Powerpoint Templates and Google slides for Cyber Security Icon
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
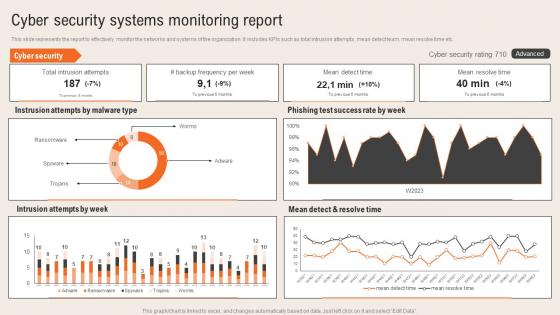 Cyber Security Systems Monitoring Report Deploying Computer Security Incident Management
Cyber Security Systems Monitoring Report Deploying Computer Security Incident ManagementThis slide represents the report to effectively monitor the networks and systems of the organization. It includes KPIs such as total intrusion attempts, mean detect team, mean resolve time etc.Present the topic in a bit more detail with this Cyber Security Systems Monitoring Report Deploying Computer Security Incident Management. Use it as a tool for discussion and navigation on Intrusion Attempts, Ransomware, Phishing Test Success. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Supply Chain Risk Management Dashboard Deploying Computer Security Incident Management
Cyber Supply Chain Risk Management Dashboard Deploying Computer Security Incident ManagementThis slide shows the dashboard representing details related to management of supply chain risks by the incident management team. It includes details related to KPIs such as policy and compliance, resource security hygiene etc.Present the topic in a bit more detail with this Cyber Supply Chain Risk Management Dashboard Deploying Computer Security Incident Management. Use it as a tool for discussion and navigation on Resource Security Hygiene, Subscription Coverage, Resource Health Monitoring. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
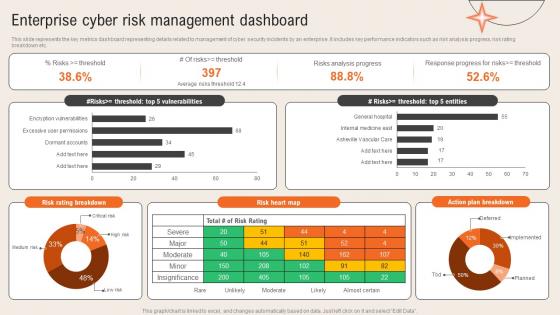 Enterprise Cyber Risk Management Dashboard Deploying Computer Security Incident Management
Enterprise Cyber Risk Management Dashboard Deploying Computer Security Incident ManagementThis slide represents the key metrics dashboard representing details related to management of cyber security incidents by an enterprise. It includes key performance indicators such as risk analysis progress, risk rating breakdown etc.Present the topic in a bit more detail with this Enterprise Cyber Risk Management Dashboard Deploying Computer Security Incident Management. Use it as a tool for discussion and navigation on Risks Analysis Progress, Response Progress, Action Plan Breakdown. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
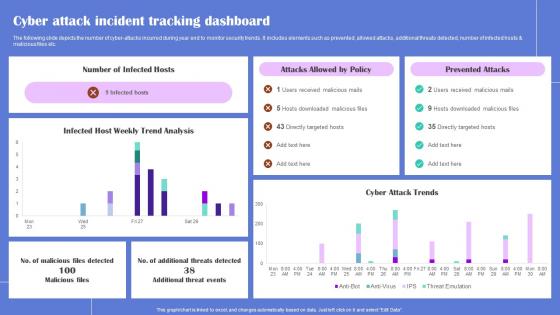 Cyber Attack Incident Generating Security Awareness Among Employees To Reduce
Cyber Attack Incident Generating Security Awareness Among Employees To ReduceThe following slide depicts the number of cyber attacks incurred during year end to monitor security trends. It includes elements such as prevented, allowed attacks, additional threats detected, number of infected hosts and malicious files etc. Present the topic in a bit more detail with this Cyber Attack Incident Generating Security Awareness Among Employees To Reduce Use it as a tool for discussion and navigation on Infected Hosts, Prevented Attacks This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Major Causes Of Cyber Generating Security Awareness Among Employees To Reduce
Major Causes Of Cyber Generating Security Awareness Among Employees To ReduceThe following slide highlights the key reasons of cyber attack to analyze and formulate actions. It includes key elements such as physical theft, human error, insider misuse, old security vulnerabilities etc. Present the topic in a bit more detail with this Major Causes Of Cyber Generating Security Awareness Among Employees To Reduce Use it as a tool for discussion and navigation on Unawareness Among, Security Trainings This template is free to edit as deemed fit for your organization. Therefore download it now.
-
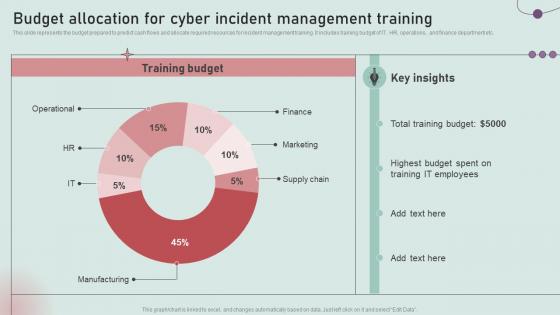 Budget Allocation For Cyber Incident Management Training Development And Implementation Of Security
Budget Allocation For Cyber Incident Management Training Development And Implementation Of SecurityThis slide represents the budget prepared to predict cash flows and allocate required resources for incident management training. It includes training budget of IT, HR, operations, and finance department etc. Deliver an outstanding presentation on the topic using this Budget Allocation For Cyber Incident Management Training Development And Implementation Of Security. Dispense information and present a thorough explanation of Total Training Budget, It Employees, Highest Budget using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
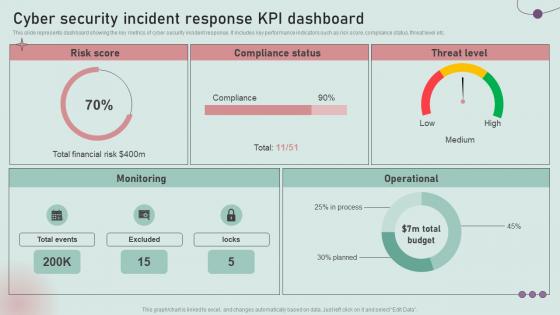 Cyber Security Incident Response KPI Dashboard Development And Implementation Of Security Incident
Cyber Security Incident Response KPI Dashboard Development And Implementation Of Security IncidentThis slide represents dashboard showing the key metrics of cyber security incident response. It includes key performance indicators such as risk score, compliance status, threat level etc. Deliver an outstanding presentation on the topic using this Cyber Security Incident Response KPI Dashboard Development And Implementation Of Security Incident. Dispense information and present a thorough explanation of Total Financial Risk, Compliance, Monitoring using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
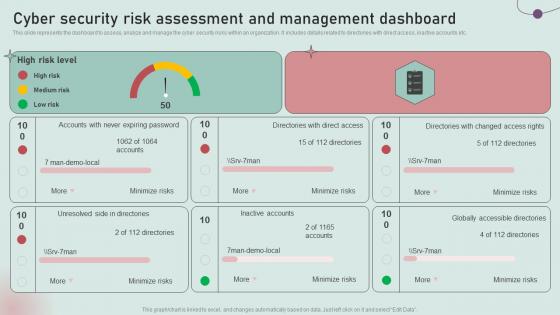 Cyber Security Risk Assessment And Management Dashboard Development And Implementation Of Security
Cyber Security Risk Assessment And Management Dashboard Development And Implementation Of SecurityThis slide represents the dashboard to assess, analyze and manage the cyber security risks within an organization. It includes details related to directories with direct access, inactive accounts etc. Deliver an outstanding presentation on the topic using this Cyber Security Risk Assessment And Management Dashboard Development And Implementation Of Security. Dispense information and present a thorough explanation of Medium Risk, Unresolved Side, Inactive Accounts using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
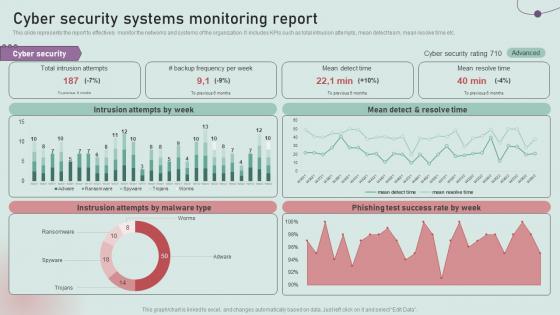 Cyber Security Systems Monitoring Report Development And Implementation Of Security Incident Management
Cyber Security Systems Monitoring Report Development And Implementation Of Security Incident ManagementThis slide represents the report to effectively monitor the networks and systems of the organization. It includes KPIs such as total intrusion attempts, mean detect team, mean resolve time etc. Deliver an outstanding presentation on the topic using this Cyber Security Systems Monitoring Report Development And Implementation Of Security Incident Management. Dispense information and present a thorough explanation of Intrusion Attempts, Mean Detect, Resolve Time using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Supply Chain Risk Management Dashboard Development And Implementation Of Security Incident
Cyber Supply Chain Risk Management Dashboard Development And Implementation Of Security IncidentThis slide shows the dashboard representing details related to management of supply chain risks by the incident management team. It includes details related to KPIs such as policy and compliance, resource security hygiene etc. Deliver an outstanding presentation on the topic using this Cyber Supply Chain Risk Management Dashboard Development And Implementation Of Security Incident. Dispense information and present a thorough explanation of Regulatory Compliance, Subscription Coverage, Resource Health using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
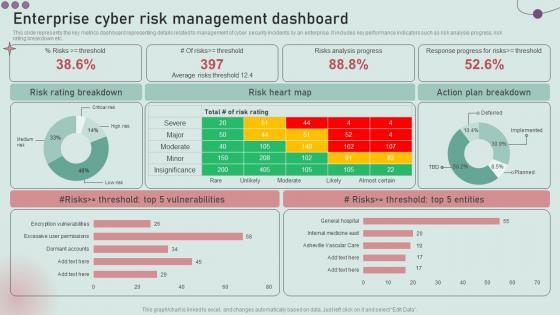 Enterprise Cyber Risk Management Dashboard Development And Implementation Of Security Incident
Enterprise Cyber Risk Management Dashboard Development And Implementation Of Security IncidentThis slide represents the key metrics dashboard representing details related to management of cyber security incidents by an enterprise. It includes key performance indicators such as risk analysis progress, risk rating breakdown etc. Present the topic in a bit more detail with this Enterprise Cyber Risk Management Dashboard Development And Implementation Of Security Incident. Use it as a tool for discussion and navigation on Risk Rating Breakdown, Risk Heart Map, Action Plan Breakdown. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
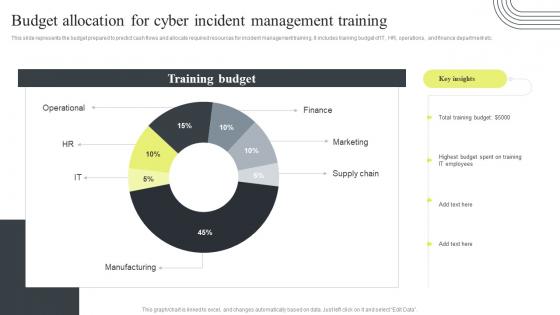 Cyber Security Attacks Response Plan Budget Allocation For Cyber Incident Management Training
Cyber Security Attacks Response Plan Budget Allocation For Cyber Incident Management TrainingThis slide represents the budget prepared to predict cash flows and allocate required resources for incident management training. It includes training budget of IT, HR, operations, and finance department etc. Deliver an outstanding presentation on the topic using this Cyber Security Attacks Response Plan Budget Allocation For Cyber Incident Management Training. Dispense information and present a thorough explanation of Budget Allocation, Cyber Incident Management, Training using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
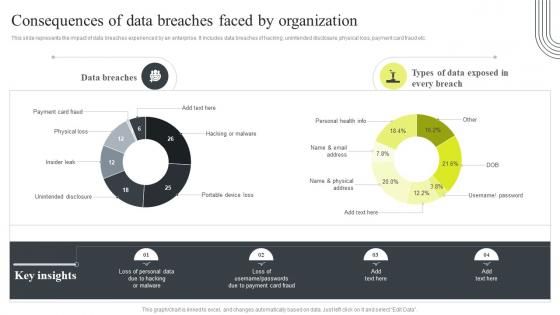 Cyber Security Attacks Response Plan Consequences Of Data Breaches Faced By Organization
Cyber Security Attacks Response Plan Consequences Of Data Breaches Faced By OrganizationThis slide represents the impact of data breaches experienced by an enterprise. It includes data breaches of hacking, unintended disclosure, physical loss, payment card fraud etc. Present the topic in a bit more detail with this Cyber Security Attacks Response Plan Consequences Of Data Breaches Faced By Organization. Use it as a tool for discussion and navigation on Consequences, Data Breaches, Unintended Disclosure. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
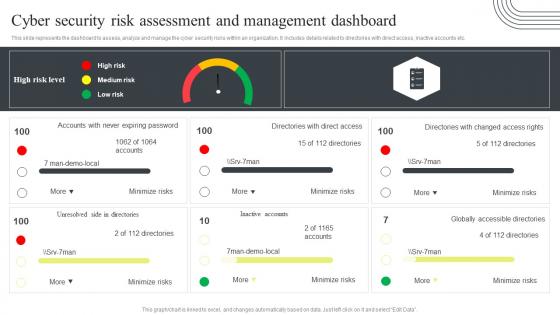 Cyber Security Attacks Response Plan Cyber Security Risk Assessment And Management Dashboard
Cyber Security Attacks Response Plan Cyber Security Risk Assessment And Management DashboardThis slide represents the dashboard to assess, analyze and manage the cyber security risks within an organization. It includes details related to directories with direct access, inactive accounts etc. Deliver an outstanding presentation on the topic using this Cyber Security Attacks Response Plan Cyber Security Risk Assessment And Management Dashboard. Dispense information and present a thorough explanation of Cyber Security, Risk Assessment, Management Dashboard using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
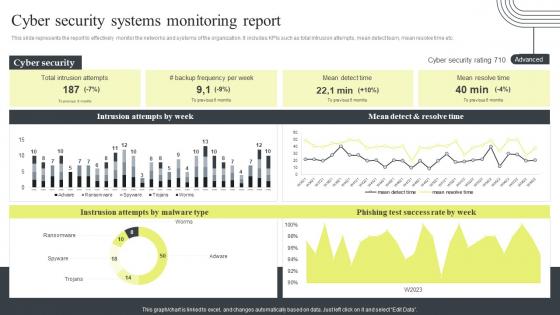 Cyber Security Attacks Response Plan Cyber Security Systems Monitoring Report
Cyber Security Attacks Response Plan Cyber Security Systems Monitoring ReportThis slide represents the report to effectively monitor the networks and systems of the organization. It includes KPIs such as total intrusion attempts, mean detect team, mean resolve time etc. Present the topic in a bit more detail with this Cyber Security Attacks Response Plan Cyber Security Systems Monitoring Report. Use it as a tool for discussion and navigation on Cyber Security Systems, Monitoring Report, Mean Detect And Resolve Time. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Security Attacks Response Plan Cyber Supply Chain Risk Management Dashboard
Cyber Security Attacks Response Plan Cyber Supply Chain Risk Management DashboardThis slide shows the dashboard representing details related to management of supply chain risks by the incident management team. It includes details related to KPIs such as policy and compliance, resource security hygiene etc. Present the topic in a bit more detail with this Cyber Security Attacks Response Plan Cyber Supply Chain Risk Management Dashboard. Use it as a tool for discussion and navigation on Cyber Supply Chain, Risk Management, Dashboard, Regulatory Compliance. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Security Attacks Response Plan Enterprise Cyber Risk Management Dashboard
Cyber Security Attacks Response Plan Enterprise Cyber Risk Management DashboardThis slide represents the key metrics dashboard representing details related to management of cyber security incidents by an enterprise. It includes key performance indicators such as risk analysis progress, risk rating breakdown etc. Deliver an outstanding presentation on the topic using this Cyber Security Attacks Response Plan Enterprise Cyber Risk Management Dashboard. Dispense information and present a thorough explanation of Enterprise Cyber, Risk Management, Dashboard, Action Plan Breakdown using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
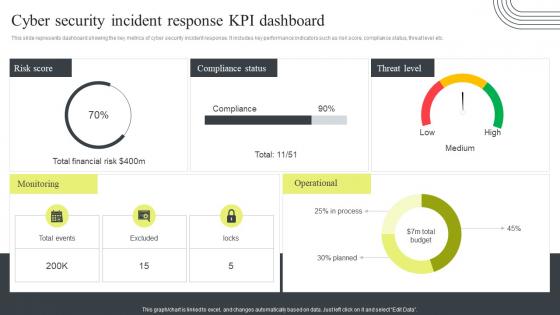 Cyber Security Incident Response Kpi Dashboard Cyber Security Attacks Response Plan
Cyber Security Incident Response Kpi Dashboard Cyber Security Attacks Response PlanThis slide represents dashboard showing the key metrics of cyber security incident response. It includes key performance indicators such as risk score, compliance status, threat level etc. Present the topic in a bit more detail with this Cyber Security Incident Response Kpi Dashboard Cyber Security Attacks Response Plan. Use it as a tool for discussion and navigation on Cyber Security, Incident Response, KPI Dashboard. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
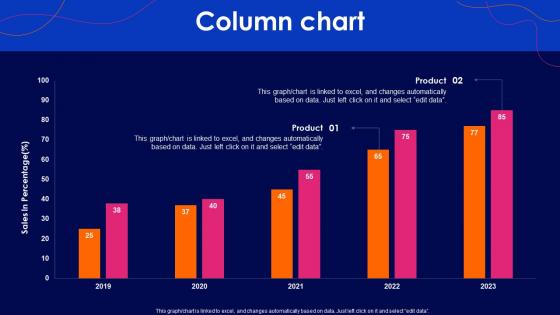 Cyber Security Policy Column Chart Ppt Show Graphics Tutorials
Cyber Security Policy Column Chart Ppt Show Graphics TutorialsDeliver an outstanding presentation on the topic using this Cyber Security Policy Column Chart Ppt Show Graphics Tutorials. Dispense information and present a thorough explanation of Column Chart using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Table Of Contents Cyber Security Policy Ppt Professional Graphics Pictures
Table Of Contents Cyber Security Policy Ppt Professional Graphics PicturesIntroducing Table Of Contents Cyber Security Policy Ppt Professional Graphics Pictures to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Information, Importance, Introduction, using this template. Grab it now to reap its full benefits.
-
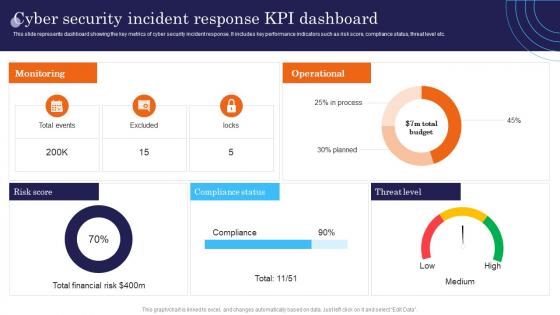 Cyber Security Incident Response KPI Dashboard Incident Response Strategies Deployment
Cyber Security Incident Response KPI Dashboard Incident Response Strategies DeploymentThis slide represents dashboard showing the key metrics of cyber security incident response. It includes key performance indicators such as risk score, compliance status, threat level etc. Deliver an outstanding presentation on the topic using this Cyber Security Incident Response KPI Dashboard Incident Response Strategies Deployment. Dispense information and present a thorough explanation of Monitoring, Operational, Score using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
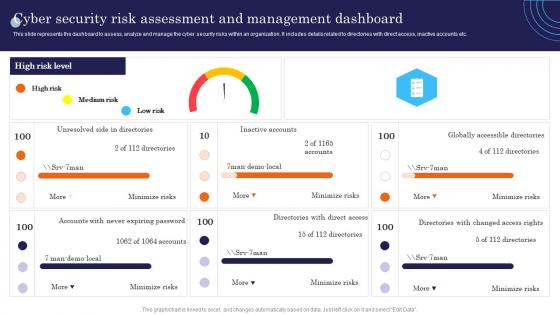 Cyber Security Risk Assessment And Management Dashboard Incident Response Strategies Deployment
Cyber Security Risk Assessment And Management Dashboard Incident Response Strategies DeploymentThis slide represents the dashboard to assess, analyze and manage the cyber security risks within an organization. It includes details related to directories with direct access, inactive accounts etc. Present the topic in a bit more detail with this Cyber Security Risk Assessment And Management Dashboard Incident Response Strategies Deployment. Use it as a tool for discussion and navigation on Accounts, Globally, Unresolved. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
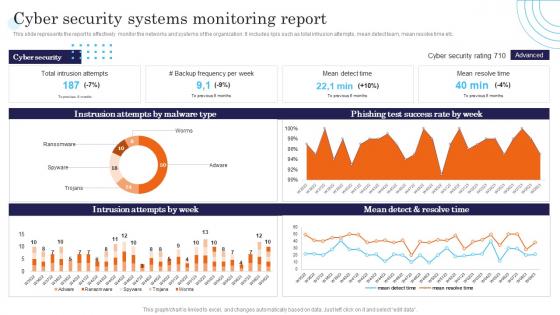 Cyber Security Systems Monitoring Report Incident Response Strategies Deployment
Cyber Security Systems Monitoring Report Incident Response Strategies DeploymentThis slide represents the report to effectively monitor the networks and systems of the organization. It includes kpis such as total intrusion attempts, mean detect team, mean resolve time etc. Present the topic in a bit more detail with this Cyber Security Systems Monitoring Report Incident Response Strategies Deployment. Use it as a tool for discussion and navigation on Success, Resolve, Intrusion. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
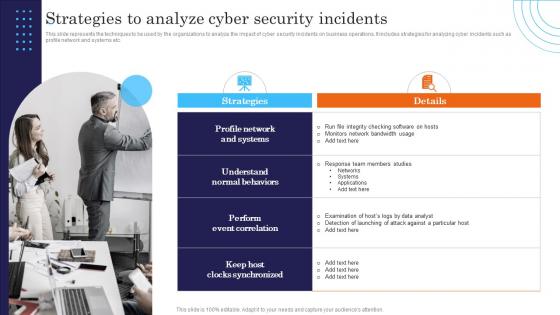 Strategies To Analyze Cyber Security Incidents Response Strategies Deployment
Strategies To Analyze Cyber Security Incidents Response Strategies DeploymentThis slide represents the techniques to be used by the organizations to analyze the impact of cyber security incidents on business operations. It includes strategies for analyzing cyber incidents such as profile network and systems etc. Introducing Strategies To Analyze Cyber Security Incidents Response Strategies Deployment to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Details, Strategies, Correlation, using this template. Grab it now to reap its full benefits.
-
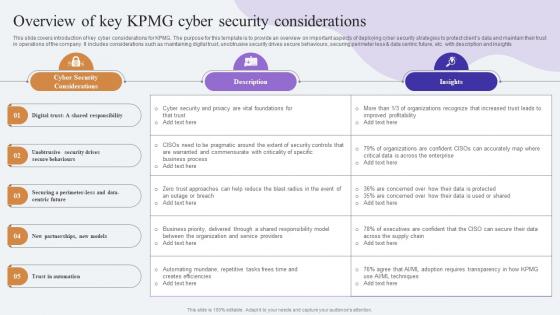 Overview Of Key KPMG Cyber Security Comprehensive Guide To KPMG Strategy SS
Overview Of Key KPMG Cyber Security Comprehensive Guide To KPMG Strategy SSThis slide covers introduction of key cyber considerations for KPMG. The purpose for this template is to provide an overview on important aspects of deploying cyber security strategies to protect clients data and maintain their trust in operations of the company. It includes considerations such as maintaining digital trust, unobtrusive security drives secure behaviours, securing perimeter less data centric future, etc. with description and insights.Present the topic in a bit more detail with this Overview Of Key KPMG Cyber Security Comprehensive Guide To KPMG Strategy SS. Use it as a tool for discussion and navigation on Security Considerations, Warranted Commensurate, Automating Mundane. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
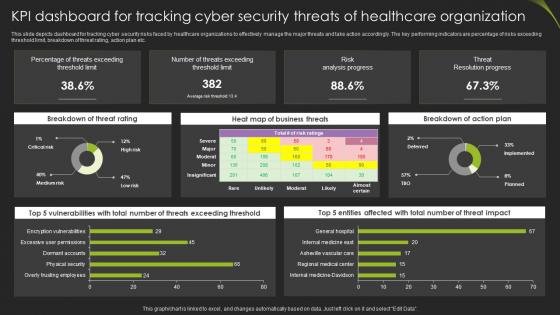 Kpi Dashboard For Tracking Cyber Security Threats Of Healthcare Organization
Kpi Dashboard For Tracking Cyber Security Threats Of Healthcare OrganizationThis slide depicts dashboard for tracking cyber security risks faced by healthcare organizations to effectively manage the major threats and take action accordingly. The key performing indicators are percentage of risks exceeding threshold limit, breakdown of threat rating, action plan etc. Introducing our Kpi Dashboard For Tracking Cyber Security Threats Of Healthcare Organization set of slides. The topics discussed in these slides are Breakdown Of Threat, Business Threats. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
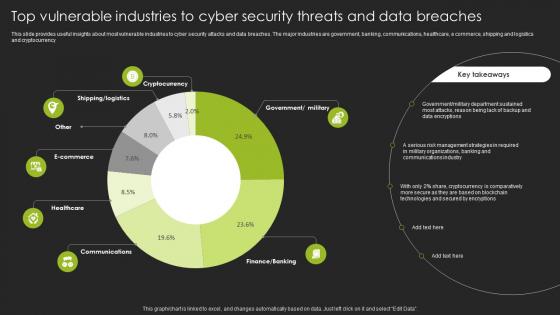 Top Vulnerable Industries To Cyber Security Threats And Data Breaches
Top Vulnerable Industries To Cyber Security Threats And Data BreachesThis slide provides useful insights about most vulnerable industries to cyber security attacks and data breaches. The major industries are government, banking, communications, healthcare, e commerce, shipping and logistics and cryptocurrency Introducing our Top Vulnerable Industries To Cyber Security Threats And Data Breaches set of slides. The topics discussed in these slides are Government, Department. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
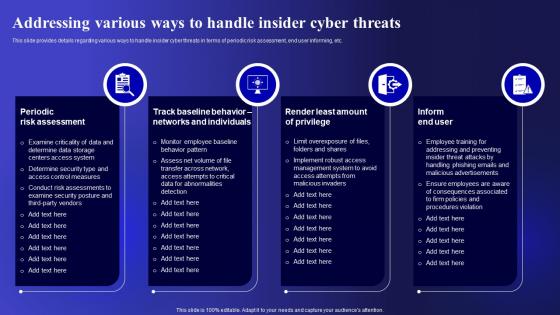 Addressing Various Ways To Handle Cyber Threats Management To Enable Digital Assets Security
Addressing Various Ways To Handle Cyber Threats Management To Enable Digital Assets SecurityThis slide provides details regarding various ways to handle insider cyber threats in terms of periodic risk assessment, end user informing, etc. Present the topic in a bit more detail with this Addressing Various Ways To Handle Cyber Threats Management To Enable Digital Assets Security. Use it as a tool for discussion and navigation on Periodic Risk Assessment, Individuals, Implement. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
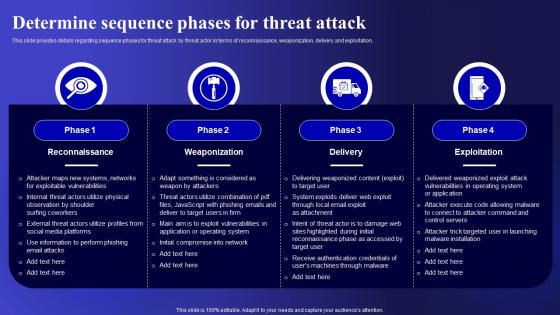 Determine Sequence Phases For Cyber Threats Management To Enable Digital Assets Security
Determine Sequence Phases For Cyber Threats Management To Enable Digital Assets SecurityThis slide provides details regarding sequence phases for threat attack by threat actor in terms of reconnaissance, weaponization, delivery and exploitation. Deliver an outstanding presentation on the topic using this Determine Sequence Phases For Cyber Threats Management To Enable Digital Assets Security. Dispense information and present a thorough explanation of Reconnaissance, Weaponization, Exploitation using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
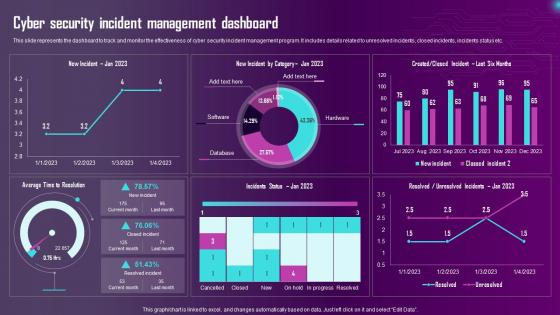 Cyber Security Incident Management Dashboard Ppt Summary Design Ideas
Cyber Security Incident Management Dashboard Ppt Summary Design IdeasThis slide represents the dashboard to track and monitor the effectiveness of cyber security incident management program. It includes details related to unresolved incidents, closed incidents, incidents status etc.Deliver an outstanding presentation on the topic using this Cyber Security Incident Management Dashboard Ppt Summary Design Ideas. Dispense information and present a thorough explanation of Cyber Security Incident, Management Dashboard using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
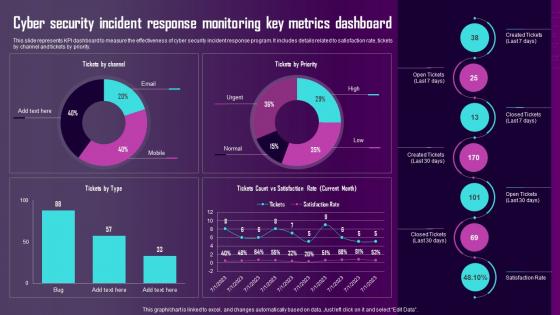 Cyber Security Incident Response Monitoring Key Metrics Dashboard Ppt Slides Inspiration
Cyber Security Incident Response Monitoring Key Metrics Dashboard Ppt Slides InspirationThis slide represents KPI dashboard to measure the effectiveness of cyber security incident response program. It includes details related to satisfaction rate, tickets by channel and tickets by priority.Deliver an outstanding presentation on the topic using this Cyber Security Incident Response Monitoring Key Metrics Dashboard Ppt Slides Inspiration. Dispense information and present a thorough explanation of Cyber Security, Incident Response, Monitoring Key using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Emerging Cyber Security Incident Management Trends For 2023 Ppt Slides Background
Emerging Cyber Security Incident Management Trends For 2023 Ppt Slides BackgroundThis slide represents the emerging trends in cyber attacks faced by the enterprises. It includes details related to cyber attacks experienced by enterprises, top global fraud types and volume of cyber security incidents by sector.Deliver an outstanding presentation on the topic using this Emerging Cyber Security Incident Management Trends For 2023 Ppt Slides Background. Dispense information and present a thorough explanation of Cyber Attacks, Experienced Enterprises, Security Incidents using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber security risk assessment matrix ppt powerpoint presentation file guidelines cpb
Cyber security risk assessment matrix ppt powerpoint presentation file guidelines cpbPresenting this set of slides with name Cyber Security Risk Assessment Matrix Ppt Powerpoint Presentation File Guidelines Cpb. This is an editable Powerpoint four stages graphic that deals with topics like Cyber Security Risk Assessment Matrix to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Cyber security risk management ppt powerpoint presentation file background image cpb
Cyber security risk management ppt powerpoint presentation file background image cpbPresenting this set of slides with name Cyber Security Risk Management Ppt Powerpoint Presentation File Background Image Cpb. This is an editable Powerpoint three stages graphic that deals with topics like Cyber Security Risk Management to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Cyber security awareness ppt powerpoint presentation infographic template slide cpb
Cyber security awareness ppt powerpoint presentation infographic template slide cpbPresenting this set of slides with name Cyber Security Awareness Ppt Powerpoint Presentation Infographic Template Slide Cpb. This is an editable Powerpoint five stages graphic that deals with topics like Cyber Security Awareness to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
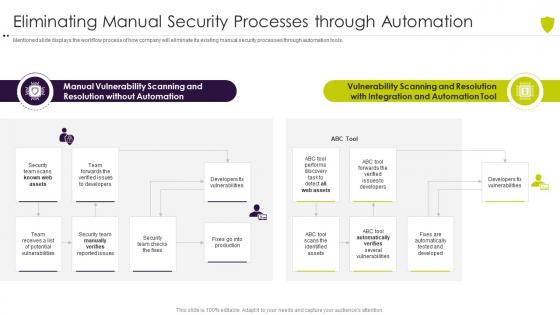 Eliminating manual security processes managing cyber risk in a digital age
Eliminating manual security processes managing cyber risk in a digital ageMentioned slide displays the workflow process of how company will eliminate its existing manual security processes through automation tools. Present the topic in a bit more detail with this Eliminating Manual Security Processes Managing Cyber Risk In A Digital Age. Use it as a tool for discussion and navigation on Vulnerability, Scanning, Resolution, Team. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
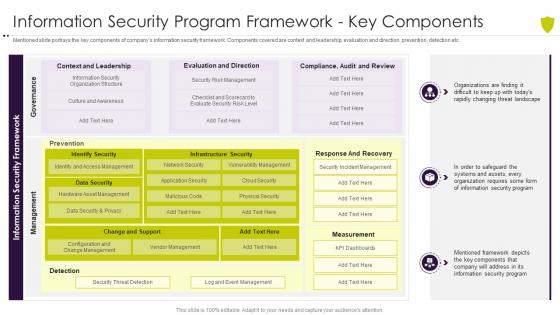 Information security program framework managing cyber risk in a digital age
Information security program framework managing cyber risk in a digital ageMentioned slide portrays the key components of companys information security framework. Components covered are context and leadership, evaluation and direction, prevention, detection etc. Deliver an outstanding presentation on the topic using this Information Security Program Framework Managing Cyber Risk In A Digital Age. Dispense information and present a thorough explanation of Information Security Program Framework Key Components using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
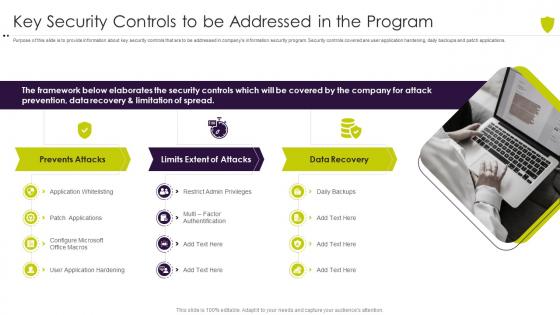 Key security controls to be addressed in the program managing cyber risk in a digital age
Key security controls to be addressed in the program managing cyber risk in a digital agePurpose of this slide is to provide information about key security controls that are to be addressed in companys information security program. Security controls covered are user application hardening, daily backups and patch applications. Increase audience engagement and knowledge by dispensing information using Key Security Controls To Be Addressed In The Program Managing Cyber Risk In A Digital Age. This template helps you present information on three stages. You can also present information on Framework, Elaborates, Security, Controls, Recovery using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
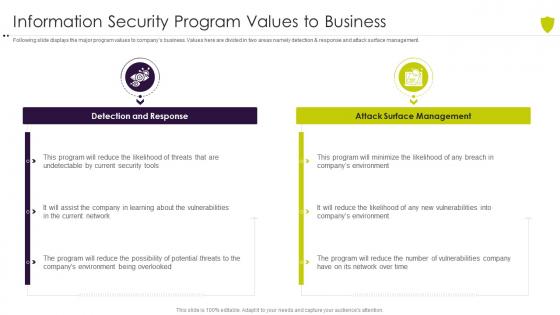 Managing cyber risk in a digital age information security program values to business
Managing cyber risk in a digital age information security program values to businessFollowing slide displays the major program values to companys business. Values here are divided in two areas namely detection and response and attack surface management. Introducing Managing Cyber Risk In A Digital Age Information Security Program Values To Business to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Response, Management, Vulnerabilities, using this template. Grab it now to reap its full benefits.
-
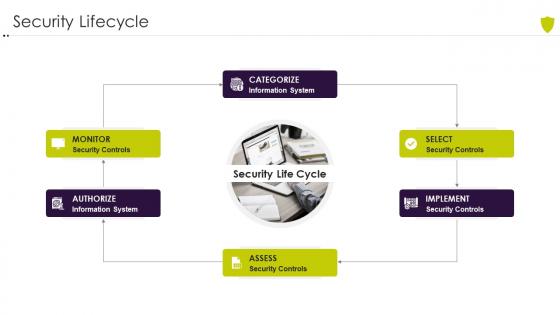 Security lifecycle managing cyber risk in a digital age
Security lifecycle managing cyber risk in a digital ageIncrease audience engagement and knowledge by dispensing information using Security Lifecycle Managing Cyber Risk In A Digital Age. This template helps you present information on one stages. You can also present information on Security Lifecycle using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
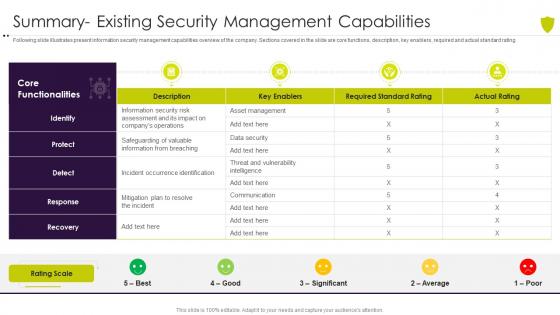 Summary existing security managing cyber risk in a digital age
Summary existing security managing cyber risk in a digital ageFollowing slide illustrates present information security management capabilities overview of the company. Sections covered in the slide are core functions, description, key enablers, required and actual standard rating. Present the topic in a bit more detail with this Summary Existing Security Managing Cyber Risk In A Digital Age. Use it as a tool for discussion and navigation on Summary Existing Security Management Capabilities. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
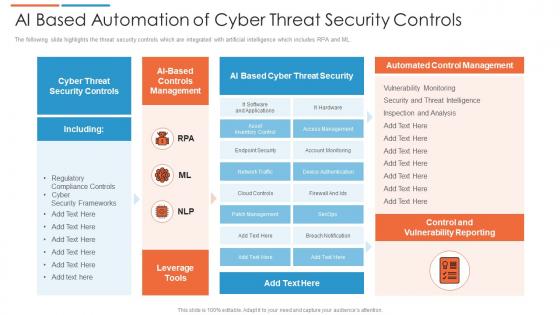 Ai based automation of cyber threat security controls
Ai based automation of cyber threat security controlsThe following slide highlights the threat security controls which are integrated with artificial intelligence which includes RPA and ML. Introducing our AI Based Automation Of Cyber Threat Security Controls set of slides. The topics discussed in these slides are Cyber Threat Security, Automated Control Management, Control And Vulnerability Reporting. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
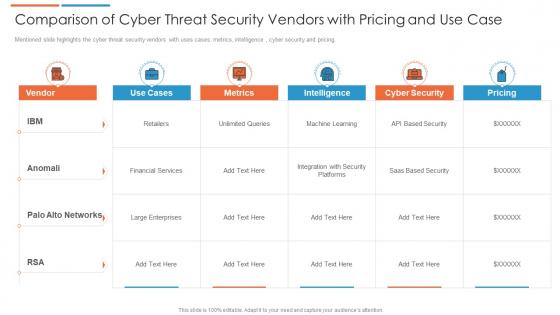 Comparison of cyber threat security vendors with pricing and use case
Comparison of cyber threat security vendors with pricing and use caseMentioned slide highlights the cyber threat security vendors with uses cases, metrics, intelligence , cyber security and pricing. Presenting our well structured Comparison Of Cyber Threat Security Vendors With Pricing And Use Case. The topics discussed in this slide are Financial Services, Cyber Security, Intelligence. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
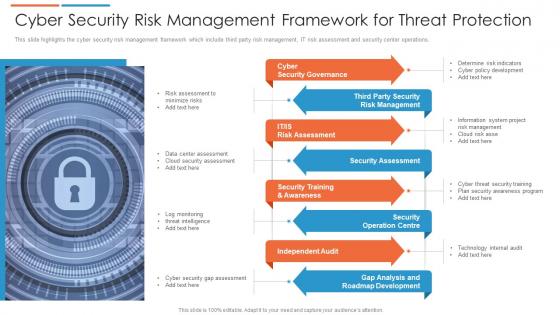 Cyber security risk management framework for threat protection
Cyber security risk management framework for threat protectionThis slide highlights the cyber security risk management framework which include third party risk management, IT risk assessment and security center operations. Presenting our set of slides with Cyber Security Risk Management Framework For Threat Protection. This exhibits information on eight stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cyber Security Governance, Security Assessment, Independent Audit.
-
 Cyber security threat management system
Cyber security threat management systemThe following slide illustrates the cyber security threat management system which includes threat containment, logging and traceability management. Introducing our Cyber Security Threat Management System set of slides. The topics discussed in these slides are Threat Containment And Remediation, Identify Management, Application Visibility And Control. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
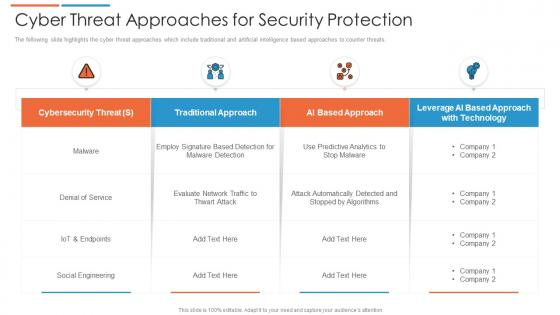 Cyber threat approaches for security protection
Cyber threat approaches for security protectionThe following slide highlights the cyber threat approaches which include traditional and artificial intelligence based approaches to counter threats. Presenting our well structured Cyber Threat Approaches For Security Protection. The topics discussed in this slide are Cybersecurity Threat, Social Engineering, Traditional Approach. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
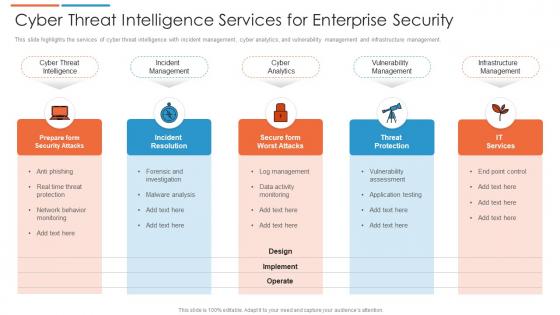 Cyber threat intelligence services for enterprise security
Cyber threat intelligence services for enterprise securityThis slide highlights the services of cyber threat intelligence with incident management, cyber analytics, and vulnerability management and infrastructure management. Presenting our set of slides with Cyber Threat Intelligence Services For Enterprise Security. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Infrastructure Management, Vulnerability Management, Cyber Analytics.
-
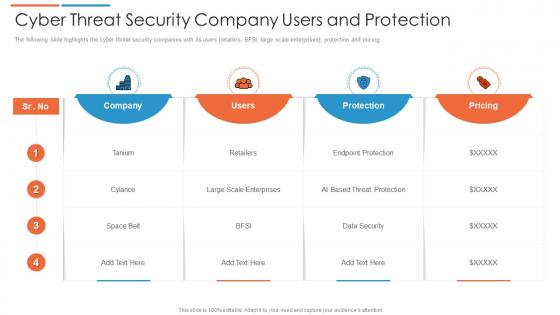 Cyber threat security company users and protection
Cyber threat security company users and protectionThe following slide highlights the cyber threat security companies with its users retailers, BFSI, large scale enterprises, protection and pricing. Introducing our Cyber Threat Security Company Users And Protection set of slides. The topics discussed in these slides are Pricing, Company, Users. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Cyber threat security icon to capture sensitive information
Cyber threat security icon to capture sensitive informationIntroducing our premium set of slides with Cyber Threat Security Icon To Capture Sensitive Information. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cyber Threat Security Icon To Capture Sensitive Information. So download instantly and tailor it with your information.
-
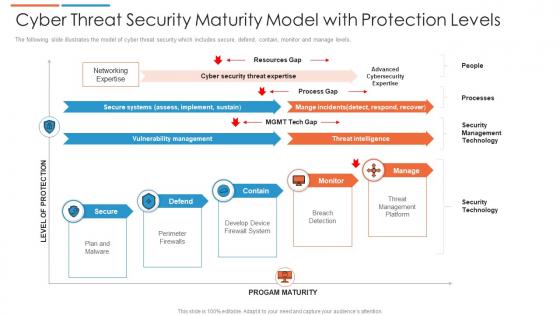 Cyber threat security maturity model with protection levels
Cyber threat security maturity model with protection levelsThe following slide illustrates the model of cyber threat security which includes secure, defend, contain, monitor and manage levels. Presenting our well structured Cyber Threat Security Maturity Model With Protection Levels. The topics discussed in this slide are Security Management Technology, Threat Management Platform, Threat Intelligence. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
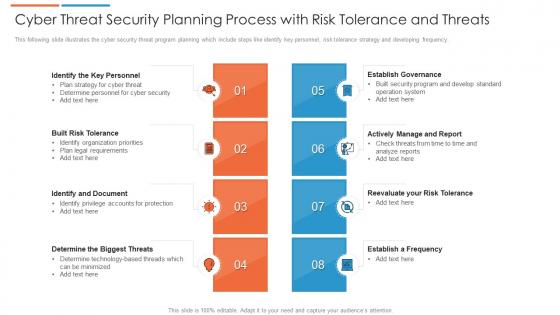 Cyber threat security planning process with risk tolerance and threats
Cyber threat security planning process with risk tolerance and threatsThis following slide illustrates the cyber security threat program planning which include steps like identify key personnel, risk tolerance strategy and developing frequency. Presenting our set of slides with Cyber Threat Security Planning Process With Risk Tolerance And Threats. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Built Risk Tolerance, Identify And Document, Establish Governance.
-
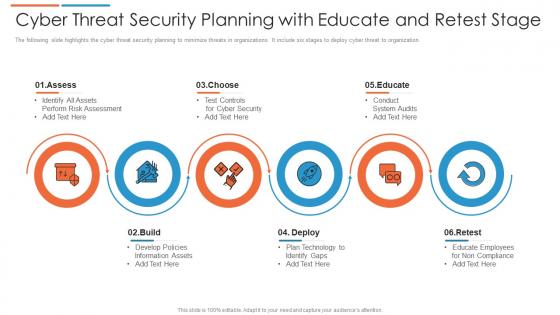 Cyber threat security planning with educate and retest stage
Cyber threat security planning with educate and retest stageThe following slide highlights the cyber threat security planning to minimize threats in organizations. It include six stages to deploy cyber threat to organization. Introducing our premium set of slides with Cyber Threat Security Planning With Educate And Retest Stage. Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Deploy, Retest, Educate. So download instantly and tailor it with your information.
-
 Cyber threat strategies for security protection
Cyber threat strategies for security protectionThis slide highlights the cyber threat strategies that include risk assessment, phishing program, software protocols and end point protection. Presenting our set of slides with Cyber Threat Strategies For Security Protection. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Phishing Program, Software Protocols, End Point Protection.
-
 Key cyber security threat to organizations
Key cyber security threat to organizationsThis slide displays different types of cyber security threats which impacts organization negatively. It include malware, emotet, phishing and SQL injection. Introducing our premium set of slides with Key Cyber Security Threat To Organizations. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Malware, Phishing, SQL Injection. So download instantly and tailor it with your information.
-
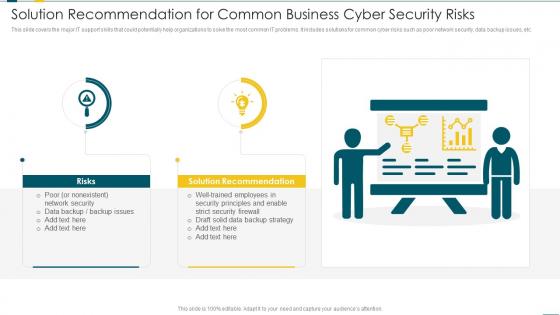 Solution Recommendation For Common Business Cyber Security Risks
Solution Recommendation For Common Business Cyber Security RisksThis slide covers the major IT support skills that could potentially help organizations to solve the most common IT problems. It includes solutions for common cyber risks such as poor network security, data backup issues, etc. Introducing our premium set of slides with Solution Recommendation For Common Business Cyber Security Risks. Ellicudate the two stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Risks, Solution Recommendation, Network Security. So download instantly and tailor it with your information.
-
 Checklist For Effectively Managing Asset Security Risk Based Methodology To Cyber
Checklist For Effectively Managing Asset Security Risk Based Methodology To CyberFollowing slide displays system management checklist that company will use for effectively managing asset security. It also includes system management activities and frequency of performing them.Increase audience engagement and knowledge by dispensing information using Checklist For Effectively Managing Asset Security Risk Based Methodology To Cyber This template helps you present information on one stage. You can also present information on System Monitoring, Data Backup, Security Patches using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
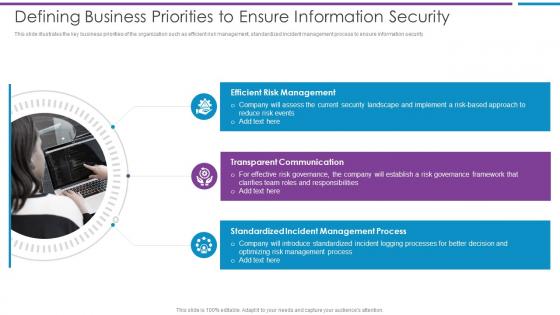 Defining Business Priorities To Ensure Information Security Risk Based Methodology To Cyber
Defining Business Priorities To Ensure Information Security Risk Based Methodology To CyberThis slide illustrates the key business priorities of the organization such as efficient risk management, standardized incident management process to ensure information security.Increase audience engagement and knowledge by dispensing information using Defining Business Priorities To Ensure Information Security Risk Based Methodology To Cyber This template helps you present information on three stages. You can also present information on Efficient Risk Management, Transparent Communication, Standardized Incident using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Eliminating Manual Security Processes Through Automation Risk Based Methodology To Cyber
Eliminating Manual Security Processes Through Automation Risk Based Methodology To CyberMentioned slide displays the workflow process of how company will eliminate its existing manual security processes through automation tools.Present the topic in a bit more detail with this Eliminating Manual Security Processes Through Automation Risk Based Methodology To Cyber Use it as a tool for discussion and navigation on Manual Vulnerability, Scanning And Resolution, Vulnerability Scanning This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Icons Slide For Risk Based Methodology To Cyber and Information Security
Icons Slide For Risk Based Methodology To Cyber and Information SecurityPresenting our well crafted Icons Slide For Risk Based Methodology To Cyber and Information Security set of slides. The slides include icons that are innovatively designed by our team of experts. The icons are easy to edit so you can conveniently increase or decrease their size without any loss in resolution. Therefore, grab them instantly
-
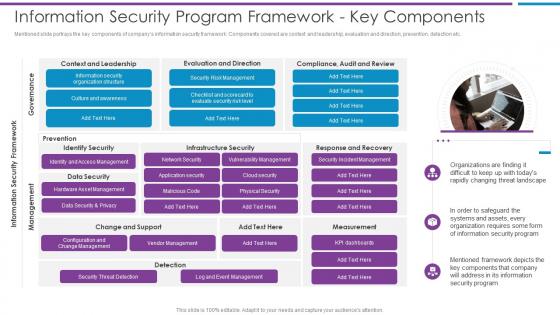 Information Security Program Framework Key Components Risk Based Methodology To Cyber
Information Security Program Framework Key Components Risk Based Methodology To CyberMentioned slide portrays the key components of companys information security framework. Components covered are context and leadership, evaluation and direction, prevention, detection etc.Introducing Information Security Program Framework Key Components Risk Based Methodology To Cyber to increase your presentation threshold. Encompassed with one stage this template is a great option to educate and entice your audience. Dispence information on Culture And Awareness, Security Risk Management, Data Security And Privacy using this template. Grab it now to reap its full benefits.