Powerpoint Templates and Google slides for Cyber Risk Mitigation Techniques
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Cyber Risk Assessment And Mitigation Planning Complete Deck
Cyber Risk Assessment And Mitigation Planning Complete DeckDeliver this complete deck to your team members and other collaborators. Encompassed with stylized slides presenting various concepts, this Cyber Risk Assessment And Mitigation Planning Complete Deck is the best tool you can utilize. Personalize its content and graphics to make it unique and thought-provoking. All the sixty slides are editable and modifiable, so feel free to adjust them to your business setting. The font, color, and other components also come in an editable format making this PPT design the best choice for your next presentation. So, download now.
-
 Cyber Attack Risks Mitigation Strategies Powerpoint Ppt Template Bundles DK MD
Cyber Attack Risks Mitigation Strategies Powerpoint Ppt Template Bundles DK MDIf you require a professional template with great design, then this Cyber Attack Risks Mitigation Strategies Powerpoint Ppt Template Bundles DK MD is an ideal fit for you. Deploy it to enthrall your audience and increase your presentation threshold with the right graphics, images, and structure. Portray your ideas and vision using eighteen slides included in this complete deck. This template is suitable for expert discussion meetings presenting your views on the topic. With a variety of slides having the same thematic representation, this template can be regarded as a complete package. It employs some of the best design practices, so everything is well structured. Not only this, it responds to all your needs and requirements by quickly adapting itself to the changes you make. This PPT slideshow is available for immediate download in PNG, JPG, and PDF formats, further enhancing its usability. Grab it by clicking the download button.
-
 Blockchain Cyber Security Issues And Risk Mitigation Powerpoint Ppt Template Bundles BCT MM
Blockchain Cyber Security Issues And Risk Mitigation Powerpoint Ppt Template Bundles BCT MMIf you require a professional template with great design, then this Blockchain Cyber Security Issues And Risk Mitigation Powerpoint Ppt Template Bundles BCT MM is an ideal fit for you. Deploy it to enthrall your audience and increase your presentation threshold with the right graphics, images, and structure. Portray your ideas and vision using thirteen slides included in this complete deck. This template is suitable for expert discussion meetings presenting your views on the topic. With a variety of slides having the same thematic representation, this template can be regarded as a complete package. It employs some of the best design practices, so everything is well structured. Not only this, it responds to all your needs and requirements by quickly adapting itself to the changes you make. This PPT slideshow is available for immediate download in PNG, JPG, and PDF formats, further enhancing its usability. Grab it by clicking the download button.
-
 Cyber Security Risk Mitigation Strategy Action Plan Icon
Cyber Security Risk Mitigation Strategy Action Plan IconIntroducing our premium set of slides with Cyber Security Risk Mitigation Strategy Action Plan Icon. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Mitigation, Strategy, Action. So download instantly and tailor it with your information.
-
 Incident Mitigation Strategies For Cyber Risks In Finance Industry
Incident Mitigation Strategies For Cyber Risks In Finance IndustryThis slide shows strategic techniques to mitigate cyber security risks in finance industry. The purpose of this slide is to strengthen security of financial sector by protecting its complex IT infrastructure and digital assets. It covers strategies such as threat intelligence, external asset protection, brand abuse scanning and dark web monitoring. Presenting our set of slides with Incident Mitigation Strategies For Cyber Risks In Finance Industry This exhibits information on Four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Mean Time To Detect, Mean Time To Resolve, Incident Escalation Rate.
-
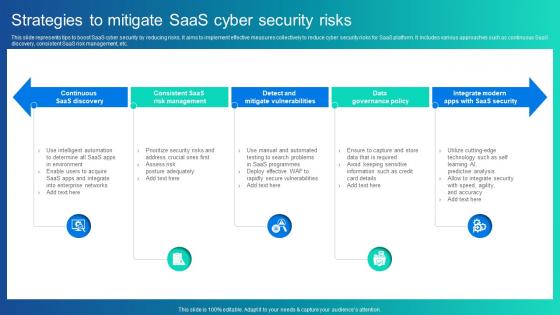 Strategies To Mitigate Saas Cyber Security Risks
Strategies To Mitigate Saas Cyber Security RisksThis slide represents tips to boost SaaS cyber security by reducing risks. It aims to implement effective measures collectively to reduce cyber security risks for SaaS platform. It includes various approaches such as continuous SaaS discovery, consistent SaaS risk management, etc. Introducing our premium set of slides with Strategies To Mitigate Saas Cyber Security Risks Ellicudate the Five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Continuous Saas Discovery, Risk Management, Mitigate Vulnerabilities. So download instantly and tailor it with your information.
-
 Conduct Third Party Risk Assessment Implementing Strategies To Mitigate Cyber Security Threats
Conduct Third Party Risk Assessment Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide illustrates checklist to evaluate third party risk assessment to eliminate unnecessary threats. It includes elements such as cyber security policies, patch management process, physical security guidelines, information safety etc. Deliver an outstanding presentation on the topic using this Conduct Third Party Risk Assessment Implementing Strategies To Mitigate Cyber Security Threats Dispense information and present a thorough explanation of Parameters, Response, Status using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Determine Cyber Security Risks And Threats Implementing Strategies To Mitigate Cyber Security Threats
Determine Cyber Security Risks And Threats Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide highlights cyber security risks and threats identified within the company to analyze and protect from potential loss. It includes elements such as objectives, issue identifier, malware, phishing, ransomware, weak credentials, data breach etc. Deliver an outstanding presentation on the topic using this Determine Cyber Security Risks And Threats Implementing Strategies To Mitigate Cyber Security Threats Dispense information and present a thorough explanation of Malware, Phishing, Ransomware using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 KPIs To Evaluate Cyber Security Risk Management Implementing Strategies To Mitigate Cyber Security Threats
KPIs To Evaluate Cyber Security Risk Management Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide highlights some key performance indicators to measure the impact of cyber security risk administration to assess its effectiveness and take improved decisions. It includes elements such as level of preparedness, mean time to detect, success rating etc. Present the topic in a bit more detail with this KPIs To Evaluate Cyber Security Risk Management Implementing Strategies To Mitigate Cyber Security Threats Use it as a tool for discussion and navigation on Level Of Preparedness, Mean Time To Detect, Mean Time To Resolve This template is free to edit as deemed fit for your organization. Therefore download it now.
-
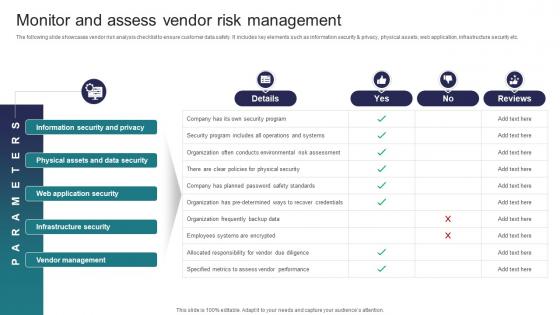 Monitor And Assess Vendor Risk Management Implementing Strategies To Mitigate Cyber Security Threats
Monitor And Assess Vendor Risk Management Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide showcases vendor risk analysis checklist to ensure customer data safety. It includes key elements such as information security and privacy, physical assets, web application, infrastructure security etc. Present the topic in a bit more detail with this Monitor And Assess Vendor Risk Management Implementing Strategies To Mitigate Cyber Security Threats Use it as a tool for discussion and navigation on Information Security And Privacy, Physical Assets And Data Security, Web Application Security This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Run Penetration Testing To Review Risk Implementing Strategies To Mitigate Cyber Security Threats
Run Penetration Testing To Review Risk Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide showcases various methods to review cyber risks to determine probability and impact of risks. It includes elements such as penetration, red team and risk based testing along with objectives, features, cost, outcomes, duration etc. Present the topic in a bit more detail with this Run Penetration Testing To Review Risk Implementing Strategies To Mitigate Cyber Security Threats Use it as a tool for discussion and navigation on Objectives, Features, Duration This template is free to edit as deemed fit for your organization. Therefore download it now.
-
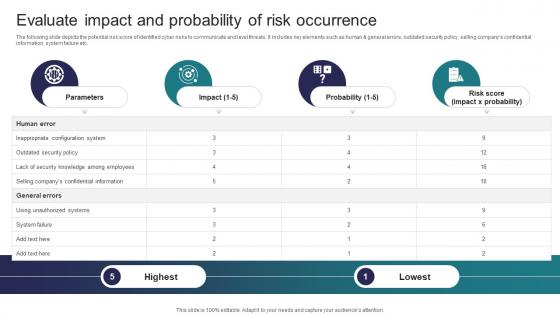 Implementing Strategies To Mitigate Cyber Security Evaluate Impact And Probability Of Risk Occurrence
Implementing Strategies To Mitigate Cyber Security Evaluate Impact And Probability Of Risk OccurrenceThe following slide depicts the potential risk score of identified cyber risks to communicate and level threats. It includes key elements such as human and general errors, outdated security policy, selling companys confidential information, system failure etc. Present the topic in a bit more detail with this Implementing Strategies To Mitigate Cyber Security Evaluate Impact And Probability Of Risk Occurrence Use it as a tool for discussion and navigation on Parameters, Impact, Probability This template is free to edit as deemed fit for your organization. Therefore download it now.
-
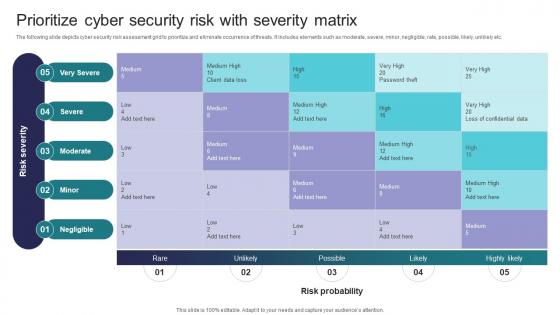 Implementing Strategies To Mitigate Cyber Security Threats Prioritize Cyber Security Risk With Severity Matrix
Implementing Strategies To Mitigate Cyber Security Threats Prioritize Cyber Security Risk With Severity MatrixThe following slide depicts cyber security risk assessment grid to prioritize and eliminate occurrence of threats. It includes elements such as moderate, severe, minor, negligible, rate, possible, likely, unlikely etc. Introducing Implementing Strategies To Mitigate Cyber Security Threats Prioritize Cyber Security Risk With Severity Matrix to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Very Severe, Severe, Moderate using this template. Grab it now to reap its full benefits.
-
 Agenda Cyber Risk Assessment And Mitigation Planning
Agenda Cyber Risk Assessment And Mitigation PlanningIntroducing Agenda Cyber Risk Assessment And Mitigation Planning to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Awareness Trends, Risk Management Process using this template. Grab it now to reap its full benefits.
-
 Cyber Risk Assessment And Mitigation Planning Table Of Contents
Cyber Risk Assessment And Mitigation Planning Table Of ContentsIntroducing Cyber Risk Assessment And Mitigation Planning Table Of Contents to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispence information on Effective Cyber Security, Strategies, Password Management using this template. Grab it now to reap its full benefits.
-
 Icons Slide For Cyber Risk Assessment And Mitigation Planning
Icons Slide For Cyber Risk Assessment And Mitigation PlanningIntroducing our well researched set of slides titled Icons Slide For Cyber Risk Assessment And Mitigation Planning It displays a hundred percent editable icons. You can use these icons in your presentation to captivate your audiences attention. Download now and use it multiple times.
-
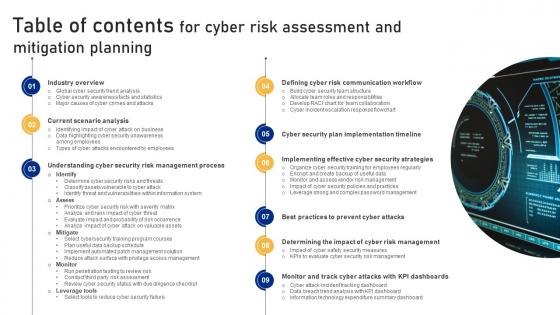 Table Of Contents For Cyber Risk Assessment And Mitigation Planning
Table Of Contents For Cyber Risk Assessment And Mitigation PlanningIncrease audience engagement and knowledge by dispensing information using Table Of Contents For Cyber Risk Assessment And Mitigation Planning This template helps you present information on nine stages. You can also present information on Industry Overview, Scenario Analysis, Management Process using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Mitigating Cloning Risks In Cyber Security
Mitigating Cloning Risks In Cyber SecurityThis slide shows strategies to counter cloning attacks. The purpose of this slide is to help cybersecurity experts in identifying and preventing cybersecurity threats. It covers mitigating measures such as security awareness training, email credentials security, link authentication, etc. Introducing our premium set of slides with name Mitigating Cloning Risks In Cyber Security. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Security Awareness, Link Authentication, Security Solutions. So download instantly and tailor it with your information.
-
 Implement Cyber Incident Report Template Phases For Risk Mitigation
Implement Cyber Incident Report Template Phases For Risk MitigationThis slide demonstrates cyber report template phases for supporting incidents systematically by using appropriate actions to follow consistent process. It includes stages such as preparation, detection and analysis, containment, elimination, recovery, etc. Presenting our set of slides with Implement Cyber Incident Report Template Phases For Risk Mitigation. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Detection And Analysis, Containment, Elimination.
-
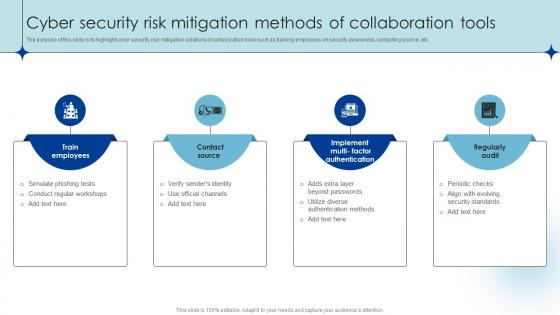 Cyber Security Risk Mitigation Methods Of Collaboration Tools
Cyber Security Risk Mitigation Methods Of Collaboration ToolsThe purpose of this slide is to highlight cyber security risk mitigation solutions of collaboration tools such as training employees on security awareness, contacting source, etc. Introducing our premium set of slides with Cyber Security Risk Mitigation Methods Of Collaboration Tools. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Simulate Phishing Tests, Verify Senders Identity, Use Official Channels . So download instantly and tailor it with your information.
-
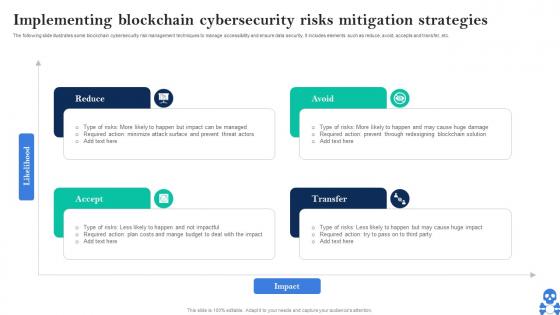 Cyber Threats In Blockchain Implementing Blockchain Cybersecurity Risks Mitigation Strategies BCT SS V
Cyber Threats In Blockchain Implementing Blockchain Cybersecurity Risks Mitigation Strategies BCT SS VThe following slide illustrates some blockchain cybersecurity risk management techniques to manage accessibility and ensure data security. It includes elements such as reduce, avoid, accepts and transfer, etc. Introducing Cyber Threats In Blockchain Implementing Blockchain Cybersecurity Risks Mitigation Strategies BCT SS V to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Reduce, Avoid, Transfer, Accept using this template. Grab it now to reap its full benefits.
-
 Cyber Emergency Plan Icon For Risk Mitigation And Preparedness
Cyber Emergency Plan Icon For Risk Mitigation And PreparednessIntroducing our premium set of slides with Cyber Emergency Plan Icon For Risk Mitigation And Preparedness. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cyber Emergency Plan, Risk Mitigation. So download instantly and tailor it with your information.
-
 Enterprise Cyber Risk Management Dashboard Risk Management And Mitigation Strategy
Enterprise Cyber Risk Management Dashboard Risk Management And Mitigation StrategyThis slide represents dashboard representing details related to management of strategic risks in the organization. It includes details related to risk rating breakdown, risk heat map, top 5 vulnerabilities etc. Deliver an outstanding presentation on the topic using this Enterprise Cyber Risk Management Dashboard Risk Management And Mitigation Strategy. Dispense information and present a thorough explanation of Risk Rating, Risk Heat Map, Action Plan Breakdown using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Enterprise Cyber Risk Management Dashboard Enterprise Management Mitigation Plan
Enterprise Cyber Risk Management Dashboard Enterprise Management Mitigation PlanThis slide represents dashboard representing details related to management of strategic risks in the organization. It includes details related to risk rating breakdown, risk heat map, top 5 vulnerabilities etc. Present the topic in a bit more detail with this Enterprise Cyber Risk Management Dashboard Enterprise Management Mitigation Plan. Use it as a tool for discussion and navigation on Management, Dashboard, Enterprise. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Enterprise Cyber Risk Management Dashboard Enterprise Risk Mitigation Strategies
Enterprise Cyber Risk Management Dashboard Enterprise Risk Mitigation StrategiesThis slide represents dashboard representing details related to management of strategic risks in the organization. It includes details related to risk rating breakdown, risk heat map, top 5 vulnerabilities etc. Present the topic in a bit more detail with this Enterprise Cyber Risk Management Dashboard Enterprise Risk Mitigation Strategies. Use it as a tool for discussion and navigation on Management, Dashboard, Enterprise. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Mitigating Cyber Security Risks In Powerpoint And Google Slides Cpb
Mitigating Cyber Security Risks In Powerpoint And Google Slides CpbPresenting Mitigating Cyber Security Risks In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase five stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Mitigating Cyber Security Risks. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Risk Mitigating Business Cyber Security Strategies
Risk Mitigating Business Cyber Security StrategiesThis slide covers risk mitigating business cyber security strategies which are training employees, installing spyware, backup data and privileged access. Presenting our set of slides with name Risk Mitigating Business Cyber Security Strategies. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Employees, Spyware, Data, Employee Access.
-
 IT Risk Management Strategies Prioritized Cyber Security Threats With Risk Mitigation Plan
IT Risk Management Strategies Prioritized Cyber Security Threats With Risk Mitigation PlanThis slide highlights the cyber security threats with key risks and their mitigation plan and owner with risk reduction timeline. Increase audience engagement and knowledge by dispensing information using IT Risk Management Strategies Prioritized Cyber Security Threats With Risk Mitigation Plan. This template helps you present information on one stages. You can also present information on Threat, Risk, Risk Priority, Risk Reduction Timeline using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
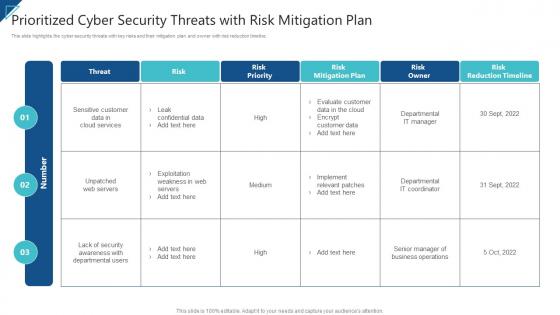 Enterprise Risk Management Prioritized Cyber Security Threats With Risk Mitigation Plan
Enterprise Risk Management Prioritized Cyber Security Threats With Risk Mitigation PlanThis slide highlights the cyber security threats with key risks and their mitigation plan and owner with risk reduction timeline. Present the topic in a bit more detail with this Enterprise Risk Management Prioritized Cyber Security Threats With Risk Mitigation Plan. Use it as a tool for discussion and navigation on Threat, Risk, Risk Priority, Risk Reduction Timeline. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
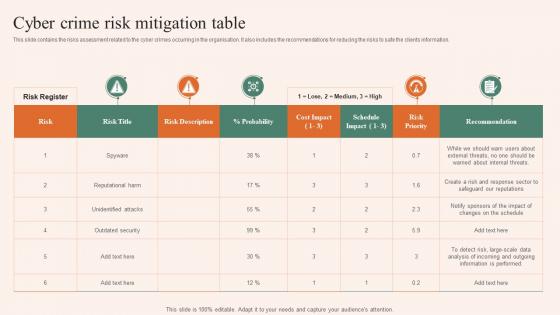 Cyber Crime Risk Mitigation Table
Cyber Crime Risk Mitigation TableThis slide contains the risks assessment related to the cyber crimes occurring in the organisation. It also includes the recommendations for reducing the risks to safe the clients information. Introducing our Cyber Crime Risk Mitigation Table set of slides. The topics discussed in these slides are Cyber Crime, Risk Mitigation, Table. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
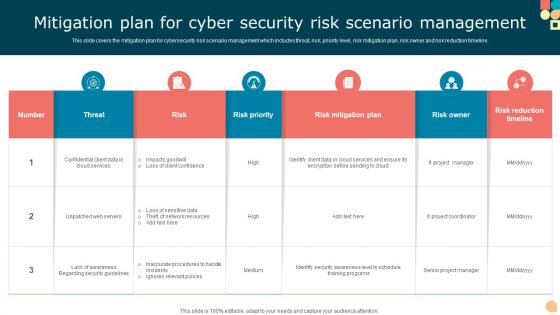 Mitigation Plan For Cyber Security Risk Scenario Management
Mitigation Plan For Cyber Security Risk Scenario ManagementThis slide covers the mitigation plan for cybersecurity risk scenario management which includes threat, risk, priority level, risk mitigation plan, risk owner and risk reduction timeline. Presenting our well structured Mitigation Plan For Cyber Security Risk Scenario Management. The topics discussed in this slide are Risk, Risk Priority, Risk Mitigation Plan. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
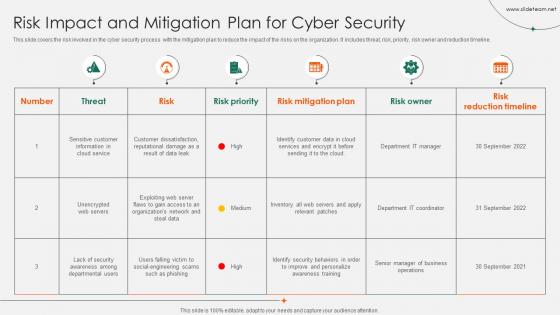 Risk Impact And Mitigation Plan For Cyber Security
Risk Impact And Mitigation Plan For Cyber SecurityThis slide covers the risk involved in the cyber security process with the mitigation plan to reduce the impact of the risks on the organization. It includes threat, risk, priority, risk owner and reduction timeline. Introducing our Risk Impact And Mitigation Plan For Cyber Security set of slides. The topics discussed in these slides are Risk Priority, Risk Mitigation Plan, Risk Owner. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Prioritized Cyber Security Threats With Risk Mitigation Plan Risk Assessment Of It Systems
Prioritized Cyber Security Threats With Risk Mitigation Plan Risk Assessment Of It SystemsThis slide highlights the cyber security threats with key risks and their mitigation plan and owner with risk reduction timeline. Present the topic in a bit more detail with this Prioritized Cyber Security Threats With Risk Mitigation Plan Risk Assessment Of It Systems. Use it as a tool for discussion and navigation on Mitigation Plan, Prioritized, Security Threats. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Top Cyber Risks Faced By The Real Estate Company Implementing Risk Mitigation Strategies For Real
Top Cyber Risks Faced By The Real Estate Company Implementing Risk Mitigation Strategies For Realfollowing slide exhibits four cyber risks which are faced by the real estate organization. It provides key information about the ransomware, phishing, webbased attack and email fraud attack. Introducing Top Cyber Risks Faced By The Real Estate Company Implementing Risk Mitigation Strategies For Real to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Ransomware, Phishing, Business Email, using this template. Grab it now to reap its full benefits.
-
 Cybersecurity Risk Assessment Program Strategic Plan To Mitigate Cyber Attacks
Cybersecurity Risk Assessment Program Strategic Plan To Mitigate Cyber AttacksThe slide indicates the risk mitigation plan for the multiple cyber attacks. It also includes details of cost involved and implementation time required for each mitigation approach. Deliver an outstanding presentation on the topic using this Cybersecurity Risk Assessment Program Strategic Plan To Mitigate Cyber Attacks. Dispense information and present a thorough explanation of Strategic Plan, Mitigate Cyber Attacks, Malware Attack, Recommended Mitigation Strategy using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Adopt Cyber Security Data Policies Cyber Attack Risks Mitigation
Adopt Cyber Security Data Policies Cyber Attack Risks MitigationThe following slide highlights various cyber security policies to manage data control and breach. It includes elements such as network security, data, workstations, remote access etc. Introducing Adopt Cyber Security Data Policies Cyber Attack Risks Mitigation to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Network Security Policies, Data Security Policies, Workstation Policies, using this template. Grab it now to reap its full benefits.
-
 Adopting Strategies By Cyber Attack Type Cyber Attack Risks Mitigation
Adopting Strategies By Cyber Attack Type Cyber Attack Risks MitigationThe following slide depicts the various strategies to manage data control and breach. It includes elements such as attrition, malware, hacking, social tactic, improper usage, train and educate employees, automate identification, data management etc. Present the topic in a bit more detail with this Adopting Strategies By Cyber Attack Type Cyber Attack Risks Mitigation. Use it as a tool for discussion and navigation on Educate Employees, Data Management, Automate Attack Identification. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
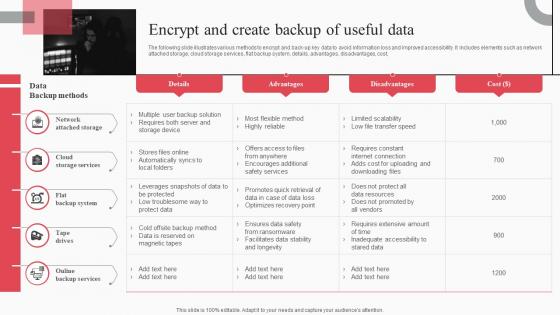 Encrypt And Create Backup Of Useful Data Cyber Attack Risks Mitigation
Encrypt And Create Backup Of Useful Data Cyber Attack Risks MitigationThe following slide illustrates various methods to encrypt and back-up key data to avoid information loss and improved accessibility. It includes elements such as network attached storage, cloud storage services, flat backup system, details, advantages, disadvantages, cost, Deliver an outstanding presentation on the topic using this Encrypt And Create Backup Of Useful Data Cyber Attack Risks Mitigation. Dispense information and present a thorough explanation of Network Attached Storage, Cloud Storage Services, Flat Backup System using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Impact Of Cyber Security Policies And Practices Cyber Attack Risks Mitigation
Impact Of Cyber Security Policies And Practices Cyber Attack Risks MitigationThe following slide focuses on drafting cyber security policies to manage data control and breach. It mainly includes elements such as impact of existing cyber safety policies, mitigation actions, etc. Present the topic in a bit more detail with this Impact Of Cyber Security Policies And Practices Cyber Attack Risks Mitigation. Use it as a tool for discussion and navigation on Inadequate Security Guidelines, Inappropriate Privacy Policies. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
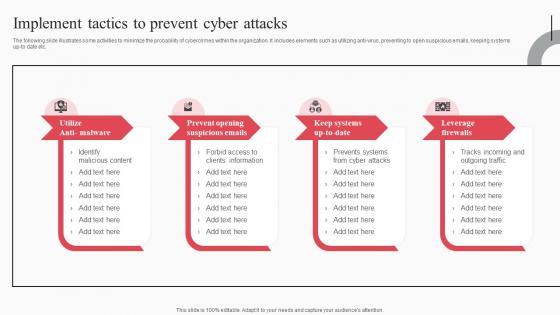 Implement Tactics To Prevent Cyber Attacks Cyber Attack Risks Mitigation
Implement Tactics To Prevent Cyber Attacks Cyber Attack Risks MitigationThe following slide illustrates some activities to minimize the probability of cybercrimes within the organization. It includes elements such as utilizing anti virus, preventing to open suspicious emails, keeping systems up to date etc. Introducing Implement Tactics To Prevent Cyber Attacks Cyber Attack Risks Mitigation to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Prevent Opening Suspicious Emails, Keep Systems Up To Date, Leverage Firewalls, using this template. Grab it now to reap its full benefits.
-
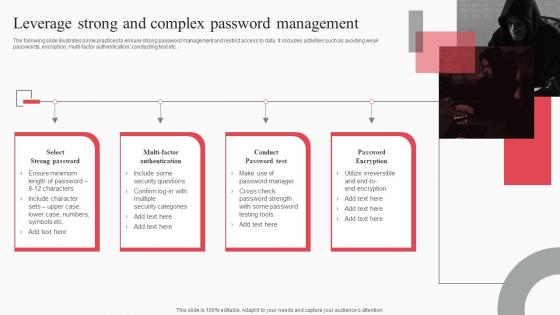 Leverage Strong And Complex Password Management Cyber Attack Risks Mitigation
Leverage Strong And Complex Password Management Cyber Attack Risks MitigationThe following slide illustrates some practices to ensure strong password management and restrict access to data. It includes activities such as avoiding weak passwords, encryption, multi-factor authentication, conducting test etc. Increase audience engagement and knowledge by dispensing information using Leverage Strong And Complex Password Management Cyber Attack Risks Mitigation. This template helps you present information on four stages. You can also present information on Select Strong Password, Multi Factor Authentication, Conduct Password Test using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Monitor And Assess Vendor Risk Management Cyber Attack Risks Mitigation
Monitor And Assess Vendor Risk Management Cyber Attack Risks MitigationThe following slide showcases vendor risk analysis checklist to ensure customer data safety. It includes key elements such as information security and privacy, physical assets, web application, infrastructure security etc. Introducing Monitor And Assess Vendor Risk Management Cyber Attack Risks Mitigation to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispence information on Web Application Security, Infrastructure Security, Vendor Management, using this template. Grab it now to reap its full benefits.
-
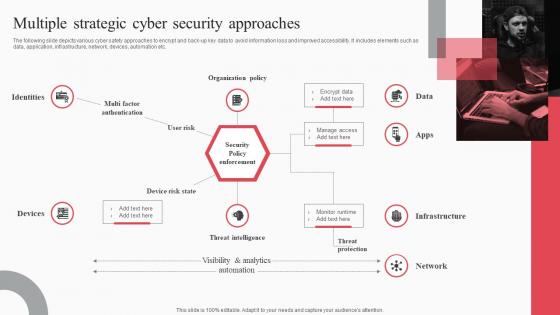 Multiple Strategic Cyber Security Approaches Cyber Attack Risks Mitigation
Multiple Strategic Cyber Security Approaches Cyber Attack Risks MitigationThe following slide depicts various cyber safety approaches to encrypt and back up key data to avoid information loss and improved accessibility. It includes elements such as data, application, infrastructure, network, devices, automation etc. Increase audience engagement and knowledge by dispensing information using Multiple Strategic Cyber Security Approaches Cyber Attack Risks Mitigation. This template helps you present information on one stage. You can also present information on Identities, Organization Policy, Threat Intelligence using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Organize Cyber Security Training For Employees Regularly Cyber Attack Risks Mitigation
Organize Cyber Security Training For Employees Regularly Cyber Attack Risks MitigationThe following slide depicts the staff cyber security training plan to educate them regarding technology threats and practices. It mainly includes elements such as topics to be covered, target audience, trainer name, mode, proposed date, timings etc. Introducing Organize Cyber Security Training For Employees Regularly Cyber Attack Risks Mitigation to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispence information on Document Management, Response Process, Social Media Policy, using this template. Grab it now to reap its full benefits.
-
 Passive Active And Offensive Cyber Security Strategies Cyber Attack Risks Mitigation
Passive Active And Offensive Cyber Security Strategies Cyber Attack Risks MitigationThe following slide showcases passive, active and offensive cyber safety techniques to ensure customer data safety. It includes elements such as inspecting vulnerabilities, penetration testing, deception technology, threat hunting etc. Increase audience engagement and knowledge by dispensing information using Passive Active And Offensive Cyber Security Strategies Cyber Attack Risks Mitigation. This template helps you present information on three stages. You can also present information on Passive Safety, Active Safety, Offensive Safety using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
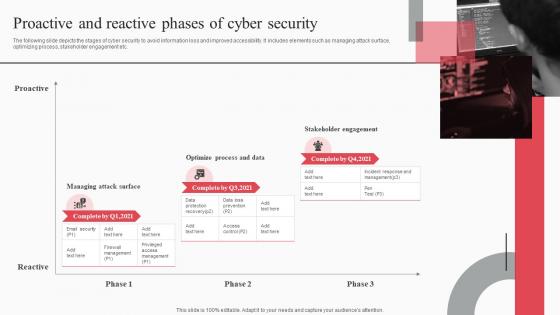 Proactive And Reactive Phases Of Cyber Security Cyber Attack Risks Mitigation
Proactive And Reactive Phases Of Cyber Security Cyber Attack Risks MitigationThe following slide depicts the stages of cyber security to avoid information loss and improved accessibility. It includes elements such as managing attack surface, optimizing process, stakeholder engagement etc. Introducing Proactive And Reactive Phases Of Cyber Security Cyber Attack Risks Mitigation to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Proactive, Managing Attack Surface, Optimize Process, Stakeholder Engagement, using this template. Grab it now to reap its full benefits.
-
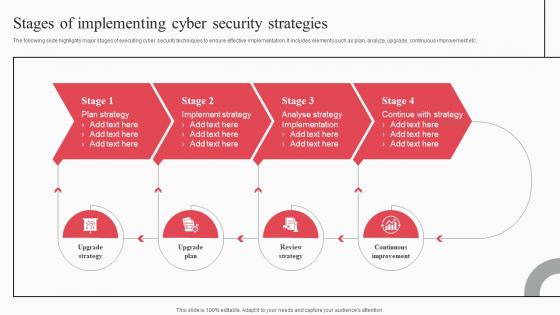 Stages Of Implementing Cyber Security Strategies Cyber Attack Risks Mitigation
Stages Of Implementing Cyber Security Strategies Cyber Attack Risks MitigationThe following slide highlights major stages of executing cyber security techniques to ensure effective implementation. It includes elements such as plan, analyze, upgrade, continuous improvement etc. Increase audience engagement and knowledge by dispensing information using Stages Of Implementing Cyber Security Strategies Cyber Attack Risks Mitigation. This template helps you present information on four stages. You can also present information on Plan Strategy, Implement Strategy, Analyse Strategy using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
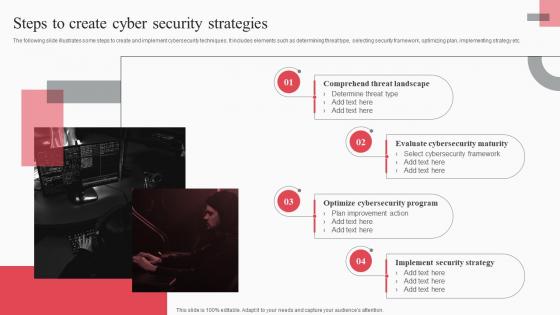 Steps To Create Cyber Security Strategies Cyber Attack Risks Mitigation
Steps To Create Cyber Security Strategies Cyber Attack Risks MitigationThe following slide illustrates some steps to create and implement cybersecurity techniques. It includes elements such as determining threat type, selecting security framework, optimizing plan, implementing strategy etc. Introducing Steps To Create Cyber Security Strategies Cyber Attack Risks Mitigation to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Comprehend Threat Landscape, Evaluate Cybersecurity Maturity, Optimize Cybersecurity Program, using this template. Grab it now to reap its full benefits.
-
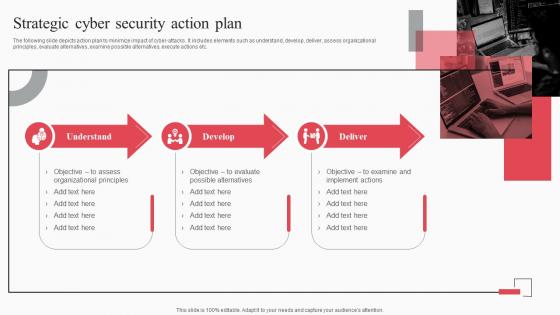 Strategic Cyber Security Action Plan Cyber Attack Risks Mitigation
Strategic Cyber Security Action Plan Cyber Attack Risks MitigationThe following slide depicts action plan to minimize impact of cyber attacks. It includes elements such as understand, develop, deliver, assess organizational principles, evaluate alternatives, examine possible alternatives, execute actions etc. Increase audience engagement and knowledge by dispensing information using Strategic Cyber Security Action Plan Cyber Attack Risks Mitigation. This template helps you present information on three stages. You can also present information on Understand, Develop, Deliver, Organizational Principles using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
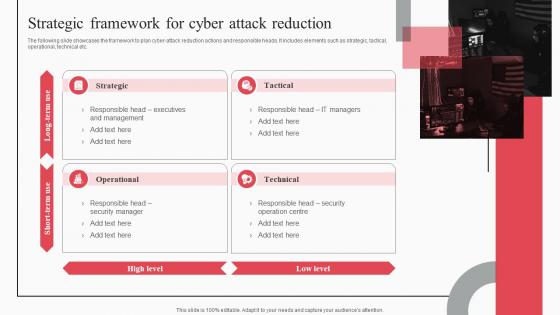 Strategic Framework For Cyber Attack Reduction Cyber Attack Risks Mitigation
Strategic Framework For Cyber Attack Reduction Cyber Attack Risks MitigationThe following slide showcases the framework to plan cyber-attack reduction actions and responsible heads. It includes elements such as strategic, tactical, operational, technical etc. Introducing Strategic Framework For Cyber Attack Reduction Cyber Attack Risks Mitigation to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Strategic, Tactical, Operational, Technical, using this template. Grab it now to reap its full benefits.
-
 Table Of Contents For Cyber Attack Risks Mitigation Strategies Ppt Slides
Table Of Contents For Cyber Attack Risks Mitigation Strategies Ppt SlidesIntroducing Table Of Contents For Cyber Attack Risks Mitigation Strategies Ppt Slides to increase your presentation threshold. Encompassed with fifteen stages, this template is a great option to educate and entice your audience. Dispence information on Security Strategies, Strategic Framework, Password Management, using this template. Grab it now to reap its full benefits.
-
 Steps to mitigate cyber security risks
Steps to mitigate cyber security risksPresenting this set of slides with name Steps To Mitigate Cyber Security Risks. This is a five stage process. The stages in this process are Assets Identification, Asset Protection, Incident Detection, Build Plan To Respond, Recovery To Normal Operation. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Mitigation plans to address key risks cyber incident ppt powerpoint presentation slides
Mitigation plans to address key risks cyber incident ppt powerpoint presentation slidesThis slide provides information regarding the identified risks that are needed to be addressed. The plan will help in keeping the track of potential risks that are existing and what are the resources required to handle them. Presenting this set of slides with name Mitigation Plans To Address Key Risks Cyber Incident Ppt Powerpoint Presentation S. The topics discussed in these slides are Risk Level, Risk Mitigation, Duration, Communication, Risk Treated. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Risks involved and mitigation strategies overcome challenge cyber security healthcare ppt ideas
Risks involved and mitigation strategies overcome challenge cyber security healthcare ppt ideasThe slide shows the risks associated with the implementation of strategy. Also, it provides the level of the risk low, medium or high, Potential Risk Impact on the Company and Key Strategies or Measures for mitigating the risk. Present the topic in a bit more detail with this Risks Involved And Mitigation Strategies Overcome Challenge Cyber Security Healthcare Ppt Ideas. Use it as a tool for discussion and navigation on Revenue, Opportunities, Management, Security, Data. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
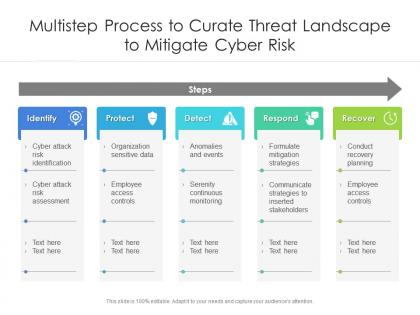 Multistep process to curate threat landscape to mitigate cyber risk
Multistep process to curate threat landscape to mitigate cyber riskIntroducing our premium set of slides with Multistep Process To Curate Threat Landscape To Mitigate Cyber Risk. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Identify, Protect, Detect. So download instantly and tailor it with your information.

