Powerpoint Templates and Google slides for Protocol Security Connections
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
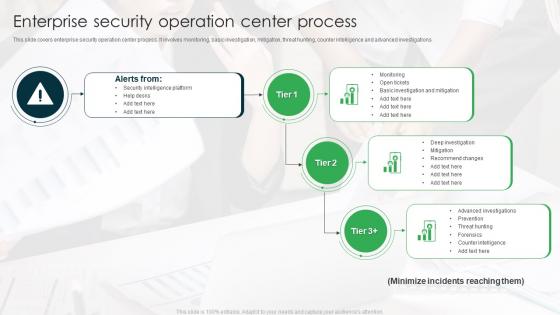 Enterprise Security Operation Center Process
Enterprise Security Operation Center ProcessThis slide covers enterprise security operation center process. It involves monitoring, basic investigation, mitigation, threat hunting, counter intelligence and advanced investigations. Introducing our Enterprise Security Operation Center Process set of slides. The topics discussed in these slides are Security Intelligence Platform, Help Desks, Monitoring. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
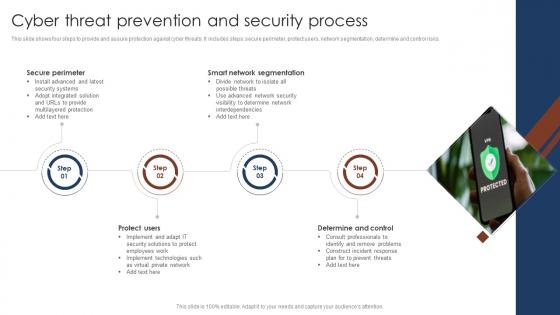 Cyber Threat Prevention And Security Process
Cyber Threat Prevention And Security ProcessThis slide shows four steps to provide and assure protection against cyber threats. It includes steps secure perimeter, protect users, network segmentation, determine and control risks. Introducing our premium set of slides with name Cyber Threat Prevention And Security Process. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Secure Perimeter, Smart Network Segmentation, Determine And Control. So download instantly and tailor it with your information.
-
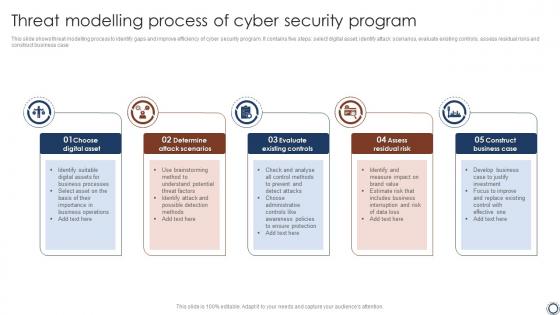 Threat Modelling Process Of Cyber Security Program
Threat Modelling Process Of Cyber Security ProgramThis slide shows threat modelling process to identify gaps and improve efficiency of cyber security program. It contains five steps select digital asset, identify attack scenarios, evaluate existing controls, assess residual risks and construct business case. Presenting our set of slides with name Threat Modelling Process Of Cyber Security Program. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Threat Modelling, Cyber Security, Assess Residual Risk .
-
 Security Uses SSL Protocol In Powerpoint And Google Slides Cpb
Security Uses SSL Protocol In Powerpoint And Google Slides CpbPresenting Security Uses SSL Protocol In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Security Uses SSL Protocol. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 4 Step Process To Improve Safety And Security
4 Step Process To Improve Safety And SecurityThis slide shows the four stage process to increase safety and security. It includes firewall installation, separate network for payment, passwords change and vulnerabilities test. Presenting our set of slides with 4 Step Process To Improve Safety And Security. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Separate Network For Payment, Passwords Change, Firewall Installation.
-
 Five Step Process Of Safety And Security
Five Step Process Of Safety And SecurityThis slide shows the five stages process of safety and security. These stages are audit, plan, execute, monitor and repeat. Introducing our premium set of slides with Five Step Process Of Safety And Security. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Audit, Cyber Security Training, Quarterly Plan Review. So download instantly and tailor it with your information.
-
 Security Strategic Planning Process For Cps Collective Intelligence Systems
Security Strategic Planning Process For Cps Collective Intelligence SystemsThis slide represents the security strategic planning process for CPS, including business strategy, technology roadmap, vision statement environment trends, current state assessment, and so on. Increase audience engagement and knowledge by dispensing information using Security Strategic Planning Process For Cps Collective Intelligence Systems. This template helps you present information on one stages. You can also present information on Business Strategy, Environmental Trends, Gap Analysis, Prioritization using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
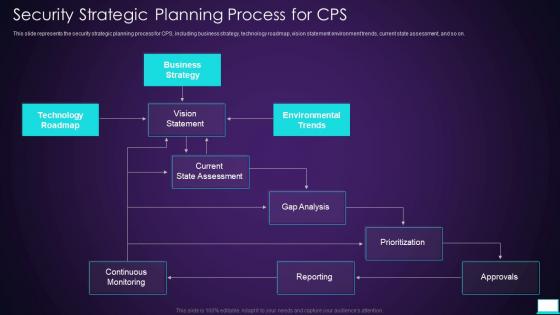 Security Strategic Planning Process For Cps Intelligent System
Security Strategic Planning Process For Cps Intelligent SystemThis slide represents the security strategic planning process for CPS, including business strategy, technology roadmap, vision statement environment trends, current state assessment, and so on. Deliver an outstanding presentation on the topic using this Security Strategic Planning Process For Cps Intelligent System. Dispense information and present a thorough explanation of Strategic, Planning, Process using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
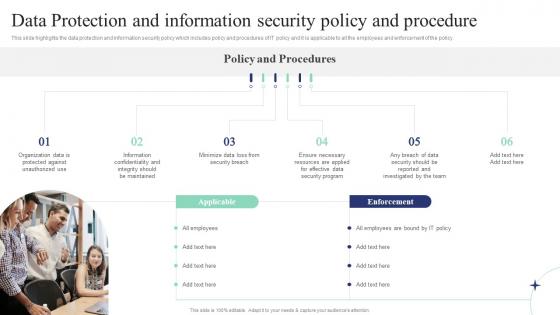 Data Protection And Information Security Policy And Procedure Corporate Induction Program For New Staff
Data Protection And Information Security Policy And Procedure Corporate Induction Program For New StaffThis slide highlights the data protection and information security policy which includes policy and procedures of IT policy and it is applicable to all the employees and enforcement of the policy. Introducing Data Protection And Information Security Policy And Procedure Corporate Induction Program For New Staff to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Protection, Information, Procedure, using this template. Grab it now to reap its full benefits.
-
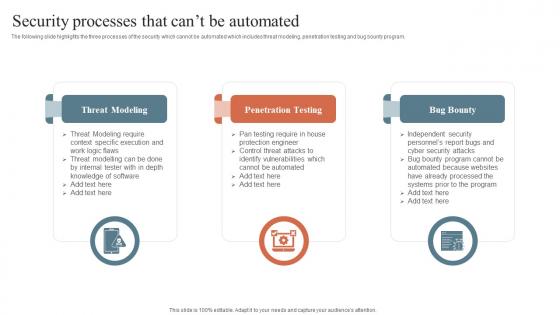 Security Processes That Cant Be Automated Security Orchestration Automation And Response Guide
Security Processes That Cant Be Automated Security Orchestration Automation And Response GuideThe following slide highlights the three processes of the security which cannot be automated which includes threat modeling, penetration testing and bug bounty program. Introducing Security Processes That Cant Be Automated Security Orchestration Automation And Response Guide to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Threat Modeling, Penetration Testing, Bug Bounty, using this template. Grab it now to reap its full benefits.
-
 Why To Automate The It Security Process Security Orchestration Automation And Response Guide
Why To Automate The It Security Process Security Orchestration Automation And Response GuideThis slide highlights the benefits or importance of automation security process which includes better threat detection, faster containment, improve productivity, admin role delegation and incident response. Increase audience engagement and knowledge by dispensing information using Why To Automate The It Security Process Security Orchestration Automation And Response Guide. This template helps you present information on five stages. You can also present information on Better Threat Detection, Faster Containment, Improve Productivity using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
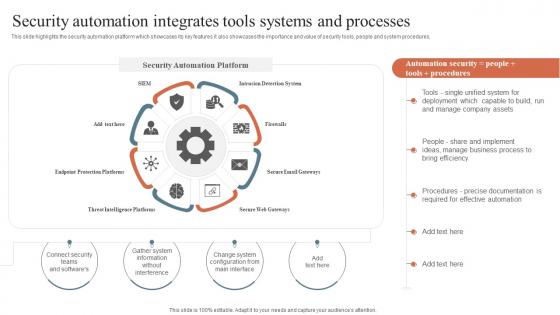 Security Orchestration Automation Security Automation Integrates Tools Systems And Processes
Security Orchestration Automation Security Automation Integrates Tools Systems And ProcessesThis slide highlights the different security automation tools which incudes robotic process automation. Security orchestration, automation and response, extended detection and SIEM. Deliver an outstanding presentation on the topic using this Security Orchestration Automation Security Automation Integrates Tools Systems And Processes. Dispense information and present a thorough explanation of Security Automation, Robotic Process, Security Information using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
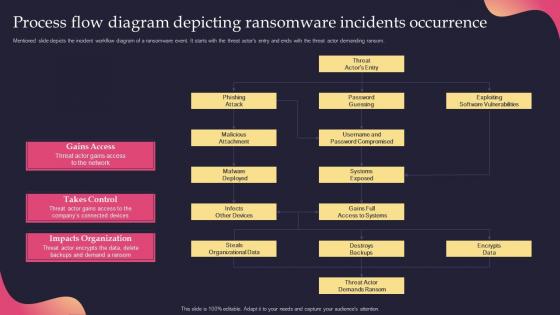 Process Flow Diagram Depicting Ransomware Incidents Occurrence Security Incident Response Playbook
Process Flow Diagram Depicting Ransomware Incidents Occurrence Security Incident Response PlaybookMentioned slide depicts the incident workflow diagram of a ransomware event. It starts with the threat actors entry and ends with the threat actor demanding ransom. Deliver an outstanding presentation on the topic using this Process Flow Diagram Depicting Ransomware Incidents Occurrence Security Incident Response Playbook. Dispense information and present a thorough explanation of Process, Ransomware, Occurrence using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Security Incident Response Playbook Addressing The Cyber Incident Logging Process
Security Incident Response Playbook Addressing The Cyber Incident Logging ProcessThis slide displays logging process for a cyber incident logging. It covers information about process ID, procedure, its description and owner details. Deliver an outstanding presentation on the topic using this Security Incident Response Playbook Addressing The Cyber Incident Logging Process. Dispense information and present a thorough explanation of Process, Information, Procedure using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
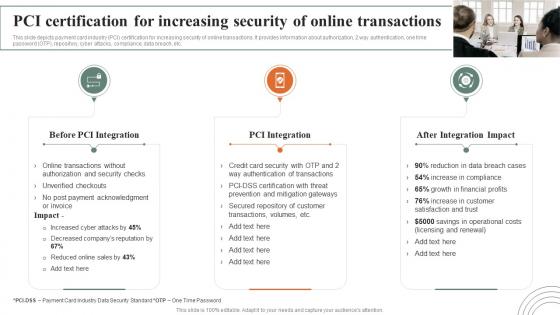 Pci Certification For Increasing Security Online Transactions How Ecommerce Financial Process Can Be Improved
Pci Certification For Increasing Security Online Transactions How Ecommerce Financial Process Can Be ImprovedThis slide depicts payment card industry PCI certification for increasing security of online transactions. It provides information about authorization, 2 way authentication, one time password OTP, repository, cyber attacks, compliance, data breach, etc. Deliver an outstanding presentation on the topic using this Pci Certification For Increasing Security Online Transactions How Ecommerce Financial Process Can Be Improved. Dispense information and present a thorough explanation of Transactions, Certification, Integration using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
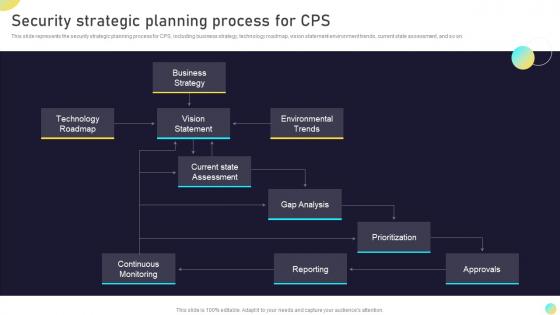 Security Strategic Planning Process For Cps Next Generation Computing Systems
Security Strategic Planning Process For Cps Next Generation Computing SystemsThis slide represents the security strategic planning process for CPS, including business strategy, technology roadmap, vision statement environment trends, current state assessment, and so on. Present the topic in a bit more detail with this Security Strategic Planning Process For Cps Next Generation Computing Systems. Use it as a tool for discussion and navigation on Strategic, Planning, Process. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
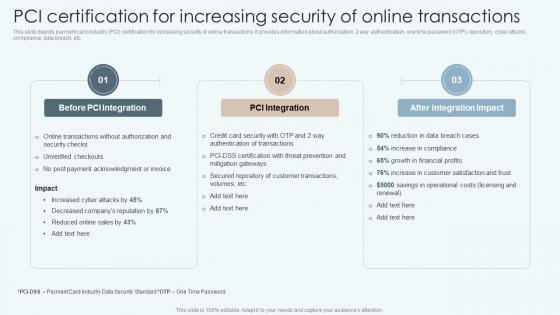 PCI Certification For Increasing Security Of Online Transactions Improving Financial Management Process
PCI Certification For Increasing Security Of Online Transactions Improving Financial Management ProcessThis slide depicts payment card industry PCI certification for increasing security of online transactions. It provides information about authorization, 2 way authentication, one time password OTP, repository, cyber attacks, compliance, data breach, etc. Increase audience engagement and knowledge by dispensing information using PCI Certification For Increasing Security Of Online Transactions Improving Financial Management Process. This template helps you present information on three stages. You can also present information on Before PCI Integration, PCI Integration, After Integration Impact using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
 Employees Rules And Regulations Security And Manpower Services Company Profile
Employees Rules And Regulations Security And Manpower Services Company ProfileThis slide highlights the security guard company rules and regulations which showcases In and out time, note visitor name, and wear uniform at working hours. Present the topic in a bit more detail with this Employees Rules And Regulations Security And Manpower Services Company Profile. Use it as a tool for discussion and navigation on Security Officer Must Wear Uniform, Security Officer Must Note Down Name, Rules And Regulations. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Bank Frauds Prevention Process With Cyber Security Program
Bank Frauds Prevention Process With Cyber Security ProgramThe slide illustrates a banking frauds mitigation process for client to reduce and prevent issues. Its key steps are establish governance structure, define culture shift, introduce staff training, improve payment process, implement technology controls and harden human firewall. Introducing our premium set of slides with Bank Frauds Prevention Process With Cyber Security Program. Elucidate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Introduce Staff Training, Implement Technology Controls, Improve Payment Process, Harden Human Firewall. So download instantly and tailor it with your information.
-
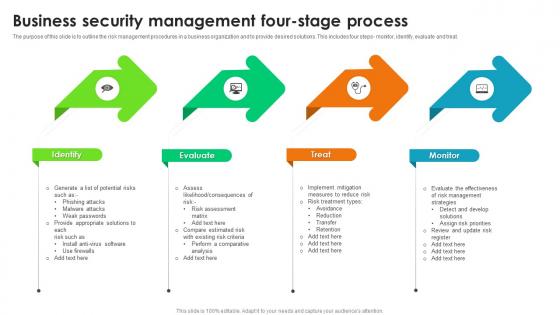 Business Security Management Four Stage Process
Business Security Management Four Stage ProcessThe purpose of this slide is to outline the risk management procedures in a business organization and to provide desired solutions. This includes four steps- monitor, identify, evaluate and treat. Presenting our set of slides with name Business Security Management Four Stage Process. This exhibits information on four stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Identify, Evaluate, Treat, Monitor.
-
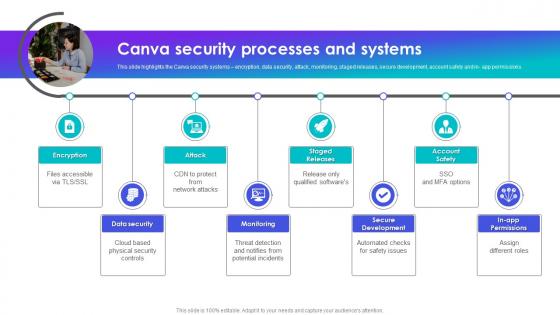 Canva Security Processes And Systems Canva Company Profile Ppt Summary Graphics Tutorials
Canva Security Processes And Systems Canva Company Profile Ppt Summary Graphics TutorialsThis slide highlights the Canva security systems encryption, data security, attack, monitoring, staged releases, secure development, account safety and in app permissions. Introducing Canva Security Processes And Systems Canva Company Profile Ppt Summary Graphics Tutorials to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Secure Development, Monitoring, Data Security, using this template. Grab it now to reap its full benefits.
-
 Cyber Security Risk Communication Process Framework
Cyber Security Risk Communication Process FrameworkThis slide showcases a model of risk communication process for cyber security. It includes identify issues, set goals, and objectives, community and constraints, stakeholder assessment, communication and engagement tools, implement strategy and evaluate and follow up. Introducing our premium set of slides with Cyber Security Risk Communication Process Framework. Ellicudate the eight stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Identify Issue, Implement Strategy, Identify Messages. So download instantly and tailor it with your information.
-
 Cyber Security Protocols In Powerpoint And Google Slides Cpb
Cyber Security Protocols In Powerpoint And Google Slides CpbPresenting our Cyber Security Protocols In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases nine stages. It is useful to share insightful information on Cyber Security Protocols This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
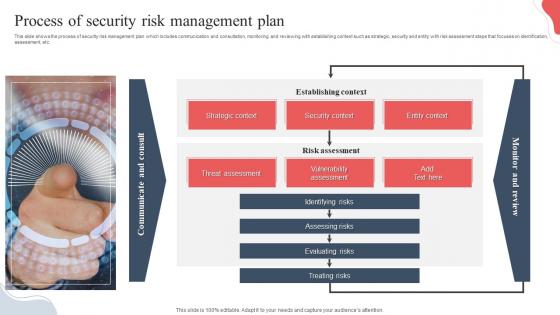 Process Of Security Risk Management Plan
Process Of Security Risk Management PlanThis slide shows the process of security risk management plan which includes communication and consultation, monitoring and reviewing with establishing context such as strategic, security and entity with risk assessment steps that focuses on identification, assessment, etc. Introducing our Process Of Security Risk Management Plan set of slides. The topics discussed in these slides are Threat Assessment, Vulnerability Assessment, Security Context . This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
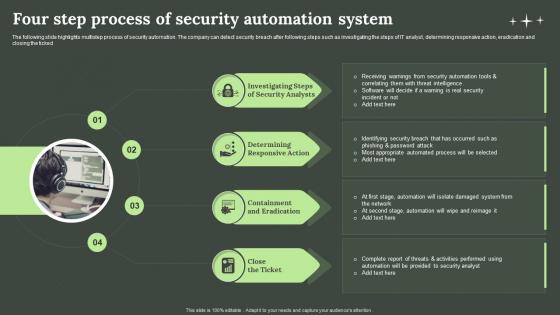 Four Step Process Of Security Automation System
Four Step Process Of Security Automation SystemThe following slide highlights multistep process of security automation. The company can detect security breach after following steps such as investigating the steps of IT analyst, determining responsive action, eradication and closing the ticked Presenting our set of slides with name Four Step Process Of Security Automation System. This exhibits information on four stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Investigating Steps, Security Analysts, Eradication.
-
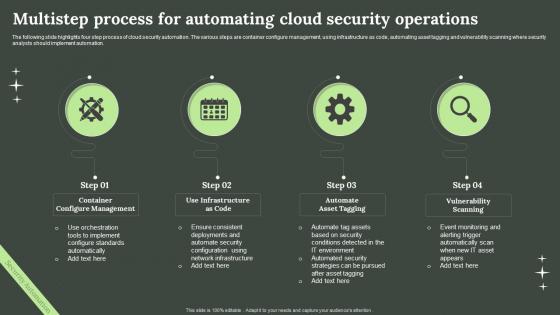 Multistep Process For Automating Cloud Security Operations
Multistep Process For Automating Cloud Security OperationsThe following slide highlights four step process of cloud security automation. The various steps are container configure management, using infrastructure as code, automating asset tagging and vulnerability scanning where security analysts should implement automation. Introducing our premium set of slides with Multistep Process For Automating Cloud Security Operations. Elucidate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Container Configure Management, Infrastructure As Code, Vulnerability Scanning. So download instantly and tailor it with your information.
-
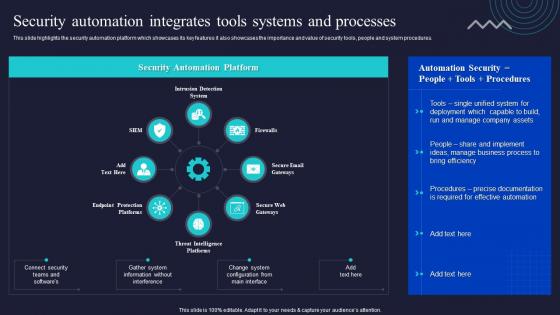 Security Automation Integrates Tools Systems And Processes Enabling Automation In Cyber Security Operations
Security Automation Integrates Tools Systems And Processes Enabling Automation In Cyber Security OperationsThis slide highlights the security automation platform which showcases its key features it also showcases the importance and value of security tools, people and system procedures. Present the topic in a bit more detail with this Security Automation Integrates Tools Systems And Processes Enabling Automation In Cyber Security Operations. Use it as a tool for discussion and navigation on Security Automation, Integrates, Processes. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
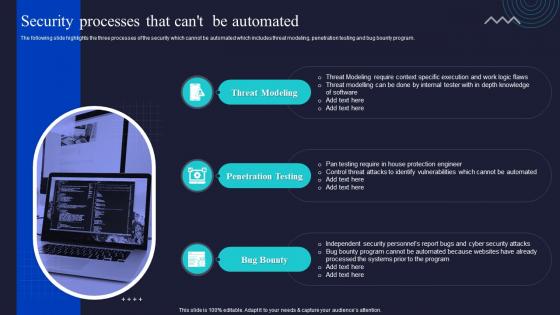 Security Processes That Cant Be Automated Enabling Automation In Cyber Security Operations
Security Processes That Cant Be Automated Enabling Automation In Cyber Security OperationsThe following slide highlights the three processes of the security which cannot be automated which includes threat modeling, penetration testing and bug bounty program. Increase audience engagement and knowledge by dispensing information using Security Processes That Cant Be Automated Enabling Automation In Cyber Security Operations. This template helps you present information on three stages. You can also present information on Threat Modeling, Penetration Testing, Bug Bounty using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Why To Automate The It Security Process Enabling Automation In Cyber Security Operations
Why To Automate The It Security Process Enabling Automation In Cyber Security OperationsThis slide highlights the benefits or importance of automation security process which includes better threat detection, faster containment, improve productivity, admin role delegation and incident response. Increase audience engagement and knowledge by dispensing information using Why To Automate The It Security Process Enabling Automation In Cyber Security Operations. This template helps you present information on five stages. You can also present information on Better Threat Detection, Faster Containment, Improve Productivity using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
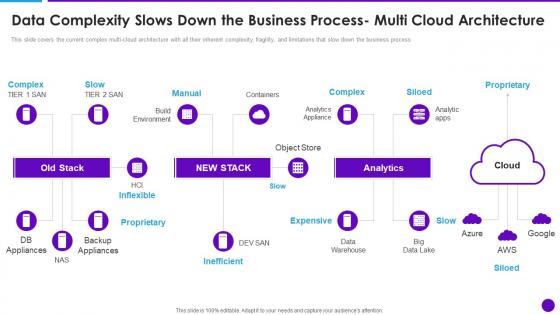 Cloud Architecture And Security Review Data Complexity Slows Down The Business Process Multi Cloud
Cloud Architecture And Security Review Data Complexity Slows Down The Business Process Multi CloudThis slide covers the current complex multi cloud architecture with all their inherent complexity, fragility, and limitations that slow down the business process. Introducing Cloud Architecture And Security Review Data Complexity Slows Down The Business Process Multi Cloud to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Data Complexity, Slows Down The Business, Multi Cloud Architecture, using this template. Grab it now to reap its full benefits.
-
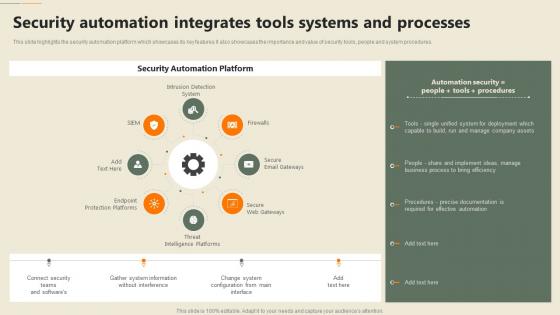 Security Automation Integrates Tools Systems And Processes Security Automation In Information Technology
Security Automation Integrates Tools Systems And Processes Security Automation In Information TechnologyThis slide highlights the security automation platform which showcases its key features it also showcases the importance and value of security tools, people and system procedures. Increase audience engagement and knowledge by dispensing information using Security Automation Integrates Tools Systems And Processes Security Automation In Information Technology. This template helps you present information on eight stages. You can also present information on Automation, Integrates, Processes using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations
-
 Security Processes That Cant Be Automated Security Automation In Information Technology
Security Processes That Cant Be Automated Security Automation In Information TechnologyThe following slide highlights the three processes of the security which cannot be automated which includes threat modeling, penetration testing and bug bounty program. Increase audience engagement and knowledge by dispensing information using Security Processes That Cant Be Automated Security Automation In Information Technology. This template helps you present information on three stages. You can also present information on Threat Modeling, Penetration Testing, Bug Bounty using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Why To Automate The It Security Process Security Automation In Information Technology
Why To Automate The It Security Process Security Automation In Information TechnologyThis slide highlights the benefits or importance of automation security process which includes better threat detection, faster containment, improve productivity, admin role delegation and incident response. Increase audience engagement and knowledge by dispensing information using Why To Automate The It Security Process Security Automation In Information Technology. This template helps you present information on five stages. You can also present information on Better Threat Detection, Faster Containment, Improve Productivity using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
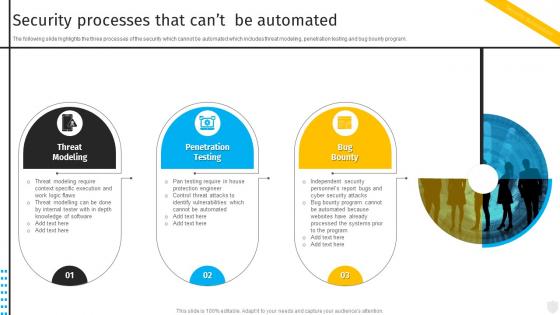 Security Processes That Cant Be Automated Security Automation To Investigate And Remediate Cyberthreats
Security Processes That Cant Be Automated Security Automation To Investigate And Remediate CyberthreatsThe following slide highlights the three processes of the security which cannot be automated which includes threat modeling, penetration testing and bug bounty program. Introducing Security Processes That Cant Be Automated Security Automation To Investigate And Remediate Cyberthreats to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Threat Modeling, Penetration Testing, Bug Bounty , using this template. Grab it now to reap its full benefits.
-
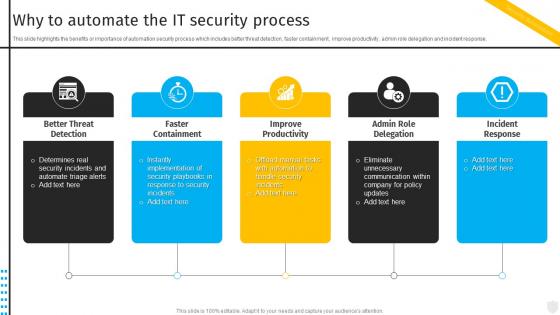 Why To Automate The It Security Process Security Automation To Investigate And Remediate Cyberthreats
Why To Automate The It Security Process Security Automation To Investigate And Remediate CyberthreatsThis slide highlights the benefits or importance of automation security process which includes better threat detection, faster containment, improve productivity, admin role delegation and incident response. Introducing Why To Automate The It Security Process Security Automation To Investigate And Remediate Cyberthreats to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Better Threat Detection, Faster Containment, Improve Productivity, using this template. Grab it now to reap its full benefits.
-
 Multistep Process Of Security Risk Acceptance
Multistep Process Of Security Risk AcceptanceThis slide shows multistep process of security risk acceptance which contains identifying risk, summarizing risk and risk acceptance and action. This can assist businesses in understanding the cause and effect of risks. Introducing our premium set of slides with Multistep Process Of Security Risk Acceptance. Elucidate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Identifying Risk, Summarizing Risk, Risk Acceptance Action. So download instantly and tailor it with your information.
-
 Problem Management Process For Enhancing Cyber Security
Problem Management Process For Enhancing Cyber SecurityThis slide signifies increasing cyber security and IT through problem management process. It includes stages like detection, define, investigate, identify resolutions, implement and follow up Introducing our premium set of slides with Problem Management Process For Enhancing Cyber Security. Elucidate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Problem Detection, Define, Investigate, Identify Resolutions, Implement. So download instantly and tailor it with your information.
-
 Data Warehouse Security Policy And Procedure Icon
Data Warehouse Security Policy And Procedure IconIntroducing our Data Warehouse Security Policy And Procedure Icon set of slides. The topics discussed in these slides are Data Warehouse Security Policy, Procedure Icon. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
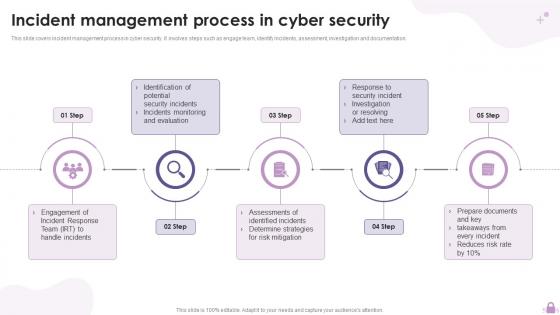 Incident Management Process In Cyber Security
Incident Management Process In Cyber SecurityThis slide covers incident management process in cyber security. It involves steps such as engage team, identify incidents, assessment, investigation and documentation. Presenting our set of slides with name Incident Management Process In Cyber Security. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Incident Response Team, Monitoring And Evaluation, Investigation Or Resolving.
-
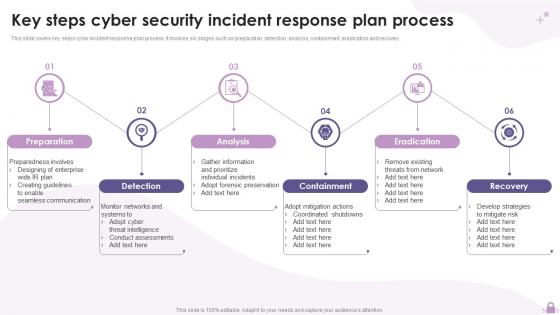 Key Steps Cyber Security Incident Response Plan Process
Key Steps Cyber Security Incident Response Plan ProcessThis slide covers key steps cyber incident response plan process. It involves six stages such as preparation, detection, analysis, containment, eradication and recovery. Presenting our set of slides with name Key Steps Cyber Security Incident Response Plan Process. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Preparation, Detection, Containment, Eradication.
-
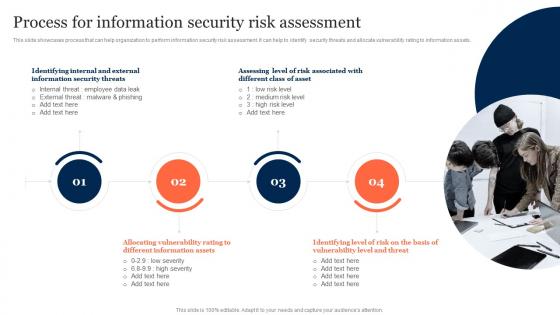 Process For Information Security Risk Assessment Information Security Risk Management
Process For Information Security Risk Assessment Information Security Risk ManagementThis slide showcases process that can help organization to perform information security risk assessment. It can help to identify security threats and allocate vulnerability rating to information assets. Introducing Process For Information Security Risk Assessment Information Security Risk Management to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispense information on Information Security Threats, Allocating Vulnerability, Risk Assessment, using this template. Grab it now to reap its full benefits.
-
 6 Stage Process For Implementation Of Risk Management In Cyber Security Project
6 Stage Process For Implementation Of Risk Management In Cyber Security ProjectThis This slide signifies the six step process for successful implementation of risk assessment in cyber security project. It covers information about stages like identify, analyse, evaluate, prioritize, treat and monitor. Presenting our set of slides with name 6 Stage Process For Implementation Of Risk Management In Cyber Security Project. This exhibits information on six stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Identify, Analyse, Evaluate, Prioritize, Treat.
-
 Cyber Data Security Risk Management Response Process
Cyber Data Security Risk Management Response ProcessThis slide covers process to respond towards cyber data security risk. It includes steps such as preparation of incident response plan, detection of data compromises, analyse use of malicious tools, eradicate network threats, data recovery as the final step. Presenting our set of slides with name Cyber Data Security Risk Management Response Process. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Network Threats, Compromised Data, Data Compromises.
-
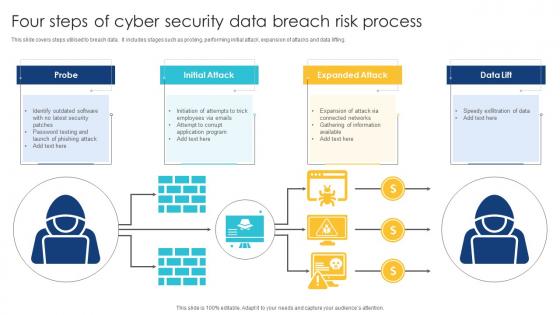 Four Steps Of Cyber Security Data Breach Risk Process
Four Steps Of Cyber Security Data Breach Risk ProcessThis slide covers steps utilised to breach data. It includes stages such as probing, performing initial attack, expansion of attacks and data lifting. Introducing our premium set of slides with name Four Steps Of Cyber Security Data Breach Risk Process. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Initial Attack, Expanded Attack, Breach Risk Process. So download instantly and tailor it with your information.
-
 Employees Rules And Regulations Manpower Security Services Company Profile
Employees Rules And Regulations Manpower Security Services Company ProfileThis slide highlights the security guard company rules and regulations which showcases In and out time, note visitor name, and wear uniform at working hours. Deliver an outstanding presentation on the topic using this Employees Rules And Regulations Manpower Security Services Company Profile. Dispense information and present a thorough explanation of Regulations, Employees Rules, Highlights using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Employees Rules And Regulations Security Services Business Profile Ppt Sample
Employees Rules And Regulations Security Services Business Profile Ppt SampleThis slide highlights the security guard company rules and regulations which showcases In and out time, note visitor name, and wear uniform at working hours. Present the topic in a bit more detail with this Employees Rules And Regulations Security Services Business Profile Ppt Sample. Use it as a tool for discussion and navigation on Employees Rules, Regulations. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Data Security Protocols Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Cyber Data Security Protocols Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Cyber data security protocols colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Cyber Data Security Protocols Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Cyber Data Security Protocols Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Cyber data security protocols monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
 Data Security Protocols Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Data Security Protocols Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Data security protocols colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Data Security Protocols Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Data Security Protocols Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Data security protocols monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
 Lock Data Security Protocols Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Lock Data Security Protocols Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Lock data security protocols colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Lock Data Security Protocols Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Lock Data Security Protocols Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Lock data security protocols monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
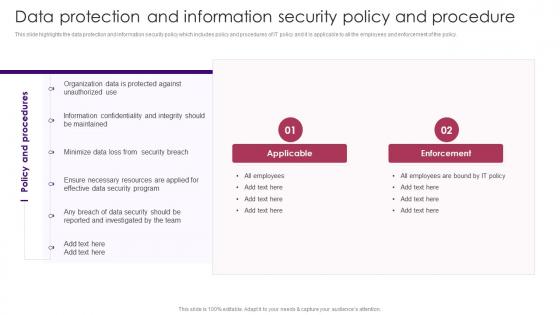 Data Protection And Information Security Policy And Procedure Staff Induction Training Guide
Data Protection And Information Security Policy And Procedure Staff Induction Training GuideThis slide highlights the data protection and information security policy which includes policy and procedures of IT policy and it is applicable to all the employees and enforcement of the policy. Present the topic in a bit more detail with this Data Protection And Information Security Policy And Procedure Staff Induction Training Guide. Use it as a tool for discussion and navigation on Applicable, Enforcement, Organization Data. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Information Security Protocol Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Information Security Protocol Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Information security protocol colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Information Security Protocol Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Information Security Protocol Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Information security protocol monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
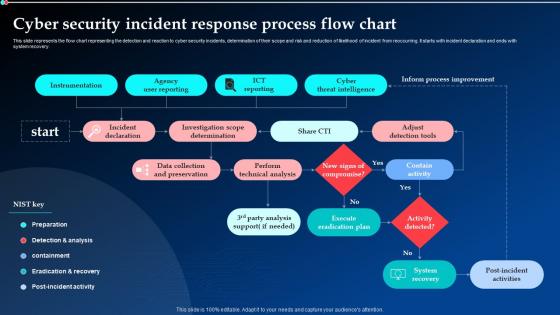 Cyber Security Incident Response Process Flow Chart Ppt Powerpoint Presentation Model File Formats
Cyber Security Incident Response Process Flow Chart Ppt Powerpoint Presentation Model File FormatsThis slide represents the flow chart representing the detection and reaction to cyber security incidents, determination of their scope and risk and reduction of likelihood of incident from reoccurring. It starts with incident declaration and ends with system recovery. Deliver an outstanding presentation on the topic using this Cyber Security Incident Response Process Flow Chart Ppt Powerpoint Presentation Model File Formats. Dispense information and present a thorough explanation of Instrumentation, Agency User Reporting, Cyber Threat Intelligence using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
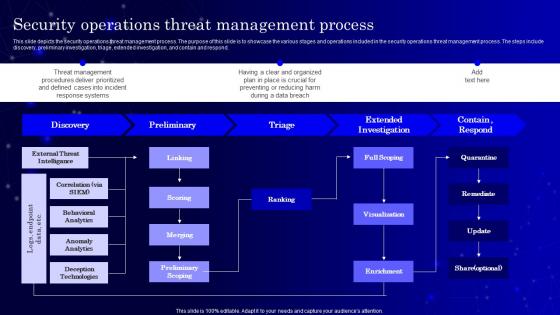 SecOps Security Operations Threat Management Process Ppt Professional
SecOps Security Operations Threat Management Process Ppt ProfessionalThis slide depicts the security operations threat management process. The purpose of this slide is to showcase the various stages and operations included in the security operations threat management process. The steps include discovery, preliminary investigation, triage, extended investigation, and contain and respond. Present the topic in a bit more detail with this SecOps Security Operations Threat Management Process Ppt Professional. Use it as a tool for discussion and navigation on External Threat Intelligance, Behavioral Analytics . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Process To Formulate Cyber Security Communication Plan
Process To Formulate Cyber Security Communication PlanThis slide provides information to develop a cyber security communication plan effectively and efficiently. It includes elements such as formulate committee, identify scenarios, draft statement, rehearse plan and regulatory compliance. Introducing our premium set of slides with Process To Formulate Cyber Security Communication Plan Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Formulate Committee, Draft Statement, Rehearse, Plan, Regulatory Compliance So download instantly and tailor it with your information.
-
 SASE IT Cloud Access Security Broker Working Process Ppt Powerpoint Demonstration
SASE IT Cloud Access Security Broker Working Process Ppt Powerpoint DemonstrationThis slide outlines the working process of a cloud access security broker. The purpose of this slide is to showcase the overview and working process steps of CASB. The main steps include discovery, classification, and remediation. Increase audience engagement and knowledge by dispensing information using SASE IT Cloud Access Security Broker Working Process Ppt Powerpoint Demonstration. This template helps you present information on one stages. You can also present information on Discovery, Classification, Remediation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
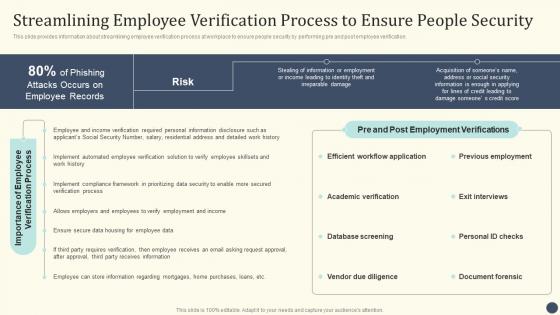 Essential Initiatives To Safeguard Streamlining Employee Verification Process To Ensure People Security
Essential Initiatives To Safeguard Streamlining Employee Verification Process To Ensure People SecurityThis slide provides information about streamlining employee verification process at workplace to ensure people security by performing pre and post employee verification. Present the topic in a bit more detail with this Essential Initiatives To Safeguard Streamlining Employee Verification Process To Ensure People Security. Use it as a tool for discussion and navigation on Academic Verification, Database Screening, Vendor Due Diligence This template is free to edit as deemed fit for your organization. Therefore download it now.




