Powerpoint Templates and Google slides for Secured Information Management System
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Roadmap information security risk management program
Roadmap information security risk management programIntroducing Roadmap Information Security Risk Management Program to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Roadmap, using this template. Grab it now to reap its full benefits.
-
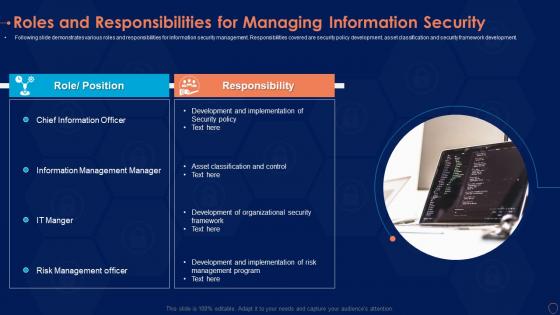 Roles and responsibilities for managing information security ppt ideas graphics
Roles and responsibilities for managing information security ppt ideas graphicsFollowing slide demonstrates various roles and responsibilities for information security management. Responsibilities covered are security policy development, asset classification and security framework development. Increase audience engagement and knowledge by dispensing information using Roles And Responsibilities For Managing Information Security Ppt Ideas Graphics. This template helps you present information on five stages. You can also present information on Information, Asset, Classification using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
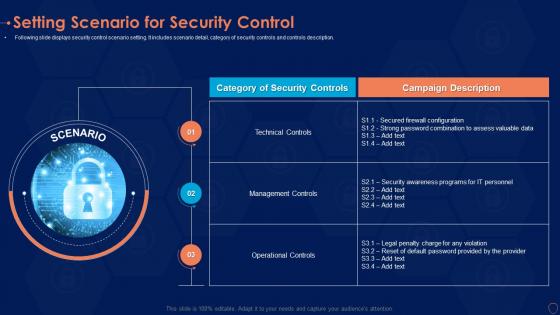 Setting scenario control information security risk management program
Setting scenario control information security risk management programFollowing slide displays security control scenario setting. It includes scenario detail, category of security controls and controls description. Present the topic in a bit more detail with this Setting Scenario Control Information Security Risk Management Program. Use it as a tool for discussion and navigation on Controls, Security, Management Controls. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 System disposal checklist information security risk management program
System disposal checklist information security risk management programMentioned slide shows system disposal checklist. It covers information such as system requirement, its compliance and remarks. Deliver an outstanding presentation on the topic using this System Disposal Checklist Information Security Risk Management Program. Dispense information and present a thorough explanation of Information, Transferred, Requirement using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 System key activities information security risk management program
System key activities information security risk management programFollowing slide displays system management checklist. It includes system management activities and frequency of performing them. Present the topic in a bit more detail with this System Key Activities Information Security Risk Management Program. Use it as a tool for discussion and navigation on System Monitoring, Security Patches, Virus Scanning . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Table of contents information security risk management program
Table of contents information security risk management programIntroducing Table Of Contents Information Security Risk Management Program to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Security, Management, Capabilities, using this template. Grab it now to reap its full benefits.
-
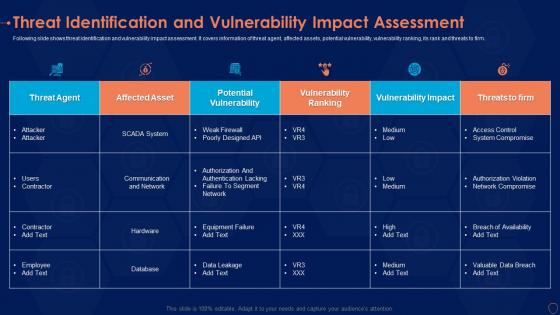 Threat identification assessment information security risk management program
Threat identification assessment information security risk management programThreat Agent, Potential Vulnerability, Vulnerability Ranking Deliver an outstanding presentation on the topic using this Threat Identification Assessment Information Security Risk Management Program. Dispense information and present a thorough explanation of Threat Agent, Potential Vulnerability, Vulnerability Ranking using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Threat vulnerability dashboard information security risk management program
Threat vulnerability dashboard information security risk management programFollowing slide displays threat and vulnerability management dashboard. It covers KPIs such as organization exposure score, system configuration score and severity score. Present the topic in a bit more detail with this Threat Vulnerability Dashboard Information Security Risk Management Program. Use it as a tool for discussion and navigation on Exposure Score, Vulnerable Software, Security Recommendation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Timeline information security risk management program
Timeline information security risk management programIncrease audience engagement and knowledge by dispensing information using Timeline Information Security Risk Management Program. This template helps you present information on six stages. You can also present information on Timeline, 2016 To 2021 using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
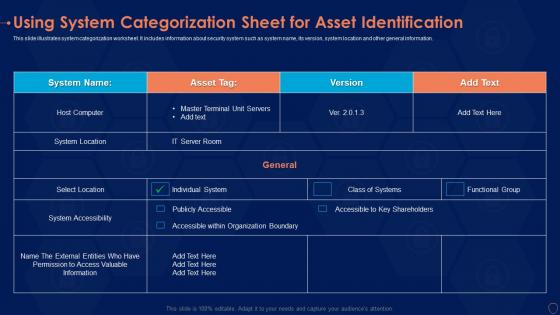 Using system categorization information security risk management program
Using system categorization information security risk management programDeliver an outstanding presentation on the topic using this Using System Categorization Information Security Risk Management Program. Dispense information and present a thorough explanation of Accessibility, Location, System using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
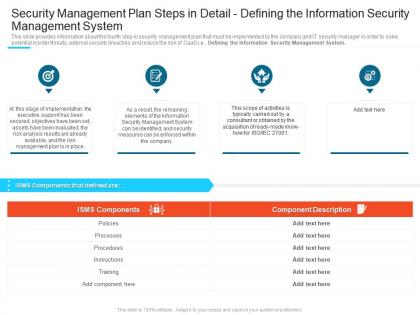 Defining the information security management system steps set up advanced security management plan
Defining the information security management system steps set up advanced security management planThis slide provides information about the fourth step in security management plan that must be implemented by the company and IT security manager in order to solve potential insider threats, external security breaches and reduce the risk of CaaS i.e., Defining the Information Security Management System. Introducing Defining The Information Security Management System Steps Set Up Advanced Security Management Plan to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Security Management Plan Steps In Detail Defining The Information Security Management System, using this template. Grab it now to reap its full benefits.
-
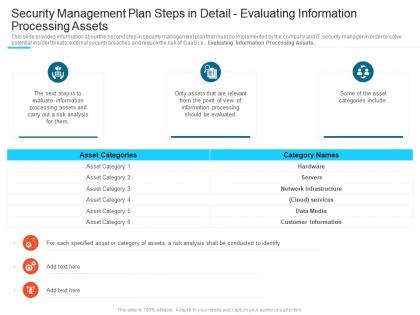 Evaluating information processing assets steps set up advanced security management plan ppt tips
Evaluating information processing assets steps set up advanced security management plan ppt tipsThis slide provides information about the second step in security management plan that must be implemented by the company and IT security manager in order to solve potential insider threats, external security breaches and reduce the risk of CaaS i.e. Evaluating Information Processing Assets. Increase audience engagement and knowledge by dispensing information using Evaluating Information Processing Assets Steps Set Up Advanced Security Management Plan Ppt Tips. This template helps you present information on three stages. You can also present information on Security Management Plan Steps In Detail Evaluating Information Processing Assets using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
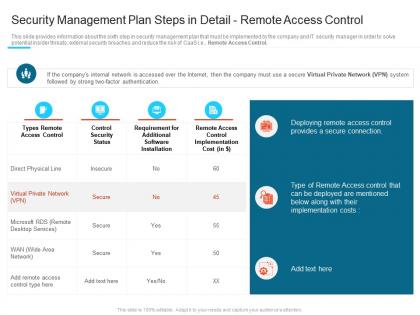 Remote access control steps set up advanced security management plan ppt information
Remote access control steps set up advanced security management plan ppt informationThis slide provides information about the sixth step in security management plan that must be implemented by the company and IT security manager in order to solve potential insider threats, external security breaches and reduce the risk of CaaS i.e., Remote Access Control. Deliver an outstanding presentation on the topic using this Remote Access Control Steps Set Up Advanced Security Management Plan Ppt Information. Dispense information and present a thorough explanation of Types Remote Access Control, Control Security Status, Remote Access Control using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Roadmap steps set up advanced security management plan ppt information
Roadmap steps set up advanced security management plan ppt informationIntroducing Roadmap Steps Set Up Advanced Security Management Plan Ppt Information to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Roadmap, using this template. Grab it now to reap its full benefits.
-
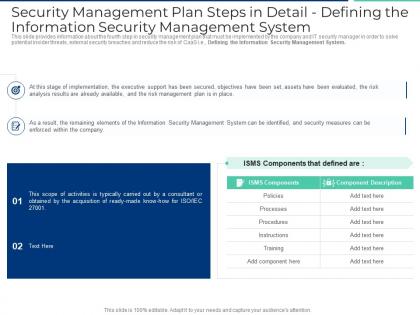 Security management plan steps in detail defining the information security management system ppt show
Security management plan steps in detail defining the information security management system ppt showThis slide provides information about the fourth step in security management plan that must be implemented by the company and IT security manager in order to solve potential insider threats, external security breaches and reduce the risk of CaaS i.e. Defining the Information Security Management System. Present the topic in a bit more detail with this Security Management Plan Steps In Detail Defining The Information Security Management System Ppt Show. Use it as a tool for discussion and navigation on Processes, Procedures, Instructions, Training, Policies. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
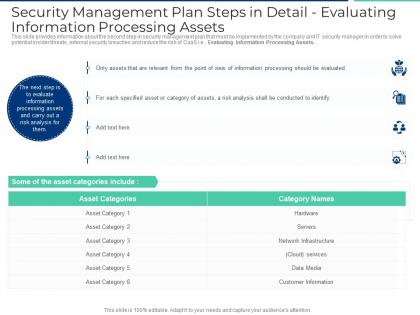 Security management plan steps in detail evaluating information processing assets ppt file design
Security management plan steps in detail evaluating information processing assets ppt file designThis slide provides information about the second step in security management plan that must be implemented by the company and IT security manager in order to solve potential insider threats, external security breaches and reduce the risk of CaaS i.e. Evaluating Information Processing Assets. Deliver an outstanding presentation on the topic using this Security Management Plan Steps In Detail Evaluating Information Processing Assets Ppt File Design. Dispense information and present a thorough explanation of Information Processing, Identify, Category Of Assets, Risk Analysis using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Management information security ppt powerpoint presentation professional background designs cpb
Management information security ppt powerpoint presentation professional background designs cpbPresenting our Management Information Security Ppt Powerpoint Presentation Professional Background Designs Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Management Information Security This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
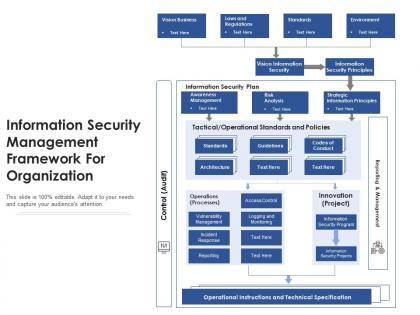 Information security management framework for organization
Information security management framework for organizationPresenting our well-structured Information Security Management Framework For Organization. The topics discussed in this slide are Operations, Innovation, Information Security Plan, Operational Standards, Policies. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Quantitative framework for information security risk management
Quantitative framework for information security risk managementPresenting our well-structured Quantitative Framework For Information Security Risk Management. The topics discussed in this slide are Discovery, Evaluation, Metrics. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
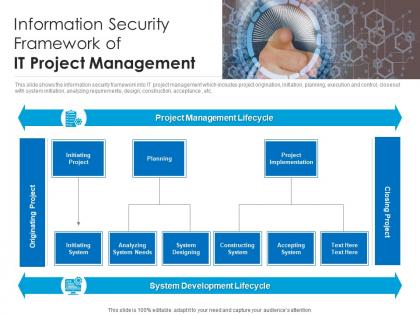 Information security framework of it project management
Information security framework of it project managementThis slide shows the information security framework into IT project management which includes project origination, initiation, planning, execution and control, closeout with system initiation, analyzing requirements, design, construction, acceptance, etc. Introducing our Information Security Framework Of IT Project Management set of slides. The topics discussed in these slides are Initiating Project, Planning, Project Implementation, Initiating System, System Designing. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
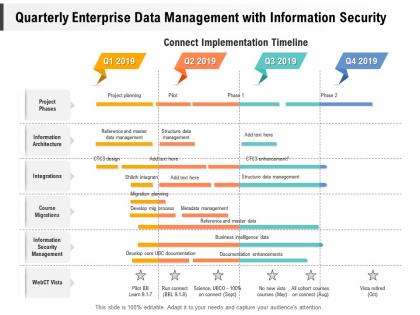 Quarterly enterprise data management with information security
Quarterly enterprise data management with information securityPresenting Quarterly Enterprise Data Management With Information Security PowerPoint slide. This PPT slide is available at 4,3 and 16,9 aspect ratios. You can download this PPT theme in various formats like PDF, PNG, and JPG. This PowerPoint template is completely editable and you can modify the font size, font type, and shapes as per your requirements. Our PPT layout is compatible with Google Slides.
-
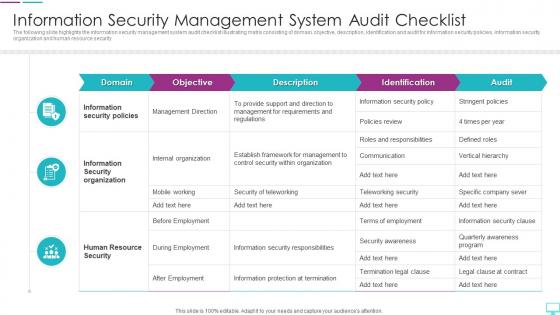 Information Security Management System Audit Checklist
Information Security Management System Audit ChecklistThe following slide highlights the information security management system audit checklist illustrating matrix consisting of domain, objective, description, identification and audit for information security policies, information security organization and human resource security Introducing our Information Security Management System Audit Checklist set of slides. The topics discussed in these slides are Information, Security, Management. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Information Security Management System Audit Framework
Information Security Management System Audit FrameworkThe following slide highlights the information security system audit framework illustrating key headings which includes act, plan, do and check which are used for update and improve isms, establish isms, implement policy and control and monitor and review performance Presenting our set of slides with name Information Security Management System Audit Framework. This exhibits information on four stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Framework, Management, Information.
-
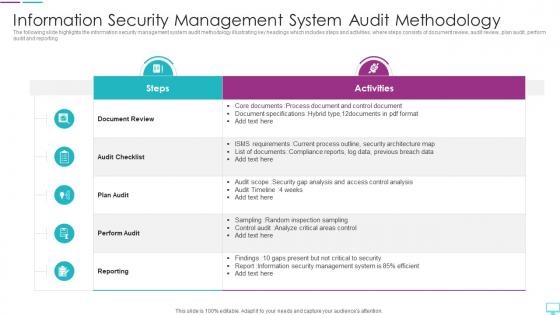 Information Security Management System Audit Methodology
Information Security Management System Audit MethodologyThe following slide highlights the information security management system audit methodology illustrating key headings which includes steps and activities, where steps consists of document review, audit review, plan audit, perform audit and reporting Presenting our well-structured Information Security Management System Audit Methodology. The topics discussed in this slide are Management, Methodology, Information Security. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
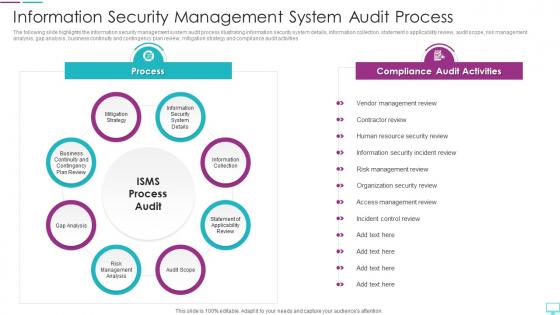 Information Security Management System Audit Process
Information Security Management System Audit ProcessThe following slide highlights the information security management system audit process illustrating information security system details, information collection, statement o applicability review, audit scope, risk management analysis, gap analysis, business continuity and contingency plan review, mitigation strategy and compliance audit activities Introducing our Information Security Management System Audit Process set of slides. The topics discussed in these slides are Information Collection, Mitigation Strategy, Gap Analysis. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Steps Of Information Security Management System Internal Audit
Steps Of Information Security Management System Internal AuditThe following slide highlights the steps of information security management system internal audit illustrating document review, management review, field review, analysis and reporting to assist the organization to find out the gaps in the security management system Presenting our set of slides with name Steps Of Information Security Management System Internal Audit. This exhibits information on five stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Document Review, Management Review, Information.
-
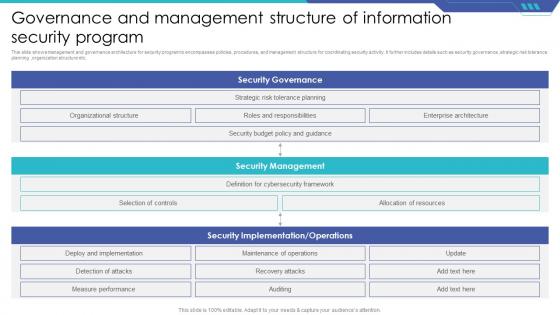 Governance And Management Structure Of Information Security Program
Governance And Management Structure Of Information Security ProgramThis slide shows management and governance architecture for security program to encompasses policies, procedures, and management structure for coordinating security activity. It further includes details such as security governance ,strategic risk tolerance planning ,organization structure etc. Presenting our well structured Governance And Management Structure Of Information Security Program The topics discussed in this slide are Security Governance, Security Management. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Information Security Management Program To Protect Data
Information Security Management Program To Protect DataThis slide shows information security program checklist that helps toidentify potential weaknesses or vulnerabilities in system. It further includes metrics such as risk management, information security policy ,information security responsibility etc. Presenting our well structured Information Security Management Program To Protect Data The topics discussed in this slide are Risk Management, Information Security Policy. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
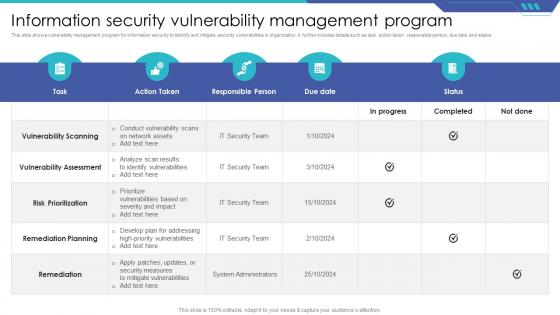 Information Security Vulnerability Management Program
Information Security Vulnerability Management ProgramThis slide shows vulnerability management program for information security to identify and mitigate security vulnerabilities in organization. It further includes details such as task, action taken, responsible person, due date and status. Presenting our well structured Information Security Vulnerability Management Program The topics discussed in this slide are Vulnerability Scanning, Remediation Planning, Remediation. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.


