Powerpoint Templates and Google slides for Risk Introducing Technologies
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Introducing A Risk Based Approach To Cyber Security Powerpoint Presentation Slides
Introducing A Risk Based Approach To Cyber Security Powerpoint Presentation SlidesDeliver an informational PPT on various topics by using this Introducing A Risk Based Approach To Cyber Security Powerpoint Presentation Slides. This deck focuses and implements best industry practices, thus providing a birds eye view of the topic. Encompassed with fifty two slides, designed using high-quality visuals and graphics, this deck is a complete package to use and download. All the slides offered in this deck are subjective to innumerable alterations, thus making you a pro at delivering and educating. You can modify the color of the graphics, background, or anything else as per your needs and requirements. It suits every business vertical because of its adaptable layout.
-
 Introducing operational risk management framework in banks complete deck
Introducing operational risk management framework in banks complete deckPresenting Introducing Operational Risk Management Framework In Banks Complete Deck. Our slideshow is easy to download and can be presented in standard screen(14:6) and widescreen (16:9) ratios. You can alter the font style, font color, and other components. This presentation is compatible with Google slides. This PPT can be transformed into numerous documents or image formats like PDF or JPEG. High-quality graphics ensure that the picture quality is maintained.
-
 Introducing Risk Management Strategy To Minimize Corporate Regulatory Compliance Strategy SS V
Introducing Risk Management Strategy To Minimize Corporate Regulatory Compliance Strategy SS VThis slide presents an overview of risk management and associated benefits for the company. It includes benefits such as protection of assets, increased operational efficiency, improve decision making, enhanced reputation and compliance with regulations. Increase audience engagement and knowledge by dispensing information using Introducing Risk Management Strategy To Minimize Corporate Regulatory Compliance Strategy SS V. This template helps you present information on six stages. You can also present information on Enhanced Reputation, Compliance With Regulations using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
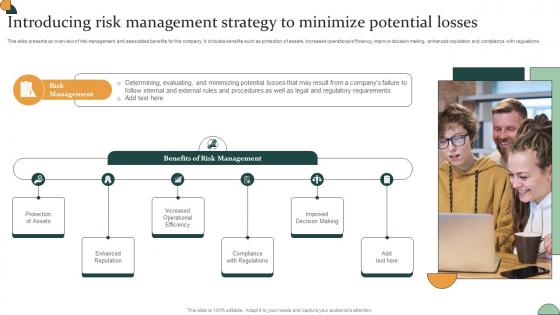
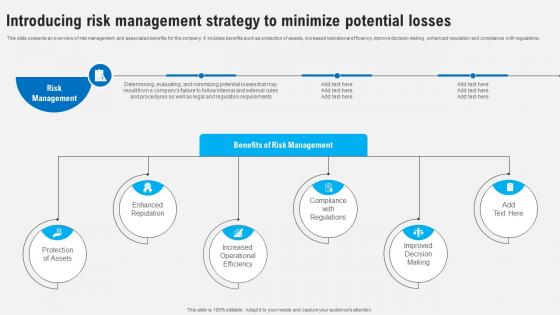 Introducing Risk Management Strategy To Minimize Potential Strategies To Comply Strategy SS V
Introducing Risk Management Strategy To Minimize Potential Strategies To Comply Strategy SS VThis slide presents an overview of risk management and associated benefits for the company. It includes benefits such as protection of assets, increased operational efficiency, improve decision making, enhanced reputation and compliance with regulations. Introducing Introducing Risk Management Strategy To Minimize Potential Strategies To Comply Strategy SS V to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Protection Of Assets, Enhanced Reputation, Compliance With Regulations, using this template. Grab it now to reap its full benefits.
-
 Introducing Risk Management Strategy To Developing Shareholder Trust With Efficient Strategy SS V
Introducing Risk Management Strategy To Developing Shareholder Trust With Efficient Strategy SS VThis slide presents an overview of risk management and associated benefits for the company. It includes benefits such as protection of assets, increased operational efficiency, improve decision making, enhanced reputation and compliance with regulations. Introducing Introducing Risk Management Strategy To Developing Shareholder Trust With Efficient Strategy SS V to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Protection, Reputation, Operational, using this template. Grab it now to reap its full benefits.
-
 Employee And Workplace Introducing Risk Management Strategy To Minimize Potential Strategy SS V
Employee And Workplace Introducing Risk Management Strategy To Minimize Potential Strategy SS VThis slide presents an overview of risk management and associated benefits for the company. It includes benefits such as protection of assets, increased operational efficiency, improve decision making, enhanced reputation and compliance with regulations. Introducing Employee And Workplace Introducing Risk Management Strategy To Minimize Potential Strategy SS V to increase your presentation threshold. Encompassed with Six stages, this template is a great option to educate and entice your audience. Dispence information on Ethical Behavior, Impacts Organizational using this template. Grab it now to reap its full benefits.
-
 Corporate Compliance Strategy Introducing Risk Management Strategy To Minimize Strategy SS V
Corporate Compliance Strategy Introducing Risk Management Strategy To Minimize Strategy SS VThis slide presents an overview of risk management and associated benefits for the company. It includes benefits such as protection of assets, increased operational efficiency, improve decision making, enhanced reputation and compliance with regulations. Increase audience engagement and knowledge by dispensing information using Corporate Compliance Strategy Introducing Risk Management Strategy To Minimize Strategy SS V This template helps you present information on Six stages. You can also present information on Policies And Procedures, Standards For Compliance using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
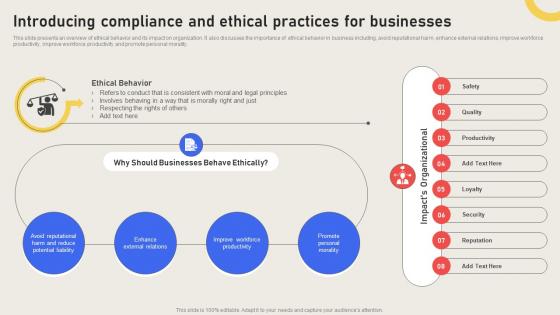 Introducing Compliance And Ethical Practices For Businesses Effective Business Risk Strategy SS V
Introducing Compliance And Ethical Practices For Businesses Effective Business Risk Strategy SS VThis slide presents an overview of ethical behavior and its impact on organization. It also discusses the importance of ethical behavior in business including, avoid reputational harm, enhance external relations, improve workforce productivity, improve workforce productivity and promote personal morality. Present the topic in a bit more detail with this Introducing Compliance And Ethical Practices For Businesses Effective Business Risk Strategy SS V. Use it as a tool for discussion and navigation on Should Businesses Behave, Ethical Behavior. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Introducing Data Compliance And Management Strategy Effective Business Risk Strategy SS V
Introducing Data Compliance And Management Strategy Effective Business Risk Strategy SS VThis slide provides an overview of data compliance and its importance in business. It includes benefits such as easier business process automation, increased trust and credibility, improved data management, protected and enhanced enterprise reputation. Introducing Introducing Data Compliance And Management Strategy Effective Business Risk Strategy SS V to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Easier Business, Process Automation, using this template. Grab it now to reap its full benefits.
-
 Introducing Risk Management Strategy To Minimize Potential Effective Business Risk Strategy SS V
Introducing Risk Management Strategy To Minimize Potential Effective Business Risk Strategy SS VThis slide presents an overview of risk management and associated benefits for the company. It includes benefits such as protection of assets, increased operational efficiency, improve decision making, enhanced reputation and compliance with regulations. Increase audience engagement and knowledge by dispensing information using Introducing Risk Management Strategy To Minimize Potential Effective Business Risk Strategy SS V. This template helps you present information on six stages. You can also present information on Protection Of Assets, Enhanced Reputation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Global Market Insights Cybersecurity Introducing A Risk Based Approach To Cyber Security
Global Market Insights Cybersecurity Introducing A Risk Based Approach To Cyber SecurityFollowing slide illustrates the global market insights of cybersecurity covering statistics related to integrated risk management, investment in cybersecurity and digital transformation.Present the topic in a bit more detail with this Global Market Insights Cybersecurity Introducing A Risk Based Approach To Cyber Security Use it as a tool for discussion and navigation on Fastest Growing Market, Largest Market, Approach To Digital Risk This template is free to edit as deemed fit for your organization. Therefore download it now.
-
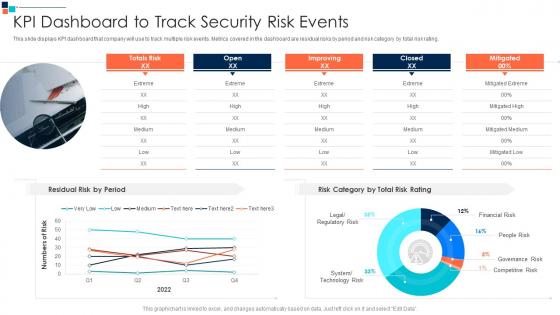 KPI Dashboard To Track Security Risk Events Introducing A Risk Based Approach To Cyber Security
KPI Dashboard To Track Security Risk Events Introducing A Risk Based Approach To Cyber SecurityThis slide displays KPI dashboard that company will use to track multiple risk events. Metrics covered in the dashboard are residual risks by period and risk category by total risk rating.Present the topic in a bit more detail with this KPI Dashboard To Track Security Risk Events Introducing A Risk Based Approach To Cyber Security Use it as a tool for discussion and navigation on Kpi Dashboard To Track Security Risk Events This template is free to edit as deemed fit for your organization. Therefore download it now.
-
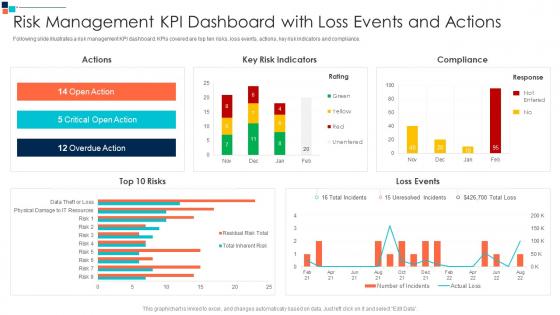 Risk Management KPI Dashboard With Loss Events And Actions Introducing A Risk Based Approach
Risk Management KPI Dashboard With Loss Events And Actions Introducing A Risk Based ApproachFollowing slide illustrates a risk management KPI dashboard. KPIs covered are top ten risks, loss events, actions, key risk indicators and compliance.Present the topic in a bit more detail with this Risk Management KPI Dashboard With Loss Events And Actions Introducing A Risk Based Approach Use it as a tool for discussion and navigation on Critical Open Action, Overdue Action, Key Risk Indicators This template is free to edit as deemed fit for your organization. Therefore download it now.
-
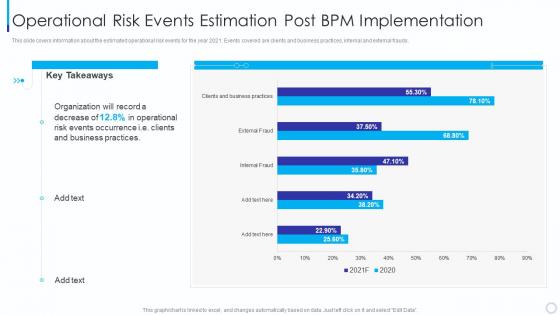 Operational Risk Events Introducing Business Process Management Methodology
Operational Risk Events Introducing Business Process Management MethodologyThis slide covers information about the estimated operational risk events for the year 2021. Events covered are clients and business practices, internal and external frauds. Present the topic in a bit more detail with this Operational Risk Events Introducing Business Process Management Methodology. Use it as a tool for discussion and navigation on Operational Risk Events Estimation Post Bpm Implementation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
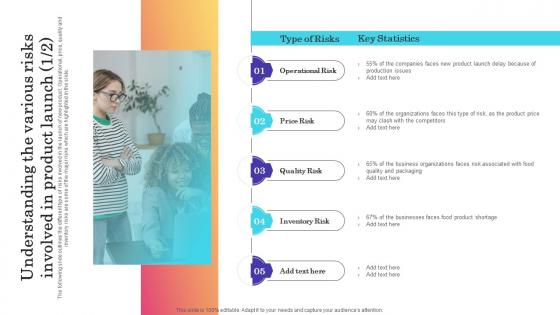 Understanding The Various Risks Involved In Product Introducing New Product In Food And Beverage
Understanding The Various Risks Involved In Product Introducing New Product In Food And BeverageThe following slide outlines the different type of risks involved in the launch of new product. Operational, price, quality and inventory risks are some of the major risks which are highlighted in the slide. Increase audience engagement and knowledge by dispensing information using Understanding The Various Risks Involved In Product Introducing New Product In Food And Beverage. This template helps you present information on one stages. You can also present information on Operational Risk, Price Risk, Quality Risk using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
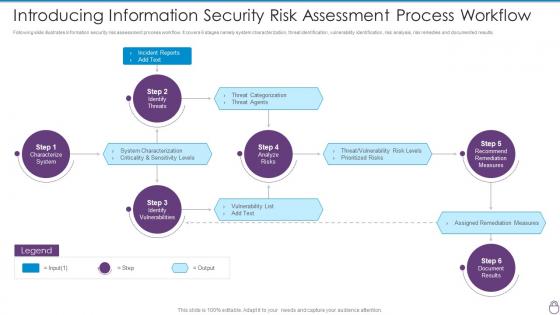 Cybersecurity Risk Management Framework Introducing Information Security Risk Assessment
Cybersecurity Risk Management Framework Introducing Information Security Risk AssessmentFollowing slide illustrates information security risk assessment process workflow. It covers 6 stages namely system characterization, threat identification, vulnerability identification, risk analysis, risk remedies and documented results. Increase audience engagement and knowledge by dispensing information using Cybersecurity Risk Management Framework Introducing Information Security Risk Assessment. This template helps you present information on six stages. You can also present information on Incident Reports, Characterize System, Identify Vulnerabilities, Identify Threats, Analyze Risks using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
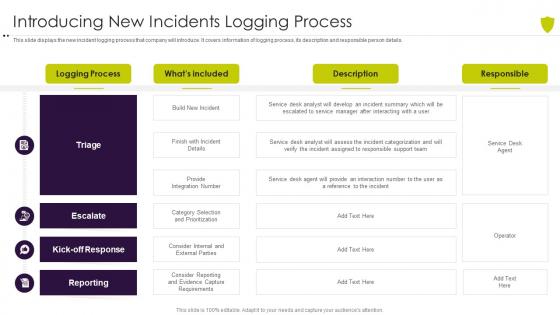 Introducing new incidents logging process managing cyber risk in a digital age
Introducing new incidents logging process managing cyber risk in a digital ageThis slide displays the new incident logging process that company will introduce. It covers information of logging process, its description and responsible person details. Present the topic in a bit more detail with this Introducing New Incidents Logging Process Managing Cyber Risk In A Digital Age. Use it as a tool for discussion and navigation on Introducing New Incidents Logging Process. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
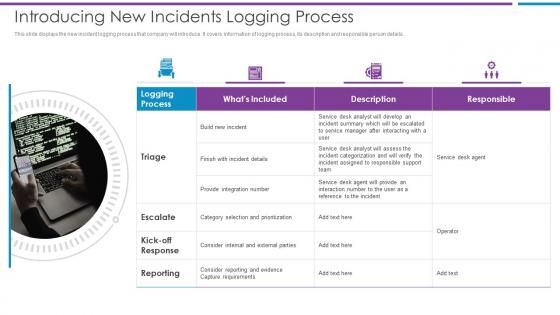 Introducing New Incidents Logging Process Risk Based Methodology To Cyber
Introducing New Incidents Logging Process Risk Based Methodology To CyberThis slide displays the new incident logging process that company will introduce. It covers information of logging process, its description and responsible person details.Increase audience engagement and knowledge by dispensing information using Introducing New Incidents Logging Process Risk Based Methodology To Cyber This template helps you present information on one stage. You can also present information on Provide Integration, Category Selection, Consider Internal using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
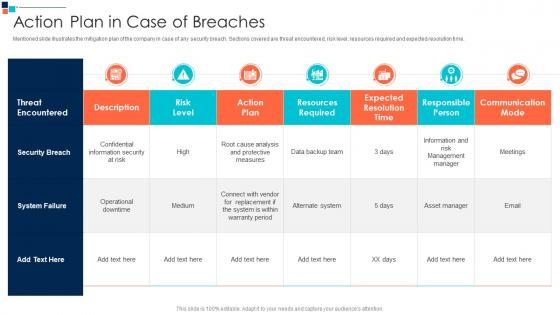 Action Plan In Case Of Breaches Introducing A Risk Based Approach To Cyber Security
Action Plan In Case Of Breaches Introducing A Risk Based Approach To Cyber SecurityMentioned slide illustrates the mitigation plan of the company in case of any security breach. Sections covered are threat encountered, risk level, resources required and expected resolution time.Present the topic in a bit more detail with this Action Plan In Case Of Breaches Introducing A Risk Based Approach To Cyber Security Use it as a tool for discussion and navigation on Expected Resolution Time, Responsible Person, Communication Mode This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Agenda Of Introducing A Risk Based Approach To Cyber Security
Agenda Of Introducing A Risk Based Approach To Cyber SecurityIntroducing Agenda Of Introducing A Risk Based Approach To Cyber Security to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Agenda using this template. Grab it now to reap its full benefits.
-
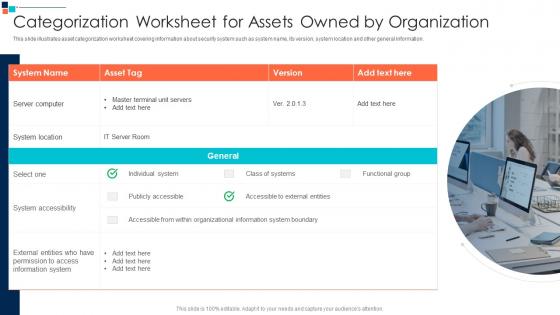 Categorization Worksheet For Assets Owned By Organization Introducing A Risk Based
Categorization Worksheet For Assets Owned By Organization Introducing A Risk BasedThis slide illustrates asset categorization worksheet covering information about security system such as system name, its version, system location and other general information.Increase audience engagement and knowledge by dispensing information using Categorization Worksheet For Assets Owned By Organization Introducing A Risk Based This template helps you present information on one stage. You can also present information on System Accessibility, External Entities, Information System using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Checklist For Effectively Managing Asset Security Introducing A Risk Based Approach
Checklist For Effectively Managing Asset Security Introducing A Risk Based ApproachFollowing slide displays system management checklist that company will use for effectively managing asset security. It also includes system management activities and frequency of performing them.Introducing Checklist For Effectively Managing Asset Security Introducing A Risk Based Approach to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispence information on System Monitoring, Virus Scanning, System Monitoring using this template. Grab it now to reap its full benefits.
-
 Communication Plan For Cyber Breaches Introducing A Risk Based Approach To Cyber Security
Communication Plan For Cyber Breaches Introducing A Risk Based Approach To Cyber SecurityMentioned slide portrays communication plan that company will use for effectively managing cyber breaches. Sections covered here are what to communicate, description, delivery method, frequency and responsible.Present the topic in a bit more detail with this Communication Plan For Cyber Breaches Introducing A Risk Based Approach To Cyber Security Use it as a tool for discussion and navigation on Evaluate Sprint Status, Quality Standards, Project Coordinator This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Criticality Assessment Of Identified Assets Introducing A Risk Based Approach To Cyber Security
Criticality Assessment Of Identified Assets Introducing A Risk Based Approach To Cyber SecurityFollowing slide demonstrates the asset criticality of identified system components. It covers details such as major components used along with criticality rating and failure cost.Deliver an outstanding presentation on the topic using this Criticality Assessment Of Identified Assets Introducing A Risk Based Approach To Cyber Security Dispense information and present a thorough explanation of Infrastructure Hardware, Routers And Switches, Server Computers using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Defining Business Security Introducing A Risk Based Approach To Cyber Security
Defining Business Security Introducing A Risk Based Approach To Cyber SecurityThis slide illustrates the key business priorities of the organization such as efficient risk management, standardized incident management process to ensure information security.Introducing Defining Business Security Introducing A Risk Based Approach To Cyber Security to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Efficient Risk Management, Standardized Incident, Management Process using this template. Grab it now to reap its full benefits.
-
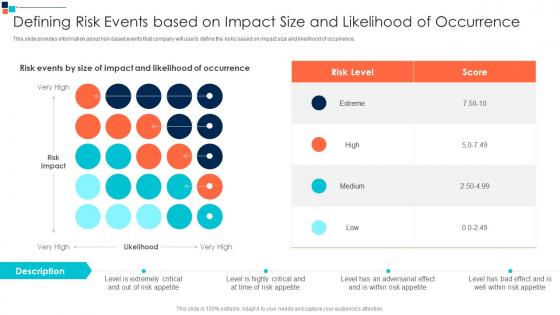 Defining Risk Events Based On Introducing A Risk Based Approach To Cyber Security
Defining Risk Events Based On Introducing A Risk Based Approach To Cyber SecurityThis slide provides information about risk based events that company will use to define the risks based on impact size and likelihood of occurrence.Present the topic in a bit more detail with this Defining Risk Events Based On Introducing A Risk Based Approach To Cyber Security Use it as a tool for discussion and navigation on Defining Risk Events Based On Impact Size And Likelihood Of Occurrence This template is free to edit as deemed fit for your organization. Therefore download it now.
-
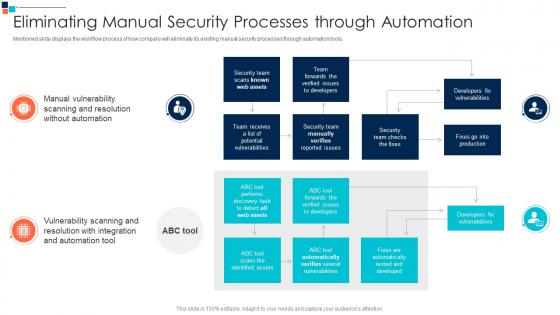 Eliminating Manual Security Introducing A Risk Based Approach To Cyber Security
Eliminating Manual Security Introducing A Risk Based Approach To Cyber SecurityMentioned slide displays the workflow process of how company will eliminate its existing manual security processes through automation tools.Present the topic in a bit more detail with this Eliminating Manual Security Introducing A Risk Based Approach To Cyber Security Use it as a tool for discussion and navigation on Manual Vulnerability, Scanning And Resolution, Automation Vulnerability This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Embedding Risk Based Approach Into Introducing A Risk Based Approach To Cyber Security
Embedding Risk Based Approach Into Introducing A Risk Based Approach To Cyber SecurityPurpose of this slide is to highlight the risK based approach and process efficiency along with the cost incur details. It also shows that company will develop agile security and privacy models.Introducing Embedding Risk Based Approach Into Introducing A Risk Based Approach To Cyber Security to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Cyberrisk Management, Security Organization, Information Security Processes using this template. Grab it now to reap its full benefits.
-
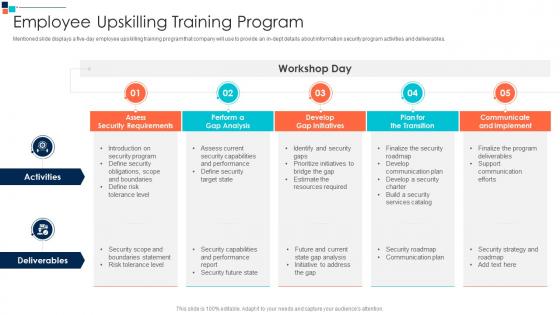 Employee Upskilling Training Program Introducing A Risk Based Approach To Cyber Security
Employee Upskilling Training Program Introducing A Risk Based Approach To Cyber SecurityMentioned slide displays a five day employee upskilling training program that company will use to provide an in dept details about information security program activities and deliverables.Present the topic in a bit more detail with this Employee Upskilling Training Program Introducing A Risk Based Approach To Cyber Security Use it as a tool for discussion and navigation on Assess Security Requirements, Perform A Gap Analysis, Develop Gap Initiatives This template is free to edit as deemed fit for your organization. Therefore download it now.
-
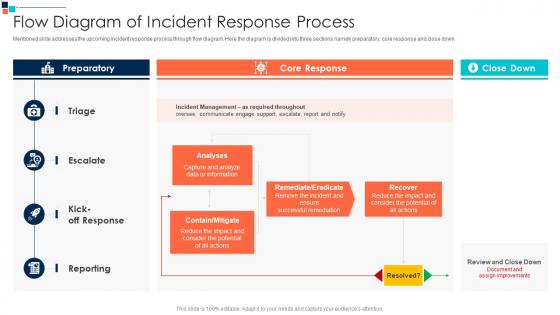 Flow Diagram Of Incident Response Process Introducing A Risk Based Approach To Cyber Security
Flow Diagram Of Incident Response Process Introducing A Risk Based Approach To Cyber SecurityMentioned slide addresses the upcoming incident response process through flow diagram. Here the diagram is divided into three sections namely preparatory, core response and close down.Present the topic in a bit more detail with this Flow Diagram Of Incident Response Process Introducing A Risk Based Approach To Cyber Security Use it as a tool for discussion and navigation on Remediate Eradicate, Contain Mitigate, Consider The Potential This template is free to edit as deemed fit for your organization. Therefore download it now.
-
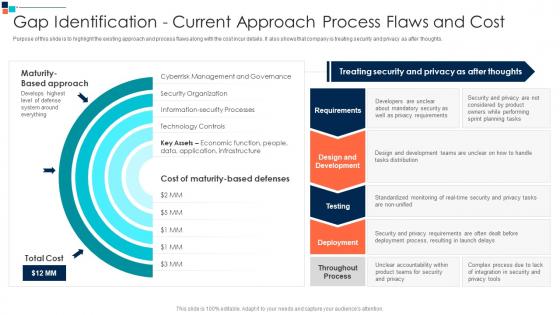 Gap Identification Current Approach Process Flaws And Cost Introducing A Risk Based Approach
Gap Identification Current Approach Process Flaws And Cost Introducing A Risk Based ApproachPurpose of this slide is to highlight the existing approach and process flaws along with the cost incur details. It also shows that company is treating security and privacy as after thoughts.Introducing Gap Identification Current Approach Process Flaws And Cost Introducing A Risk Based Approach to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Maturity Based Approach, Cyberrisk Management, Security Organization using this template. Grab it now to reap its full benefits.
-
 Icons Slide For Introducing A Risk Based Approach To Cyber Security
Icons Slide For Introducing A Risk Based Approach To Cyber SecurityPresenting our premium Icons Slide For Introducing A Risk Based Approach To Cyber Security set of slides with flexible icons. The icons are designed by our group of professionals. Add these Icons Slide For Introducing A Risk Based Approach To Cyber Security to your presentation to make it visually appealing. Also, edit them according to your requirement. Download it and captive your audience.
-
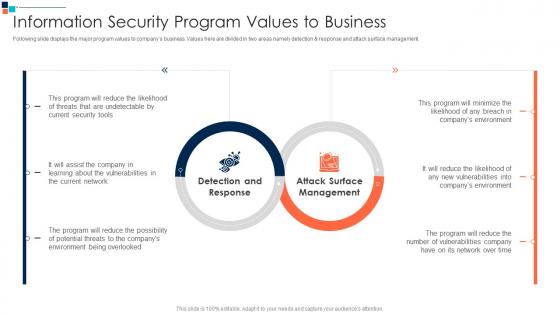 Information Security Program Values To Business Introducing A Risk Based Approach To Cyber
Information Security Program Values To Business Introducing A Risk Based Approach To CyberFollowing slide displays the major program values to companys business. Values here are divided in two areas namely detection AND response and attack surface management.Deliver an outstanding presentation on the topic using this Information Security Program Values To Business Introducing A Risk Based Approach To Cyber Dispense information and present a thorough explanation of Detection And Response, Attack Surface Management, Program Will Reduce using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
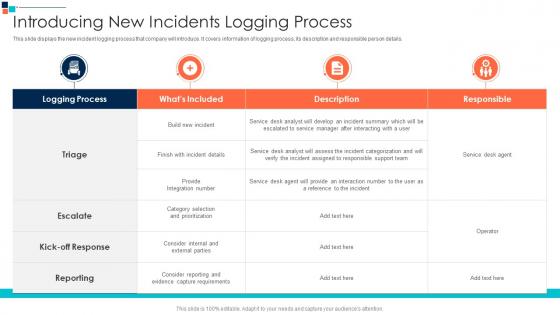 Introducing New Incidents Logging Process Introducing A Risk Based Approach To Cyber Security
Introducing New Incidents Logging Process Introducing A Risk Based Approach To Cyber SecurityThis slide displays the new incident logging process that company will introduce. It covers information of logging process, its description and responsible person details.Present the topic in a bit more detail with this Introducing New Incidents Logging Process Introducing A Risk Based Approach To Cyber Security Use it as a tool for discussion and navigation on Category Selection, Assigned To Responsible, Provide An Interaction This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Key Security Controls To Be Addressed In The Program Introducing A Risk Based Approach
Key Security Controls To Be Addressed In The Program Introducing A Risk Based ApproachPurpose of this slide is to provide information about key security controls that are to be addressed in companys information security program. Security controls covered are user application hardening, daily backups and patch applications.Deliver an outstanding presentation on the topic using this Key Security Controls To Be Addressed In The Program Introducing A Risk Based Approach Dispense information and present a thorough explanation of Restrict Admin Privileges, Factor Authentication, Limits Extent Of Attacks using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
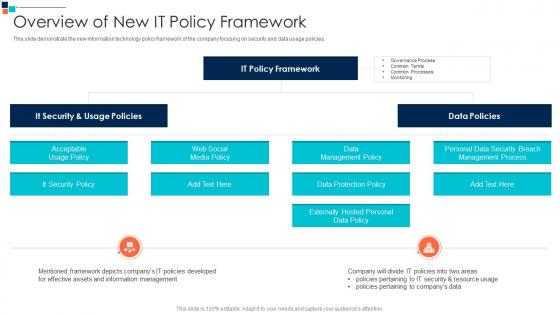 Overview Of New It Policy Framework Introducing A Risk Based Approach To Cyber Security
Overview Of New It Policy Framework Introducing A Risk Based Approach To Cyber SecurityThis slide demonstrate the new information technology policy framework of the company focusing on security and data usage policies.Deliver an outstanding presentation on the topic using this Overview Of New It Policy Framework Introducing A Risk Based Approach To Cyber Security Dispense information and present a thorough explanation of Data Management Policy, Data Protection Policy, Externally Hosted Personal using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
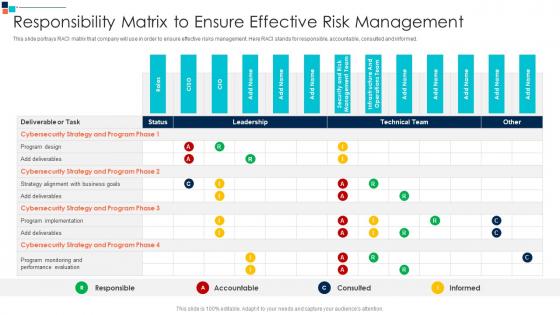 Responsibility Matrix To Ensure Effective Risk Management Introducing A Risk Based Approach
Responsibility Matrix To Ensure Effective Risk Management Introducing A Risk Based ApproachThis slide portrays RACI matrix that company will use in order to ensure effective risks management. Here RACI stands for responsible, accountable, consulted and informed.Present the topic in a bit more detail with this Responsibility Matrix To Ensure Effective Risk Management Introducing A Risk Based Approach Use it as a tool for discussion and navigation on Cybersecurity Strategy, Program Monitoring, Performance Evaluation This template is free to edit as deemed fit for your organization. Therefore download it now.
-
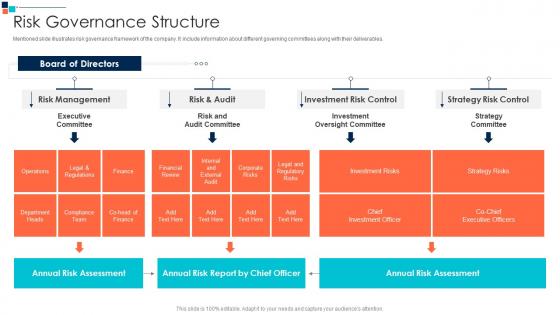 Risk Governance Structure Introducing A Risk Based Approach To Cyber Security
Risk Governance Structure Introducing A Risk Based Approach To Cyber SecurityMentioned slide illustrates risk governance framework of the company. It include information about different governing committees along with their deliverables.Deliver an outstanding presentation on the topic using this Risk Governance Structure Introducing A Risk Based Approach To Cyber Security Dispense information and present a thorough explanation of Legal And Regulatory Risks, Annual Risk Assessment, Investment Risks using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
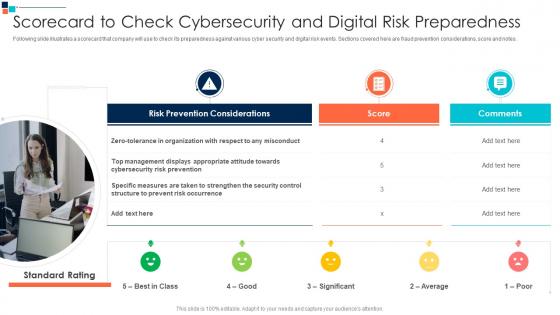 Scorecard To Check Cybersecurity And Digital Risk Preparedness Introducing A Risk Based Approach
Scorecard To Check Cybersecurity And Digital Risk Preparedness Introducing A Risk Based ApproachFollowing slide illustrates a scorecard that company will use to check its preparedness against various cyber security and digital risk events. Sections covered here are fraud prevention considerations, score and notes.Introducing Scorecard To Check Cybersecurity And Digital Risk Preparedness Introducing A Risk Based Approach to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Management Displays, Cybersecurity Risk Prevention, Respect To Any Misconduct using this template. Grab it now to reap its full benefits.
-
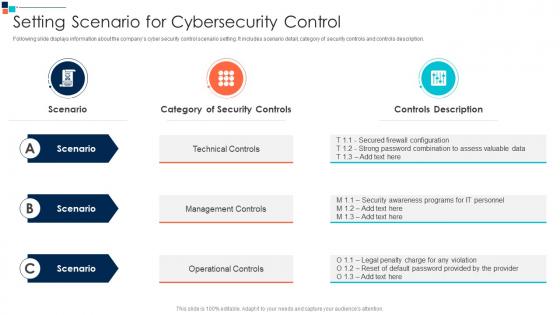 Setting Scenario For Cybersecurity Control Introducing A Risk Based Approach To Cyber Security
Setting Scenario For Cybersecurity Control Introducing A Risk Based Approach To Cyber SecurityFollowing slide displays information about the companys cyber security control scenario setting. It includes scenario detail, category of security controls and controls description.Present the topic in a bit more detail with this Setting Scenario For Cybersecurity Control Introducing A Risk Based Approach To Cyber Security Use it as a tool for discussion and navigation on Technical Controls, Management Controls, Operational Controls This template is free to edit as deemed fit for your organization. Therefore download it now.
-
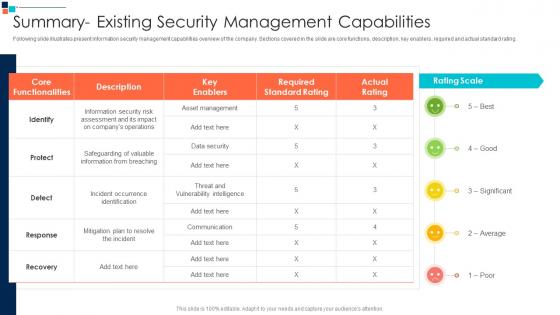 Summary Existing Security Management Capabilities Introducing A Risk Based
Summary Existing Security Management Capabilities Introducing A Risk BasedFollowing slide illustrates present information security management capabilities overview of the company. Sections covered in the slide are core functions, description, key enablers, required and actual standard rating.Deliver an outstanding presentation on the topic using this Summary Existing Security Management Capabilities Introducing A Risk Based Dispense information and present a thorough explanation of Incident Occurrence Identification, Safeguarding Of Valuable, Information From Breaching using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Table Of Contents For Introducing A Risk Based Approach To Cyber Security
Table Of Contents For Introducing A Risk Based Approach To Cyber SecurityPresent the topic in a bit more detail with this Table Of Contents For Introducing A Risk Based Approach To Cyber Security Use it as a tool for discussion and navigation on Global Market Insights, Companies Digitization Levels, About Security Program This template is free to edit as deemed fit for your organization. Therefore download it now.
-
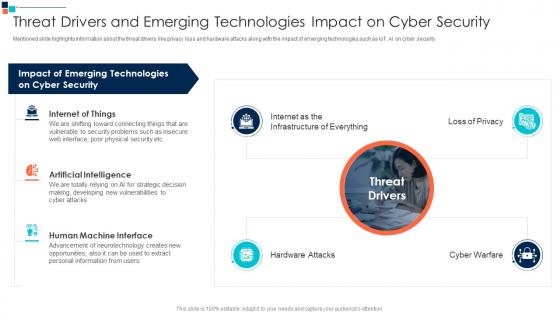 Threat Drivers And Emerging Introducing A Risk Based Approach To Cyber Security
Threat Drivers And Emerging Introducing A Risk Based Approach To Cyber SecurityMentioned slide highlights information about the threat drivers like privacy loss and hardware attacks along with the impact of emerging technologies such as IoT, AI on cyber security.Increase audience engagement and knowledge by dispensing information using Threat Drivers And Emerging Introducing A Risk Based Approach To Cyber Security This template helps you present information on one stage. You can also present information on Internet Of Things, Artificial Intelligence, Human Machine Interface using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
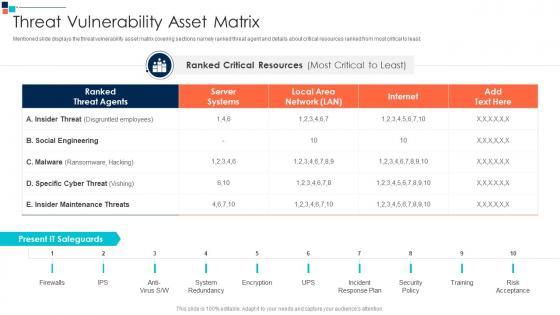 Threat Vulnerability Asset Matrix Introducing A Risk Based Approach To Cyber Security
Threat Vulnerability Asset Matrix Introducing A Risk Based Approach To Cyber SecurityMentioned slide displays the threat vulnerability asset matrix covering sections namely ranked threat agent and details about critical resources ranked from most critical to least.Present the topic in a bit more detail with this Threat Vulnerability Asset Matrix Introducing A Risk Based Approach To Cyber Security Use it as a tool for discussion and navigation on System Redundancy, Incident Response Plan, Security Policy This template is free to edit as deemed fit for your organization. Therefore download it now.
-
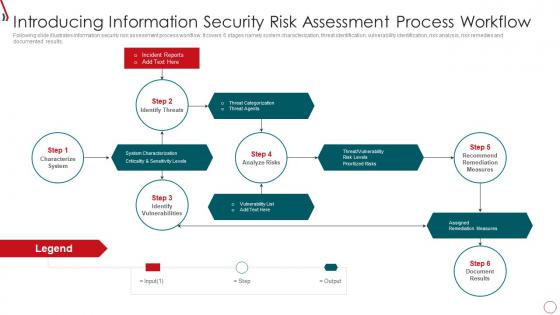 Risk Management Framework For Information Security Introducing Information Security Risk
Risk Management Framework For Information Security Introducing Information Security RiskFollowing slide illustrates information security risk assessment process workflow. It covers 6 stages namely system characterization, threat identification, vulnerability identification, risk analysis, risk remedies and documented results. Increase audience engagement and knowledge by dispensing information using Risk Management Framework For Information Security Introducing Information Security Risk. This template helps you present information on six stages. You can also present information on Identify Threats, Incident Reports, Identify Vulnerabilities, Characterize System, Recommend Remediation Measures using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
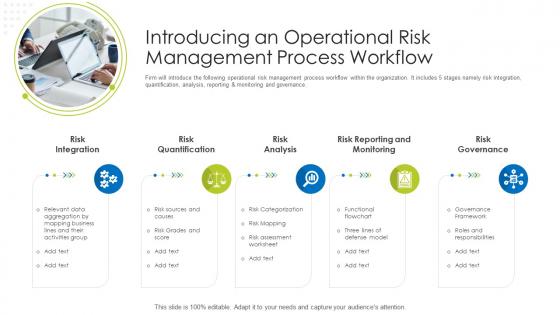 How Mitigate Operational Risk Banks Introducing An Operational Risk
How Mitigate Operational Risk Banks Introducing An Operational RiskFirm will introduce the following operational risk management process workflow within the organization. It includes 5 stages namely risk integration, quantification, analysis, reporting and monitoring and governance. Introducing How Mitigate Operational Risk Banks Introducing An Operational Risk to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Risk Integration, Risk Quantification, Risk Analysis, Risk Reporting And Monitoring, Risk Governance, using this template. Grab it now to reap its full benefits.
-
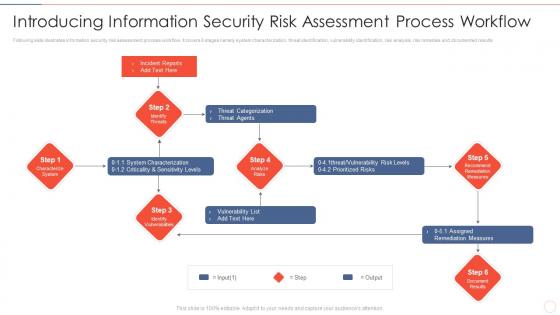 Effective information security introducing information security risk assessment process
Effective information security introducing information security risk assessment processFollowing slide illustrates information security risk assessment process workflow. It covers 6 stages namely system characterization, threat identification, vulnerability identification, risk analysis, risk remedies and documented results Increase audience engagement and knowledge by dispensing information using Effective Information Security Introducing Information Security Risk Assessment Process. This template helps you present information on six stages. You can also present information on Incident Reports, Threat Categorization, Vulnerability List, Assigned Remediation Measures using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
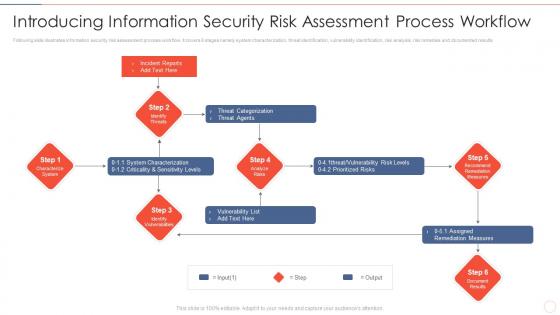 Introducing process workflow effective information security risk management process
Introducing process workflow effective information security risk management processFollowing slide illustrates information security risk assessment process workflow. It covers 6 stages namely system characterization, threat identification, vulnerability identification, risk analysis, risk remedies and documented results Deliver an outstanding presentation on the topic using this Introducing Process Workflow Effective Information Security Risk Management Process. Dispense information and present a thorough explanation of Threat Categorization, System Characterization, Assigned Remediation Measures using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
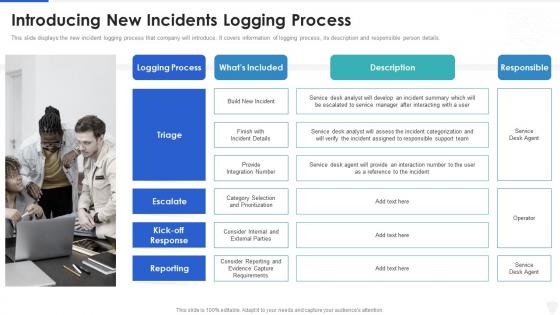 Cybersecurity and digital business risk management introducing new incidents logging process
Cybersecurity and digital business risk management introducing new incidents logging processThis slide displays the new incident logging process that company will introduce. It covers information of logging process, its description and responsible person details. Introducing Cybersecurity And Digital Business Risk Management Introducing New Incidents Logging Process to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Process, Requirements, Service, using this template. Grab it now to reap its full benefits.
-
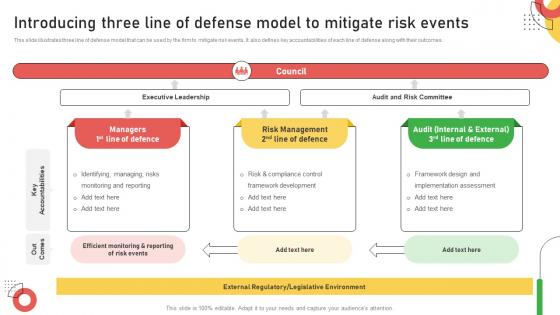 Introducing Three Line Of Defense Model To Mitigate Risk Improving Customer Service And Ensuring
Introducing Three Line Of Defense Model To Mitigate Risk Improving Customer Service And EnsuringThis slide illustrates three line of defense model that can be used by the firm to mitigate risk events. It also defines key accountabilities of each line of defense along with their outcomes. Deliver an outstanding presentation on the topic using this Introducing Three Line Of Defense Model To Mitigate Risk Improving Customer Service And Ensuring. Dispense information and present a thorough explanation of Executive Leadership, Risk Committee, Framework Development using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
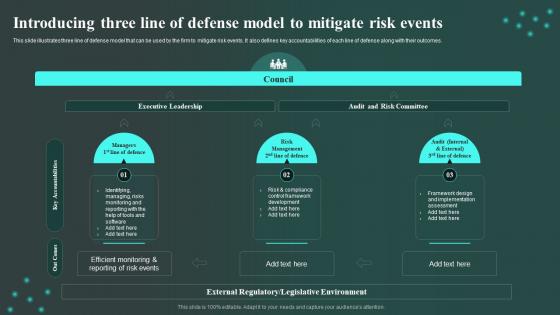 Introducing Three Line Of Defense Model To Mitigate Risk Events Workplace Innovation And Technological
Introducing Three Line Of Defense Model To Mitigate Risk Events Workplace Innovation And TechnologicalThis slide illustrates three line of defense model that can be used by the firm to mitigate risk events. It also defines key accountabilities of each line of defense along with their outcomes. Deliver an outstanding presentation on the topic using this Introducing Three Line Of Defense Model To Mitigate Risk Events Workplace Innovation And Technological. Dispense information and present a thorough explanation of Executive Leadership, Audit, Risk Committee using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Enhancing Business Performance Through Introducing Three Line Of Defense Model To Mitigate Risk
Enhancing Business Performance Through Introducing Three Line Of Defense Model To Mitigate RiskThis slide illustrates three line of defense model that can be used by the firm to mitigate risk events. It also defines key accountabilities of each line of defense along with their outcomes. Increase audience engagement and knowledge by dispensing information using Enhancing Business Performance Through Introducing Three Line Of Defense Model To Mitigate Risk. This template helps you present information on three stages. You can also present information on Risk Management, Mitigate Risk Events, Monitoring And Reporting using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
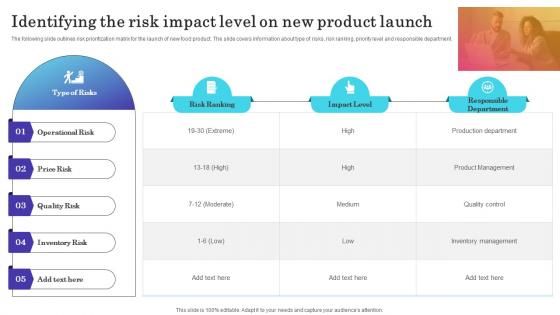 Identifying The Risk Impact Level On New Launch Introducing New Product In Food And Beverage
Identifying The Risk Impact Level On New Launch Introducing New Product In Food And BeverageThe following slide outlines risk prioritization matrix for the launch of new food product. The slide covers information about type of risks, risk ranking, priority level and responsible department. Introducing Identifying The Risk Impact Level On New Launch Introducing New Product In Food And Beverage to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Operational Risk, Price Risk, Quality Risk, using this template. Grab it now to reap its full benefits.
-
 Introducing Compliance And Ethical Practices For Mitigating Risks And Building Trust Strategy SS
Introducing Compliance And Ethical Practices For Mitigating Risks And Building Trust Strategy SSThis slide presents an overview of ethical behavior and its impact on organization. It also discusses the importance of ethical behavior in business including, avoid reputational harm, enhance external relations, improve workforce productivity, improve workforce productivity and promote personal morality. Deliver an outstanding presentation on the topic using this Introducing Compliance And Ethical Practices For Mitigating Risks And Building Trust Strategy SS. Dispense information and present a thorough explanation of Businesses, Compliance, Introducing using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
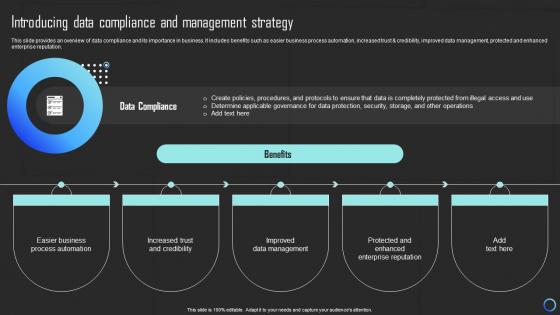 Introducing Data Compliance And Management Mitigating Risks And Building Trust Strategy SS
Introducing Data Compliance And Management Mitigating Risks And Building Trust Strategy SSThis slide provides an overview of data compliance and its importance in business. It includes benefits such as easier business process automation, increased trust and credibility, improved data management, protected and enhanced enterprise reputation. Introducing Introducing Data Compliance And Management Mitigating Risks And Building Trust Strategy SS to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Strategy, Management, Data, using this template. Grab it now to reap its full benefits.
-
 Introducing Risk Management Strategy To Minimize Mitigating Risks And Building Trust Strategy SS
Introducing Risk Management Strategy To Minimize Mitigating Risks And Building Trust Strategy SSThis slide presents an overview of risk management and associated benefits for the company. It includes benefits such as protection of assets, increased operational efficiency, improve decision making, enhanced reputation and compliance with regulations. Increase audience engagement and knowledge by dispensing information using Introducing Risk Management Strategy To Minimize Mitigating Risks And Building Trust Strategy SS. This template helps you present information on six stages. You can also present information on Management, Strategy, Potential Losses using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Risk introducing technologies ppt powerpoint presentation file design templates cpb
Risk introducing technologies ppt powerpoint presentation file design templates cpbPresenting Risk Introducing Technologies Ppt Powerpoint Presentation File Design Templates Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Risk Introducing Technologies. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
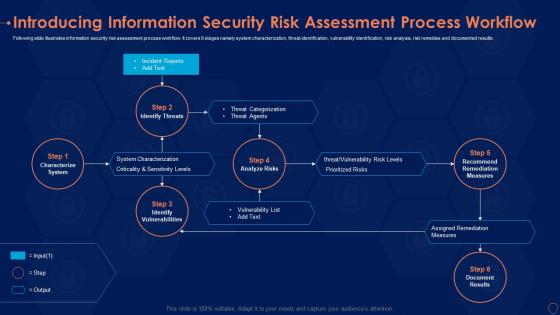 Introducing information security risk assessment process workflow ppt portfolio
Introducing information security risk assessment process workflow ppt portfolioFollowing slide illustrates information security risk assessment process workflow. It covers 6 stages namely system characterization, threat identification, vulnerability identification, risk analysis, risk remedies and documented results. Deliver an outstanding presentation on the topic using this Introducing Information Security Risk Assessment Process Workflow Ppt Portfolio. Dispense information and present a thorough explanation of Categorization, Prioritized Risks, System Characterization using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
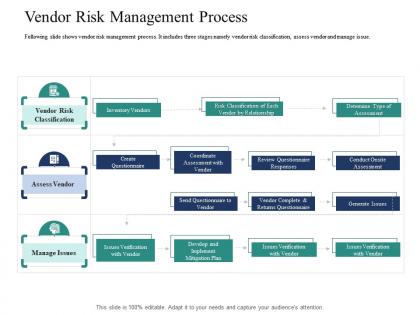 Vendor risk management process introducing effective vpm process in the organization ppt elements
Vendor risk management process introducing effective vpm process in the organization ppt elementsFollowing slide shows vendor risk management process. It includes three stages namely vendor risk classification, assess vendor and manage issue.Introducing Vendor Risk Management Process Introducing Effective VPM Process In The Organization Ppt Elements to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Vendor Risk Classification, Create Questionnaire, Inventory Vendors, using this template. Grab it now to reap its full benefits.
-
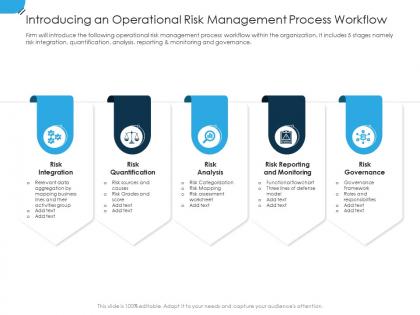 Introducing an operational risk establishing operational risk framework organization
Introducing an operational risk establishing operational risk framework organizationFirm will introduce the following operational risk management process workflow within the organization. It includes 5 stages namely risk integration, quantification, analysis, reporting and monitoring and governance. Introducing Introducing An Operational Risk Establishing Operational Risk Framework Organization to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Risk Integration, Risk Quantification, Risk Analysis, Risk Reporting And Monitoring, Risk Governance, using this template. Grab it now to reap its full benefits.


