Powerpoint Templates and Google slides for Methodology Risk
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Risk Based Methodology To Cyber And Information Security Powerpoint Presentation Slides
Risk Based Methodology To Cyber And Information Security Powerpoint Presentation SlidesDeliver this complete deck to your team members and other collaborators. Encompassed with stylized slides presenting various concepts, this Risk Based Methodology To Cyber And Information Security Powerpoint Presentation Slides is the best tool you can utilize. Personalize its content and graphics to make it unique and thought provoking. All the fifty four slides are editable and modifiable, so feel free to adjust them to your business setting. The font, color, and other components also come in an editable format making this PPT design the best choice for your next presentation. So, download now.
-
 Risk Assessment Measures Evaluation Methodology Analyze Management Process
Risk Assessment Measures Evaluation Methodology Analyze Management ProcessThis complete presentation has PPT slides on wide range of topics highlighting the core areas of your business needs. It has professionally designed templates with relevant visuals and subject driven content. This presentation deck has total of eleven slides. Get access to the customizable templates. Our designers have created editable templates for your convenience. You can edit the colour, text and font size as per your need. You can add or delete the content if required. You are just a click to away to have this ready-made presentation. Click the download button now.
-
 Project Management Guide Other Methodologies Used Mitigate Risk And Manage Projects PM SS
Project Management Guide Other Methodologies Used Mitigate Risk And Manage Projects PM SSFollowing slide showcases PRINCE2 and PRiSM methods used to mitigate risk and reduce environmental impact. They also help in resource allocation and green project management. Increase audience engagement and knowledge by dispensing information using Project Management Guide Other Methodologies Used Mitigate Risk And Manage Projects PM SS. This template helps you present information on four stages. You can also present information on Green Project Management, Ensures Greater Control, Assists In Resource Allocation, Business Justification using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
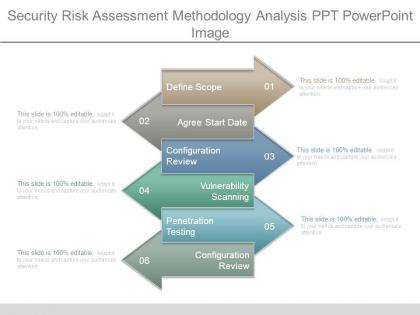 Security risk assessment methodology analysis ppt powerpoint image
Security risk assessment methodology analysis ppt powerpoint imagePresenting security risk assessment methodology analysis ppt powerpoint image. This is a security risk assessment methodology analysis ppt powerpoint image. This is a six stage process. The stages in this process are define scope, agree start date, configuration review, vulnerability scanning, penetration testing, configuration review.
-
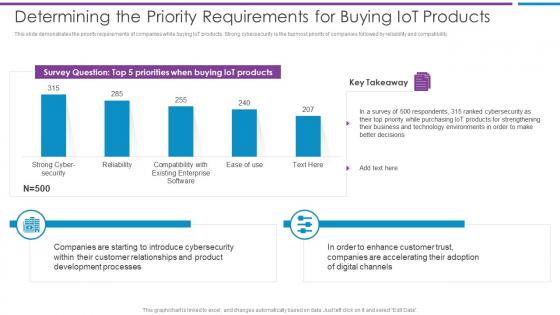 Determining The Priority Requirements For Buying Iot Products Risk Based Methodology To Cyber
Determining The Priority Requirements For Buying Iot Products Risk Based Methodology To CyberThis slide demonstrates the priority requirements of companies while buying IoT products. Strong cybersecurity is the topmost priority of companies followed by reliability and compatibility.Deliver an outstanding presentation on the topic using this Determining The Priority Requirements For Buying Iot Products Risk Based Methodology To Cyber Dispense information and present a thorough explanation of Companies Are Starting, Customer Relationships, Development Processes using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
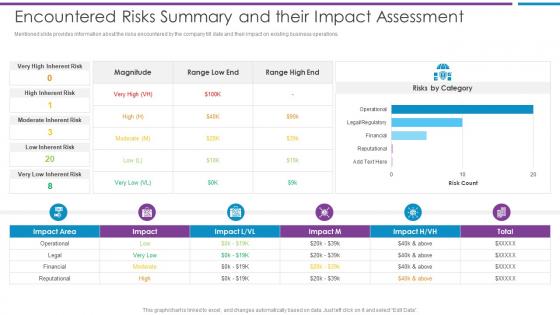 Encountered Risks Summary And Their Impact Assessment Risk Based Methodology To Cyber
Encountered Risks Summary And Their Impact Assessment Risk Based Methodology To CyberMentioned slide provides information about the risks encountered by the company till date and their impact on existing business operations.Present the topic in a bit more detail with this Encountered Risks Summary And Their Impact Assessment Risk Based Methodology To Cyber Use it as a tool for discussion and navigation on Encountered Risks Summary And Their Impact Assessment This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Global Market Insights Cyber Security Risk Based Methodology To Cyber
Global Market Insights Cyber Security Risk Based Methodology To CyberFollowing slide illustrates the global market insights of cybersecurity covering statistics related to integrated risk management, investment in cybersecurity and digital transformation.Present the topic in a bit more detail with this Global Market Insights Cyber Security Risk Based Methodology To Cyber Use it as a tool for discussion and navigation on Global Market Insights-Cybersecurity This template is free to edit as deemed fit for your organization. Therefore download it now.
-
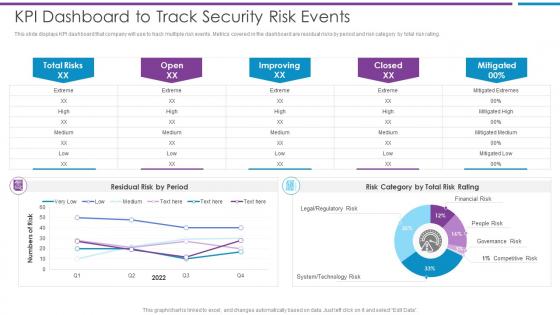 KPI Dashboard To Track Security Risk Events Risk Based Methodology To Cyber
KPI Dashboard To Track Security Risk Events Risk Based Methodology To CyberThis slide displays KPI dashboard that company will use to track multiple risk events. Metrics covered in the dashboard are residual risks by period and risk category by total risk rating.Deliver an outstanding presentation on the topic using this KPI Dashboard To Track Security Risk Events Risk Based Methodology To Cyber Dispense information and present a thorough explanation of KPI Dashboard To Track Security Risk Events using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
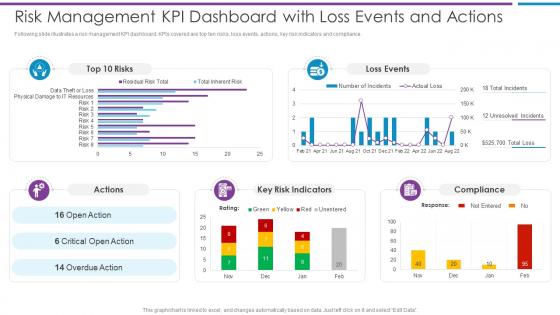 Risk Management KPI Dashboard With Risk Based Methodology To Cyber
Risk Management KPI Dashboard With Risk Based Methodology To CyberFollowing slide illustrates a risk management KPI dashboard. KPIs covered are top ten risks, loss events, actions, key risk indicators and compliance.Present the topic in a bit more detail with this Risk Management KPI Dashboard With Risk Based Methodology To Cyber Use it as a tool for discussion and navigation on Risk Management KPI Dashboard With Loss Events And Actions This template is free to edit as deemed fit for your organization. Therefore download it now.
-
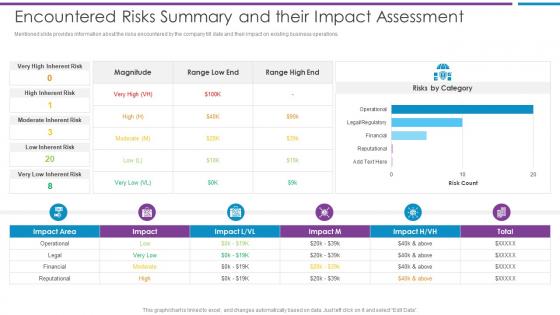 Risk Based Methodology To Cyber Encountered Risks Summary And Their Impact Assessment
Risk Based Methodology To Cyber Encountered Risks Summary And Their Impact AssessmentMentioned slide provides information about the risks encountered by the company till date and their impact on existing business operations.Present the topic in a bit more detail with thisRisk Based Methodology To Cyber Encountered Risks Summary And Their Impact Assessment Use it as a tool for discussion and navigation on Encountered Risks Summary And Their Impact Assessment This template is free to edit as deemed fit for your organization. Therefore download it now.
-
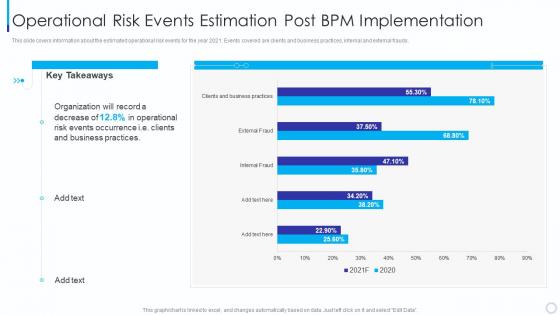 Operational Risk Events Introducing Business Process Management Methodology
Operational Risk Events Introducing Business Process Management MethodologyThis slide covers information about the estimated operational risk events for the year 2021. Events covered are clients and business practices, internal and external frauds. Present the topic in a bit more detail with this Operational Risk Events Introducing Business Process Management Methodology. Use it as a tool for discussion and navigation on Operational Risk Events Estimation Post Bpm Implementation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
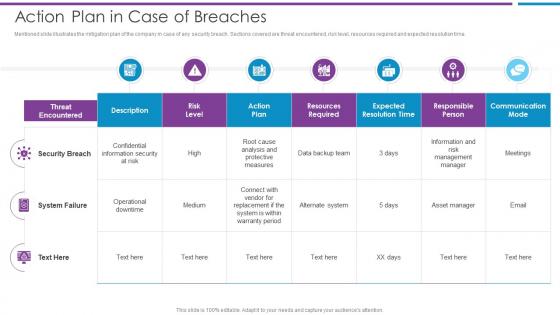 Action Plan In Case Of Breaches Risk Based Methodology To Cyber
Action Plan In Case Of Breaches Risk Based Methodology To CyberMentioned slide illustrates the mitigation plan of the company in case of any security breach. Sections covered are threat encountered, risk level, resources required and expected resolution time.Present the topic in a bit more detail with this Action Plan In Case Of Breaches Risk Based Methodology To Cyber Use it as a tool for discussion and navigation on Security Breach, Confidential Information, Resources Required This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Addressing The Companies Digitization Levelsby Sectors Risk Based Methodology To Cyber
Addressing The Companies Digitization Levelsby Sectors Risk Based Methodology To CyberMentioned slide provides information about the companys digitalization levels by sectors. Digitalization level is measured based on asset, usage and labor.Deliver an outstanding presentation on the topic using this Addressing The Companies Digitization Levelsby Sectors Risk Based Methodology To Cyber Dispense information and present a thorough explanation of Business Processes, Digital Spend On Workers, Digitalization Of Work using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Agenda Of Risk Based Methodology To Cyberand Information Security
Agenda Of Risk Based Methodology To Cyberand Information SecurityPresent the topic in a bit more detail with this Agenda Of Risk Based Methodology To Cyberand Information Security. Use it as a tool for discussion and navigation on Agenda. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
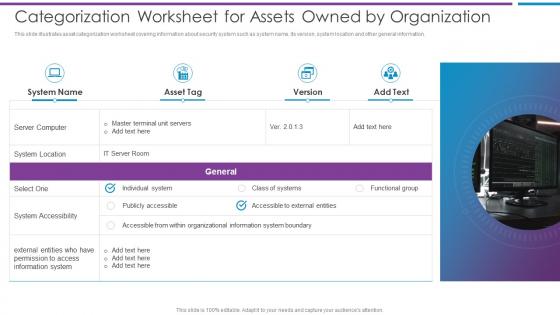 Categorization Worksheet For Assets Owned By Organization Risk Based Methodology To Cyber
Categorization Worksheet For Assets Owned By Organization Risk Based Methodology To CyberThis slide illustrates asset categorization worksheet covering information about security system such as system name, its version, system location and other general information.Introducing Categorization Worksheet For Assets Owned By Organization Risk Based Methodology To Cyber to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on System Accessibility, Individual System, Organizational Information using this template. Grab it now to reap its full benefits.
-
 Checklist For Effectively Managing Asset Security Risk Based Methodology To Cyber
Checklist For Effectively Managing Asset Security Risk Based Methodology To CyberFollowing slide displays system management checklist that company will use for effectively managing asset security. It also includes system management activities and frequency of performing them.Increase audience engagement and knowledge by dispensing information using Checklist For Effectively Managing Asset Security Risk Based Methodology To Cyber This template helps you present information on one stage. You can also present information on System Monitoring, Data Backup, Security Patches using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
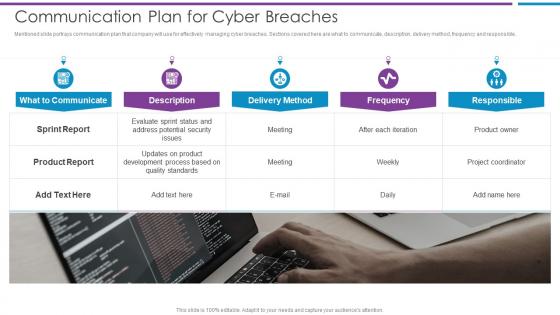 Communication Plan For Cyberbreaches Risk Based Methodology To Cyber
Communication Plan For Cyberbreaches Risk Based Methodology To CyberMentioned slide portrays communication plan that company will use for effectively managing cyber breaches. Sections covered here are what to communicate, description, delivery method, frequency and responsible.Introducing Communication Plan For Cyberbreaches Risk Based Methodology To Cyber to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Address Potential Security, Development Process, Quality Standards using this template. Grab it now to reap its full benefits.
-
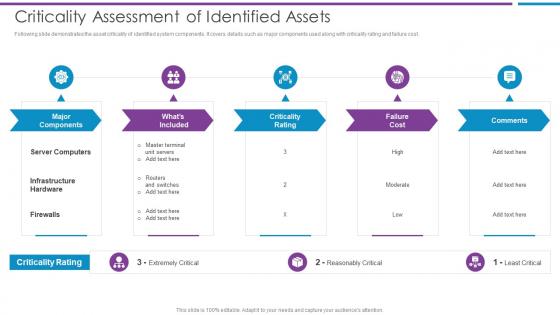 Criticality Assessment Of Identified Assets Risk Based Methodology To Cyber
Criticality Assessment Of Identified Assets Risk Based Methodology To CyberFollowing slide demonstrates the asset criticality of identified system components. It covers details such as major components used along with criticality rating and failure cost.Increase audience engagement and knowledge by dispensing information using Criticality Assessment Of Identified Assets Risk Based Methodology To Cyber This template helps you present information on five stages. You can also present information on Major Components, Criticality Rating, Infrastructure Hardware using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
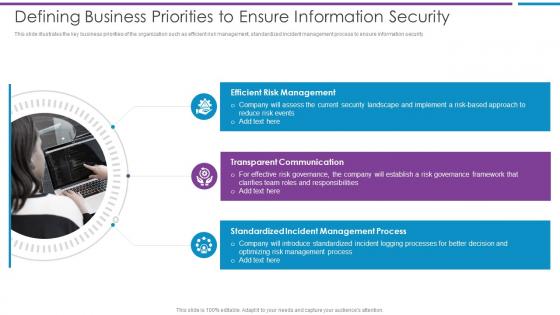 Defining Business Priorities To Ensure Information Security Risk Based Methodology To Cyber
Defining Business Priorities To Ensure Information Security Risk Based Methodology To CyberThis slide illustrates the key business priorities of the organization such as efficient risk management, standardized incident management process to ensure information security.Increase audience engagement and knowledge by dispensing information using Defining Business Priorities To Ensure Information Security Risk Based Methodology To Cyber This template helps you present information on three stages. You can also present information on Efficient Risk Management, Transparent Communication, Standardized Incident using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
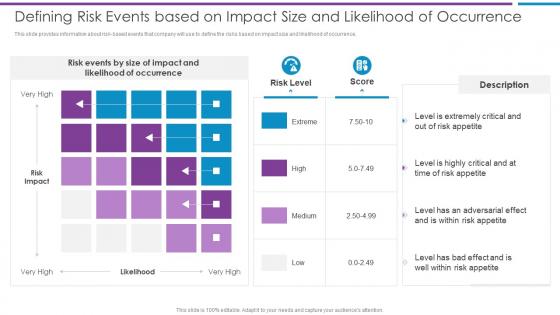 Defining Risk Events Based On Impact Size And Risk Based Methodology To Cyber
Defining Risk Events Based On Impact Size And Risk Based Methodology To CyberThis slide provides information about risk based events that company will use to define the risks based on impact size and likelihood of occurrence.Present the topic in a bit more detail with this Defining Risk Events Based On Impact Size And Risk Based Methodology To Cyber Use it as a tool for discussion and navigation on Level Is Extremely, Risk Appetite, Level Is Highly Critical This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Eliminating Manual Security Processes Through Automation Risk Based Methodology To Cyber
Eliminating Manual Security Processes Through Automation Risk Based Methodology To CyberMentioned slide displays the workflow process of how company will eliminate its existing manual security processes through automation tools.Present the topic in a bit more detail with this Eliminating Manual Security Processes Through Automation Risk Based Methodology To Cyber Use it as a tool for discussion and navigation on Manual Vulnerability, Scanning And Resolution, Vulnerability Scanning This template is free to edit as deemed fit for your organization. Therefore download it now.
-
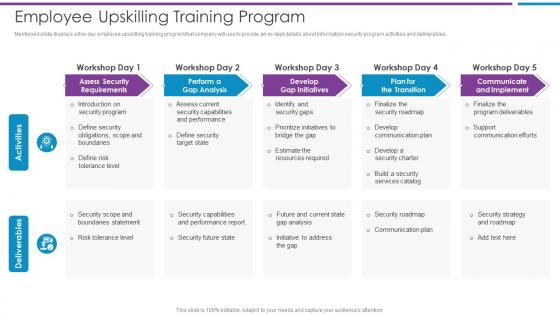 Employee Upskilling Training Program Risk Based Methodology To Cyber
Employee Upskilling Training Program Risk Based Methodology To CyberMentioned slide displays a five day employee upskilling training program that company will use to provide an in dept details about information security program activities and deliverables.Deliver an outstanding presentation on the topic using this Employee Upskilling Training Program Risk Based Methodology To Cyber Dispense information and present a thorough explanation of Assess Security Requirements, Perform A Gap Analysis, Develop Gap Initiatives using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
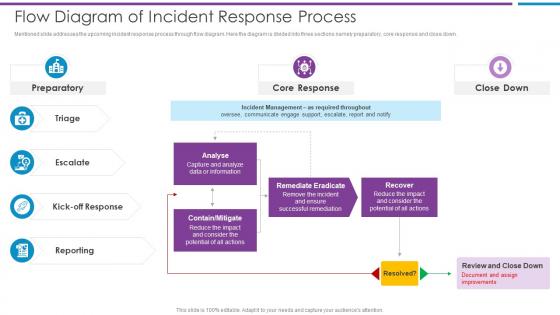 Flow Diagram Of Incident Response Process Risk Based Methodology To Cyber
Flow Diagram Of Incident Response Process Risk Based Methodology To CyberMentioned slide addresses the upcoming incident response process through flow diagram. Here the diagram is divided into three sections namely preparatory, core response and close down.Deliver an outstanding presentation on the topic using this Flow Diagram Of Incident Response Process Risk Based Methodology To Cyber Dispense information and present a thorough explanation of Capture And Analyze, Contain Mitigate, Remediate Eradicate using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
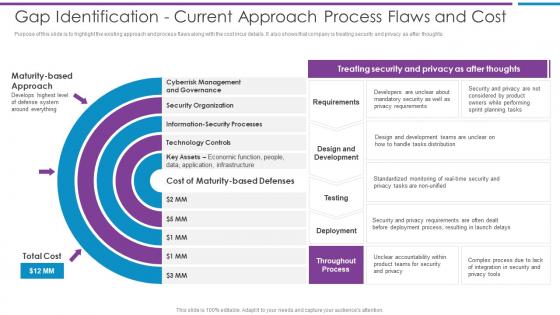 Gap Identification Current Approach Process Flaws And Cost Risk Based Methodology To Cyber
Gap Identification Current Approach Process Flaws And Cost Risk Based Methodology To CyberPurpose of this slide is to highlight the existing approach and process flaws along with the cost incur details. It also shows that company is treating security and privacy as after thoughts.Introducing Gap Identification Current Approach Process Flaws And Cost Risk Based Methodology To Cyber to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Design And Development, Requirements, Deployment using this template. Grab it now to reap its full benefits.
-
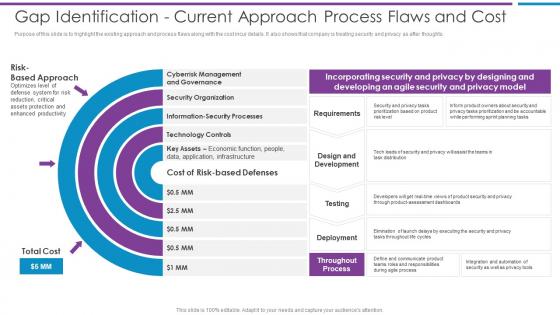 Gap Identification Current Approach Process Flaws And Risk Based Methodology To Cyber
Gap Identification Current Approach Process Flaws And Risk Based Methodology To CyberPurpose of this slide is to highlight the existing approach and process flaws along with the cost incur details. It also shows that company is treating security and privacy as after thoughts.Increase audience engagement and knowledge by dispensing information using Gap Identification Current Approach Process Flaws And Risk Based Methodology To Cyber This template helps you present information on three stages. You can also present information on Security Organization, Information Security Processes, Technology Controls using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Icons Slide For Risk Based Methodology To Cyber and Information Security
Icons Slide For Risk Based Methodology To Cyber and Information SecurityPresenting our well crafted Icons Slide For Risk Based Methodology To Cyber and Information Security set of slides. The slides include icons that are innovatively designed by our team of experts. The icons are easy to edit so you can conveniently increase or decrease their size without any loss in resolution. Therefore, grab them instantly
-
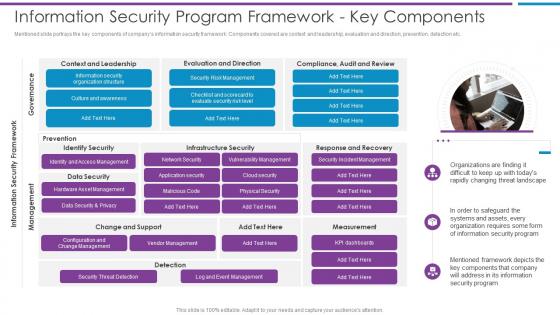 Information Security Program Framework Key Components Risk Based Methodology To Cyber
Information Security Program Framework Key Components Risk Based Methodology To CyberMentioned slide portrays the key components of companys information security framework. Components covered are context and leadership, evaluation and direction, prevention, detection etc.Introducing Information Security Program Framework Key Components Risk Based Methodology To Cyber to increase your presentation threshold. Encompassed with one stage this template is a great option to educate and entice your audience. Dispence information on Culture And Awareness, Security Risk Management, Data Security And Privacy using this template. Grab it now to reap its full benefits.
-
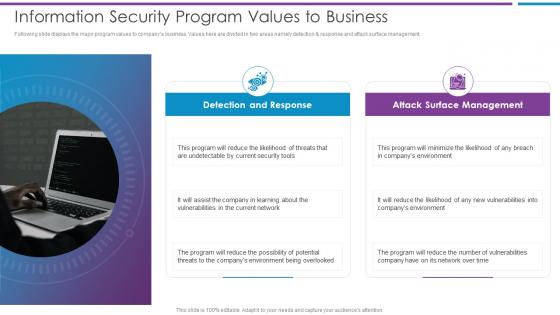 Information Security Program Values To Business Risk Based Methodology To Cyber
Information Security Program Values To Business Risk Based Methodology To CyberFollowing slide displays the major program values to companys business. Values here are divided in two areas namely detection and response and attack surface management.Increase audience engagement and knowledge by dispensing information using Information Security Program Values To Business Risk Based Methodology To Cyber This template helps you present information on two stages. You can also present information on Undetectable By Current, Vulnerabilities In The Current, Threats To The Companys Environment using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
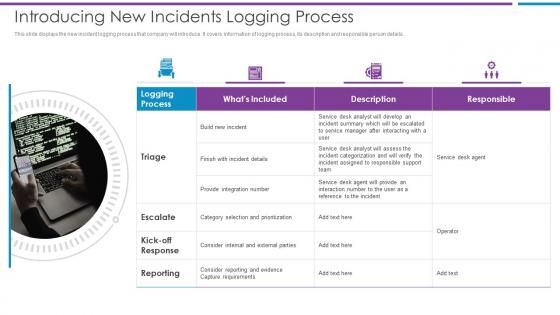 Introducing New Incidents Logging Process Risk Based Methodology To Cyber
Introducing New Incidents Logging Process Risk Based Methodology To CyberThis slide displays the new incident logging process that company will introduce. It covers information of logging process, its description and responsible person details.Increase audience engagement and knowledge by dispensing information using Introducing New Incidents Logging Process Risk Based Methodology To Cyber This template helps you present information on one stage. You can also present information on Provide Integration, Category Selection, Consider Internal using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Key Security Controls To Be Addressed In The Program Risk Based Methodology To Cyber
Key Security Controls To Be Addressed In The Program Risk Based Methodology To CyberPurpose of this slide is to provide information about key security controls that are to be addressed in companys information security program. Security controls covered are user application hardening, daily backups and patch applications.Present the topic in a bit more detail with this Key Security Controls To Be Addressed In The Program Risk Based Methodology To Cyber Use it as a tool for discussion and navigation on Prevents Attacks, Limits Extent Of Attacks, Data Recovery This template is free to edit as deemed fit for your organization. Therefore download it now.
-
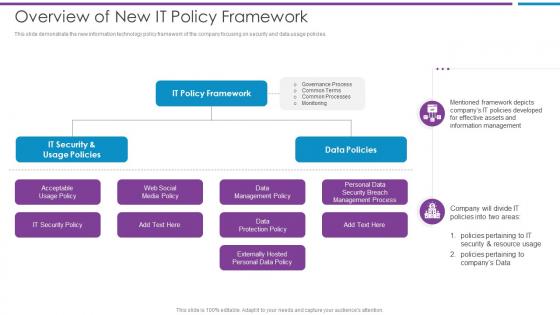 Overview Of New It Policy Framework Risk Based Methodology To Cyber
Overview Of New It Policy Framework Risk Based Methodology To CyberThis slide demonstrate the new information technology policy framework of the company focusing on security and data usage policies.Introducing Overview Of New It Policy Framework Risk Based Methodology To Cyber to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Acceptable Usage Policy, Data Policies, Data Management Policy using this template. Grab it now to reap its full benefits.
-
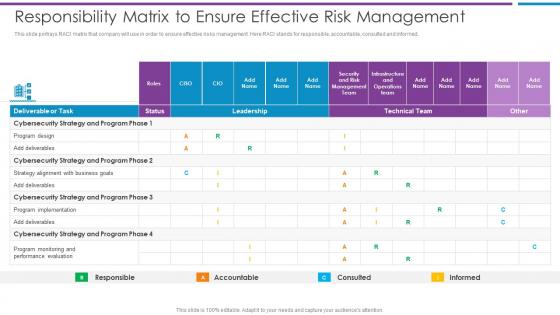 Responsibility Matrix To Ensure Effective Risk Management Risk Based Methodology To Cyber
Responsibility Matrix To Ensure Effective Risk Management Risk Based Methodology To CyberThis slide portrays RACI matrix that company will use in order to ensure effective risks management. Here RACI stands for responsible, accountable, consulted and informed.Present the topic in a bit more detail with this Responsibility Matrix To Ensure Effective Risk Management Risk Based Methodology To Cyber Use it as a tool for discussion and navigation on Cybersecurity Strategy, Program Implementation, Program Monitoring This template is free to edit as deemed fit for your organization. Therefore download it now.
-
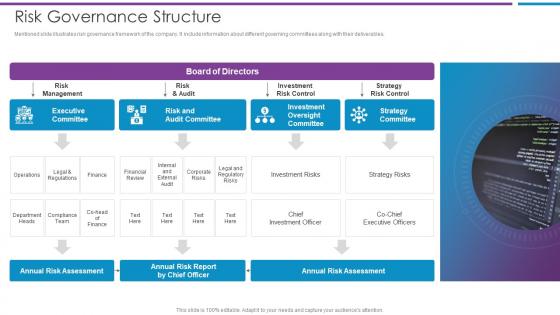 Risk Governance Structure Risk Based Methodology To Cyber
Risk Governance Structure Risk Based Methodology To CyberMentioned slide illustrates risk governance framework of the company. It include information about different governing committees along with their deliverables.Deliver an outstanding presentation on the topic using this Risk Governance Structure Risk Based Methodology To Cyber Dispense information and present a thorough explanation of Executive Committee, Risk And Audit Committee, Investment Oversight Committee using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
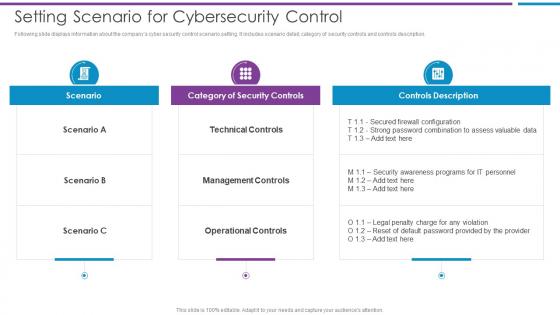 Setting Scenario For Cybersecurity Control Risk Based Methodology To Cyber
Setting Scenario For Cybersecurity Control Risk Based Methodology To CyberFollowing slide displays information about the companys cyber security control scenario setting. It includes scenario detail, category of security controls and controls description.Present the topic in a bit more detail with this Setting Scenario For Cybersecurity Control Risk Based Methodology To Cyber Use it as a tool for discussion and navigation on Technical Controls, Management Controls, Operational Controls This template is free to edit as deemed fit for your organization. Therefore download it now.
-
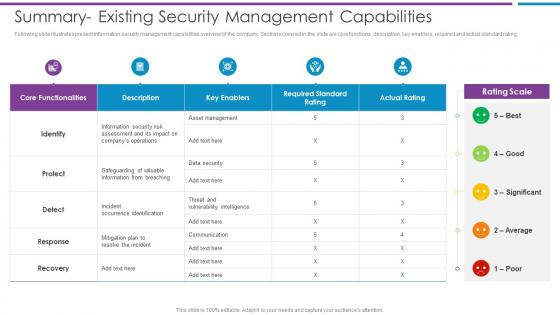 Summary Existing Security Management Capabilities Risk Based Methodology To Cyber
Summary Existing Security Management Capabilities Risk Based Methodology To CyberFollowing slide illustrates present information security management capabilities overview of the company. Sections covered in the slide are core functions, description, key enablers, required and actual standard rating.Deliver an outstanding presentation on the topic using this Summary Existing Security Management Capabilities Risk Based Methodology To Cyber Dispense information and present a thorough explanation of Information From Breaching, Occurrence Identification, Information Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
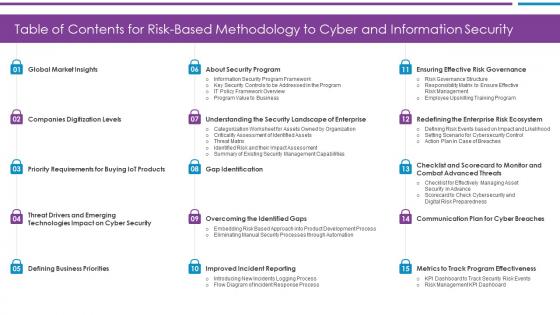 Table Of Contents For Risk Based Methodology To Cyber and Information Security
Table Of Contents For Risk Based Methodology To Cyber and Information SecurityPresent the topic in a bit more detail with this Table Of Contents For Risk Based Methodology To Cyber and Information Security Use it as a tool for discussion and navigation on Defining Business Priorities, Global Market Insights, Companies Digitization Levels This template is free to edit as deemed fit for your organization. Therefore download it now.
-
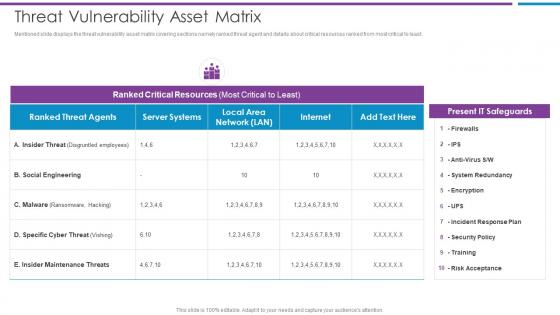 Threat Vulnerability Asset Matrix Risk Based Methodology To Cyber
Threat Vulnerability Asset Matrix Risk Based Methodology To CyberMentioned slide displays the threat vulnerability asset matrix covering sections namely ranked threat agent and details about critical resources ranked from most critical to least.Present the topic in a bit more detail with this Threat Vulnerability Asset Matrix Risk Based Methodology To Cyber Use it as a tool for discussion and navigation on Social Engineering, Ranked Critical Resources, Present IT Safeguards This template is free to edit as deemed fit for your organization. Therefore download it now.
-
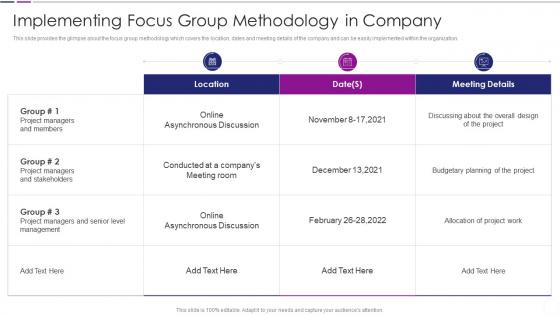 Implementing Focus Group Methodology Quantitative Risk Analysis
Implementing Focus Group Methodology Quantitative Risk AnalysisThis slide provides the glimpse about the focus group methodology which covers the location, dates and meeting details of the company and can be easily implemented within the organization. Deliver an outstanding presentation on the topic using this Implementing Focus Group Methodology Quantitative Risk Analysis. Dispense information and present a thorough explanation of Implementing Focus Group Methodology In Company using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
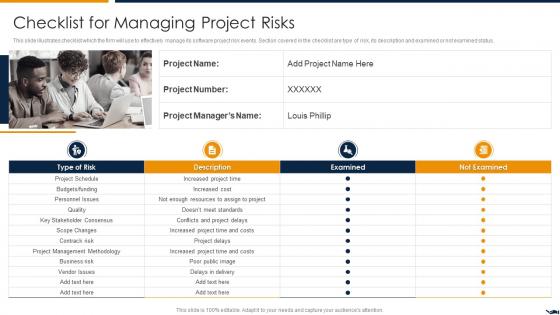 Checklist For Managing Project Risks Project Quality Assurance Using Agile Methodology IT
Checklist For Managing Project Risks Project Quality Assurance Using Agile Methodology ITThis slide illustrates checklist which the firm will use to effectively manage its software project risk events. Section covered in the checklist are type of risk, its description and examined or not examined status.Increase audience engagement and knowledge by dispensing information using Checklist For Managing Project Risks Project Quality Assurance Using Agile Methodology IT This template helps you present information on four stages. You can also present information on Increased Project Time, Increased Project Time And Costs, Project Management Methodology using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
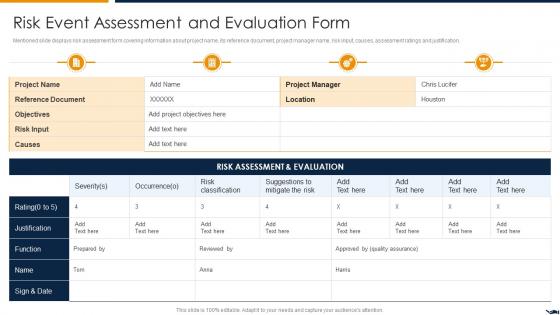 Risk Event Assessment And Project Quality Assurance Using Agile Methodology IT
Risk Event Assessment And Project Quality Assurance Using Agile Methodology ITMentioned slide displays risk assessment form covering information about project name, its reference document, project manager name, risk input, causes, assessment ratings and justification.Deliver an outstanding presentation on the topic using this Risk Event Assessment And Project Quality Assurance Using Agile Methodology IT Dispense information and present a thorough explanation of Regression And Performance Testing, Test Automation, Sprint Planning using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
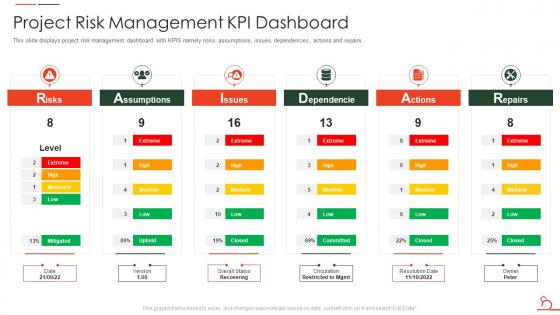 Agile Methodology For Data Migration Project It Project Risk Management Kpi Dashboard
Agile Methodology For Data Migration Project It Project Risk Management Kpi DashboardThis slide displays project risk management dashboard with KPIS namely risks, assumptions, issues, dependencies, actions and repairs. Deliver an outstanding presentation on the topic using this Agile Methodology For Data Migration Project It Project Risk Management Kpi Dashboard. Dispense information and present a thorough explanation of Project Risk Management Kpi Dashboard using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
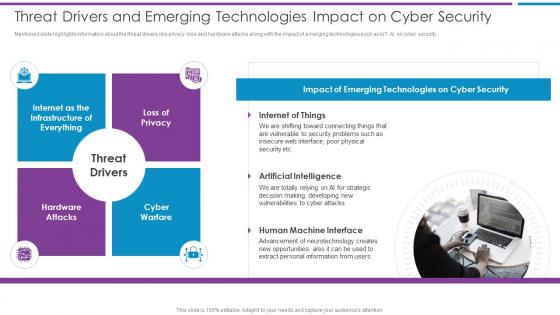 Risk Based Methodology To Cyber Threat Drivers And Emerging Technologies Impact On Cyber Security
Risk Based Methodology To Cyber Threat Drivers And Emerging Technologies Impact On Cyber SecurityMentioned slide highlights information about the threat drivers like privacy loss and hardware attacks along with the impact of emerging technologies such as IoT, AI on cyber security.Increase audience engagement and knowledge by dispensing information using Risk Based Methodology To Cyber Risk Based Methodology To Cyber Threat Drivers And Emerging Technologies Impact On Cyber Security security This template helps you present information on one stage. You can also present information on Artificial Intelligence, Human Machine Interface, Internet Of Things using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
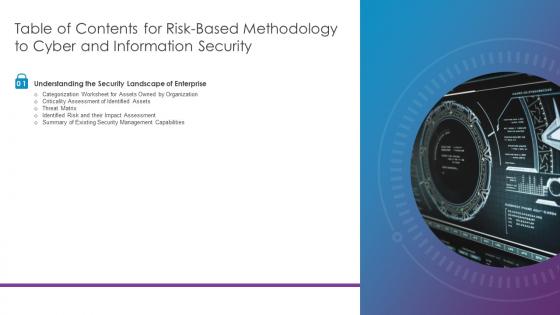 Risk Based Methodology To Cyber And Information Security Table Of Contents
Risk Based Methodology To Cyber And Information Security Table Of ContentsDeliver an outstanding presentation on the topic using this Risk Based Methodology To Cyber And Information Security Table Of Contents Dispense information and present a thorough explanation of Threat Matrix, Identified Assets, Impact Assessment using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
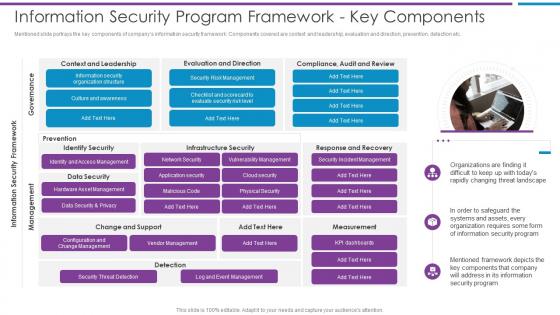 Risk Based Methodology To Cyber Information Security Program Framework Key Components
Risk Based Methodology To Cyber Information Security Program Framework Key ComponentsMentioned slide portrays the key components of companys information security framework. Components covered are context and leadership, evaluation and direction, prevention, detection etc.Introducing Risk Based Methodology To Cyber Information Security Program Framework Key Components to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispence information on Culture And Awareness, Security Risk Management, Data Security And Privacy, using this template. Grab it now to reap its full benefits.
-
 Owasp risk rating methodology ppt powerpoint presentation layouts structure cpb
Owasp risk rating methodology ppt powerpoint presentation layouts structure cpbPresenting our OWASP Risk Rating Methodology Ppt Powerpoint Presentation Layouts Structure Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on OWASP Risk Rating Methodology This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Methodologies to handle accounts receivable process risks associated with account receivables
Methodologies to handle accounts receivable process risks associated with account receivablesThis slide shows the risks associated with accounts receivables such as existence or occurrence, completeness, rights and obligations, etc. Increase audience engagement and knowledge by dispensing information using Methodologies To Handle Accounts Receivable Process Risks Associated With Account Receivables. This template helps you present information on four stages. You can also present information on Existence Or Occurrence, Completeness, Obligations using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Risk Assessment Methodology Scoring Tool In Powerpoint And Google Slides Cpb
Risk Assessment Methodology Scoring Tool In Powerpoint And Google Slides CpbPresenting Risk Assessment Methodology Scoring Tool In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Risk Assessment Methodology Scoring Tool. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Risk Management Methodology In Information Technology Security
Risk Management Methodology In Information Technology SecurityThis slide focuses on the risk management methodology in information technology security which includes three different phases such as assessment, mitigation and continual evaluation assessment that are helpful in effective management of security risks and hazards. Deliver an outstanding presentation on the topic using this Risk Management Methodology In Information Technology Security. Dispense information and present a thorough explanation of Assessment, Mitigation, Continual Evaluation Assessment using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Customer Risk Rating Methodology In Powerpoint And Google Slides Cpb
Customer Risk Rating Methodology In Powerpoint And Google Slides CpbPresenting Customer Risk Rating Methodology In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Customer Risk Rating Methodology. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
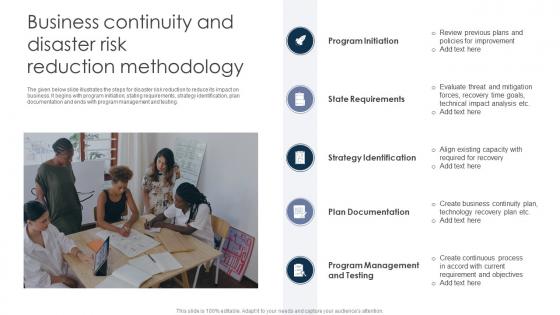 Business Continuity And Disaster Risk Reduction Methodology
Business Continuity And Disaster Risk Reduction MethodologyThe given below slide illustrates the steps for disaster risk reduction to reduce its impact on business. It begins with program initiation, stating requirements, strategy identification, plan documentation and ends with program management and testing. Introducing our premium set of slides with Business Continuity And Disaster Risk Reduction Methodology. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Program Initiation, State Requirements, Strategy Identification. So download instantly and tailor it with your information.
-
 Risk Management Methodologies Icon To Improve Financial Project Planning
Risk Management Methodologies Icon To Improve Financial Project PlanningPresenting our set of slides with name Risk Management Methodologies Icon To Improve Financial Project Planning. This exhibits information on four stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Risk Management Methodologies, Icon, Financial Project Planning.
-
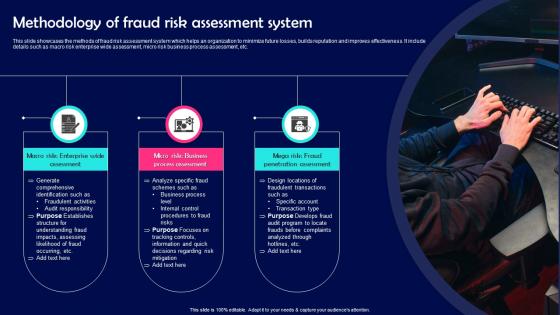 Methodology Of Fraud Risk Assessment System
Methodology Of Fraud Risk Assessment SystemThis slide showcases the methods of fraud risk assessment system which helps an organization to minimize future losses, builds reputation and improves effectiveness. It include details such as macro risk enterprise wide assessment, micro risk business process assessment, etc. Presenting our set of slides with Methodology Of Fraud Risk Assessment System. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Penetration Assessment, Process Assessment.
-
 Assessment Methodology To Evaluate Organisation Risk
Assessment Methodology To Evaluate Organisation RiskThis slide includes risk assessment methodologies that helps to evaluate an organizations risk posture. These include asset based, vulnerability based, threat-based, qualitative, and quantitative. Presenting our set of slides with Assessment Methodology To Evaluate Organisation Risk. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Vulnerability Based, Quantitative, Threat Based.
-
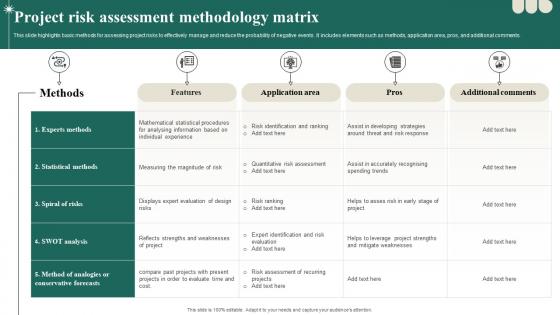 Project Risk Assessment Methodology Matrix
Project Risk Assessment Methodology MatrixThis slide highlights basic methods for assessing project risks to effectively manage and reduce the probability of negative events. It includes elements such as methods, application area, pros, and additional comments. Presenting our well structured Project Risk Assessment Methodology Matrix. The topics discussed in this slide are Assessment, Methodology, Application. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
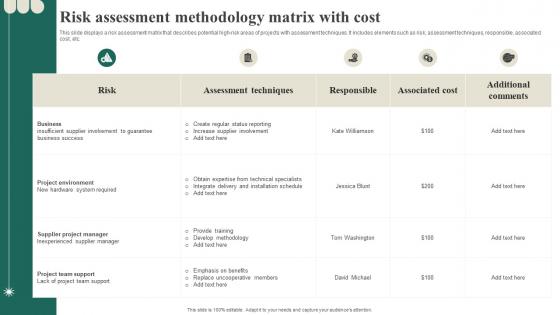 Risk Assessment Methodology Matrix With Cost
Risk Assessment Methodology Matrix With CostThis slide displays a risk assessment matrix that describes potential high-risk areas of projects with assessment techniques. It includes elements such as risk, assessment techniques, responsible, associated cost, etc. Introducing our Risk Assessment Methodology Matrix With Cost set of slides. The topics discussed in these slides are Assessment, Methodology, Techniques. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Risk analysis methodology powerpoint slide background image
Risk analysis methodology powerpoint slide background imagePresenting risk analysis methodology powerpoint slide background image. This is a risk analysis methodology powerpoint slide background image. This is a three stage process. The stages in this process are teamwork, risk analysis, security measures, risk planning, risk retention model.
-
 Risk assessment methodology powerpoint templates
Risk assessment methodology powerpoint templatesIntroducing risk assessment methodology PPT templates. Promptly conformable and downloadable PPT Slide. Quite suitable for business professionals from diverse fields or areas. Editable text, font, background, and PowerPoint Image. Easily convertible into PDF or JPG formats. Can be used with Google slides and on other software platforms. Offers an option to insert the titles or subtitles as required in this Presentation slide diagram.
-
 0514 risk assessment methodology powerpoint presentation
0514 risk assessment methodology powerpoint presentationPPT slide can be presented in both standard and widescreen view. Effortlessly download and changeable into JPEG and PDF document. PowerPoint designs are totally compatible with Google slides. Choice of insertion of corporate symbol and image for personalization. Availability to download similar designs with different nodes and stages. Easily editable presentation layout as color, text and font are editable.
-
 Three staged text box for risk assessment methodology flat powerpoint design
Three staged text box for risk assessment methodology flat powerpoint designDesigner’s cordial format slides. Use of prevalent quality visuals, symbols, representation in PPT layouts. Download in a split second with a tick and simple to share. Ease to change the format hues, look, plans, and foundations. Different hubs and stages format slides are accessible. Effortless inclusion of association exchange stamp, logo and name. Versatile to change over JPG and PDF design.
-
 Risk management methodologies strategic human resource management management standard cpb
Risk management methodologies strategic human resource management management standard cpbPresenting this set of slides with name - Risk Management Methodologies Strategic Human Resource Management Management Standard Cpb. This is an editable five stages graphic that deals with topics like Risk Management Methodologies, Strategic Human Resource Management, Management Standard to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.


