Powerpoint Templates and Google slides for Threat Of Entrants
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
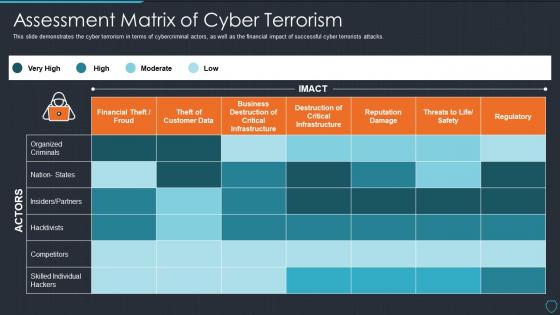 Cyberterrorism it assessment matrix of cyber terrorism ppt slides picture
Cyberterrorism it assessment matrix of cyber terrorism ppt slides pictureThis slide demonstrate cyber terrorism in terms of cybercriminal actors, as well as the financial impact of successful cyber terrorists attacks. Present the topic in a bit more detail with this Cyberterrorism IT Assessment Matrix Of Cyber Terrorism Ppt Slides Picture. Use it as a tool for discussion and navigation on Organized Criminals, Financial Theft Froud, Business Destruction. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyberterrorism it peroration of cyber terrorism ppt slides layout
Cyberterrorism it peroration of cyber terrorism ppt slides layoutThis slide explains the conclusion or peroration of cyber terrorism and how it is different from information warfare as it targets civilians rather than operations. Increase audience engagement and knowledge by dispensing information using Cyberterrorism IT Peroration Of Cyber Terrorism Ppt Slides Layout. This template helps you present information on six stages. You can also present information on Cyber Terrorism, Information Warfare, Except IT Targets, Cyber Terrorism using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
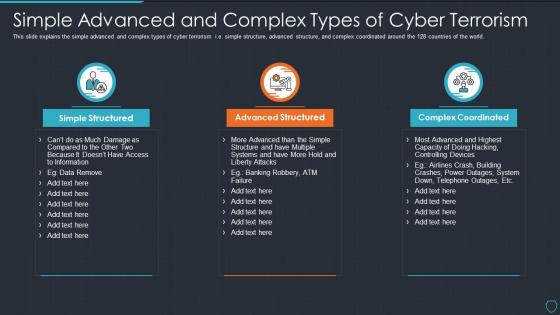 Cyberterrorism it simple advanced and complex types of cyber terrorism
Cyberterrorism it simple advanced and complex types of cyber terrorismThis slide explains the simple advanced and complex types of cyber terrorism i.e. simple structure, advanced structure, and complex coordinated around the 128 countries of the world. Increase audience engagement and knowledge by dispensing information using Cyberterrorism IT Simple Advanced And Complex Types Of Cyber Terrorism. This template helps you present information on three stages. You can also present information on Simple Structured, Advanced Structured, Complex Coordinated using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
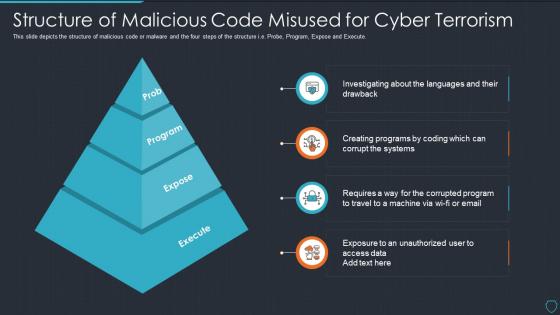 Cyberterrorism it structure of malicious code misused for cyber terrorism
Cyberterrorism it structure of malicious code misused for cyber terrorismThis slide depicts the structure of malicious code or malware and the four steps of the structure i.e. Probe, Program, Expose and Execute. Increase audience engagement and knowledge by dispensing information using Cyberterrorism IT Structure Of Malicious Code Misused For Cyber Terrorism. This template helps you present information on four stages. You can also present information on Prob, Program, Expose, Execute using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyberterrorism it table of contents for cyber terrorism ppt slides sample
Cyberterrorism it table of contents for cyber terrorism ppt slides samplePresent the topic in a bit more detail with this Cyberterrorism IT Table Of Contents For Cyber Terrorism Ppt Slides Sample. Use it as a tool for discussion and navigation on Assessment Matrix, Cyber Terrorism, Timeline, Dashboard, Threat Tracking. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
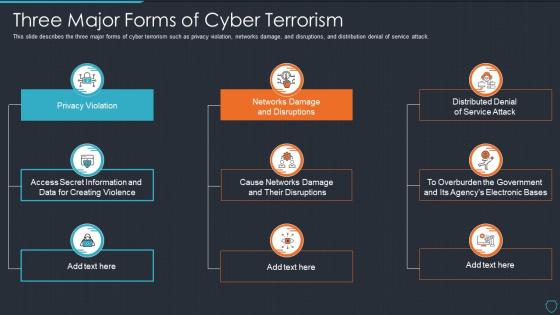 Cyberterrorism it three major forms of cyber terrorism ppt slides tips
Cyberterrorism it three major forms of cyber terrorism ppt slides tipsThis slide describes the three major forms of cyber terrorism such as privacy violation, networks damage, and disruptions, and distribution denial of service attack. Introducing Cyberterrorism IT Three Major Forms Of Cyber Terrorism Ppt Slides Tips to increase your presentation threshold. Encompassed with nine stages, this template is a great option to educate and entice your audience. Dispence information on Privacy Violation, Networks Damage And Disruptions, Distributed Denial Service Attack, Cause Networks Damage And Their Disruptions, using this template. Grab it now to reap its full benefits.
-
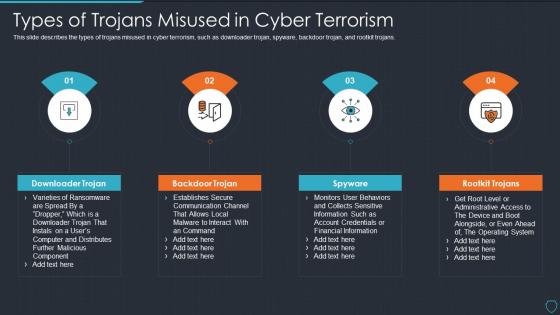 Cyberterrorism it types of trojans misused in cyber terrorism ppt slides tips
Cyberterrorism it types of trojans misused in cyber terrorism ppt slides tipsThis slide describes the types of trojans misused in cyber terrorism, such as downloader trojan, spyware, backdoor trojan, and rootkit trojans. Introducing Cyberterrorism IT Types Of Trojans Misused In Cyber Terrorism Ppt Slides Tips to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Downloader Trojan, Backdoor Trojan, Spyware, Rootkit Trojans, using this template. Grab it now to reap its full benefits.
-
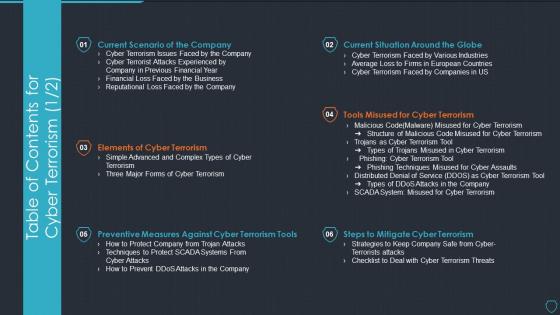 Table of contents for cyber terrorism cyberterrorism it ppt slides tools
Table of contents for cyber terrorism cyberterrorism it ppt slides toolsPresent the topic in a bit more detail with this Table Of Contents For Cyber Terrorism Cyberterrorism IT Ppt Slides Tools. Use it as a tool for discussion and navigation on Current Scenario Company, Elements Cyber Terrorism, Preventive Measures, Against Cyber Terrorism Tools, Steps To Mitigate Cyber Terrorism, Tools Misused Cyber Terrorism, Current Situation Around Globe. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Real time analysis of security alerts threat intelligence services
Real time analysis of security alerts threat intelligence servicesThis slide covers the threat intelligence services such as global intelligence, local intelligence, and other effective threat detection services. Increase audience engagement and knowledge by dispensing information using Real Time Analysis Of Security Alerts Threat Intelligence Services. This template helps you present information on three stages. You can also present information on Global Intelligence, Local Intelligence, Other Services using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
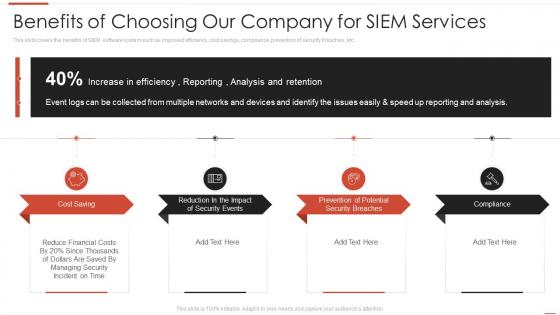 Automating threat identification benefits of choosing our company for siem services
Automating threat identification benefits of choosing our company for siem servicesThis slide covers the benefits of SIEM software system such as improved efficiency, cost savings, compliance, prevention of security breaches, etc. Introducing Automating Threat Identification Benefits Of Choosing Our Company For Siem Services to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Services, Potential, Compliance, using this template. Grab it now to reap its full benefits.
-
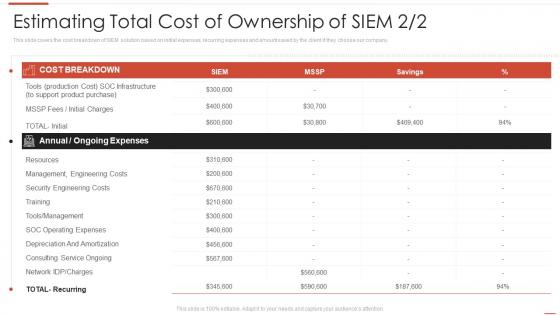 Automating threat identification estimating total cost of ownership of siem
Automating threat identification estimating total cost of ownership of siemThis slide covers the cost breakdown of SIEM solution based on initial expenses, recurring expenses and amount saved by the client if they choose our company. Present the topic in a bit more detail with this Automating Threat Identification Estimating Total Cost Of Ownership Of Siem. Use it as a tool for discussion and navigation on Estimating Total Cost Of Ownership Of SIEM. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Automating threat identification key features of siem software
Automating threat identification key features of siem softwareThis slide provides the details about our companys SIEM key features such as automated reports, log collection and classification, high scalability, security automation, etc. Introducing Automating Threat Identification Key Features Of Siem Softwa to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Comprehensive, Classification, Enrichment, using this template. Grab it now to reap its full benefits.
-
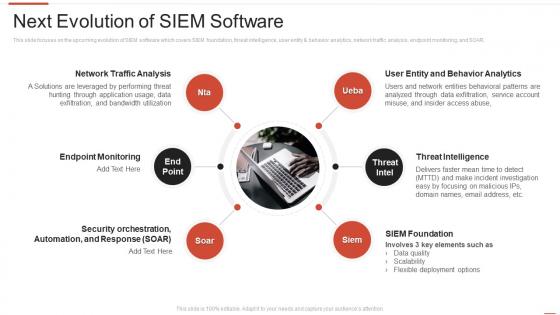 Automating threat identification next evolution of siem software
Automating threat identification next evolution of siem softwareThis slide focuses on the upcoming evolution of SIEM software which covers SIEM foundation, threat intelligence, user entity and behavior analytics, network traffic analysis, endpoint monitoring, and SOAR. Increase audience engagement and knowledge by dispensing information using Automating Threat Identification Next Evolution Of Siem Software. This template helps you present information on six stages. You can also present information on Threat Intelligence, Siem Foundation, Endpoint Monitoring using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Automating threat identification table of contents security information and event management
Automating threat identification table of contents security information and event managementIncrease audience engagement and knowledge by dispensing information using Automating Threat Identification Table Of Contents Security Information And Event Management. This template helps you present information on eleven stages. You can also present information on Company Overview, Management, Information using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
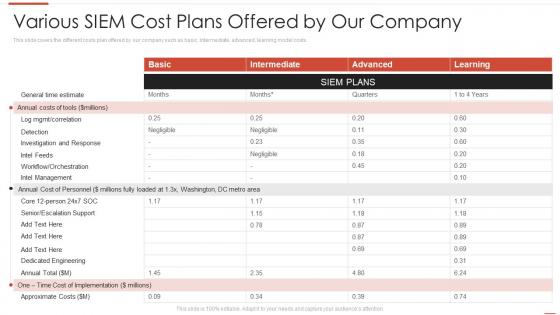 Automating threat identification various siem cost plans offered by our company
Automating threat identification various siem cost plans offered by our companyThis slide covers the different costs plan offered by our company such as basic, intermediate, advanced, learning model costs. Present the topic in a bit more detail with this Automating Threat Identification Various Siem Cost Plans Offered By Our Company. Use it as a tool for discussion and navigation on Various SIEM Cost Plans Offered By Our Company. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
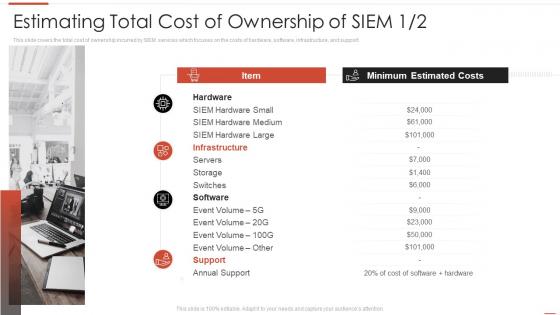 Estimating total cost of ownership of siem automating threat identification
Estimating total cost of ownership of siem automating threat identificationThis slide covers the total cost of ownership incurred by SIEM services which focuses on the costs of hardware, software, infrastructure, and support. Introducing Estimating Total Cost Of Ownership Of Siem Automating Threat Identification to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Estimating Total Cost Of Ownership Of SIEM, using this template. Grab it now to reap its full benefits.
-
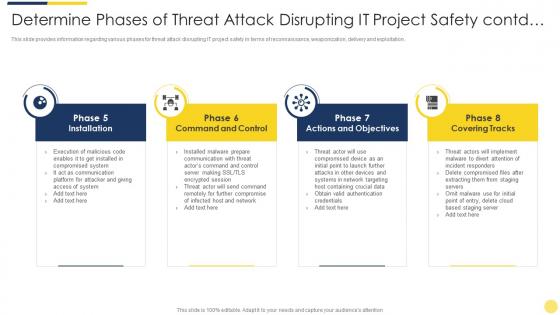 Determine phases of threat attack disrupting it project safety contd key initiatives for project safety it
Determine phases of threat attack disrupting it project safety contd key initiatives for project safety itThis slide provides information regarding various phases for threat attack disrupting IT project safety in terms of reconnaissance, weaponization, delivery and exploitation. Increase audience engagement and knowledge by dispensing information using Determine Phases Of Threat Attack Disrupting It Project Safety Contd Key Initiatives For Project Safety It. This template helps you present information on four stages. You can also present information on System, Communication, Network, Implement using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
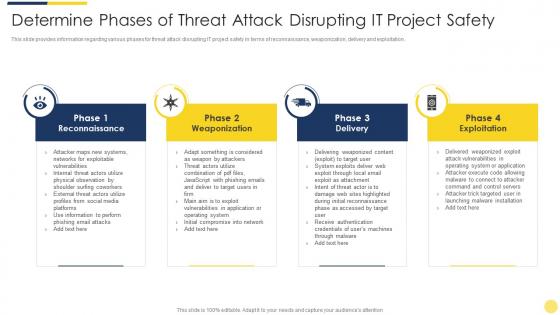 Determine phases of threat attack disrupting it project safety key initiatives for project safety it
Determine phases of threat attack disrupting it project safety key initiatives for project safety itThis slide provides information regarding various phases for threat attack disrupting IT project safety in terms of reconnaissance, weaponization, delivery and exploitation. Introducing Determine Phases Of Threat Attack Disrupting It Project Safety Key Initiatives For Project Safety It to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Networks, Systems, Email, Information, Target, using this template. Grab it now to reap its full benefits.
-
 Threat management for organization critical addressing internal and external sources of threat data gathering
Threat management for organization critical addressing internal and external sources of threat data gatheringThis slide provides details regarding internal and external sources of threat data gathering with threat intelligence category. Present the topic in a bit more detail with this Threat Management For Organization Critical Addressing Internal And External Sources Of Threat Data Gathering. Use it as a tool for discussion and navigation on Targeted Intelligence, Malware Intelligence, Reputation Intelligence. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Threat management for organization critical agenda of threat management for organization critical assets
Threat management for organization critical agenda of threat management for organization critical assetsIntroducing Threat Management For Organization Critical Agenda Of Threat Management For Organization Critical Assets to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Agenda, using this template. Grab it now to reap its full benefits.
-
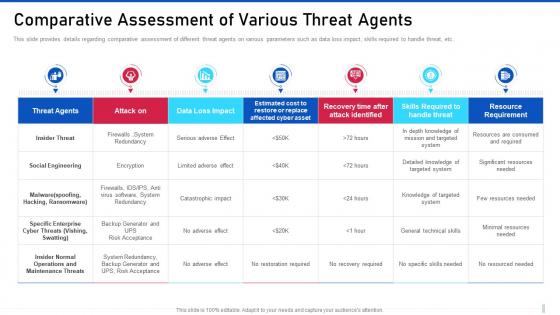 Threat management for organization critical comparative assessment of various threat agents
Threat management for organization critical comparative assessment of various threat agentsThis slide provides details regarding comparative assessment of different threat agents on various parameters such as data loss impact, skills required to handle threat, etc. Deliver an outstanding presentation on the topic using this Threat Management For Organization Critical Comparative Assessment Of Various Threat Agents. Dispense information and present a thorough explanation of Social Engineering, Specific Enterprise, Operations And Maintenance using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Threat management for organization critical different kinds of insider digital threats
Threat management for organization critical different kinds of insider digital threatsThis slide provides details regarding various kinds of insider digital threats such as malicious insider, negligent insider, third party insider, etc. Introducing Threat Management For Organization Critical Different Kinds Of Insider Digital Threats to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Malicious Insider, Negligent Or Careless Insider, Compromised Third, using this template. Grab it now to reap its full benefits.
-
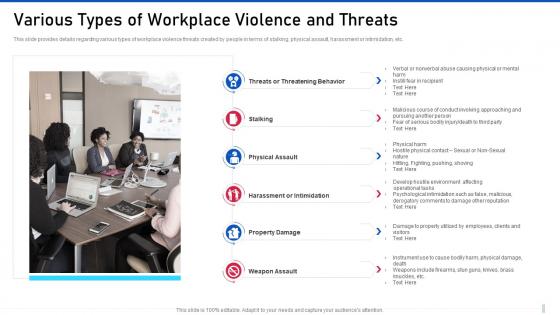 Threat management for organization critical various types of workplace violence and threats
Threat management for organization critical various types of workplace violence and threatsThis slide provides details regarding various types of workplace violence threats created by people in terms of stalking, physical assault, harassment or intimidation, etc. Increase audience engagement and knowledge by dispensing information using Threat Management For Organization Critical Various Types Of Workplace Violence And Threats. This template helps you present information on six stages. You can also present information on Threatening Behavior, Physical Assault, Harassment Or Intimidation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyber security risk management different kinds of insider digital threats
Cyber security risk management different kinds of insider digital threatsThis slide provides details regarding various kinds of insider digital threats such as malicious insider, negligent insider, third party insider, etc. Introducing Cyber Security Risk Management Different Kinds Of Insider Digital Threats to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Malicious Insider, Negligent Or Careless Insider, Third Party Insider, using this template. Grab it now to reap its full benefits.
-
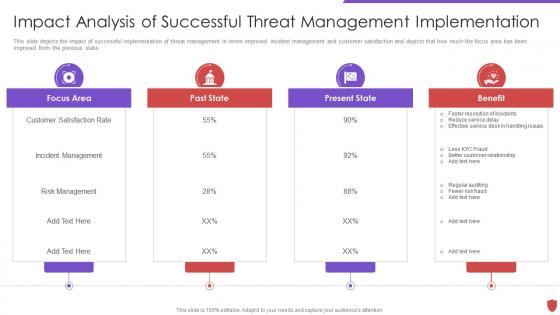 Cyber security risk management impact analysis of successful threat management
Cyber security risk management impact analysis of successful threat managementThis slide depicts the impact of successful implementation of threat management in terms improved incident management and customer satisfaction and depicts that how much the focus area has been improved from the previous state. Increase audience engagement and knowledge by dispensing information using Cyber Security Risk Management Impact Analysis Of Successful Threat Management. This template helps you present information on four stages. You can also present information on Focus Area, Past State, Present State, Benefit, Customer Satisfaction Rate using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
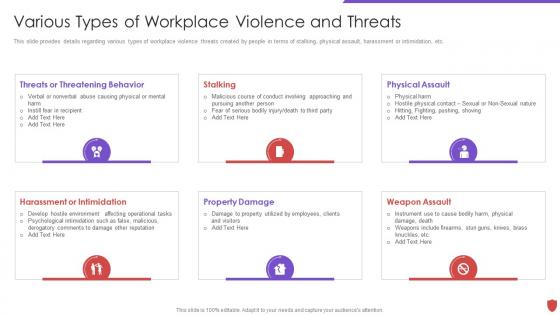 Cyber security risk management various types of workplace violence and threats
Cyber security risk management various types of workplace violence and threatsThis slide provides details regarding various types of workplace violence threats created by people in terms of stalking, physical assault, harassment or intimidation, etc. Introducing Cyber Security Risk Management Various Types Of Workplace Violence And Threats to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Threats Or Threatening Behavior, Physical Assault, Property Damage, using this template. Grab it now to reap its full benefits.
-
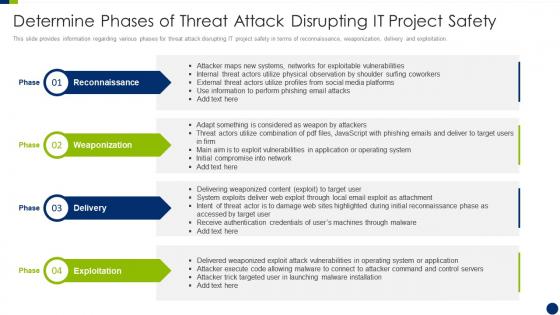 Determine phases of threat attack disrupting it project safety enhancing overall project security it
Determine phases of threat attack disrupting it project safety enhancing overall project security itThis slide provides information regarding various phases for threat attack disrupting IT project safety in terms of reconnaissance, weaponization, delivery and exploitation. Introducing Determine Phases Of Threat Attack Disrupting It Project Safety Enhancing Overall Project Security It to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Reconnaissance, Weaponization, Exploitation, using this template. Grab it now to reap its full benefits.
-
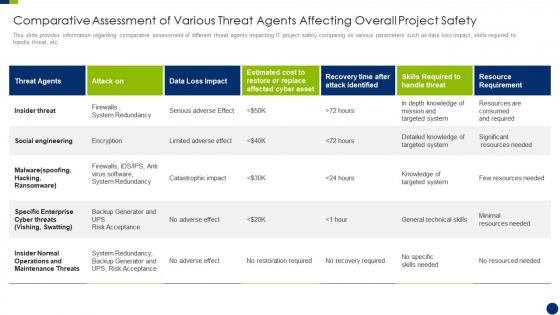 Enhancing overall project security it comparative assessment of various threat agents affecting
Enhancing overall project security it comparative assessment of various threat agents affectingThis slide provides information regarding comparative assessment of different threat agents impacting IT project safety comparing on various parameters such as data loss impact, skills required to handle threat, etc. Present the topic in a bit more detail with this Enhancing Overall Project Security It Comparative Assessment Of Various Threat Agents Affecting. Use it as a tool for discussion and navigation on Assessment, Operations, Maintenance. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
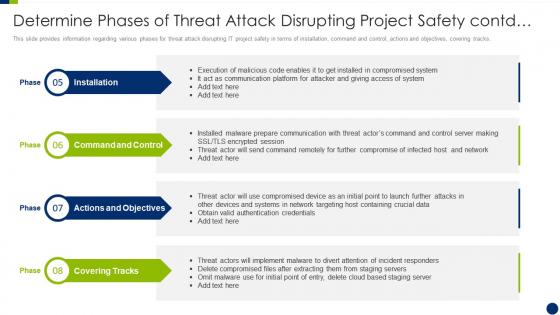 Enhancing overall project security it determine phases of threat attack disrupting project safety contd
Enhancing overall project security it determine phases of threat attack disrupting project safety contdThis slide provides information regarding various phases for threat attack disrupting IT project safety in terms of installation, command and control, actions and objectives, covering tracks. Introducing Enhancing Overall Project Security It Determine Phases Of Threat Attack Disrupting Project Safety Contd to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Command And Control, Actions And Objectives, Covering Tracks, using this template. Grab it now to reap its full benefits.
-
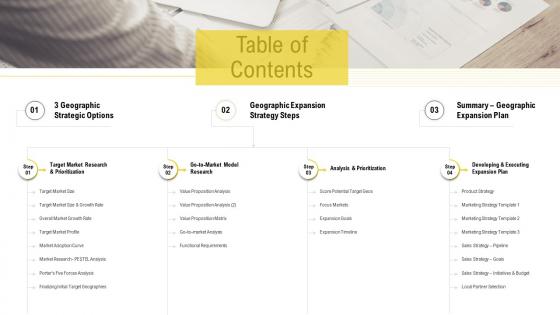 Opportunities and threats entering new markets new geos table of contents
Opportunities and threats entering new markets new geos table of contentsIntroducing Opportunities And Threats Entering New Markets New Geos Table Of Contents to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Geographic, Strategic, Strategy Steps, using this template. Grab it now to reap its full benefits.
-
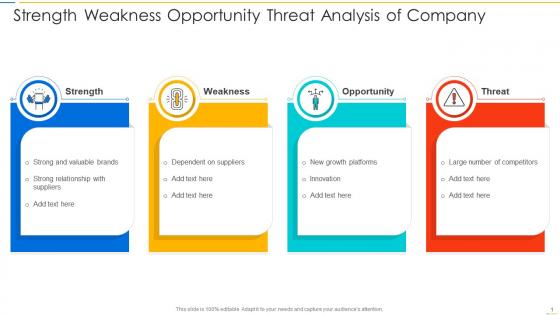 Strength weakness opportunity threat analysis of company
Strength weakness opportunity threat analysis of companyIntroducing our premium set of slides with Strength Weakness Opportunity Threat Analysis Of Company. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Strength, Weakness, Threats, Opportunity. So download instantly and tailor it with your information.
-
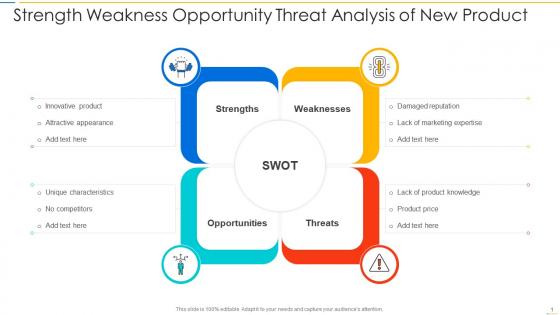 Strength weakness opportunity threat analysis of new product
Strength weakness opportunity threat analysis of new productPresenting our set of slides with Strength Weakness Opportunity Threat Analysis Of New Product. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Strength, Weakness, Threats, Opportunity.
-
 Strength weakness opportunity threat analysis of project management
Strength weakness opportunity threat analysis of project managementIntroducing our premium set of slides with Strength Weakness Opportunity Threat Analysis Of Project Management. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Strength, Weakness, Threats, Opportunity. So download instantly and tailor it with your information.
-
 Strength weakness opportunity threat analysis of social media strategy
Strength weakness opportunity threat analysis of social media strategyPresenting our set of slides with Strength Weakness Opportunity Threat Analysis Of Project Management. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Strength, Weakness, Threats, Opportunity.
-
 Strength weakness opportunity threat analysis of strategic management
Strength weakness opportunity threat analysis of strategic managementIntroducing our premium set of slides with Strength Weakness Opportunity Threat Analysis Of Strategic Management. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Strength, Weakness, Threats, Opportunity. So download instantly and tailor it with your information.
-
 Types of latest threats in electronic information security
Types of latest threats in electronic information securityThis slide depicts the categories of recent threats that recently emerged in the United States, United Kingdom, and Australia in previous years. Increase audience engagement and knowledge by dispensing information using Types Of Latest Threats In Electronic Information Security. This template helps you present information on eight stages. You can also present information on Dridex Malware, Romance Scams, Emotet Malware, Business using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Types of threats in electronic information security
Types of threats in electronic information securityThis slide depicts the main types of threats in cyber security, such as cybercrime, cyber terrorism, and cyberattacks to an organization and the purpose of each category threat. Introducing Types Of Threats In Electronic Information Security to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Cyber Crime, Cyber Terrorism, using this template. Grab it now to reap its full benefits.
-
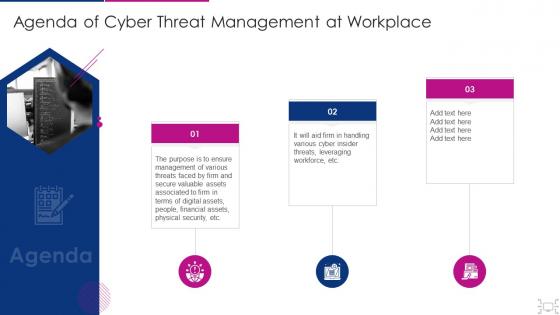 Agenda of cyber threat management at workplace
Agenda of cyber threat management at workplaceIntroducing Agenda Of Cyber Threat Management At Workplace to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Management, Various Threats, Assets Associated, Digital Assets, People, Financial Assets, Physical Security, using this template. Grab it now to reap its full benefits.
-
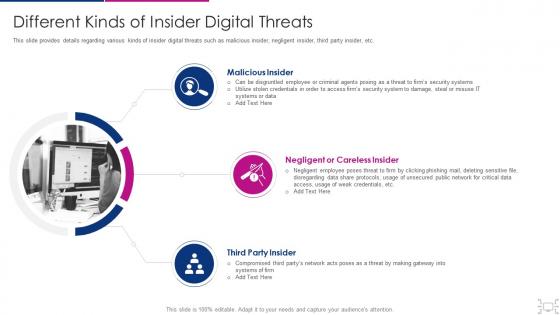 Cyber threat management workplace different kinds of insider digital threats
Cyber threat management workplace different kinds of insider digital threatsThis slide provides details regarding various kinds of insider digital threats such as malicious insider, negligent insider, third party insider, etc. Increase audience engagement and knowledge by dispensing information using Cyber Threat Management Workplace Different Kinds Of Insider Digital Threats. This template helps you present information on three stages. You can also present information on Malicious Insider, Negligent Or Careless Insider, Third Party Insider using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
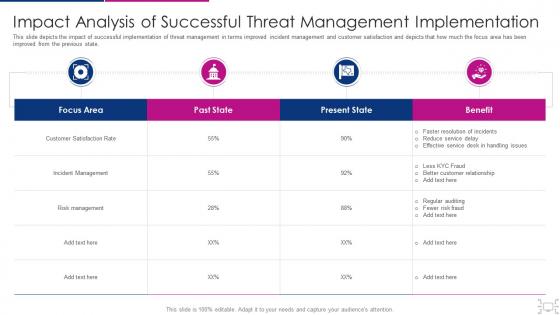 Cyber threat management workplace impact analysis of successful
Cyber threat management workplace impact analysis of successfulThis slide depicts the impact of successful implementation of threat management in terms improved incident management and customer satisfaction and depicts that how much the focus area has been improved from the previous state. Present the topic in a bit more detail with this Cyber Threat Management Workplace Impact Analysis Of Successful. Use it as a tool for discussion and navigation on Focus Area, Past State, Present State, Benefit, Customer Satisfaction Rate. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber threat management workplace various types of workplace violence
Cyber threat management workplace various types of workplace violenceThis slide provides details regarding various types of workplace violence threats created by people in terms of stalking, physical assault, harassment or intimidation, etc. Introducing Cyber Threat Management Workplace Various Types Of Workplace Violence to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Threats Or Threatening Behavior, Physical Assault, Property Damage, Stalking Harassment Or Intimidation, Weapon Assault, using this template. Grab it now to reap its full benefits.
-
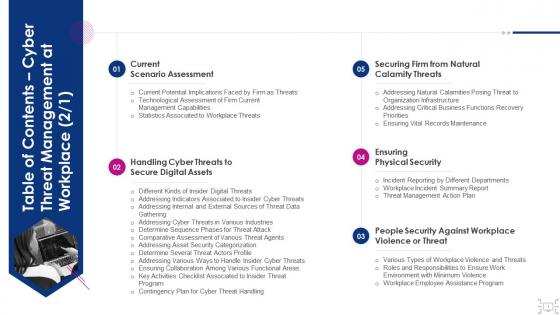 Table of contents cyber threat management workplace
Table of contents cyber threat management workplaceIncrease audience engagement and knowledge by dispensing information using Table Of Contents Cyber Threat Management Workplace. This template helps you present information on five stages. You can also present information on Current Scenario Assessment, Handling Cyber Threats, Secure Digital Assets, Securing Firm, Natural Calamity Threats, Ensuring Physical Security, People Security Against Workplace Violence Or Threat using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
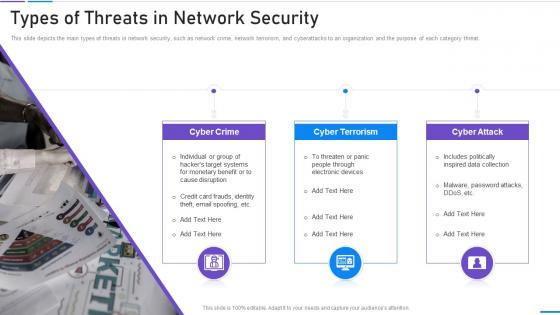 Network Security Types Of Threats In Network Security
Network Security Types Of Threats In Network SecurityThis slide depicts the main types of threats in network security, such as network crime, network terrorism, and cyberattacks to an organization and the purpose of each category threat. Increase audience engagement and knowledge by dispensing information using Network Security Types Of Threats In Network Security. This template helps you present information on three stages. You can also present information on Cyber Crime, Cyber Terrorism, Cyber Attack using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
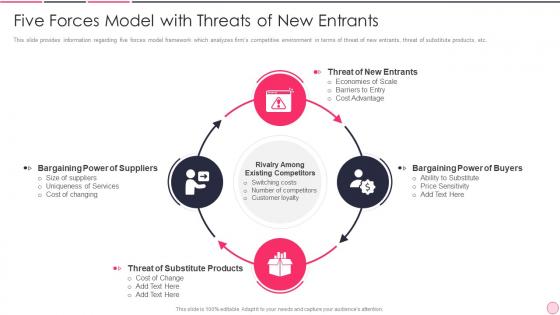 Business Strategy Best Practice Model With Threats Of New Entrants
Business Strategy Best Practice Model With Threats Of New EntrantsThis slide provides information regarding five forces model framework which analyzes firms competitive environment in terms of threat of new entrants, threat of substitute products, etc. Increase audience engagement and knowledge by dispensing information using Business Strategy Best Practice Model With Threats Of New Entrants This template helps you present information on four stages. You can also present information on Determine Organizational, Process Oriented Implementation, Collaboration Among using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Analysing The Impact Of Security Threats Information System Security And Risk Administration Plan
Analysing The Impact Of Security Threats Information System Security And Risk Administration PlanIncrease audience engagement and knowledge by dispensing information using Analysing The Impact Of Security Threats Information System Security And Risk Administration Plan. This template helps you present information on one stages. You can also present information on Security Threats, Malware, Phishing using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
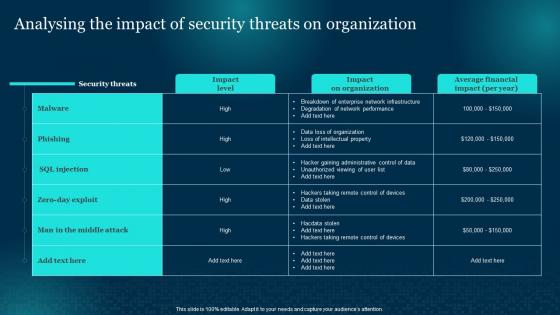 Cybersecurity Risk Analysis And Management Plan Analysing The Impact Of Security Threats
Cybersecurity Risk Analysis And Management Plan Analysing The Impact Of Security ThreatsPresent the topic in a bit more detail with this Cybersecurity Risk Analysis And Management Plan Analysing The Impact Of Security Threats. Use it as a tool for discussion and navigation on Analysing, Organization, Security Threats. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Analysing The Impact Of Security Threats On Organization Formulating Cybersecurity Plan
Analysing The Impact Of Security Threats On Organization Formulating Cybersecurity PlanPresent the topic in a bit more detail with this Analysing The Impact Of Security Threats On Organization Formulating Cybersecurity Plan. Use it as a tool for discussion and navigation on Organization, Average Financial, Analysing. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
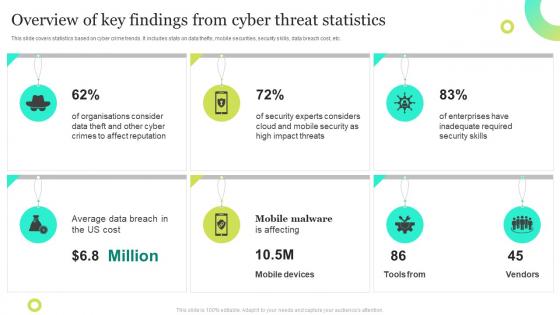 Overview Of Key Findings From Cyber Threat Statistics
Overview Of Key Findings From Cyber Threat StatisticsThis slide covers statistics based on cyber crime trends. It includes stats on data thefts, mobile securities, security skills, data breach cost, etc. Presenting our set of slides with Overview Of Key Findings From Cyber Threat Statistics. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cyber Crimes, Mobile Security, Mobile Devices.
-
 Cyber Security Checklist To Mitigate Threats Of Attack
Cyber Security Checklist To Mitigate Threats Of AttackThe given slide provides the key activities to be done to alleviate the effects of cyber threats. It includes managing social media profiles, backing up the data, crosschecking privacy and security settings etc. Introducing our premium set of slides with Cyber Security Checklist To Mitigate Threats Of Attack. Ellicudate the seven stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cyber Security Checklist, Mitigate Threats Attack. So download instantly and tailor it with your information.
-
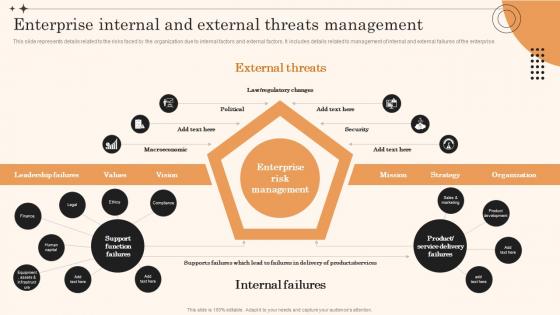 Enterprise Internal And External Threats Management Overview Of Enterprise Risk Management
Enterprise Internal And External Threats Management Overview Of Enterprise Risk ManagementThis slide represents details related to the risks faced by the organization due to internal factors and external factors. It includes details related to management of internal and external failures of the enterprise. Present the topic in a bit more detail with this Enterprise Internal And External Threats Management Overview Of Enterprise Risk Management. Use it as a tool for discussion and navigation on Management, Enterprise, Organization. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Five Step Process Of Cyber Threat Hunting
Five Step Process Of Cyber Threat HuntingThis slide shows steps for effective and successful cyber security systems to prevent from threats.it contains steps hypothesis, process data, trigger, investigation and resolution. Presenting our set of slides with name Five Step Process Of Cyber Threat Hunting. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Hypothesis, Trigger, Resolution, Investigation.
-
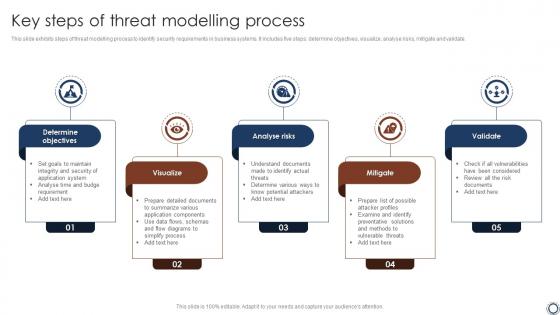 Key Steps Of Threat Modelling Process
Key Steps Of Threat Modelling ProcessThis slide exhibits steps of threat modelling process to identify security requirements in business systems. It includes five steps determine objectives, visualize, analyse risks, mitigate and validate. Presenting our set of slides with name Key Steps Of Threat Modelling Process. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Visualize, Validate, Analyse Risks, Mitigate.
-
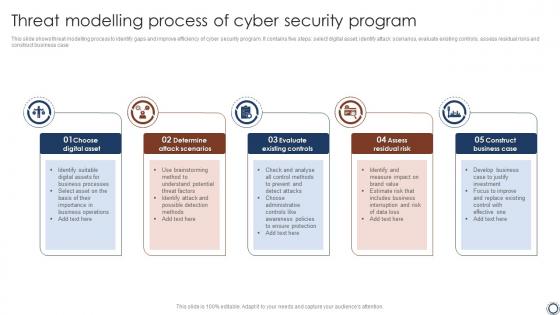 Threat Modelling Process Of Cyber Security Program
Threat Modelling Process Of Cyber Security ProgramThis slide shows threat modelling process to identify gaps and improve efficiency of cyber security program. It contains five steps select digital asset, identify attack scenarios, evaluate existing controls, assess residual risks and construct business case. Presenting our set of slides with name Threat Modelling Process Of Cyber Security Program. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Threat Modelling, Cyber Security, Assess Residual Risk .
-
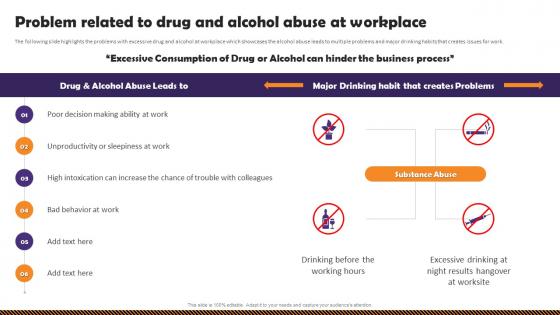 Health And Safety Of Employees Problem Related To Drug And Alcohol Abuse At Workplace
Health And Safety Of Employees Problem Related To Drug And Alcohol Abuse At WorkplaceThe following slide highlights the problems with excessive drug and alcohol at workplace which showcases the alcohol abuse leads to multiple problems and major drinking habits that creates issues for work. Deliver an outstanding presentation on the topic using this Health And Safety Of Employees Problem Related To Drug And Alcohol Abuse At Workplace. Dispense information and present a thorough explanation of Hangover At Worksite, Drug And Alcohol, Abuse At Workplace using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Health And Safety Of Employees Safety Guidelines To Detect And Prevent Alcohol Abuse
Health And Safety Of Employees Safety Guidelines To Detect And Prevent Alcohol AbuseThis slide highlights the preventive and detective measures for alcohol abuse which showcase multiple ways to deal the situation with training program, and experts assistance. Introducing Health And Safety Of Employees Safety Guidelines To Detect And Prevent Alcohol Abuse to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Safety Guidelines, Prevent Alcohol Abuse, Plan Training Program, using this template. Grab it now to reap its full benefits.
-
 General Mills Threats Industry Report Of Commercially Prepared Food Part 1
General Mills Threats Industry Report Of Commercially Prepared Food Part 1Present the topic in a bit more detail with this General Mills Threats Industry Report Of Commercially Prepared Food Part 1. Use it as a tool for discussion and navigation on Competition, Increased Concerns For Health, Threats. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Kellogg Threats Industry Report Of Commercially Prepared Food Part 1
Kellogg Threats Industry Report Of Commercially Prepared Food Part 1Deliver an outstanding presentation on the topic using this Kellogg Threats Industry Report Of Commercially Prepared Food Part 1. Dispense information and present a thorough explanation of Consumer, Threats, Intense Competition using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
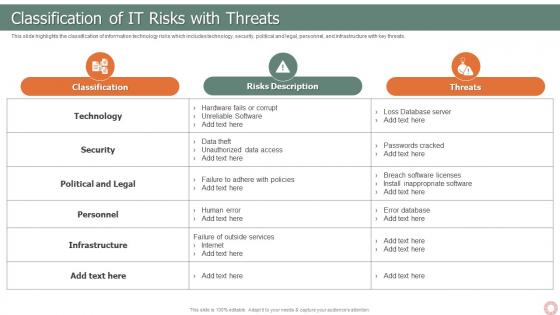 IT Risk Management Strategies Classification Of IT Risks With Threats
IT Risk Management Strategies Classification Of IT Risks With ThreatsThis slide highlights the classification of information technology risks which includes technology, security, political and legal, personnel, and infrastructure with key threats. Present the topic in a bit more detail with this IT Risk Management Strategies Classification Of IT Risks With Threats. Use it as a tool for discussion and navigation on Technology, Security, Political And Legal. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
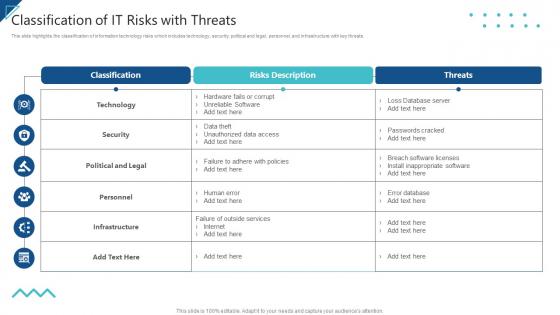 Enterprise Risk Management Classification Of IT Risks With Threats
Enterprise Risk Management Classification Of IT Risks With ThreatsThis slide highlights the classification of information technology risks which includes technology, security, political and legal, personnel, and infrastructure with key threats. Present the topic in a bit more detail with this Enterprise Risk Management Classification Of IT Risks With Threats. Use it as a tool for discussion and navigation on Technology, Security, Political And Legal. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Threat Actors Supporting Russia And Ukraine String Of Cyber Attacks Against Ukraine 2022
Threat Actors Supporting Russia And Ukraine String Of Cyber Attacks Against Ukraine 2022This slide shows the threat actors supporting russia and ukraine, such as hacker organization anonymous, cyber partisan hacking organization, and conti ransomware gang. Introducing Threat Actors Supporting Russia And Ukraine String Of Cyber Attacks Against Ukraine 2022 to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Security Community, Organization, Hacking Organization Attacked, using this template. Grab it now to reap its full benefits.



