Powerpoint Templates and Google slides for Government Cyber Attacks
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Cyber Security Policy Powerpoint Presentation Slides
Cyber Security Policy Powerpoint Presentation SlidesThis complete deck covers various topics and highlights important concepts. It has PPT slides which cater to your business needs. This complete deck presentation emphasizes Cyber Security Policy Powerpoint Presentation Slides and has templates with professional background images and relevant content. This deck consists of total of sixty two slides. Our designers have created customizable templates, keeping your convenience in mind. You can edit the color, text and font size with ease. Not just this, you can also add or delete the content if needed. Get access to this fully editable complete presentation by clicking the download button below.
-
 Cyber Security Policy Powerpoint Ppt Template Bundles
Cyber Security Policy Powerpoint Ppt Template BundlesDeliver a credible and compelling presentation by deploying this Cyber Security Policy Powerpoint Ppt Template Bundles Intensify your message with the right graphics, images, icons, etc. presented in this complete deck. This PPT template is a great starting point to convey your messages and build a good collaboration. The Twenty slides added to this PowerPoint slideshow helps you present a thorough explanation of the topic. You can use it to study and present various kinds of information in the form of stats, figures, data charts, and many more. This Cyber Security Policy Powerpoint Ppt Template Bundles PPT slideshow is available for use in standard and widescreen aspects ratios. So, you can use it as per your convenience. Apart from this, it can be downloaded in PNG, JPG, and PDF formats, all completely editable and modifiable. The most profound feature of this PPT design is that it is fully compatible with Google Slides making it suitable for every industry and business domain.
-
 Information Security Policy In Cybersecurity Training Ppt
Information Security Policy In Cybersecurity Training PptPresenting Information Security Policy in Cybersecurity. This PPT presentation is meticulously researched and each slide consists of relevant content. Designed by SlideTeams PowerPoint experts, this PPT is fully customizable alter the colors, text, icons, and font size to meet your requirements. Compatible with Google Slides and backed by excellent customer support. Download to present with poise and assurance.
-
 Acceptable Use Policy In Cybersecurity Training Ppt
Acceptable Use Policy In Cybersecurity Training PptPresenting Acceptable Use Policy in Cybersecurity. This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizable alter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
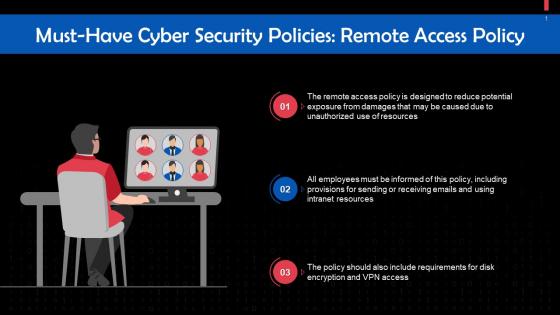 Remote Access Policy In Cybersecurity Training Ppt
Remote Access Policy In Cybersecurity Training PptPresenting Remote Access Policy in Cybersecurity. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. It is well crafted and designed by our PowerPoint specialists. Suitable for use by managers, employees, and organizations. You can edit the color, text, icon, and font size to suit your requirements. The PPT also supports Google Slides. Even Premium Customer Support is also available. Download now and present with confidence.
-
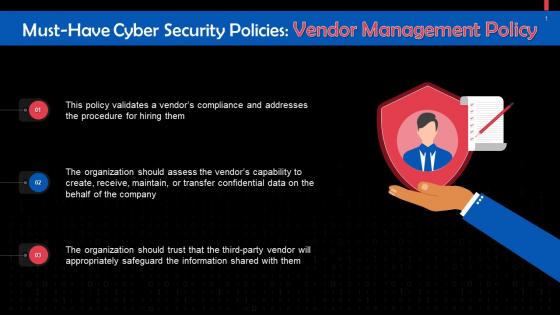 Vendor Management Policy In Cybersecurity Training Ppt
Vendor Management Policy In Cybersecurity Training PptPresenting Vendor Management Policy in Cybersecurity. This PPT presentation is meticulously researched and each slide consists of relevant content. Designed by SlideTeams PowerPoint experts, this PPT is fully customizable alter the colors, text, icons, and font size to meet your requirements. Compatible with Google Slides and backed by excellent customer support. Download to present with poise and assurance.
-
 Data Retention Policy In Cybersecurity Training Ppt
Data Retention Policy In Cybersecurity Training PptPresenting Data Retention Policy in Cybersecurity. This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizable alter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
 Clean Desk Policy In Cybersecurity Training Ppt
Clean Desk Policy In Cybersecurity Training PptPresenting Clean Desk Policy in Cybersecurity. This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizable alter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
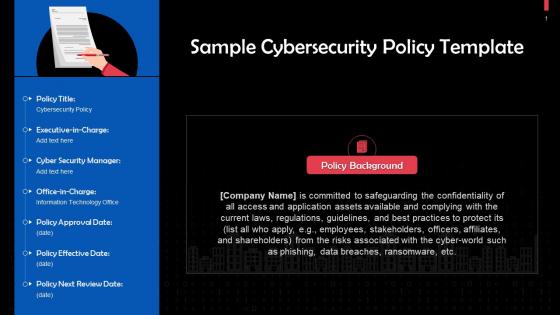 Sample Cyber Security Policy Template Training Ppt
Sample Cyber Security Policy Template Training PptPresenting Sample Cyber Security Policy Template. This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizable alter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
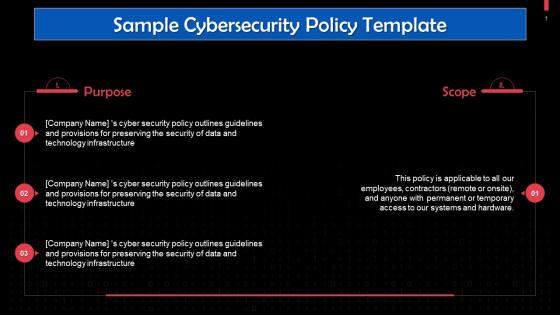 Purpose And Scope Of A Sample Cybersecurity Policy Template Training Ppt
Purpose And Scope Of A Sample Cybersecurity Policy Template Training PptPresenting Purpose and Scope of a Sample Cybersecurity Policy Template. This PPT presentation is meticulously researched and each slide consists of relevant content. Designed by SlideTeams PowerPoint experts, this PPT is fully customizable alter the colors, text, icons, and font size to meet your requirements. Compatible with Google Slides and backed by excellent customer support. Download to present with poise and assurance.
-
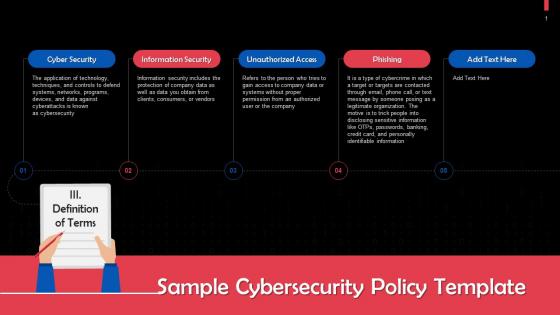 Important Definitions In A Sample Cybersecurity Policy Template Training Ppt
Important Definitions In A Sample Cybersecurity Policy Template Training PptPresenting Important Definitions in a Sample Cybersecurity Policy Template. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. It is well crafted and designed by our PowerPoint specialists. Suitable for use by managers, employees, and organizations. You can edit the color, text, icon, and font size to suit your requirements. The PPT also supports Google Slides. Even Premium Customer Support is also available. Download now and present with confidence.
-
 Training And Awareness About Cybersecurity Policy Training Ppt
Training And Awareness About Cybersecurity Policy Training PptPresenting Training and Awareness about Cybersecurity Policy. This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizable alter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
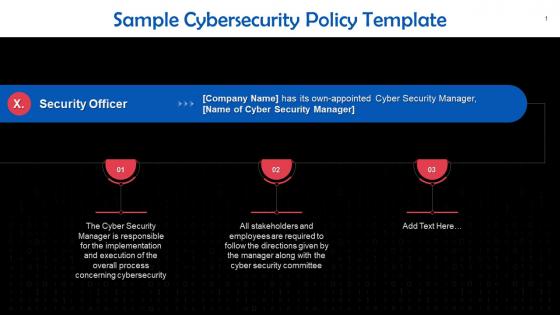 Security Officer Profile In Sample Cybersecurity Policy Template Training Ppt
Security Officer Profile In Sample Cybersecurity Policy Template Training PptPresenting Security Officer Profile in Sample Cybersecurity Policy Template. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. It is well crafted and designed by our PowerPoint specialists. Suitable for use by managers, employees, and organizations. You can edit the color, text, icon, and font size to suit your requirements. The PPT also supports Google Slides. Even Premium Customer Support is also available. Download now and present with confidence.
-
 Policy Review Section In Sample Cybersecurity Policy Template Training Ppt
Policy Review Section In Sample Cybersecurity Policy Template Training PptPresenting Policy Review Section in Sample Cybersecurity Policy Template. This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizable alter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
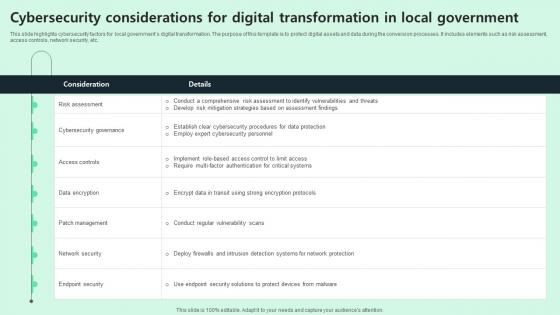 Cybersecurity Considerations For Digital Transformation In Local Government
Cybersecurity Considerations For Digital Transformation In Local GovernmentThis slide highlights cybersecurity factors for local governments digital transformation. The purpose of this template is to protect digital assets and data during the conversion processes. It includes elements such as risk assessment, access controls, network security, etc.Presenting our well structured Cybersecurity Considerations For Digital Transformation In Local Government. The topics discussed in this slide are Cybersecurity Governance, Access Controls, Patch Management. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Business Owners Policy Insurance Cyber Liability In Powerpoint And Google Slides Cpb
Business Owners Policy Insurance Cyber Liability In Powerpoint And Google Slides CpbPresenting our Business Owners Policy Insurance Cyber Liability In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Business Owners Policy Insurance Cyber Liability This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Cyber Attacks Government In Powerpoint And Google Slides Cpb
Cyber Attacks Government In Powerpoint And Google Slides CpbPresenting our Cyber Attacks Government In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Cyber Attacks Government This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Cybersecurity Risk Trends For Security Policy Development
Cybersecurity Risk Trends For Security Policy DevelopmentThis slide highlights cybersecurity risk trends for enhancing organization security ensuring digital operations resilience. It includes developments such as attack surface expansion, identify system defense, digital supply chain risk, etc. Presenting our well structured Cybersecurity Risk Trends For Security Policy Development. The topics discussed in this slide are Attack Surface Expansion, Identify System Defense, Digital Supply Chain Risk. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Big Data Governance Icon For Cyber Security
Big Data Governance Icon For Cyber SecurityIntroducing our premium set of slides with Big Data Governance Icon For Cyber Security. Ellicudate the Three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Big Data Governance Icon, Cyber Security. So download instantly and tailor it with your information.
-
 Cyber Security Policy Icon For Data Theft Prevention
Cyber Security Policy Icon For Data Theft PreventionIntroducing our Cyber Security Policy Icon For Data Theft Prevention set of slides. The topics discussed in these slides are Cyber Security Policy, Icon For Data Theft Prevention. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Cyber Security Policy Icon For Securing Digital Assets
Cyber Security Policy Icon For Securing Digital AssetsPresenting our set of slides with Cyber Security Policy Icon For Securing Digital Assets This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cyber Security Policy Icon, Securing Digital Assets
-
 Global Cyber Security Policy Components
Global Cyber Security Policy ComponentsThis slide covers the key components of a National Cyber Security Strategy NCSS. The purpose of this template is to provide a succinct overview of the main pillars of the NCSS including strengthening the regulatory framework, promoting research and development, etc. Introducing our premium set of slides with Global Cyber Security Policy Components Ellicudate the Seven stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Regulatory Framework, Encourage Open Standards, Assurance Framework. So download instantly and tailor it with your information.
-
 Global Cyber Security Policy Icon
Global Cyber Security Policy IconPresenting our set of slides with Global Cyber Security Policy Icon This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Global Cyber Security Policy Icon
-
 Impact Of Cyber Security Threats On Organisational Policy
Impact Of Cyber Security Threats On Organisational PolicyThis slide covers the negative impacts of prevalent cybersecurity threats. This template aims to highlight two key negative impacts of threats, including DNS Attacks, SQL Injection, Malware, Phishing, and Ransomware. Presenting our set of slides with Impact Of Cyber Security Threats On Organisational Policy This exhibits information on Six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Malware, DNS Attack, SQL Injection
-
 Importance Of Cyber Security Policy For IT Organisation
Importance Of Cyber Security Policy For IT OrganisationThis slide covers the essential importance of a cybersecurity policy for IT organizations. The purpose of this template is to emphasize the role of a cybersecurity policy in safeguarding sensitive data, preventing cyber threats, ensuring regulatory adherence, and maintaining uninterrupted business operations. Introducing our premium set of slides with Importance Of Cyber Security Policy For IT Organisation Ellicudate the Four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Data Protection, Threat Mitigation, Regulatory Compliance. So download instantly and tailor it with your information.
-
 Key Elements Of Cyber Security Policy
Key Elements Of Cyber Security PolicyThis slide covers the key elements of an effective security policy. The purpose of this template is to provide a concise overview of the essential components, emphasizing the need for a clear purpose and objectives, defining scope and applicability, etc. Presenting our set of slides with Key Elements Of Cyber Security Policy This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Clear Objectives, Scope And Applicability
-
 Key Factors For Updating Cyber Security Policy
Key Factors For Updating Cyber Security PolicyThis slide covers key reasons for updating cybersecurity policies. The purpose of this template is to serve as a quick reference for stakeholders, outlining the pivotal circumstances that necessitate policy revisions. It includes regulatory changes, technology upgrades, security incidents, and organizational shifts. Introducing our premium set of slides with Key Factors For Updating Cyber Security Policy Ellicudate the Four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Regulatory Changes, Technology Upgrades, Security Incidents. So download instantly and tailor it with your information.
-
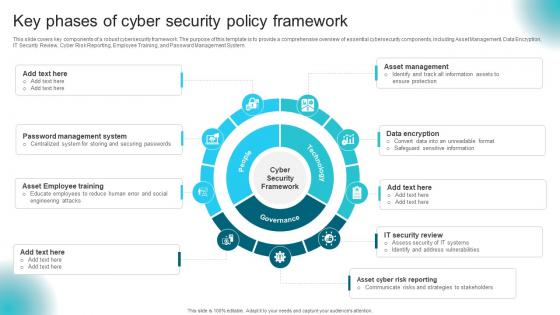 Key Phases Of Cyber Security Policy Framework
Key Phases Of Cyber Security Policy FrameworkThis slide covers key components of a robust cybersecurity framework. The purpose of this template is to provide a comprehensive overview of essential cybersecurity components, including Asset Management, Data Encryption, IT Security Review, Cyber Risk Reporting, Employee Training, and Password Management System. Presenting our set of slides with Key Phases Of Cyber Security Policy Framework This exhibits information on Eight stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cyber Security Framework, Data Encryption
-
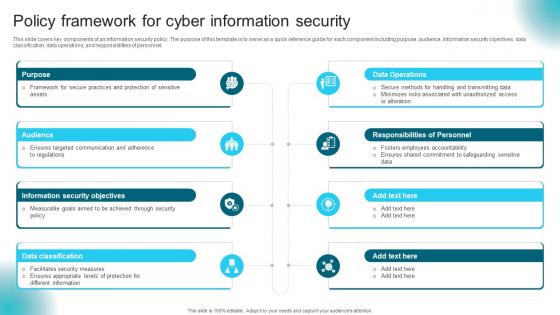 Policy Framework For Cyber Information Security
Policy Framework For Cyber Information SecurityThis slide covers key components of an information security policy. The purpose of this template is to serve as a quick reference guide for each component including purpose, audience, information security objectives, data classification, data operations, and responsibilities of personnel. Presenting our set of slides with Policy Framework For Cyber Information Security This exhibits information on Eight stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Purpose, Audience, Information Security Objectives
-
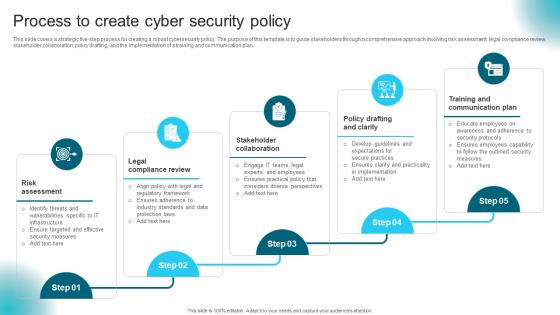 Process To Create Cyber Security Policy
Process To Create Cyber Security PolicyIntroducing our premium set of slides with Process To Create Cyber Security Policy Ellicudate the Five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Risk Assessment, Legal Compliance Review, Stakeholder Collaboration. So download instantly and tailor it with your information.
-
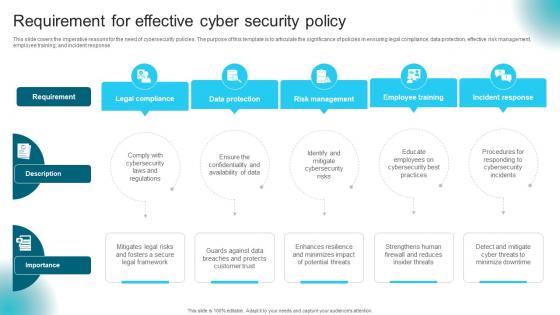 Requirement For Effective Cyber Security Policy
Requirement For Effective Cyber Security PolicyThis slide covers the imperative reasons for the need of cybersecurity policies. The purpose of this template is to articulate the significance of policies in ensuring legal compliance, data protection, effective risk management, employee training, and incident response. Presenting our set of slides with Requirement For Effective Cyber Security Policy This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Legal Compliance, Data Protection, Risk Management
-
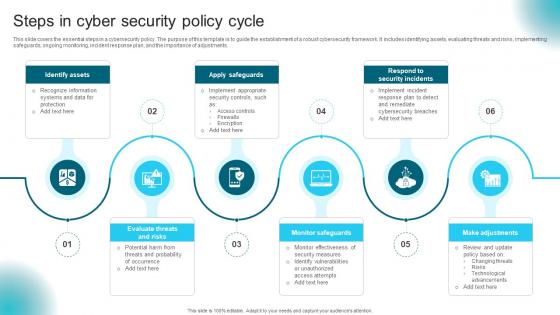 Steps In Cyber Security Policy Cycle
Steps In Cyber Security Policy CycleThis slide covers the essential steps in a cybersecurity policy. The purpose of this template is to guide the establishment of a robust cybersecurity framework. It includes identifying assets, evaluating threats and risks, implementing safeguards, ongoing monitoring, incident response plan, and the importance of adjustments. Presenting our set of slides with Steps In Cyber Security Policy Cycle This exhibits information on Six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Identify Assets, Apply Safeguards, Monitor Safeguards
-
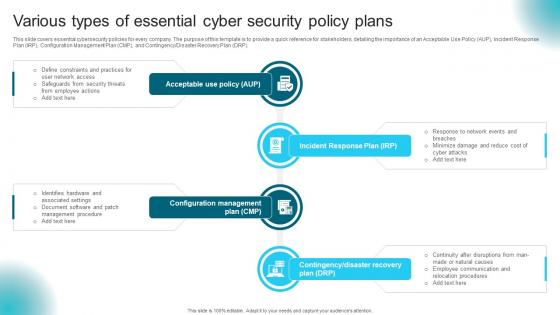 Various Types Of Essential Cyber Security Policy Plans
Various Types Of Essential Cyber Security Policy PlansThis slide covers essential cybersecurity policies for every company. The purpose of this template is to provide a quick reference for stakeholders, detailing the importance of an Acceptable Use Policy AUP, Incident Response Plan IRP, Configuration Management Plan CMP, and ContingencyDisaster Recovery Plan DRP. Introducing our premium set of slides with Various Types Of Essential Cyber Security Policy Plans Ellicudate the Six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Incident Response Plan, Configuration Management, Acceptable Use Policy. So download instantly and tailor it with your information.
-
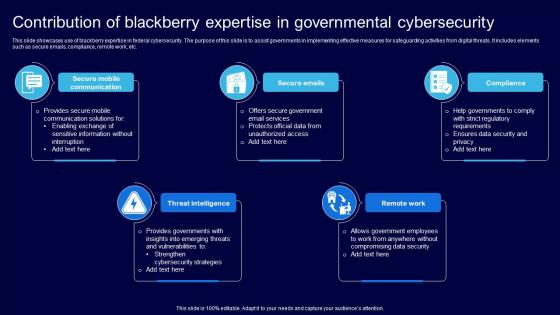 Contribution Of Blackberry Expertise In Governmental Cybersecurity
Contribution Of Blackberry Expertise In Governmental CybersecurityThis slide showcases use of blackberry expertise in federal cybersecurity. The purpose of this slide is to assist governments in implementing effective measures for safeguarding activities from digital threats. It includes elements such as secure emails, compliance, remote work, etc. Presenting our set of slides with Contribution Of Blackberry Expertise In Governmental Cybersecurity. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Communication, Secure, Compliance.
-
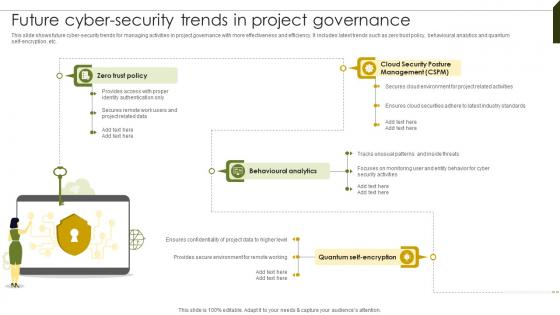 Future Cyber Security Trends Implementing Project Governance Framework For Quality PM SS
Future Cyber Security Trends Implementing Project Governance Framework For Quality PM SSThis slide shows future cyber-security trends for managing activities in project governance with more effectiveness and efficiency. It includes latest trends such as zero trust policy, behavioural analytics and quantum self-encryption, etc. Present the topic in a bit more detail with this Future Cyber Security Trends Implementing Project Governance Framework For Quality PM SS. Use it as a tool for discussion and navigation on Cloud Security, Behavioural Analytics, Trust Policy. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Framework For SCADA Cyber Security Policy
Framework For SCADA Cyber Security PolicyThis slide represents framework of various policies that assist IT companies to optimize their SCADA cyber security for effective data protection. It includes policies related to data security, platform security, communication security, audit, etc. Introducing our Framework For SCADA Cyber Security Policy set of slides. The topics discussed in these slides are System Security Program, Cyber Security Policy This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
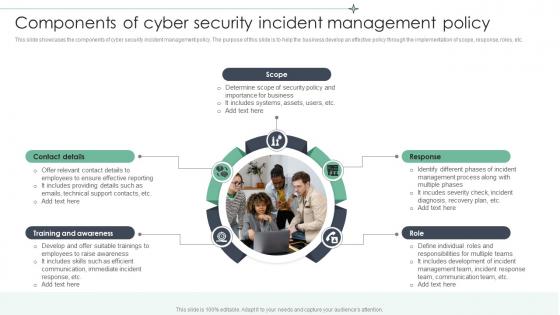 Components Of Cyber Security Incident Management Policy
Components Of Cyber Security Incident Management PolicyThis slide showcases the components of cyber security incident management policy. The purpose of this slide is to help the business develop an effective policy through the implementation of scope, response, roles, etc. Presenting our set of slides with Components Of Cyber Security Incident Management Policy. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Contact Details, Training And Awareness, Includes Systems.
-
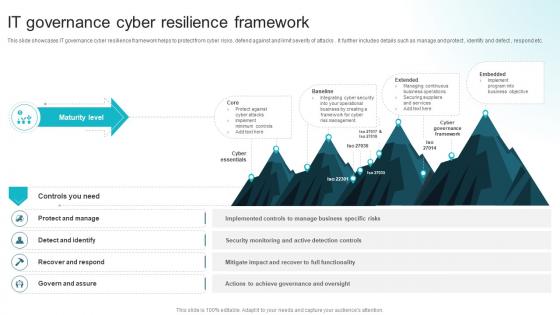 IT Governance Cyber Resilience Framework
IT Governance Cyber Resilience FrameworkThis slide showcases IT governance cyber resilience framework helps to protect from cyber risks, defend against and limit severity of attacks . It further includes details such as manage and protect , identify and defect , respond etc. Introducing our IT Governance Cyber Resilience Framework set of slides. The topics discussed in these slides are Protect And Manage, Detect And Identify, Recover And Respond, Govern And Assure. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
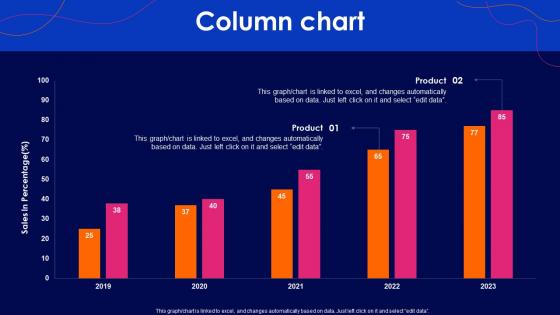 Cyber Security Policy Column Chart Ppt Show Graphics Tutorials
Cyber Security Policy Column Chart Ppt Show Graphics TutorialsDeliver an outstanding presentation on the topic using this Cyber Security Policy Column Chart Ppt Show Graphics Tutorials. Dispense information and present a thorough explanation of Column Chart using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Table Of Contents Cyber Security Policy Ppt Professional Graphics Pictures
Table Of Contents Cyber Security Policy Ppt Professional Graphics PicturesIntroducing Table Of Contents Cyber Security Policy Ppt Professional Graphics Pictures to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Information, Importance, Introduction, using this template. Grab it now to reap its full benefits.
-
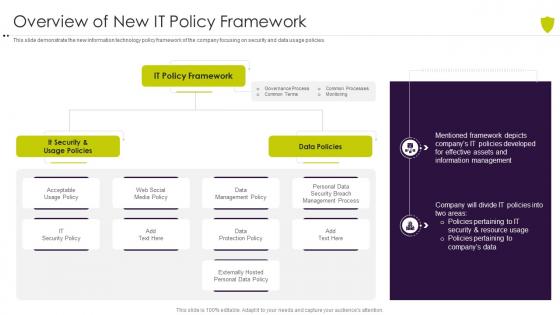 Overview of new it policy framework managing cyber risk in a digital age
Overview of new it policy framework managing cyber risk in a digital ageThis slide demonstrate the new information technology policy framework of the company focusing on security and data usage policies. Present the topic in a bit more detail with this Overview Of New It Policy Framework Managing Cyber Risk In A Digital Age. Use it as a tool for discussion and navigation on Overview Of New IT Policy Framework. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
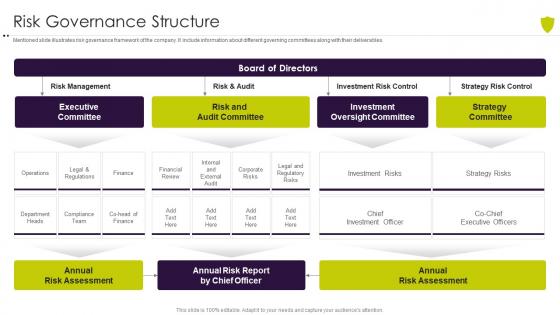 Risk governance structure managing cyber risk in a digital age
Risk governance structure managing cyber risk in a digital ageMentioned slide illustrates risk governance framework of the company. It include information about different governing committees along with their deliverables. Present the topic in a bit more detail with this Risk Governance Structure Managing Cyber Risk In A Digital Age. Use it as a tool for discussion and navigation on Risk Governance Structure. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
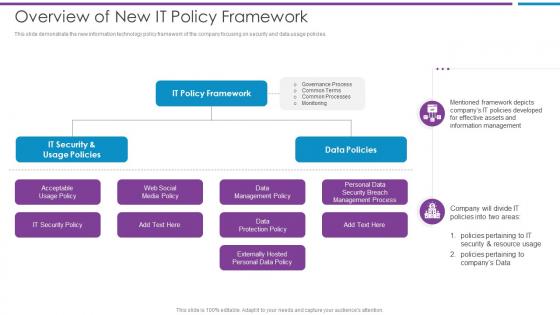 Overview Of New It Policy Framework Risk Based Methodology To Cyber
Overview Of New It Policy Framework Risk Based Methodology To CyberThis slide demonstrate the new information technology policy framework of the company focusing on security and data usage policies.Introducing Overview Of New It Policy Framework Risk Based Methodology To Cyber to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Acceptable Usage Policy, Data Policies, Data Management Policy using this template. Grab it now to reap its full benefits.
-
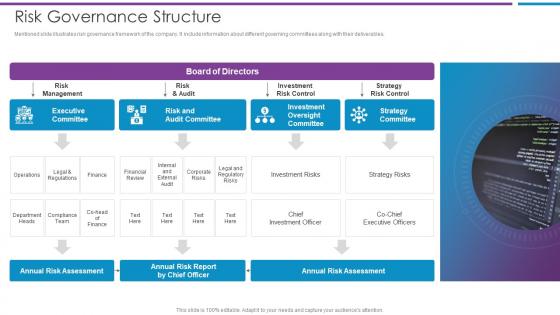 Risk Governance Structure Risk Based Methodology To Cyber
Risk Governance Structure Risk Based Methodology To CyberMentioned slide illustrates risk governance framework of the company. It include information about different governing committees along with their deliverables.Deliver an outstanding presentation on the topic using this Risk Governance Structure Risk Based Methodology To Cyber Dispense information and present a thorough explanation of Executive Committee, Risk And Audit Committee, Investment Oversight Committee using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
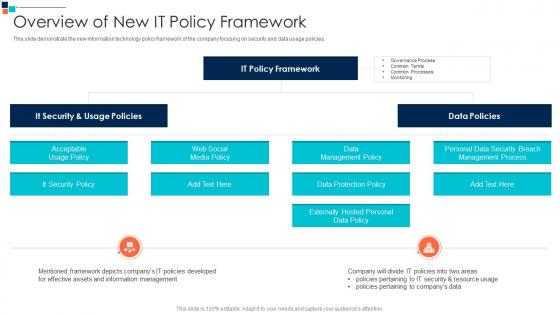 Overview Of New It Policy Framework Introducing A Risk Based Approach To Cyber Security
Overview Of New It Policy Framework Introducing A Risk Based Approach To Cyber SecurityThis slide demonstrate the new information technology policy framework of the company focusing on security and data usage policies.Deliver an outstanding presentation on the topic using this Overview Of New It Policy Framework Introducing A Risk Based Approach To Cyber Security Dispense information and present a thorough explanation of Data Management Policy, Data Protection Policy, Externally Hosted Personal using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
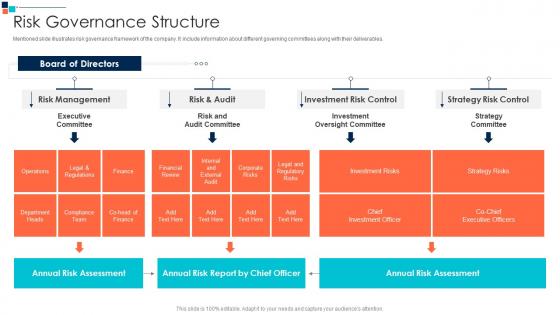 Risk Governance Structure Introducing A Risk Based Approach To Cyber Security
Risk Governance Structure Introducing A Risk Based Approach To Cyber SecurityMentioned slide illustrates risk governance framework of the company. It include information about different governing committees along with their deliverables.Deliver an outstanding presentation on the topic using this Risk Governance Structure Introducing A Risk Based Approach To Cyber Security Dispense information and present a thorough explanation of Legal And Regulatory Risks, Annual Risk Assessment, Investment Risks using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
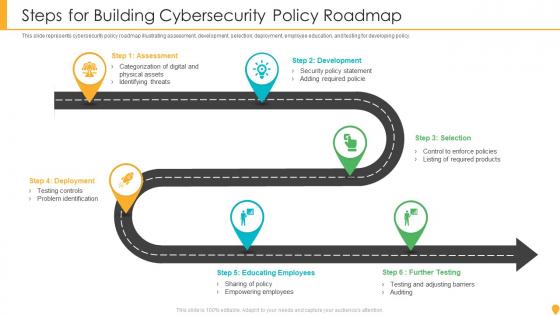 Steps For Building Cybersecurity Policy Roadmap
Steps For Building Cybersecurity Policy RoadmapThis slide represents cybersecurity policy roadmap illustrating assessment, development, selection, deployment, employee education, and testing for developing policy. Introducing our premium set of slides with Steps For Building Cybersecurity Policy Roadmap. Elucidate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Development, Assessment, Deployment, Selection, Educating Employees. So download instantly and tailor it with your information.
-
 Cyber Policy Ppt Powerpoint Presentation Pictures Templates Cpb
Cyber Policy Ppt Powerpoint Presentation Pictures Templates CpbPresenting Cyber Policy Ppt Powerpoint Presentation Pictures Templates Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like NAMEEEEE. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
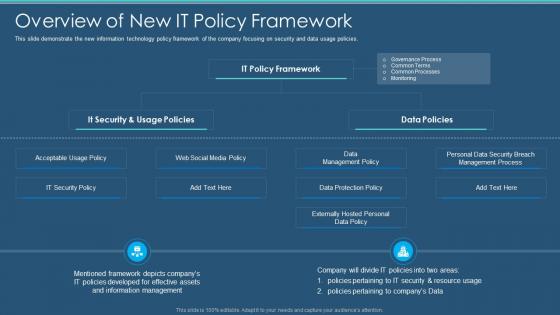 Information Security Program Cybersecurity Overview Of New It Policy Framework
Information Security Program Cybersecurity Overview Of New It Policy FrameworkThis slide demonstrate the new information technology policy framework of the company focusing on security and data usage policies. Present the topic in a bit more detail with this Information Security Program Cybersecurity Overview Of New It Policy Framework. Use it as a tool for discussion and navigation on Information, Management, Framework. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
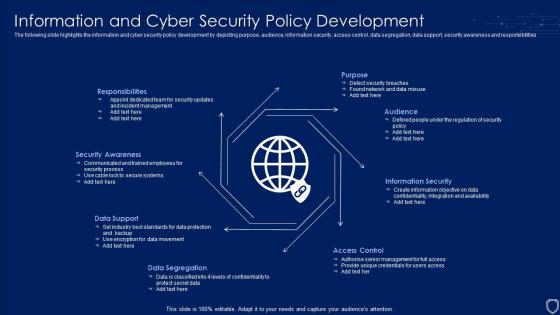 Information And Cyber Security Policy Development
Information And Cyber Security Policy DevelopmentThe following slide highlights the information and cyber security policy development by depicting purpose, audience, information security, access control, data segregation, data support, security awareness and responsibilities. Introducing our premium set of slides with name Information And Cyber Security Policy Development. Ellicudate the eight stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Security Awareness, Responsibilities, Information Security, Data Segregation. So download instantly and tailor it with your information.
-
 Roadmap Of Cyber Security Asset Assessment And Security Policy Development
Roadmap Of Cyber Security Asset Assessment And Security Policy DevelopmentThe following slide highlights the roadmap of cyber security asset assessment and security policy development for organisation to draft system security policy which describes assessment, build, select, deployment, awareness and audit. Presenting our set of slides with name Roadmap Of Cyber Security Asset Assessment And Security Policy Development. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Audit, Awareness, Assessment, Build, Deployment.
-
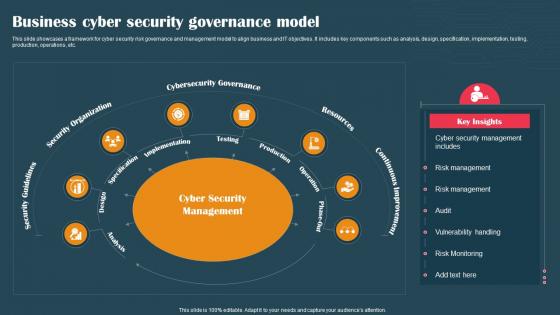 Business Cyber Security Governance Model
Business Cyber Security Governance ModelThis slide showcases a framework for cyber security risk governance and management model to align business and IT objectives. It includes key components such as analysis, design, specification, implementation, testing, production, operations, etc. Presenting our set of slides with Business Cyber Security Governance Model. This exhibits information on eight stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Security Organization, Resources, Cybersecurity Governance.
-
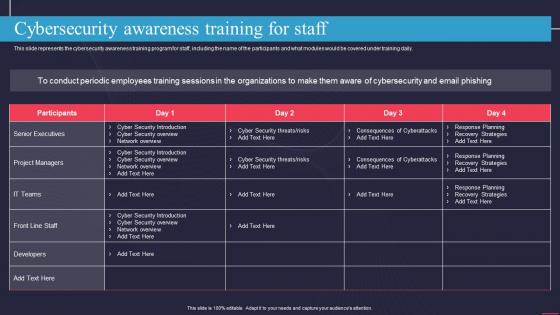 Cybersecurity Awareness Training For Staff Information Technology Policy
Cybersecurity Awareness Training For Staff Information Technology PolicyThis slide represents the cybersecurity awareness training program for staff, including the name of the participants and what modules would be covered under training daily. Present the topic in a bit more detail with this Cybersecurity Awareness Training For Staff Information Technology Policy. Use it as a tool for discussion and navigation on Senior Executives, Project Managers, IT Teams. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
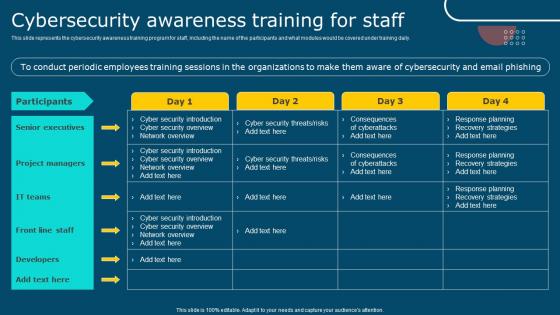 IT Policy Cybersecurity Awareness Training For Staff Ppt Infographics
IT Policy Cybersecurity Awareness Training For Staff Ppt InfographicsThis slide represents the cybersecurity awareness training program for staff, including the name of the participants and what modules would be covered under training daily. Present the topic in a bit more detail with this IT Policy Cybersecurity Awareness Training For Staff Ppt Infographics. Use it as a tool for discussion and navigation on Participants, Senior Executives, Project Managers, Front Line Staff. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Agenda Cyber Security Policy Ppt Slides Background Images
Agenda Cyber Security Policy Ppt Slides Background ImagesIntroducing Agenda Cyber Security Policy Ppt Slides Background Images to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Information, Technology, Implementation, using this template. Grab it now to reap its full benefits.
-
 Cyber Security Policy About Us Ppt Slides Infographic Template
Cyber Security Policy About Us Ppt Slides Infographic TemplateIncrease audience engagement and knowledge by dispensing information using Cyber Security Policy About Us Ppt Slides Infographic Template. This template helps you present information on three stages. You can also present information on About Us using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyber Security Policy Acceptable Use Of Equipment Policy Overview
Cyber Security Policy Acceptable Use Of Equipment Policy OverviewThis slide outlines the acceptable use policy, and it includes how official computers should be used, risks associated with improper usage, and appropriate behavior while handling sensitive information. Introducing Cyber Security Policy Acceptable Use Of Equipment Policy Overview to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Overview, Consumers, Information, using this template. Grab it now to reap its full benefits.
-
 Cyber Security Policy Access Authorization Modification And Identity Access Management
Cyber Security Policy Access Authorization Modification And Identity Access ManagementThis slide represents the access authorization, modification, and identity access management based on polp, including the departments involved in creating this policy, such as HR and IT. Increase audience engagement and knowledge by dispensing information using Cyber Security Policy Access Authorization Modification And Identity Access Management. This template helps you present information on seven stages. You can also present information on Management, Authorization, Modification using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyber Security Policy Bring Your Own Device Byod Policy Objective And Scope
Cyber Security Policy Bring Your Own Device Byod Policy Objective And ScopeThis slide represents the bring your own device policy, including its objective and scope. It also includes the types of devices used in BYOD policy, which comprises cellphones, smartphones, tablets, laptops, and PCs. Present the topic in a bit more detail with this Cyber Security Policy Bring Your Own Device Byod Policy Objective And Scope. Use it as a tool for discussion and navigation on Technological, Compatibility, Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Security Policy Byod Lost Stolen Hacked Or Damaged Equipment
Cyber Security Policy Byod Lost Stolen Hacked Or Damaged EquipmentThis slide describes the scenarios of lost, stolen, hacked, or damaged personal equipment under BYOD policy. It also includes that remote wipe software should be installed on employees devices to remove the work data remotely in case of theft. Introducing Cyber Security Policy Byod Lost Stolen Hacked Or Damaged Equipment to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Equipment, Information, Department, using this template. Grab it now to reap its full benefits.


