Powerpoint Templates and Google slides for Securing The Wheels
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 IoT Security And Privacy Safeguarding The Digital Ecosystem Powerpoint Presentation Slides IoT CD
IoT Security And Privacy Safeguarding The Digital Ecosystem Powerpoint Presentation Slides IoT CDDeliver this complete deck to your team members and other collaborators. Encompassed with stylized slides presenting various concepts, this IoT Security And Privacy Safeguarding The Digital Ecosystem Powerpoint Presentation Slides IoT CD is the best tool you can utilize. Personalize its content and graphics to make it unique and thought-provoking. All the seventy six slides are editable and modifiable, so feel free to adjust them to your business setting. The font, color, and other components also come in an editable format making this PPT design the best choice for your next presentation. So, download now.
-
 Case competition overcome the challenge of cyber security in healthcare complete deck
Case competition overcome the challenge of cyber security in healthcare complete deckDeliver this complete deck to your team members and other collaborators. Encompassed with stylized slides presenting various concepts, this Case Competition Overcome The Challenge Of Cyber Security In Healthcare Complete Deck is the best tool you can utilize. Personalize its content and graphics to make it unique and thought provoking. All the fourty nine slides are editable and modifiable, so feel free to adjust them to your business setting. The font, color, and other components also come in an editable format making this PPT design the best choice for your next presentation. So, download now.
-
 Overcome the it security challenges facing by healthcare company case competition complete deck
Overcome the it security challenges facing by healthcare company case competition complete deckDeliver this complete deck to your team members and other collaborators. Encompassed with stylized slides presenting various concepts, this Overcome The It Security Challenges Facing By Healthcare Company Case Competition Complete Deck is the best tool you can utilize. Personalize its content and graphics to make it unique and thought provoking. All the fourty six slides are editable and modifiable, so feel free to adjust them to your business setting. The font, color, and other components also come in an editable format making this PPT design the best choice for your next presentation. So, download now.
-
 Man In The Middle Attack In Cyber Security Training Ppt
Man In The Middle Attack In Cyber Security Training PptPresenting Man in the Browser Attack in Cyber Security. These slides are 100 percent made in PowerPoint and are compatible with all screen types and monitors. They also support Google Slides. Premium Customer Support available. Suitable for use by managers, employees, and organizations. These slides are easily customizable. You can edit the color, text, icon, and font size to suit your requirements.
-
 Man In The Browser Attack In Cyber Security Training Ppt
Man In The Browser Attack In Cyber Security Training PptPresenting Man in the Browser Attack in Cyber Security. These slides are 100 percent made in PowerPoint and are compatible with all screen types and monitors. They also support Google Slides. Premium Customer Support available. Suitable for use by managers, employees, and organizations. These slides are easily customizable. You can edit the color, text, icon, and font size to suit your requirements.
-
 Application Security In The Cloud Training Ppt
Application Security In The Cloud Training PptPresenting Application Security in the Cloud. This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizable alter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
 Understanding The Working Of Network Security Training Ppt
Understanding The Working Of Network Security Training PptPresenting Understanding the Working of Network Security. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. It is well crafted and designed by our PowerPoint specialists. Suitable for use by managers, employees, and organizations. You can edit the color, text, icon, and font size to suit your requirements. The PPT also supports Google Slides. Even Premium Customer Support is also available. Download now and present with confidence.
-
 Securing Your Accounts As One Of The Tips For Investing In Cryptocurrency Training Ppt
Securing Your Accounts As One Of The Tips For Investing In Cryptocurrency Training PptPresenting Securing your accounts as one of the tips for Investing in Cryptocurrency. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. All slides are customizable. You can add or delete the content as per your need. Download this professionally designed business presentation, add your content, and present it with confidence.
-
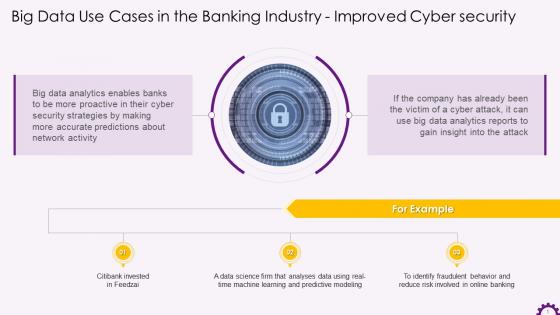 Big Data For Improved Cyber Security In The Banking Training Ppt
Big Data For Improved Cyber Security In The Banking Training PptPresenting Implementing Big Data for improved cyber security in the Banking Industry. This slide is well crafted and designed by our PowerPoint specialists. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. You can add or delete the content as per your need.
-
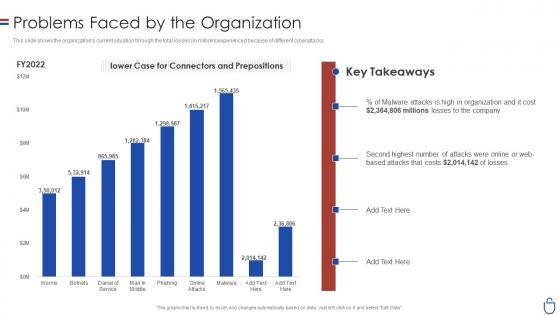 Data security it problems faced by the organization ppt slides layout
Data security it problems faced by the organization ppt slides layoutThis slide shows the organizations current situation through the total losses in millions experienced because of different cyberattacks. Deliver an outstanding presentation on the topic using this Data Security IT Problems Faced By The Organization Ppt Slides Layout. Dispense information and present a thorough explanation of Worms, Phishing, Online Attacks, Man Middle using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
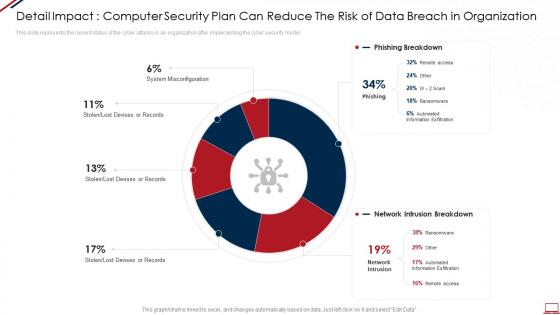 Computer system security detail impact computer security plan can reduce the risk of data breach in organization
Computer system security detail impact computer security plan can reduce the risk of data breach in organizationThis slide represents the current status of the cyber attacks in an organization after implementing the cyber security model. Present the topic in a bit more detail with this Computer System Security Detail Impact Computer Security Plan Can Reduce The Risk Of Data Breach In Organization. Use it as a tool for discussion and navigation on System Misconfiguration, Network Intrusion, Automated Information Exfiltration. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
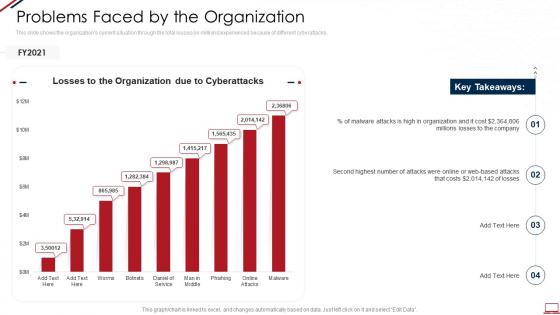 Computer system security problems faced by the organization
Computer system security problems faced by the organizationThis slide shows the organizations current situation through the total losses in millions experienced because of different cyberattacks. Deliver an outstanding presentation on the topic using this Computer System Security Problems Faced By The Organization. Dispense information and present a thorough explanation of Problems Faced By The Organization using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
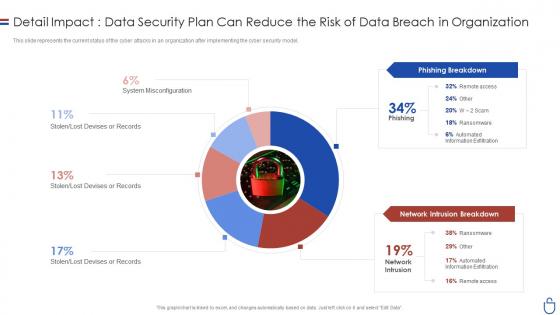 Data security it detail impactdata security plan can reduce the risk of data
Data security it detail impactdata security plan can reduce the risk of dataThis slide represents the current status of the cyber attacks in an organization after implementing the cyber security model. Deliver an outstanding presentation on the topic using this Data Security IT Detail Impactdata Security Plan Can Reduce The Risk Of Data. Dispense information and present a thorough explanation of System Misconfiguration, Lost Devises Or Records, Stolen, Lost Devises Or Records, Phishing Breakdown, Network Intrusion Breakdown using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
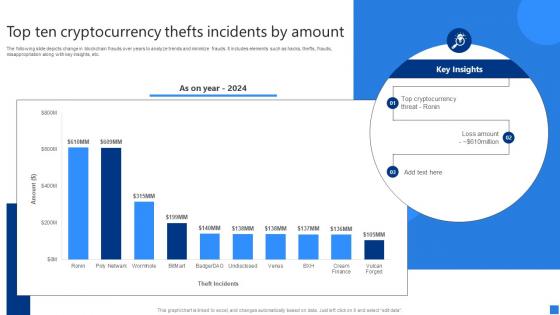 Top Ten Cryptocurrency Thefts Securing Blockchain Transactions A Beginners Guide BCT SS V
Top Ten Cryptocurrency Thefts Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide depicts change in blockchain frauds over years to analyze trends and minimize frauds. It includes elements such as hacks, thefts, frauds, misappropriation along with key insights, etc. Deliver an outstanding presentation on the topic using this Top Ten Cryptocurrency Thefts Securing Blockchain Transactions A Beginners Guide BCT SS V. Dispense information and present a thorough explanation of Top Cryptocurrency Threat, Loss Amount, Incidents Amount using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Table Of Contents IoT Security And Privacy Safeguarding The Digital Ecosystem IoT SS
Table Of Contents IoT Security And Privacy Safeguarding The Digital Ecosystem IoT SSIncrease audience engagement and knowledge by dispensing information using Table Of Contents IoT Security And Privacy Safeguarding The Digital Ecosystem IoT SS. This template helps you present information on five stages. You can also present information on Introduction Iot Security, Need Iot, Security Management using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
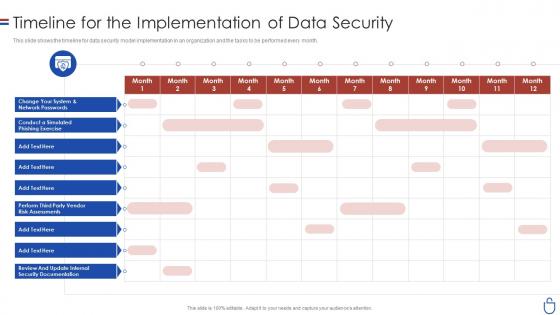 Data security it timeline for the implementation of data security
Data security it timeline for the implementation of data securityThis slide shows the timeline for data security model implementation in an organization and the tasks to be performed every month. Present the topic in a bit more detail with this Data Security IT Timeline For The Implementation Of Data Security. Use it as a tool for discussion and navigation on Phishing Exercise, Risk Assessments, Security Documentation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
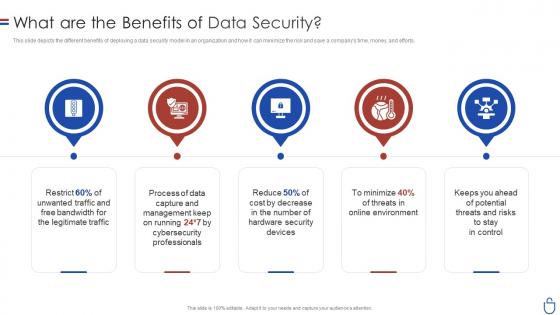 Data security it what are the benefits of data security
Data security it what are the benefits of data securityThis slide depicts the different benefits of deploying a data security model in an organization and how it can minimize the risk and save a companys time, money, and efforts. Increase audience engagement and knowledge by dispensing information using Data Security IT What Are The Benefits Of Data Security. This template helps you present information on five stages. You can also present information on Legitimate Traffic, Hardware Security Devices, Threats And Risks, Management using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
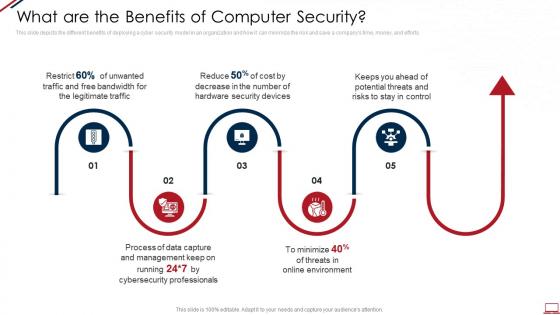 Computer system security what are the benefits of computer security
Computer system security what are the benefits of computer securityThis slide depicts the different benefits of deploying a cyber security model in an organization and how it can minimize the risk and save a companys time, money, and efforts. Increase audience engagement and knowledge by dispensing information using Computer System Security What Are The Benefits Of Computer Security. This template helps you present information on five stages. You can also present information on Management, Process, Security Devices, Potential Threats using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
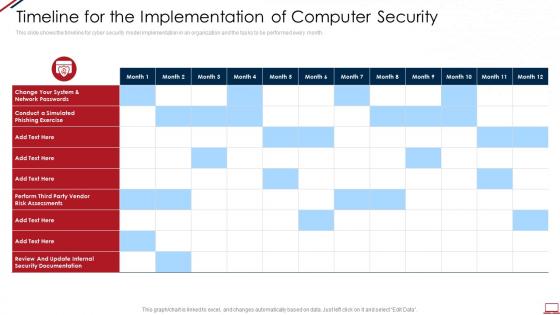 Computer system security timeline for the implementation of computer security
Computer system security timeline for the implementation of computer securityThis slide shows the timeline for cyber security model implementation in an organization and the tasks to be performed every month. Present the topic in a bit more detail with this Computer System Security Timeline For The Implementation Of Computer Security. Use it as a tool for discussion and navigation on Security, Risk Assessments, Perform. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Testimonials in the security guard services proposal ppt slides design templates
Testimonials in the security guard services proposal ppt slides design templatesIncrease audience engagement and knowledge by dispensing information using Testimonials In The Security Guard Services Proposal Ppt Slides Design Templates. This template helps you present information on two stages. You can also present information on Testimonials, Security Guard Services using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Contact us in the security guard services proposal ppt slides model
Contact us in the security guard services proposal ppt slides modelPresent the topic in a bit more detail with this Contact Us In The Security Guard Services Proposal Ppt Slides Model. Use it as a tool for discussion and navigation on Contact Us, Security Guard Services. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Next steps in the security guard services proposal ppt slides visuals
Next steps in the security guard services proposal ppt slides visualsIncrease audience engagement and knowledge by dispensing information using Next Steps In The Security Guard Services Proposal Ppt Slides Visuals. This template helps you present information on three stages. You can also present information on Next Steps, Security Guard Services using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Our services for the security guard services proposal ppt slides guide
Our services for the security guard services proposal ppt slides guidePresent the topic in a bit more detail with this Our Services For The Security Guard Services Proposal Ppt Slides Guide. Use it as a tool for discussion and navigation on Health Facilities, Corporate Complexes, Educational Institutions, Physical Security. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
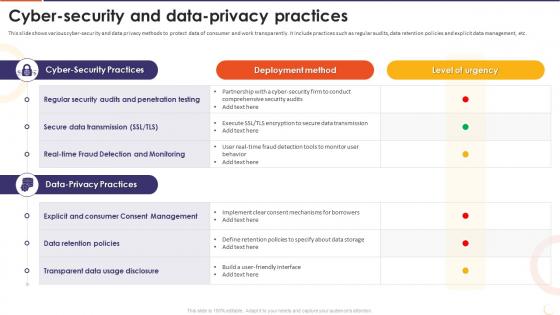 The Future Of Financing Digital Cyber Security And Data Privacy Practices
The Future Of Financing Digital Cyber Security And Data Privacy PracticesThis slide shows various cyber-security and data privacy methods to protect data of consumer and work transparently. It include practices such as regular audits, data retention policies and explicit data management, etc. Present the topic in a bit more detail with this The Future Of Financing Digital Cyber Security And Data Privacy Practices. Use it as a tool for discussion and navigation on Regular Security Audits, Penetration Testing, Secure Data Transmission, Data Retention Policies, Transparent Data Usage Disclosure. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
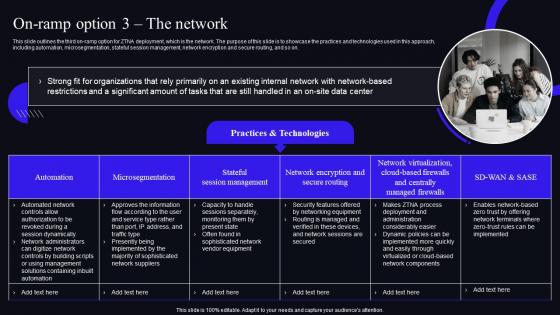 On Ramp Option 3 The Network Zero Trust Security Model
On Ramp Option 3 The Network Zero Trust Security ModelThis slide outlines the third on-ramp option for ZTNA deployment, which is the network. The purpose of this slide is to showcase the practices and technologies used in this approach, including automation, microsegmentation, stateful session management, network encryption and secure routing, and so on. Present the topic in a bit more detail with this On Ramp Option 3 The Network Zero Trust Security Model. Use it as a tool for discussion and navigation on Organizations, Microsegmentation, Stateful Session Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
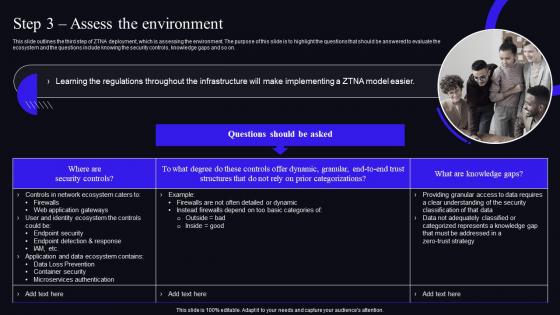 Step 3 Assess The Environment Zero Trust Security Model
Step 3 Assess The Environment Zero Trust Security ModelThis slide outlines the third step of ZTNA deployment, which is assessing the environment. The purpose of this slide is to highlight the questions that should be answered to evaluate the ecosystem and the questions include knowing the security controls, knowledge gaps and so on. Deliver an outstanding presentation on the topic using this Step 3 Assess The Environment Zero Trust Security Model. Dispense information and present a thorough explanation of Knowledge, Categorizations, Structures using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
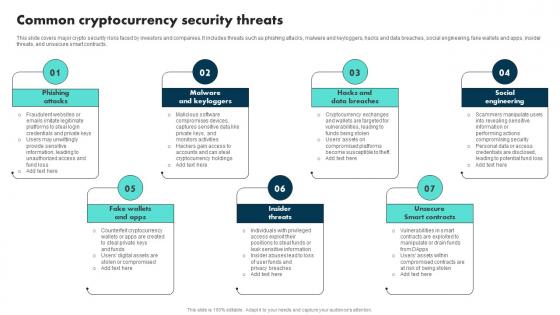 Common Cryptocurrency Security Threats Exploring The Role BCT SS
Common Cryptocurrency Security Threats Exploring The Role BCT SSThis slide covers major crypto security risks faced by investors and companies. It includes threats such as phishing attacks, malware and keyloggers, hacks and data breaches, social engineering, fake wallets and apps, insider threats, and unsecure smart contracts. Introducing Common Cryptocurrency Security Threats Exploring The Role BCT SS to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Phishing Attacks, Malware And Keyloggers, Insider Threats, using this template. Grab it now to reap its full benefits.
-
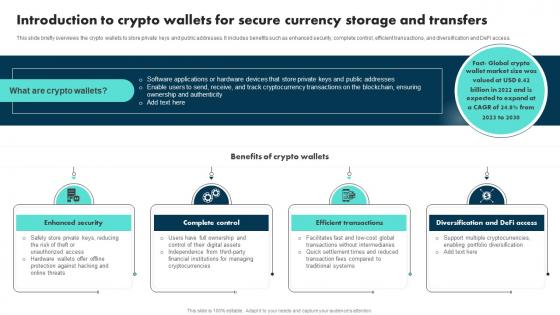 Introduction To Crypto Wallets For Secure Currency Storage And Transfers Exploring The Role BCT SS
Introduction To Crypto Wallets For Secure Currency Storage And Transfers Exploring The Role BCT SSThis slide briefly overviews the crypto wallets to store private keys and public addresses. It includes benefits such as enhanced security, complete control, efficient transactions, and diversification and DeFi access. Introducing Introduction To Crypto Wallets For Secure Currency Storage And Transfers Exploring The Role BCT SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Enhanced Security, Complete Control, Efficient Transactions, using this template. Grab it now to reap its full benefits.
-
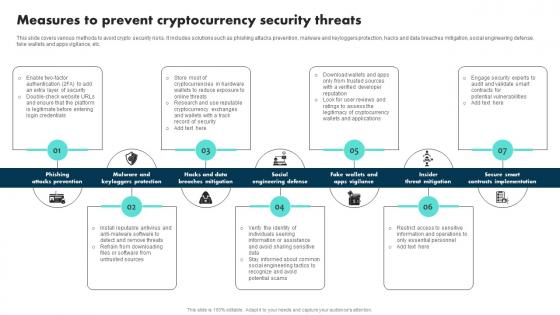 Measures To Prevent Cryptocurrency Security Threats Exploring The Role BCT SS
Measures To Prevent Cryptocurrency Security Threats Exploring The Role BCT SSThis slide covers various methods to avoid crypto security risks. It includes solutions such as phishing attacks prevention, malware and keyloggers protection, hacks and data breaches mitigation, social engineering defense, fake wallets and apps vigilance, etc. Introducing Measures To Prevent Cryptocurrency Security Threats Exploring The Role BCT SS to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Phishing Attacks Prevention, Breaches Mitigation, Social Engineering Defense, using this template. Grab it now to reap its full benefits.
-
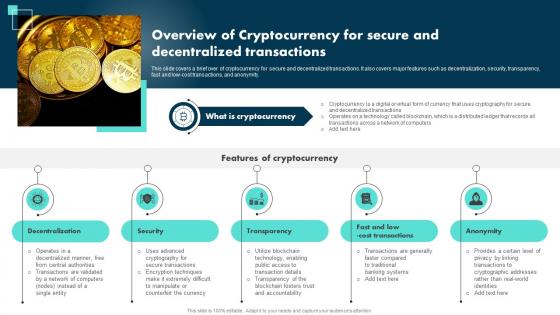 Overview Of Cryptocurrency For Secure And Decentralized Transactions Exploring The Role BCT SS
Overview Of Cryptocurrency For Secure And Decentralized Transactions Exploring The Role BCT SSThis slide covers a brief over of cryptocurrency for secure and decentralized transactions. It also covers major features such as decentralization, security, transparency, fast and low-cost transactions, and anonymity. Introducing Overview Of Cryptocurrency For Secure And Decentralized Transactions Exploring The Role BCT SS to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Decentralization, Security, Transparency, Anonymity, using this template. Grab it now to reap its full benefits.
-
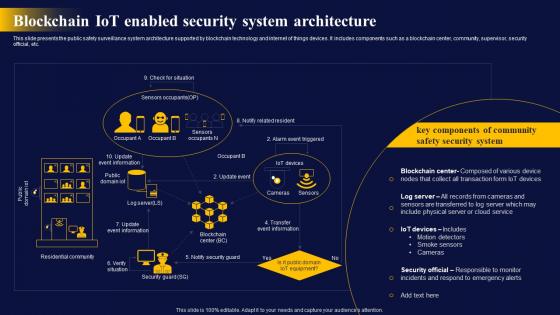 Blockchain IoT Enabled Security The Ultimate Guide To Blockchain Integration IoT SS
Blockchain IoT Enabled Security The Ultimate Guide To Blockchain Integration IoT SSThis slide presents the public safety surveillance system architecture supported by blockchain technology and internet of things devices. It includes components such as a blockchain center, community, supervisor, security official, etc. Present the topic in a bit more detail with this Blockchain IoT Enabled Security The Ultimate Guide To Blockchain Integration IoT SS. Use it as a tool for discussion and navigation on Security, System, Architecture. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Navigating The Banking Industry Banking Industry Framework For Economic Financial Security
Navigating The Banking Industry Banking Industry Framework For Economic Financial SecurityThis slide showcases conceptualisation of bank operations. This template focuses on providing an easy way for people to pay for goods and services and save their money. It includes information related to customer relationship management, etc. Present the topic in a bit more detail with this Navigating The Banking Industry Banking Industry Framework For Economic Financial Security. Use it as a tool for discussion and navigation on Contact Management, Customer Risk, Customer Relationship Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Proactively Assess The Impact Of Potential Security Internet Of Things IoT Security Cybersecurity SS
Proactively Assess The Impact Of Potential Security Internet Of Things IoT Security Cybersecurity SSThis slide showcases application of impact assessment on internet of things IoT device security events, referable for businesses in developing mitigation process. It provides details about threat model, security layers, etc. Introducing Proactively Assess The Impact Of Potential Security Internet Of Things IoT Security Cybersecurity SS to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Comprehensive Security, Assessment And Security Layers, Credential Provisioning, using this template. Grab it now to reap its full benefits.
-
 Crypto Wallets Types And Applications Best Practices For The Security Of Crypto Wallets In Market
Crypto Wallets Types And Applications Best Practices For The Security Of Crypto Wallets In MarketThis slide aims to highlight some broad security aspects of crypto wallets. This slide outlines the general security purposes such as passwords, 2FA accounts, phrases for secure passwords, secure hardware, keeping the seed phrase off devices as well, etc. Deliver an outstanding presentation on the topic using this Crypto Wallets Types And Applications Best Practices For The Security Of Crypto Wallets In Market. Dispense information and present a thorough explanation of Storage Mechanism, Network, Crypto Wallets In Market, Multisignature Wallets using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Ethical Hacking And Network Security Overview Of The Company
Ethical Hacking And Network Security Overview Of The CompanyThis slide describes the overview of the company including the number of countries in which services are provided, total number of certified experts, number of tools and technologies and so on. Increase audience engagement and knowledge by dispensing information using Ethical Hacking And Network Security Overview Of The Company. This template helps you present information on four stages. You can also present information on Tools And Technologies, Subject Matter Professionals Engaged, Course Development using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
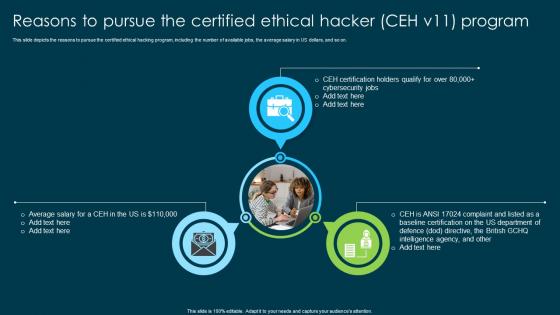 Ethical Hacking And Network Security Reasons To Pursue The Certified Ethical Hacker Ceh V11 Program
Ethical Hacking And Network Security Reasons To Pursue The Certified Ethical Hacker Ceh V11 ProgramThis slide depicts the reasons to pursue the certified ethical hacking program, including the number of available jobs, the average salary in US dollars, and so on. Increase audience engagement and knowledge by dispensing information using Ethical Hacking And Network Security Reasons To Pursue The Certified Ethical Hacker Ceh V11 Program. This template helps you present information on three stages. You can also present information on Ethical Hacking Program, Reasons To Pursue, Certified Ethical Hacker, Baseline Certification using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Agenda IoT Security And Privacy Safeguarding The Digital Ecosystem IoT SS
Agenda IoT Security And Privacy Safeguarding The Digital Ecosystem IoT SSIntroducing Agenda IoT Security And Privacy Safeguarding The Digital Ecosystem IoT SS to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Agenda, using this template. Grab it now to reap its full benefits.
-
 Icons Slide For IoT Security And Privacy Safeguarding The Digital Ecosystem IoT SS
Icons Slide For IoT Security And Privacy Safeguarding The Digital Ecosystem IoT SSPresenting our well crafted Icons Slide For IoT Security And Privacy Safeguarding The Digital Ecosystem IoT SS set of slides. The slides include icons that are innovatively designed by our team of experts. The icons are easy to edit so you can conveniently increase or decrease their size without any loss in resolution. Therefore, grab them instantly
-
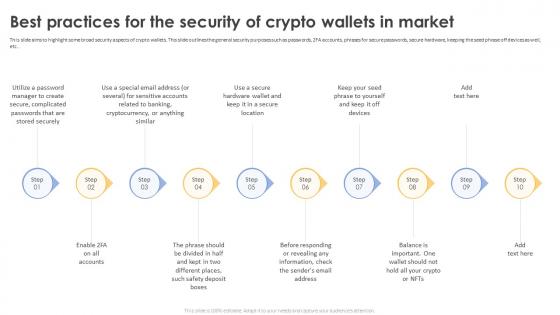 Secure Your Digital Assets Best Practices For The Security Of Crypto Wallets In Market
Secure Your Digital Assets Best Practices For The Security Of Crypto Wallets In MarketThis slide aims to highlight some broad security aspects of crypto wallets. This slide outlines the general security purposes such as passwords, 2FA accounts, phrases for secure passwords, secure hardware, keeping the seed phrase off devices as well, etc. Introducing Secure Your Digital Assets Best Practices For The Security Of Crypto Wallets In Market to increase your presentation threshold. Encompassed with ten stages, this template is a great option to educate and entice your audience. Dispence information on Security Of Crypto Wallets, Secure Hardware, Special Email Address, Complicated Passwords, using this template. Grab it now to reap its full benefits.
-
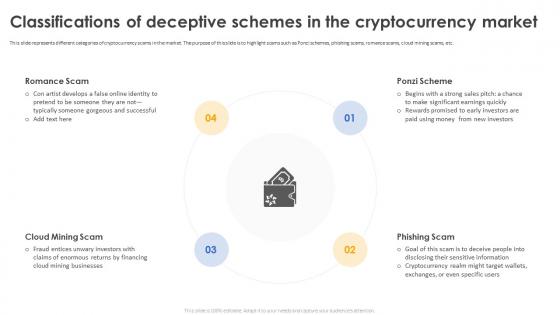 Secure Your Digital Assets Classifications Of Deceptive Schemes In The Cryptocurrency Market
Secure Your Digital Assets Classifications Of Deceptive Schemes In The Cryptocurrency MarketThis slide represents different categories of cryptocurrency scams in the market. The purpose of this slide is to highlight scams such as Ponzi schemes, phishing scams, romance scams, cloud mining scams, etc. Introducing Secure Your Digital Assets Classifications Of Deceptive Schemes In The Cryptocurrency Market to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Romance Scam, Ponzi Scheme, Phishing Scam, Cloud Mining Scam, Cryptocurrency Market, using this template. Grab it now to reap its full benefits.
-
 Secure Your Digital Assets Ways Cryptocurrency Can Alter The Global Economy
Secure Your Digital Assets Ways Cryptocurrency Can Alter The Global EconomyThis slide showcases the ways cryptocurrency can alter the global economy. The purpose of this slide is to highlight different ways of altering the global economy such as reducing inflation, giving financial stability, security, creativity, etc. Increase audience engagement and knowledge by dispensing information using Secure Your Digital Assets Ways Cryptocurrency Can Alter The Global Economy. This template helps you present information on seven stages. You can also present information on Reduces Inflation, Financial Stability, Potential To Replace Financial System, Cryptocurrencies Became using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
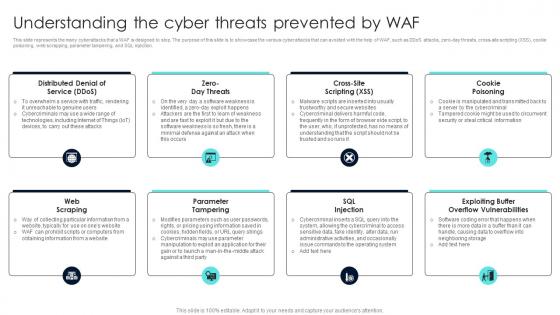 Firewall Network Security Understanding The Cyber Threats Prevented By Waf
Firewall Network Security Understanding The Cyber Threats Prevented By WafThis slide represents the many cyberattacks that a WAF is designed to stop. The purpose of this slide is to showcase the various cyber attacks that can avoided with the help of WAF, such as DDoS attacks, zero-day threats, cross-site scripting XSS, cookie poisoning, web scrapping, parameter tampering, and SQL injection. Introducing Firewall Network Security Understanding The Cyber Threats Prevented By Waf to increase your presentation threshold. Encompassed with Eight stages, this template is a great option to educate and entice your audience. Dispence information on Cookie Poisoning, Sql Injection, Parameter Tampering using this template. Grab it now to reap its full benefits.
-
 Firewall Network Security Firewall Best Practices To Secure The Network
Firewall Network Security Firewall Best Practices To Secure The NetworkThis slide represents the different critical practices to secure a network through a firewall. The purpose of this slide is to showcase a few key steps that organizations should keep in mind to secure their network properly, such as strengthening and configuring the firewall correctly, planning firewall deployment, and so on. Deliver an outstanding presentation on the topic using this Firewall Network Security Firewall Best Practices To Secure The Network Dispense information and present a thorough explanation of Problem,Solution,Outcome using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
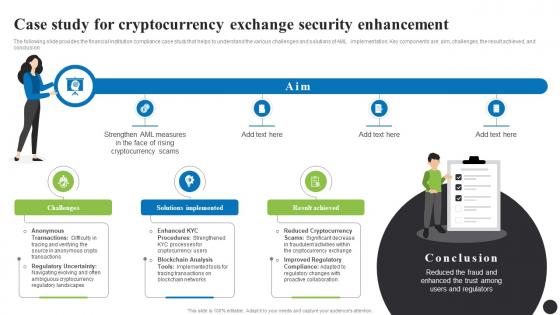 Case Study For Cryptocurrency Exchange Security Navigating The Anti Money Laundering Fin SS
Case Study For Cryptocurrency Exchange Security Navigating The Anti Money Laundering Fin SSThe following slide provides the financial institution compliance case study that helps to understand the various challenges and solutions of AML implementation. Key components are aim, challenges, the result achieved, and conclusion. Increase audience engagement and knowledge by dispensing information using Case Study For Cryptocurrency Exchange Security Navigating The Anti Money Laundering Fin SS. This template helps you present information on three stages. You can also present information on Challenges, Solutions Implemented, Result Achieved using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
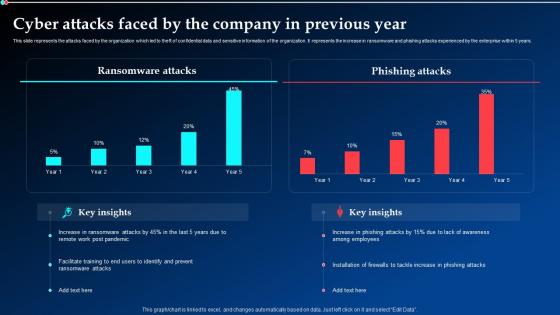 Cyber Attacks Faced By The Company In Previous Year Implementing Cyber Security Ppt Demonstration
Cyber Attacks Faced By The Company In Previous Year Implementing Cyber Security Ppt DemonstrationThis slide represents the attacks faced by the organization which led to theft of confidential data and sensitive information of the organization. It represents the increase in ransomware and phishing attacks experienced by the enterprise within 5 years. Present the topic in a bit more detail with this Cyber Attacks Faced By The Company In Previous Year Implementing Cyber Security Ppt Demonstration. Use it as a tool for discussion and navigation on Ransomware Attacks, Phishing Attacks, Previous Year. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
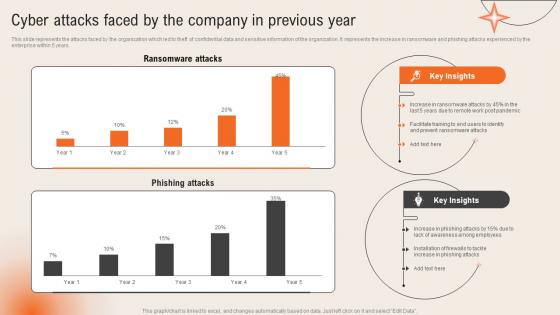 Cyber Attacks Faced By The Company In Previous Year Deploying Computer Security Incident Management
Cyber Attacks Faced By The Company In Previous Year Deploying Computer Security Incident ManagementThis slide represents the attacks faced by the organization which led to theft of confidential data and sensitive information of the organization. It represents the increase in ransomware and phishing attacks experienced by the enterprise within 5 years.Present the topic in a bit more detail with this Cyber Attacks Faced By The Company In Previous Year Deploying Computer Security Incident Management. Use it as a tool for discussion and navigation on Ransomware Attacks, Phishing Attacks, Awareness Among Employees. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
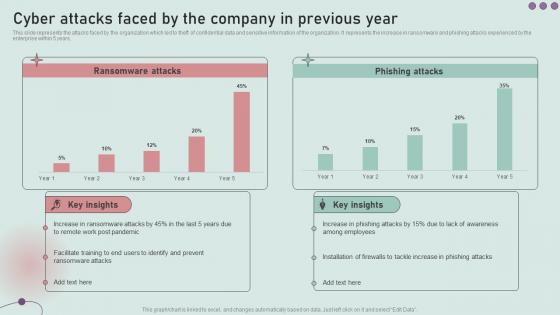 Cyber Attacks Faced By The Company In Previous Year Development And Implementation Of Security
Cyber Attacks Faced By The Company In Previous Year Development And Implementation Of SecurityThis slide represents the attacks faced by the organization which led to theft of confidential data and sensitive information of the organization. It represents the increase in ransomware and phishing attacks experienced by the enterprise within 5 years. Present the topic in a bit more detail with this Cyber Attacks Faced By The Company In Previous Year Development And Implementation Of Security. Use it as a tool for discussion and navigation on Ransomware Attacks, Phishing Attacks. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
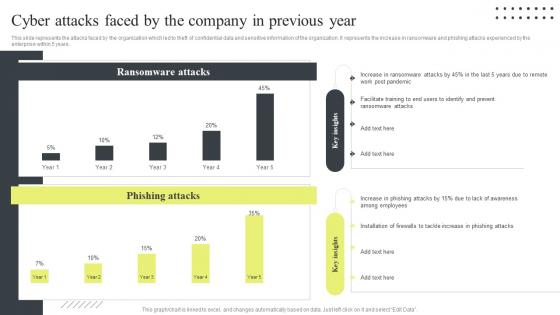 Cyber Security Attacks Response Plan Cyber Attacks Faced By The Company In Previous Year
Cyber Security Attacks Response Plan Cyber Attacks Faced By The Company In Previous YearThis slide represents the attacks faced by the organization which led to theft of confidential data and sensitive information of the organization. It represents the increase in ransomware and phishing attacks experienced by the enterprise within 5 years. Deliver an outstanding presentation on the topic using this Cyber Security Attacks Response Plan Cyber Attacks Faced By The Company In Previous Year. Dispense information and present a thorough explanation of Ransomware Attacks, Phishing Attacks, Post Pandemic using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
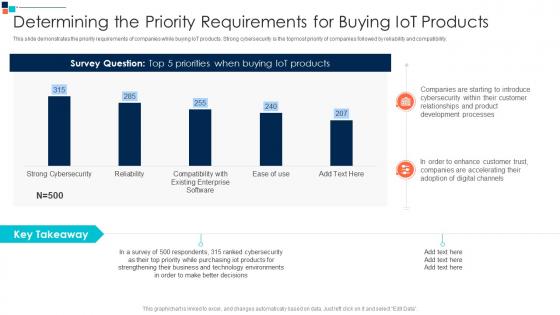 Determining The Priority A Risk Based Approach To Cyber Security
Determining The Priority A Risk Based Approach To Cyber SecurityThis slide demonstrates the priority requirements of companies while buying IoT products. Strong cybersecurity is the topmost priority of companies followed by reliability and compatibility.Deliver an outstanding presentation on the topic using this Determining The Priority A Risk Based Approach To Cyber Security Dispense information and present a thorough explanation of Companies Are Starting, Relationships And Product, Development Processes using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
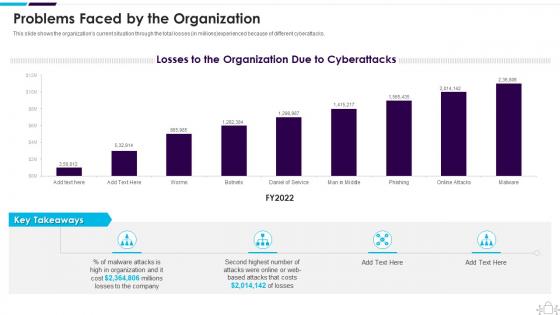 Information Technology Security Problems Faced By The Organization
Information Technology Security Problems Faced By The OrganizationThis slide shows the organizations current situation through the total losses in millions experienced because of different cyberattacks. Present the topic in a bit more detail with this Information Technology Security Problems Faced By The Organization. Use it as a tool for discussion and navigation on Problems Faced By The Organization. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Information Security Program Determining The Priority Requirements For Buying Iot Products
Information Security Program Determining The Priority Requirements For Buying Iot ProductsThis slide demonstrates the priority requirements of companies while buying IoT products. Strong cybersecurity is the topmost priority of companies followed by reliability and compatibility. Present the topic in a bit more detail with this Information Security Program Determining The Priority Requirements For Buying Iot Products. Use it as a tool for discussion and navigation on Requirements, Products, Determining. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
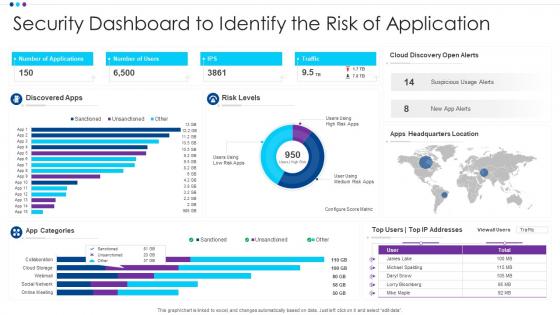 Security Dashboard To Identify The Risk Of Application
Security Dashboard To Identify The Risk Of ApplicationIntroducing our Security Dashboard To Identify The Risk Of Application set of slides. The topics discussed in these slides are App Categories, Discovered Apps, Risk Levels. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
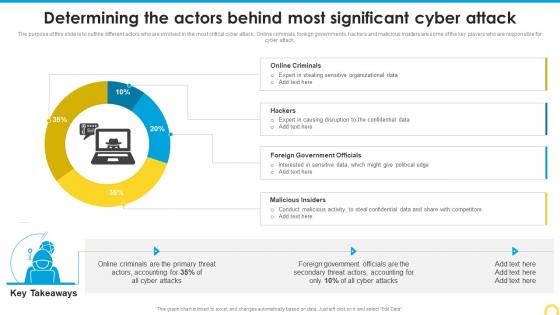 Determining The Actors Behind Building A Security Awareness Program
Determining The Actors Behind Building A Security Awareness ProgramThe purpose of this slide is to outline different actors who are involved in the most critical cyber attack. Online criminals, foreign governments, hackers and malicious insiders are some of the key players who are responsible for cyber attack. Deliver an outstanding presentation on the topic using this Determining The Actors Behind Building A Security Awareness Program. Dispense information and present a thorough explanation of Foreign Government, Malicious Insiders, Significant Cyber Attack using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
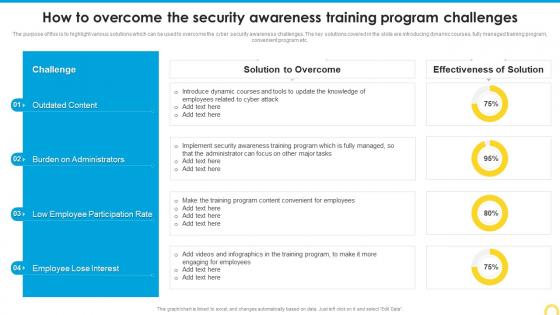 How To Overcome The Security Building A Security Awareness Program
How To Overcome The Security Building A Security Awareness ProgramThe purpose of this is to highlight various solutions which can be used to overcome the cyber security awareness challenges. The key solutions covered in the slide are introducing dynamic courses, fully managed training program, convenient program etc. Deliver an outstanding presentation on the topic using this How To Overcome The Security Building A Security Awareness Program. Dispense information and present a thorough explanation of Outdated Content, Participation Rate, Burden Administrators using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
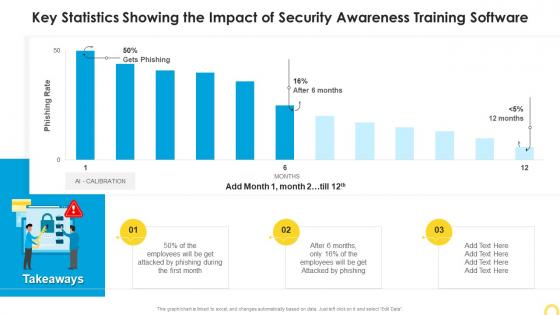 Key Statistics Showing The Impact Of Building A Security Awareness Program
Key Statistics Showing The Impact Of Building A Security Awareness ProgramPresent the topic in a bit more detail with this Key Statistics Showing The Impact Of Building A Security Awareness Program. Use it as a tool for discussion and navigation on Statistics Showing, Security Awareness, Training Software. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
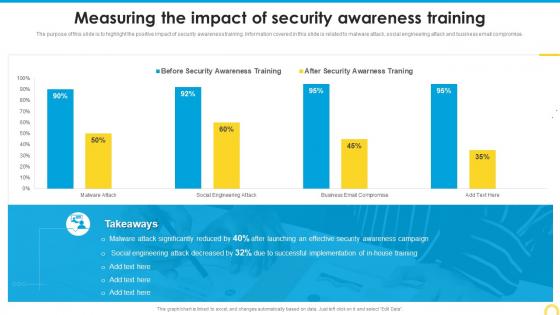 Measuring The Impact Of Security Building A Security Awareness Program
Measuring The Impact Of Security Building A Security Awareness ProgramThe purpose of this slide is to highlight the positive impact of security awareness training. Information covered in this slide is related to malware attack, social engineering attack and business email compromise. Deliver an outstanding presentation on the topic using this Measuring The Impact Of Security Building A Security Awareness Program. Dispense information and present a thorough explanation of Security Awareness, Training, Measuring Impact using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
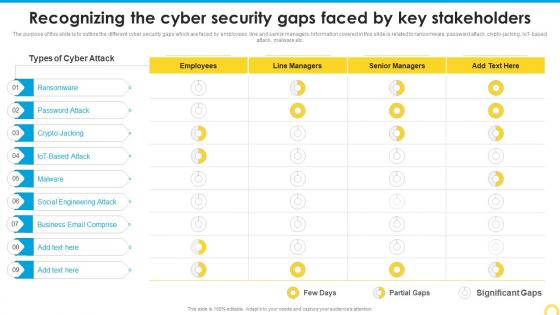 Recognizing The Cyber Security Building A Security Awareness Program
Recognizing The Cyber Security Building A Security Awareness ProgramThe purpose of this slide is to outline the different cyber security gaps which are faced by employees, line and senior managers. Information covered in this slide is related to ransomware, password attack, crypto-jacking, IoT based attack, malware etc. Present the topic in a bit more detail with this Recognizing The Cyber Security Building A Security Awareness Program. Use it as a tool for discussion and navigation on Ransomware, Social Engineering Attack, Business Email Comprise. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
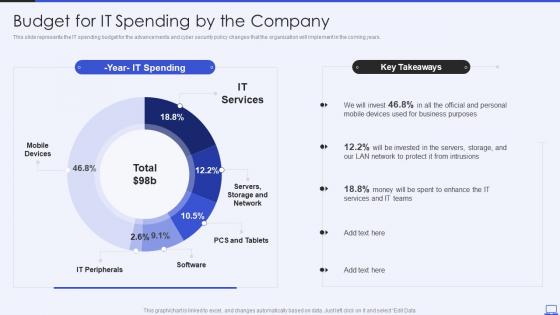 Security Hacker Budget For IT Spending By The Company Ppt Powerpoint Presentation Slides
Security Hacker Budget For IT Spending By The Company Ppt Powerpoint Presentation SlidesThis slide represents the IT spending budget for the advancements and cyber security policy changes that the organization will implement in the coming years. Present the topic in a bit more detail with this Security Hacker Budget For IT Spending By The Company Ppt Powerpoint Presentation Slides. Use it as a tool for discussion and navigation on IT Services, IT Peripherals, Mobile Devices. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
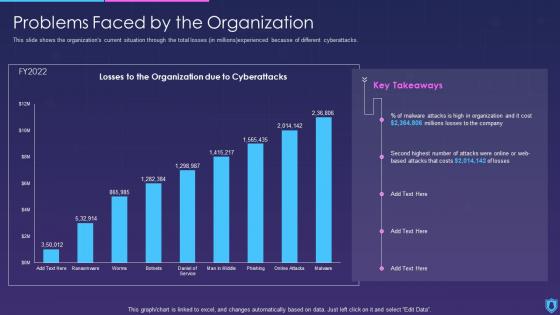 Information Security Problems Faced By The Organization
Information Security Problems Faced By The OrganizationThis slide shows the organizations current situation through the total losses in millions experienced because of different cyberattacks. Deliver an outstanding presentation on the topic using this Information Security Problems Faced By The Organization. Dispense information and present a thorough explanation of Problems Faced By The Organization using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
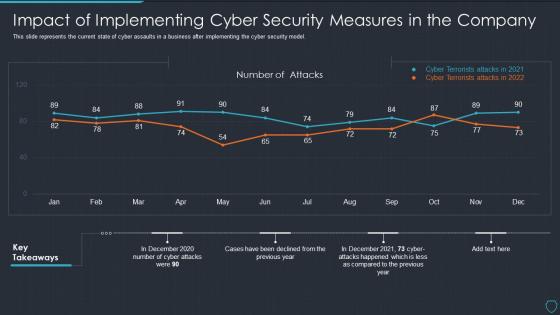 Cyberterrorism it impact of implementing cyber security measures in the company
Cyberterrorism it impact of implementing cyber security measures in the companyThis slide represents the current state of cyber assaults in a business after implementing the cyber security model. Present the topic in a bit more detail with this Cyberterrorism IT Impact Of Implementing Cyber Security Measures In The Company. Use it as a tool for discussion and navigation on Number Attacks, Cyber Terrorists Attacks 2021, Cyber Terrorists Attacks 2022. This template is free to edit as deemed fit for your organization. Therefore download it now.


