Powerpoint Templates and Google slides for IT Infrastructure Services
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
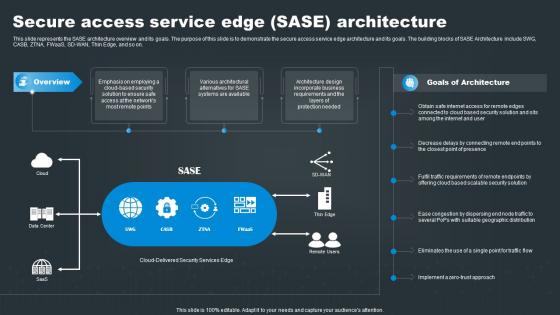 Secure Access Service Edge SASE Architecture SASE Network Security
Secure Access Service Edge SASE Architecture SASE Network SecurityThis slide represents the SASE architecture overview and its goals. The purpose of this slide is to demonstrate the secure access service edge architecture and its goals. The building blocks of SASE Architecture include SWG, CASB, ZTNA, FWaaS, SD WAN, Thin Edge, and so on. Present the topic in a bit more detail with this Secure Access Service Edge SASE Architecture SASE Network Security. Use it as a tool for discussion and navigation on Connected, Presence, Scalable. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
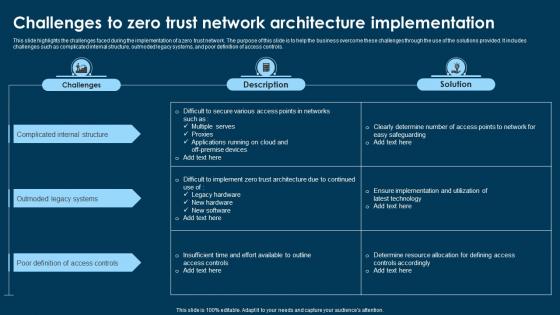 Challenges To Zero Trust Network Architecture Implementation
Challenges To Zero Trust Network Architecture ImplementationThis slide highlights the challenges faced during the implementation of a zero trust network. The purpose of this slide is to help the business overcome these challenges through the use of the solutions provided. It includes challenges such as complicated internal structure, outmoded legacy systems, and poor definition of access controls. Presenting our well structured Challenges To Zero Trust Network Architecture Implementation. The topics discussed in this slide are Complicated Internal Structure, Outmoded Legacy Systems, Poor Definition Access Controls. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Icon For Network Security Through Zero Trust Architecture
Icon For Network Security Through Zero Trust ArchitecturePresenting our set of slides with Icon For Network Security Through Zero Trust Architecture. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Icon Network Security, Zero Trust Architecture.
-
 Icon For Zero Trust Network Architecture
Icon For Zero Trust Network ArchitectureIntroducing our premium set of slides with Icon For Zero Trust Network Architecture. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Icon Zero Trust, Network Architecture. So download instantly and tailor it with your information.
-
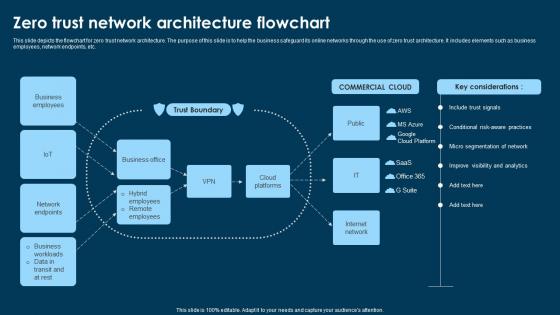 Zero Trust Network Architecture Flowchart
Zero Trust Network Architecture FlowchartThis slide depicts the flowchart for zero trust network architecture. The purpose of this slide is to help the business safeguard its online networks through the use of zero trust architecture. It includes elements such as business employees, network endpoints, etc. Introducing our Zero Trust Network Architecture Flowchart set of slides. The topics discussed in these slides are Trust Boundary, Business Office, COMMERCIAL CLOUD. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
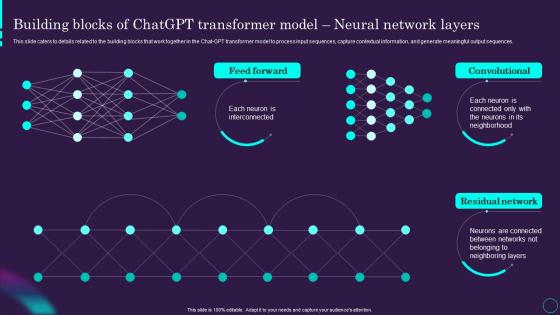 Building Model Neural Network Layers Chatgpt Ai Powered Architecture Explained ChatGPT SS
Building Model Neural Network Layers Chatgpt Ai Powered Architecture Explained ChatGPT SSThis slide caters to details related to the building blocks that work together in the Chat-GPT transformer model to process input sequences, capture contextual information, and generate meaningful output sequences. Deliver an outstanding presentation on the topic using this Building Model Neural Network Layers Chatgpt Ai Powered Architecture Explained ChatGPT SS. Dispense information and present a thorough explanation of Transformer, Neighborhood, Convolutional using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
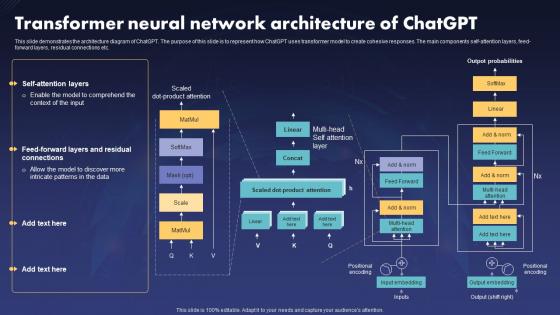 Transformer Neural Network Architecture Of ChatGPT V2
Transformer Neural Network Architecture Of ChatGPT V2This slide demonstrates the architecture diagram of ChatGPT. The purpose of this slide is to represent how ChatGPT uses transformer model to create cohesive responses. The main components self-attention layers, feed-forward layers, residual connections etc. Deliver an outstanding presentation on the topic using this Transformer Neural Network Architecture Of ChatGPT V2. Dispense information and present a thorough explanation of Transformer Neural Network Architecture, Residual Connections, Create Cohesive Responses using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
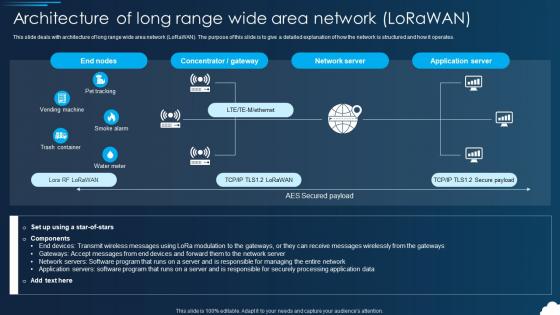 Lorawan Architecture Of Long Range Wide Area Network Lorawan
Lorawan Architecture Of Long Range Wide Area Network LorawanThis slide deals with architecture of long range wide area network LoRaWAN. The purpose of this slide is to give a detailed explanation of how the network is structured and how it operates. Present the topic in a bit more detail with this Lorawan Architecture Of Long Range Wide Area Network Lorawan. Use it as a tool for discussion and navigation on Architecture, Application, Servers. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
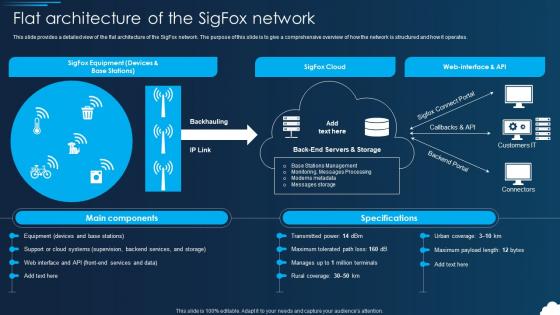 Lorawan Flat Architecture Of The Sigfox Network Ppt Slides Example File
Lorawan Flat Architecture Of The Sigfox Network Ppt Slides Example FileThis slide provides a detailed view of the flat architecture of the SigFox network. The purpose of this slide is to give a comprehensive overview of how the network is structured and how it operates. Present the topic in a bit more detail with this Lorawan Flat Architecture Of The Sigfox Network Ppt Slides Example File. Use it as a tool for discussion and navigation on Architecture, Services, Backhauling. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
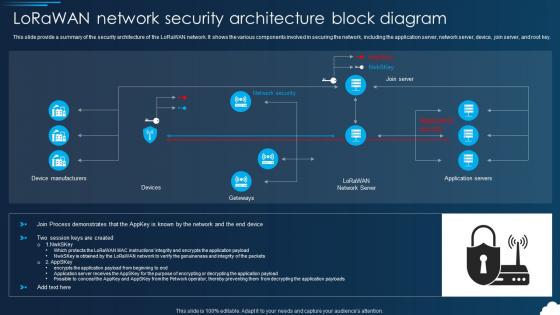 Lorawan Lorawan Network Security Architecture Block Diagram
Lorawan Lorawan Network Security Architecture Block DiagramThis slide provide a summary of the security architecture of the LoRaWAN network. It shows the various components involved in securing the network, including the application server, network server, device, join server, and root key. Present the topic in a bit more detail with this Lorawan Lorawan Network Security Architecture Block Diagram. Use it as a tool for discussion and navigation on Device Manufacturers, Architecture, Application Servers . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
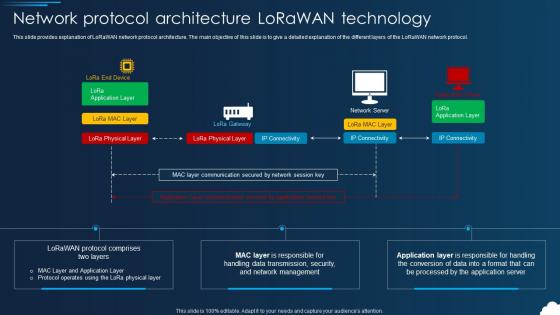 Lorawan Network Protocol Architecture Lorawan Technology
Lorawan Network Protocol Architecture Lorawan TechnologyThis slide provides explanation of LoRaWAN network protocol architecture. The main objective of this slide is to give a detailed explanation of the different layers of the LoRaWAN network protocol. Deliver an outstanding presentation on the topic using this Lorawan Network Protocol Architecture Lorawan Technology. Dispense information and present a thorough explanation of Technology, Protocol, Architecture using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
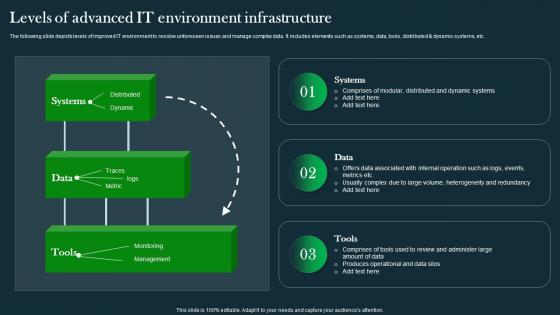 Levels Of Advanced It Environment Infrastructure IT Operations Automation An AIOps AI SS V
Levels Of Advanced It Environment Infrastructure IT Operations Automation An AIOps AI SS VThe following slide depicts levels of improved IT environment to resolve unforeseen issues and manage complex data. It includes elements such as systems, data, tools, distributed dynamic systems, etc.Deliver an outstanding presentation on the topic using this Levels Of Advanced It Environment Infrastructure IT Operations Automation An AIOps AI SS V. Dispense information and present a thorough explanation of Modular Distributed, Amount Data, Produces Operational using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
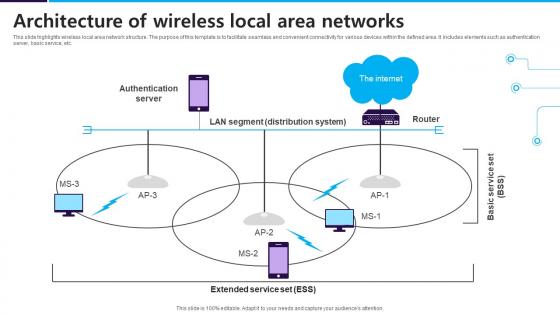 Architecture Of Wireless Local Area Networks
Architecture Of Wireless Local Area NetworksThis slide highlights wireless local area network structure. The purpose of this template is to facilitate seamless and convenient connectivity for various devices within the defined area. It includes elements such as authentication server, basic service, etc. Introducing our Architecture Of Wireless Local Area Networks set of slides. The topics discussed in these slides are Authentication Server, The Internet. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
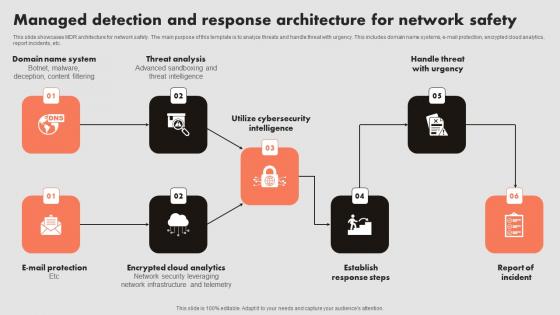 Managed Detection And Response Architecture For Network Safety
Managed Detection And Response Architecture For Network SafetyThis slide showcases MDR architecture for network safety. The main purpose of this template is to analyze threats and handle threat with urgency. This includes domain name systems, e-mail protection, encrypted cloud analytics, report incidents, etc. Presenting our well structured Managed Detection And Response Architecture For Network Safety. The topics discussed in this slide are System, Analysis, Intelligence. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
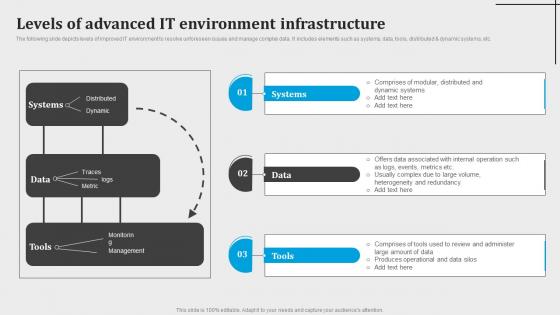 Levels Of Advanced It Environment Infrastructure Introduction To Aiops AI SS V
Levels Of Advanced It Environment Infrastructure Introduction To Aiops AI SS VThe following slide depicts levels of improved IT environment to resolve unforeseen issues and manage complex data. It includes elements such as systems, data, tools, distributed and dynamic systems, etc. Introducing Levels Of Advanced It Environment Infrastructure Introduction To Aiops AI SS V to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Systems, Data, using this template. Grab it now to reap its full benefits.
-
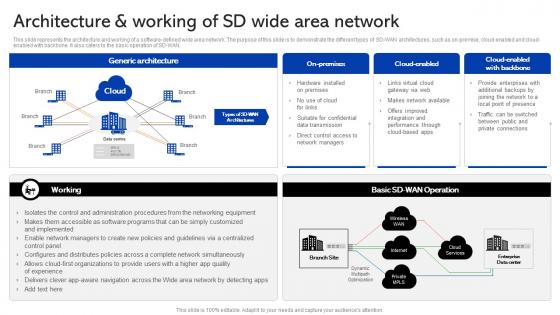 Sase Security Architecture And Working Of Sd Wide Area Network
Sase Security Architecture And Working Of Sd Wide Area NetworkThis slide represents the architecture and working of a software-defined wide area network. The purpose of this slide is to demonstrate the different types of SD-WAN architectures, such as on-premise, cloud-enabled and cloud-enabled with backbone. It also caters to the basic operation of SD-WAN. Present the topic in a bit more detail with this Sase Security Architecture And Working Of Sd Wide Area Network. Use it as a tool for discussion and navigation on Architecture, Enterprises, Connections. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
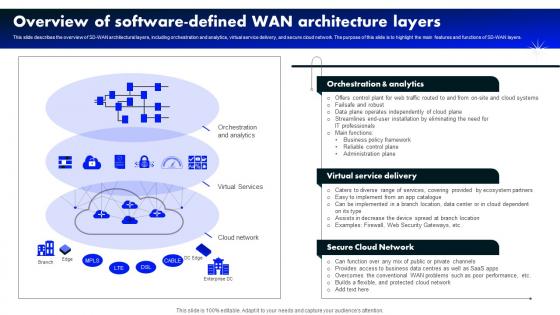 Overview Of Software Defined Wan Architecture Layers Software Defined Wide Area Network
Overview Of Software Defined Wan Architecture Layers Software Defined Wide Area NetworkThis slide describes the overview of SD-WAN architectural layers, including orchestration and analytics, virtual service delivery, and secure cloud network. The purpose of this slide is to highlight the main features and functions of SD-WAN layers. Present the topic in a bit more detail with this Overview Of Software Defined Wan Architecture Layers Software Defined Wide Area Network. Use it as a tool for discussion and navigation on Orchestration Analytics, Virtual Service Delivery, Secure Cloud Network. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
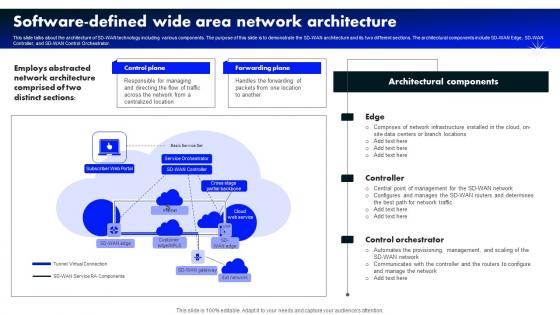 Software Wide Area Network Architecture Software Defined Wide Area Network
Software Wide Area Network Architecture Software Defined Wide Area NetworkThis slide talks about the architecture of SD-WAN technology including various components. The purpose of this slide is to demonstrate the SD-WAN architecture and its two different sections. The architectural components include SD-WAN Edge, SD-WAN Controller, and SD-WAN Control Orchestrator. Deliver an outstanding presentation on the topic using this Software Wide Area Network Architecture Software Defined Wide Area Network. Dispense information and present a thorough explanation of Architecture, Software, Management using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
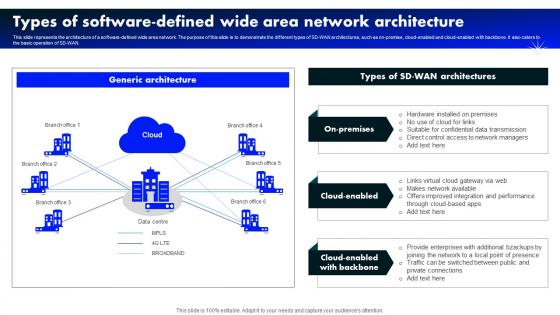 Types Of Software Defined Wide Area Network Architecture Software Defined Wide Area Network
Types Of Software Defined Wide Area Network Architecture Software Defined Wide Area NetworkThis slide represents the architecture of a software-defined wide area network. The purpose of this slide is to demonstrate the different types of SD-WAN architectures, such as on-premise, cloud-enabled and cloud-enabled with backbone. It also caters to the basic operation of SD-WAN. Deliver an outstanding presentation on the topic using this Types Of Software Defined Wide Area Network Architecture Software Defined Wide Area Network. Dispense information and present a thorough explanation of On Premises, Cloud Enabled, Architecture using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
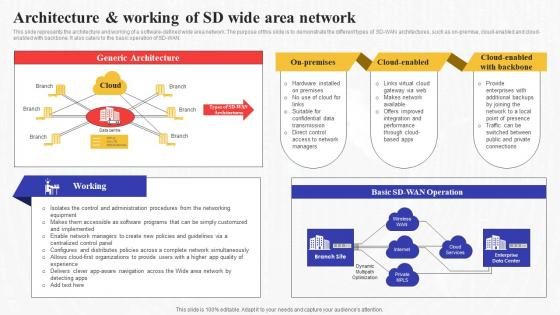 Architecture And Working Of Sd Wide Area Network Secure Access Service Edge Sase
Architecture And Working Of Sd Wide Area Network Secure Access Service Edge SaseThis slide represents the architecture and working of a software-defined wide area network. The purpose of this slide is to demonstrate the different types of SD-WAN architectures, such as on-premise, cloud-enabled and cloud-enabled with backbone. It also caters to the basic operation of SD-WAN. Present the topic in a bit more detail with this Architecture And Working Of Sd Wide Area Network Secure Access Service Edge Sase. Use it as a tool for discussion and navigation on Architecture, Enterprises, Connections. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
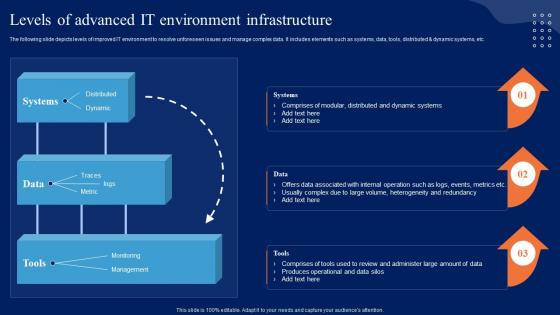 Levels Of Advanced It Environment Infrastructure Comprehensive Guide To Begin AI SS V
Levels Of Advanced It Environment Infrastructure Comprehensive Guide To Begin AI SS VThe following slide depicts levels of improved IT environment to resolve unforeseen issues and manage complex data. It includes elements such as systems, data, tools, distributed dynamic systems, etc.Present the topic in a bit more detail with this Levels Of Advanced It Environment Infrastructure Comprehensive Guide To Begin AI SS V. Use it as a tool for discussion and navigation on Modular Distributed, Internal Operation, Heterogeneity Redundancy. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
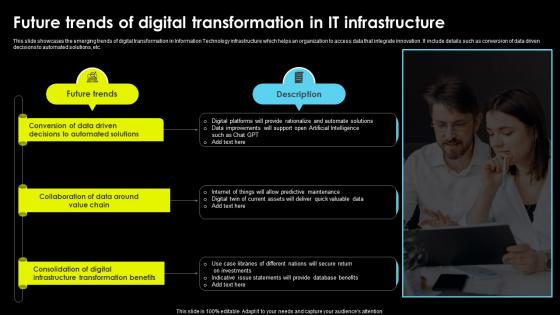 Future Trends Of Digital Transformation In It Infrastructure
Future Trends Of Digital Transformation In It InfrastructureThis slide showcases the emerging trends of digital transformation in Information Technology infrastructure which helps an organization to access data that integrate innovation. It include details such as conversion of data driven decisions to automated solutions, etc. Introducing our premium set of slides with Future Trends Of Digital Transformation In It Infrastructure. Ellicudate the one stage and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Decisions Automated, Collaboration Data Around, Predictive Maintenance. So download instantly and tailor it with your information.
-
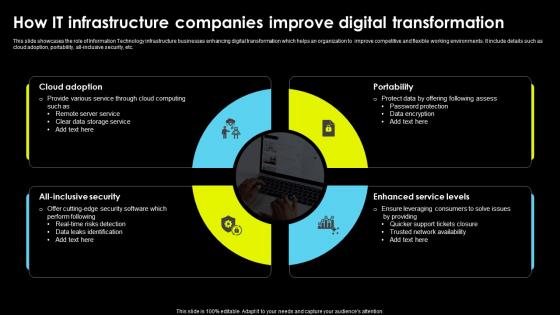 How It Infrastructure Companies Improve Digital Transformation
How It Infrastructure Companies Improve Digital TransformationThis slide showcases the role of Information Technology infrastructure businesses enhancing digital transformation which helps an organization to improve competitive and flexible working environments. It include details such as cloud adoption, portability, all-inclusive security, etc.Presenting our set of slides with How It Infrastructure Companies Improve Digital Transformation. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cloud Adoption, Enhanced Service Levels, Ensure Leveraging Consumers.
-
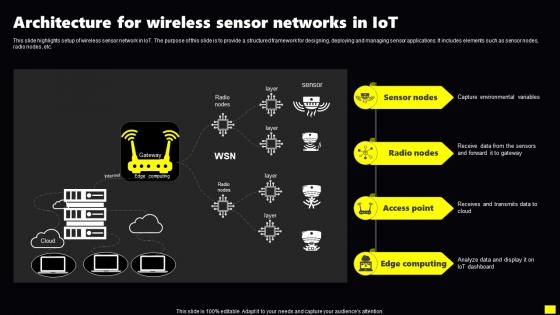 Architecture For Wireless Sensor Networks In IoT
Architecture For Wireless Sensor Networks In IoTThis slide highlights setup of wireless sensor network in IoT. The purpose of this slide is to provide a structured framework for designing, deploying and managing sensor applications. It includes elements such as sensor nodes, radio nodes, etc.Presenting our well structured Architecture For Wireless Sensor Networks In IoT. The topics discussed in this slide are Capture Environmental Variables, Forward Gateway, Edge Computing. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
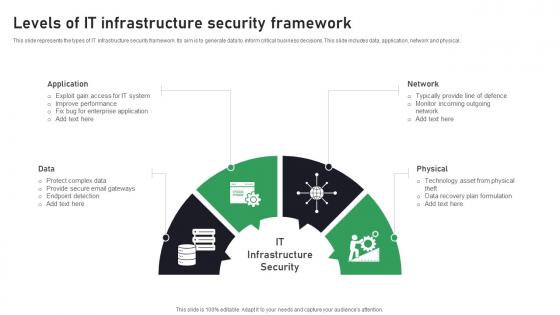 Levels Of IT Infrastructure Security Framework
Levels Of IT Infrastructure Security FrameworkThis slide represents the types of IT infrastructure security framework. Its aim is to generate data to inform critical business decisions. This slide includes data, application, network and physical. Introducing our premium set of slides with Levels Of IT Infrastructure Security Framework. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Protect, Secure, Application. So download instantly and tailor it with your information.
-
 Types Of Threats In IT Infrastructure Security
Types Of Threats In IT Infrastructure SecurityThis slide showcases the common threats faced in infrastructure security. Its aim is to identify threats and eliminate them. This slide includes phishing, ransomware, botnet and physical theft. Presenting our set of slides with Types Of Threats In IT Infrastructure Security. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Infrastructure, Personal, Exploitation.
-
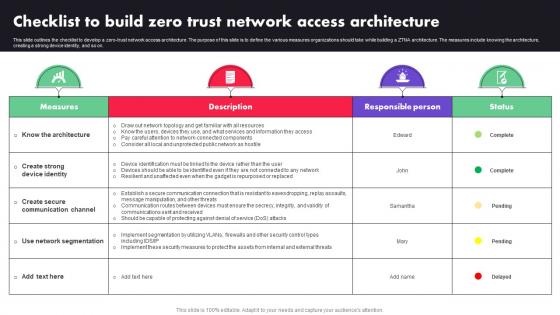 Checklist To Build Zero Trust Network Access Architecture Ppt Diagram Lists
Checklist To Build Zero Trust Network Access Architecture Ppt Diagram ListsThis slide outlines the checklist to develop a zero-trust network access architecture. The purpose of this slide is to define the various measures organizations should take while building a ZTNA architecture. The measures include knowing the architecture, creating a strong device identity, and so on. Deliver an outstanding presentation on the topic using this Checklist To Build Zero Trust Network Access Architecture Ppt Diagram Lists. Dispense information and present a thorough explanation of Public Network, Network Topology, Devices using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
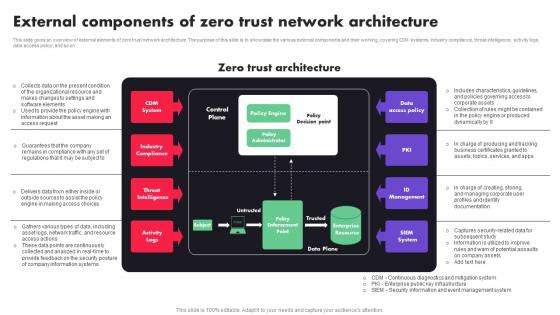 External Components Of Zero Trust Network Architecture Ppt File Example File
External Components Of Zero Trust Network Architecture Ppt File Example FileThis slide gives an overview of external elements of zero trust network architecture. The purpose of this slide is to showcase the various external components and their working, covering CDM systems, industry compliance, threat intelligence, activity logs, data access policy, and so on. Deliver an outstanding presentation on the topic using this External Components Of Zero Trust Network Architecture Ppt File Example File. Dispense information and present a thorough explanation of CDM System, Industry Compliance, Threat Intelligence using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
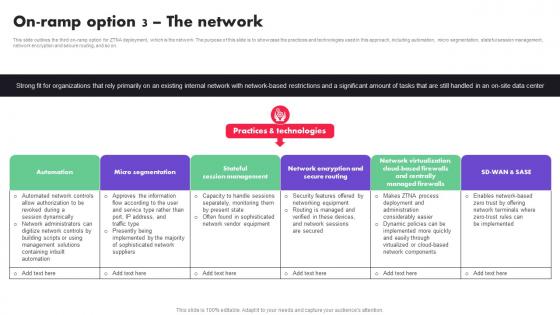 On Ramp Option 3 The Network Zero Trust Architecture ZTA
On Ramp Option 3 The Network Zero Trust Architecture ZTAThis slide outlines the third on-ramp option for ZTNA deployment, which is the network. The purpose of this slide is to showcase the practices and technologies used in this approach, including automation, micro segmentation, stateful session management, network encryption and secure routing, and so on. Introducing On Ramp Option 3 The Network Zero Trust Architecture ZTA to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Automation, Micro segmentation, session management, using this template. Grab it now to reap its full benefits.
-
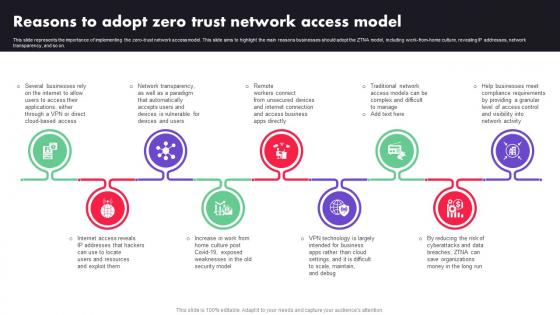 Reasons To Adopt Zero Trust Network Access Model Zero Trust Architecture ZTA
Reasons To Adopt Zero Trust Network Access Model Zero Trust Architecture ZTAThis slide represents the importance of implementing the zero-trust network access model. This slide aims to highlight the main reasons businesses should adopt the ZTNA model, including work-from-home culture, revealing IP addresses, network transparency, and so on. Introducing Reasons To Adopt Zero Trust Network Access Model Zero Trust Architecture ZTA to increase your presentation threshold. Encompassed with nine stages, this template is a great option to educate and entice your audience. Dispence information on Traditional Network, Apps Directly, VPN, using this template. Grab it now to reap its full benefits.
-
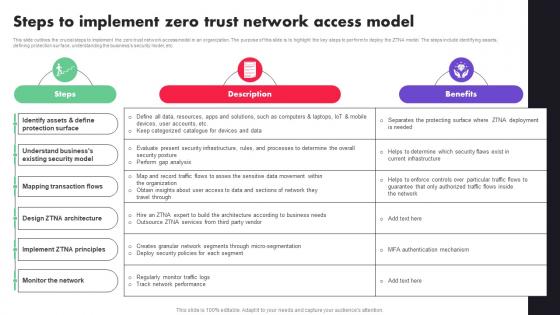 Steps To Implement Zero Trust Network Access Model Zero Trust Architecture ZTA
Steps To Implement Zero Trust Network Access Model Zero Trust Architecture ZTAThis slide outlines the crucial steps to implement the zero trust network access model in an organization. The purpose of this slide is to highlight the key steps to perform to deploy the ZTNA model. The steps include identifying assets, defining protection surface, understanding the businesss security model, etc. Present the topic in a bit more detail with this Steps To Implement Zero Trust Network Access Model Zero Trust Architecture ZTA. Use it as a tool for discussion and navigation on Protection Surface, Security Model, Mapping Transaction Flows. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
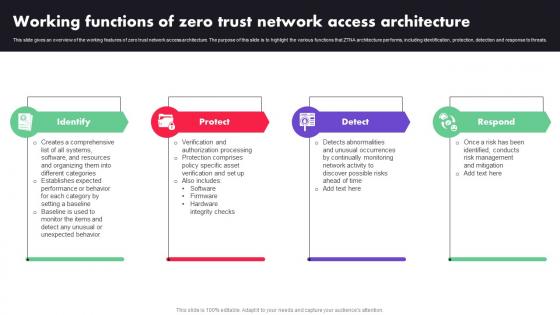 Working Functions Of Zero Trust Network Access Architecture Zero Trust Architecture ZTA
Working Functions Of Zero Trust Network Access Architecture Zero Trust Architecture ZTAThis slide gives an overview of the working features of zero trust network access architecture. The purpose of this slide is to highlight the various functions that ZTNA architecture performs, including identification, protection, detection and response to threats. Introducing Working Functions Of Zero Trust Network Access Architecture Zero Trust Architecture ZTA to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Identify, Protect, Detect, using this template. Grab it now to reap its full benefits.
-
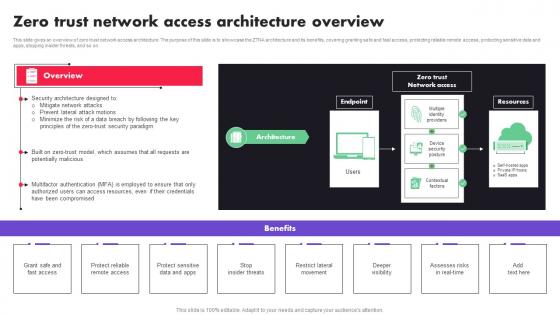 Zero Trust Network Access Architecture Overview Ppt File Introduction
Zero Trust Network Access Architecture Overview Ppt File IntroductionThis slide gives an overview of zero trust network access architecture. The purpose of this slide is to showcase the ZTNA architecture and its benefits, covering granting safe and fast access, protecting reliable remote access, protecting sensitive data and apps, stopping insider threats, and so on. Deliver an outstanding presentation on the topic using this Zero Trust Network Access Architecture Overview Ppt File Introduction. Dispense information and present a thorough explanation of Mitigate Network Attacks, Security Paradigm, Multifactor Authentication using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
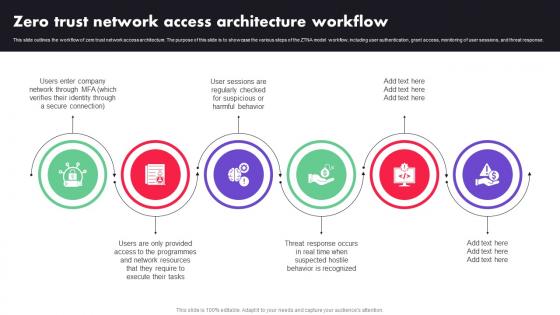 Zero Trust Network Access Architecture Workflow Ppt File Picture
Zero Trust Network Access Architecture Workflow Ppt File PictureThis slide outlines the workflow of zero trust network access architecture. The purpose of this slide is to showcase the various steps of the ZTNA model workflow, including user authentication, grant access, monitoring of user sessions, and threat response. Introducing Zero Trust Network Access Architecture Workflow Ppt File Picture to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Network Resources, Tasks, Programmes, using this template. Grab it now to reap its full benefits.
-
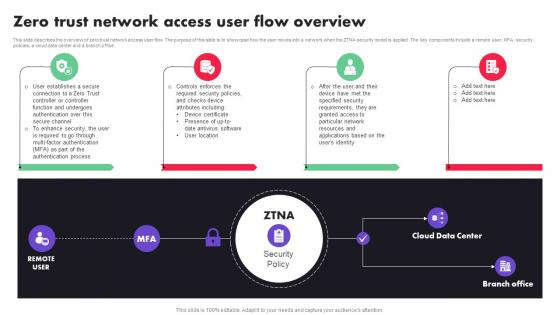 Zero Trust Network Access User Flow Overview Zero Trust Architecture ZTA
Zero Trust Network Access User Flow Overview Zero Trust Architecture ZTAThis slide describes the overview of zero trust network access user flow. The purpose of this slide is to showcase how the user moves into a network when the ZTNA security model is applied. The key components include a remote user, MFA, security policies, a cloud data center and a branch office. Introducing Zero Trust Network Access User Flow Overview Zero Trust Architecture ZTA to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Security, Policy, Cloud Data Center, Branch Office, using this template. Grab it now to reap its full benefits.
-
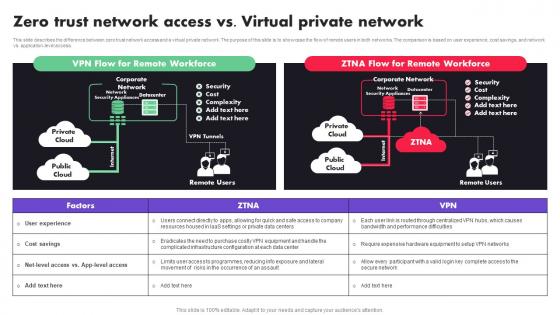 Zero Trust Network Access Vs Virtual Private Network Zero Trust Architecture ZTA
Zero Trust Network Access Vs Virtual Private Network Zero Trust Architecture ZTAThis slide describes the difference between zero trust network access and a virtual private network. The purpose of this slide is to showcase the flow of remote users in both networks. The comparison is based on user experience, cost savings, and network vs. application-level access. Introducing Zero Trust Network Access Vs Virtual Private Network Zero Trust Architecture ZTA to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Iaas Settings, Data Centers, Apps, using this template. Grab it now to reap its full benefits.
-
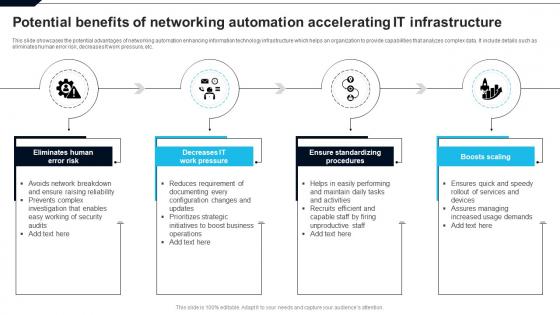 Potential Benefits Of Networking Automation Accelerating It Infrastructure
Potential Benefits Of Networking Automation Accelerating It InfrastructureThis slide showcases the potential advantages of networking automation enhancing information technology infrastructure which helps an organization to provide capabilities that analyzes complex data. It include details such as eliminates human error risk, decreases It work pressure, etc. Introducing our premium set of slides with Potential Benefits Of Networking Automation Accelerating It Infrastructure. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Eliminates Human Error Risk, Decreases IT Work Pressure, Ensure Standardizing Procedures. So download instantly and tailor it with your information.
-
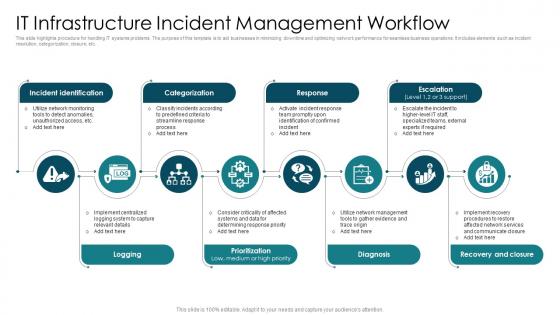 It Infrastructure Incident Management Workflow
It Infrastructure Incident Management WorkflowThis slide highlights procedure for handlingIT systems problems. The purpose of this template is to aid businesses in minimizing downtime and optimizing network performance for seamless business operations. It includes elements such as incident resolution, categorization, closure, etc. Presenting our set of slides with It Infrastructure Incident Management Workflow. This exhibits information on Eight stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Categorization, Response, Recovery And Closure.
-
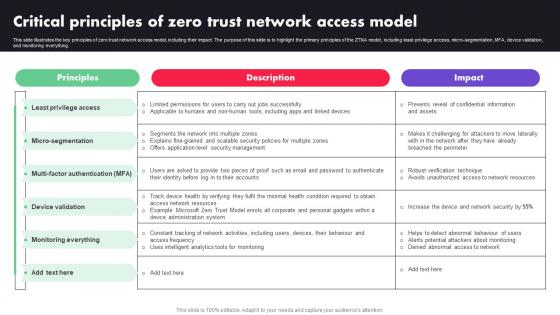 Zero Trust Architecture ZTA Critical Principles Of Zero Trust Network Access Model
Zero Trust Architecture ZTA Critical Principles Of Zero Trust Network Access ModelThis slide illustrates the key principles of zero trust network access model, including their impact. The purpose of this slide is to highlight the primary principles of the ZTNA model, including least privilege access, micro-segmentation, MFA, device validation, and monitoring everything. Deliver an outstanding presentation on the topic using this Zero Trust Architecture ZTA Critical Principles Of Zero Trust Network Access Model. Dispense information and present a thorough explanation of Privilege Access, Micro Segmentation, Device Validation using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
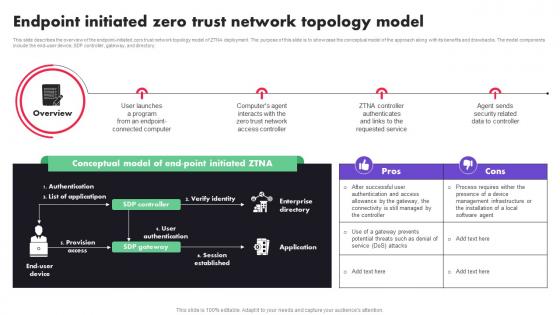 Zero Trust Architecture ZTA Endpoint Initiated Zero Trust Network Topology Model
Zero Trust Architecture ZTA Endpoint Initiated Zero Trust Network Topology ModelThis slide describes the overview of the endpoint-initiated zero trust network topology model of ZTNA deployment. The purpose of this slide is to showcase the conceptual model of the approach along with its benefits and drawbacks. The model components include the end-user device, SDP controller, gateway, and directory. Introducing Zero Trust Architecture ZTA Endpoint Initiated Zero Trust Network Topology Model to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Overview, Computer, service, using this template. Grab it now to reap its full benefits.
-
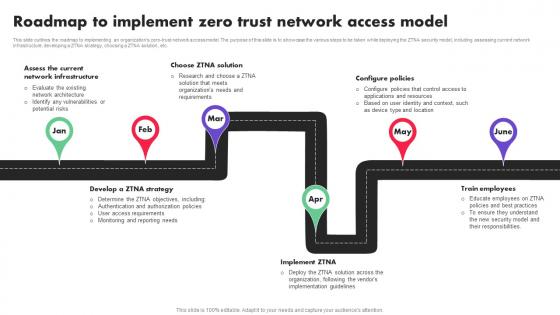 Zero Trust Architecture ZTA Roadmap To Implement Zero Trust Network Access Model
Zero Trust Architecture ZTA Roadmap To Implement Zero Trust Network Access ModelThis slide outlines the roadmap to implementing an organizations zero-trust network access model. The purpose of this slide is to showcase the various steps to be taken while deploying the ZTNA security model, including assessing current network infrastructure, developing a ZTNA strategy, choosing a ZTNA solution, etc. Introducing Zero Trust Architecture ZTA Roadmap To Implement Zero Trust Network Access Model to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Network Infrastructure, Ztna Solution, Configure Policies, using this template. Grab it now to reap its full benefits.
-
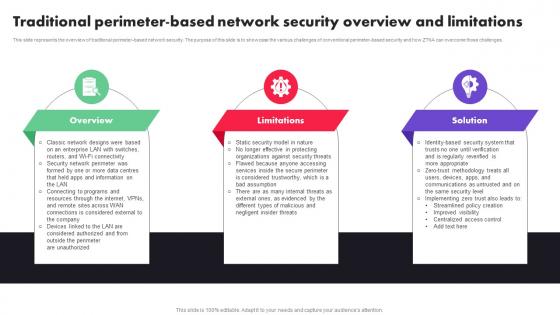 Zero Trust Architecture Traditional Perimeter Based Network Security Overview And Limitations Ppt File Guide
Zero Trust Architecture Traditional Perimeter Based Network Security Overview And Limitations Ppt File GuideThis slide represents the overview of traditional perimeter-based network security. The purpose of this slide is to showcase the various challenges of conventional perimeter-based security and how ZTNA can overcome those challenges. Introducing Zero Trust Architecture Traditional Perimeter Based Network Security Overview And Limitations Ppt File Guide to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Overview, Limitations, Solution, using this template. Grab it now to reap its full benefits.
-
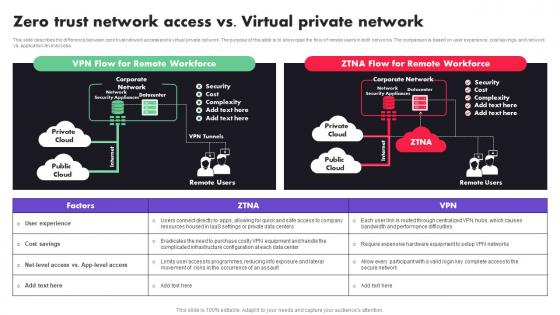 Zero Trust Architecture ZTA Zero Trust Network Access Vs Virtual Private Network
Zero Trust Architecture ZTA Zero Trust Network Access Vs Virtual Private NetworkThis slide describes the difference between zero trust network access and a virtual private network. The purpose of this slide is to showcase the flow of remote users in both networks. The comparison is based on user experience, cost savings, and network vs. application-level access. Introducing Zero Trust Architecture ZTA Zero Trust Network Access Vs Virtual Private Network to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Iaas Settings, Data Centers, Apps, using this template. Grab it now to reap its full benefits.
-
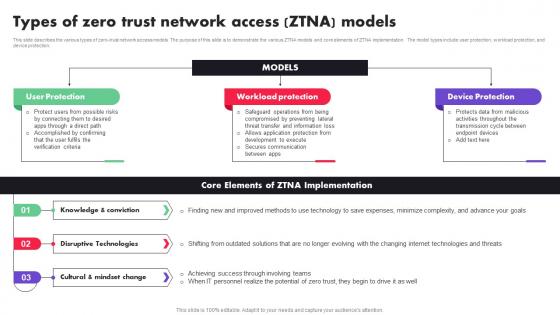 Types Of Zero Trust Network Access ZTNA Models Zero Trust Architecture ZTA
Types Of Zero Trust Network Access ZTNA Models Zero Trust Architecture ZTAThis slide describes the various types of zero-trust network access models. The purpose of this slide is to demonstrate the various ZTNA models and core elements of ZTNA implementation. The model types include user protection, workload protection, and device protection. Introducing Types Of Zero Trust Network Access ZTNA Models Zero Trust Architecture ZTA to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on User Protection, Workload protection, Device Protection, using this template. Grab it now to reap its full benefits.
-
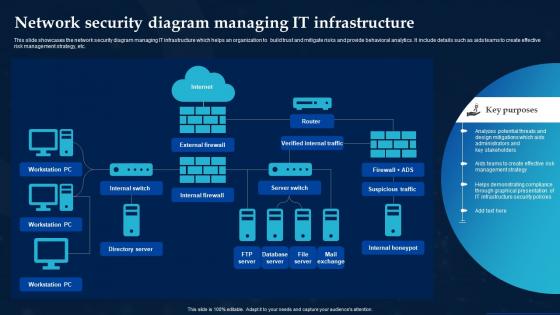 Network Security Diagram Managing It Infrastructure
Network Security Diagram Managing It InfrastructureThis slide showcases the network security diagram managing IT infrastructure which helps an organization to build trust and mitigate risks and provide behavioral analytics. It include details such as aids teams to create effective risk management strategy, etc. Introducing our Network Security Diagram Managing It Infrastructure set of slides. The topics discussed in these slides are Internal Switch, Internal Firewall, Server Switch. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
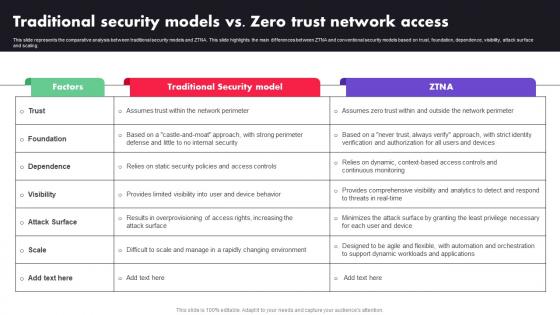 M72 Traditional Security Models Vs Zero Trust Network Access Zero Trust Architecture ZTA
M72 Traditional Security Models Vs Zero Trust Network Access Zero Trust Architecture ZTAThis slide represents the comparative analysis between traditional security models and ZTNA. This slide highlights the main differences between ZTNA and conventional security models based on trust, foundation, dependence, visibility, attack surface and scaling. Deliver an outstanding presentation on the topic using this M72 Traditional Security Models Vs Zero Trust Network Access Zero Trust Architecture ZTA. Dispense information and present a thorough explanation of Factors, Traditional Security Model, ZTNA using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
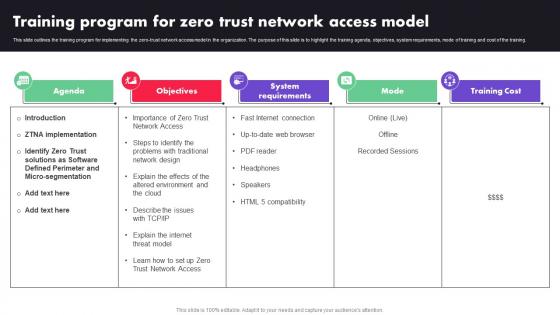 M73 Training Program For Zero Trust Network Access Model Zero Trust Architecture ZTA
M73 Training Program For Zero Trust Network Access Model Zero Trust Architecture ZTAThis slide outlines the training program for implementing the zero-trust network access model in the organization. The purpose of this slide is to highlight the training agenda, objectives, system requirements, mode of training and cost of the training. Present the topic in a bit more detail with this M73 Training Program For Zero Trust Network Access Model Zero Trust Architecture ZTA. Use it as a tool for discussion and navigation on Agenda, Objectives, System Requirements. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
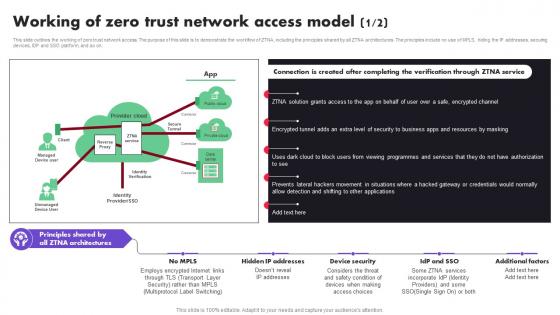 M74 Working Functions Of Zero Trust Network Access Architecture Zero Trust Architecture ZTA
M74 Working Functions Of Zero Trust Network Access Architecture Zero Trust Architecture ZTAThis slide gives an overview of the working features of zero trust network access architecture. The purpose of this slide is to highlight the various functions that ZTNA architecture performs, including identification, protection, detection and response to threats. Introducing M74 Working Functions Of Zero Trust Network Access Architecture Zero Trust Architecture ZTA to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Identify, Protect, Detect, using this template. Grab it now to reap its full benefits.
-
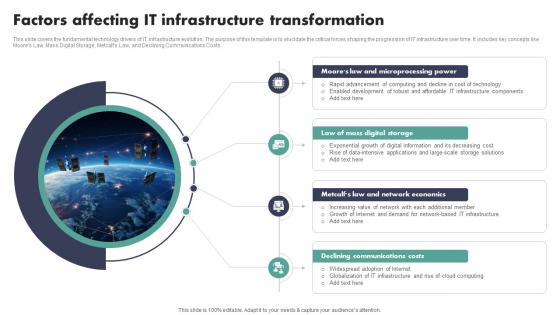 Factors Affecting IT Infrastructure Transformation
Factors Affecting IT Infrastructure TransformationThis slide covers the fundamental technology drivers of IT infrastructure evolution. The purpose of this template is to elucidate the critical forces shaping the progression of IT infrastructure over time. It includes key concepts like Moores Law, Mass Digital Storage, Metcalfs Law, and Declining Communications Costs. Presenting our set of slides with Factors Affecting IT Infrastructure Transformation This exhibits information on Four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Microprocessing Power, Mass Digital Storage, Network Economics
-
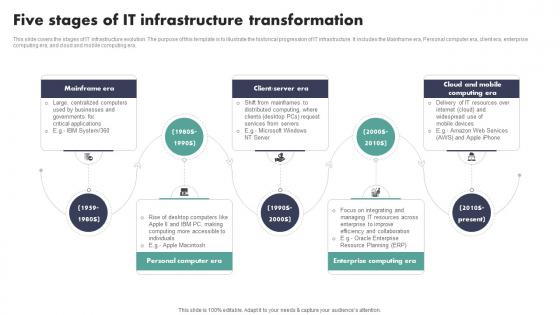 Five Stages Of IT Infrastructure Transformation
Five Stages Of IT Infrastructure TransformationThis slide covers the stages of IT infrastructure evolution. The purpose of this template is to illustrate the historical progression of IT infrastructure. It includes the Mainframe era, Personal computer era, client era, enterprise computing era, and cloud and mobile computing era. Introducing our premium set of slides with Five Stages Of IT Infrastructure Transformation Ellicudate the Five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Mainframe Era, Personal Computer Era, Enterprise Computing Era. So download instantly and tailor it with your information.
-
 Future Trends In IT Infrastructure Transformation Market
Future Trends In IT Infrastructure Transformation MarketThis slide covers four compelling future trends in IT infrastructure transformation. The purpose of this template is to shed light on the imminent changes that will shape the landscape of IT infrastructure, influencing how organizations process data, adopt artificial intelligence, structure their infrastructure, and manage network functions. Presenting our set of slides with Future Trends In IT Infrastructure Transformation Market This exhibits information on Four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Edge Computing, Disaggregated Infrastructure
-
 Icon Showing Global IT Infrastructure Transformation
Icon Showing Global IT Infrastructure TransformationIntroducing our Icon Showing Global IT Infrastructure Transformation set of slides. The topics discussed in these slides are Icon Showing Global, It Infrastructure Transformation This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 IT Infrastructure Icon Showing Digital Transformation
IT Infrastructure Icon Showing Digital TransformationPresenting our set of slides with Information Technology Infrastructure Transformation Icon This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on It Infrastructure Icon Showing Digital Transformation
-
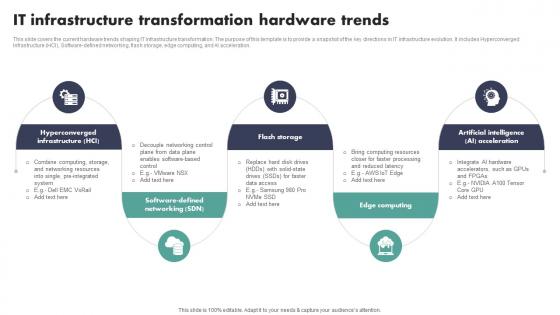 IT Infrastructure Transformation Hardware Trends
IT Infrastructure Transformation Hardware TrendsThis slide covers the current hardware trends shaping IT infrastructure transformation. The purpose of this template is to provide a snapshot of the key directions in IT infrastructure evolution. It includes Hyperconverged Infrastructure HCI, Software-defined networking, flash storage, edge computing, and AI acceleration. Presenting our set of slides with IT Infrastructure Transformation Hardware Trends This exhibits information on Five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Flash Storage, Edge Computing, Artificial Intelligence
-
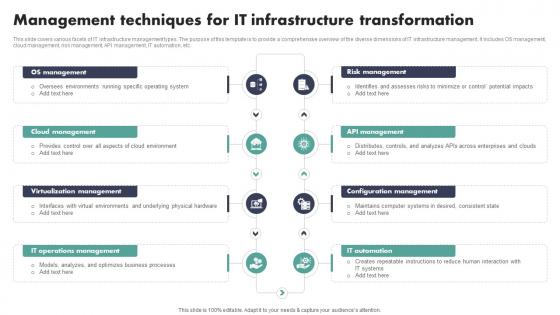 Management Techniques For IT Infrastructure Transformation
Management Techniques For IT Infrastructure TransformationThis slide covers various facets of IT infrastructure management types. The purpose of this template is to provide a comprehensive overview of the diverse dimensions of IT infrastructure management. It includes OS management, cloud management, risk management, API management, IT automation, etc. Introducing our premium set of slides with Management Techniques For IT Infrastructure Transformation Ellicudate the Eight stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Os Management, Cloud Management, Risk Management. So download instantly and tailor it with your information.
-
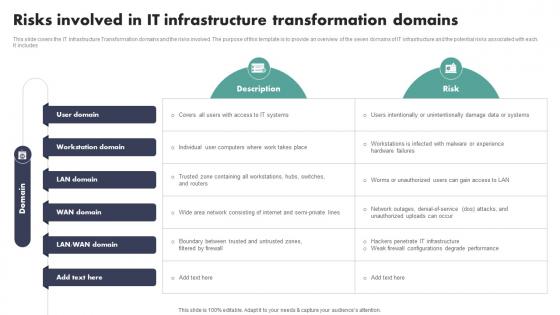 Risks Involved In IT Infrastructure Transformation Domains
Risks Involved In IT Infrastructure Transformation DomainsThis slide covers the IT Infrastructure Transformation domains and the risks involved. The purpose of this template is to provide an overview of the seven domains of IT infrastructure and the potential risks associated with each It includes Introducing our Risks Involved In IT Infrastructure Transformation Domains set of slides. The topics discussed in these slides are User Domain, Wan Domain This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
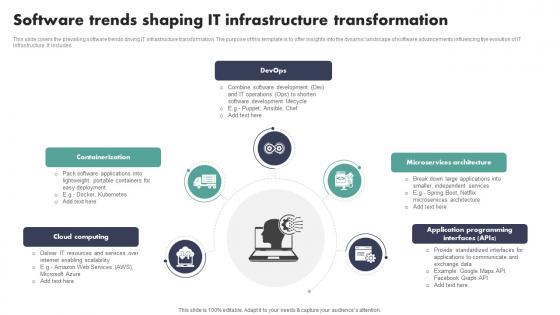 Software Trends Shaping IT Infrastructure Transformation
Software Trends Shaping IT Infrastructure TransformationThis slide covers the prevailing software trends driving IT infrastructure transformation. The purpose of this template is to offer insights into the dynamic landscape of software advancements influencing the evolution of IT infrastructure. It includes Presenting our set of slides with Software Trends Shaping IT Infrastructure Transformation This exhibits information on Five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Containerization, Microservices Architecture, Cloud Computing
-
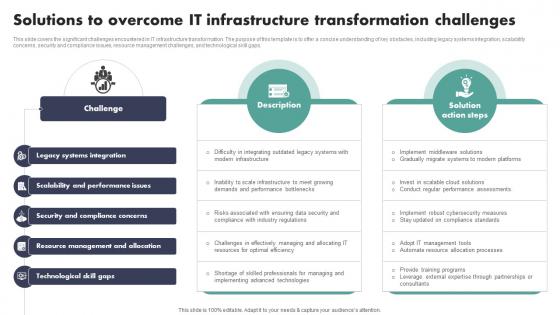 Solutions To Overcome IT Infrastructure Transformation Challenges
Solutions To Overcome IT Infrastructure Transformation ChallengesThis slide covers the significant challenges encountered in IT infrastructure transformation. The purpose of this template is to offer a concise understanding of key obstacles, including legacy systems integration, scalability concerns, security and compliance issues, resource management challenges, and technological skill gaps. Introducing our Solutions To Overcome IT Infrastructure Transformation Challenges set of slides. The topics discussed in these slides are Legacy Systems Integration, Scalability And Performance Issues, Security And Compliance Concerns This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
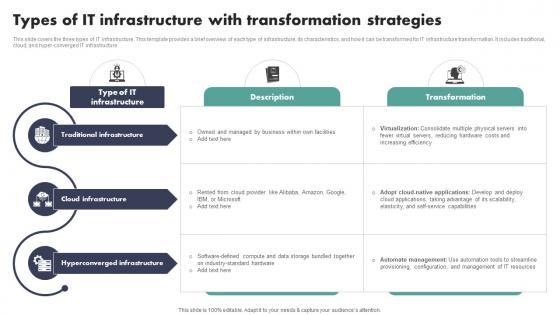 Types Of IT Infrastructure With Transformation Strategies
Types Of IT Infrastructure With Transformation StrategiesThis slide covers the three types of IT infrastructure. This template provides a brief overview of each type of infrastructure, its characteristics, and how it can be transformed for IT infrastructure transformation. It includes traditional, cloud, and hyper-converged IT infrastructure. Introducing our premium set of slides with Types Of IT Infrastructure With Transformation Strategies Ellicudate the Three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Traditional Infrastructure, Cloud Infrastructure, Hyperconverged Infrastructure. So download instantly and tailor it with your information.
-
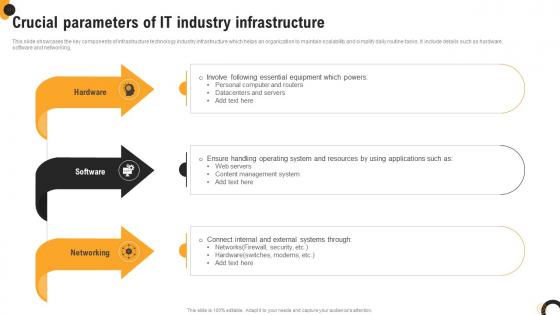 Crucial Parameters Of IT Industry Infrastructure
Crucial Parameters Of IT Industry InfrastructureThis slide showcases the key components of infrastructure technology industry infrastructure which helps an organization to maintain scalability and simplify daily routine tasks. It include details such as hardware, software and networking. Introducing our premium set of slides with Crucial Parameters Of IT Industry Infrastructure. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Hardware, Networking, Software.So download instantly and tailor it with your information.



