Powerpoint Templates and Google slides for Cyber Security Icon
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
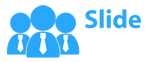
 Importance Of Cyber Security In Automotive Systems
Importance Of Cyber Security In Automotive SystemsThis slide highlights relevance of cyber security in vehicles. The purpose of this slide is to aid professionals in ensuring safety, privacy and functionality of automobiles against potential cyber threats and attacks. It includes elements such as safety, data protection, etc. Presenting our set of slides with Importance Of Cyber Security In Automotive Systems This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Data Protection, Vehicle Integrity, Financial Implications.
-
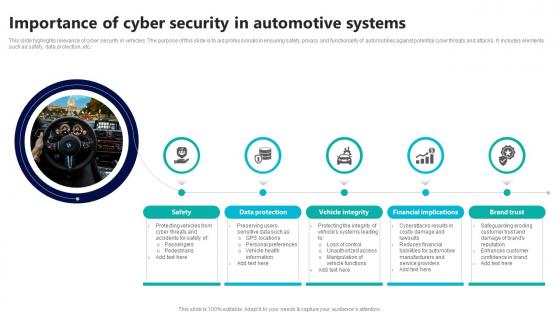
 Role Of Ecu In Automotive Cyber Security
Role Of Ecu In Automotive Cyber SecurityThis slide highlights significance of ECU in automotive cyber security. The purpose of this slide is to assist professionals in safeguarding the integrity and operation of automobiles. It includes elements such as control, communication, etc. Presenting our set of slides with Role Of Ecu In Automotive Cyber Security This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Communication, Authentication, Incident Response
-
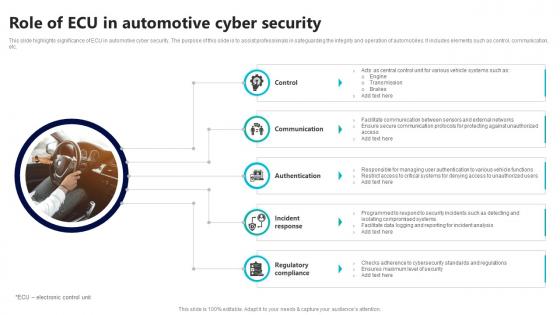
 Use Case Of Cyber Security In Automotive Systems
Use Case Of Cyber Security In Automotive SystemsThis slide highlights application of cyber security to automotive components. The purpose of this slide is to assist businesses in protecting vehicles from system manipulation in interconnected environment. It includes elements such as access control, data encryption, etc. Introducing our premium set of slides with Use Case Of Cyber Security In Automotive Systems Ellicudate the seven stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Access Control, Data Encryption, Firmware Updates So download instantly and tailor it with your information.
-
 Cyber Security Crisis Monitoring Solutions
Cyber Security Crisis Monitoring SolutionsThe purpose of this slide is to help cybersecurity professionals in monitoring potential threats and implementing proactive solutions such as detecting security incidents, assessing account activity, monitoring network traffic, etc. Presenting our set of slides with Cyber Security Crisis Monitoring Solutions This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Detect Security Incidents, Cyber Risk Management, Assess Account Activity
-
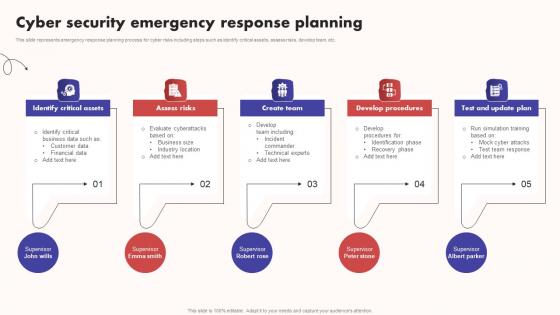 Cyber Security Emergency Response Planning
Cyber Security Emergency Response PlanningThis slide represents emergency response planning process for cyber risks including steps such as identify critical assets, assess risks, develop team, etc. Introducing our premium set of slides with Cyber Security Emergency Response Planning. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Identify Critical Assets, Assess Risks, Develop Procedures. So download instantly and tailor it with your information.
-
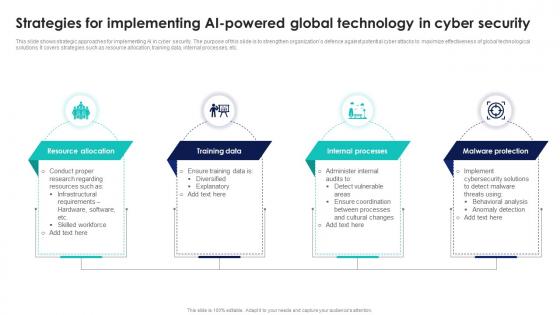 Strategies For Implementing AI Powered Global Technology In Cyber Security
Strategies For Implementing AI Powered Global Technology In Cyber SecurityThis slide shows strategic approaches for implementing AI in cyber security. The purpose of this slide is to strengthen organizations defence against potential cyber attacks to maximize effectiveness of global technological solutions. It covers strategies such as resource allocation, training data, internal processes, etc. Presenting our set of slides with Strategies For Implementing AI Powered Global Technology In Cyber Security. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Resource Allocation, Training Data, Internal Processes.
-
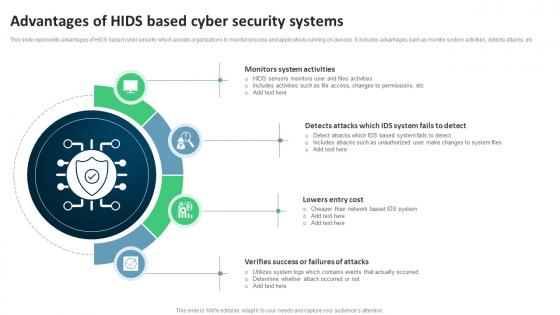 Advantages Of Hids Based Cyber Security Systems
Advantages Of Hids Based Cyber Security SystemsThis slide represents advantages of HIDS based cyber security which assists organizations to monitor process and applications running on devices. It includes advantages such as monitor system activities, detects attacks, etc Presenting our set of slides with Advantages Of Hids Based Cyber Security Systems. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Monitors System Activities, Lowers Entry Cost, Verifies Success Or Failures Of Attacks.
-
 Best Practices For Implementing Hids Cyber Security
Best Practices For Implementing Hids Cyber SecurityThis slide represents best practices for implementing HIDS cyber security which monitors IT systems for signs of suspicious activities and unusual behaviours. It includes best practices for implementing HIDS cyber security such as monitor all hosts, contextualize data, etc Introducing our premium set of slides with Best Practices For Implementing Hids Cyber Security. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Monitor All Hosts, Contextualize Data, Consider Agentless HIDS. So download instantly and tailor it with your information.
-
 Comparative Analysis Of Hids And Nids Cyber Security
Comparative Analysis Of Hids And Nids Cyber SecurityThis slide represents comparative analysis of HIDS and NIDS cyber security which assists to detect suspicious attack and about system administrator. It includes comparative analysis of HIDS and NIDS cyber security based on features such as management, detects large network attacks, etc Introducing our Comparative Analysis Of Hids And Nids Cyber Security set of slides. The topics discussed in these slides are Management, Analyse Encrypted Network Traffic, Protection Against Targeted Attacks . This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Computer Safety Through Hids Cyber Security Icon
Computer Safety Through Hids Cyber Security IconPresenting our set of slides with Computer Safety Through Hids Cyber Security Icon. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cyber Security Icon, Computer.
-
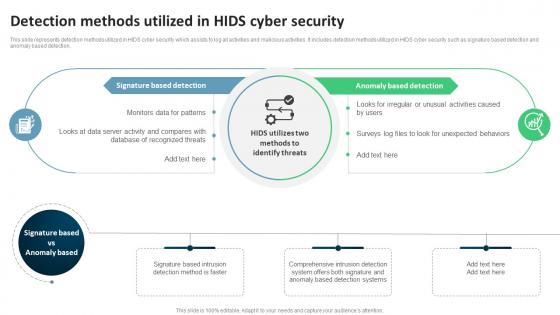 Detection Methods Utilized In Hids Cyber Security
Detection Methods Utilized In Hids Cyber SecurityThis slide represents detection methods utilized in HIDS cyber security which assists to log all activities and malicious activities. It includes detection methods utilized in HIDS cyber security such as signature based detection and anomaly based detection. Presenting our well structured Detection Methods Utilized In Hids Cyber Security. The topics discussed in this slide are Anomaly Based Detection, Signature Based Detection, Comprehensive. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
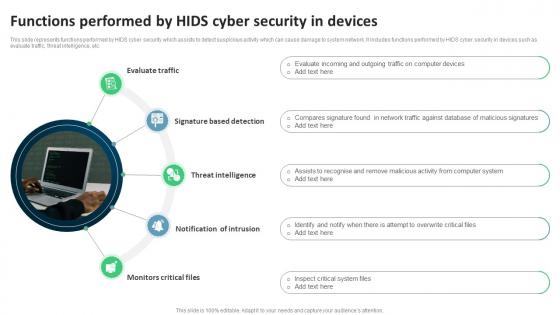 Functions Performed By Hids Cyber Security In Devices
Functions Performed By Hids Cyber Security In DevicesThis slide represents functions performed by HIDS cyber security which assists to detect suspicious activity which can cause damage to system network. It includes functions performed by HIDS cyber security in devices such as evaluate traffic, threat intelligence, etc Presenting our set of slides with Functions Performed By Hids Cyber Security In Devices. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Evaluate Traffic, Signature Based Detection, Threat Intelligence .
-
 Hids Based Cyber Security Icon
Hids Based Cyber Security IconIntroducing our Hids Based Cyber Security Icon set of slides. The topics discussed in these slides are Security Icon, Hids Based Cyber. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Hids Cyber Security Architecture And Working
Hids Cyber Security Architecture And WorkingThis slide represents HIDS cyber security architecture and working which operates in encrypted network environment and prevents network based attacks. It includes ley components such as touter, firewall, IDS, etc Presenting our well structured Hids Cyber Security Architecture And Working. The topics discussed in this slide are Architecture, Administrator, Computers. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Hids Cyber Security Software Comparison
Hids Cyber Security Software ComparisonThis slide represents HIDS cyber security software comparison which provides visibility across networks and assist to meet security regulations. It includes HIDS cyber security software comparison based on features and price. Presenting our well structured Hids Cyber Security Software Comparison. The topics discussed in this slide are Solar Winds Security Event Manager, Open Source Security, Comparison. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
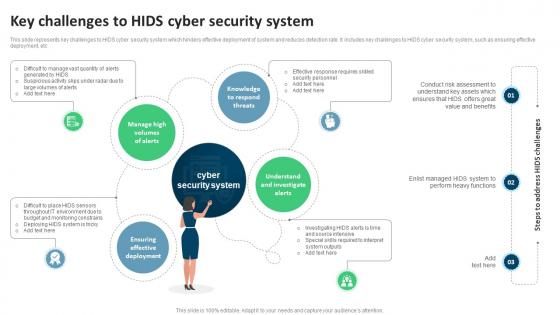 Key Challenges To Hids Cyber Security System
Key Challenges To Hids Cyber Security SystemThis slide represents key challenges to HIDS cyber security system which hinders effective deployment of system and reduces detection rate. It includes key challenges to HIDS cyber security system, such as ensuring effective deployment, etc Presenting our well structured Key Challenges To Hids Cyber Security System. The topics discussed in this slide are Knowledge, Deployment, Investigate. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
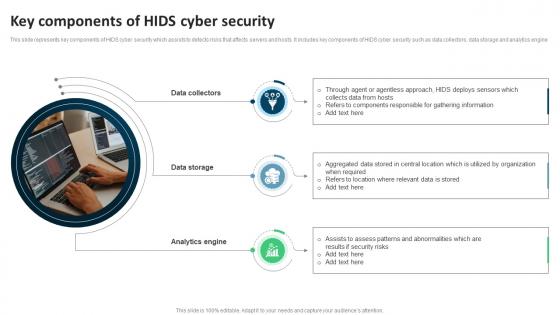 Key Components Of Hids Cyber Security
Key Components Of Hids Cyber SecurityThis slide represents key components of HIDS cyber security which assists to detects risks that affects servers and hosts. It includes key components of HIDS cyber security such as data collectors, data storage and analytics engine Presenting our set of slides with Key Components Of Hids Cyber Security. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Data Collectors, Data Storage, Analytics Engine.
-
 Key Features Of Hids Cyber Security
Key Features Of Hids Cyber SecurityThis slide represents key features of HIDS cyber security which assists to collects data from servers, computer and other host systems and analyse any abnormalities. It includes key features of HIDS cyber security such as log analysis, real time alerts, etc Introducing our premium set of slides with Key Features Of Hids Cyber Security. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Log Analysis, Behavioral Analysis, Real Time Alerts. So download instantly and tailor it with your information.
-
 Threats Eliminated By Hids Cyber Security
Threats Eliminated By Hids Cyber SecurityThis slide represents threats eliminated by HIDS cyber security which detects suspicious activities and generates alerts when they are detected. It includes threats eliminated by HIDS cyber security such as malicious attacks, asymmetric routing, etc. Presenting our set of slides with Threats Eliminated By Hids Cyber Security. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Malicious Attacks, Asymmetric Routing, Buffer Overflow Attacks.
-
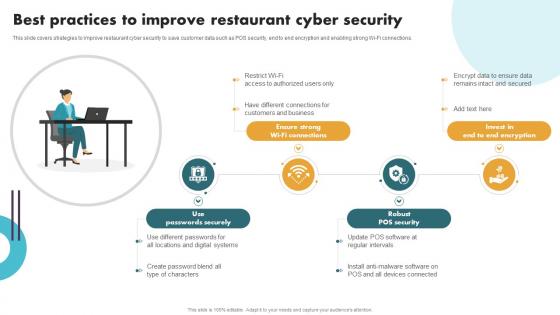 Securing Food Safety In Online Best Practices To Improve Restaurant Cyber Security
Securing Food Safety In Online Best Practices To Improve Restaurant Cyber SecurityThis slide covers strategies to improve restaurant cyber security to save customer data such as POS security, end to end encryption and enabling strong Wi-Fi connections. Introducing Securing Food Safety In Online Best Practices To Improve Restaurant Cyber Security to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Use Passwords Securely, Ensure Strong Wi-Fi Connections, Robust POS Security, using this template. Grab it now to reap its full benefits.
-
 Securing Food Safety In Online Major Cyber Security Challenges Faced By Restaurant
Securing Food Safety In Online Major Cyber Security Challenges Faced By RestaurantThis slide covers cyber security issues faced by restaurant businesses such as lack of uniformity in digital systems, untrained employees and ineffective POS system. Introducing Securing Food Safety In Online Major Cyber Security Challenges Faced By Restaurant to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Lack Of Uniformity In Digital Systems, Ineffective Security Management Software, Untrained Employees, Loop Holes In POS System, using this template. Grab it now to reap its full benefits.
-
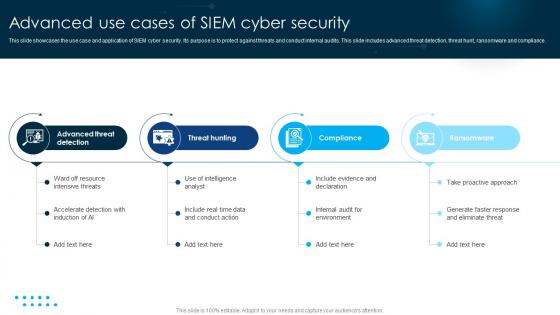 Advanced Use Cases Of SIEM Cyber Security
Advanced Use Cases Of SIEM Cyber SecurityThis slide showcases the use case and application of SIEM cyber security. Its purpose is to protect against threats and conduct internal audits. This slide includes advanced threat detection, threat hunt, ransomware and compliance. Presenting our set of slides with name Advanced Use Cases Of SIEM Cyber Security. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Advanced Threat Detection, Threat Hunting, Compliance.
-
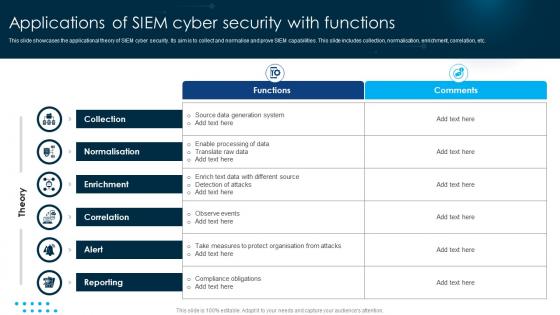 Applications Of SIEM Cyber Security With Functions
Applications Of SIEM Cyber Security With FunctionsThis slide showcases the applicational theory of SIEM cyber security. Its aim is to collect and normalise and prove SIEM capabilities. This slide includes collection, normalisation, enrichment, correlation, etc. Introducing our Applications Of SIEM Cyber Security With Functions set of slides. The topics discussed in these slides are Collection, Enrichment, Correlation . This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Benefits Of Including SIEM Cyber Security
Benefits Of Including SIEM Cyber SecurityThis slide showcases the benefits of SIEM cyber security. Its aim is to make business capable of security workflow. This slide includes analysis of data, efficiency, value, tools, productivity and cybersecurity. Presenting our set of slides with name Benefits Of Including SIEM Cyber Security. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Increases Efficiency, Incident Response Tools, Reduce Cybersecurity.
-
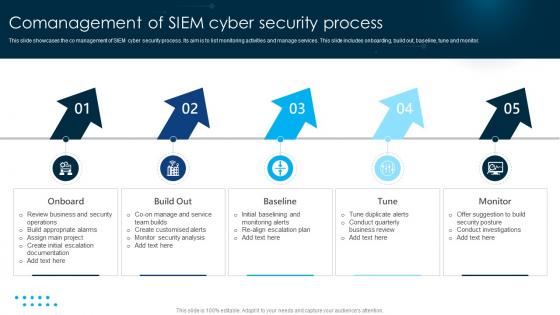 Comanagement Of SIEM Cyber Security Process
Comanagement Of SIEM Cyber Security ProcessThis slide showcases the co management of SIEM cyber security process. Its aim is to list monitoring activities and manage services. This slide includes onboarding, build out, baseline, tune and monitor. Introducing our premium set of slides with name Comanagement Of SIEM Cyber Security Process. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Onboard, Build Out, Baseline. So download instantly and tailor it with your information.
-
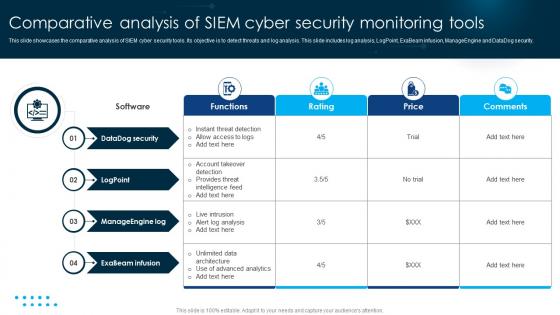 Comparative Analysis Of SIEM Cyber Security Monitoring Tools
Comparative Analysis Of SIEM Cyber Security Monitoring ToolsThis slide showcases the comparative analysis of SIEM cyber security tools. Its objective is to detect threats and log analysis. This slide includes log analysis, LogPoint, ExaBeam infusion, ManageEngine and DataDog security. Presenting our well structured Comparative Analysis Of SIEM Cyber Security Monitoring Tools. The topics discussed in this slide are Datadog Security, Logpoint, Manageengine Log. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
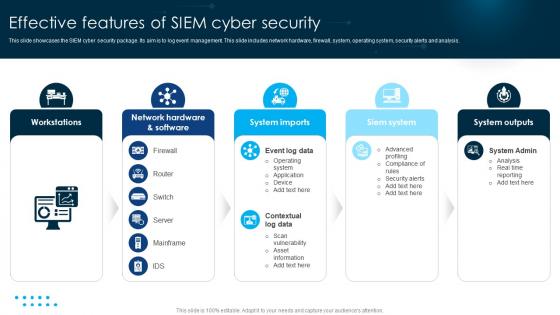 Effective Features Of SIEM Cyber Security
Effective Features Of SIEM Cyber SecurityThis slide showcases the SIEM cyber security package. Its aim is to log event management. This slide includes network hardware, firewall, system, operating system, security alerts and analysis. Introducing our premium set of slides with name Effective Features Of SIEM Cyber Security. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Workstations, System Imports, Siem System. So download instantly and tailor it with your information.
-
 Evolution Of Technological SIEM Cyber Security
Evolution Of Technological SIEM Cyber SecurityThis slide showcases the evolution of technology SIEM cyber security. Its aim is to set rule and awareness for threat data management. This slide includes machine learning, risk management, rules, event, etc. Presenting our set of slides with name Evolution Of Technological SIEM Cyber Security. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Early 2000s, Mid 2000s, Late 2000s.
-
 Impact Of Integrating SIEM Cyber Security In Business
Impact Of Integrating SIEM Cyber Security In BusinessThis slide showcases the benefits of incorporation SIEM cyber security. Its objective is to propose a better threat detection system. This slide includes threat detection, staff and less spend. Introducing our premium set of slides with name Impact Of Integrating SIEM Cyber Security In Business. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Better Threat Detection, Fewer Staff, Less Spend. So download instantly and tailor it with your information.
-
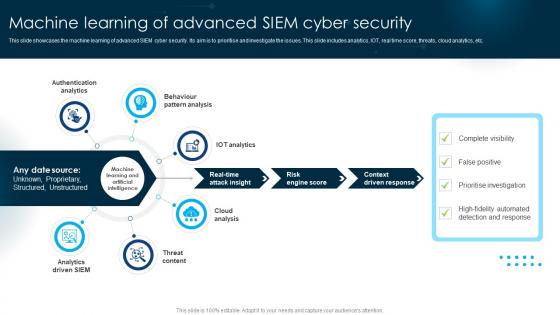 Machine Learning Of Advanced SIEM Cyber Security
Machine Learning Of Advanced SIEM Cyber SecurityThis slide showcases the machine learning of advanced SIEM cyber security. Its aim is to prioritise and investigate the issues. This slide includes analytics, IOT, real time score, threats, cloud analytics, etc. Presenting our set of slides with name Machine Learning Of Advanced SIEM Cyber Security. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Authentication Analytics, Behaviour Pattern Analysis , IOT Analytics.
-
 Network SIEM Cyber Security Icon
Network SIEM Cyber Security IconIntroducing our Network SIEM Cyber Security Icon set of slides. The topics discussed in these slides are Network SIEM, Cyber Security, Icon. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
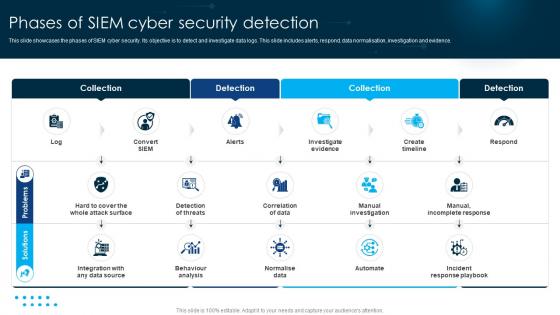 Phases Of SIEM Cyber Security Detection
Phases Of SIEM Cyber Security DetectionThis slide showcases the phases of SIEM cyber security. Its objective is to detect and investigate data logs. This slide includes alerts, respond, data normalisation, investigation and evidence. Presenting our set of slides with name Phases Of SIEM Cyber Security Detection. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Solutions, Problems, Business.
-
 Preparation Of Successful Steps To SIEM Cyber Security
Preparation Of Successful Steps To SIEM Cyber SecurityThis slide showcases the SIEM cyber security plan. Its aim is to manage and prepare the SIEM functions. This slide includes embedding, integration, preparation and success criteria. Introducing our premium set of slides with name Preparation Of Successful Steps To SIEM Cyber Security. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Success Criteria, Preparation, Integration. So download instantly and tailor it with your information.
-
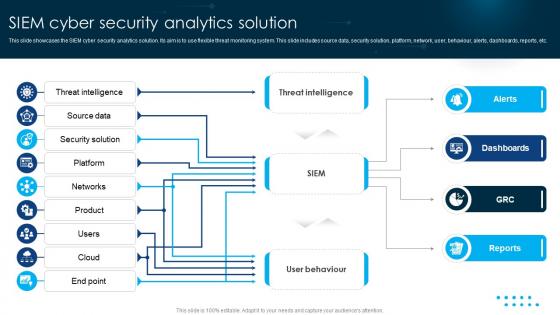 SIEM Cyber Security Analytics Solution
SIEM Cyber Security Analytics SolutionThis slide showcases the SIEM cyber security analytics solution. Its aim is to use flexible threat monitoring system. This slide includes source data, security solution, platform, network, user, behaviour, alerts, dashboards, reports, etc. Presenting our set of slides with name SIEM Cyber Security Analytics Solution. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Threat Intelligence, Source Data, Security Solution.
-
 SIEM Cyber Security Architecture Platform
SIEM Cyber Security Architecture PlatformThis slide showcases the SIEM cyber security architecture. Its aim is to investigate security incidents and detect attacks. This slide includes network traffic, firewall, logs, reports, analyse and investigate. Presenting our set of slides with name SIEM Cyber Security Architecture Platform. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Investigate, Analyse, Reports.
-
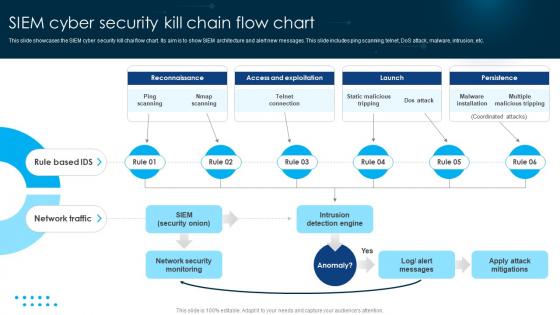 SIEM Cyber Security Kill Chain Flow Chart
SIEM Cyber Security Kill Chain Flow ChartThis slide showcases the SIEM cyber security kill chai flow chart. Its aim is to show SIEM architecture and alert new messages. This slide includes ping scanning, telnet, DoS attack, malware, intrusion, etc. Presenting our set of slides with name SIEM Cyber Security Kill Chain Flow Chart. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Ping Scanning, Nmap Scanning, Telnet Connection.
-
 SIEM Cyber Security Protection Icon
SIEM Cyber Security Protection IconIntroducing our premium set of slides with name SIEM Cyber Security Protection Icon. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like SIEM Cyber, Security Protection, Icon. So download instantly and tailor it with your information.
-
 SIEM Data Cyber Security Icon
SIEM Data Cyber Security IconPresenting our set of slides with name SIEM Data Cyber Security Icon. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on SIEM data cyber security icon.
-
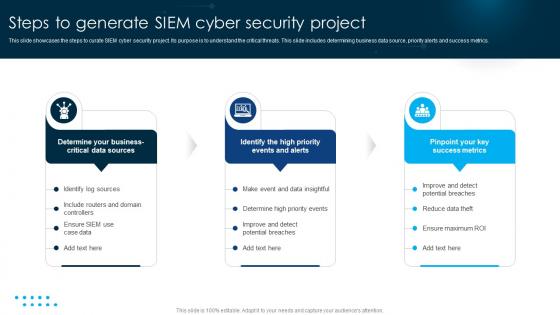 Steps To Generate SIEM Cyber Security Project
Steps To Generate SIEM Cyber Security ProjectThis slide showcases the steps to curate SIEM cyber security project. Its purpose is to understand the critical threats. This slide includes determining business data source, priority alerts and success metrics. Introducing our premium set of slides with name Steps To Generate SIEM Cyber Security Project. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Make Event, Data Insightful, Determine Business Critical. So download instantly and tailor it with your information.
-
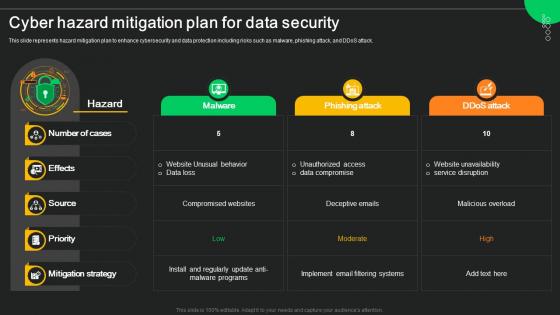 Cyber Hazard Mitigation Plan For Data Security
Cyber Hazard Mitigation Plan For Data SecurityThis slide represents hazard mitigation plan to enhance cybersecurity and data protection including risks such as malware, phishing attack, and DDoS attack. Presenting our well structured Cyber Hazard Mitigation Plan For Data Security. The topics discussed in this slide are Malware, Phishing Attack, Ddos Attack. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
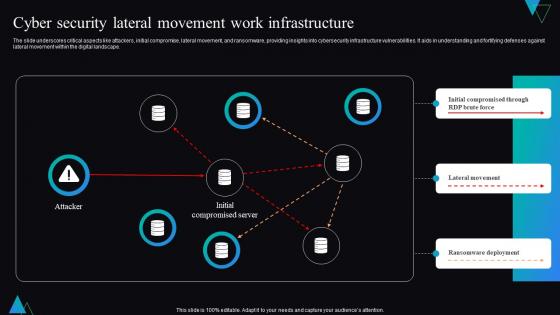 Cyber Security Lateral Movement Work Infrastructure
Cyber Security Lateral Movement Work InfrastructureThe slide underscores critical aspects like attackers, initial compromise, lateral movement, and ransomware, providing insights into cybersecurity infrastructure vulnerabilities. It aids in understanding and fortifying defenses against lateral movement within the digital landscape. Introducing our Cyber Security Lateral Movement Work Infrastructure set of slides. The topics discussed in these slides are Infrastructure, Lateral Movement, Ransomware Deployment. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
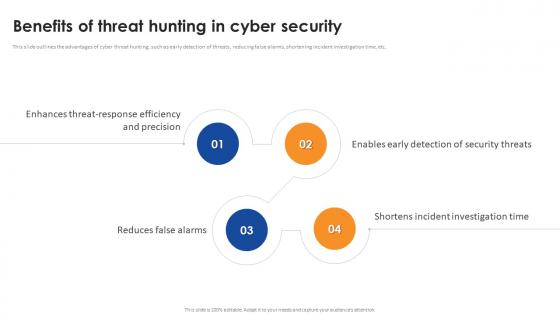 Benefits Of Threat Hunting In Cyber Security
Benefits Of Threat Hunting In Cyber SecurityThis slide outlines the advantages of cyber threat hunting, such as early detection of threats, reducing false alarms, shortening incident investigation time, etc. Increase audience engagement and knowledge by dispensing information using Benefits Of Threat Hunting In Cyber Security. This template helps you present information on four stages. You can also present information on Threat Hunting, Cyber Security, Incident Investigation Time, Early Detection Of Threats using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Introduction To Threat Hunting In Cyber Security
Introduction To Threat Hunting In Cyber SecurityThis slide gives an overview of the cyber threat hunting process for network and data security. It detects threats that bypass the initial defenses. Increase audience engagement and knowledge by dispensing information using Introduction To Threat Hunting In Cyber Security. This template helps you present information on six stages. You can also present information on Threat Hunting In Cyber Security, Bypass The Initial Defenses, Cyber Threat Hunting Process using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Icon For Role Of 5g Technology In Retail Cyber Security
Icon For Role Of 5g Technology In Retail Cyber SecurityIntroducing our Icon For Role Of 5g Technology In Retail Cyber Security set of slides. The topics discussed in these slides are Icon For Role Of 5G Technology, Retail Cyber Security This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Icon For Utilization Of Blockchain In Retail Cyber Security
Icon For Utilization Of Blockchain In Retail Cyber SecurityPresenting our well structured Icon For Utilization Of Blockchain In Retail Cyber Security The topics discussed in this slide are Icon For Utilization Of Blockchain, Retail Cyber Security This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
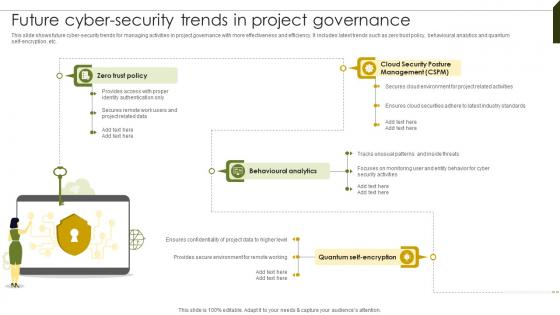 Future Cyber Security Trends Implementing Project Governance Framework For Quality PM SS
Future Cyber Security Trends Implementing Project Governance Framework For Quality PM SSThis slide shows future cyber-security trends for managing activities in project governance with more effectiveness and efficiency. It includes latest trends such as zero trust policy, behavioural analytics and quantum self-encryption, etc. Present the topic in a bit more detail with this Future Cyber Security Trends Implementing Project Governance Framework For Quality PM SS. Use it as a tool for discussion and navigation on Cloud Security, Behavioural Analytics, Trust Policy. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
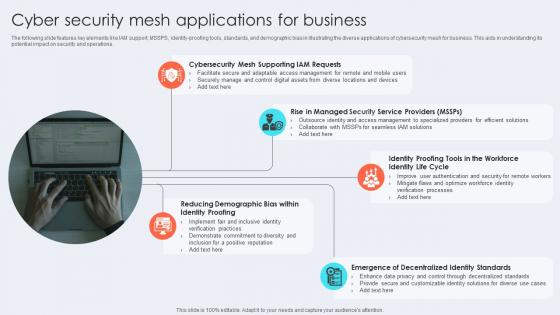 Cyber Security Mesh Applications For Business
Cyber Security Mesh Applications For BusinessThe following slide features key elements like IAM support, MSSPS, identity-proofing tools, standards, and demographic bias in illustrating the diverse applications of cybersecurity mesh for business. This aids in understanding its potential impact on security and operations. Presenting our set of slides with Cyber Security Mesh Applications For Business This exhibits information on Five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Mesh Supporting Iam Requests, Identity Life Cycle, Decentralized Identity Standards
-
 Cyber Security Mesh Architecture
Cyber Security Mesh ArchitectureThe following slide highlights components like centralized dashboard, alerting, investigation, reporting, users, robotics, and processes in the cybersecurity mesh architecture. It aids in illustrating the structure and functionalities of the system. Presenting our well structured Cyber Security Mesh Architecture The topics discussed in this slide are Centralized Dashboard, Centralized Alerting, Centralized Reporting This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
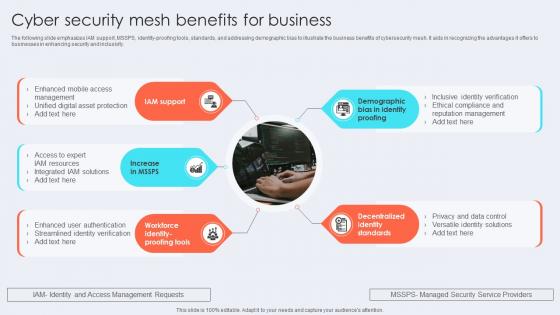 Cyber Security Mesh Benefits For Business
Cyber Security Mesh Benefits For BusinessThe following slide emphasizes IAM support, MSSPS, identity-proofing tools, standards, and addressing demographic bias to illustrate the business benefits of cybersecurity mesh. It aids in recognizing the advantages it offers to businesses in enhancing security and inclusivity. Presenting our set of slides with Cyber Security Mesh Benefits For Business This exhibits information on Five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Iam Support, Identity Standards, Identity Proofing
-
 Cyber Security Mesh Improved Scalability
Cyber Security Mesh Improved ScalabilityIntroducing our Cyber Security Mesh Improved Scalability set of slides. The topics discussed in these slides are Cyber Security Mesh, Improved Scalability. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Four Layers Of Cyber Security Mesh
Four Layers Of Cyber Security MeshThe following slide features essential elements such as security analytics, consolidated policy management, Distributed identity fabric, and unified dashboards to depict the four layers of cybersecurity mesh. This aids in understanding the comprehensive structure and capabilities of cyber mesh. Presenting our set of slides with Four Layers Of Cyber Security Mesh This exhibits information on Four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Posture Management, Distributed Identity Fabric, Consolidated Dashboards
-
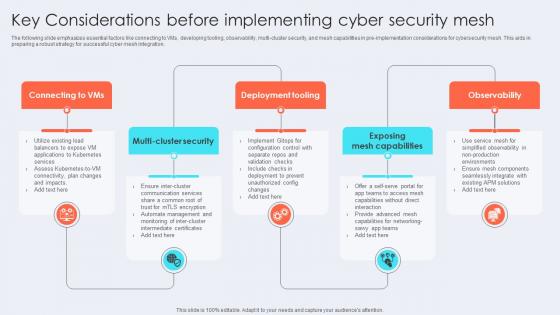 Key Considerations Before Implementing Cyber Security Mesh
Key Considerations Before Implementing Cyber Security MeshThe following slide emphasizes essential factors like connecting to VMs, developing tooling, observability, multi-cluster security, and mesh capabilities in pre-implementation considerations for cybersecurity mesh. This aids in preparing a robust strategy for successful cyber mesh integration. Presenting our set of slides with Key Considerations Before Implementing Cyber Security Mesh This exhibits information on Five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Deployment Tooling, Exposing Mesh Capabilities, Observability
-
 Reducing Attack Surface By Cyber Security Mesh Icon
Reducing Attack Surface By Cyber Security Mesh IconIntroducing our premium set of slides with Reducing Attack Surface By Cyber Security Mesh Icon Ellicudate the Three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Reducing Attack Surface, Cyber Security Mesh Icon. So download instantly and tailor it with your information.
-
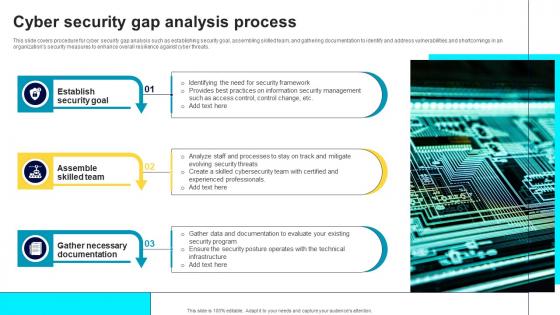 Cyber Security Gap Analysis Process
Cyber Security Gap Analysis ProcessThis slide covers procedure for cyber security gap analysis such as establishing security goal, assembling skilled team, and gathering documentation to identify and address vulnerabilities and shortcomings in an organizations security measures to enhance overall resilience against cyber threats. Presenting our set of slides with name Cyber Security Gap Analysis Process. This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Establish Security Goal, Assemble Skilled Team, Gather Necessary Documentation.
-
 Cyber Security Threat Icon To Prevent Gap
Cyber Security Threat Icon To Prevent GapPresenting our set of slides with name Cyber Security Threat Icon To Prevent Gap. This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cyber Security Threat, Icon Prevent Gap.
-
 Checklist To Enhance Cyber Security Of SCADA Networks
Checklist To Enhance Cyber Security Of SCADA NetworksThis slide represents checklist that assist IT companies to enhance their SCADA networks cyber security for improving data protection. It includes various elements such as recognizing connections, disconnecting irrelevant networks, etc. Introducing our Checklist To Enhance Cyber Security Of SCADA Networks set of slides. The topics discussed in these slides are Essential Connections, Inadvertent Disclosure, SCADA Network This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
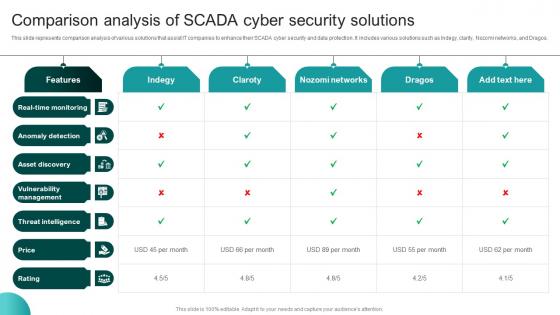 Comparison Analysis Of SCADA Cyber Security Solutions
Comparison Analysis Of SCADA Cyber Security SolutionsThis slide represents comparison analysis of various solutions that assist IT companies to enhance their SCADA cyber security and data protection. It includes various solutions such as Indegy, clarity, Nozomi networks, and Dragos. Presenting our well structured Comparison Analysis Of SCADA Cyber Security Solutions The topics discussed in this slide are Anomaly Detection, Asset Discovery, Vulnerability Management. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Framework For SCADA Cyber Security Policy
Framework For SCADA Cyber Security PolicyThis slide represents framework of various policies that assist IT companies to optimize their SCADA cyber security for effective data protection. It includes policies related to data security, platform security, communication security, audit, etc. Introducing our Framework For SCADA Cyber Security Policy set of slides. The topics discussed in these slides are System Security Program, Cyber Security Policy This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
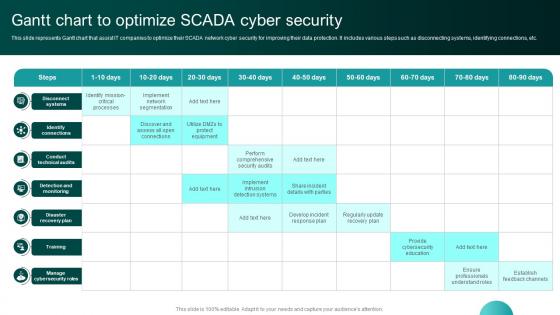 Gantt Chart To Optimize SCADA Cyber Security
Gantt Chart To Optimize SCADA Cyber SecurityThis slide represents Gantt chart that assist IT companies to optimize their SCADA network cyber security for improving their data protection. It includes various steps such as disconnecting systems, identifying connections, etc. Presenting our well structured Gantt Chart To Optimize SCADA Cyber Security The topics discussed in this slide are Identify Connections, Conduct Technical Audits. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
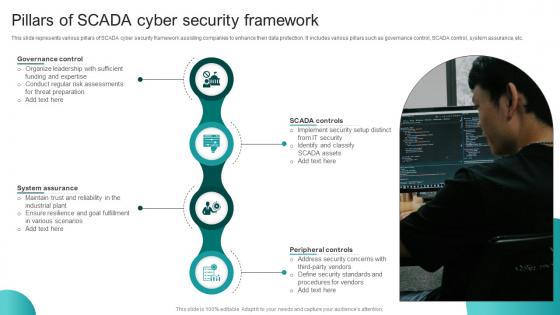 Pillars Of SCADA Cyber Security Framework
Pillars Of SCADA Cyber Security FrameworkThis slide represents various pillars of SCADA cyber security framework assisting companies to enhance their data protection. It includes various pillars such as governance control, SCADA control, system assurance, etc. Presenting our set of slides with Pillars Of SCADA Cyber Security Framework This exhibits information on Four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Governance Control, SCADA Controls, Peripheral Controls