Powerpoint Templates and Google slides for Cyber Risk Profiling
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Cyber Supply Chain Risk Management Dashboard Ppt Powerpoint Presentation Pictures Topics
Cyber Supply Chain Risk Management Dashboard Ppt Powerpoint Presentation Pictures TopicsThis slide shows the dashboard representing details related to management of supply chain risks by the incident management team. It includes details related to KPIs such as policy and compliance, resource security hygiene etc. Present the topic in a bit more detail with this Cyber Supply Chain Risk Management Dashboard Ppt Powerpoint Presentation Pictures Topics. Use it as a tool for discussion and navigation on Regulatory Compliance, Cyber Supply Chain, Management Dashboard. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Enterprise Cyber Risk Management Dashboard Implementing Cyber Security Ppt Demonstration
Enterprise Cyber Risk Management Dashboard Implementing Cyber Security Ppt DemonstrationThis slide represents the key metrics dashboard representing details related to management of cyber security incidents by an enterprise. It includes key performance indicators such as risk analysis progress, risk rating breakdown etc. Deliver an outstanding presentation on the topic using this Enterprise Cyber Risk Management Dashboard Implementing Cyber Security Ppt Demonstration. Dispense information and present a thorough explanation of Enterprise Cyber, Risk Management, Dashboard using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
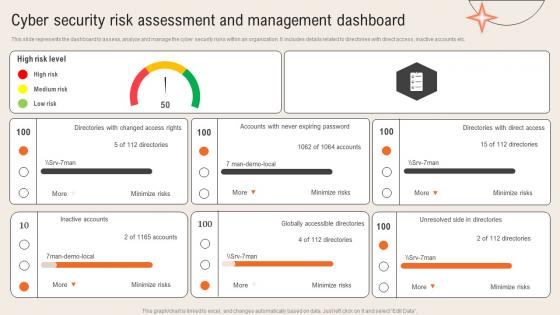 Cyber Security Risk Assessment And Management Dashboard Deploying Computer Security Incident
Cyber Security Risk Assessment And Management Dashboard Deploying Computer Security IncidentThis slide represents the dashboard to assess, analyze and manage the cyber security risks within an organization. It includes details related to directories with direct access, inactive accounts etc.Present the topic in a bit more detail with this Cyber Security Risk Assessment And Management Dashboard Deploying Computer Security Incident. Use it as a tool for discussion and navigation on Expiring Password, Accessible Directories, Directories Direct Access. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Supply Chain Risk Management Dashboard Deploying Computer Security Incident Management
Cyber Supply Chain Risk Management Dashboard Deploying Computer Security Incident ManagementThis slide shows the dashboard representing details related to management of supply chain risks by the incident management team. It includes details related to KPIs such as policy and compliance, resource security hygiene etc.Present the topic in a bit more detail with this Cyber Supply Chain Risk Management Dashboard Deploying Computer Security Incident Management. Use it as a tool for discussion and navigation on Resource Security Hygiene, Subscription Coverage, Resource Health Monitoring. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
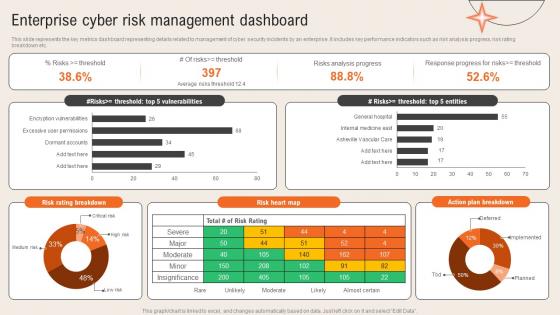 Enterprise Cyber Risk Management Dashboard Deploying Computer Security Incident Management
Enterprise Cyber Risk Management Dashboard Deploying Computer Security Incident ManagementThis slide represents the key metrics dashboard representing details related to management of cyber security incidents by an enterprise. It includes key performance indicators such as risk analysis progress, risk rating breakdown etc.Present the topic in a bit more detail with this Enterprise Cyber Risk Management Dashboard Deploying Computer Security Incident Management. Use it as a tool for discussion and navigation on Risks Analysis Progress, Response Progress, Action Plan Breakdown. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
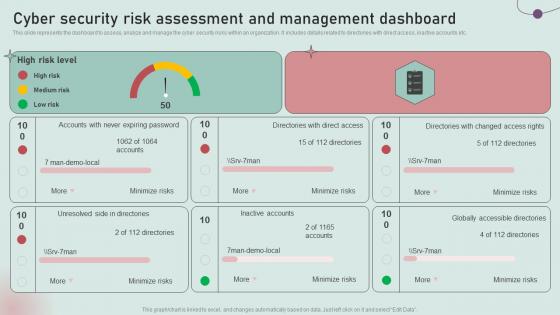 Cyber Security Risk Assessment And Management Dashboard Development And Implementation Of Security
Cyber Security Risk Assessment And Management Dashboard Development And Implementation Of SecurityThis slide represents the dashboard to assess, analyze and manage the cyber security risks within an organization. It includes details related to directories with direct access, inactive accounts etc. Deliver an outstanding presentation on the topic using this Cyber Security Risk Assessment And Management Dashboard Development And Implementation Of Security. Dispense information and present a thorough explanation of Medium Risk, Unresolved Side, Inactive Accounts using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Supply Chain Risk Management Dashboard Development And Implementation Of Security Incident
Cyber Supply Chain Risk Management Dashboard Development And Implementation Of Security IncidentThis slide shows the dashboard representing details related to management of supply chain risks by the incident management team. It includes details related to KPIs such as policy and compliance, resource security hygiene etc. Deliver an outstanding presentation on the topic using this Cyber Supply Chain Risk Management Dashboard Development And Implementation Of Security Incident. Dispense information and present a thorough explanation of Regulatory Compliance, Subscription Coverage, Resource Health using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
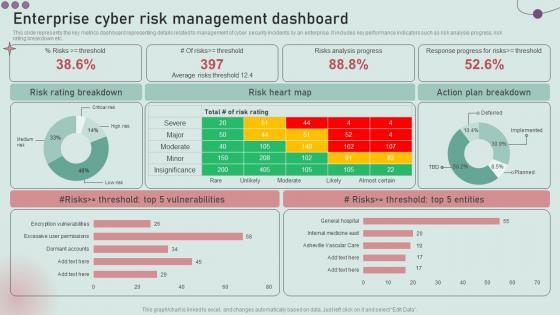 Enterprise Cyber Risk Management Dashboard Development And Implementation Of Security Incident
Enterprise Cyber Risk Management Dashboard Development And Implementation Of Security IncidentThis slide represents the key metrics dashboard representing details related to management of cyber security incidents by an enterprise. It includes key performance indicators such as risk analysis progress, risk rating breakdown etc. Present the topic in a bit more detail with this Enterprise Cyber Risk Management Dashboard Development And Implementation Of Security Incident. Use it as a tool for discussion and navigation on Risk Rating Breakdown, Risk Heart Map, Action Plan Breakdown. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
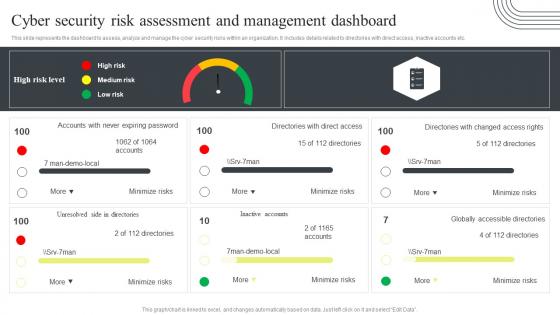 Cyber Security Attacks Response Plan Cyber Security Risk Assessment And Management Dashboard
Cyber Security Attacks Response Plan Cyber Security Risk Assessment And Management DashboardThis slide represents the dashboard to assess, analyze and manage the cyber security risks within an organization. It includes details related to directories with direct access, inactive accounts etc. Deliver an outstanding presentation on the topic using this Cyber Security Attacks Response Plan Cyber Security Risk Assessment And Management Dashboard. Dispense information and present a thorough explanation of Cyber Security, Risk Assessment, Management Dashboard using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Security Attacks Response Plan Cyber Supply Chain Risk Management Dashboard
Cyber Security Attacks Response Plan Cyber Supply Chain Risk Management DashboardThis slide shows the dashboard representing details related to management of supply chain risks by the incident management team. It includes details related to KPIs such as policy and compliance, resource security hygiene etc. Present the topic in a bit more detail with this Cyber Security Attacks Response Plan Cyber Supply Chain Risk Management Dashboard. Use it as a tool for discussion and navigation on Cyber Supply Chain, Risk Management, Dashboard, Regulatory Compliance. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Security Attacks Response Plan Enterprise Cyber Risk Management Dashboard
Cyber Security Attacks Response Plan Enterprise Cyber Risk Management DashboardThis slide represents the key metrics dashboard representing details related to management of cyber security incidents by an enterprise. It includes key performance indicators such as risk analysis progress, risk rating breakdown etc. Deliver an outstanding presentation on the topic using this Cyber Security Attacks Response Plan Enterprise Cyber Risk Management Dashboard. Dispense information and present a thorough explanation of Enterprise Cyber, Risk Management, Dashboard, Action Plan Breakdown using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
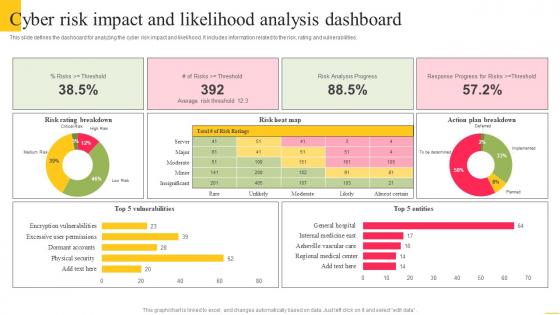 Cyber Risk Impact And Likelihood Analysis Dashboard
Cyber Risk Impact And Likelihood Analysis DashboardThis slide defines the dashboard for analyzing the cyber risk impact and likelihood. It includes information related to the risk, rating and vulnerabilities. Introducing our Cyber Risk Impact And Likelihood Analysis Dashboard set of slides. The topics discussed in these slides are Risk Rating Breakdown, Risk Heat Map, Action Plan Breakdown. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
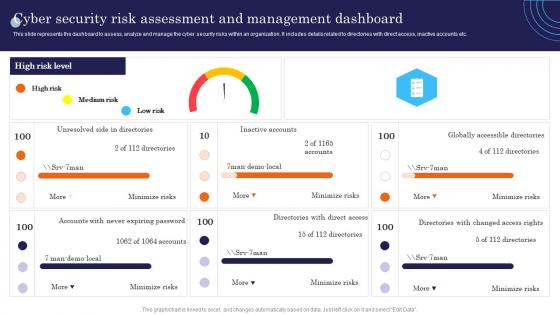 Cyber Security Risk Assessment And Management Dashboard Incident Response Strategies Deployment
Cyber Security Risk Assessment And Management Dashboard Incident Response Strategies DeploymentThis slide represents the dashboard to assess, analyze and manage the cyber security risks within an organization. It includes details related to directories with direct access, inactive accounts etc. Present the topic in a bit more detail with this Cyber Security Risk Assessment And Management Dashboard Incident Response Strategies Deployment. Use it as a tool for discussion and navigation on Accounts, Globally, Unresolved. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Supply Chain Risk Management Dashboard Incident Response Strategies Deployment
Cyber Supply Chain Risk Management Dashboard Incident Response Strategies DeploymentThis slide shows the dashboard representing details related to management of supply chain risks by the incident management team. It includes details related to KPIs such as policy and compliance, resource security hygiene etc. Deliver an outstanding presentation on the topic using this Cyber Supply Chain Risk Management Dashboard Incident Response Strategies Deployment. Dispense information and present a thorough explanation of Regulatory, Subscription, Threat using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Enterprise Cyber Risk Management Dashboard Incident Response Strategies Deployment
Enterprise Cyber Risk Management Dashboard Incident Response Strategies DeploymentThis slide represents the key metrics dashboard representing details related to management of cyber security incidents by an enterprise. It includes key performance indicators such as risk analysis progress, risk rating breakdown etc. Present the topic in a bit more detail with this Enterprise Cyber Risk Management Dashboard Incident Response Strategies Deployment. Use it as a tool for discussion and navigation on Rating, Management, Enterprise. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
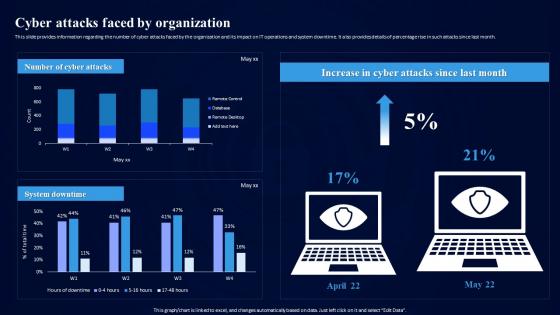 Cybersecurity Risk Assessment Program Cyber Attacks Faced By Organization
Cybersecurity Risk Assessment Program Cyber Attacks Faced By OrganizationThis slide provides information regarding the number of cyber attacks faced by the organization and its impact on IT operations and system downtime. It also provides details of percentage rise in such attacks since last month. Present the topic in a bit more detail with this Cybersecurity Risk Assessment Program Cyber Attacks Faced By Organization. Use it as a tool for discussion and navigation on Cyber Attacks, IT Operations, System Downtime. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cybersecurity Risk Assessment Program Dashboard For Tracking Cyber Attack Risk Levels
Cybersecurity Risk Assessment Program Dashboard For Tracking Cyber Attack Risk LevelsThe slide represents the dashboard for tracking cyber attack risk levels. It includes information regarding the multiple threat agents, attack methods, preventive controls along with details of risk score and infected systems. Deliver an outstanding presentation on the topic using this Cybersecurity Risk Assessment Program Dashboard For Tracking Cyber Attack Risk Levels. Dispense information and present a thorough explanation of Infrastructure Controls, Preventive Controls, Detective Controls using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
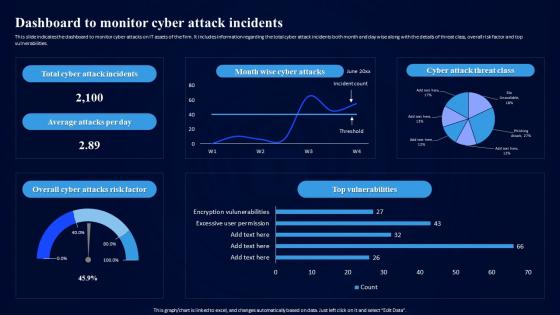 Cybersecurity Risk Assessment Program Dashboard To Monitor Cyber Attack Incidents
Cybersecurity Risk Assessment Program Dashboard To Monitor Cyber Attack IncidentsThis slide indicates the dashboard to monitor cyber attacks on IT assets of the firm. It includes information regarding the total cyber attack incidents both month and day wise along with the details of threat class, overall risk factor and top vulnerabilities. Present the topic in a bit more detail with this Cybersecurity Risk Assessment Program Dashboard To Monitor Cyber Attack Incidents. Use it as a tool for discussion and navigation on Dashboard To Monitor, Cyber Attack Incidents, Vulnerabilities, Dashboard. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cybersecurity Risk Assessment Program Monetary Losses Due To Cyber Crime Events
Cybersecurity Risk Assessment Program Monetary Losses Due To Cyber Crime EventsThis slide tabulates the financial losses faced by the organization in multiple regions across the globe due to cyber crime incidents. The major losses highlighted are data, operational and revenue loss. It also contains details of solution, a cybersecurity program with risk assessment module. Present the topic in a bit more detail with this Cybersecurity Risk Assessment Program Monetary Losses Due To Cyber Crime Events. Use it as a tool for discussion and navigation on Monetary Losses Due, Cyber Crime Events, Mitigation Strategy. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
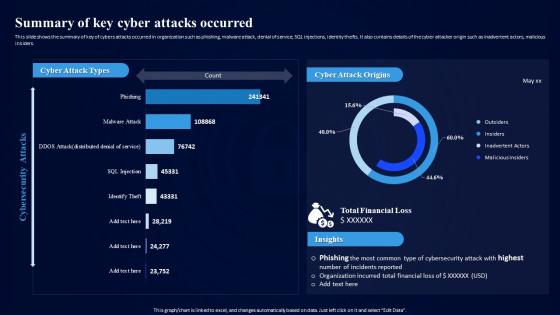 Cybersecurity Risk Assessment Program Summary Of Key Cyber Attacks Occurred
Cybersecurity Risk Assessment Program Summary Of Key Cyber Attacks OccurredThis slide shows the summary of key of cybers attacks occurred in organization such as phishing, malware attack, denial of service, SQL injections, identity thefts. It also contains details of the cyber attacker origin such as inadvertent actors, malicious insiders. Present the topic in a bit more detail with this Cybersecurity Risk Assessment Program Summary Of Key Cyber Attacks Occurred. Use it as a tool for discussion and navigation on Cyber Attacks Occurred, Financial Loss, Cyber Attack Origins. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
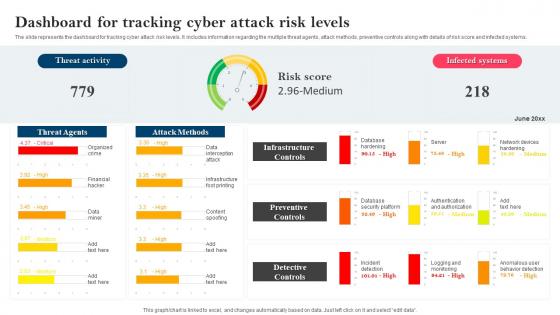 Strategy To Minimize Cyber Attacks Dashboard For Tracking Cyber Attack Risk Levels
Strategy To Minimize Cyber Attacks Dashboard For Tracking Cyber Attack Risk LevelsThe slide represents the dashboard for tracking cyber attack risk levels. It includes information regarding the multiple threat agents, attack methods, preventive controls along with details of risk score and infected systems. Present the topic in a bit more detail with this Strategy To Minimize Cyber Attacks Dashboard For Tracking Cyber Attack Risk Levels. Use it as a tool for discussion and navigation on Dashboard For Tracking, Cyber Attack Risk Levels, Infrastructure Controls, Preventive Controls, Detective Controls. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber security risk assessment matrix ppt powerpoint presentation file guidelines cpb
Cyber security risk assessment matrix ppt powerpoint presentation file guidelines cpbPresenting this set of slides with name Cyber Security Risk Assessment Matrix Ppt Powerpoint Presentation File Guidelines Cpb. This is an editable Powerpoint four stages graphic that deals with topics like Cyber Security Risk Assessment Matrix to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Cyber security risk management ppt powerpoint presentation file background image cpb
Cyber security risk management ppt powerpoint presentation file background image cpbPresenting this set of slides with name Cyber Security Risk Management Ppt Powerpoint Presentation File Background Image Cpb. This is an editable Powerpoint three stages graphic that deals with topics like Cyber Security Risk Management to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
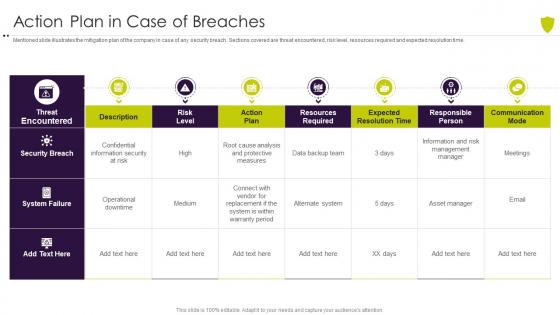 Action plan in case of breaches managing cyber risk in a digital age
Action plan in case of breaches managing cyber risk in a digital ageMentioned slide illustrates the mitigation plan of the company in case of any security breach. Sections covered are threat encountered, risk level, resources required and expected resolution time. Present the topic in a bit more detail with this Action Plan In Case Of Breaches Managing Cyber Risk In A Digital Age. Use it as a tool for discussion and navigation on Action Plan In Case Of Breaches. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
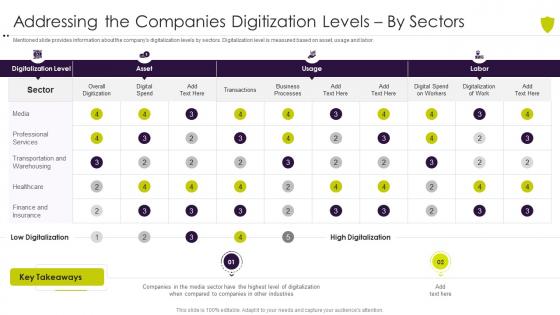 Addressing the companies digitization managing cyber risk in a digital age
Addressing the companies digitization managing cyber risk in a digital ageMentioned slide provides information about the companys digitalization levels by sectors. Digitalization level is measured based on asset, usage and labor. Deliver an outstanding presentation on the topic using this Addressing The Companies Digitization Managing Cyber Risk In A Digital Age. Dispense information and present a thorough explanation of Addressing The Companies Digitization Levels By Sectors using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Agenda of managing cyber risk in a digital age
Agenda of managing cyber risk in a digital ageIntroducing Agenda Of Managing Cyber Risk In A Digital Age to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Information, Security, Digitalization, Threat, using this template. Grab it now to reap its full benefits.
-
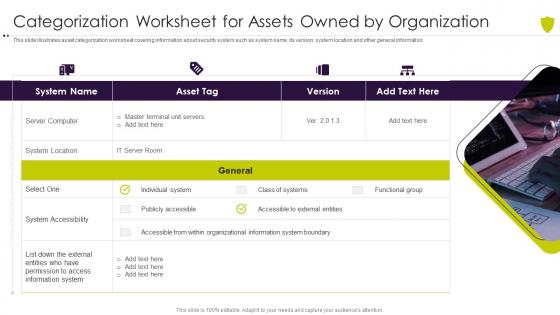 Categorization worksheet for assets managing cyber risk in a digital age
Categorization worksheet for assets managing cyber risk in a digital ageThis slide illustrates asset categorization worksheet covering information about security system such as system name, its version, system location and other general information. Increase audience engagement and knowledge by dispensing information using Categorization Worksheet For Assets Managing Cyber Risk In A Digital Age. This template helps you present information on four stages. You can also present information on Categorization Worksheet For Assets Owned By Organization using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Checklist for effectively managing asset managing cyber risk in a digital age
Checklist for effectively managing asset managing cyber risk in a digital ageFollowing slide displays system management checklist that company will use for effectively managing asset security. It also includes system management activities and frequency of performing them. Present the topic in a bit more detail with this Checklist For Effectively Managing Asset Managing Cyber Risk In A Digital Age. Use it as a tool for discussion and navigation on Checklist For Effectively Managing Asset Security. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
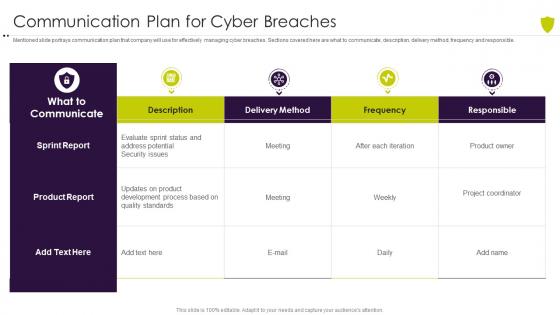 Communication plan for cyber breaches managing cyber risk in a digital age
Communication plan for cyber breaches managing cyber risk in a digital ageMentioned slide portrays communication plan that company will use for effectively managing cyber breaches. Sections covered here are what to communicate, description, delivery method, frequency and responsible. Deliver an outstanding presentation on the topic using this Communication Plan For Cyber Breaches Managing Cyber Risk In A Digital Age. Dispense information and present a thorough explanation of Communication Plan For Cyber Breaches using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
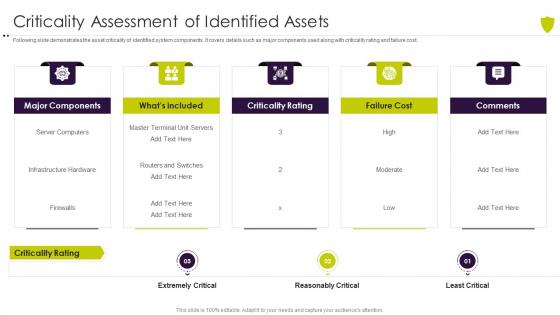 Criticality assessment of identified assets managing cyber risk in a digital age
Criticality assessment of identified assets managing cyber risk in a digital ageFollowing slide demonstrates the asset criticality of identified system components. It covers details such as major components used along with criticality rating and failure cost. Introducing Criticality Assessment Of Identified Assets Managing Cyber Risk In A Digital Age to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Major Components, Criticality, Infrastructure, using this template. Grab it now to reap its full benefits.
-
 Defining business priorities to ensure managing cyber risk in a digital age
Defining business priorities to ensure managing cyber risk in a digital ageThis slide illustrates the key business priorities of the organization such as efficient risk management, standardized incident management process to ensure information security. Increase audience engagement and knowledge by dispensing information using Defining Business Priorities To Ensure Managing Cyber Risk In A Digital Age. This template helps you present information on five stages. You can also present information on Management, Process, Standardized, Communication using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Defining risk events based on impact size managing cyber risk in a digital age
Defining risk events based on impact size managing cyber risk in a digital ageThis slide provides information about risk based events that company will use to define the risks based on impact size and likelihood of occurrence. Present the topic in a bit more detail with this Events Based On Impact Size Managing Cyber Risk In A Digital Age. Use it as a tool for discussion and navigation on Defining Risk Events Based On Impact Size And Likelihood Of Occurrence. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
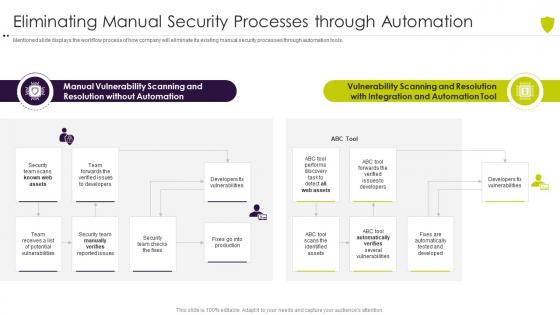 Eliminating manual security processes managing cyber risk in a digital age
Eliminating manual security processes managing cyber risk in a digital ageMentioned slide displays the workflow process of how company will eliminate its existing manual security processes through automation tools. Present the topic in a bit more detail with this Eliminating Manual Security Processes Managing Cyber Risk In A Digital Age. Use it as a tool for discussion and navigation on Vulnerability, Scanning, Resolution, Team. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
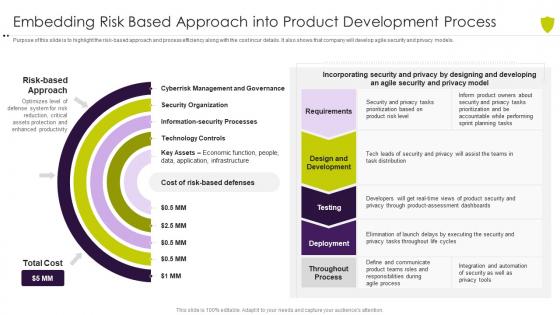 Embedding risk based approach managing cyber risk in a digital age
Embedding risk based approach managing cyber risk in a digital agePurpose of this slide is to highlight the risk based approach and process efficiency along with the cost incur details. It also shows that company will develop agile security and privacy models. Deliver an outstanding presentation on the topic using this Embedding Risk Based Approach Managing Cyber Risk In A Digital Age. Dispense information and present a thorough explanation of Management, Organization, Processes, Information Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
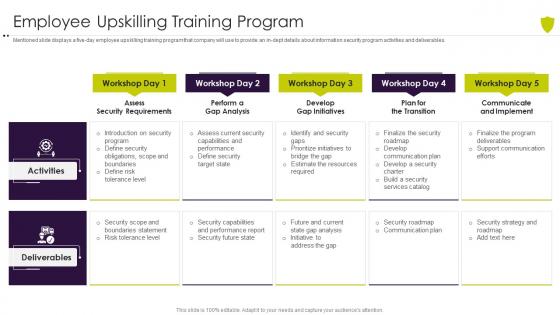 Employee upskilling training program managing cyber risk in a digital age
Employee upskilling training program managing cyber risk in a digital ageMentioned slide displays a five day employee upskilling training program that company will use to provide an in dept details about information security program activities and deliverables. Introducing Employee Upskilling Training Program Managing Cyber Risk In A Digital Age to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Introduction, Obligations, Scope, Security, Boundaries, using this template. Grab it now to reap its full benefits.
-
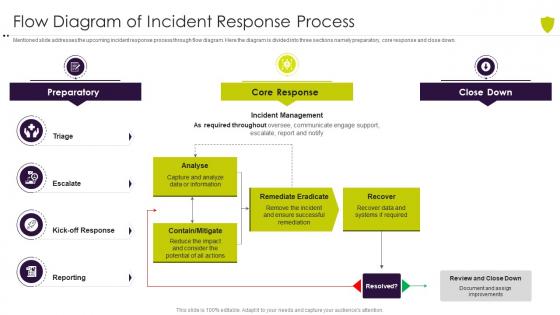 Flow diagram of incident response process managing cyber risk in a digital age
Flow diagram of incident response process managing cyber risk in a digital ageMentioned slide addresses the upcoming incident response process through flow diagram. Here the diagram is divided into three sections namely preparatory, core response and close down. Deliver an outstanding presentation on the topic using this Flow Diagram Of Incident Response Process Managing Cyber Risk In A Digital Age. Dispense information and present a thorough explanation of Flow Diagram Of Incident Response Process using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
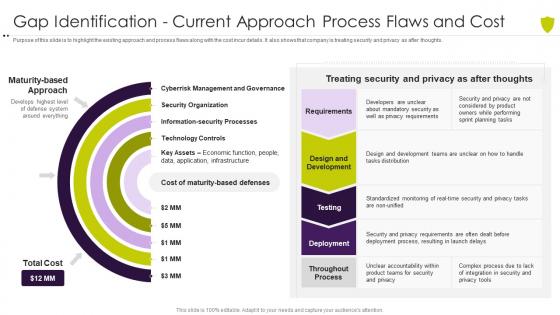 Gap identification current approach process flaws managing cyber risk in a digital age
Gap identification current approach process flaws managing cyber risk in a digital agePurpose of this slide is to highlight the existing approach and process flaws along with the cost incur details. It also shows that company is treating security and privacy as after thoughts. Present the topic in a bit more detail with this Gap Identification Current Approach Process Flaws Managing Cyber Risk In A Digital Age. Use it as a tool for discussion and navigation on Gap Identification Current Approach Process Flaws And Cost. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Icons slide for managing cyber risk in a digital age
Icons slide for managing cyber risk in a digital agePresenting our well crafted Icons Slide For Managing Cyber Risk In A Digital Age set of slides. The slides include icons that are innovatively designed by our team of experts. The icons are easy to edit so you can conveniently increase or decrease their size without any loss in resolution. Therefore, grab them instantly.
-
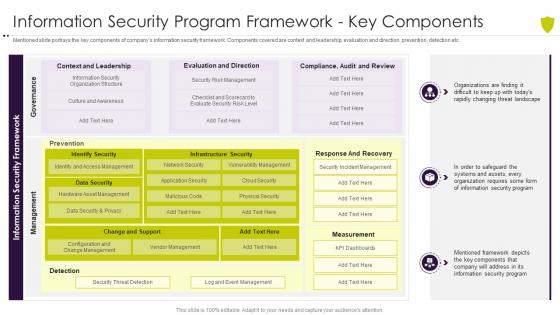 Information security program framework managing cyber risk in a digital age
Information security program framework managing cyber risk in a digital ageMentioned slide portrays the key components of companys information security framework. Components covered are context and leadership, evaluation and direction, prevention, detection etc. Deliver an outstanding presentation on the topic using this Information Security Program Framework Managing Cyber Risk In A Digital Age. Dispense information and present a thorough explanation of Information Security Program Framework Key Components using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
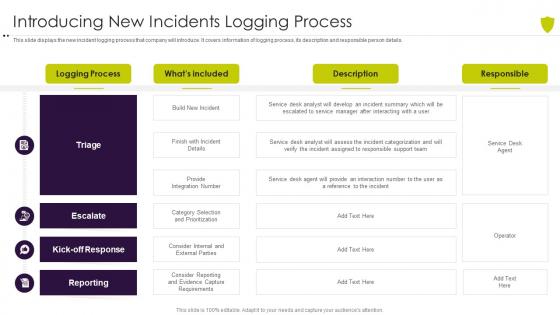 Introducing new incidents logging process managing cyber risk in a digital age
Introducing new incidents logging process managing cyber risk in a digital ageThis slide displays the new incident logging process that company will introduce. It covers information of logging process, its description and responsible person details. Present the topic in a bit more detail with this Introducing New Incidents Logging Process Managing Cyber Risk In A Digital Age. Use it as a tool for discussion and navigation on Introducing New Incidents Logging Process. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
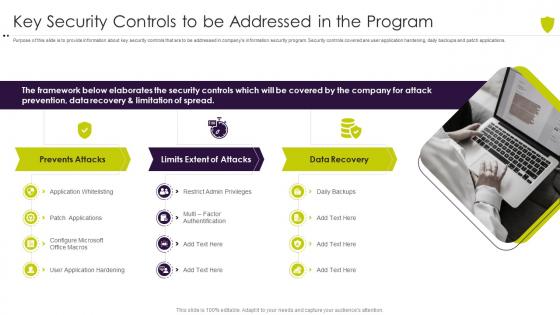 Key security controls to be addressed in the program managing cyber risk in a digital age
Key security controls to be addressed in the program managing cyber risk in a digital agePurpose of this slide is to provide information about key security controls that are to be addressed in companys information security program. Security controls covered are user application hardening, daily backups and patch applications. Increase audience engagement and knowledge by dispensing information using Key Security Controls To Be Addressed In The Program Managing Cyber Risk In A Digital Age. This template helps you present information on three stages. You can also present information on Framework, Elaborates, Security, Controls, Recovery using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
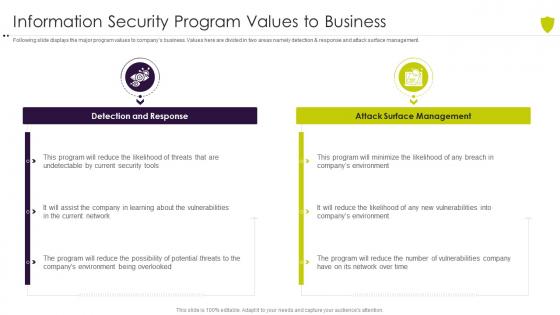 Managing cyber risk in a digital age information security program values to business
Managing cyber risk in a digital age information security program values to businessFollowing slide displays the major program values to companys business. Values here are divided in two areas namely detection and response and attack surface management. Introducing Managing Cyber Risk In A Digital Age Information Security Program Values To Business to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Response, Management, Vulnerabilities, using this template. Grab it now to reap its full benefits.
-
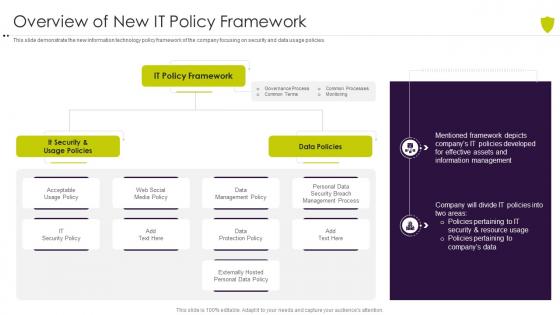 Overview of new it policy framework managing cyber risk in a digital age
Overview of new it policy framework managing cyber risk in a digital ageThis slide demonstrate the new information technology policy framework of the company focusing on security and data usage policies. Present the topic in a bit more detail with this Overview Of New It Policy Framework Managing Cyber Risk In A Digital Age. Use it as a tool for discussion and navigation on Overview Of New IT Policy Framework. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
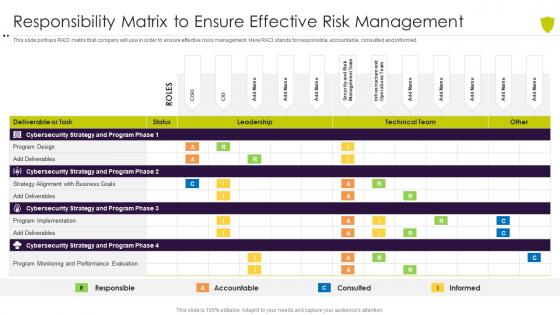 Responsibility matrix to ensure effective risk managing cyber risk in a digital age
Responsibility matrix to ensure effective risk managing cyber risk in a digital ageThis slide portrays RACI matrix that company will use in order to ensure effective risks management. Here RACI stands for responsible, accountable, consulted and informed. Deliver an outstanding presentation on the topic using this Responsibility Matrix To Ensure Effective Risk Managing Cyber Risk In A Digital Age. Dispense information and present a thorough explanation of Responsibility Matrix To Ensure Effective Risk Management using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
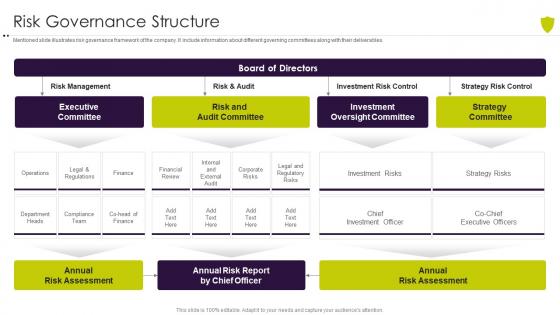 Risk governance structure managing cyber risk in a digital age
Risk governance structure managing cyber risk in a digital ageMentioned slide illustrates risk governance framework of the company. It include information about different governing committees along with their deliverables. Present the topic in a bit more detail with this Risk Governance Structure Managing Cyber Risk In A Digital Age. Use it as a tool for discussion and navigation on Risk Governance Structure. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
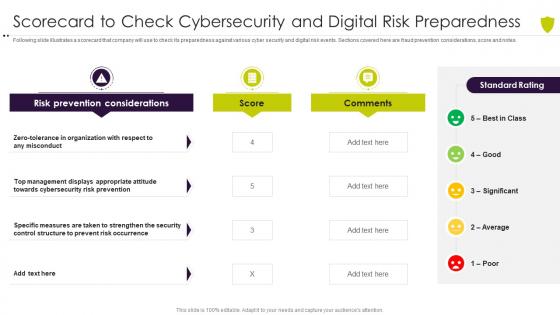 Scorecard to check cybersecurity managing cyber risk in a digital age
Scorecard to check cybersecurity managing cyber risk in a digital ageFollowing slide illustrates a scorecard that company will use to check its preparedness against various cyber security and digital risk events. Sections covered here are fraud prevention considerations, score and notes. Present the topic in a bit more detail with this Scorecard To Check Cybersecurity Managing Cyber Risk In A Digital Age. Use it as a tool for discussion and navigation on Organization, Misconduct, Prevention, Appropriate. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
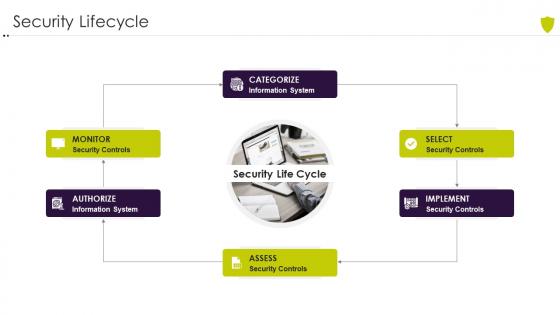 Security lifecycle managing cyber risk in a digital age
Security lifecycle managing cyber risk in a digital ageIncrease audience engagement and knowledge by dispensing information using Security Lifecycle Managing Cyber Risk In A Digital Age. This template helps you present information on one stages. You can also present information on Security Lifecycle using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
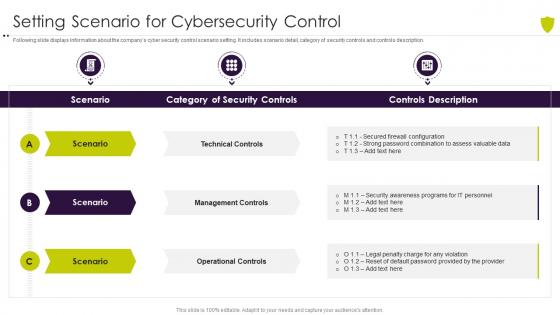 Setting scenario for cybersecurity control managing cyber risk in a digital age
Setting scenario for cybersecurity control managing cyber risk in a digital ageFollowing slide displays information about the companys cyber security control scenario setting. It includes scenario detail, category of security controls and controls description. Deliver an outstanding presentation on the topic using this Setting Scenario For Cybersecurity Control Managing Cyber Risk In A Digital Age. Dispense information and present a thorough explanation of Setting Scenario For Cybersecurity Control using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
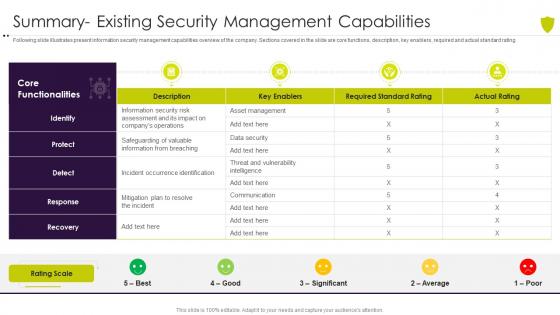 Summary existing security managing cyber risk in a digital age
Summary existing security managing cyber risk in a digital ageFollowing slide illustrates present information security management capabilities overview of the company. Sections covered in the slide are core functions, description, key enablers, required and actual standard rating. Present the topic in a bit more detail with this Summary Existing Security Managing Cyber Risk In A Digital Age. Use it as a tool for discussion and navigation on Summary Existing Security Management Capabilities. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Table of contents managing cyber risk in a digital age
Table of contents managing cyber risk in a digital ageDeliver an outstanding presentation on the topic using this Table Of Contents Managing Cyber Risk In A Digital Age. Dispense information and present a thorough explanation of Market, Digitization, Understanding, Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
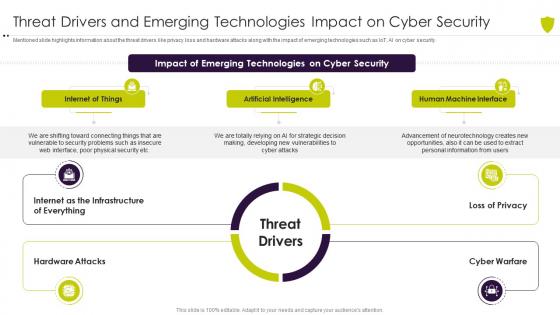 Threat drivers and emerging managing cyber risk in a digital age
Threat drivers and emerging managing cyber risk in a digital ageMentioned slide highlights information about the threat drivers like privacy loss and hardware attacks along with the impact of emerging technologies such as IoT, AI on cyber security. Introducing Threat Drivers And Emerging Managing Cyber Risk In A Digital Age to increase your presentation threshold. Encompassed with threee stages, this template is a great option to educate and entice your audience. Dispence information on Internet Of Things, Artificial Intelligence, Human Machine Interface, using this template. Grab it now to reap its full benefits.
-
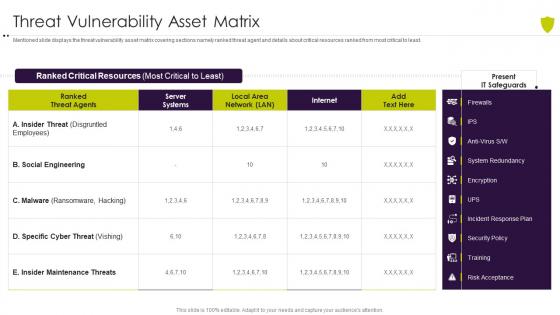 Threat vulnerability asset matrix managing cyber risk in a digital age
Threat vulnerability asset matrix managing cyber risk in a digital ageMentioned slide displays the threat vulnerability asset matrix covering sections namely ranked threat agent and details about critical resources ranked from most critical to least. Present the topic in a bit more detail with this Threat Vulnerability Asset Matrix Managing Cyber Risk In A Digital Age. Use it as a tool for discussion and navigation on Threat Vulnerability Asset Matrix. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
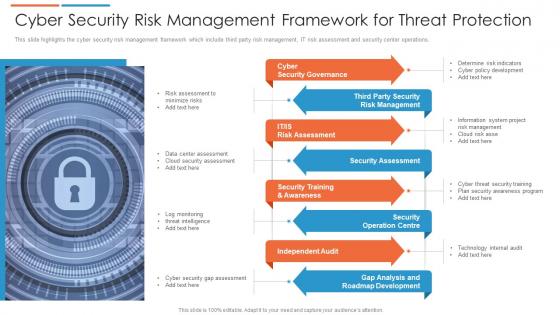 Cyber security risk management framework for threat protection
Cyber security risk management framework for threat protectionThis slide highlights the cyber security risk management framework which include third party risk management, IT risk assessment and security center operations. Presenting our set of slides with Cyber Security Risk Management Framework For Threat Protection. This exhibits information on eight stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cyber Security Governance, Security Assessment, Independent Audit.
-
 Cyber threat report with risk indicator and affected systems
Cyber threat report with risk indicator and affected systemsPresenting our well structured Cyber Threat Report With Risk Indicator And Affected Systems. The topics discussed in this slide are Risk Level, Risk Indication, Potential Affected Systems. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
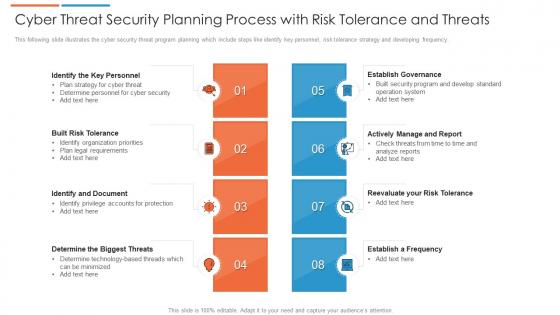 Cyber threat security planning process with risk tolerance and threats
Cyber threat security planning process with risk tolerance and threatsThis following slide illustrates the cyber security threat program planning which include steps like identify key personnel, risk tolerance strategy and developing frequency. Presenting our set of slides with Cyber Threat Security Planning Process With Risk Tolerance And Threats. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Built Risk Tolerance, Identify And Document, Establish Governance.
-
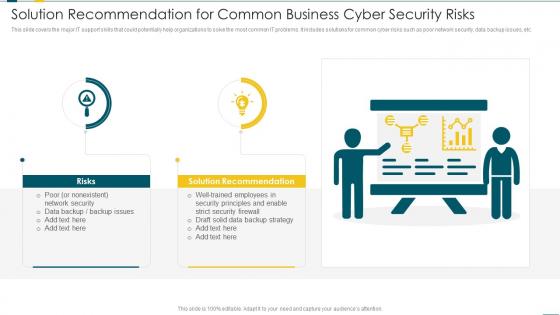 Solution Recommendation For Common Business Cyber Security Risks
Solution Recommendation For Common Business Cyber Security RisksThis slide covers the major IT support skills that could potentially help organizations to solve the most common IT problems. It includes solutions for common cyber risks such as poor network security, data backup issues, etc. Introducing our premium set of slides with Solution Recommendation For Common Business Cyber Security Risks. Ellicudate the two stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Risks, Solution Recommendation, Network Security. So download instantly and tailor it with your information.
-
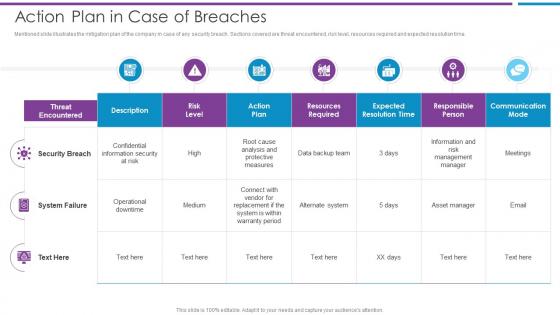 Action Plan In Case Of Breaches Risk Based Methodology To Cyber
Action Plan In Case Of Breaches Risk Based Methodology To CyberMentioned slide illustrates the mitigation plan of the company in case of any security breach. Sections covered are threat encountered, risk level, resources required and expected resolution time.Present the topic in a bit more detail with this Action Plan In Case Of Breaches Risk Based Methodology To Cyber Use it as a tool for discussion and navigation on Security Breach, Confidential Information, Resources Required This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Addressing The Companies Digitization Levelsby Sectors Risk Based Methodology To Cyber
Addressing The Companies Digitization Levelsby Sectors Risk Based Methodology To CyberMentioned slide provides information about the companys digitalization levels by sectors. Digitalization level is measured based on asset, usage and labor.Deliver an outstanding presentation on the topic using this Addressing The Companies Digitization Levelsby Sectors Risk Based Methodology To Cyber Dispense information and present a thorough explanation of Business Processes, Digital Spend On Workers, Digitalization Of Work using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
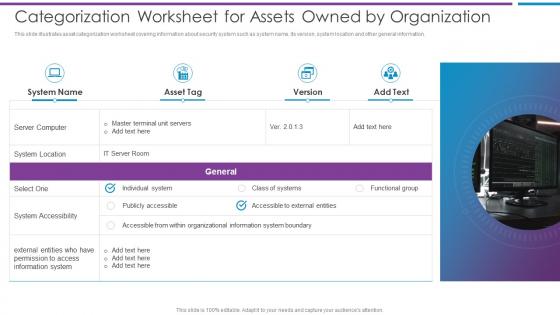 Categorization Worksheet For Assets Owned By Organization Risk Based Methodology To Cyber
Categorization Worksheet For Assets Owned By Organization Risk Based Methodology To CyberThis slide illustrates asset categorization worksheet covering information about security system such as system name, its version, system location and other general information.Introducing Categorization Worksheet For Assets Owned By Organization Risk Based Methodology To Cyber to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on System Accessibility, Individual System, Organizational Information using this template. Grab it now to reap its full benefits.
-
 Checklist For Effectively Managing Asset Security Risk Based Methodology To Cyber
Checklist For Effectively Managing Asset Security Risk Based Methodology To CyberFollowing slide displays system management checklist that company will use for effectively managing asset security. It also includes system management activities and frequency of performing them.Increase audience engagement and knowledge by dispensing information using Checklist For Effectively Managing Asset Security Risk Based Methodology To Cyber This template helps you present information on one stage. You can also present information on System Monitoring, Data Backup, Security Patches using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.



