Powerpoint Templates and Google slides for Access Manager
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Identity And Access Management Function As Security Tool IAM Process For Effective Access
Identity And Access Management Function As Security Tool IAM Process For Effective AccessThis slide showcases function of Identity and Access Management as a security tool. The purpose of this slide is to explain the function of IAM as an essential security tool these include context awareness, identity and access governance, and so on. Present the topic in a bit more detail with this Identity And Access Management Function As Security Tool IAM Process For Effective Access. Use it as a tool for discussion and navigation on Context Awareness, Identity And Access Governance, Management Function. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
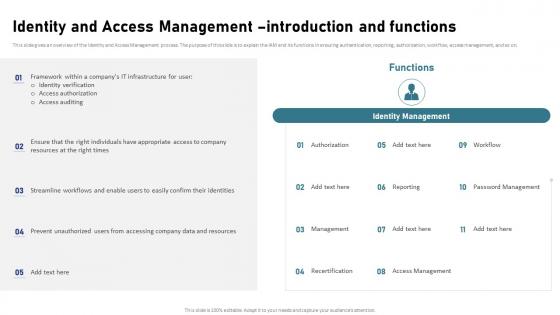 Identity And Access Management Introduction And Functions IAM Process For Effective Access
Identity And Access Management Introduction And Functions IAM Process For Effective AccessThis slide gives an overview of the Identity and Access Management process. The purpose of this slide is to explain the IAM and its functions in ensuring authentication, reporting, authorization, workflow, access management, and so on. Introducing Identity And Access Management Introduction And Functions IAM Process For Effective Access to increase your presentation threshold. Encompassed with eleven stages, this template is a great option to educate and entice your audience. Dispence information on Authorization, Password Management, Access Management, Recertification, using this template. Grab it now to reap its full benefits.
-
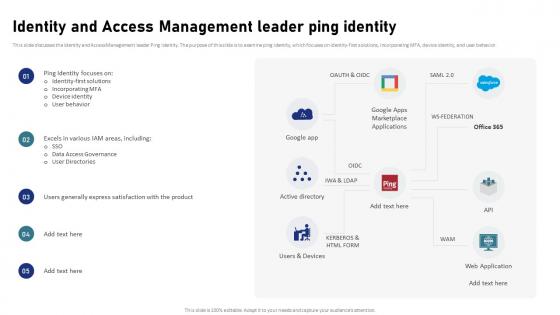 Identity And Access Management Leader Ping Identity IAM Process For Effective Access
Identity And Access Management Leader Ping Identity IAM Process For Effective AccessThis slide discusses the Identity and Access Management leader Ping identity. The purpose of this slide is to examine ping identity, which focuses on identity-first solutions, incorporating MFA, device identity, and user behavior. Present the topic in a bit more detail with this Identity And Access Management Leader Ping Identity IAM Process For Effective Access. Use it as a tool for discussion and navigation on Identity First Solutions, Incorporating MFA, Device Identity, User Behavior. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
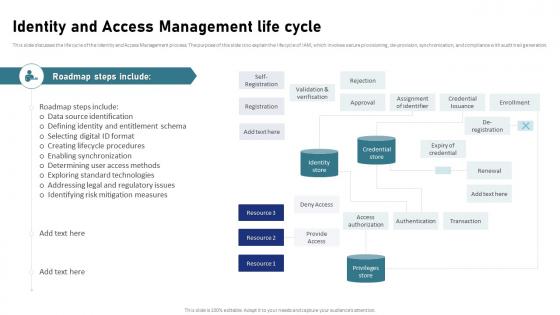 Identity And Access Management Life Cycle IAM Process For Effective Access
Identity And Access Management Life Cycle IAM Process For Effective AccessThis slide discusses the life cycle of the Identity and Access Management process. The purpose of this slide is to explain the life cycle of IAM, which involves secure provisioning, de-provision, synchronization, and compliance with audit trail generation. Deliver an outstanding presentation on the topic using this Identity And Access Management Life Cycle IAM Process For Effective Access. Dispense information and present a thorough explanation of Data Source Identification, Creating Lifecycle Procedures, Enabling Synchronization using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
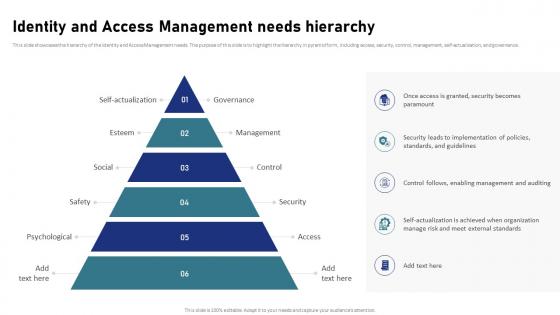 Identity And Access Management Needs Hierarchy IAM Process For Effective Access
Identity And Access Management Needs Hierarchy IAM Process For Effective AccessThis slide showcases the hierarchy of the Identity and Access Management needs. The purpose of this slide is to highlight the hierarchy in pyramid form, including access, security, control, management, self-actualization, and governance. Increase audience engagement and knowledge by dispensing information using Identity And Access Management Needs Hierarchy IAM Process For Effective Access. This template helps you present information on six stages. You can also present information on Identity And Access Management, Security, Control, Management, Self Actualization using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
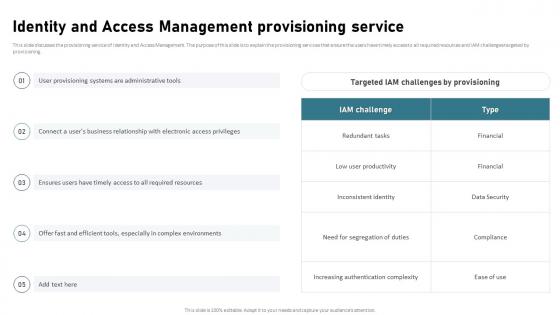 Identity And Access Management Provisioning Service IAM Process For Effective Access
Identity And Access Management Provisioning Service IAM Process For Effective AccessThis slide discusses the provisioning service of Identity and Access Management. The purpose of this slide is to explain the provisioning services that ensure the users have timely access to all required resources and IAM challenges targeted by provisioning. Deliver an outstanding presentation on the topic using this Identity And Access Management Provisioning Service IAM Process For Effective Access. Dispense information and present a thorough explanation of Identity And Access Management, Provisioning Service, Inconsistent Identity using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Identity And Access Management Regulatory Compliance Issue IAM Process For Effective Access
Identity And Access Management Regulatory Compliance Issue IAM Process For Effective AccessThis slide discusses the regulatory compliance issue of the Identity and Access Management process. The purpose of this slide is to explain the regulatory challenges of IAM these include the need for auditing, privacy control, and segregation of duties, etc. Present the topic in a bit more detail with this Identity And Access Management Regulatory Compliance Issue IAM Process For Effective Access. Use it as a tool for discussion and navigation on Identity And Access Management, Regulatory Compliance Issue, Segregation Of Duties, Privacy Control. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
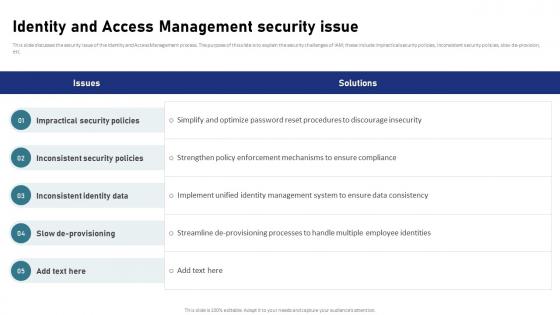 Identity And Access Management Security Issue IAM Process For Effective Access
Identity And Access Management Security Issue IAM Process For Effective AccessThis slide discusses the security issue of the Identity and Access Management process. The purpose of this slide is to explain the security challenges of IAM these include impractical security policies, inconsistent security policies, slow de-provision, etc. Deliver an outstanding presentation on the topic using this Identity And Access Management Security Issue IAM Process For Effective Access. Dispense information and present a thorough explanation of Impractical Security Policies, Inconsistent Security Policies, Inconsistent Identity Data using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
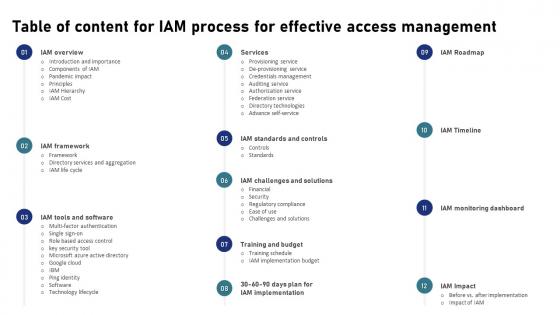 Table Of Content For IAM Process For Effective Access Management
Table Of Content For IAM Process For Effective Access ManagementIntroducing Table Of Content For IAM Process For Effective Access Management to increase your presentation threshold. Encompassed with twelve stages, this template is a great option to educate and entice your audience. Dispence information on IAM Monitoring Dashboard, Training And Budget, Services, Effective Access Management, using this template. Grab it now to reap its full benefits.
-
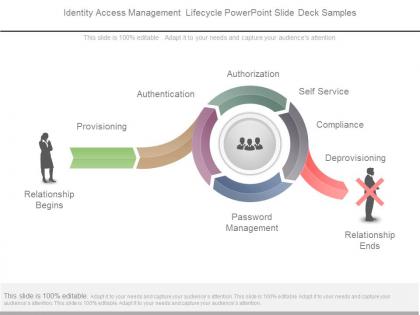 Identity access management lifecycle powerpoint slide deck samples
Identity access management lifecycle powerpoint slide deck samplesPresenting identity access management lifecycle powerpoint slide deck samples. This is a identity access management lifecycle powerpoint slide deck samples. This is a four stage process. The stages in this process are relationship begins, provisioning, authentication, authorization, self service, compliance, de provisioning, password management.
-
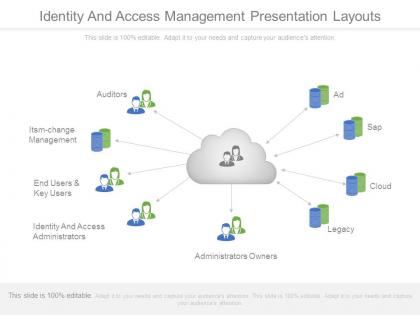 Identity and access management presentation layouts
Identity and access management presentation layoutsImpressive picture quality. High resolution of visuals ensures clear projection on wide screen. Compatible with multiple online and offline software. Harmonious with numerous formats like JPEG/JPG/PDF. Ease of executing changes in presentation as per individual preferences. Easy inclusion and exclusion of slide content as per the need of an hour. Personalize the content with your company name, logo and trademark. Professionally equipped and aesthetically designed set of slides. Widely accessible by students, teachers, engineers, entrepreneurs and IT professionals.
-
 Accessibility management diagram powerpoint slide templates
Accessibility management diagram powerpoint slide templatesPresenting accessibility management diagram powerpoint slide templates. This is a accessibility management diagram powerpoint slide templates. This is a five stage process. The stages in this process are assistive technology, availability report, capacity management, problem management, service level management.
-
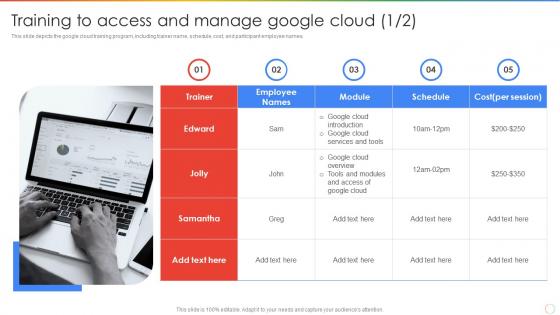 Training To Access And Manage Google Cloud Ppt Powerpoint Presentation Outline Introduction
Training To Access And Manage Google Cloud Ppt Powerpoint Presentation Outline IntroductionThis slide depicts the google cloud training program, including trainer name, schedule, cost, and participant employee names. Introducing Training To Access And Manage Google Cloud Ppt Powerpoint Presentation Outline Introduction to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Training To Access, Manage Google Cloud, using this template. Grab it now to reap its full benefits.
-
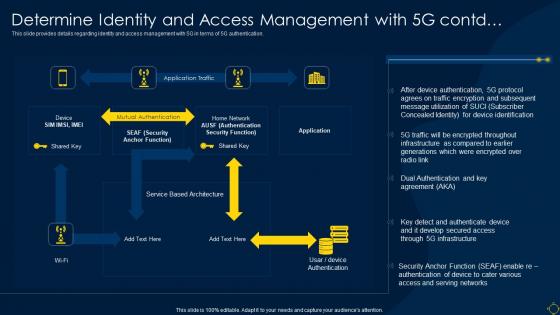 Determine Identity And Access Management With 5g Contd Deployment Of 5g Wireless System
Determine Identity And Access Management With 5g Contd Deployment Of 5g Wireless SystemThis slide provides details regarding identity and access management with 5G in terms of 5G authentication. Deliver an outstanding presentation on the topic using this Determine Identity And Access Management With 5g Contd Deployment Of 5g Wireless System. Dispense information and present a thorough explanation of Infrastructure, Generations, Management using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
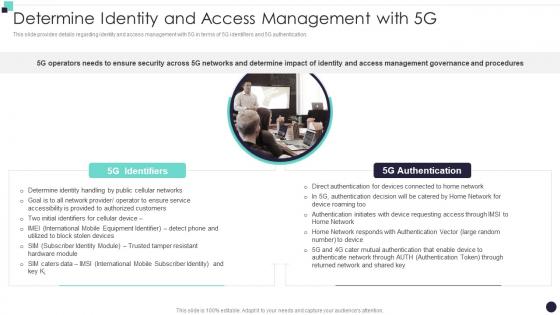 Determine Identity And Access Management With 5G Building 5G Wireless Mobile Network
Determine Identity And Access Management With 5G Building 5G Wireless Mobile NetworkThis slide provides details regarding identity and access management with 5G in terms of 5G identifiers and 5G authentication. Introducing Determine Identity And Access Management With 5G Building 5G Wireless Mobile Network to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Identifiers, Authentication, Access Management, using this template. Grab it now to reap its full benefits.
-
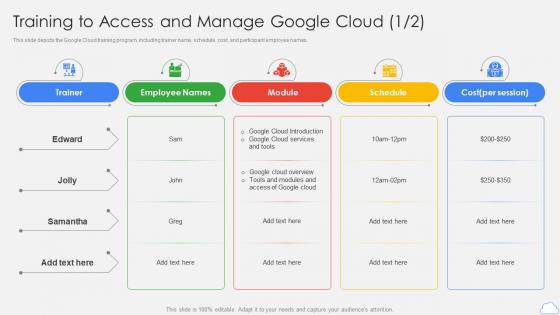 Google Cloud Platform Training To Access And Manage Google Cloud Ppt Infographics
Google Cloud Platform Training To Access And Manage Google Cloud Ppt InfographicsThis slide depicts the Google Cloud training program, including trainer name, schedule, cost, and participant employee names. Present the topic in a bit more detail with this Google Cloud Platform Training To Access And Manage Google Cloud Ppt Infographics. Use it as a tool for discussion and navigation on Schedule, Manage Google Cloud, Trainer. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 5G Technology Enabling Determine Identity And Access Management With 5G
5G Technology Enabling Determine Identity And Access Management With 5GThis slide provides details regarding identity and access management with 5G in terms of 5G identifiers and 5G authentication. Introducing 5G Technology Enabling Determine Identity And Access Management With 5G to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on 5G Identifiers, 5G Authentication, Determine Identity, using this template. Grab it now to reap its full benefits.
-
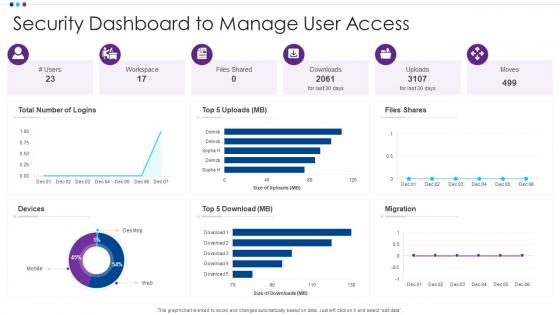 Security Dashboard To Manage User Access
Security Dashboard To Manage User AccessPresenting our well structured Security Dashboard To Manage User Access. The topics discussed in this slide are Migration, Security Dashboard, Manage User Access. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
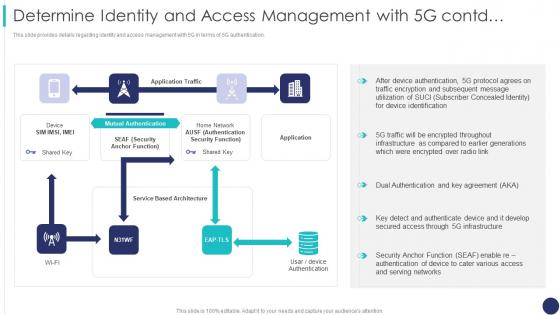 Determine Identity And Access Management With 5g Contd 5g Mobile Technology Guidelines Operators
Determine Identity And Access Management With 5g Contd 5g Mobile Technology Guidelines OperatorsThis slide provides details regarding identity and access management with 5G in terms of 5G authentication. Deliver an outstanding presentation on the topic using this Determine Identity And Access Management With 5g Contd 5g Mobile Technology Guidelines Operators. Dispense information and present a thorough explanation of Management, Authentication, Application using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
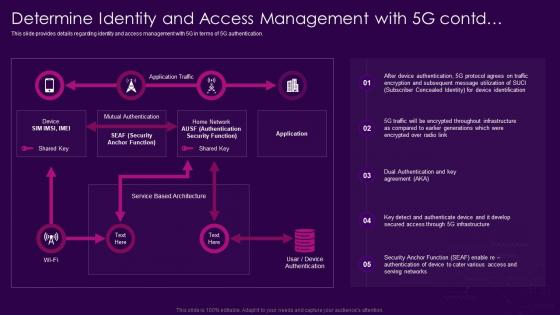 Determine Identity And Access Management With 5g Contd 5g Network Architecture Guidelines
Determine Identity And Access Management With 5g Contd 5g Network Architecture GuidelinesThis slide provides details regarding identity and access management with 5G in terms of 5G authentication. Deliver an outstanding presentation on the topic using this Determine Identity And Access Management With 5g Contd 5g Network Architecture Guidelines. Dispense information and present a thorough explanation of Management, Agreement, Infrastructure using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
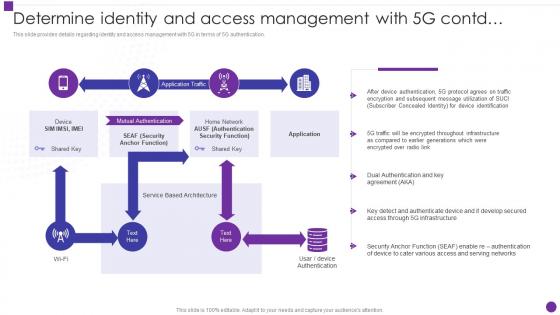 Determine Identity And Access Management With 5g Contd Developing 5g Transformative Technology
Determine Identity And Access Management With 5g Contd Developing 5g Transformative TechnologyThis slide provides details regarding identity and access management with 5G in terms of 5G authentication. Present the topic in a bit more detail with this Determine Identity And Access Management With 5g Contd Developing 5g Transformative Technology. Use it as a tool for discussion and navigation on Management, Generations, Infrastructure. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Privileged Access Management Ppt Powerpoint Presentation File Example Introduction Cpb
Privileged Access Management Ppt Powerpoint Presentation File Example Introduction CpbPresenting Privileged Access Management Ppt Powerpoint Presentation File Example Introduction Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Privileged Access Management. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
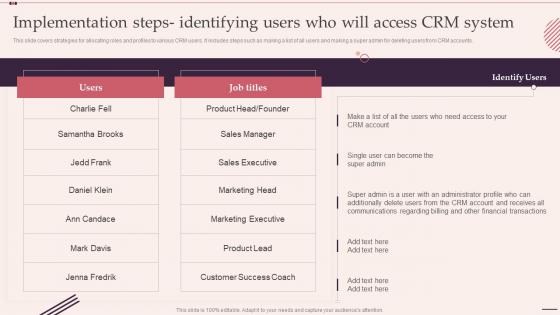 F504 Implementation Steps Identifying Users Who Will Access Customer Relationship Management System
F504 Implementation Steps Identifying Users Who Will Access Customer Relationship Management SystemThis slide covers strategies for allocating roles and profiles to various CRM users. It includes steps such as making a list of all users and making a super admin for deleting users from CRM accounts. Present the topic in a bit more detail with this F504 Implementation Steps Identifying Users Who Will Access Customer Relationship Management System. Use it as a tool for discussion and navigation on Implementation, Identifying, Strategies. This template is free to edit as deemed fit for your organization. Therefore download it now
-
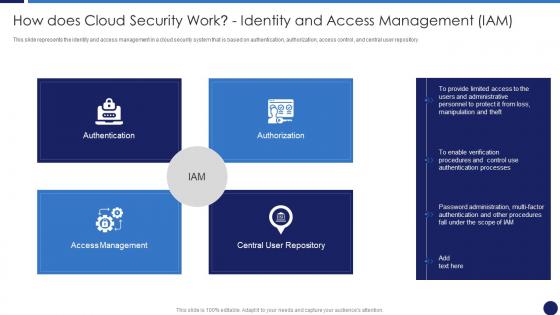 How Does Cloud Security Work Identity And Access Management Cloud Data Protection
How Does Cloud Security Work Identity And Access Management Cloud Data ProtectionThis slide represents the identity and access management in a cloud security system that is based on authentication, authorization, access control, and central user repository. Introducing How Does Cloud Security Work Identity And Access Management Cloud Data Protection to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispense information on Access Management, Authentication, Authorization, Central User Repository, using this template. Grab it now to reap its full benefits.
-
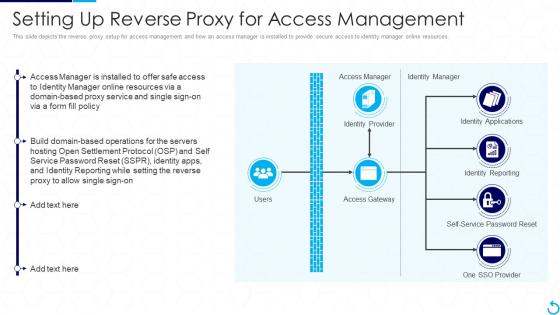 Reverse Proxy It Setting Up Reverse Proxy For Access Management
Reverse Proxy It Setting Up Reverse Proxy For Access ManagementThis slide depicts the reverse proxy setup for access management and how an access manager is installed to provide secure access to identity manager online resources. Present the topic in a bit more detail with this Reverse Proxy It Setting Up Reverse Proxy For Access Management. Use it as a tool for discussion and navigation on Management, Access Manager, Identity Provider. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
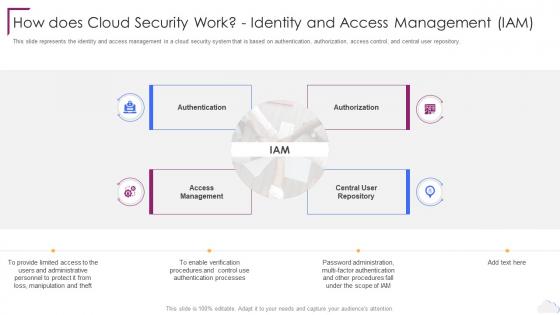 Cloud Computing Security How Does Cloud Security Work Identity And Access Management
Cloud Computing Security How Does Cloud Security Work Identity And Access ManagementThis slide represents the identity and access management in a cloud security system that is based on authentication, authorization, access control, and central user repository. Introducing Cloud Computing Security How Does Cloud Security Work Identity And Access Management to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Authentication, Authorization, Access Management, Central User Repository, using this template. Grab it now to reap its full benefits.
-
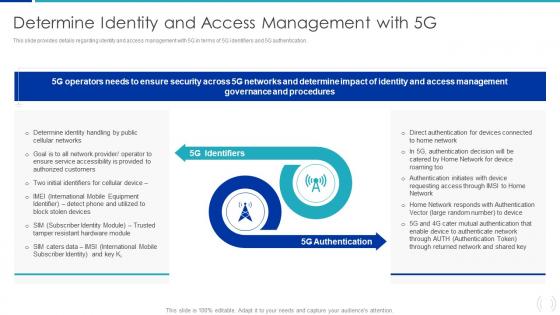 Determine Identity And Access Management With 5G Proactive Approach For 5G Deployment
Determine Identity And Access Management With 5G Proactive Approach For 5G DeploymentThis slide provides details regarding identity and access management with 5G in terms of 5G identifiers and 5G authentication. Introducing Determine Identity And Access Management With 5G Proactive Approach For 5G Deployment to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on 5G Identifiers, 5G Authentication, Governance, using this template. Grab it now to reap its full benefits.
-
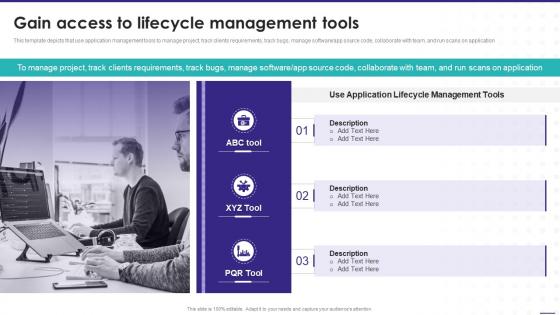 Gain Access To Lifecycle Management Tools Enterprise Software Playbook
Gain Access To Lifecycle Management Tools Enterprise Software PlaybookThis template depicts that use application management tools to manage project, track clients requirements, track bugs, manage software app source code, collaborate with team, and run scans on application. Increase audience engagement and knowledge by dispensing information using Gain Access To Lifecycle Management Tools Enterprise Software Playbook. This template helps you present information on three stages. You can also present information on Manage Project, Application Lifecycle, Management Tools using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Data Accessibility Management Goal On Multiple Domain Icon
Data Accessibility Management Goal On Multiple Domain IconIntroducing our Data Accessibility Management Goal On Multiple Domain Icon set of slides. The topics discussed in these slides are Data Accessibility, Management Goal, Multiple Domain Icon. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Examples Access Management In Powerpoint And Google Slides Cpb
Examples Access Management In Powerpoint And Google Slides CpbPresenting our Examples Access Management In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Examples Access Management This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
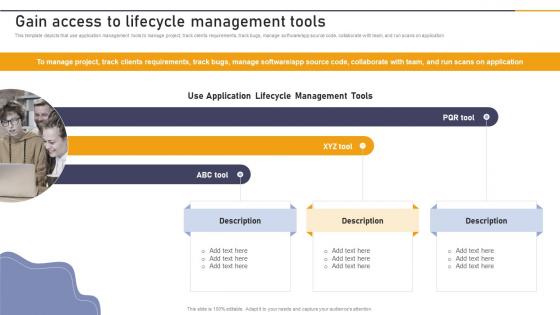 Gain Access To Lifecycle Management Tools Enterprise Application Playbook
Gain Access To Lifecycle Management Tools Enterprise Application PlaybookThis template depicts that use application management tools to manage project, track clients requirements, track bugs, manage software or app source code, collaborate with team, and run scans on application. Introducing Gain Access To Lifecycle Management Tools Enterprise Application Playbook to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Use Application, Lifecycle Management Tools, ABC Tool, using this template. Grab it now to reap its full benefits.
-
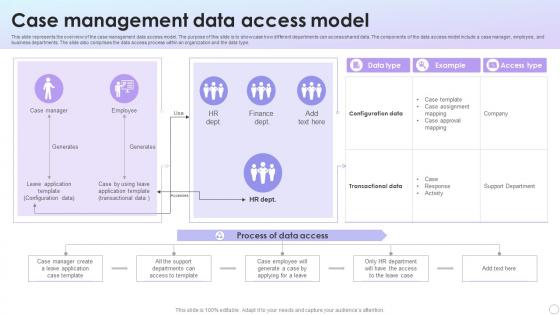 Case Management Data Access Model
Case Management Data Access ModelThis slide represents the overview of the case management data access model. The purpose of this slide is to showcase how different departments can access shared data. The components of the data access model include a case manager, employee, and business departments. The slide also comprises the data access process within an organization and the data type. Introducing our Case Management Data Access Model set of slides. The topics discussed in these slides are Data Type, Example, Access Type, Process Of Data Access. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Data Access Management Checklist For Businesses
Data Access Management Checklist For BusinessesThis slide outlines the checklist for data access management in an organization. The purpose of this slide is to enlist all the crucial tasks and steps. The key points include creating an inventory, identifying data ownership and location of data, creating security groups, conducting regular data audits, and creating a certification program. Introducing our Data Access Management Checklist For Businesses set of slides. The topics discussed in these slides are Create Inventory, Create Security Group, Conduct Regular Audits. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Icon For Server Data Access Management
Icon For Server Data Access ManagementPresenting our well structured Icon For Server Data Access Management. The topics discussed in this slide are Icon For Server Data, Access Management. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
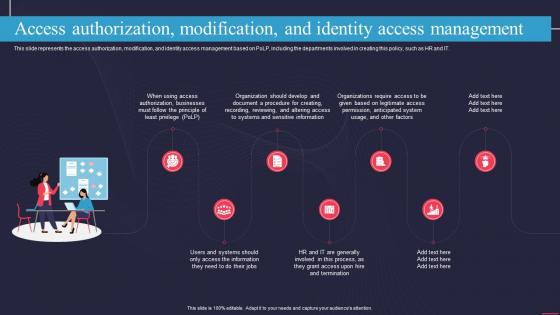 Access Authorization Modification And Identity Access Management Information Technology Policy
Access Authorization Modification And Identity Access Management Information Technology PolicyThis slide represents the access authorization, modification, and identity access management based on PoLP, including the departments involved in creating this policy, such as HR and IT. Increase audience engagement and knowledge by dispensing information using Access Authorization Modification And Identity Access Management Information Technology Policy. This template helps you present information on seven stages. You can also present information on Authorization, Businesses, Sensitive Information using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Determine Identity And Access Management With 5g Leading And Preparing For 5g World
Determine Identity And Access Management With 5g Leading And Preparing For 5g WorldThis slide provides details regarding identity and access management with 5G in terms of 5G identifiers and 5G authentication. Increase audience engagement and knowledge by dispensing information using Determine Identity And Access Management With 5g Leading And Preparing For 5g World. This template helps you present information on two stages. You can also present information on 5G Identifiers, 5G Authentication, Authorized Customers using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
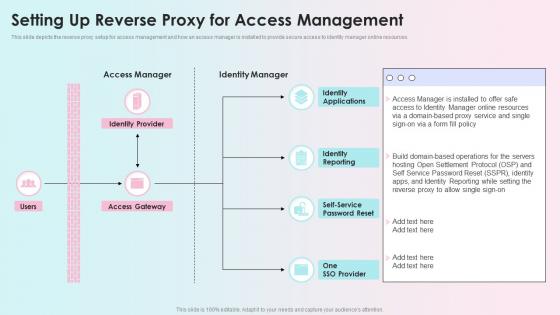 Setting Up Reverse Proxy For Access Management Reverse Proxy Load Balancer Ppt Rules
Setting Up Reverse Proxy For Access Management Reverse Proxy Load Balancer Ppt RulesThis slide depicts the reverse proxy setup for access management and how an access manager is installed to provide secure access to identity manager online resources. Present the topic in a bit more detail with this Setting Up Reverse Proxy For Access Management Reverse Proxy Load Balancer Ppt Rules. Use it as a tool for discussion and navigation on Identity Applications, Identity Reporting, Self Service Password Reset. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
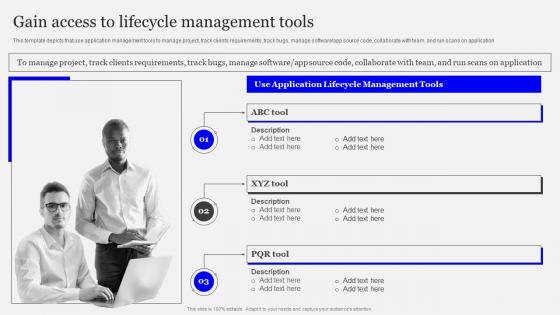 Gain Access To Lifecycle Management Tools Playbook Designing Developing Software
Gain Access To Lifecycle Management Tools Playbook Designing Developing SoftwareThis template depicts that use application management tools to manage project, track clients requirements, track bugs, manage software app source code, collaborate with team, and run scans on application. Introducing Gain Access To Lifecycle Management Tools Playbook Designing Developing Software to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Application Lifecycle, Management Tools, Gain Access, using this template. Grab it now to reap its full benefits.
-
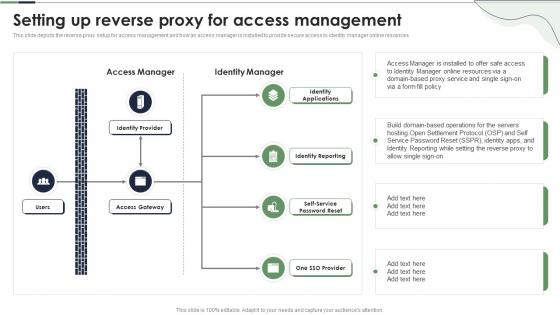 Setting Up Reverse Proxy For Access Management Ppt Powerpoint Presentation Gallery Themes
Setting Up Reverse Proxy For Access Management Ppt Powerpoint Presentation Gallery ThemesThis slide depicts the reverse proxy setup for access management and how an access manager is installed to provide secure access to identity manager online resources. Deliver an outstanding presentation on the topic using this Setting Up Reverse Proxy For Access Management Ppt Powerpoint Presentation Gallery Themes. Dispense information and present a thorough explanation of Identity Applications, Identity Reporting, Self Service Password Reset using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
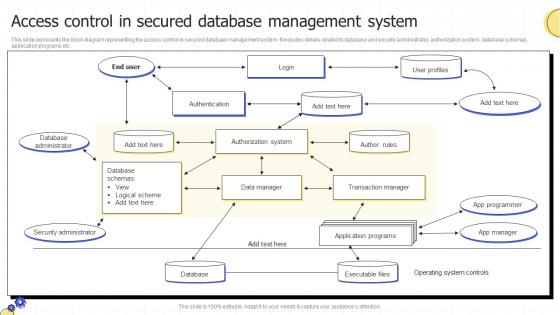 Access Control In Secured Database Management System
Access Control In Secured Database Management SystemThis slide represents the block diagram representing the access control in secured database management system. It includes details related to database and security administrator, authorization system, database schemas, application programs etc. Presenting our well structured Access Control In Secured Database Management System. The topics discussed in this slide are Access Control, Secured Database, Management System. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Gain Access To Lifecycle Management Tools Enterprise Software Development Playbook
Gain Access To Lifecycle Management Tools Enterprise Software Development PlaybookThis template depicts that use application management tools to manage project, track clients requirements, track bugs, manage software and app source code, collaborate with team, and run scans on application Present the topic in a bit more detail with this Gain Access To Lifecycle Management Tools Enterprise Software Development Playbook. Use it as a tool for discussion and navigation on Gain Access, Lifecycle, Management Tools. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Gain Access To Lifecycle Management Tools Design And Build Custom
Gain Access To Lifecycle Management Tools Design And Build CustomThis template depicts that use application management tools to manage project, track clients requirements, track bugs, manage software or app source code, collaborate with team, and run scans on application. Introducing Gain Access To Lifecycle Management Tools Design And Build Custom to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on ABC Tool, XYZ Tool, PQR Tool, using this template. Grab it now to reap its full benefits.
-
 Gain Access To Lifecycle Management Tools Playbook For Enterprise Software Firms
Gain Access To Lifecycle Management Tools Playbook For Enterprise Software FirmsThis template depicts that use application management tools to manage project, track clients requirements, track bugs, manage software app source code, collaborate with team, and run scans on application.Increase audience engagement and knowledge by dispensing information using Gain Access To Lifecycle Management Tools Playbook For Enterprise Software Firms. This template helps you present information on two stages. You can also present information on Apple Developer Enterprise, Program License, Organizations using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Customer Identity Access Management In Powerpoint And Google Slides Cpb
Customer Identity Access Management In Powerpoint And Google Slides CpbPresenting Customer Identity Access Management In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Customer Identity Access Management. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
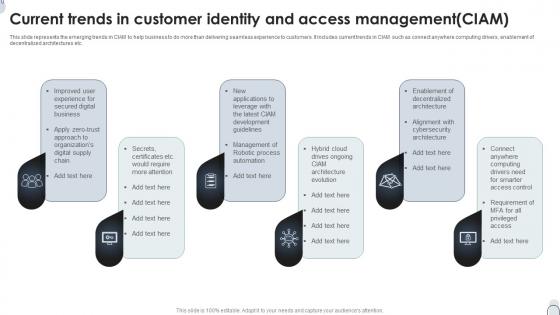 Current Trends In Customer Identity And Access Management CIAM
Current Trends In Customer Identity And Access Management CIAMThis slide represents the emerging trends in CIAM to help business to do more than delivering seamless experience to customers. It includes current trends in CIAM such as connect anywhere computing drivers, enablement of decentralized architectures etc. Introducing our premium set of slides with name Current Trends In Customer Identity And Access Management CIAM. Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Robotic Process, Digital Business, Architecture Evolution. So download instantly and tailor it with your information.
-
 Customer Identity And Access Management CIAM Framework Icon
Customer Identity And Access Management CIAM Framework IconIntroducing our Customer Identity And Access Management CIAM Framework Icon set of slides. The topics discussed in these slides are Customer Identity, Access Management, CIAM Framework Icon. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Customer Identity And Access Management CIAM Icon
Customer Identity And Access Management CIAM IconPresenting our set of slides with name Customer Identity And Access Management CIAM Icon. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Customer Identity, Access Management, CIAM Icon.
-
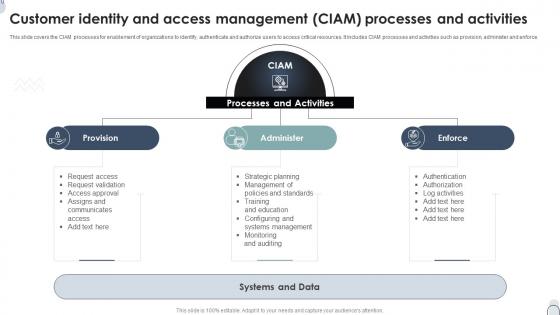 Customer Identity And Access Management CIAM Processes And Activities
Customer Identity And Access Management CIAM Processes And ActivitiesThis slide covers the CIAM processes for enablement of organizations to identify, authenticate and authorize users to access critical resources. It includes CIAM processes and activities such as provision, administer and enforce. Introducing our premium set of slides with name Customer Identity And Access Management CIAM Processes And Activities. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Processes And Activities, Systems And Data, Administer. So download instantly and tailor it with your information.
-
 Customer Identity And Access Management CIAM Tools Icon
Customer Identity And Access Management CIAM Tools IconPresenting our set of slides with name Customer Identity And Access Management CIAM Tools Icon. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Customer Identity, Access Management, CIAM Tools Icon.
-
 Brand Portfolio Management Components Of Brand Portfolio Strategy For Better Access Branding SS
Brand Portfolio Management Components Of Brand Portfolio Strategy For Better Access Branding SSThis slide covers the fundamental principles of creating an effective brand communication strategy. It includes guidelines such as building and leveraging strong corporate bonds, defining strategic objectives for brands, employing simple and clear brand architecture, etc. Introducing Brand Portfolio Management Components Of Brand Portfolio Strategy For Better Access Branding SS to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Price Or Value Relationship, Brand Architecture Or Linkage, Brand Positioning, using this template. Grab it now to reap its full benefits.
-
 IT Policy Access Authorization Modification And Identity Access Management
IT Policy Access Authorization Modification And Identity Access ManagementThis slide represents the access authorization, modification, and identity access management based on PoLP, including the departments involved in creating this policy, such as HR and IT. Introducing IT Policy Access Authorization Modification And Identity Access Management to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Access Authorization, Modification, Identity Access, using this template. Grab it now to reap its full benefits.
-
 Cyber Security Policy Access Authorization Modification And Identity Access Management
Cyber Security Policy Access Authorization Modification And Identity Access ManagementThis slide represents the access authorization, modification, and identity access management based on polp, including the departments involved in creating this policy, such as HR and IT. Increase audience engagement and knowledge by dispensing information using Cyber Security Policy Access Authorization Modification And Identity Access Management. This template helps you present information on seven stages. You can also present information on Management, Authorization, Modification using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
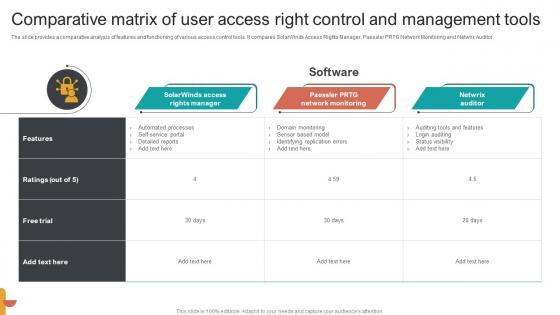 Comparative Matrix Of User Access Right Control And Management Tools
Comparative Matrix Of User Access Right Control And Management ToolsThe slide provides a comparative analysis of features and functioning of various access control tools. It compares SolarWinds Access Rights Manager, Paessler PRTG Network Monitoring and Netwrix Auditor. Introducing our Comparative Matrix Of User Access Right Control And Management Tools set of slides. The topics discussed in these slides are Solarwinds Access, Rights Manager, Paessler PRTG, Network Monitoring, Netwrix Auditor. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Identity And User Access Management Lifecycle
Identity And User Access Management LifecycleFollowing slide provides an outline of user identity lifecycle. It includes provisioning, authentication, authorization, self-services, password management, governance and deprovisioning. Presenting our set of slides with Identity And User Access Management Lifecycle. This exhibits information on seven stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Authentication, Authorization, Password Management, Governance.
-
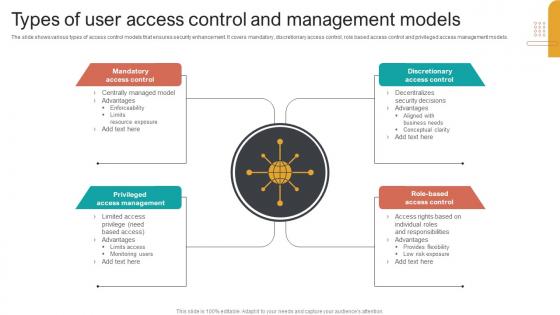 Types Of User Access Control And Management Models
Types Of User Access Control And Management ModelsThe slide shows various types of access control models that ensures security enhancement. It covers mandatory, discretionary access control, role based access control and privileged access management models. Introducing our premium set of slides with Types Of User Access Control And Management Models. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Mandatory Access Control, Discretionary Access Control, Role Based, Access Control. So download instantly and tailor it with your information.
-
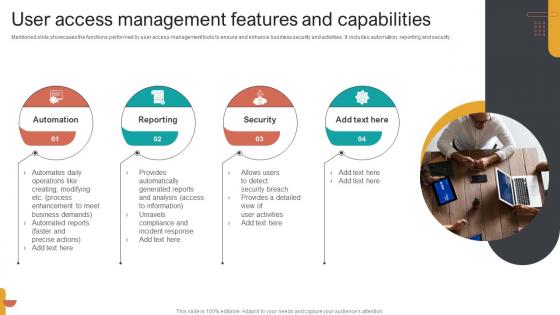 User Access Management Features And Capabilities
User Access Management Features And CapabilitiesMentioned slide showcases the functions performed by user access management tools to ensure and enhance business security and activities. it includes automation, reporting and security. Presenting our set of slides with User Access Management Features And Capabilities. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Automation, Reporting, Security.
-
 User Access Management Open Source Tools Icon
User Access Management Open Source Tools IconIntroducing our premium set of slides with User Access Management Open Source Tools Icon. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like User Access Management, Open Source Tools, Icon. So download instantly and tailor it with your information.
-
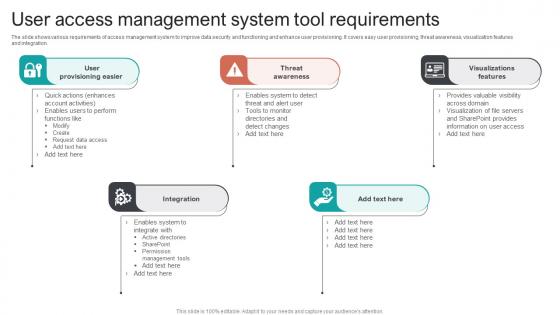 User Access Management System Tool Requirements
User Access Management System Tool RequirementsThe slide shows various requirements of access management system to improve data security and functioning and enhance user provisioning. It covers easy user provisioning, threat awareness, visualization features and integration. Presenting our set of slides with User Access Management System Tool Requirements. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on User Provisioning Easie, Threat Awareness, Visualizations Features.
-
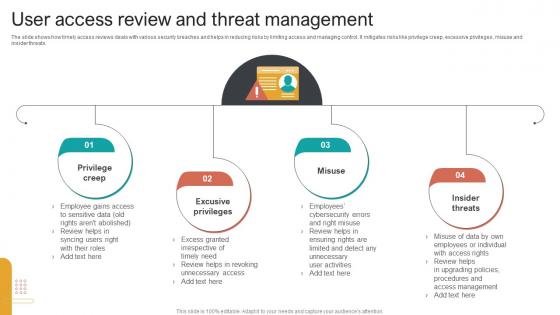 User Access Review And Threat Management
User Access Review And Threat ManagementThe slide shows how timely access reviews deals with various security breaches and helps in reducing risks by limiting access and managing control. It mitigates risks like privilege creep, excessive privileges, misuse and insider threats. Introducing our premium set of slides with User Access Review And Threat Management. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Privilege Creep, Excusive Privileges, Misuse Insider, Threats. So download instantly and tailor it with your information.
-
 User Identity And Access Management Audit Checklist Requirements
User Identity And Access Management Audit Checklist RequirementsFollowing slide provides checklist steps for a robust access management system to fulfil IAM identity access management audit requirements. It includes create security policy, forming formal procedures, user account management and documentation management. Presenting our set of slides with User Identity And Access Management Audit Checklist Requirements. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Create Security Policy, Develop Formal Procedures, User Account Management.