Powerpoint Templates and Google slides for Vulnerability Information
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Information Security Vulnerabilities Threats In Powerpoint And Google Slides Cpb
Information Security Vulnerabilities Threats In Powerpoint And Google Slides CpbPresenting Information Security Vulnerabilities Threats In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase Eight stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Information Security Vulnerabilities Threats. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
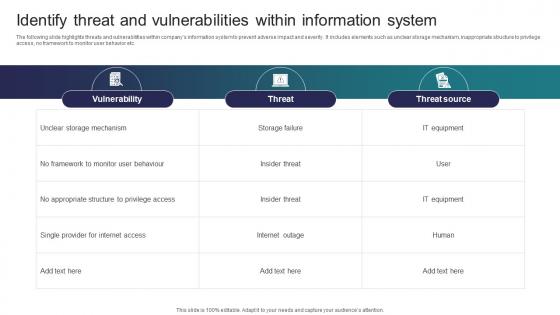 Identify Threat And Vulnerabilities Within Information System Implementing Strategies To Mitigate Cyber Security
Identify Threat And Vulnerabilities Within Information System Implementing Strategies To Mitigate Cyber SecurityThe following slide highlights threats and vulnerabilities within companys information system to prevent adverse impact and severity. It includes elements such as unclear storage mechanism, inappropriate structure to privilege access, no framework to monitor user behavior etc. Deliver an outstanding presentation on the topic using this Identify Threat And Vulnerabilities Within Information System Implementing Strategies To Mitigate Cyber Security Dispense information and present a thorough explanation of Vulnerability, Threat, Threat Source using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
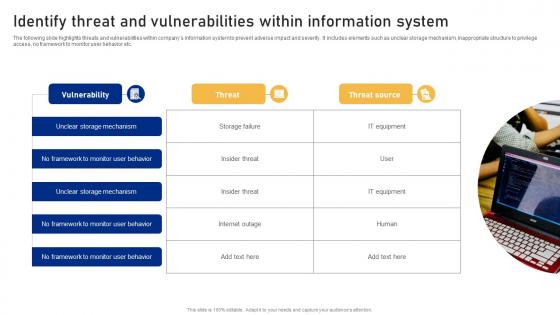 Identify Threat And Vulnerabilities Within Information System Cyber Risk Assessment
Identify Threat And Vulnerabilities Within Information System Cyber Risk AssessmentThe following slide highlights threats and vulnerabilities within companys information system to prevent adverse impact and severity. It includes elements such as unclear storage mechanism, inappropriate structure to privilege access, no framework to monitor user behavior etc. Introducing Identify Threat And Vulnerabilities Within Information System Cyber Risk Assessment to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on No Framework, Monitor User Behavior, Vulnerability using this template. Grab it now to reap its full benefits.
-
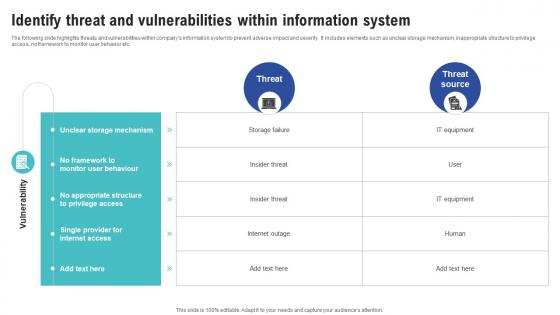 Identify Threat And Vulnerabilities Within Information System Creating Cyber Security Awareness
Identify Threat And Vulnerabilities Within Information System Creating Cyber Security AwarenessThe following slide highlights threats and vulnerabilities within companys information system to prevent adverse impact and severity. It includes elements such as unclear storage mechanism, inappropriate structure to privilege access, no framework to monitor user behavior etc. Deliver an outstanding presentation on the topic using this Identify Threat And Vulnerabilities Within Information System Creating Cyber Security Awareness Dispense information and present a thorough explanation of Unclear Storage Mechanism, Monitor User Behaviour, No Appropriate Structure using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
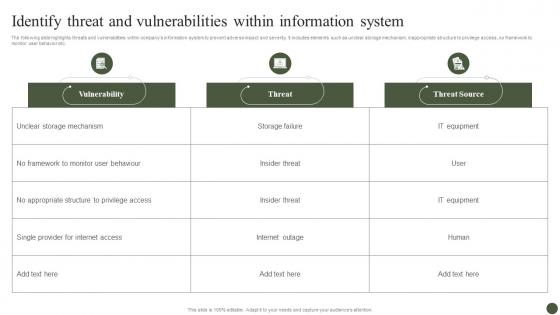 Identify Threat And Vulnerabilities Within Information Implementing Cyber Risk Management Process
Identify Threat And Vulnerabilities Within Information Implementing Cyber Risk Management ProcessThe following slide highlights threats and vulnerabilities within companys information system to prevent adverse impact and severity. It includes elements such as unclear storage mechanism, inappropriate structure to privilege access, no framework to monitor user behavior etc. Present the topic in a bit more detail with this Identify Threat And Vulnerabilities Within Information Implementing Cyber Risk Management Process. Use it as a tool for discussion and navigation on Vulnerability, Threat, Threat Source. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
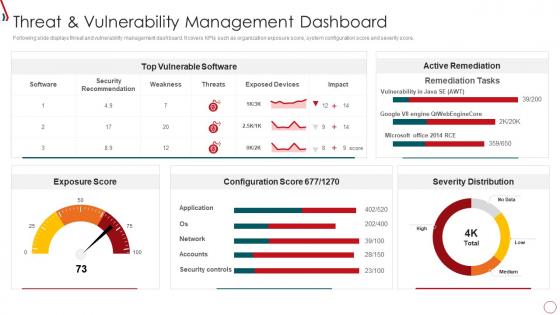 Risk Management Framework For Information Security Threat And Vulnerability
Risk Management Framework For Information Security Threat And VulnerabilityFollowing slide displays threat and vulnerability management dashboard. It covers KPIs such as organization exposure score, system configuration score and severity score. Present the topic in a bit more detail with this Risk Management Framework For Information Security Threat And Vulnerability. Use it as a tool for discussion and navigation on Exposure Score, Top Vulnerable Software, Severity Distribution, Active Remediation, Configuration Score. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
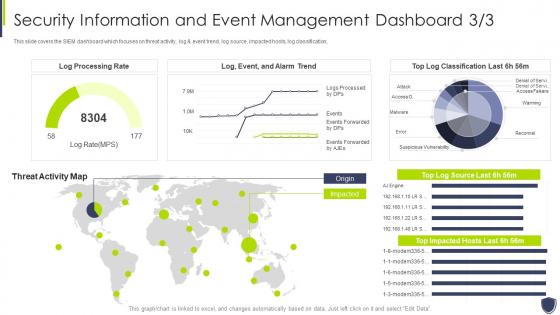 Improve it security vulnerability security information event management dashboard
Improve it security vulnerability security information event management dashboardThis slide covers the SIEM dashboard which focuses on threat activity, log and event trend, log source, impacted hosts, log classification, Deliver an outstanding presentation on the topic using this Improve It Security Vulnerability Security Information Event Management Dashboard. Dispense information and present a thorough explanation of Information, Management, Dashboard using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
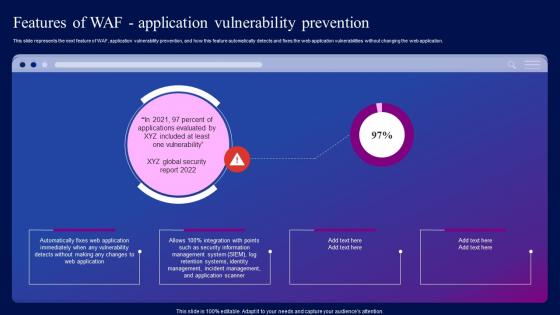 Features Of WAF Application Vulnerability Prevention Ppt Information
Features Of WAF Application Vulnerability Prevention Ppt InformationThis slide represents the next feature of WAF, application vulnerability prevention, and how this feature automatically detects and fixes the web application vulnerabilities without changing the web application. Deliver an outstanding presentation on the topic using this Features Of WAF Application Vulnerability Prevention Ppt Information. Dispense information and present a thorough explanation of Application, Vulnerability, Prevention using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Security information event management dashboard improve security vulnerability management
Security information event management dashboard improve security vulnerability managementThis slide covers the SIEM dashboard which focuses on server status, log sources, total logs, last log, collectors, log sources etc. Deliver an outstanding presentation on the topic using this Security Information Event Management Dashboard Improve Security Vulnerability Management. Dispense information and present a thorough explanation of Management, Dashboard, Information using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Information Security Program Cybersecurity Management Threat Vulnerability Asset Matrix
Information Security Program Cybersecurity Management Threat Vulnerability Asset MatrixMentioned slide displays the threat vulnerability asset matrix covering sections namely ranked threat agent and details about critical resources ranked from most critical to least. Deliver an outstanding presentation on the topic using this Information Security Program Cybersecurity Management Threat Vulnerability Asset Matrix. Dispense information and present a thorough explanation of Threat Vulnerability Asset Matrix using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
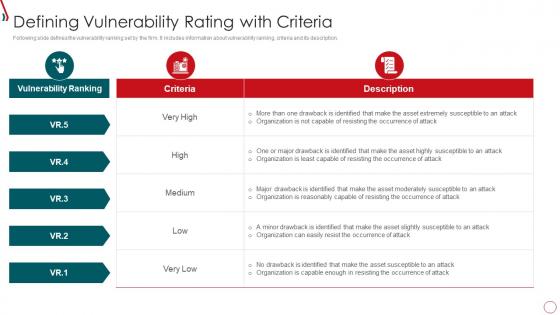 Risk Management Framework For Information Security Defining Vulnerability Rating With Criteria
Risk Management Framework For Information Security Defining Vulnerability Rating With CriteriaFollowing slide defines the vulnerability ranking set by the firm. It includes information about vulnerability ranking, criteria and its description. Present the topic in a bit more detail with this Risk Management Framework For Information Security Defining Vulnerability Rating With Criteria. Use it as a tool for discussion and navigation on Vulnerability Ranking, Organization, High, Low, Medium. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
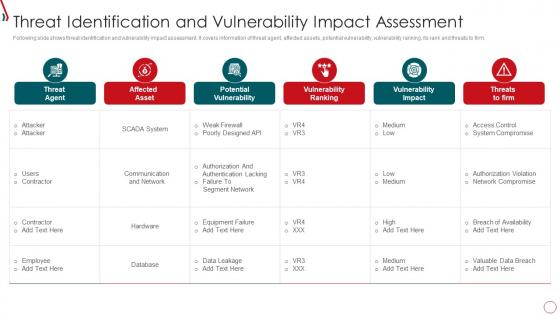 Risk Management Framework For Information Security Threat Identification And Vulnerability
Risk Management Framework For Information Security Threat Identification And VulnerabilityFollowing slide shows threat identification and vulnerability impact assessment. It covers information of threat agent, affected assets, potential vulnerability, vulnerability ranking, its rank and threats to firm. Deliver an outstanding presentation on the topic using this Risk Management Framework For Information Security Threat Identification And Vulnerability. Dispense information and present a thorough explanation of Communication And Network, Database, Failure To Segment Network using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cloud Security Threats Shared Vulnerabilities Cloud Information Security
Cloud Security Threats Shared Vulnerabilities Cloud Information SecurityThis slide describes how organizations and providers share vulnerabilities of a system, so each party must take precautions to protect data.Introducing Cloud Security Threats Shared Vulnerabilities Cloud Information Security to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Information Centers, Reduced Upfront, Diminished Opportunity using this template. Grab it now to reap its full benefits.
-
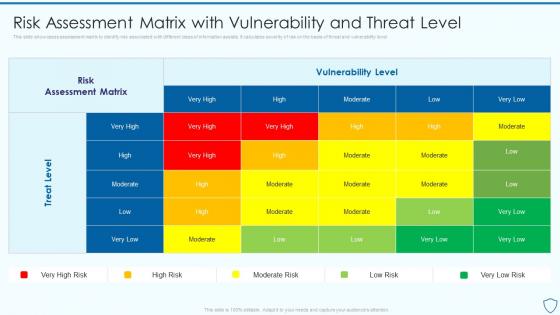 Risk Assessment Matrix With Vulnerability Risk Assessment And Management Plan For Information Security
Risk Assessment Matrix With Vulnerability Risk Assessment And Management Plan For Information SecurityThis slide showcases assessment matrix to identify risk associated with different class of information assists. It calculates severity of risk on the basis of threat and vulnerability level Present the topic in a bit more detail with this Risk Assessment Matrix With Vulnerability Risk Assessment And Management Plan For Information Security. Use it as a tool for discussion and navigation on Assessment, Vulnerability, Associated. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
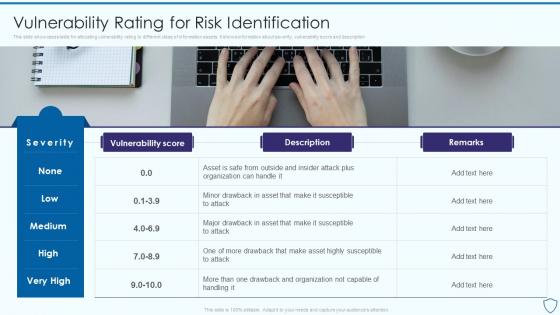 Vulnerability Rating For Risk Identification Risk Assessment And Management Plan For Information Security
Vulnerability Rating For Risk Identification Risk Assessment And Management Plan For Information SecurityThis slide showcases table for allocating vulnerability rating to different class of information assets. It shows information about severity, vulnerability score and description Present the topic in a bit more detail with this Vulnerability Rating For Risk Identification Risk Assessment And Management Plan For Information Security. Use it as a tool for discussion and navigation on Identification, Information, Vulnerability. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
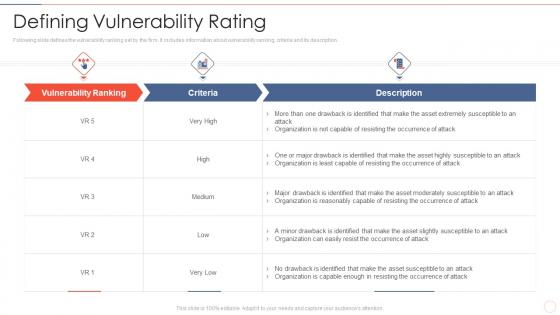 Effective information security defining vulnerability rating
Effective information security defining vulnerability ratingFollowing slide defines the vulnerability ranking set by the firm. It includes information about vulnerability ranking, criteria and its description. Present the topic in a bit more detail with this Effective Information Security Defining Vulnerability Rating. Use it as a tool for discussion and navigation on Vulnerability Ranking, Organization, Occurrence Attack. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
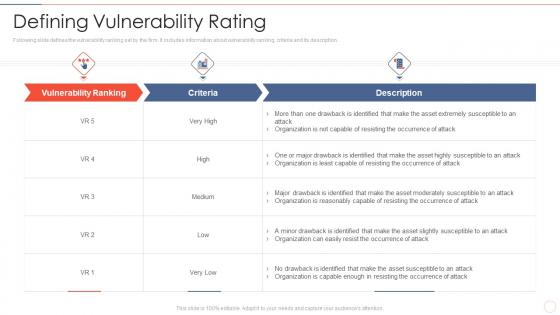 Defining vulnerability rating effective information security risk management process
Defining vulnerability rating effective information security risk management processFollowing slide defines the vulnerability ranking set by the firm. It includes information about vulnerability ranking, criteria and its description.Present the topic in a bit more detail with this Defining Vulnerability Rating Effective Information Security Risk Management Process. Use it as a tool for discussion and navigation on Occurrence Of Attack, Organization Is Reasonably, Organization Is Capable Enough. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
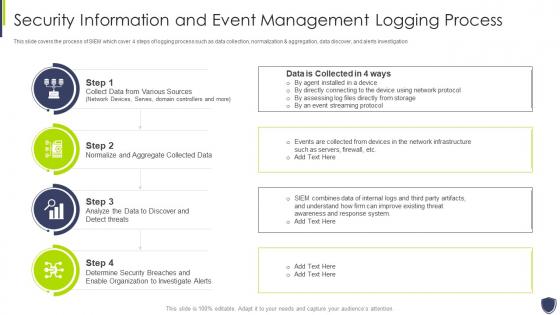 Improve it security with vulnerability information and event management logging process
Improve it security with vulnerability information and event management logging processThis slide covers the process of SIEM which cover 4 steps of logging process such as data collection, normalization and aggregation, data discover, and alerts investigation Introducing Improve It Security With Vulnerability Information And Event Management Logging Process to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Information, Management, Process, using this template. Grab it now to reap its full benefits.
-
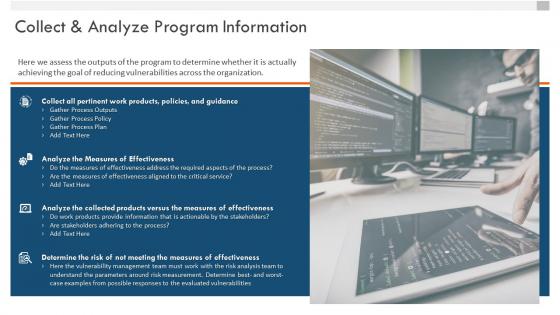 Vulnerability management whitepaper collect and analyze program information
Vulnerability management whitepaper collect and analyze program informationIncrease audience engagement and knowledge by dispensing information using Vulnerability Management Whitepaper Collect And Analyze Program Information. This template helps you present information on four stages. You can also present information on Gather Process Outputs, Gather Process Policy, Gather Process Plan, Analyze Measures Effectiveness using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
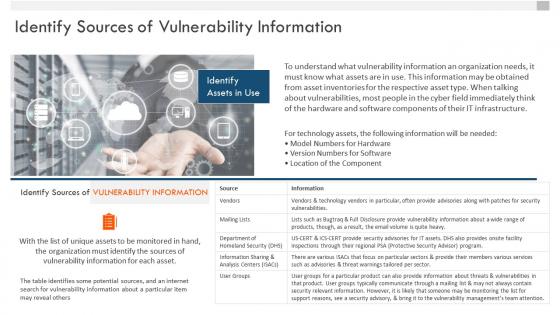 Vulnerability management whitepaper identify sources of vulnerability information
Vulnerability management whitepaper identify sources of vulnerability informationIncrease audience engagement and knowledge by dispensing information using Vulnerability Management Whitepaper Identify Sources Of Vulnerability Information. This template helps you present information on one stages. You can also present information on Vulnerability Information, Organization, Vulnerability Information using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Enterprise vulnerability management collect and analyze program information
Enterprise vulnerability management collect and analyze program informationIncrease audience engagement and knowledge by dispensing information using Enterprise Vulnerability Management Collect And Analyze Program Information. This template helps you present information on four stages. You can also present information on Collect All Pertinent, Analyze The Measures Of Effectiveness, Analyze The Collected Products using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
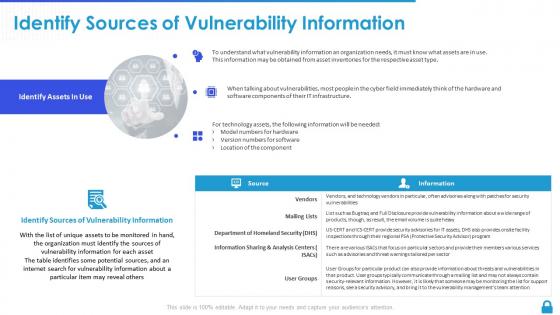 Enterprise vulnerability management identify sources of vulnerability information
Enterprise vulnerability management identify sources of vulnerability informationDeliver an outstanding presentation on the topic using this Enterprise Vulnerability Management Identify Sources Of Vulnerability Information. Dispense information and present a thorough explanation of Location Of The Component, Vulnerability Information, Vulnerability Information using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Threat Identification And Vulnerability Assessment For Information System Security And Risk Administration Plan
Threat Identification And Vulnerability Assessment For Information System Security And Risk Administration PlanThis slide showcases identification of threat and assessment of vulnerability and can help organization to identify the information breach risk. Its key components are vulnerability, severity, threat, threat source, likelihood, impact and risk rating. Deliver an outstanding presentation on the topic using this Threat Identification And Vulnerability Assessment For Information System Security And Risk Administration Plan. Dispense information and present a thorough explanation of Vulnerability Severity, Threat Source, Risk Rating using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Vulnerability Rating For Risk Identification Information System Security And Risk Administration Plan
Vulnerability Rating For Risk Identification Information System Security And Risk Administration PlanThis slide showcases table for allocating vulnerability rating to different class of information assets. Its shows information about severity, vulnerability score and description. Increase audience engagement and knowledge by dispensing information using Vulnerability Rating For Risk Identification Information System Security And Risk Administration Plan. This template helps you present information on one stages. You can also present information on Severity, Vulnerability Score, Vulnerability Rating using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
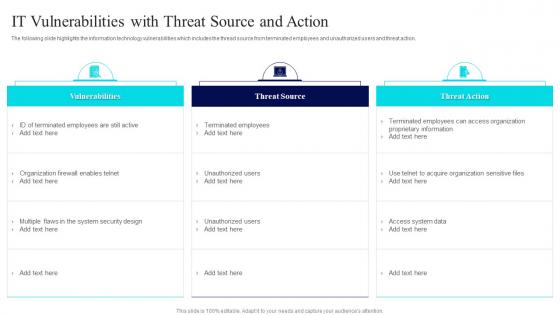 IT Vulnerabilities With Threat Source Risk Management Guide For Information Technology Systems
IT Vulnerabilities With Threat Source Risk Management Guide For Information Technology SystemsThe following slide highlights the information technology vulnerabilities which includes the thread source from terminated employees and unauthorized users and threat action. Present the topic in a bit more detail with this IT Vulnerabilities With Threat Source Risk Management Guide For Information Technology Systems. Use it as a tool for discussion and navigation on Vulnerabilities, Threat Source, Threat Action. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
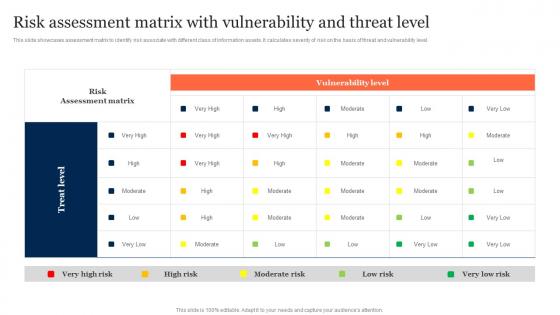 Risk Assessment Matrix With Vulnerability And Threat Level Information Security Risk Management
Risk Assessment Matrix With Vulnerability And Threat Level Information Security Risk ManagementThis slide showcases assessment matrix to identify risk associate with different class of information assets. It calculates severity of risk on the basis of threat and vulnerability level. Deliver an outstanding presentation on the topic using this Risk Assessment Matrix With Vulnerability And Threat Level Information Security Risk Management. Dispense information and present a thorough explanation of Risk Assessment Matrix, Vulnerability Level, Threat Level using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
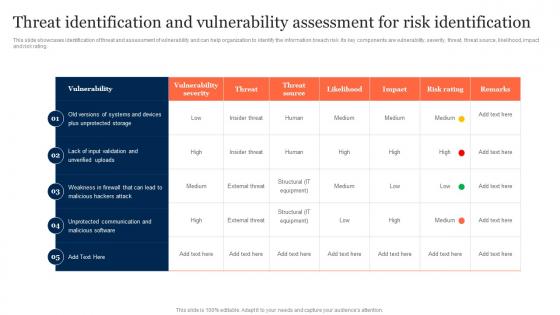 Threat Identification And Vulnerability Assessment Information Security Risk Management
Threat Identification And Vulnerability Assessment Information Security Risk ManagementThis slide showcases identification of threat and assessment of vulnerability and can help organization to identify the information breach risk. Its key components are vulnerability, severity, threat, threat source, likelihood, impact and risk rating. Present the topic in a bit more detail with this Threat Identification And Vulnerability Assessment Information Security Risk Management. Use it as a tool for discussion and navigation on Threat Identification, Vulnerability Assessment, Risk Identification. This template is free to edit as deemed fit for your organization. Therefore download it now
-
 Vulnerability Rating For Risk Identification Information Security Risk Management
Vulnerability Rating For Risk Identification Information Security Risk ManagementThis slide showcases table for allocating vulnerability rating to different class of information assets. Its shows information about severity, vulnerability score and description. Present the topic in a bit more detail with this Vulnerability Rating For Risk Identification Information Security Risk Management. Use it as a tool for discussion and navigation on Vulnerability Score, Risk Identification, Severity. This template is free to edit as deemed fit for your organization. Therefore download it now
-
 Information System Vulnerability Management Process Flow Icon
Information System Vulnerability Management Process Flow IconIntroducing our premium set of slides with Information System Vulnerability Management Process Flow Icon. Ellicudate the Three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Information System Vulnerability, Management Process Flow Icon. So download instantly and tailor it with your information.
-
 Vulnerability management activities inform assess prioritize remediate
Vulnerability management activities inform assess prioritize remediatePresenting this set of slides with name - Vulnerability Management Activities Inform Assess Prioritize Remediate. This is a five stage process. The stages in this process are Vulnerability Management, Risk Management, Vulnerability Planning.
-
 Vulnerability management information compliance remediation reporting
Vulnerability management information compliance remediation reportingPresenting this set of slides with name - Vulnerability Management Information Compliance Remediation Reporting. This is a six stage process. The stages in this process are Vulnerability Management, Risk Management, Vulnerability Planning.
-
 Information security identifying vulnerabilities ppt powerpoint presentation file model cpb
Information security identifying vulnerabilities ppt powerpoint presentation file model cpbPresenting this set of slides with name Information Security Identifying Vulnerabilities Ppt Powerpoint Presentation File Model Cpb. This is an editable Powerpoint four stages graphic that deals with topics like Information Security Identifying Vulnerabilities to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Information technology threats vulnerabilities ppt powerpoint presentation inspiration cpb
Information technology threats vulnerabilities ppt powerpoint presentation inspiration cpbPresenting this set of slides with name Information Technology Threats Vulnerabilities Ppt Powerpoint Presentation Inspiration Cpb. This is an editable Powerpoint graphic that deals with topics like Information Technology Threats Vulnerabilities to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Vulnerability socially informed peer peer systems ppt powerpoint presentation infographic template themes cpb
Vulnerability socially informed peer peer systems ppt powerpoint presentation infographic template themes cpbPresenting this set of slides with name Vulnerability Socially Informed Peer Peer Systems Ppt Powerpoint Presentation Infographic Template Themes Cpb. This is an editable Powerpoint four stages graphic that deals with topics like Vulnerability Socially Informed Peer Peer Systems to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Information security threats vulnerabilities ppt powerpoint presentation infographic template microsoft cpb
Information security threats vulnerabilities ppt powerpoint presentation infographic template microsoft cpbPresenting this set of slides with name Information Security Threats Vulnerabilities Ppt Powerpoint Presentation Infographic Template Microsoft Cpb. This is an editable Powerpoint four stages graphic that deals with topics like Information Security Threats Vulnerabilities to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Vulnerability assessment report ppt powerpoint presentation summary information cpb
Vulnerability assessment report ppt powerpoint presentation summary information cpbPresenting this set of slides with name Vulnerability Assessment Report Ppt Powerpoint Presentation Summary Information Cpb. This is an editable Powerpoint three stages graphic that deals with topics like Vulnerability Assessment Report to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
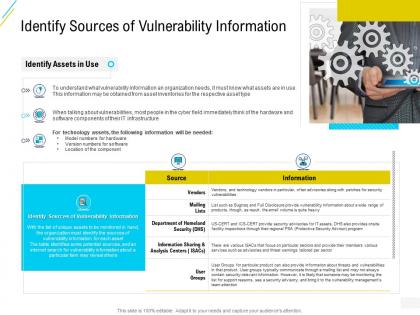 Organization risk probability management identify sources of vulnerability information ppt grid
Organization risk probability management identify sources of vulnerability information ppt gridIncrease audience engagement and knowledge by dispensing information using Organization Risk Probability Management Identify Sources Of Vulnerability Information Ppt Grid. This template helps you present information on six stages. You can also present information on Identify, Sources, Assets, Department, Groups using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
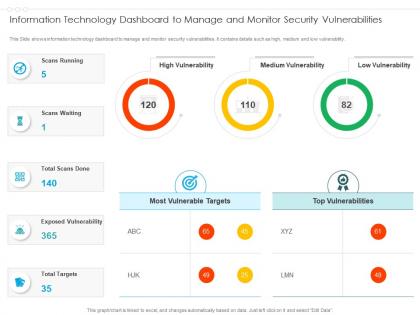 Information technology dashboard to manage and monitor security vulnerabilities
Information technology dashboard to manage and monitor security vulnerabilitiesPresenting our well structured Information Technology Dashboard To Manage And Monitor Security Vulnerabilities. The topics discussed in this slide are Information Technology Dashboard To Manage And Monitor Security Vulnerabilities. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
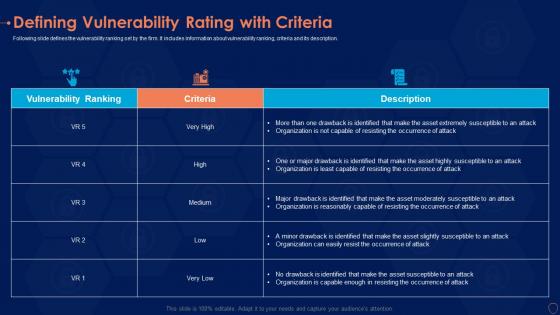 Defining vulnerability rating information security risk management program
Defining vulnerability rating information security risk management programFollowing slide defines the vulnerability ranking set by the firm. It includes information about vulnerability ranking, criteria and its description. Deliver an outstanding presentation on the topic using this Defining Vulnerability Rating Information Security Risk Management Program. Dispense information and present a thorough explanation of Organization, Occurrence, Asset using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Threat vulnerability dashboard information security risk management program
Threat vulnerability dashboard information security risk management programFollowing slide displays threat and vulnerability management dashboard. It covers KPIs such as organization exposure score, system configuration score and severity score. Present the topic in a bit more detail with this Threat Vulnerability Dashboard Information Security Risk Management Program. Use it as a tool for discussion and navigation on Exposure Score, Vulnerable Software, Security Recommendation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
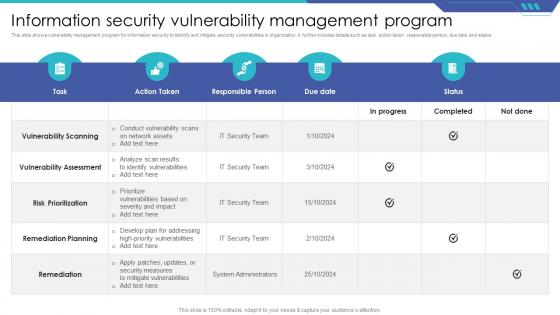 Information Security Vulnerability Management Program
Information Security Vulnerability Management ProgramThis slide shows vulnerability management program for information security to identify and mitigate security vulnerabilities in organization. It further includes details such as task, action taken, responsible person, due date and status. Presenting our well structured Information Security Vulnerability Management Program The topics discussed in this slide are Vulnerability Scanning, Remediation Planning, Remediation. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
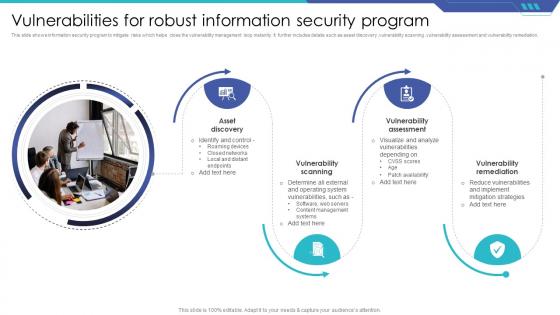 Vulnerabilities For Robust Information Security Program
Vulnerabilities For Robust Information Security ProgramThis slide shows information security program to mitigate risks which helps close the vulnerability management loop instantly. It further includes details such as asset discovery ,vulnerability scanning ,vulnerability assessment and vulnerability remediation. Presenting our set of slides with Vulnerabilities For Robust Information Security Program This exhibits information on Four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Asset Discovery, Vulnerability Scanning, Vulnerability Assessment
-
 Information Security Audit Icon For Vulnerability Assessment
Information Security Audit Icon For Vulnerability AssessmentPresenting our set of slides with Information Security Audit Icon For Vulnerability Assessment. This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Information Security Audit, Icon For Vulnerability Assessment

