategy To Minimize Cyber Attacks Risks to increase your presentation threshold. Encompassed with nine stages, this template is a great option to educate and entice your audience. Dispence information on Cyber Attacks Faced By Organization, Risk Heatmap, Risk Register, Mitigation Plan, Cybersecurity Risk Assessment Program, using this template. Grab it now to reap its full benefits.
-
 Third Party Cyber Security Risk Management In Powerpoint And Google Slides Cpb
Third Party Cyber Security Risk Management In Powerpoint And Google Slides CpbPresenting our Third Party Cyber Security Risk Management In Powerpoint And Google Slides Cpb. PowerPoint template design. This PowerPoint slide showcases five stages. It is useful to share insightful information on Third Party Cyber Security Risk Management. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
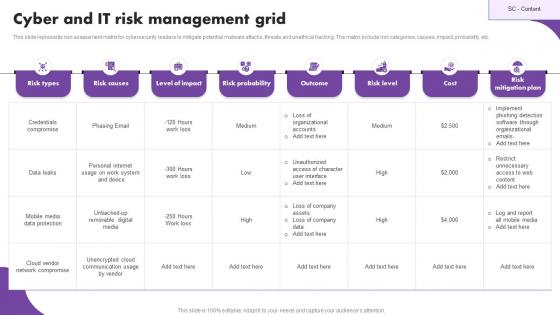 Cyber And IT Risk Management Grid
Cyber And IT Risk Management GridThis slide represents risk assessment matrix for cybersecurity leaders to mitigate potential malware attacks, threats and unethical hacking. The matrix include risk categories, causes, impact, probability, etc. Introducing our Cyber And IT Risk Management Grid set of slides. The topics discussed in these slides are Risk Types, Level Of Impact, Risk Probability. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Adopt Cyber Security Data Policies Cyber Attack Risks Mitigation
Adopt Cyber Security Data Policies Cyber Attack Risks MitigationThe following slide highlights various cyber security policies to manage data control and breach. It includes elements such as network security, data, workstations, remote access etc. Introducing Adopt Cyber Security Data Policies Cyber Attack Risks Mitigation to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Network Security Policies, Data Security Policies, Workstation Policies, using this template. Grab it now to reap its full benefits.
-
 Adopting Strategies By Cyber Attack Type Cyber Attack Risks Mitigation
Adopting Strategies By Cyber Attack Type Cyber Attack Risks MitigationThe following slide depicts the various strategies to manage data control and breach. It includes elements such as attrition, malware, hacking, social tactic, improper usage, train and educate employees, automate identification, data management etc. Present the topic in a bit more detail with this Adopting Strategies By Cyber Attack Type Cyber Attack Risks Mitigation. Use it as a tool for discussion and navigation on Educate Employees, Data Management, Automate Attack Identification. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
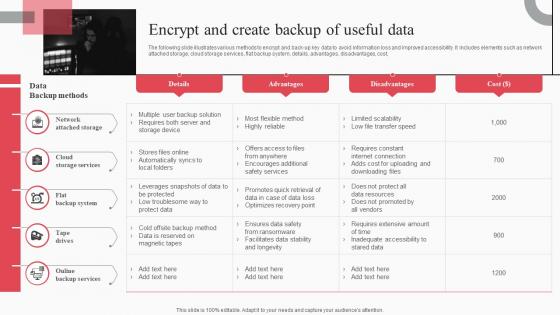 Encrypt And Create Backup Of Useful Data Cyber Attack Risks Mitigation
Encrypt And Create Backup Of Useful Data Cyber Attack Risks MitigationThe following slide illustrates various methods to encrypt and back-up key data to avoid information loss and improved accessibility. It includes elements such as network attached storage, cloud storage services, flat backup system, details, advantages, disadvantages, cost, Deliver an outstanding presentation on the topic using this Encrypt And Create Backup Of Useful Data Cyber Attack Risks Mitigation. Dispense information and present a thorough explanation of Network Attached Storage, Cloud Storage Services, Flat Backup System using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Impact Of Cyber Security Policies And Practices Cyber Attack Risks Mitigation
Impact Of Cyber Security Policies And Practices Cyber Attack Risks MitigationThe following slide focuses on drafting cyber security policies to manage data control and breach. It mainly includes elements such as impact of existing cyber safety policies, mitigation actions, etc. Present the topic in a bit more detail with this Impact Of Cyber Security Policies And Practices Cyber Attack Risks Mitigation. Use it as a tool for discussion and navigation on Inadequate Security Guidelines, Inappropriate Privacy Policies. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
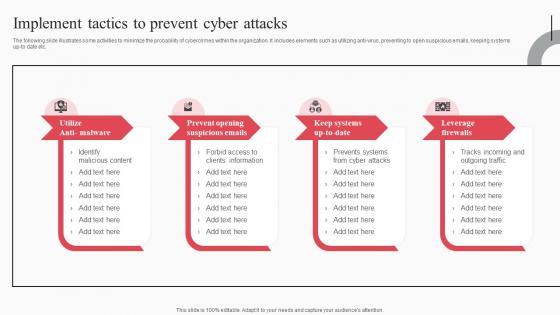 Implement Tactics To Prevent Cyber Attacks Cyber Attack Risks Mitigation
Implement Tactics To Prevent Cyber Attacks Cyber Attack Risks MitigationThe following slide illustrates some activities to minimize the probability of cybercrimes within the organization. It includes elements such as utilizing anti virus, preventing to open suspicious emails, keeping systems up to date etc. Introducing Implement Tactics To Prevent Cyber Attacks Cyber Attack Risks Mitigation to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Prevent Opening Suspicious Emails, Keep Systems Up To Date, Leverage Firewalls, using this template. Grab it now to reap its full benefits.
-
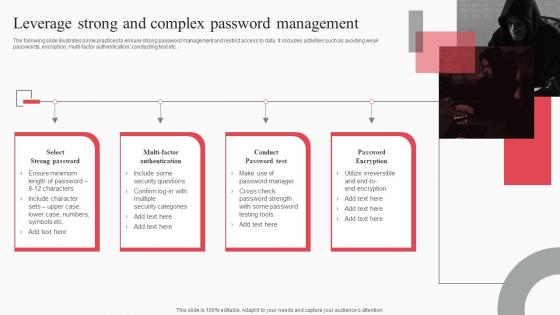 Leverage Strong And Complex Password Management Cyber Attack Risks Mitigation
Leverage Strong And Complex Password Management Cyber Attack Risks MitigationThe following slide illustrates some practices to ensure strong password management and restrict access to data. It includes activities such as avoiding weak passwords, encryption, multi-factor authentication, conducting test etc. Increase audience engagement and knowledge by dispensing information using Leverage Strong And Complex Password Management Cyber Attack Risks Mitigation. This template helps you present information on four stages. You can also present information on Select Strong Password, Multi Factor Authentication, Conduct Password Test using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Monitor And Assess Vendor Risk Management Cyber Attack Risks Mitigation
Monitor And Assess Vendor Risk Management Cyber Attack Risks MitigationThe following slide showcases vendor risk analysis checklist to ensure customer data safety. It includes key elements such as information security and privacy, physical assets, web application, infrastructure security etc. Introducing Monitor And Assess Vendor Risk Management Cyber Attack Risks Mitigation to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispence information on Web Application Security, Infrastructure Security, Vendor Management, using this template. Grab it now to reap its full benefits.
-
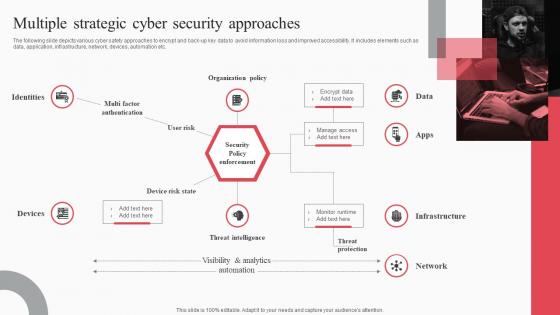 Multiple Strategic Cyber Security Approaches Cyber Attack Risks Mitigation
Multiple Strategic Cyber Security Approaches Cyber Attack Risks MitigationThe following slide depicts various cyber safety approaches to encrypt and back up key data to avoid information loss and improved accessibility. It includes elements such as data, application, infrastructure, network, devices, automation etc. Increase audience engagement and knowledge by dispensing information using Multiple Strategic Cyber Security Approaches Cyber Attack Risks Mitigation. This template helps you present information on one stage. You can also present information on Identities, Organization Policy, Threat Intelligence using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Organize Cyber Security Training For Employees Regularly Cyber Attack Risks Mitigation
Organize Cyber Security Training For Employees Regularly Cyber Attack Risks MitigationThe following slide depicts the staff cyber security training plan to educate them regarding technology threats and practices. It mainly includes elements such as topics to be covered, target audience, trainer name, mode, proposed date, timings etc. Introducing Organize Cyber Security Training For Employees Regularly Cyber Attack Risks Mitigation to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispence information on Document Management, Response Process, Social Media Policy, using this template. Grab it now to reap its full benefits.
-
 Passive Active And Offensive Cyber Security Strategies Cyber Attack Risks Mitigation
Passive Active And Offensive Cyber Security Strategies Cyber Attack Risks MitigationThe following slide showcases passive, active and offensive cyber safety techniques to ensure customer data safety. It includes elements such as inspecting vulnerabilities, penetration testing, deception technology, threat hunting etc. Increase audience engagement and knowledge by dispensing information using Passive Active And Offensive Cyber Security Strategies Cyber Attack Risks Mitigation. This template helps you present information on three stages. You can also present information on Passive Safety, Active Safety, Offensive Safety using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
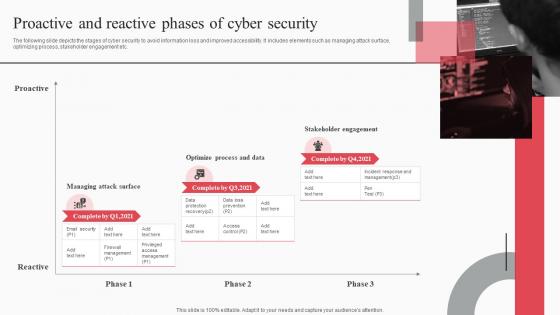 Proactive And Reactive Phases Of Cyber Security Cyber Attack Risks Mitigation
Proactive And Reactive Phases Of Cyber Security Cyber Attack Risks MitigationThe following slide depicts the stages of cyber security to avoid information loss and improved accessibility. It includes elements such as managing attack surface, optimizing process, stakeholder engagement etc. Introducing Proactive And Reactive Phases Of Cyber Security Cyber Attack Risks Mitigation to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Proactive, Managing Attack Surface, Optimize Process, Stakeholder Engagement, using this template. Grab it now to reap its full benefits.
-
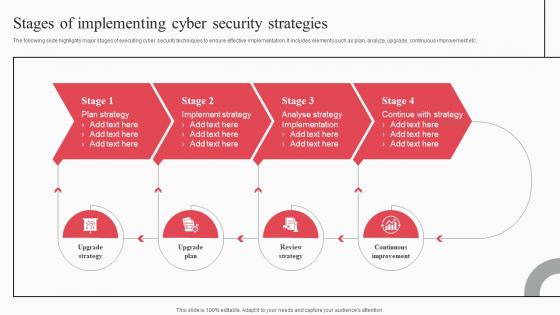 Stages Of Implementing Cyber Security Strategies Cyber Attack Risks Mitigation
Stages Of Implementing Cyber Security Strategies Cyber Attack Risks MitigationThe following slide highlights major stages of executing cyber security techniques to ensure effective implementation. It includes elements such as plan, analyze, upgrade, continuous improvement etc. Increase audience engagement and knowledge by dispensing information using Stages Of Implementing Cyber Security Strategies Cyber Attack Risks Mitigation. This template helps you present information on four stages. You can also present information on Plan Strategy, Implement Strategy, Analyse Strategy using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
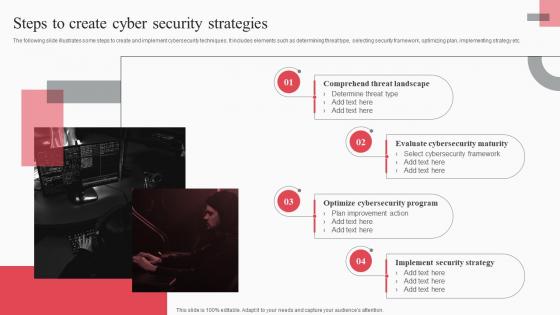 Steps To Create Cyber Security Strategies Cyber Attack Risks Mitigation
Steps To Create Cyber Security Strategies Cyber Attack Risks MitigationThe following slide illustrates some steps to create and implement cybersecurity techniques. It includes elements such as determining threat type, selecting security framework, optimizing plan, implementing strategy etc. Introducing Steps To Create Cyber Security Strategies Cyber Attack Risks Mitigation to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Comprehend Threat Landscape, Evaluate Cybersecurity Maturity, Optimize Cybersecurity Program, using this template. Grab it now to reap its full benefits.
-
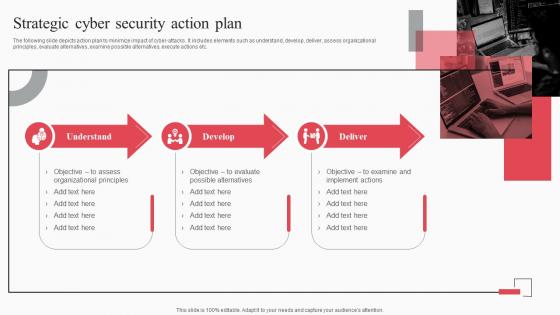 Strategic Cyber Security Action Plan Cyber Attack Risks Mitigation
Strategic Cyber Security Action Plan Cyber Attack Risks MitigationThe following slide depicts action plan to minimize impact of cyber attacks. It includes elements such as understand, develop, deliver, assess organizational principles, evaluate alternatives, examine possible alternatives, execute actions etc. Increase audience engagement and knowledge by dispensing information using Strategic Cyber Security Action Plan Cyber Attack Risks Mitigation. This template helps you present information on three stages. You can also present information on Understand, Develop, Deliver, Organizational Principles using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
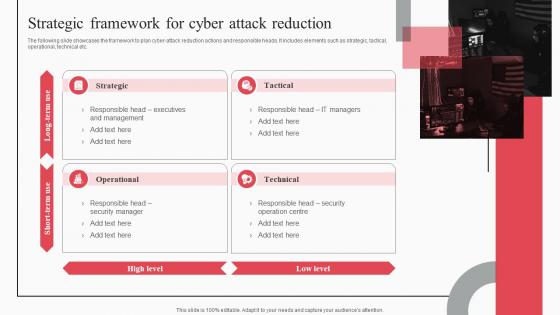 Strategic Framework For Cyber Attack Reduction Cyber Attack Risks Mitigation
Strategic Framework For Cyber Attack Reduction Cyber Attack Risks MitigationThe following slide showcases the framework to plan cyber-attack reduction actions and responsible heads. It includes elements such as strategic, tactical, operational, technical etc. Introducing Strategic Framework For Cyber Attack Reduction Cyber Attack Risks Mitigation to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Strategic, Tactical, Operational, Technical, using this template. Grab it now to reap its full benefits.
-
 Table Of Contents For Cyber Attack Risks Mitigation Strategies Ppt Slides
Table Of Contents For Cyber Attack Risks Mitigation Strategies Ppt SlidesIntroducing Table Of Contents For Cyber Attack Risks Mitigation Strategies Ppt Slides to increase your presentation threshold. Encompassed with fifteen stages, this template is a great option to educate and entice your audience. Dispence information on Security Strategies, Strategic Framework, Password Management, using this template. Grab it now to reap its full benefits.
-
 Icon For Minimizing Digital Risk And Cyber Attacks
Icon For Minimizing Digital Risk And Cyber AttacksIntroducing our Icon For Minimizing Digital Risk And Cyber Attacks set of slides. The topics discussed in these slides are Minimizing Digital Risk Cyber Attacks This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Risk factors showing innovation cyber security price capital access and productivity
Risk factors showing innovation cyber security price capital access and productivityPresenting this set of slides with name - Risk Factors Showing Innovation Cyber Security Price Capital Access And Productivity. This is a five stage process. The stages in this process are Risk Factors, Risk Management, Risk Variable.
-
 Cyber risk management ethical supply chain leadership effectiveness assessment cpb
Cyber risk management ethical supply chain leadership effectiveness assessment cpbPresenting this set of slides with name - Cyber Risk Management Ethical Supply Chain Leadership Effectiveness Assessment Cpb. This is an editable one stages graphic that deals with topics like Cyber Risk Management, Ethical Supply Chain, Leadership Effectiveness Assessment to help convey your message better graphically. This product is a premium product available for immediate download,and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Churn customers blockchain introduction executive cyber risk management cpb
Churn customers blockchain introduction executive cyber risk management cpbPresenting this set of slides with name - Churn Customers Blockchain Introduction Executive Cyber Risk Management Cpb. This is an editable five stages graphic that deals with topics like Churn Customers, Blockchain Introduction, Executive Cyber Risk Management to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Cyber security risk management plan ppt powerpoint presentation gallery icons cpb
Cyber security risk management plan ppt powerpoint presentation gallery icons cpbPresenting this set of slides with name Cyber Security Risk Management Plan Ppt Powerpoint Presentation Gallery Icons Cpb. This is an editable Powerpoint three stages graphic that deals with topics like Cyber Security Risk Management Plan to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Targeted cyber risk management ppt powerpoint presentation summary files cpb
Targeted cyber risk management ppt powerpoint presentation summary files cpbPresenting this set of slides with name Targeted Cyber Risk Management Ppt Powerpoint Presentation Summary Files Cpb. This is an editable Powerpoint four stages graphic that deals with topics like Targeted Cyber Risk Management to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Cyber risk management framework ppt powerpoint presentation file introduction cpb
Cyber risk management framework ppt powerpoint presentation file introduction cpbPresenting this set of slides with name Cyber Risk Management Framework Ppt Powerpoint Presentation File Introduction Cpb. This is an editable Powerpoint six stages graphic that deals with topics like Cyber Risk Management Framework to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Relationship cyber security risk management ppt powerpoint presentation summary layouts cpb
Relationship cyber security risk management ppt powerpoint presentation summary layouts cpbPresenting this set of slides with name Relationship Cyber Security Risk Management Ppt Powerpoint Presentation Summary Layouts Cpb. This is an editable Powerpoint three stages graphic that deals with topics like Relationship Cyber Security Risk Management to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Targeted cyber risk management ppt powerpoint presentation layouts show cpb
Targeted cyber risk management ppt powerpoint presentation layouts show cpbPresenting this set of slides with name Targeted Cyber Risk Management Ppt Powerpoint Presentation Layouts Show Cpb. This is an editable Powerpoint seven stages graphic that deals with topics like Targeted Cyber Risk Management to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Cyber data security icon for fraud risk management
Cyber data security icon for fraud risk managementPresenting this set of slides with name Cyber Data Security Icon For Fraud Risk Management. This is a three stage process. The stages in this process are Cyber Data Security Icon For Fraud Risk Management. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Cyber security risk assessment report ppt powerpoint presentation outline outfit cpb
Cyber security risk assessment report ppt powerpoint presentation outline outfit cpbPresenting this set of slides with name Cyber Security Risk Assessment Report Ppt Powerpoint Presentation Outline Outfit Cpb. This is an editable Powerpoint two stages graphic that deals with topics like Cyber Security Risk Assessment Report to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Cyber security key risk indicator
Cyber security key risk indicatorPresenting this set of slides with name Cyber Security Key Risk Indicator. This is a five stage process. The stages in this process are Cyber Security, Key Risk, Indicator. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
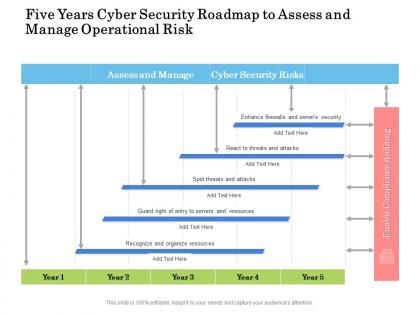 Five years cyber security roadmap to assess and manage operational risk
Five years cyber security roadmap to assess and manage operational riskPresenting Five Years Cyber Security Roadmap To Assess And Manage Operational Risk PowerPoint slide which is 100 percent editable. You can change the color, font size, font type, and shapes of this PPT layout according to your needs. This PPT template is compatible with Google Slides and is available in both 4,3 and 16,9 aspect ratios. This ready to use PowerPoint presentation can be downloaded in various formats like PDF, JPG, and PNG.
-
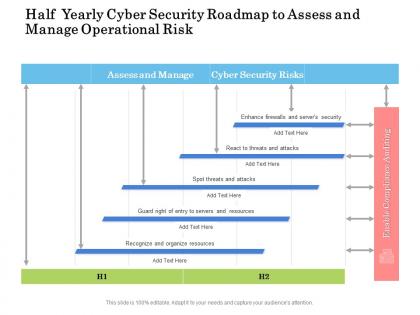 Half yearly cyber security roadmap to assess and manage operational risk
Half yearly cyber security roadmap to assess and manage operational riskPresenting Half Yearly Cyber Security Roadmap To Assess And Manage Operational Risk PowerPoint slide which is 100 percent editable. You can change the color, font size, font type, and shapes of this PPT layout according to your needs. This PPT template is compatible with Google Slides and is available in both 4,3 and 16,9 aspect ratios. This ready to use PowerPoint presentation can be downloaded in various formats like PDF, JPG, and PNG.
-
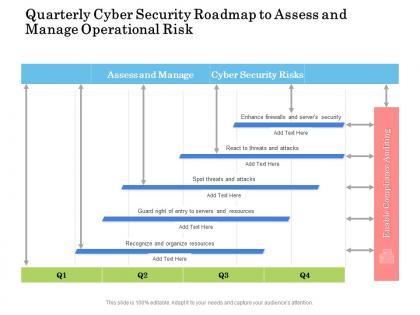 Quarterly cyber security roadmap to assess and manage operational risk
Quarterly cyber security roadmap to assess and manage operational riskPresenting Quarterly Cyber Security Roadmap To Assess And Manage Operational Risk PowerPoint slide which is 100 percent editable. You can change the color, font size, font type, and shapes of this PPT layout according to your needs. This PPT template is compatible with Google Slides and is available in both 4,3 and 16,9 aspect ratios. This ready to use PowerPoint presentation can be downloaded in various formats like PDF, JPG, and PNG.
-
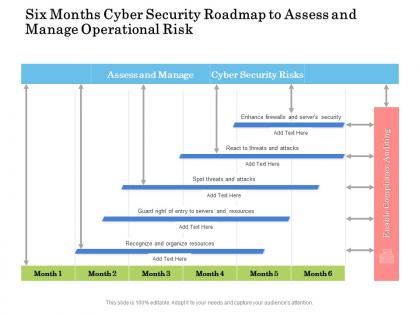 Six months cyber security roadmap to assess and manage operational risk
Six months cyber security roadmap to assess and manage operational riskPresenting Six Months Cyber Security Roadmap To Assess And Manage Operational Risk PowerPoint slide which is 100 percent editable. You can change the color, font size, font type, and shapes of this PPT layout according to your needs. This PPT template is compatible with Google Slides and is available in both 4,3 and 16,9 aspect ratios. This ready to use PowerPoint presentation can be downloaded in various formats like PDF, JPG, and PNG.
-
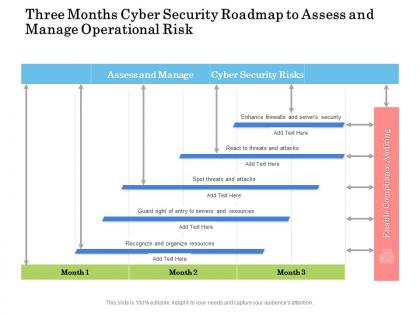 Three months cyber security roadmap to assess and manage operational risk
Three months cyber security roadmap to assess and manage operational riskPresenting Three Months Cyber Security Roadmap To Assess And Manage Operational Risk PowerPoint slide which is 100 percent editable. You can change the color, font size, font type, and shapes of this PPT layout according to your needs. This PPT template is compatible with Google Slides and is available in both 4,3 and 16,9 aspect ratios. This ready to use PowerPoint presentation can be downloaded in various formats like PDF, JPG, and PNG.
-
 Cyber risk acquisitions ppt powerpoint presentation layouts visuals cpb
Cyber risk acquisitions ppt powerpoint presentation layouts visuals cpbPresenting this set of slides with name Cyber Risk Acquisitions Ppt Powerpoint Presentation Layouts Visuals Cpb. This is an editable Powerpoint three stages graphic that deals with topics like Cyber Risk Acquisitions to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Examples cyber security risks ppt powerpoint presentation layouts guide cpb
Examples cyber security risks ppt powerpoint presentation layouts guide cpbPresenting this set of slides with name Examples Cyber Security Risks Ppt Powerpoint Presentation Layouts Guide Cpb. This is an editable Powerpoint eight stages graphic that deals with topics like Examples Cyber Security Risks to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Steps to mitigate cyber security risks
Steps to mitigate cyber security risksPresenting this set of slides with name Steps To Mitigate Cyber Security Risks. This is a five stage process. The stages in this process are Assets Identification, Asset Protection, Incident Detection, Build Plan To Respond, Recovery To Normal Operation. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Real time cyber threat risk management ppt powerpoint presentation slides backgrounds cpb
Real time cyber threat risk management ppt powerpoint presentation slides backgrounds cpbPresenting this set of slides with name Real Time Cyber Threat Risk Management Ppt Powerpoint Presentation Infographic Template Cpb. This is an editable Powerpoint three stages graphic that deals with topics like Real Time Cyber Threat Risk Management to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 List cyber security risks ppt powerpoint presentation ideas elements cpb
List cyber security risks ppt powerpoint presentation ideas elements cpbPresenting this set of slides with name List Cyber Security Risks Ppt Powerpoint Presentation Ideas Elements Cpb. This is an editable Powerpoint six stages graphic that deals with topics like List Cyber Security Risks to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Global cyber security or critical risk dashboard
Global cyber security or critical risk dashboardPresenting this set of slides with name Global Cyber Security Or Critical Risk Dashboard. The topics discussed in these slides are Global, Cybersecurity, Overall Progression, Critical Risks Identified, Highlights. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Agenda for cyber security risks optimize ppt powerpoint presentation visuals
Agenda for cyber security risks optimize ppt powerpoint presentation visualsPresenting this set of slides with name Agenda For Cyber Security Risks Optimize Ppt Powerpoint Presentation Visuals. The topics discussed in these slides are Agenda Cyber, Security, Risks Optimize. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Categorization of cyber risks statutory requirement ppt powerpoint presentation show
Categorization of cyber risks statutory requirement ppt powerpoint presentation showThis slide provides information reading the various cyber risks that firm might face. These risks are categorized into different categories such as low, medium, high, severe and extreme. This categorization is based on certain parameters such as financial impact, damage extent. Presenting this set of slides with name Categorization Of Cyber Risks Statutory Requirement Ppt Powerpoint Presentation Show. This is a five stage process. The stages in this process are Categorization, Cyber Risks, Statutory, Requirement. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Dashboard cyber risk management rating breakdown powerpoint presentation designs
Dashboard cyber risk management rating breakdown powerpoint presentation designsThis slide portrays information regarding the dashboard that firm will use to manage cyber risks. The dashboard will provide clear picture of risk prevailing and how they are treated to technical engineers and board level executives. Presenting this set of slides with name Dashboard Cyber Risk Management Rating Breakdown Powerpoint Presentation Designs. The topics discussed in these slides are Dashboard, Cyber Risk Management, Rating Breakdown. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Risk based approach to cyber and information security
Risk based approach to cyber and information securityPresenting this set of slides with name Risk Based Approach To Cyber And Information Security. This is a five stage process. The stages in this process are Perform Risk Assessment, Document Controls, Implement Controls, Assess And Report, Remediate. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Mitigation plans to address key risks cyber incident ppt powerpoint presentation slides
Mitigation plans to address key risks cyber incident ppt powerpoint presentation slidesThis slide provides information regarding the identified risks that are needed to be addressed. The plan will help in keeping the track of potential risks that are existing and what are the resources required to handle them. Presenting this set of slides with name Mitigation Plans To Address Key Risks Cyber Incident Ppt Powerpoint Presentation S. The topics discussed in these slides are Risk Level, Risk Mitigation, Duration, Communication, Risk Treated. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
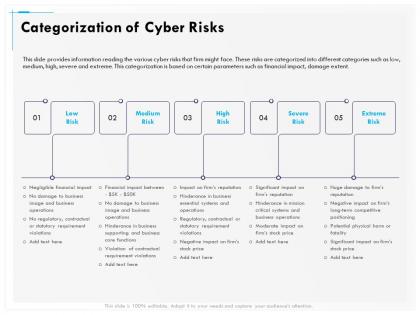 Categorization of cyber risks medium ppt gallery
Categorization of cyber risks medium ppt galleryThis slide provides information reading the various cyber risks that firm might face. These risks are categorized into different categories such as low medium high severe and extreme. This categorization is based on certain parameters such as financial impact damage extent. Presenting this set of slides with name Categorization Of Cyber Risks Medium Ppt Gallery. This is a five stage process. The stages in this process are Low Risk, Medium Risk, High Risk, Severe Risk, Extreme Risk . This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
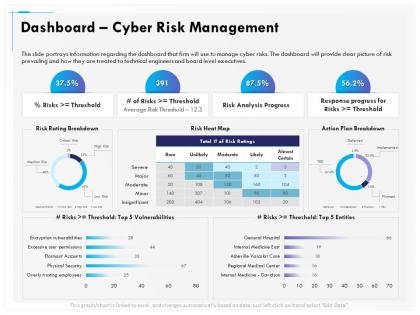 Dashboard Cyber Risk Management Breakdown Ppt Infographics
Dashboard Cyber Risk Management Breakdown Ppt InfographicsThis slide portrays information regarding the dashboard that firm will use to manage cyber risks. The dashboard will provide clear picture of risk prevailing and how they are treated to technical engineers and board level executives. Presenting this set of slides with name Dashboard Cyber Risk Management Breakdown Ppt Infographics. The topics discussed in these slides are Dashboard Cyber Risk Management. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Cyber risk analytics dashboard with different incidents powerpoint template
Cyber risk analytics dashboard with different incidents powerpoint templateThis slide Covers the Graphical Representation of Cyber Analytics. Data covered in this dashboard includes Number of incident per incident type and malware type with Number of incident per Malware type and broken by security level. This is a Cyber Risk Analytics Dashboard With Different Incidents Powerpoint Template drafted with a diverse set of graphics, that can be reformulated and edited as per your needs and requirements. Just download it in your system and make use of it in PowerPoint or Google Slides, depending upon your presentation preferences.



