Powerpoint Templates and Google slides for Attacking
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Man In The Middle Attack Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Man In The Middle Attack Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Man in the middle attack colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Man In The Middle Attack Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Man In The Middle Attack Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Man in the middle attack monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
 MITM Attack Colored Icon In Powerpoint Pptx Png And Editable Eps Format
MITM Attack Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Mitm attack colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 MITM Attack Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
MITM Attack Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Mitm attack monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
 Deal Ransomware Attacks In Powerpoint And Google Slides Cpb
Deal Ransomware Attacks In Powerpoint And Google Slides CpbPresenting Deal Ransomware Attacks In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Deal Ransomware Attacks. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Application Layer Attacks In Powerpoint And Google Slides Cpb
Application Layer Attacks In Powerpoint And Google Slides CpbPresenting Application Layer Attacks In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Application Layer Attacks. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
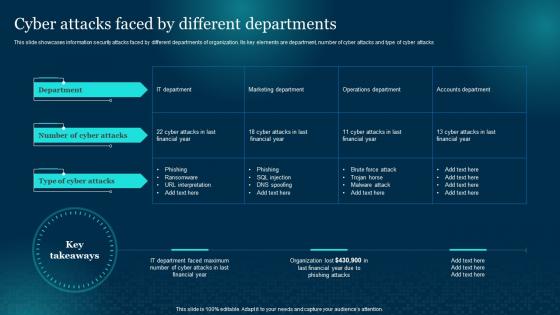 Cybersecurity Risk Analysis And Management Plan Cyber Attacks Faced By Different Departments
Cybersecurity Risk Analysis And Management Plan Cyber Attacks Faced By Different DepartmentsThis slide showcases information security attacks faced by different departments of organization. Its key elements are department, number of cyber attacks and type of cyber attacks Present the topic in a bit more detail with this Cybersecurity Risk Analysis And Management Plan Cyber Attacks Faced By Different Departments. Use it as a tool for discussion and navigation on Departments, Information, Cyber Attacks. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
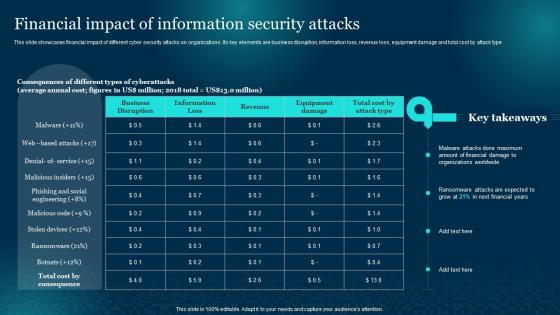 Financial Impact Of Information Security Attacks Cybersecurity Risk Analysis And Management Plan
Financial Impact Of Information Security Attacks Cybersecurity Risk Analysis And Management PlanThis slide showcases financial impact of different cyber security attacks on organizations. Its key elements are business disruption, information loss, revenue loss, equipment damage and total cost by attack type Present the topic in a bit more detail with this Financial Impact Of Information Security Attacks Cybersecurity Risk Analysis And Management Plan. Use it as a tool for discussion and navigation on Financial, Information, Organizations. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Information Security Attacks Faced By Organization Cybersecurity Risk Analysis And Management Plan
Information Security Attacks Faced By Organization Cybersecurity Risk Analysis And Management PlanThis slide showcases most common information attacks faced by organization. It includes - malware, phishing, man in the middle attack, SQL injection, zero day exploit and DNS attack Increase audience engagement and knowledge by dispensing information using Information Security Attacks Faced By Organization Cybersecurity Risk Analysis And Management Plan. This template helps you present information on six stages. You can also present information on Information, Organization, Phishing using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Coordinated Criminal Botnet Attack Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Coordinated Criminal Botnet Attack Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Coordinated criminal botnet attack colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Coordinated Criminal Botnet Attack Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Coordinated Criminal Botnet Attack Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Coordinated criminal botnet attack monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
 Robotic Criminal Botnet Attack Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Robotic Criminal Botnet Attack Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Robotic criminal botnet attack colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Robotic Criminal Botnet Attack Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Robotic Criminal Botnet Attack Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Robotic criminal botnet attack monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
 Cyber Attack Mitigation Strategies In Powerpoint And Google Slides Cpb
Cyber Attack Mitigation Strategies In Powerpoint And Google Slides CpbPresenting our er Attack Mitigation Strategies In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Cyber Attack Mitigation Strategies This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Security Threats Commerce Attacking Methods In Powerpoint And Google Slides Cpb
Security Threats Commerce Attacking Methods In Powerpoint And Google Slides CpbPresenting Security Threats Commerce Attacking Methods In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase five stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Security Threats Commerce Attacking Methods. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Attacks Work In Powerpoint And Google Slides Cpb
Attacks Work In Powerpoint And Google Slides CpbPresenting our Attacks Work In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Attacks Work. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Cyber Attacks Faced By Different Departments Formulating Cybersecurity Plan
Cyber Attacks Faced By Different Departments Formulating Cybersecurity PlanThis slide showcase information security attacks faced by different departments of organization. Its key elements are department, number of cyber attacks and type of cyber attacks. Present the topic in a bit more detail with this Cyber Attacks Faced By Different Departments Formulating Cybersecurity Plan. Use it as a tool for discussion and navigation on Marketing Department, Operations Department, Accounts Department. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
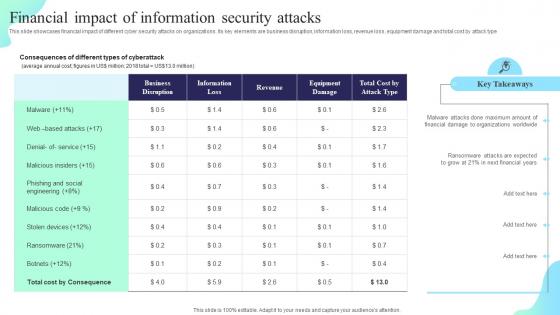 Financial Impact Of Information Security Attacks Formulating Cybersecurity Plan
Financial Impact Of Information Security Attacks Formulating Cybersecurity PlanThis slide showcases financial impact of different cyber security attacks on organizations. Its key elements are business disruption, information loss, revenue loss, equipment damage and total cost by attack type. Present the topic in a bit more detail with this Financial Impact Of Information Security Attacks Formulating Cybersecurity Plan. Use it as a tool for discussion and navigation on Financial Impact, Information, Security Attacks. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
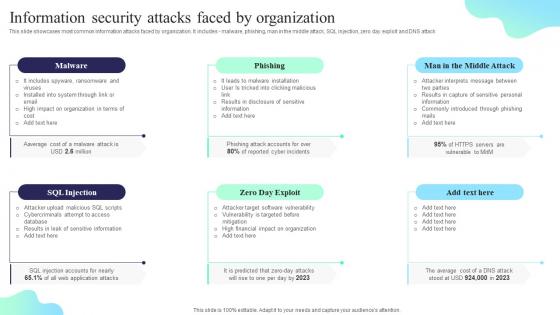 Information Security Attacks Faced By Organization Formulating Cybersecurity Plan
Information Security Attacks Faced By Organization Formulating Cybersecurity PlanThis slide showcases most common information attacks faced by organization. It includes malware, phishing, man in the middle attack, SQL injection, zero day exploit and DNS attack. Present the topic in a bit more detail with this Information Security Attacks Faced By Organization Formulating Cybersecurity Plan. Use it as a tool for discussion and navigation on Malware, Phishing, Organization. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Impact Cyber Attacks In Powerpoint And Google Slides Cpb
Impact Cyber Attacks In Powerpoint And Google Slides CpbPresenting Impact Cyber Attacks In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase five stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Impact Cyber Attacks. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Help Anxiety Attacks In Powerpoint And Google Slides Cpb
Help Anxiety Attacks In Powerpoint And Google Slides CpbPresenting Help Anxiety Attacks In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Help Anxiety Attacks. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
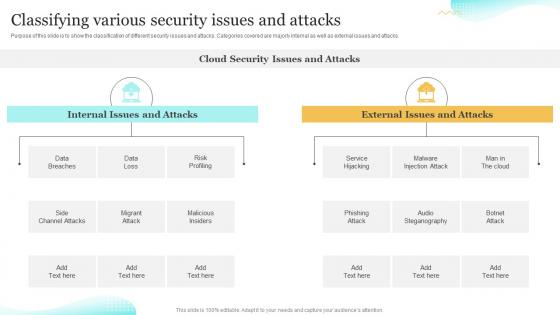 Classifying Various Security Issues And Attacks Upgrading Cybersecurity With Incident Response Playbook
Classifying Various Security Issues And Attacks Upgrading Cybersecurity With Incident Response PlaybookPurpose of this slide is to show the classification of different security issues and attacks. Categories covered are majorly internal as well as external issues and attacks. Deliver an outstanding presentation on the topic using this Classifying Various Security Issues And Attacks Upgrading Cybersecurity With Incident Response Playbook. Dispense information and present a thorough explanation of Classifying, Steganography, Classification using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Agenda For Implementing Security Awareness Training To Prevent Cyber Attacks
Agenda For Implementing Security Awareness Training To Prevent Cyber AttacksIntroducing Agenda For Implementing Security Awareness Training To Prevent Cyber Attacks to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Awareness Campaign, Cyber Security, Awareness Training, using this template. Grab it now to reap its full benefits.
-
 Dos And Donts Of Prevention From Ransomware Attack Implementing Security Awareness Training
Dos And Donts Of Prevention From Ransomware Attack Implementing Security Awareness TrainingThe purpose of this slide is to showcase the Dos and donts of ransomware prevention attack. The slide covers information about updating the software, installing a firewall software, using reliable website and sources etc. Introducing Dos And Donts Of Prevention From Ransomware Attack Implementing Security Awareness Training to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Prevention, Ransomware Attack, using this template. Grab it now to reap its full benefits.
-
 G33 Table Of Contents Implementing Security Awareness Training To Prevent Cyber Attacks
G33 Table Of Contents Implementing Security Awareness Training To Prevent Cyber AttacksIntroducing G33 Table Of Contents Implementing Security Awareness Training To Prevent Cyber Attacks to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispence information on Current Assessment, Organization, Cyber Security, using this template. Grab it now to reap its full benefits.
-
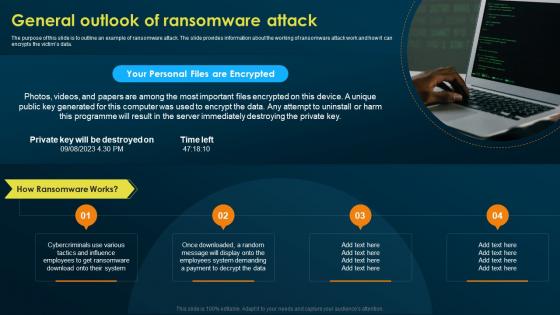 General Outlook Of Ransomware Attack Implementing Security Awareness Training
General Outlook Of Ransomware Attack Implementing Security Awareness TrainingThe purpose of this slide is to outline an example of ransomware attack. The slide provides information about the working of ransomware attack work and how it can encrypts the victims data. Increase audience engagement and knowledge by dispensing information using General Outlook Of Ransomware Attack Implementing Security Awareness Training. This template helps you present information on four stages. You can also present information on Programme, General Outlook, Ransomware Attack using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Icons Slide For Implementing Security Awareness Training To Prevent Cyber Attacks
Icons Slide For Implementing Security Awareness Training To Prevent Cyber AttacksIntroducing our well researched set of slides titled Icons Slide For Implementing Security Awareness Training To Prevent Cyber Attacks. It displays a hundred percent editable icons. You can use these icons in your presentation to captivate your audiences attention. Download now and use it multiple times.
-
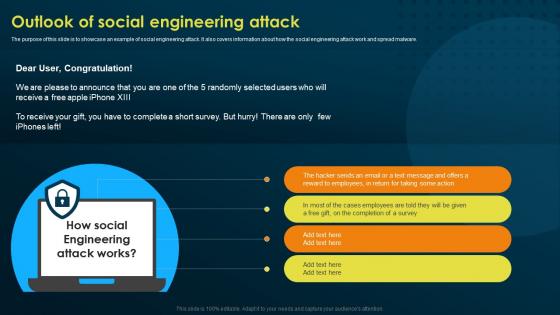 Outlook Of Social Engineering Attack Implementing Security Awareness Training
Outlook Of Social Engineering Attack Implementing Security Awareness TrainingThe purpose of this slide is to showcase an example of social engineering attack. It also covers information about how the social engineering attack work and spread malware. Introducing Outlook Of Social Engineering Attack Implementing Security Awareness Training to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispence information on Engineering Attack, Completion Of A Survey, Social Engineering Attack, using this template. Grab it now to reap its full benefits.
-
 Overview Of Business Email Compromise Attack Implementing Security Awareness Training
Overview Of Business Email Compromise Attack Implementing Security Awareness TrainingThe purpose of this slide is to delineate an example of business email compromise attack. Information covered in this slide is related to the working of this attack and how it can result in loss of company reputation. Increase audience engagement and knowledge by dispensing information using Overview Of Business Email Compromise Attack Implementing Security Awareness Training. This template helps you present information on four stages. You can also present information on Business, Compromise Attack, Risk Assessment using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Critical Infrastructure Cyber Attacks In Powerpoint And Google Slides Cpb
Critical Infrastructure Cyber Attacks In Powerpoint And Google Slides CpbPresenting our Critical Infrastructure Cyber Attacks In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Critical Infrastructure Cyber Attacks. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Botnet Hacking Network Attack Icon
Botnet Hacking Network Attack IconPresenting our set of slides with Botnet Hacking Network Attack Icon. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Botnet Hacking Network, Attack Icon.
-
 Coordinated Criminal Botnet Attack Icon
Coordinated Criminal Botnet Attack IconPresenting our well structured Coordinated Criminal Botnet Attack Icon. The topics discussed in this slide are Coordinated Criminal Botnet, Attack Icon. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
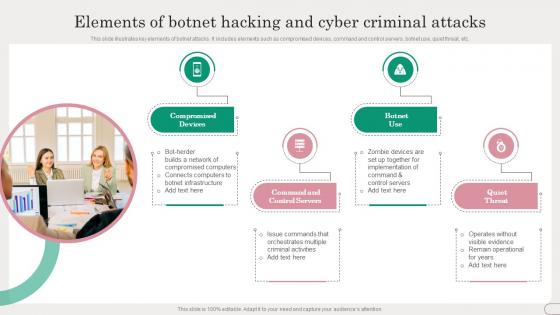 Elements Of Botnet Hacking And Cyber Criminal Attacks
Elements Of Botnet Hacking And Cyber Criminal AttacksThis slide illustrates key elements of botnet attacks. It includes elements such as compromised devices, command and control servers, botnet use, quiet threat, etc. Introducing our premium set of slides with Elements Of Botnet Hacking And Cyber Criminal Attacks. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Command and Control Servers. So download instantly and tailor it with your information.
-
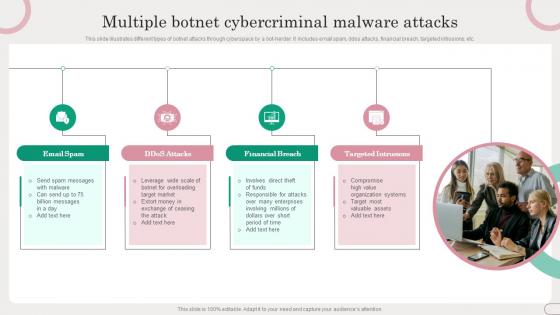 Multiple Botnet Cybercriminal Malware Attacks
Multiple Botnet Cybercriminal Malware AttacksThis slide illustrates different types of botnet attacks through cyberspace by a bot-herder. It includes email spam, ddos attacks, financial breach, targeted intrusions, etc. Presenting our set of slides with Multiple Botnet Cybercriminal Malware Attacks. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Email Spam, Financial Breach.
-
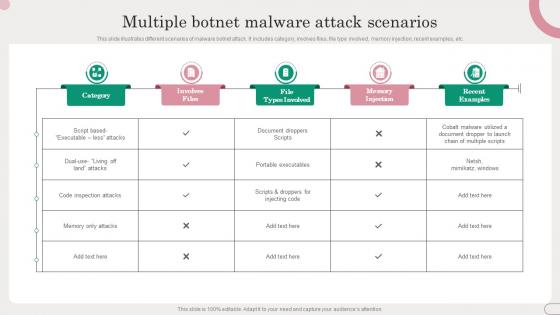 Multiple Botnet Malware Attack Scenarios
Multiple Botnet Malware Attack ScenariosThis slide illustrates different scenarios of malware botnet attack. It includes category, involves files, file type involved, memory injection, recent examples, etc. Introducing our Multiple Botnet Malware Attack Scenarios set of slides. The topics discussed in these slides are Code Inspection Attacks, Portable Executables. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
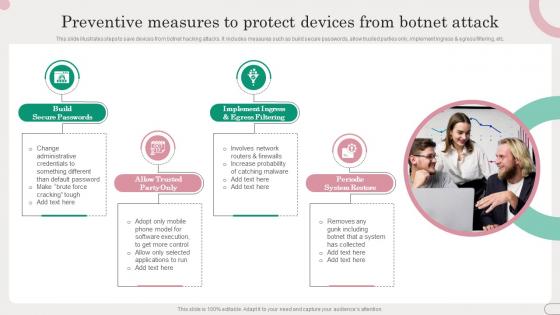 Preventive Measures To Protect Devices From Botnet Attack
Preventive Measures To Protect Devices From Botnet AttackThis slide illustrates steps to save devices from botnet hacking attacks. It includes measures such as build secure passwords, allow trusted parties only, implement ingress and egress filtering, etc. Introducing our premium set of slides with Preventive Measures To Protect Devices From Botnet Attack. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Build Secure Passwords, Periodic System Restore. So download instantly and tailor it with your information.
-
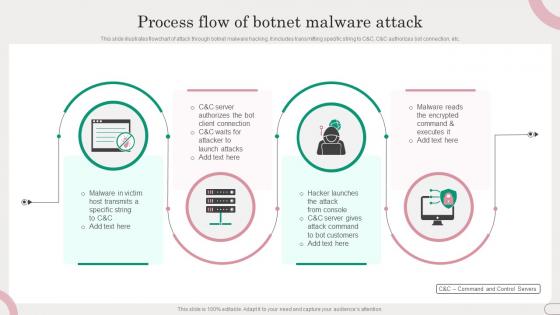 Process Flow Of Botnet Malware Attack
Process Flow Of Botnet Malware AttackThis slide illustrates flowchart of attack through botnet malware hacking. It includes transmitting specific string to C and C, C and C authorizes bot connection, etc. Presenting our set of slides with Process Flow Of Botnet Malware Attack. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Hacker Launches, Attack From Console.
-
 Stages Of Botnet Malware Cybercriminal Attacks
Stages Of Botnet Malware Cybercriminal AttacksThis slide illustrates how to create a bot and orchestrating a botnet attack. It includes stages such as expose, infect and grow, activate, etc. Introducing our premium set of slides with Stages Of Botnet Malware Cybercriminal Attacks. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Expose, Infect And Grow, Activate. So download instantly and tailor it with your information.
-
 Annual Statistical Trends In Cyber Attack
Annual Statistical Trends In Cyber AttackThe following slide depicts some key trends in cyber threats happening across the globe. It includes some facts and figures related to the malware attack, data breach records, annual losses etc. Presenting our set of slides with Annual Statistical Trends In Cyber Attack. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Facts And Figures.
-
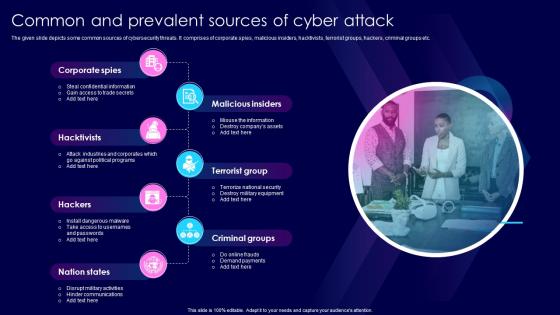 Common And Prevalent Sources Of Cyber Attack
Common And Prevalent Sources Of Cyber AttackThe given slide depicts some common sources of cybersecurity threats. It comprises of corporate spies, malicious insiders, hacktivists, terrorist groups, hackers, criminal groups etc. Introducing our premium set of slides with Common And Prevalent Sources Of Cyber Attack. Ellicudate the seven stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Malicious Insiders, Corporate Spies. So download instantly and tailor it with your information.
-
 Cyber Attack Alert Icon With Desktop Screen
Cyber Attack Alert Icon With Desktop ScreenPresenting our set of slides with Cyber Attack Alert Icon With Desktop Screen. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cyber Attack Alert Icon, Desktop Screen.
-
 Cyber Attack Icon With Man In Black Hood
Cyber Attack Icon With Man In Black HoodPresenting our set of slides with Cyber Attack Icon With Man In Black Hood. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cyber Attack Icon, Man Black Hood.
-
 Cyber Security Checklist To Mitigate Threats Of Attack
Cyber Security Checklist To Mitigate Threats Of AttackThe given slide provides the key activities to be done to alleviate the effects of cyber threats. It includes managing social media profiles, backing up the data, crosschecking privacy and security settings etc. Introducing our premium set of slides with Cyber Security Checklist To Mitigate Threats Of Attack. Ellicudate the seven stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cyber Security Checklist, Mitigate Threats Attack. So download instantly and tailor it with your information.
-
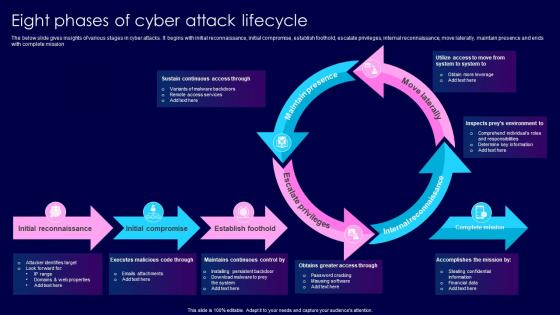 Eight Phases Of Cyber Attack Lifecycle
Eight Phases Of Cyber Attack LifecycleThe below slide gives insights of various stages in cyber attacks. It begins with initial reconnaissance, initial compromise, establish foothold, escalate privileges, internal reconnaissance, move laterally, maintain presence and ends with complete mission. Presenting our well structured Eight Phases Of Cyber Attack Lifecycle. The topics discussed in this slide are Move Laterally, Escalate Privileges, Maintain Presence. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
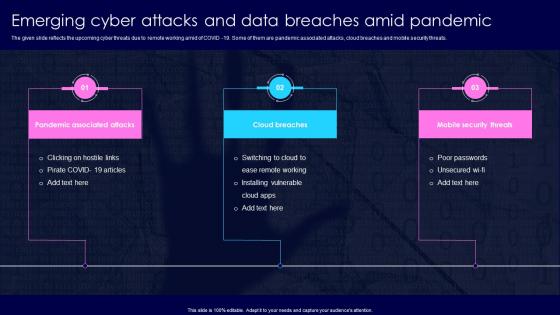 Emerging Cyber Attacks And Data Breaches Amid Pandemic
Emerging Cyber Attacks And Data Breaches Amid PandemicThe given slide reflects the upcoming cyber threats due to remote working amid of COVID 19. Some of them are pandemic associated attacks, cloud breaches and mobile security threats. Presenting our set of slides with Emerging Cyber Attacks And Data Breaches Amid Pandemic. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cloud Breaches, Mobile Security Threats.
-
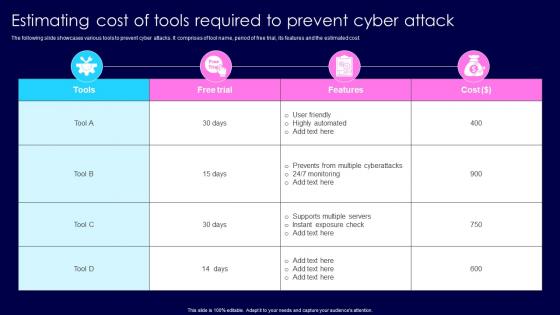 Estimating Cost Of Tools Required To Prevent Cyber Attack
Estimating Cost Of Tools Required To Prevent Cyber AttackThe following slide showcases various tools to prevent cyber attacks. It comprises of tool name, period of free trial, its features and the estimated cost. Introducing our Estimating Cost Of Tools Required To Prevent Cyber Attack set of slides. The topics discussed in these slides are Highly Automated, Supports Multiple Servers. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
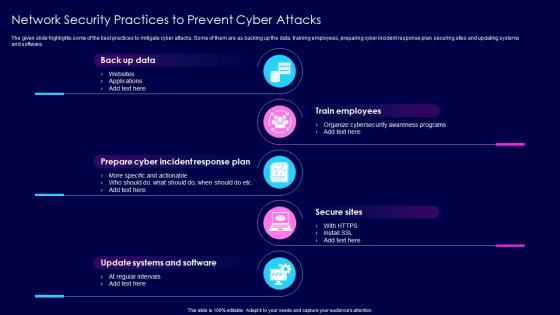 Network Security Practices To Prevent Cyber Attacks
Network Security Practices To Prevent Cyber AttacksThe given slide highlights some of the best practices to mitigate cyber attacks. Some of them are as backing up the data, training employees, preparing cyber incident response plan, securing sites and updating systems and software. Presenting our set of slides with Network Security Practices To Prevent Cyber Attacks. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Train Employees, Secure Sites.
-
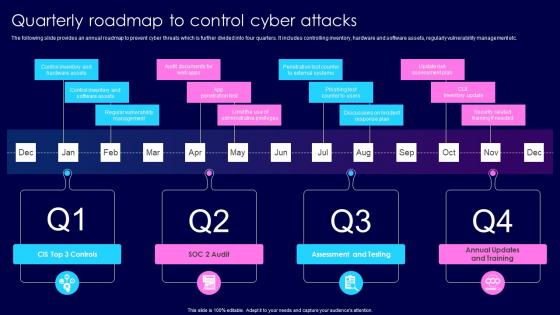 Quarterly Roadmap To Control Cyber Attacks
Quarterly Roadmap To Control Cyber AttacksThe following slide provides an annual roadmap to prevent cyber threats which is further divided into four quarters. It includes controlling inventory, hardware and software assets, regularly vulnerability management etc. Introducing our premium set of slides with Quarterly Roadmap To Control Cyber Attacks. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Assessment, Testing, Annual Updates, Training. So download instantly and tailor it with your information.
-
 Six Common Types Of Cyber Attacks
Six Common Types Of Cyber AttacksThe following slide represents the common types of cyber threats. It includes malware, phishing, password attacks, drive by downloads, man in the middle and denial of service attacks. Presenting our set of slides with Six Common Types Of Cyber Attacks. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Visiting Sites, Hacking Passwords.
-
 Recent Attacks Critical Infrastructure In Powerpoint And Google Slides Cpb
Recent Attacks Critical Infrastructure In Powerpoint And Google Slides CpbPresenting our Recent Attacks Critical Infrastructure In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Recent Attacks Critical Infrastructure This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Social Engineering Attacks Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Social Engineering Attacks Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Social engineering attacks colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Social Engineering Attacks Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Social Engineering Attacks Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Social engineering attacks monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
 Social Engineering Phishing Attacks Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Social Engineering Phishing Attacks Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Social engineering phishing attacks colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Social Engineering Phishing Attacks Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Social Engineering Phishing Attacks Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Social engineering phishing attacks monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
 Insider Attack In Powerpoint And Google Slides Cpb
Insider Attack In Powerpoint And Google Slides CpbPresenting our Insider Attack In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Insider Attack. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Input Validation Attacks In Powerpoint And Google Slides Cpb
Input Validation Attacks In Powerpoint And Google Slides CpbPresenting our Input Validation Attacks In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Input Validation Attacks This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Input Validation Vulnerability Attack In Powerpoint And Google Slides Cpb
Input Validation Vulnerability Attack In Powerpoint And Google Slides CpbPresenting our Input Validation Vulnerability Attack In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Input Validation Vulnerability Attack This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Types Internet Attacks In Powerpoint And Google Slides Cpb
Types Internet Attacks In Powerpoint And Google Slides CpbPresenting Types Internet Attacks In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Types Internet Attacks. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Addressing The Various Security Incidents And Attacks Cybersecurity Incident And Vulnerability
Addressing The Various Security Incidents And Attacks Cybersecurity Incident And VulnerabilityPurpose of this slide is to educate team members about different security incidents and attacks. It includes information about traditional security incidents, cyber security attacks and common techniques. Increase audience engagement and knowledge by dispensing information using Addressing The Various Security Incidents And Attacks Cybersecurity Incident And Vulnerability. This template helps you present information on three stages. You can also present information on Traditional IT Security Incidents, Cyber Security Attacks, Common Techniques using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
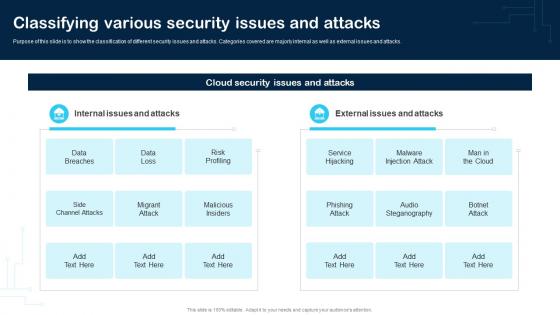 Classifying Various Security Issues And Attacks Cybersecurity Incident And Vulnerability
Classifying Various Security Issues And Attacks Cybersecurity Incident And VulnerabilityPurpose of this slide is to show the classification of different security issues and attacks. Categories covered are majorly internal as well as external issues and attacks. Present the topic in a bit more detail with this Classifying Various Security Issues And Attacks Cybersecurity Incident And Vulnerability. Use it as a tool for discussion and navigation on Data Breaches, Data Loss, Risk Profiling. This template is free to edit as deemed fit for your organization. Therefore download it now.



