Powerpoint Templates and Google slides for Secured Information Management System
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
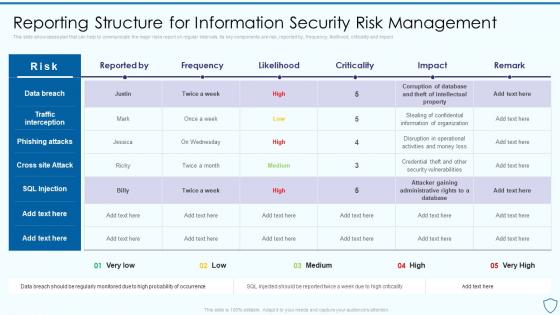 Reporting Structure For Information Security Risk Assessment And Management Plan For Information Security
Reporting Structure For Information Security Risk Assessment And Management Plan For Information SecurityThis slide showcases plan that can help to communicate the major risks report on regular intervals. Its key components are risk, reported by, frequency, likelihood, criticality and impact Deliver an outstanding presentation on the topic using this Reporting Structure For Information Security Risk Assessment And Management Plan For Information Security. Dispense information and present a thorough explanation of Structure, Information, Management using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Risk Assessment And Management Plan For Information Security Analyzing The Impact Of Security Threats
Risk Assessment And Management Plan For Information Security Analyzing The Impact Of Security ThreatsDeliver an outstanding presentation on the topic using this Risk Assessment And Management Plan For Information Security Analyzing The Impact Of Security Threats. Dispense information and present a thorough explanation of Analyzing, Organization, Financial using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
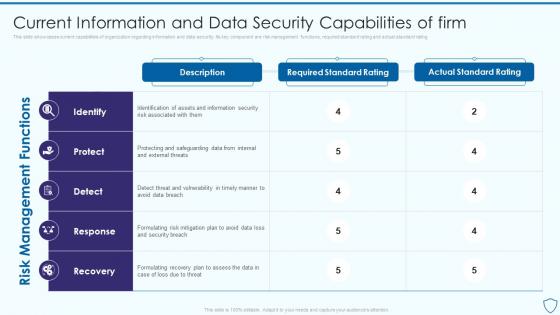 Risk Assessment And Management Plan For Information Security Current Information And Data Security
Risk Assessment And Management Plan For Information Security Current Information And Data SecurityThis slide showcases current capabilities of organization regarding information and data security. Its key component are risk management functions, required standard rating and actual standard rating Present the topic in a bit more detail with this Risk Assessment And Management Plan For Information Security Current Information And Data Security. Use it as a tool for discussion and navigation on Information, Capabilities, Risk Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
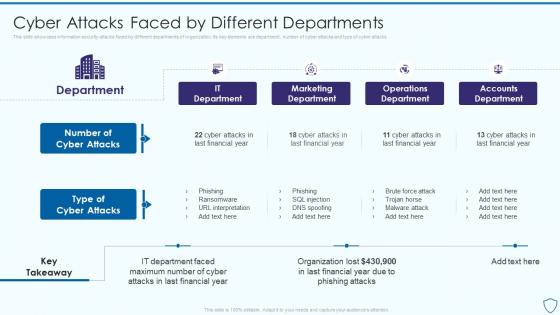 Risk Assessment And Management Plan For Information Security Cyber Attacks Faced By Different
Risk Assessment And Management Plan For Information Security Cyber Attacks Faced By DifferentThis slide showcase information security attacks faced by different departments of organization. Its key elements are department, number of cyber attacks and type of cyber attacks Deliver an outstanding presentation on the topic using this Risk Assessment And Management Plan For Information Security Cyber Attacks Faced By Different. Dispense information and present a thorough explanation of Marketing Department, Operations Department, Accounts Department using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
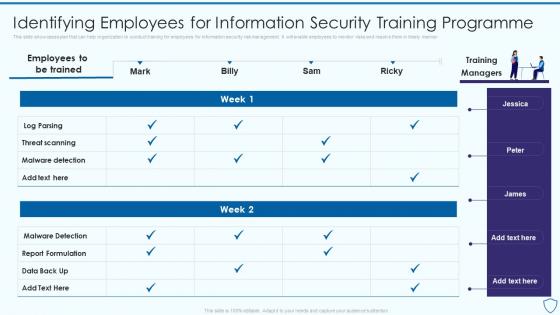 Risk Assessment And Management Plan For Information Security Identifying Employees For Information
Risk Assessment And Management Plan For Information Security Identifying Employees For InformationThis slide showcases plan that can help organization to conduct training for employees for information security risk management. It will enable employees to monitor risks and resolve them in timely manner Present the topic in a bit more detail with this Risk Assessment And Management Plan For Information Security Identifying Employees For Information. Use it as a tool for discussion and navigation on Information, Programme, Identifying. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Risk Assessment And Management Plan For Information Security Table Of Contents
Risk Assessment And Management Plan For Information Security Table Of ContentsIntroducing Risk Assessment And Management Plan For Information Security Table Of Contents to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Departments, Organization, Information, using this template. Grab it now to reap its full benefits.
-
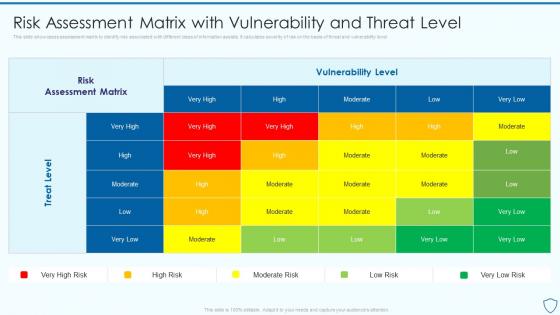 Risk Assessment Matrix With Vulnerability Risk Assessment And Management Plan For Information Security
Risk Assessment Matrix With Vulnerability Risk Assessment And Management Plan For Information SecurityThis slide showcases assessment matrix to identify risk associated with different class of information assists. It calculates severity of risk on the basis of threat and vulnerability level Present the topic in a bit more detail with this Risk Assessment Matrix With Vulnerability Risk Assessment And Management Plan For Information Security. Use it as a tool for discussion and navigation on Assessment, Vulnerability, Associated. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
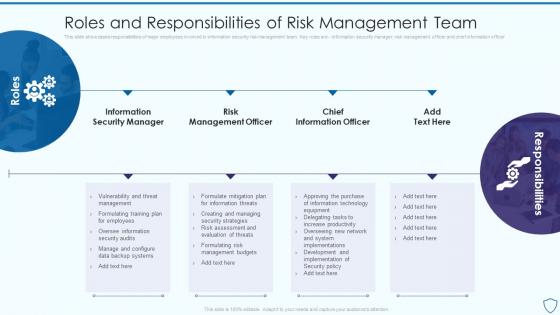 Roles And Responsibilities Of Risk Management Risk Assessment And Management Plan For Information Security
Roles And Responsibilities Of Risk Management Risk Assessment And Management Plan For Information SecurityThis slide showcases responsibilities of major employees involved in information security risk management team. Key roles are information security manager, risk management officer and chief information officer Present the topic in a bit more detail with this Roles And Responsibilities Of Risk Management Risk Assessment And Management Plan For Information Security. Use it as a tool for discussion and navigation on Responsibilities, Management, Information . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Selecting Suitable Software For Information Risk Assessment And Management Plan For Information Security
Selecting Suitable Software For Information Risk Assessment And Management Plan For Information SecurityThis slide showcases software that can help organization to monitor and manage the risk. It provides information about Cyber Risk Quantification, vvulnerability management, Ccentralized rrepository for aassets etc Deliver an outstanding presentation on the topic using this Selecting Suitable Software For Information Risk Assessment And Management Plan For Information Security. Dispense information and present a thorough explanation of Software, Information, Management using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Steps For Information Security Risk Management Risk Assessment And Management Plan For Information Security
Steps For Information Security Risk Management Risk Assessment And Management Plan For Information SecurityThis slide showcase steps which can help organization to implement information security risk management program in organization. Its key steps are identify, protect, detect and respond Present the topic in a bit more detail with this Steps For Information Security Risk Management Risk Assessment And Management Plan For Information Security. Use it as a tool for discussion and navigation on Communication, Mitigation, Response Planning. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Timeline For Information Security Risk Assessment And Management Plan For Information Security
Timeline For Information Security Risk Assessment And Management Plan For Information SecurityThis slide showcases timeline that can help organization to conduct training for information security risk management programme. It also showcases weekly and step progress Deliver an outstanding presentation on the topic using this Timeline For Information Security Risk Assessment And Management Plan For Information Security. Dispense information and present a thorough explanation of Information, Management, Email Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
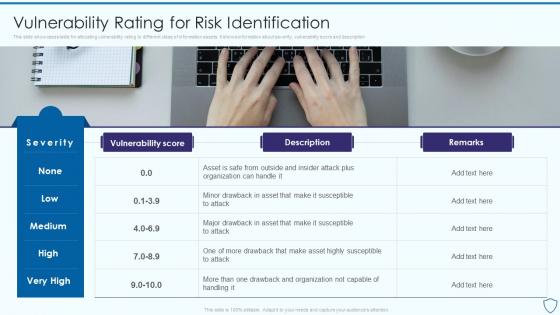 Vulnerability Rating For Risk Identification Risk Assessment And Management Plan For Information Security
Vulnerability Rating For Risk Identification Risk Assessment And Management Plan For Information SecurityThis slide showcases table for allocating vulnerability rating to different class of information assets. It shows information about severity, vulnerability score and description Present the topic in a bit more detail with this Vulnerability Rating For Risk Identification Risk Assessment And Management Plan For Information Security. Use it as a tool for discussion and navigation on Identification, Information, Vulnerability. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
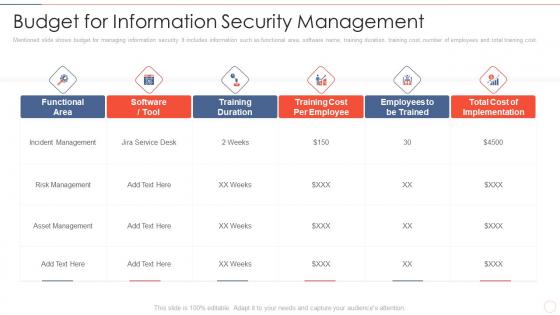 Effective information security budget for information security management
Effective information security budget for information security managementMentioned slide shows budget for managing information security. It includes information such as functional area, software name, training duration, training cost, number of employees and total training cost. Present the topic in a bit more detail with this Effective Information Security Budget For Information Security Management. Use it as a tool for discussion and navigation on Incident Management, Risk Management, Asset Management . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
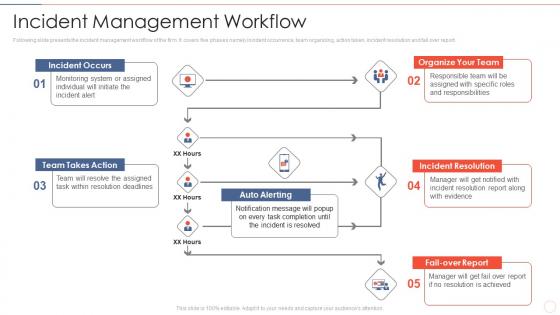 Effective information security incident management workflow
Effective information security incident management workflowFollowing slide presents the incident management workflow of the firm. It covers five phases namely incident occurrence, team organizing, action taken, incident resolution and fail over report. Present the topic in a bit more detail with this Effective Information Security Incident Management Workflow. Use it as a tool for discussion and navigation on Incident Occurs, Team Takes Action, Organize Team, Auto Alerting, Incident Resolution, Fail Over Report. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
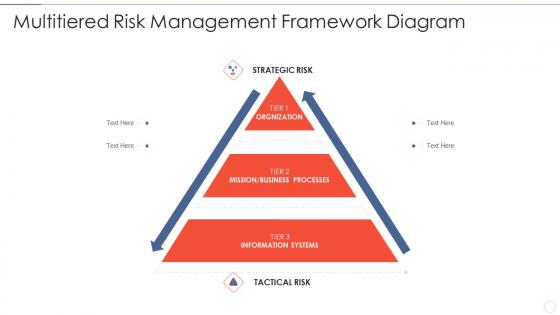 Effective information security multitiered risk management framework diagram
Effective information security multitiered risk management framework diagramIncrease audience engagement and knowledge by dispensing information using Effective Information Security Multitiered Risk Management Framework Diagram. This template helps you present information on three stages. You can also present information on Strategic Risk, Orgnization, Mission, Business Processes, Information Systems using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
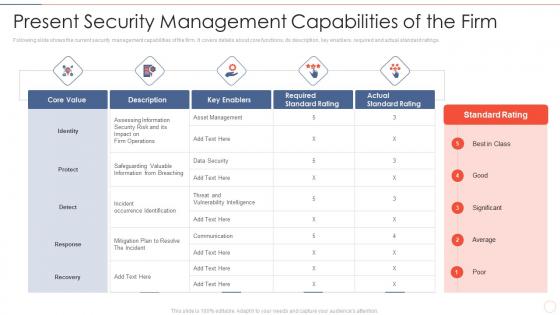 Effective information security present security management capabilities of the firm
Effective information security present security management capabilities of the firmFollowing slide shows the current security management capabilities of the firm. It covers details about core functions, its description, key enablers, required and actual standard ratings. Present the topic in a bit more detail with this Effective Information Security Present Security Management Capabilities Of The Firm. Use it as a tool for discussion and navigation on Core Value, Key Enablers, Required Standard Rating, Actual Standard Rating. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 5 practices of information and cyber security risk management
5 practices of information and cyber security risk managementMentioned slide delineates best practices for information security risk management. Knowledge of IT environment and assets, developing risk management strategy, embedding risk management into organization culture, continuous risk assessment and security protocols are the practices covered in this slide. Presenting our set of slides with 5 Practices Of Information And Cyber Security Risk Management. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Management, Organization, Risk.
-
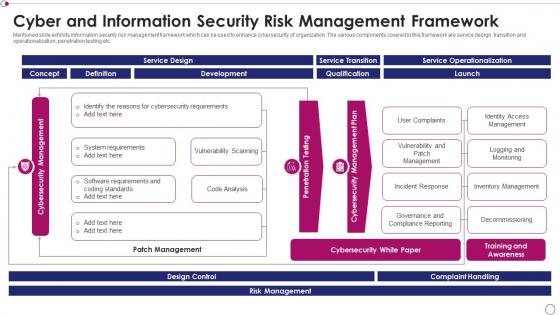 Cyber and information security risk management framework
Cyber and information security risk management frameworkMentioned slide exhibits information security risk management framework which can be used to enhance cybersecurity of organization. The various components covered in this framework are service design, transition and operationalization, penetration testing etc. Introducing our Cyber And Information Security Risk Management Framework set of slides. The topics discussed in these slides are Development, Service Transition, Service Operationalization. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Icon for information and cyber security risk management
Icon for information and cyber security risk managementIntroducing our premium set of slides with Icon For Information And Cyber Security Risk Management. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Icon For Information And Cyber Security Risk Management. So download instantly and tailor it with your information.
-
 Icon for information security and risk management team
Icon for information security and risk management teamIntroducing our premium set of slides with Icon For Information Security And Risk Management Team. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Icon For Information Security And Risk Management Team. So download instantly and tailor it with your information.
-
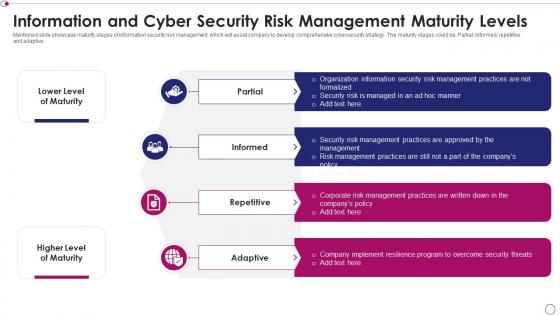 Information and cyber security risk management maturity levels
Information and cyber security risk management maturity levelsMentioned slide showcase maturity stages of information security risk management, which will assist company to develop comprehensive cybersecurity strategy. The maturity stages could be Partial informed repetitive and adaptive. Introducing our premium set of slides with Information And Cyber Security Risk Management Maturity Levels. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Partial, Informed, Repetitive. So download instantly and tailor it with your information.
-
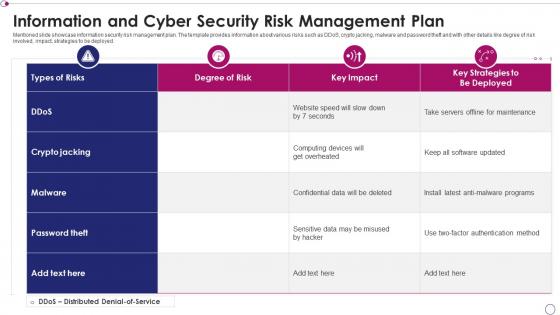 Information and cyber security risk management plan
Information and cyber security risk management planMentioned slide showcase information security risk management plan. The template provides information about various risks such as DDoS, crypto jacking, malware and password theft and with other details like degree of risk involved, impact, strategies to be deployed. Introducing our Information And Cyber Security Risk Management Plan set of slides. The topics discussed in these slides are Degree Of Risk, Strategies, Devices. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
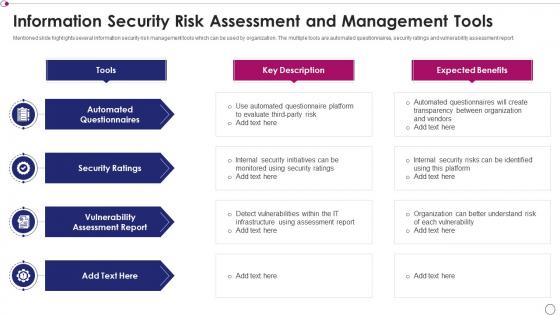 Information security risk assessment and management tools
Information security risk assessment and management toolsMentioned slide highlights several information security risk management tools which can be used by organization. The multiple tools are automated questionnaires, security ratings and vulnerability assessment report. Introducing our premium set of slides with Information Security Risk Assessment And Management Tools. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Security Ratings, Automated Questionnaires, Vulnerability Assessment Report. So download instantly and tailor it with your information.
-
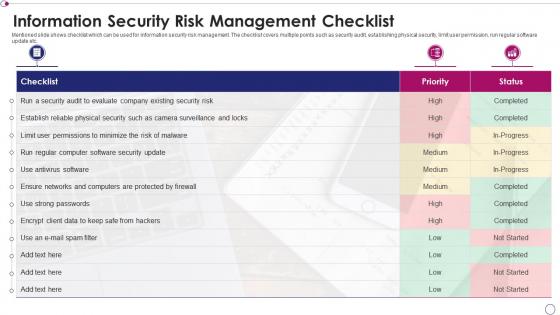 Information security risk management checklist
Information security risk management checklistMentioned slide shows checklist which can be used for information security risk management. The checklist covers multiple points such as security audit, establishing physical security, limit user permission, run regular software update etc. Introducing our Information Security Risk Management Checklist set of slides. The topics discussed in these slides are Security, Risk, Protected. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
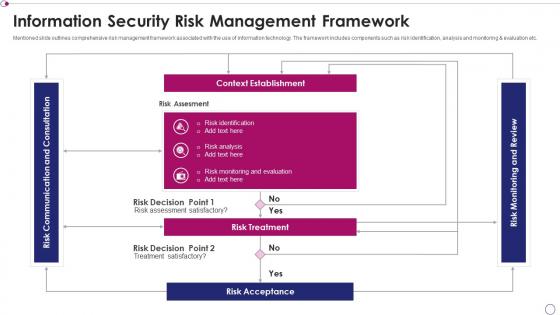 Information security risk management framework
Information security risk management frameworkMentioned slide outlines comprehensive risk management framework associated with the use of information technology. The framework includes components such as risk identification, analysis and monitoring and evaluation etc. Presenting our well structured Information Security Risk Management Framework. The topics discussed in this slide are Risk Identification, Risk Analysis, Evaluation. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Information security risk management icon
Information security risk management iconIntroducing our premium set of slides with Information Security Risk Management Icon. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Information Security Risk Management Icon. So download instantly and tailor it with your information.
-
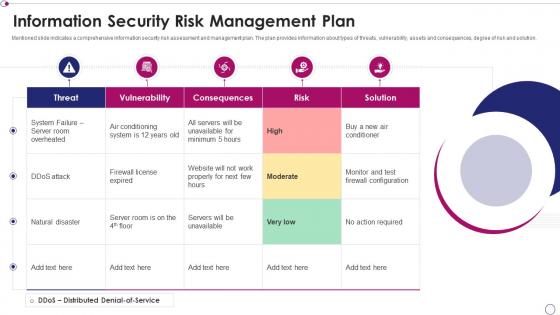 Information security risk management plan
Information security risk management planPresenting our well structured Information Security Risk Management Plan. The topics discussed in this slide are System, Risk, Required. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
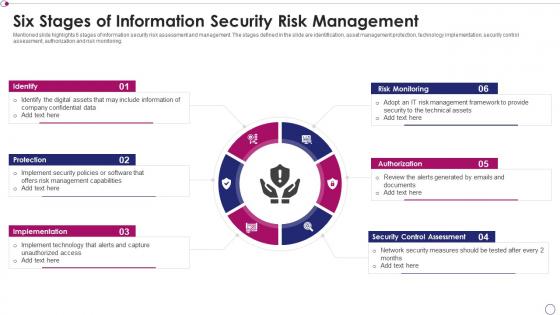 Six stages of information security risk management
Six stages of information security risk managementMentioned slide highlights 6 stages of information security risk assessment and management. The stages defined in the slide are identification, asset management protection, technology implementation, security control assessment, authorization and risk monitoring. Introducing our premium set of slides with Six Stages Of Information Security Risk Management. Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Risk Monitoring, Security Control Assessment, Authorization. So download instantly and tailor it with your information.
-
 Asset management information security ppt powerpoint presentation inspiration outfit cpb
Asset management information security ppt powerpoint presentation inspiration outfit cpbPresenting our Asset Management Information Security Ppt Powerpoint Presentation Inspiration Outfit Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Asset Management Information Security This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Real time analysis of security alerts security information and event management services
Real time analysis of security alerts security information and event management servicesThis slide covers the SIEM services offered by our company such as data aggregation, correlation, security alerts, dashboards, retention, forensic analysis, IT compliance, threat detection, etc. Increase audience engagement and knowledge by dispensing information using Real Time Analysis Of Security Alerts Security Information And Event Management Services. This template helps you present information on eight stages. You can also present information on Data Aggregation, Data Correlation, Security Alert using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Successful siem strategies audit compliance security information event management services
Successful siem strategies audit compliance security information event management servicesThis slide covers the SIEM services offered by our company such as data aggregation, correlation, security alerts, dashboards, retention, forensic analysis, IT compliance, threat detection, etc. Introducing Successful Siem Strategies Audit Compliance Security Information Event Management Services to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Data Aggregation, Data Correlation, Dashboards, using this template. Grab it now to reap its full benefits.
-
 Agenda of effective information security risk management process
Agenda of effective information security risk management processIncrease audience engagement and knowledge by dispensing information using Agenda Of Effective Information Security Risk Management Process. This template helps you present information on three stages. You can also present information on Agenda using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
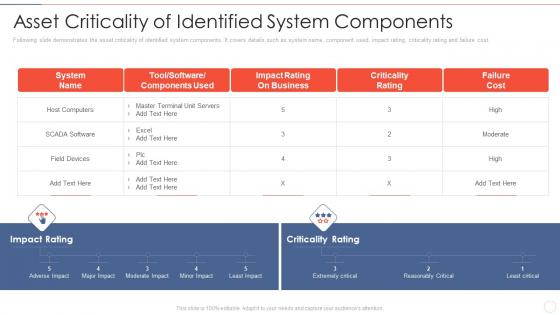 Asset components effective information security risk management process
Asset components effective information security risk management processFollowing slide demonstrates the asset criticality of identified system components. It covers details such as system name, component used, impact rating, criticality rating and failure cost.Present the topic in a bit more detail with this Asset Components Effective Information Security Risk Management Process. Use it as a tool for discussion and navigation on Impact Rating On Business, Criticality Rating, Failure Cost. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
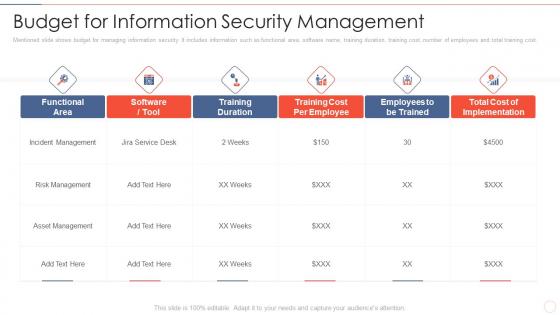 Budget for information effective information security risk management process
Budget for information effective information security risk management processMentioned slide shows budget for managing information security. It includes information such as functional area, software name, training duration, training cost, number of employees and total training cost.Deliver an outstanding presentation on the topic using this Budget For Information Effective Information Security Risk Management Process. Dispense information and present a thorough explanation of Incident Management, Asset Management, Training Duration using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Defining risk level effective information security risk management process
Defining risk level effective information security risk management processFollowing slide defines the incident risk level. It includes details about risk level, risk score and its description. Deliver an outstanding presentation on the topic using this Defining Risk Level Effective Information Security Risk Management Process. Dispense information and present a thorough explanation of Immediate Controlling, Controlling Measures, Offered By The Organization using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
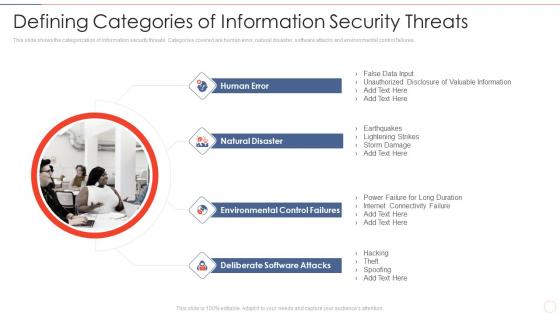 Defining security threats effective information security risk management process
Defining security threats effective information security risk management processThis slide shows the categorization of information security threats. Categories covered are human error, natural disaster, software attacks and environmental control failures.Introducing Defining Security Threats Effective Information Security Risk Management Process to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Natural Disaster, Environmental Control Failures, Deliberate Software Attacks, using this template. Grab it now to reap its full benefits.
-
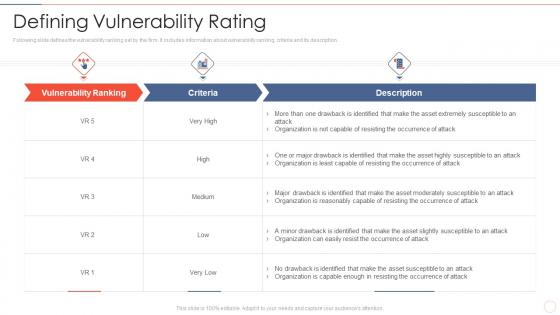 Defining vulnerability rating effective information security risk management process
Defining vulnerability rating effective information security risk management processFollowing slide defines the vulnerability ranking set by the firm. It includes information about vulnerability ranking, criteria and its description.Present the topic in a bit more detail with this Defining Vulnerability Rating Effective Information Security Risk Management Process. Use it as a tool for discussion and navigation on Occurrence Of Attack, Organization Is Reasonably, Organization Is Capable Enough. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
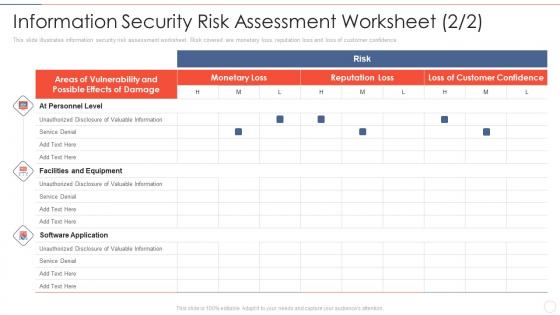 Effective information security management process information security risk assessment
Effective information security management process information security risk assessmentThis slide illustrates information security risk assessment worksheet. Risk covered are monetary loss, reputation loss and loss of customer confidence.Deliver an outstanding presentation on the topic using this Effective Information Security Management Process Information Security Risk Assessment. Dispense information and present a thorough explanation of Facilities And Equipment, Unauthorized Disclosure, Valuable Information using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
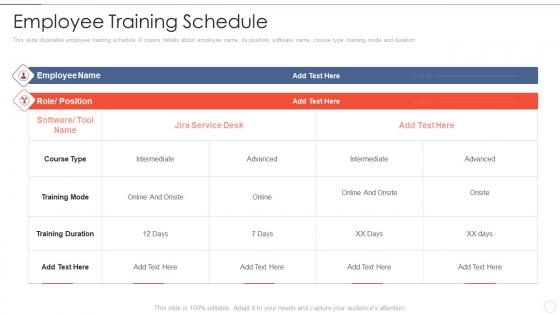 Employee training schedule effective information security risk management process
Employee training schedule effective information security risk management processThis slide illustrates employee training schedule. It covers details about employee name, its position, software name, course type, training mode and duration.Present the topic in a bit more detail with this Employee Training Schedule Effective Information Security Risk Management Process. Use it as a tool for discussion and navigation on Training Duration, Intermediate, Training Mode. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Icons slide for effective information security risk management process
Icons slide for effective information security risk management processPresenting our well crafted Icons Slide For Effective Information Security Risk Management Process set of slides. The slides include icons that are innovatively designed by our team of experts. The icons are easy to edit so you can conveniently increase or decrease their size without any loss in resolution. Therefore, grab them instantly
-
 Impact assessment matrix effective information security risk management process
Impact assessment matrix effective information security risk management processPresent the topic in a bit more detail with this Impact Assessment Matrix Effective Information Security Risk Management Process. Use it as a tool for discussion and navigation on Minor To No Infringement, Suspected Malicious Intent, Impact Medium. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
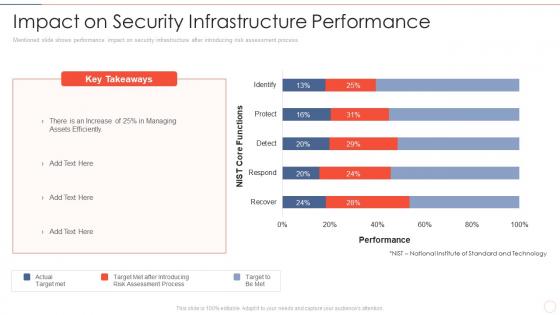 Impact on security performance effective information security risk management process
Impact on security performance effective information security risk management processMentioned slide shows performance impact on security infrastructure after introducing risk assessment process. Deliver an outstanding presentation on the topic using this Impact On Security Performance Effective Information Security Risk Management Process. Dispense information and present a thorough explanation of After Introducing, Risk Assessment Process, Assets Efficiently using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
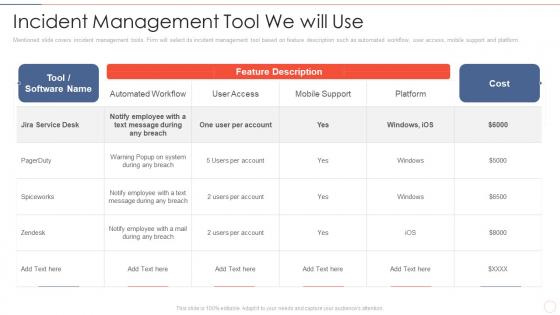 Incident management tool effective information security risk management process
Incident management tool effective information security risk management processMentioned slide covers incident management tools. Firm will select its incident management tool based on feature description such as automated workflow, user access, mobile support and platform.Present the topic in a bit more detail with this Incident Management Tool Effective Information Security Risk Management Process. Use it as a tool for discussion and navigation on Notify Employee, Message During Any Breach, Automated Workflow. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
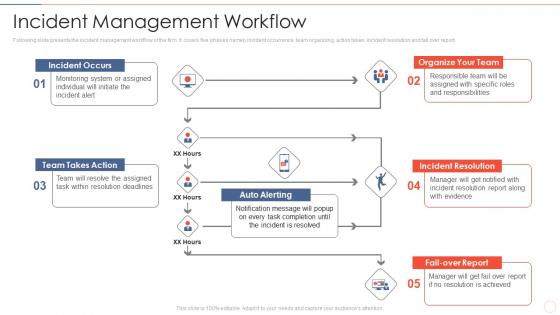 Incident management workflow effective information security risk management process
Incident management workflow effective information security risk management processFollowing slide presents the incident management workflow of the firm. It covers five phases namely incident occurrence, team organizing, action taken, incident resolution and fail over report.Introducing Incident Management Workflow Effective Information Security Risk Management Process to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Organize Your Team, Incident Resolution, Team Takes Action, using this template. Grab it now to reap its full benefits.
-
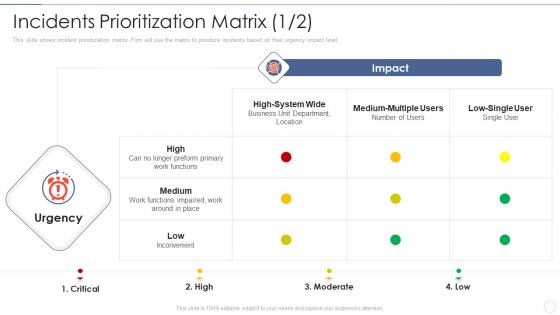 Incidents effective information security risk management process
Incidents effective information security risk management processThis slide shows incident prioritization matrix. Firm will use the matrix to prioritize incidents based on their urgency impact level.Present the topic in a bit more detail with this Incidents Effective Information Security Risk Management Process. Use it as a tool for discussion and navigation on Preform Primary Work Functions, Inconvenient, Medium Multiple. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
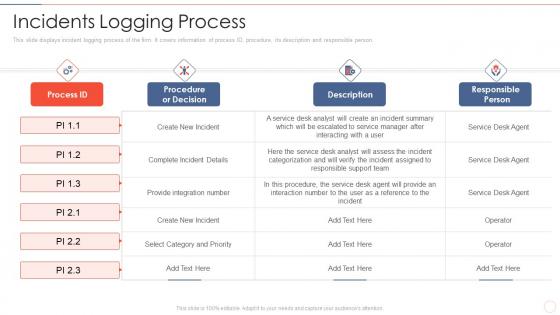 Incidents logging process effective information security risk management process
Incidents logging process effective information security risk management processThis slide displays incident logging process of the firm. It covers information of process ID, procedure, its description and responsible person.Deliver an outstanding presentation on the topic using this Incidents Logging Process Effective Information Security Risk Management Process. Dispense information and present a thorough explanation of Select Category And Priority, Procedure, The Service, Responsible Person using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
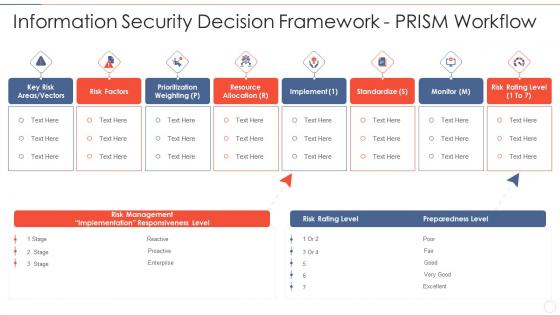 Information security decision effective information security risk management process
Information security decision effective information security risk management processIncrease audience engagement and knowledge by dispensing information using Information Security Decision Effective Information Security Risk Management Process. This template helps you present information on eight stages. You can also present information on Risk Management, Implementation Responsiveness, Prioritization Weighting using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Information security effective information security risk management process
Information security effective information security risk management processMentioned slide illustrates information security risk assessment worksheet. It include information about threat encountered, its vulnerability, asset and consequences and risk to the firm.Present the topic in a bit more detail with this Information Security Effective Information Security Risk Management Process. Use it as a tool for discussion and navigation on Asset And Consequences, Overheating In Server Room, Asset And Consequences. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
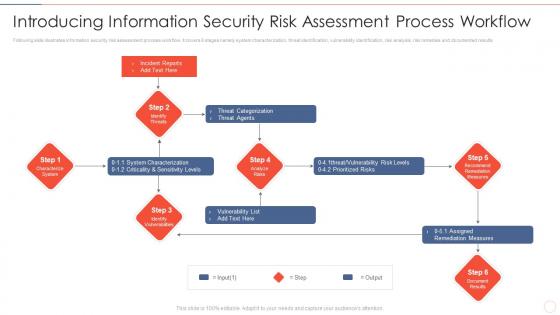 Introducing process workflow effective information security risk management process
Introducing process workflow effective information security risk management processFollowing slide illustrates information security risk assessment process workflow. It covers 6 stages namely system characterization, threat identification, vulnerability identification, risk analysis, risk remedies and documented results Deliver an outstanding presentation on the topic using this Introducing Process Workflow Effective Information Security Risk Management Process. Dispense information and present a thorough explanation of Threat Categorization, System Characterization, Assigned Remediation Measures using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
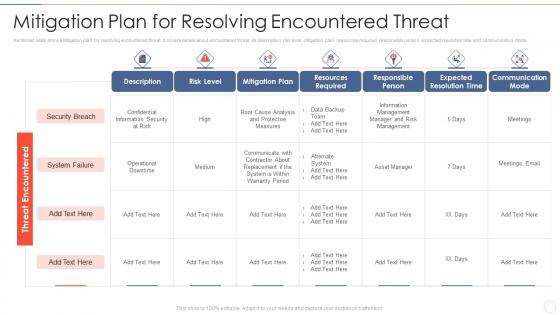 Mitigation plan for threat effective information security risk management process
Mitigation plan for threat effective information security risk management processMentioned slide shows mitigation plan for resolving encountered threat. It covers details about encountered threat, its description, risk level, mitigation plan, resources required, responsible person, expected resolution time and communication mode.Deliver an outstanding presentation on the topic using this Mitigation Plan For Threat Effective Information Security Risk Management Process. Dispense information and present a thorough explanation of Resources Required, Expected Resolution Time, Communication Mode using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
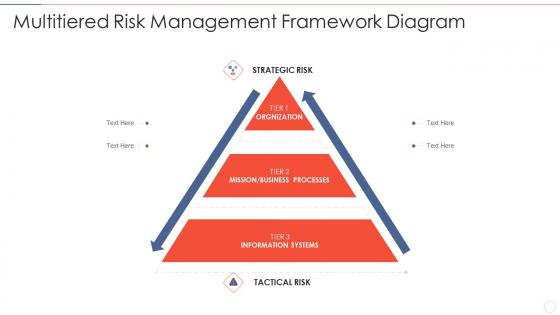 Multitiered risk effective information security risk management process
Multitiered risk effective information security risk management processIntroducing Multitiered Risk Effective Information Security Risk Management Process to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Orgnization, Mission Or Business Processes, Information Systems, using this template. Grab it now to reap its full benefits.
-
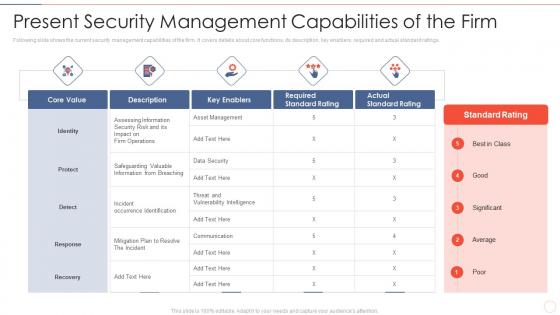 Present security effective information security risk management process
Present security effective information security risk management processFollowing slide shows the current security management capabilities of the firm. It covers details about core functions, its description, key enablers, required and actual standard ratings.Present the topic in a bit more detail with this Present Security Effective Information Security Risk Management Process. Use it as a tool for discussion and navigation on Assessing Information, Incident Occurrence Identification, Vulnerability Intelligence. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Risk reporting and likelihood effective information security risk management process
Risk reporting and likelihood effective information security risk management processMentioned slide shows encountered risk reporting and its likelihood. It includes information about risk encountered, frequency, reported by status, attack scenario, affected asset and likelihood. Deliver an outstanding presentation on the topic using this Risk Reporting And Likelihood Effective Information Security Risk Management Process. Dispense information and present a thorough explanation of Attack Scenario, Risk Encountered, Equipment Failure using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
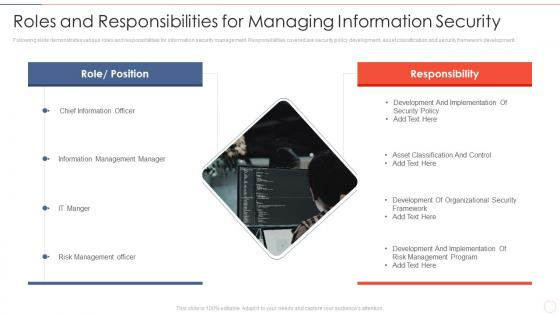 Roles and responsibilities effective information security risk management process
Roles and responsibilities effective information security risk management processFollowing slide demonstrates various roles and responsibilities for information security management. Responsibilities covered are security policy development, asset classification and security framework development.Increase audience engagement and knowledge by dispensing information using Roles And Responsibilities Effective Information Security Risk Management Process. This template helps you present information on one stage. You can also present information on Information Management Manager, Risk Management Officer, Development And Implementation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
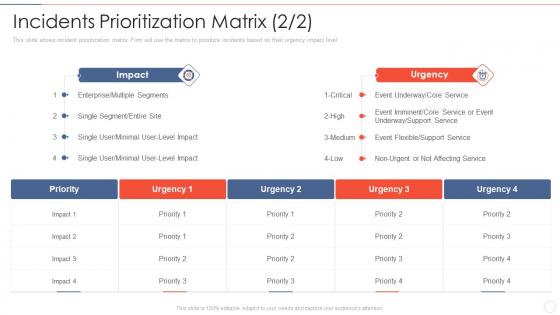 Security risk management process incidents prioritization matrix effective information
Security risk management process incidents prioritization matrix effective informationThis slide shows incident prioritization matrix. Firm will use the matrix to prioritize incidents based on their urgency impact level Present the topic in a bit more detail with this Security Risk Management Process Incidents Prioritization Matrix Effective Information. Use it as a tool for discussion and navigation on Enterprise Or Multiple Segments, Single Segment Or Entire Site, Event Underway. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Setting scenario security control effective information security risk management process
Setting scenario security control effective information security risk management processFollowing slide displays security control scenario setting. It includes scenario detail, category of security controls and controls description.Introducing Setting Scenario Security Control Effective Information Security Risk Management Process to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Management Controls, Operational Controls, Technical Controls, using this template. Grab it now to reap its full benefits.
-
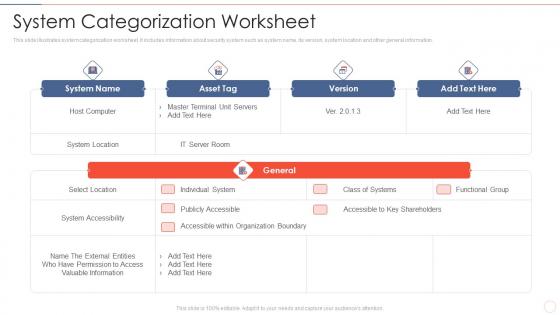 System categorization worksheet effective information security risk management process
System categorization worksheet effective information security risk management processThis slide illustrates system categorization worksheet. It includes information about security system such as system name, its version, system location and other general information.Present the topic in a bit more detail with this System Categorization Worksheet Effective Information Security Risk Management Process. Use it as a tool for discussion and navigation on System Accessibility, Accessible Within Organization Boundary, Valuable Information. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
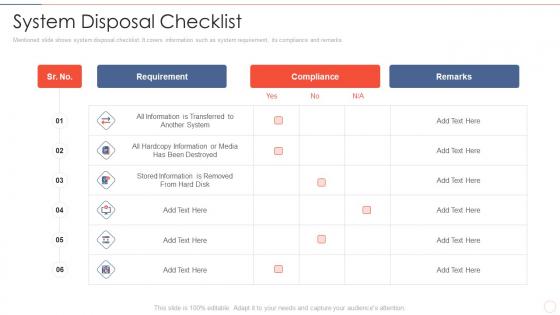 System disposal checklist effective information security risk management process
System disposal checklist effective information security risk management processMentioned slide shows system disposal checklist. It covers information such as system requirement, its compliance and remarks.Deliver an outstanding presentation on the topic using this System Disposal Checklist Effective Information Security Risk Management Process. Dispense information and present a thorough explanation of Stored Information Is Removed, Hardcopy Information, Requirement using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 System management checklist effective information security risk management process
System management checklist effective information security risk management processFollowing slide displays system management checklist. It includes system management activities and frequency of performing them.Present the topic in a bit more detail with this System Management Checklist Effective Information Security Risk Management Process. Use it as a tool for discussion and navigation on System Monitoring, Security Patches, Virus Scanning . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
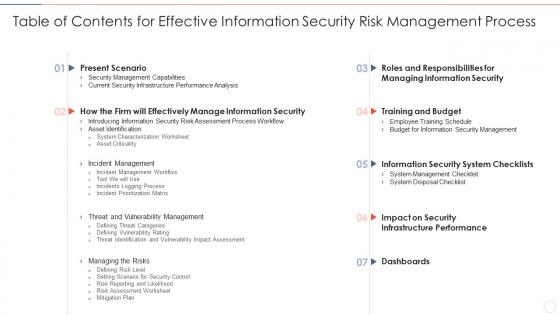 Table of contents for effective information security risk management process
Table of contents for effective information security risk management processDeliver an outstanding presentation on the topic using this Table Of Contents For Effective Information Security Risk Management Process. Dispense information and present a thorough explanation of Present Scenario, Training And Budget, Dashboards using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.



