Powerpoint Templates and Google slides for IT Cyber Security Chip Icon For Network Protection
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Evaluating It System Security Using Swot Analysis Developing Cyber Security Awareness Training Program
Evaluating It System Security Using Swot Analysis Developing Cyber Security Awareness Training ProgramThe purpose of this slide is to outline the strength, weakness, opportunities and threat SWOT evaluation of organization cyber security. Organization can detect the potential risks and opportunities in the cyber security using SWOT model. Introducing Evaluating It System Security Using Swot Analysis Developing Cyber Security Awareness Training Program to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Strengths, Weaknesses, Opportunities, Threats, using this template. Grab it now to reap its full benefits.
-
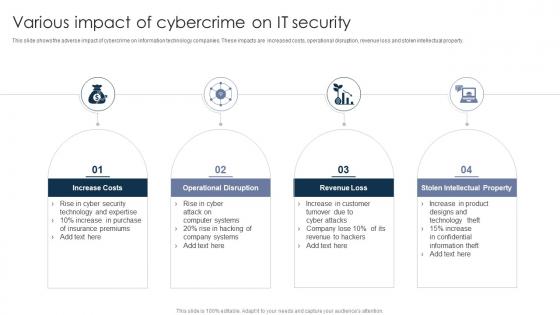 Various Impact Of Cybercrime On IT Security
Various Impact Of Cybercrime On IT SecurityThis slide shows the adverse impact of cybercrime on information technology companies. These impacts are increased costs, operational disruption, revenue loss and stolen intellectual property. Introducing our premium set of slides with Various Impact Of Cybercrime On IT Security. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Increase Costs, Operational Disruption, Revenue Loss, Stolen Intellectual Property. So download instantly and tailor it with your information.
-
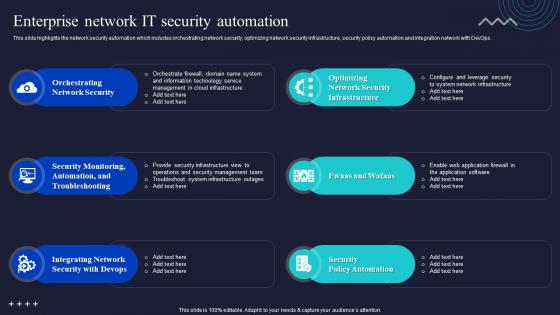 Enterprise Network It Security Automation Enabling Automation In Cyber Security Operations
Enterprise Network It Security Automation Enabling Automation In Cyber Security OperationsThis slide highlights the network security automation which includes orchestrating network security, optimizing network security infrastructure, security policy automation and integration network with DevOps. Deliver an outstanding presentation on the topic using this Enterprise Network It Security Automation Enabling Automation In Cyber Security Operations. Dispense information and present a thorough explanation of Orchestrating Network Security, Troubleshooting, Integrating Network using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Why To Automate The It Security Process Enabling Automation In Cyber Security Operations
Why To Automate The It Security Process Enabling Automation In Cyber Security OperationsThis slide highlights the benefits or importance of automation security process which includes better threat detection, faster containment, improve productivity, admin role delegation and incident response. Increase audience engagement and knowledge by dispensing information using Why To Automate The It Security Process Enabling Automation In Cyber Security Operations. This template helps you present information on five stages. You can also present information on Better Threat Detection, Faster Containment, Improve Productivity using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
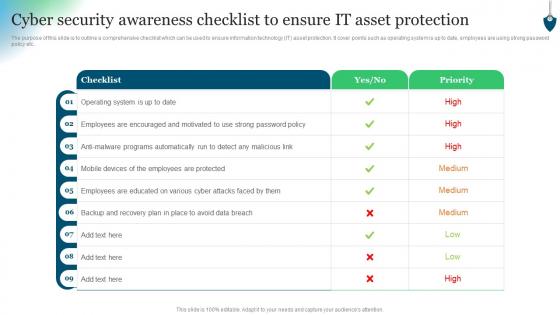 Cyber Security Awareness Checklist To Ensure IT Asset Protection Conducting Security Awareness
Cyber Security Awareness Checklist To Ensure IT Asset Protection Conducting Security AwarenessThe purpose of this slide is to outline a comprehensive checklist which can be used to ensure information technology IT asset protection. It cover points such as operating system is up to date, employees are using strong password policy etc. Present the topic in a bit more detail with this Cyber Security Awareness Checklist To Ensure IT Asset Protection Conducting Security Awareness. Use it as a tool for discussion and navigation on Checklist, Operating System, Employees Encouraged. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
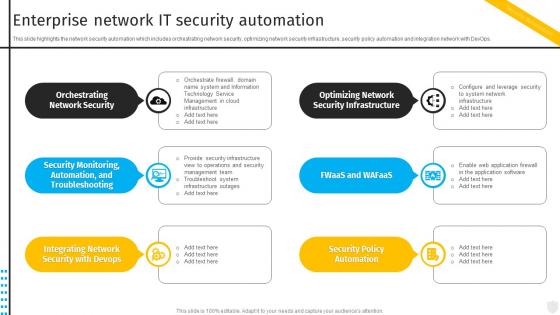 Enterprise Network It Security Automation Security Automation To Investigate And Remediate Cyberthreats
Enterprise Network It Security Automation Security Automation To Investigate And Remediate CyberthreatsThis slide highlights the network security automation which includes orchestrating network security, optimizing network security infrastructure, security policy automation and integration network with DevOps. Increase audience engagement and knowledge by dispensing information using Enterprise Network It Security Automation Security Automation To Investigate And Remediate Cyberthreats. This template helps you present information on six stages. You can also present information on Automation, Security Infrastructure, Troubleshooting using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
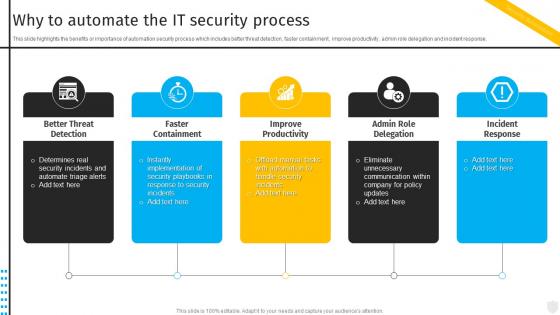 Why To Automate The It Security Process Security Automation To Investigate And Remediate Cyberthreats
Why To Automate The It Security Process Security Automation To Investigate And Remediate CyberthreatsThis slide highlights the benefits or importance of automation security process which includes better threat detection, faster containment, improve productivity, admin role delegation and incident response. Introducing Why To Automate The It Security Process Security Automation To Investigate And Remediate Cyberthreats to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Better Threat Detection, Faster Containment, Improve Productivity, using this template. Grab it now to reap its full benefits.
-
 IT Cyber Security Incident Response Icon
IT Cyber Security Incident Response IconIntroducing our premium set of slides with name IT Cyber Security Incident Response Icon. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like IT Cyber, Security Incident, Response Icon. So download instantly and tailor it with your information.
-
 Developing Cyber Security Awareness Cyber Security Awareness Checklist To Ensure It Asset Protection
Developing Cyber Security Awareness Cyber Security Awareness Checklist To Ensure It Asset ProtectionThe purpose of this slide is to outline a comprehensive checklist which can be used to ensure information technology IT asset protection. It cover points such as operating system is up to date, employees are using strong password policy etc. Introducing Developing Cyber Security Awareness Cyber Security Awareness Checklist To Ensure It Asset Protection to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Cyber Security, Awareness Checklist, IT Asset Protection, using this template. Grab it now to reap its full benefits.
-
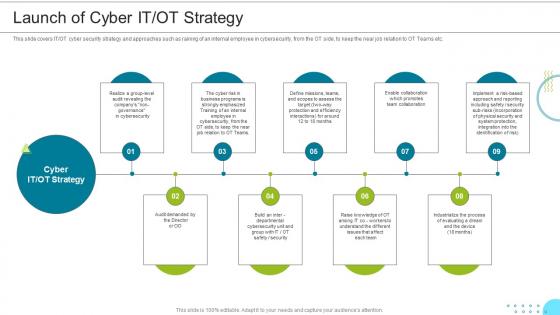 Launch Of Cyber It Ot Strategy Managing The Successful Convergence Of It And Ot
Launch Of Cyber It Ot Strategy Managing The Successful Convergence Of It And OtThis slide covers IT or OT cyber security strategy and approaches such as raining of an internal employee in cybersecurity, from the OT side, to keep the near job relation to OT Teams etc. Introducing Launch Of Cyber It Ot Strategy Managing The Successful Convergence Of It And Ot to increase your presentation threshold. Encompassed with nine stages, this template is a great option to educate and entice your audience. Dispence information on Strategy, Cybersecurity, Approaches, using this template. Grab it now to reap its full benefits
-
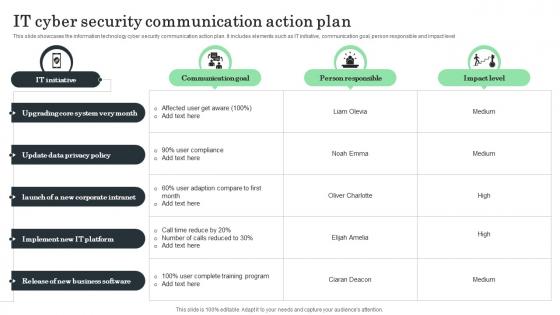 IT Cyber Security Communication Action Plan
IT Cyber Security Communication Action PlanThis slide showcases the information technology cyber security communication action plan. It includes elements such as IT initiative, communication goal, person responsible and impact level. Presenting our well structured IT Cyber Security Communication Action Plan The topics discussed in this slide are Communication Goal, Person Responsible, Impact Level. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
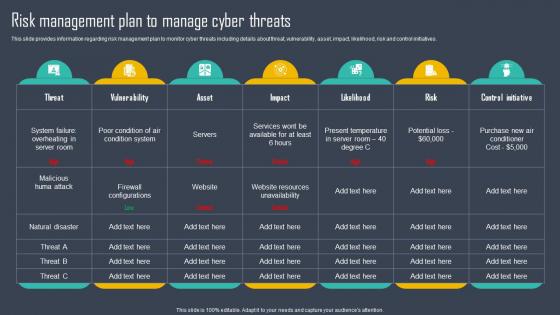 Strategic Framework To Manage IT Risk Management Plan To Manage Cyber Threats Strategy SS
Strategic Framework To Manage IT Risk Management Plan To Manage Cyber Threats Strategy SSThis slide provides information regarding risk management plan to monitor cyber threats including details about threat, vulnerability, asset, impact, likelihood, risk and control initiatives. Present the topic in a bit more detail with this Strategic Framework To Manage IT Risk Management Plan To Manage Cyber Threats Strategy SS. Use it as a tool for discussion and navigation on Risk Management Plan, Manage Cyber Threats, Vulnerability, Control Initiative. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
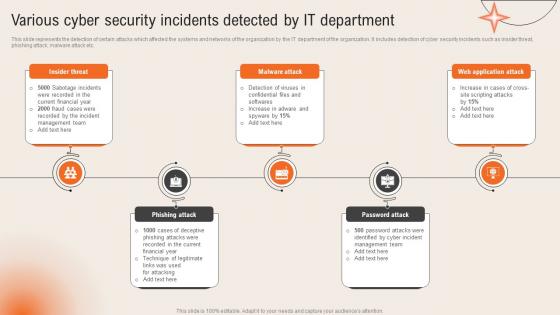 Various Cyber Security Incidents Detected By It Department Deploying Computer Security
Various Cyber Security Incidents Detected By It Department Deploying Computer SecurityThis slide represents the detection of certain attacks which affected the systems and networks of the organization by the IT department of the organization. It includes detection of cyber security incidents such as insider threat, phishing attack, malware attack etc.Introducing Various Cyber Security Incidents Detected By It Department Deploying Computer Security to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Current Financial, Sabotage Incidents, Technique Legitimate, using this template. Grab it now to reap its full benefits.
-
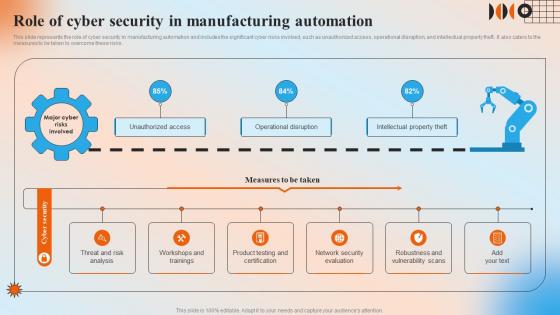 Role Of Cyber Security In Manufacturing Automation Automation In Manufacturing IT
Role Of Cyber Security In Manufacturing Automation Automation In Manufacturing ITThis slide represents the role of cyber security in manufacturing automation and includes the significant cyber risks involved, such as unauthorized access, operational disruption, and intellectual property theft. It also caters to the measures to be taken to overcome these risks. Present the topic in a bit more detail with this Role Of Cyber Security In Manufacturing Automation Automation In Manufacturing IT. Use it as a tool for discussion and navigation on Unauthorized Access, Operational Disruption, Intellectual Property Theft. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
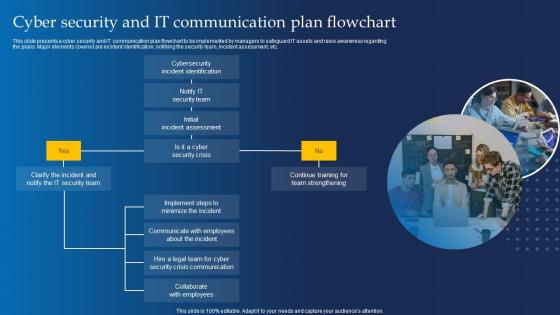 Cyber Security And It Communication Plan Flowchart
Cyber Security And It Communication Plan FlowchartThis slide presents a cyber security and IT communication plan flowchart to be implemented by managers to safeguard IT assets and raise awareness regarding the plans. Major elements covered are incident identification, notifying the security team, incident assessment, etc. Presenting our set of slides with Cyber Security And It Communication Plan Flowchart This exhibits information on one stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cybersecurity Incident Identification, Initial Incident Assessment
-
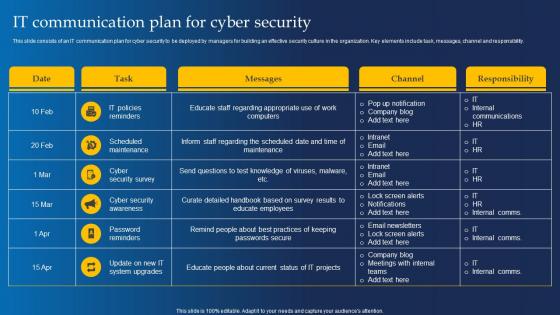 It Communication Plan For Cyber Security
It Communication Plan For Cyber SecurityThis slide consists of an IT communication plan for cyber security to be deployed by managers for building an effective security culture in the organization. Key elements include task, messages, channel and responsibility. Presenting our well structured It Communication Plan For Cyber Security The topics discussed in this slide are IT Policies Reminders, Scheduled MaintenanceThis is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
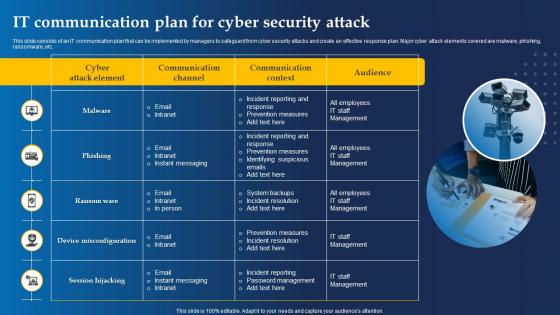 It Communication Plan For Cyber Security Attack
It Communication Plan For Cyber Security AttackThis slide consists of an IT communication plan that can be implemented by managers to safeguard from cyber security attacks and create an effective response plan. Major cyber attack elements covered are malware, phishing, ransomware, etc. Presenting our set of slides with It Communication Plan For Cyber Security Attack This exhibits information on one stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Malware, Phishing
-
 It Cyber Security Statistics Plan Related To Communication Sector
It Cyber Security Statistics Plan Related To Communication SectorThis slide consists of major statistics that relate to IT cyber security plans which can be used by managers to take action accordingly. Major statistics relate to budget, top risk, security architecture, cyber event, etc. Introducing our premium set of slides with It Cyber Security Statistics Plan Related To Communication Sector Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cyber Security, Communication Sector So download instantly and tailor it with your information.
-
 Various Cyber Security Incidents Detected By It Department Development And Implementation Of Security
Various Cyber Security Incidents Detected By It Department Development And Implementation Of SecurityThis slide represents the detection of certain attacks which affected the systems and networks of the organization by the IT department of the organization. It includes detection of cyber security incidents such as insider threat, phishing attack, malware attack etc. Increase audience engagement and knowledge by dispensing information using Various Cyber Security Incidents Detected By It Department Development And Implementation Of Security. This template helps you present information on five stages. You can also present information on Insider Threat, Phishing Attack, Malware Attack using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Risk Management Plan To Manage Cyber Threats IT Cost Optimization And Management Strategy SS
Risk Management Plan To Manage Cyber Threats IT Cost Optimization And Management Strategy SSThis slide provides information regarding risk management plan to monitor cyber threats including details about threat, vulnerability, asset, impact, likelihood, risk and control initiatives. Deliver an outstanding presentation on the topic using this Risk Management Plan To Manage Cyber Threats IT Cost Optimization And Management Strategy SS. Dispense information and present a thorough explanation of Threat, Vulnerability, Cyber Threats using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
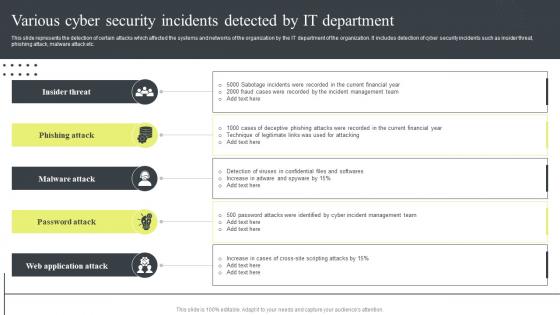 Cyber Security Attacks Response Plan Various Cyber Security Incidents Detected By It Department
Cyber Security Attacks Response Plan Various Cyber Security Incidents Detected By It DepartmentThis slide represents the detection of certain attacks which affected the systems and networks of the organization by the IT department of the organization. It includes detection of cyber security incidents such as insider threat, phishing attack, malware attack etc. Increase audience engagement and knowledge by dispensing information using Cyber Security Attacks Response Plan Various Cyber Security Incidents Detected By It Department. This template helps you present information on five stages. You can also present information on Insider Threat, Phishing Attack, Malware Attack, Password Attack using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Marketing Initiatives For Tech Segments Cybersecurity Develop Business Aligned IT Strategy
Marketing Initiatives For Tech Segments Cybersecurity Develop Business Aligned IT StrategyThis slide provides information regarding marketing initiatives for a technology firm across the cybersecurity segment. The slide includes goal and marketing initiatives such as prepare brand identity, etc. Increase audience engagement and knowledge by dispensing information using Marketing Initiatives For Tech Segments Cybersecurity Develop Business Aligned IT Strategy. This template helps you present information on three stages. You can also present information on Marketing Initiatives, Prepare Brand Identity, Formulate Thought Leadership using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
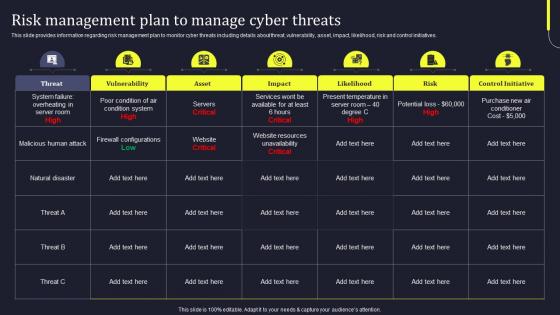 Risk Management Plan To Manage Cyber Threats Develop Business Aligned IT Strategy
Risk Management Plan To Manage Cyber Threats Develop Business Aligned IT StrategyThis slide provides information regarding risk management plan to monitor cyber threats including details about threat, vulnerability, asset, impact, likelihood, risk and control initiatives. Deliver an outstanding presentation on the topic using this Risk Management Plan To Manage Cyber Threats Develop Business Aligned IT Strategy. Dispense information and present a thorough explanation of Vulnerability, Likelihood, Control Initiative, Natural Disaster using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
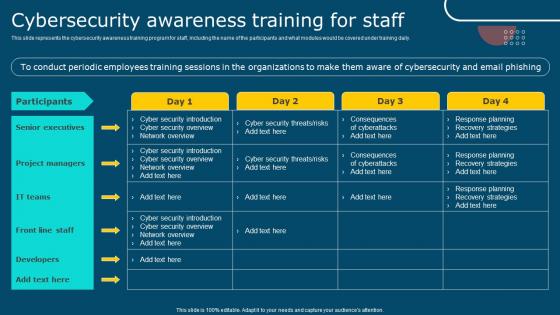 IT Policy Cybersecurity Awareness Training For Staff Ppt Infographics
IT Policy Cybersecurity Awareness Training For Staff Ppt InfographicsThis slide represents the cybersecurity awareness training program for staff, including the name of the participants and what modules would be covered under training daily. Present the topic in a bit more detail with this IT Policy Cybersecurity Awareness Training For Staff Ppt Infographics. Use it as a tool for discussion and navigation on Participants, Senior Executives, Project Managers, Front Line Staff. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Security Policy Checklist For Writing An Effective It Policy
Cyber Security Policy Checklist For Writing An Effective It PolicyThis slide describes the checklist for an effective information technology policy, and it includes all the best practices that should be considered while writing an IT policy. Present the topic in a bit more detail with this Cyber Security Policy Checklist For Writing An Effective It Policy. Use it as a tool for discussion and navigation on Assessment, Essential, Weaknesses. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
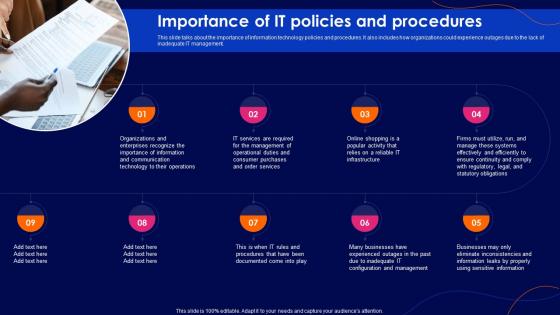 Cyber Security Policy Importance Of It Policies And Procedures
Cyber Security Policy Importance Of It Policies And ProceduresThis slide talks about the importance of information technology policies and procedures. It also includes how organizations could experience outages due to the lack of inadequate IT management. Increase audience engagement and knowledge by dispensing information using Cyber Security Policy Importance Of It Policies And Procedures. This template helps you present information on nine stages. You can also present information on Services, Operational, Management using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyber Security Policy It Ppt Show Graphics Template
Cyber Security Policy It Ppt Show Graphics TemplatePresent the topic in a bit more detail with this Cyber Security Policy It Ppt Show Graphics Template. Use it as a tool for discussion and navigation on Cyber Security Policy It. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Security Policy Post It Notes Ppt Show Example Introduction
Cyber Security Policy Post It Notes Ppt Show Example IntroductionIntroducing Cyber Security Policy Post It Notes Ppt Show Example Introduction to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Post It Notes, using this template. Grab it now to reap its full benefits.
-
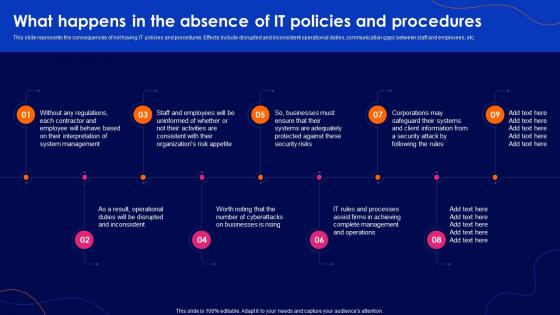 Cyber Security Policy What Happens In The Absence Of It Policies And Procedures
Cyber Security Policy What Happens In The Absence Of It Policies And ProceduresThis slide represents the consequences of not having IT policies and procedures. Effects include disrupted and inconsistent operational duties, communication gaps between staff and employees, etc. Introducing Cyber Security Policy What Happens In The Absence Of It Policies And Procedures to increase your presentation threshold. Encompassed with nine stages, this template is a great option to educate and entice your audience. Dispence information on Procedures, Information, Corporations, using this template. Grab it now to reap its full benefits.
-
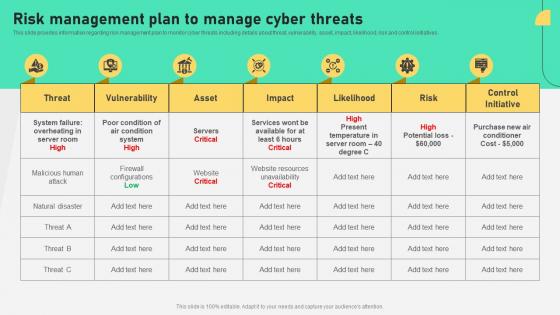 Risk Management Plan To Manage Cyber Threats Comprehensive Plan To Ensure It And Business
Risk Management Plan To Manage Cyber Threats Comprehensive Plan To Ensure It And BusinessThis slide provides information regarding risk management plan to monitor cyber threats including details about threat, vulnerability, asset, impact, likelihood, risk and control initiatives. Present the topic in a bit more detail with this Risk Management Plan To Manage Cyber Threats Comprehensive Plan To Ensure It And Business. Use it as a tool for discussion and navigation on Management, Information, Vulnerability. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Various Cyber Security Incidents Detected By IT Department Incident Response Strategies Deployment
Various Cyber Security Incidents Detected By IT Department Incident Response Strategies DeploymentThis slide represents the detection of certain attacks which affected the systems and networks of the organization by the IT department of the organization. It includes detection of cyber security incidents such as insider threat, phishing attack, malware attack etc. Introducing Various Cyber Security Incidents Detected By IT Department Incident Response Strategies Deployment to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Insider, Phishing, Application, using this template. Grab it now to reap its full benefits.
-
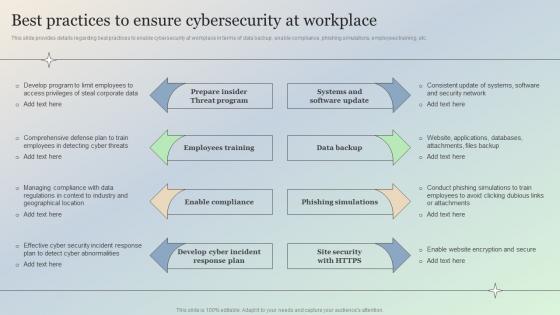 Best Practices To Ensure Cybersecurity At Workplace Managing IT Threats At Workplace Overview
Best Practices To Ensure Cybersecurity At Workplace Managing IT Threats At Workplace OverviewThis slide provides details regarding best practices to enable cybersecurity at workplace in terms of data backup, enable compliance, phishing simulations, employees training, etc. Introducing Best Practices To Ensure Cybersecurity At Workplace Managing IT Threats At Workplace Overview to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Employees, Develop, Security, using this template. Grab it now to reap its full benefits.
-
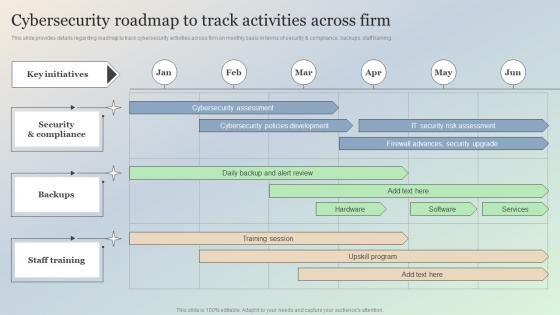 Cybersecurity Roadmap To Track Activities Across Firm Managing IT Threats At Workplace Overview
Cybersecurity Roadmap To Track Activities Across Firm Managing IT Threats At Workplace OverviewThis slide provides details regarding roadmap to track cybersecurity activities across firm on monthly basis in terms of security and compliance, backups, staff training. Deliver an outstanding presentation on the topic using this Cybersecurity Roadmap To Track Activities Across Firm Managing IT Threats At Workplace Overview. Dispense information and present a thorough explanation of Security, Backups, Training using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Enable Cybersecurity Compliance At Organization Managing IT Threats At Workplace Overview
Enable Cybersecurity Compliance At Organization Managing IT Threats At Workplace OverviewThis slide provides details regarding role of cybersecurity compliance at workplace. The importance of the security compliance include management of user trust, enhance business efficiency, secure brand reputation, etc. Increase audience engagement and knowledge by dispensing information using Enable Cybersecurity Compliance At Organization Managing IT Threats At Workplace Overview. This template helps you present information on eight stages. You can also present information on Cybersecurity, Confidentiality, Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Highlighting Ongoing Cybersecurity Trends Across Globe Managing IT Threats At Workplace Overview
Highlighting Ongoing Cybersecurity Trends Across Globe Managing IT Threats At Workplace OverviewThis slide provides details regarding cybersecurity trends existing across globe in terms of rise in automotive hacking, IoT with 5G, cloud platform as potential vulnerable, etc. Introducing Highlighting Ongoing Cybersecurity Trends Across Globe Managing IT Threats At Workplace Overview to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Automotive, Artificial, Potential, using this template. Grab it now to reap its full benefits.
-
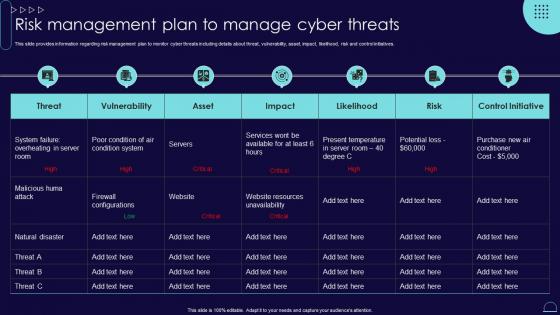 Risk Management Plan To Manage Cyber Threats Blueprint Develop Information It Roadmap Strategy Ss
Risk Management Plan To Manage Cyber Threats Blueprint Develop Information It Roadmap Strategy SsThis slide provides information regarding risk management plan to monitor cyber threats including details about threat, vulnerability, asset, impact, likelihood, risk and control initiatives. Present the topic in a bit more detail with this Risk Management Plan To Manage Cyber Threats Blueprint Develop Information It Roadmap Strategy Ss. Use it as a tool for discussion and navigation on Management, Information, Vulnerability. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
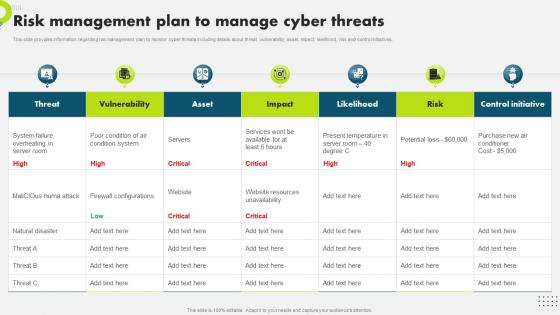 Risk Management Plan To Manage Cyber Threats Strategic Plan To Secure It Infrastructure Strategy SS V
Risk Management Plan To Manage Cyber Threats Strategic Plan To Secure It Infrastructure Strategy SS VThis slide provides information regarding risk management plan to monitor cyber threats including details about threat, vulnerability, asset, impact, likelihood, risk and control initiatives. Present the topic in a bit more detail with this Risk Management Plan To Manage Cyber Threats Strategic Plan To Secure It Infrastructure Strategy SS V. Use it as a tool for discussion and navigation on Risk Management, Initiatives, Information. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 IoT In Manufacturing IT Managing Cyber Security In Manufacturing 30 Days Plan
IoT In Manufacturing IT Managing Cyber Security In Manufacturing 30 Days PlanThis slide describes the first 30 days of managing cyber security in the manufacturing operations plan. It includes metric names, items to be measured, measurement method, time, and teams who are responsible and details. Deliver an outstanding presentation on the topic using this IoT In Manufacturing IT Managing Cyber Security In Manufacturing 30 Days Plan. Dispense information and present a thorough explanation of Managing, Security, Manufacturing using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
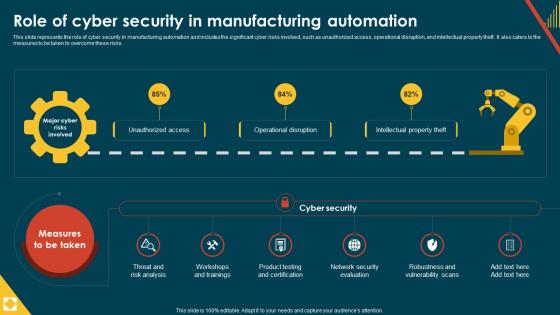 IoT In Manufacturing IT Role Of Cyber Security In Manufacturing Automation
IoT In Manufacturing IT Role Of Cyber Security In Manufacturing AutomationThis slide represents the role of cyber security in manufacturing automation and includes the significant cyber risks involved, such as unauthorized access, operational disruption, and intellectual property theft. It also caters to the measures to be taken to overcome these risks. Deliver an outstanding presentation on the topic using this IoT In Manufacturing IT Role Of Cyber Security In Manufacturing Automation. Dispense information and present a thorough explanation of Security, Manufacturing, Automation using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
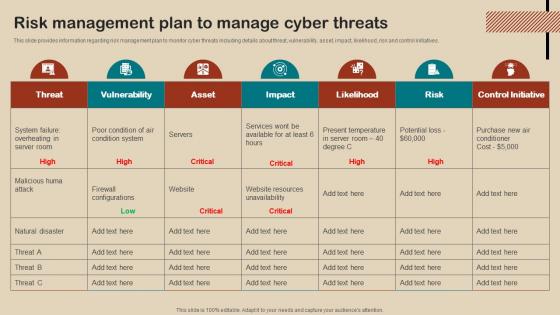 IT Strategy Planning Guide Risk Management Plan To Manage Cyber Threats Strategy SS V
IT Strategy Planning Guide Risk Management Plan To Manage Cyber Threats Strategy SS VThis slide provides information regarding risk management plan to monitor cyber threats including details about threat, vulnerability, asset, impact, likelihood, risk and control initiatives. Present the topic in a bit more detail with this IT Strategy Planning Guide Risk Management Plan To Manage Cyber Threats Strategy SS V. Use it as a tool for discussion and navigation on Risk Management Plan, Manage Cyber Threats, Natural Disaster, Website Resources Unavailability. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
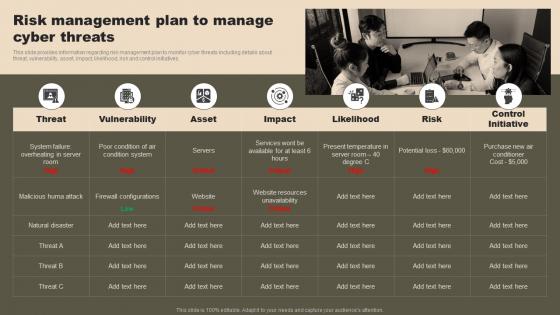 Risk Management Plan To Manage Cyber Threats Strategic Initiatives To Boost IT Strategy SS V
Risk Management Plan To Manage Cyber Threats Strategic Initiatives To Boost IT Strategy SS VThis slide provides information regarding risk management plan to monitor cyber threats including details about threat, vulnerability, asset, impact, likelihood, risk and control initiatives. Increase audience engagement and knowledge by dispensing information using Risk Management Plan To Manage Cyber Threats Strategic Initiatives To Boost IT Strategy SS V. This template helps you present information on seven stages. You can also present information on Plan, Management, Risk using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
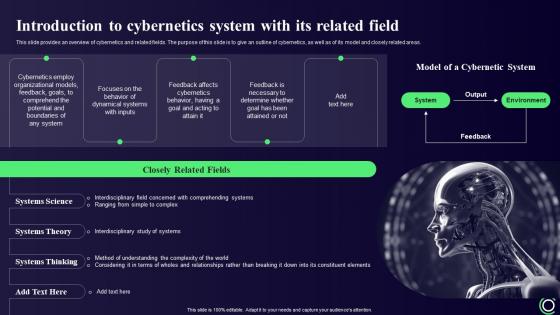 Cybernetics Introduction To Cybernetics System With Its Related Field
Cybernetics Introduction To Cybernetics System With Its Related FieldThis slide provides an overview of cybernetics and related fields. The purpose of this slide is to give an outline of cybernetics, as well as of its model and closely related areas. Deliver an outstanding presentation on the topic using this Cybernetics Introduction To Cybernetics System With Its Related Field. Dispense information and present a thorough explanation of Introduction, Cybernetics, Overview using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
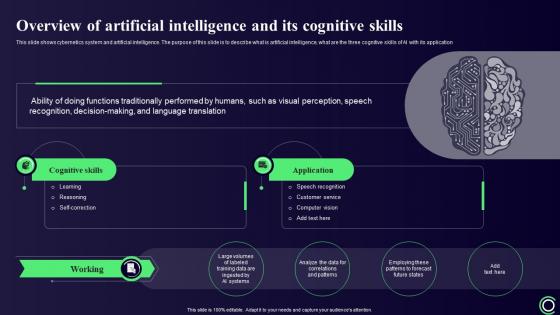 Cybernetics Overview Of Artificial Intelligence And Its Cognitive Skills
Cybernetics Overview Of Artificial Intelligence And Its Cognitive SkillsThis slide shows cybernetics system and artificial intelligence. The purpose of this slide is to describe what is artificial intelligence, what are the three cognitive skills of AI with its application Present the topic in a bit more detail with this Cybernetics Overview Of Artificial Intelligence And Its Cognitive Skills. Use it as a tool for discussion and navigation on Overview, Cognitive Skills, Application. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
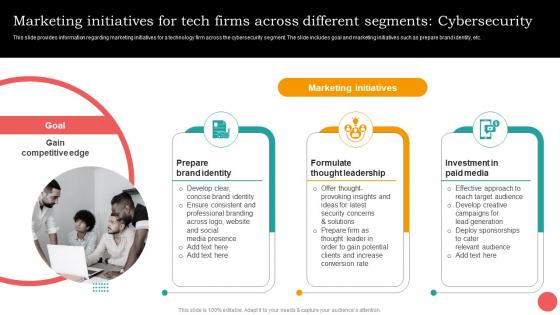 Marketing Initiatives Different Segments Cybersecurity Cios Guide For It Strategy Strategy SS V
Marketing Initiatives Different Segments Cybersecurity Cios Guide For It Strategy Strategy SS VThis slide provides information regarding marketing initiatives for a technology firm across the cybersecurity segment. The slide includes goal and marketing initiatives such as prepare brand identity, etc. Deliver an outstanding presentation on the topic using this Marketing Initiatives Different Segments Cybersecurity Cios Guide For It Strategy Strategy SS V. Dispense information and present a thorough explanation of Prepare Brand Identity, Formulate Thought Leadership, Investment In Paid Media using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
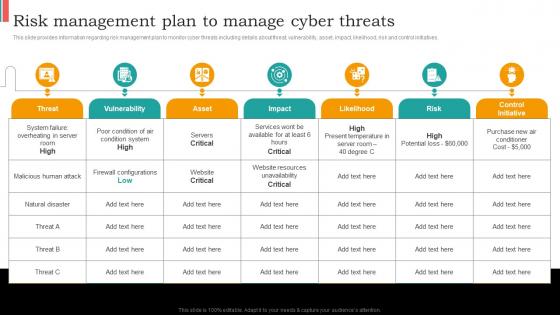 Risk Management Plan To Manage Cyber Threats Cios Guide For It Strategy Strategy SS V
Risk Management Plan To Manage Cyber Threats Cios Guide For It Strategy Strategy SS VThis slide provides information regarding risk management plan to monitor cyber threats including details about threat, vulnerability, asset, impact, likelihood, risk and control initiatives. Present the topic in a bit more detail with this Risk Management Plan To Manage Cyber Threats Cios Guide For It Strategy Strategy SS V. Use it as a tool for discussion and navigation on Risk Management, Vulnerability, Likelihood . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 IT Threats Cyber Security Malware Illustration
IT Threats Cyber Security Malware IllustrationThis PowerPoint Illustration depicts a computer with a red warning sign and is an ideal visual representation of IT threats. It can be used to highlight the dangers of cyber security and the need for proactive measures to protect data.
-
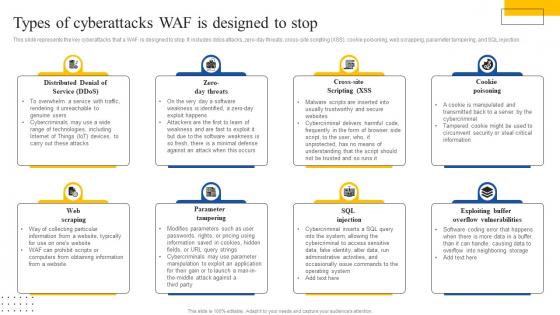 Web Application Firewall Introduction It Types Of Cyberattacks WAF Is Designed To Stop
Web Application Firewall Introduction It Types Of Cyberattacks WAF Is Designed To StopThis slide represents the key cyberattacks that a WAF is designed to stop. It includes ddos attacks, zero day threats, cross site scripting XSS, cookie poisoning, web scrapping, parameter tampering, and SQL injection. Introducing Web Application Firewall Introduction It Types Of Cyberattacks WAF Is Designed To Stop. to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Distributed Denial, Zero Day Threats, Cross Site Scripting Xss, using this template. Grab it now to reap its full benefits.
-
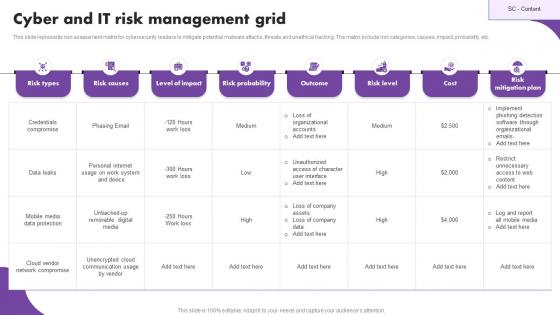 Cyber And IT Risk Management Grid
Cyber And IT Risk Management GridThis slide represents risk assessment matrix for cybersecurity leaders to mitigate potential malware attacks, threats and unethical hacking. The matrix include risk categories, causes, impact, probability, etc. Introducing our Cyber And IT Risk Management Grid set of slides. The topics discussed in these slides are Risk Types, Level Of Impact, Risk Probability. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 How Chatgpt Can Help In Preventing Cyber Crimes Open Ai Language Model It
How Chatgpt Can Help In Preventing Cyber Crimes Open Ai Language Model ItThis slide demonstrates the various applications of chatGPT in the field of cybersecurity. The purpose of this slide is to explain how chatGPT can help in predicting and avoiding cyber crimes. These include threat intelligence, anomaly detection, predictive analytics, etc. Deliver an outstanding presentation on the topic using this How Chatgpt Can Help In Preventing Cyber Crimes Open Ai Language Model It. Dispense information and present a thorough explanation of Threat Intelligence, Anomaly Detection, Predictive Analytics using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Multiple cyber security services offered by it solutions company
Multiple cyber security services offered by it solutions companyPresenting this set of slides with name Multiple Cyber Security Services Offered By It Solutions Company. This is a eight stage process. The stages in this process are Secure Payment, Global Secure, Computer Security, Mobile Security, Online Privacy. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
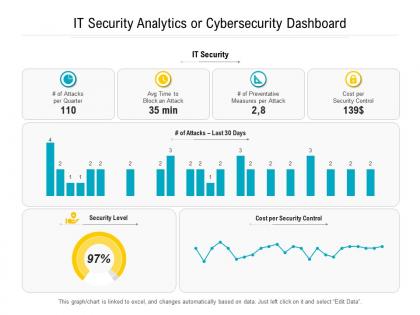 It security analytics or cybersecurity dashboard
It security analytics or cybersecurity dashboardPresenting this set of slides with name It Security Analytics Or Cybersecurity Dashboard. The topics discussed in these slides are IT Security, Cost per Security Control, Security Level. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 It cyber security chip icon for network protection
It cyber security chip icon for network protectionPresenting this set of slides with name IT Cyber Security Chip Icon For Network Protection. This is a three stage process. The stages in this process are IT Cyber Security Chip Icon For Network Protection. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
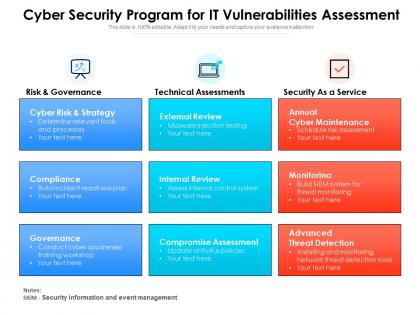 Cyber security program for it vulnerabilities assessment
Cyber security program for it vulnerabilities assessmentPresenting this set of slides with name Cyber Security Program For It Vulnerabilities Assessment. This is a three stage process. The stages in this process are Risk And Governance, Technical Assessments, Security As A Service. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 It analyst presenting cyber security program framework
It analyst presenting cyber security program frameworkPresenting this set of slides with name IT Analyst Presenting Cyber Security Program Framework. This is a one stage process. The stages in this process are IT Analyst Presenting Cyber Security Program Framework. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
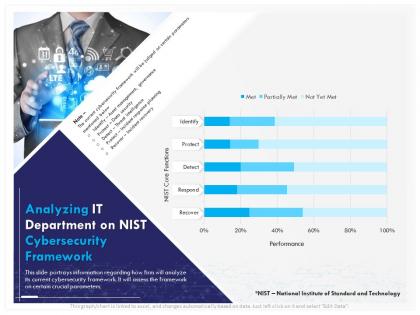 Analyzing it department on nist cybersecurity framework respond ppt gridlines
Analyzing it department on nist cybersecurity framework respond ppt gridlinesThis slide portrays information regarding how firm will analyze its current cybersecurity framework. It will assess the framework on certain crucial parameters. Presenting this set of slides with name Analyzing IT Department On Nist Cybersecurity Framework Respond Ppt Gridlines. The topics discussed in these slides are Analyzing IT Department On NIST Cybersecurity Framework. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
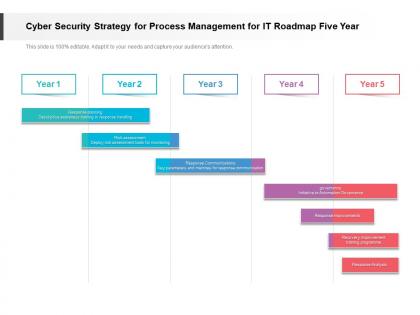 Cyber security strategy for process management for it roadmap five year
Cyber security strategy for process management for it roadmap five yearPresenting Cyber Security Strategy For Process Management For IT Roadmap Five Year PowerPoint slide. This PPT theme is available in both 4,3 and 16,9 aspect ratios. This PowerPoint template is customizable so you can modify the font size, font type, color, and shapes as per your requirements. This PPT presentation is Google Slides compatible hence it is easily accessible. You can download and save this PowerPoint layout in different formats like PDF, PNG, and JPG.
-
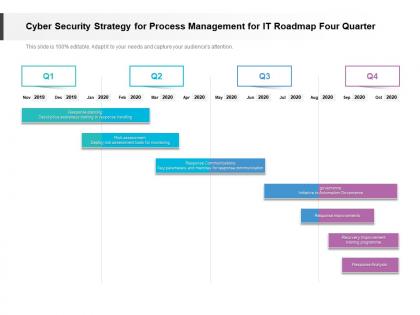 Cyber security strategy for process management for it roadmap four quarter
Cyber security strategy for process management for it roadmap four quarterPresenting Cyber Security Strategy For Process Management For IT Roadmap Four Quarter PowerPoint Template. This PPT presentation is Google Slides compatible hence it is easily accessible. You can download and save this PowerPoint layout in different formats like PDF, PNG, and JPG. This PPT theme is available in both 4,3 and 16,9 aspect ratios. This PowerPoint template is customizable so you can modify the font size, font type, color, and shapes as per your requirements.
-
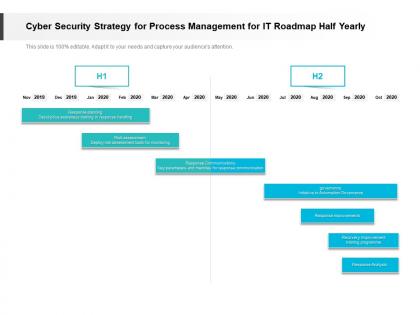 Cyber security strategy for process management for it roadmap half yearly
Cyber security strategy for process management for it roadmap half yearlyPresenting Cyber Security Strategy For Process Management For IT Roadmap Half Yearly PowerPoint slide which is 100 percent editable. You can change the color, font size, font type, and shapes of this PPT layout according to your needs. This PPT template is compatible with Google Slides and is available in both 4,3 and 16,9 aspect ratios. This ready to use PowerPoint presentation can be downloaded in various formats like PDF, JPG, and PNG.
-
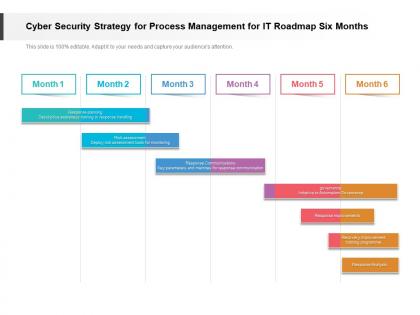 Cyber security strategy for process management for it roadmap six months
Cyber security strategy for process management for it roadmap six monthsPresenting Cyber Security Strategy For Process Management For IT Roadmap Six Months PowerPoint slide. This PPT presentation is Google Slides compatible hence it is easily accessible. This PPT theme is available in both 4,3 and 16,9 aspect ratios. This PowerPoint template is customizable so you can modify the font size, font type, color, and shapes as per your requirements. You can download and save this PowerPoint layout in different formats like PDF, PNG, and JPG.
-
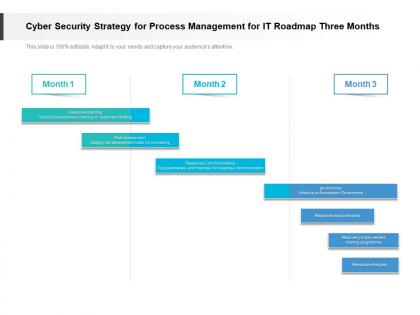 Cyber security strategy for process management for it roadmap three months
Cyber security strategy for process management for it roadmap three monthsPresenting Cyber Security Strategy For Process Management For IT Roadmap Three Months PowerPoint slide. This PPT slide is available at 4,3 and 16,9 aspect ratios. You can download this PPT theme in various formats like PDF, PNG, and JPG. This PowerPoint template is completely editable and you can modify the font size, font type, and shapes as per your requirements. Our PPT layout is compatible with Google Slides.



