Powerpoint Templates and Google slides for Security Checklist
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
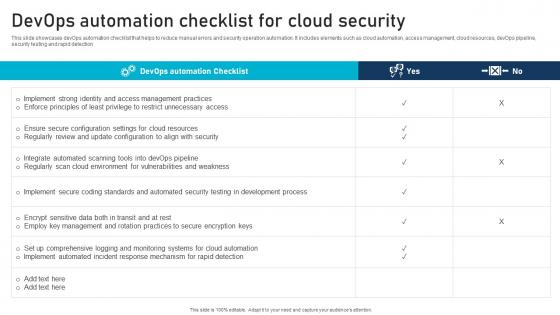
 Adopt Security Auditing Checklist To Verify Processes Guide For Blockchain BCT SS V
Adopt Security Auditing Checklist To Verify Processes Guide For Blockchain BCT SS VThe following slide depicts blockchain cybersecurity auditing checklist to minimize probability of frauds. It includes elements such as network, node, smart contract, security, consensus mechanism, data encryption, access management, etc. Present the topic in a bit more detail with this Adopt Security Auditing Checklist To Verify Processes Guide For Blockchain BCT SS V Use it as a tool for discussion and navigation on Network Security, Node Security, Consensus Mechanism This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Saas Compliance Checklist For Organizational Security
Saas Compliance Checklist For Organizational SecurityThis slide presents organizational security checklist to manage governance and compliance requirements for SaaS businesses. It aims to provide assistance during the SaaS compliance journey for securing cloud-based applications. It covers elements such as determining compliance requirements, evaluating risks, assessing compliance level, formulating strategy, implementing controls, etc. Introducing our Saas Compliance Checklist For Organizational Security set of slides. The topics discussed in these slides are Data Handling Processes, Security Risks, Resource Requirements. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
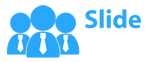
 Checklist To Implement Data Breach Security Response Plan
Checklist To Implement Data Breach Security Response PlanThis slide depicts the checklist to execute response plans during data security breaches. The purpose of this checklist is to help the business ensure all suitable actions are implemented in order to prevent data leaks. It includes elements such as activity status, person responsible, etc. Presenting our well structured Checklist To Implement Data Breach Security Response Plan. The topics discussed in this slide are Isolate Affected Systems, Notify Appropriate Stakeholders, Identify The Nature. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Social Engineering Attacks Prevention Checklist To Secure Organizations From Social Engineering
Social Engineering Attacks Prevention Checklist To Secure Organizations From Social EngineeringThis slide outlines the steps to be taken to protect the organization and its employees from social engineering attacks. The key approaches include provide staff training, update software, enable MFA and spam filters, implement real-time monitoring and develop an incident plan. Present the topic in a bit more detail with this Social Engineering Attacks Prevention Checklist To Secure Organizations From Social Engineering. Use it as a tool for discussion and navigation on Provide Staff Training, Multi Factor Authentication, Develop An Incident Response Plan. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
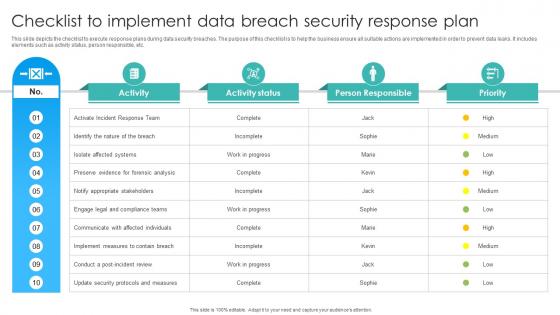
 Devops Automation Checklist For Cloud Security
Devops Automation Checklist For Cloud SecurityThis slide showcases devOps automation checklist that helps to reduce manual errors and security operation automation. It includes elements such as cloud automation, access management, cloud resources, devOps pipeline, security testing and rapid detection. Introducing our Devops Automation Checklist For Cloud Securityset of slides. The topics discussed in these slides are Management Practices, Cloud Resources, Cloud Environment. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Cyber Threats In Blockchain Adopt Security Auditing Checklist To Verify Processes BCT SS V
Cyber Threats In Blockchain Adopt Security Auditing Checklist To Verify Processes BCT SS VThe following slide depicts blockchain cybersecurity auditing checklist to minimize probability of frauds. It includes elements such as network, node, smart contract, security, consensus mechanism, data encryption, access management, etc. Deliver an outstanding presentation on the topic using this Cyber Threats In Blockchain Adopt Security Auditing Checklist To Verify Processes BCT SS V Dispense information and present a thorough explanation of Consensus Mechanism, Smart Contract Security, Data Encryption using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
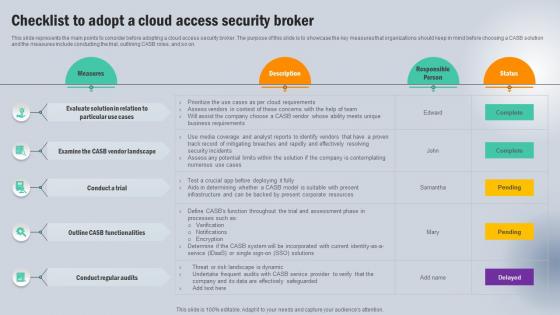 Checklist To Adopt A Cloud Access Security Broker Next Generation CASB
Checklist To Adopt A Cloud Access Security Broker Next Generation CASBThis slide represents the main points to consider before adopting a cloud access security broker. The purpose of this slide is to showcase the key measures that organizations should keep in mind before choosing a CASB solution and the measures include conducting the trial, outlining CASB roles, and so on. Deliver an outstanding presentation on the topic using this Checklist To Adopt A Cloud Access Security Broker Next Generation CASB Dispense information and present a thorough explanation of Vendor Landscape, Conduct A Trial, Functionalities using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
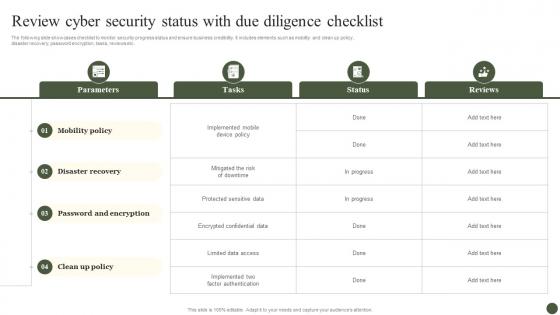 Review Cyber Security Status With Due Diligence Checklist Implementing Cyber Risk Management Process
Review Cyber Security Status With Due Diligence Checklist Implementing Cyber Risk Management ProcessThe following slide showcases checklist to monitor security progress status and ensure business credibility. It includes elements such as mobility and clean up policy, disaster recovery, password encryption, tasks, reviews etc. Present the topic in a bit more detail with this Review Cyber Security Status With Due Diligence Checklist Implementing Cyber Risk Management Process. Use it as a tool for discussion and navigation on Parameters, Tasks, Status, Reviews. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Ransomware In Digital Age Ransomware Prevention Checklist For Security Teams
Ransomware In Digital Age Ransomware Prevention Checklist For Security TeamsThis slide represents the current status of ransomware prevention measures in an organization. The purpose of this slide is to showcase the status of different security measures such as data backups, antivirus software upgradation, network segmentation, etc. Present the topic in a bit more detail with this Ransomware In Digital Age Ransomware Prevention Checklist For Security Teams. Use it as a tool for discussion and navigation on Email Protection, Vulnerability Scanning And Patching, Backup Testing And Data Restoration. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
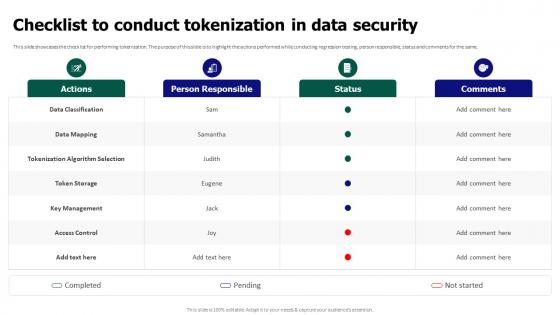 Tokenization For Improved Data Security Checklist To Conduct Tokenization In Data Security
Tokenization For Improved Data Security Checklist To Conduct Tokenization In Data SecurityThis slide showcases the checklist for performing tokenization. The purpose of this slide is to highlight the actions performed while conducting regression testing, person responsible, status and comments for the same. Present the topic in a bit more detail with this Tokenization For Improved Data Security Checklist To Conduct Tokenization In Data Security. Use it as a tool for discussion and navigation on Data Classification, Tokenization Algorithm Selection, Key Management, Access Control. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
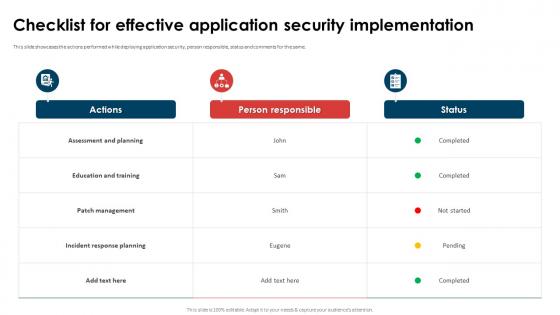 Application Security Implementation Plan Checklist For Effective Application Security Implementation
Application Security Implementation Plan Checklist For Effective Application Security ImplementationThis slide showcases the actions performed while deploying application security, person responsible, status and comments for the same. Present the topic in a bit more detail with this Application Security Implementation Plan Checklist For Effective Application Security Implementation. Use it as a tool for discussion and navigation on Assessment And Planning, Education And Training, Incident Response Planning. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
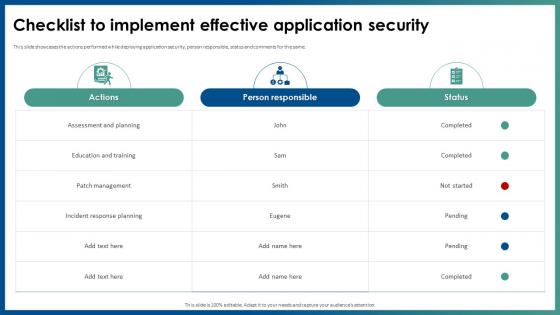 Checklist To Implement Effective Application Security
Checklist To Implement Effective Application SecurityThis slide showcases the actions performed while deploying application security, person responsible, status and comments for the same. Deliver an outstanding presentation on the topic using this Checklist To Implement Effective Application Security. Dispense information and present a thorough explanation of Assessment And Planning, Education And Training, Patch Management using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Web Based Software Security Implementation Checklist For Managers
Web Based Software Security Implementation Checklist For ManagersThis slide showcases checklist for SaaS security implementation and assessment. This includes activities such as running security tests, trAIning staff for safety practices, and planning backups for new threats, cloud sources, and security alert systems. Introducing our Web Based Software Security Implementation Checklist For Managers set of slides. The topics discussed in these slides are Run Security Test, Monitoring And Logging, Checklist For Managers. This is an immediately avAIlable PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
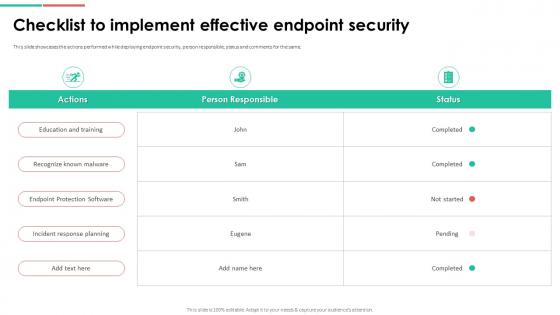 Endpoint Security Checklist To Implement Effective Endpoint Security
Endpoint Security Checklist To Implement Effective Endpoint SecurityThis slide showcases the actions performed while deploying endpoint security, person responsible, status and comments for the same. Deliver an outstanding presentation on the topic using this Endpoint Security Checklist To Implement Effective Endpoint Security. Dispense information and present a thorough explanation of Education And Training, Recognize Known Malware, Endpoint Protection Software using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
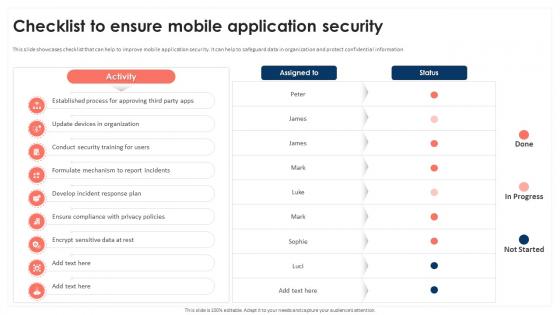 Checklist To Ensure Mobile Application Security Mobile Device Security Cybersecurity SS
Checklist To Ensure Mobile Application Security Mobile Device Security Cybersecurity SSThis slide showcases checklist that can help to improve mobile application security. It can help to safeguard data in organization and protect confidential information. Present the topic in a bit more detail with this Checklist To Ensure Mobile Application Security Mobile Device Security Cybersecurity SS Use it as a tool for discussion and navigation on Update Devices In Organization, Conduct Security Training For Users This template is free to edit as deemed fit for your organization. Therefore download it now.
-
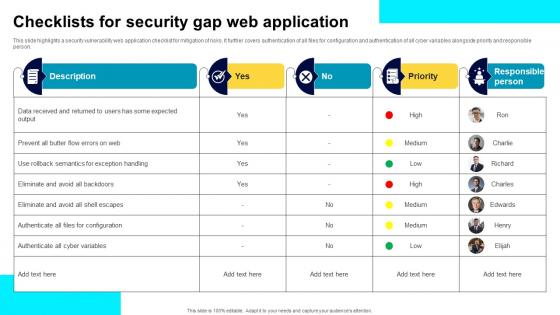 Checklists For Security Gap Web Application
Checklists For Security Gap Web ApplicationThis slide highlights a security vulnerability web application checklist for mitigation of risks. It further covers authentication of all files for configuration and authentication of all cyber variables alongside priority and responsible person. Introducing our Checklists For Security Gap Web Application set of slides. The topics discussed in these slides are Data Received, Semantics For Exception Handling, Cyber Variables. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Checklist To Enhance Cyber Security Of SCADA Networks
Checklist To Enhance Cyber Security Of SCADA NetworksThis slide represents checklist that assist IT companies to enhance their SCADA networks cyber security for improving data protection. It includes various elements such as recognizing connections, disconnecting irrelevant networks, etc. Introducing our Checklist To Enhance Cyber Security Of SCADA Networks set of slides. The topics discussed in these slides are Essential Connections, Inadvertent Disclosure, SCADA Network This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Analyzing Mobile Application Security Checklist
Analyzing Mobile Application Security ChecklistThis slide covers checklist to analyze mobile security for long-term scenarios and includes tasks, applicable and not applicable. Presenting our set of slides with name Analyzing Mobile Application Security Checklist. This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Tasks, Applicable, Not Applicable.
-
 Checklist To Establish Triage Capability In Cyber Security
Checklist To Establish Triage Capability In Cyber SecurityThis slide represents checklist to establish triage capability in cyber security which assists to analyse threat alerts and effectively response cyber threats. It includes checklist to establish triage capability in cyber security which includes steps such as type of events, skill levels, etc Introducing our Checklist To Establish Triage Capability In Cyber Security set of slides. The topics discussed in these slides are Types Of Events, Skills Levels, Channels Of Support. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Digital Facility Security Assessment Checklist
Digital Facility Security Assessment ChecklistThe purpose of this slide is to systematically evaluate and enhance security measures of digital facility by identifying potential vulnerabilities and implementing necessary safeguards. Introducing our Digital Facility Security Assessment Checklist set of slides. The topics discussed in these slides are Access Control Systems, Check Fencing Condition, Monitor Entry Point Systems, Intrusion Detection. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
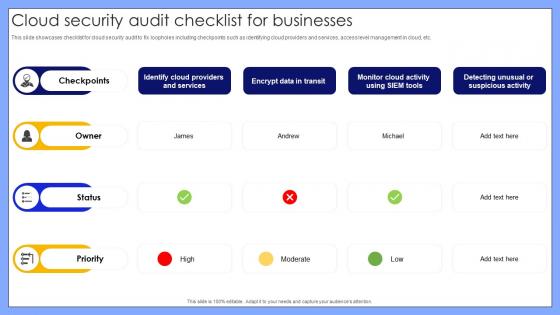 Cloud Security Audit Checklist For Businesses
Cloud Security Audit Checklist For BusinessesThis slide showcases checklist for cloud security audit to fix loopholes including checkpoints such as identifying cloud providers and services, access level management in cloud, etc. Introducing our Cloud Security Audit Checklist For Businesses set of slides. The topics discussed in these slides are Identify Cloud Providers And Services, Encrypt Data In Transit, Detecting Unusual Or Suspicious Activity. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
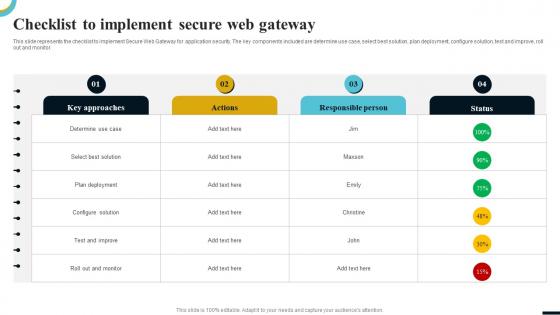 Internet Gateway Security IT Checklist To Implement Secure Web Gateway
Internet Gateway Security IT Checklist To Implement Secure Web GatewayThis slide represents the checklist to implement Secure Web Gateway for application security. The key components included are determine use case, select best solution, plan deployment, configure solution, test and improve, roll out and monitor. Present the topic in a bit more detail with this Internet Gateway Security IT Checklist To Implement Secure Web Gateway. Use it as a tool for discussion and navigation on Determine Use Case, Select Best Solution, Plan Deployment, Configure Solution, Test And Improve, Roll Out And Monitor. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Implementation Checklist Plan For Security Incident
Implementation Checklist Plan For Security IncidentPresenting our set of slides with Implementation Checklist Plan For Security Incident. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Implementation Checklist Plan, Security Incident.
-
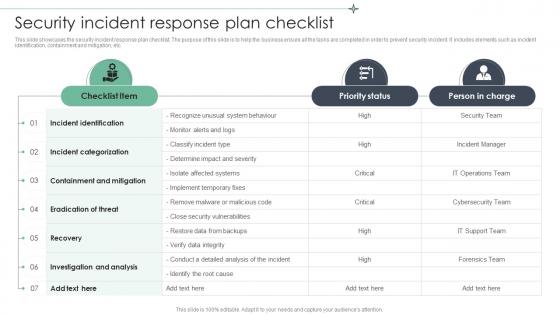 Security Incident Response Plan Checklist
Security Incident Response Plan ChecklistThis slide showcases the security incident response plan checklist. The purpose of this slide is to help the business ensure all the tasks are completed in order to prevent security incident. It includes elements such as incident identification, containment and mitigation, etc. Presenting our well structured Security Incident Response Plan Checklist. The topics discussed in this slide are Incident Identification, Incident Categorization, Containment And Mitigation. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Security Incident Response Plan Checklist Icon
Security Incident Response Plan Checklist IconIntroducing our premium set of slides with Security Incident Response Plan Checklist Icon. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Security Incident, Response Plan Checklist. So download instantly and tailor it with your information.
-
 Project Data Security And Privacy Checklist Matrix
Project Data Security And Privacy Checklist MatrixThe purpose of this slide is to introduce project data security and privacy checklist matrix, which systematically ensures and enhances data and privacy protection measures throughout the project lifecycle. Introducing our Project Data Security And Privacy Checklist Matrix set of slides. The topics discussed in these slides are Data Encryption, Access Controls, Security Audits, User Authentication. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 ATP Cyber Security Features Checklist
ATP Cyber Security Features ChecklistThis slide depicts the essential features checklist for cyber security ATP. Its aim is to include the essential features during advanced threat protection of a system. This slide includes file analytics, attacks surface management, combined prevention and rich threat intelligence, etc. Presenting our set of slides with name ATP Cyber Security Features Checklist. This exhibits information on Four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on File Analytics, Attack Surface Management, Combined Prevention, Rich Threat Intelligence.
-
 Checklist To Adopt A Cloud Access Security Broker CASB Cloud Security
Checklist To Adopt A Cloud Access Security Broker CASB Cloud SecurityThis slide represents the main points to consider before adopting a cloud access security broker. The purpose of this slide is to showcase the key measures that organizations should keep in mind before choosing a CASB solution and the measures include conducting the trial, outlining CASB roles, and so on. Deliver an outstanding presentation on the topic using this Checklist To Adopt A Cloud Access Security Broker CASB Cloud Security. Dispense information and present a thorough explanation of Cloud Access Security Broker, Contemplating Numerous, Threat Or Risk Landscape Is Dynamic using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Checklist For Holistic Data Security And Privacy In Big Data Technology
Checklist For Holistic Data Security And Privacy In Big Data TechnologyThis slide represents checklist for data security and privacy in big data technology which assists to prevent unauthorized access and provides safeguard against cyber threat. It includes key steps such as secure and monitor, find and classify, etc. Introducing our Checklist For Holistic Data Security And Privacy In Big Data Technology set of slides. The topics discussed in these slides are Find And Classify, Secure And Monitor, Harden, Protect And Remain Vigilant. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
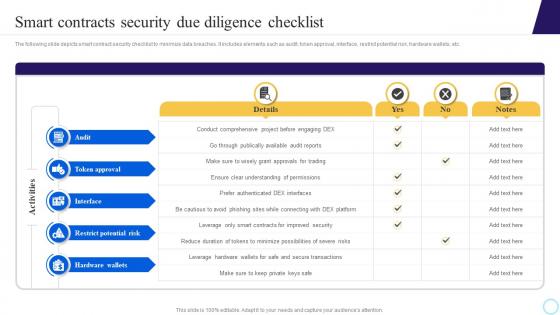 Smart Contracts Security Due Diligence Checklist Step By Step Process To Develop Blockchain BCT SS
Smart Contracts Security Due Diligence Checklist Step By Step Process To Develop Blockchain BCT SSThe following slide depicts smart contract security checklist to minimize data breaches. It includes elements such as audit, token approval, interface, restrict potential risk, hardware wallets, etc. Deliver an outstanding presentation on the topic using this Smart Contracts Security Due Diligence Checklist Step By Step Process To Develop Blockchain BCT SS. Dispense information and present a thorough explanation of Token Approval, Restrict Potential Risk, Hardware Wallets using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
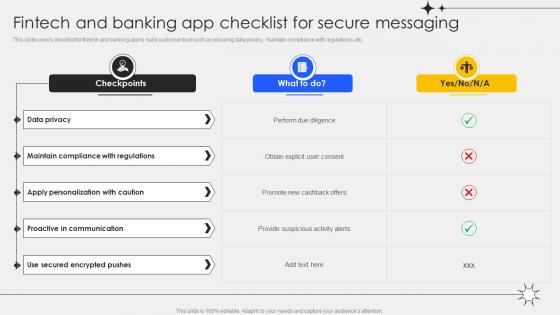 Fintech And Banking App Checklist For Secure Messaging
Fintech And Banking App Checklist For Secure MessagingThis slide covers checklist for fintech and banking app to build customer trust such as ensuring data privacy, maintain compliance with regulations, etc. Introducing our Fintech And Banking App Checklist For Secure Messaging set of slides. The topics discussed in these slides are Data Privacy, Proactive In Communication, Secured Encrypted Pushes. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Checklist To Conduct Effective Web Security
Checklist To Conduct Effective Web SecurityThis slide showcases actions performed while conducting web security in an organization which include actions, person responsible, status, etc. Presenting our well structured Checklist To Conduct Effective Web Security. The topics discussed in this slide are Authentication And Authorization, Session Management, Connectivity. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Checklist For Enhancing Organization Server Security
Checklist For Enhancing Organization Server SecurityFollowing slide showcases server security management checklist, also including description such as installation of intranet, restrict files and critical apps for admins, installation of intranet, block direct access to sensitive data, etc. Presenting our well structured Checklist For Enhancing Organization Server Security. The topics discussed in this slide are Authorized Personnel, Installation Of Intranet, Sensitive Server Data. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
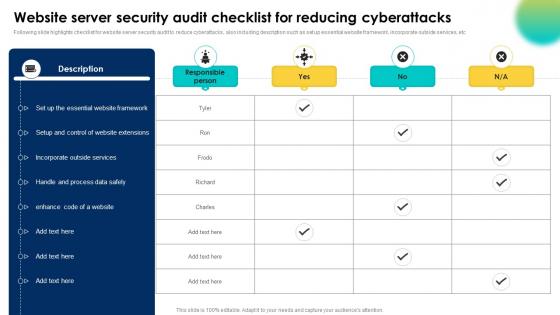 Website Server Security Audit Checklist For Reducing Cyberattacks
Website Server Security Audit Checklist For Reducing CyberattacksFollowing slide highlights checklist for website server security audit to reduce cyberattacks, also including description such as set up essential website framework, incorporate outside services, etc. Introducing our Website Server Security Audit Checklist For Reducing Cyberattacks set of slides. The topics discussed in these slides are Data Safely, Outside Services, Website Extensions. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
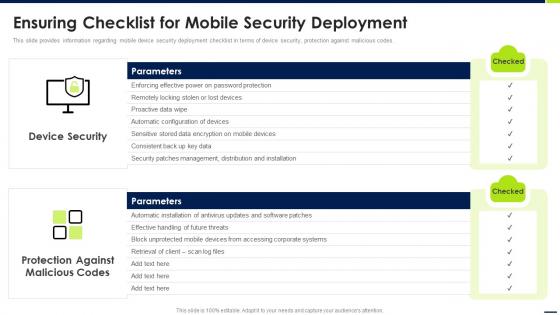
 Managing Mobile Devices For Optimizing Ensuring Checklist For Mobile Security Deployment
Managing Mobile Devices For Optimizing Ensuring Checklist For Mobile Security DeploymentThis slide provides information regarding mobile device security deployment checklist in terms of device security, protection against malicious codes. Present the topic in a bit more detail with this Managing Mobile Devices For Optimizing Ensuring Checklist For Mobile Security Deployment. Use it as a tool for discussion and navigation on Parameters, Protection, Malicious Codes, Mobile Security Deployment. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Ensuring Checklist For Mobile Security Deployment Management And Monitoring
Ensuring Checklist For Mobile Security Deployment Management And MonitoringThis slide provides information regarding mobile device security deployment checklist in terms of device security, protection against malicious codes. Introducing Ensuring Checklist For Mobile Security Deployment Management And Monitoring to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Ensuring Checklist, Mobile Security Deployment, using this template. Grab it now to reap its full benefits.
-
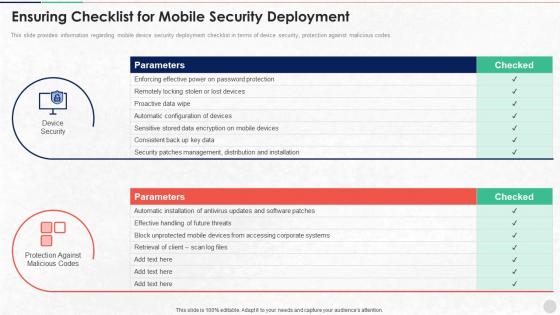 Ensuring Checklist For Mobile Security Deployment Unified Endpoint Security
Ensuring Checklist For Mobile Security Deployment Unified Endpoint SecurityThis slide provides information regarding mobile device security deployment checklist in terms of device security, protection against malicious codes. Introducing Ensuring Checklist For Mobile Security Deployment Unified Endpoint Security to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Password Protection, Automatic Configuration, Patches Management, using this template. Grab it now to reap its full benefits.
-
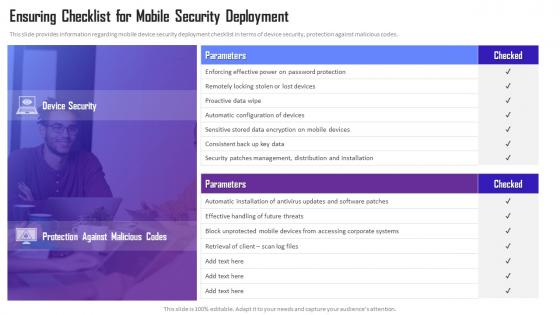 Managing Mobile Device Solutions For Workforce Ensuring Checklist For Mobile Security Deployment
Managing Mobile Device Solutions For Workforce Ensuring Checklist For Mobile Security DeploymentThis slide provides information regarding mobile device security deployment checklist in terms of device security, protection against malicious codes. Present the topic in a bit more detail with this Managing Mobile Device Solutions For Workforce Ensuring Checklist For Mobile Security Deployment. Use it as a tool for discussion and navigation on Device Security, Protection Against, Malicious Codes. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Ensuring Checklist For Mobile Security Deployment Contd Android Device Security Management
Ensuring Checklist For Mobile Security Deployment Contd Android Device Security ManagementThis slide provides information regarding mobile device security deployment checklist in terms of ensuring secure connections to corporate networks, prevent network based intrusion, centralized policies control and corporate directories. Introducing Ensuring Checklist For Mobile Security Deployment Contd Android Device Security Management to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Parameters, Ensuring Checklist, Mobile Security Deployment, using this template. Grab it now to reap its full benefits.
-
 Ensuring Checklist For Mobile Security Deployment Enterprise Mobile Security For On Device
Ensuring Checklist For Mobile Security Deployment Enterprise Mobile Security For On DeviceThis slide provides information regarding mobile device security deployment checklist in terms of device security, protection against malicious codes. Deliver an outstanding presentation on the topic using this Ensuring Checklist For Mobile Security Deployment Enterprise Mobile Security For On Device. Dispense information and present a thorough explanation of Enforcing Effective, Automatic Configuration, Effective Handling using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Checklist For Effectively Managing Asset Security Risk Based Methodology To Cyber
Checklist For Effectively Managing Asset Security Risk Based Methodology To CyberFollowing slide displays system management checklist that company will use for effectively managing asset security. It also includes system management activities and frequency of performing them.Increase audience engagement and knowledge by dispensing information using Checklist For Effectively Managing Asset Security Risk Based Methodology To Cyber This template helps you present information on one stage. You can also present information on System Monitoring, Data Backup, Security Patches using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Checklist For Effectively Managing Asset Security Introducing A Risk Based Approach
Checklist For Effectively Managing Asset Security Introducing A Risk Based ApproachFollowing slide displays system management checklist that company will use for effectively managing asset security. It also includes system management activities and frequency of performing them.Introducing Checklist For Effectively Managing Asset Security Introducing A Risk Based Approach to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispence information on System Monitoring, Virus Scanning, System Monitoring using this template. Grab it now to reap its full benefits.
-
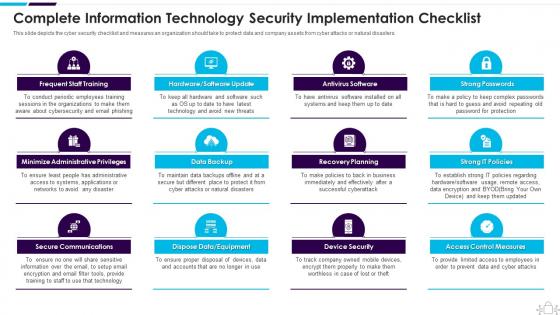 Information Technology Security Complete Information Security Implementation Checklist
Information Technology Security Complete Information Security Implementation ChecklistThis slide depicts the cyber security checklist and measures an organization should take to protect data and company assets from cyber attacks or natural disasters. Introducing Information Technology Security Complete Information Security Implementation Checklist to increase your presentation threshold. Encompassed with twelve stages, this template is a great option to educate and entice your audience. Dispence information on Frequent Staff Training, Administrative Privileges, Data Backup, using this template. Grab it now to reap its full benefits.
-
 Security Policy Checklist Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Security Policy Checklist Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Security policy checklist colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Security Policy Checklist Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Security Policy Checklist Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Security policy checklist monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
 Security And Safety Checklist For Hotel Industry
Security And Safety Checklist For Hotel IndustryThis slide covers checklist for ensuring safety of visitors at hotels. The checklist includes security screening of bags, professional security team and screening of people at entrance. Introducing our Security And Safety Checklist For Hotel Industry set of slides. The topics discussed in these slides are Security And Safety Checklist For Hotel Industry. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
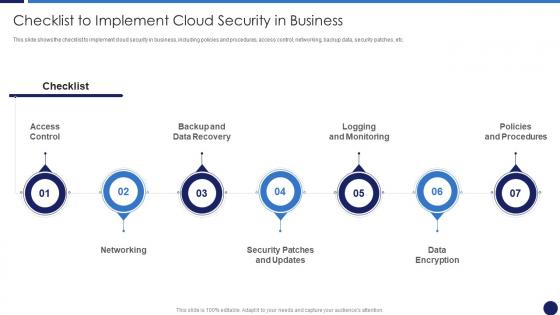 Checklist To Implement Cloud Security In Business Cloud Data Protection
Checklist To Implement Cloud Security In Business Cloud Data ProtectionThis slide shows the checklist to implement cloud security in business, including policies and procedures, access control, networking, backup data, security patches, etc. Introducing Checklist To Implement Cloud Security In Business Cloud Data Protection to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispense information on Logging And Monitoring, Networking, Data Encryption, using this template. Grab it now to reap its full benefits.
-
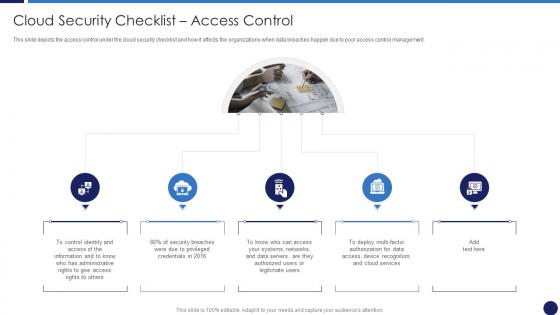 Cloud Security Checklist Access Control Cloud Data Protection
Cloud Security Checklist Access Control Cloud Data ProtectionThis slide depicts the access control under the cloud security checklist and how it affects the organizations when data breaches happen due to poor access control management. Introducing Cloud Security Checklist Access Control Cloud Data Protection to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispense information on Cloud Services, Information, Data Servers, using this template. Grab it now to reap its full benefits.
-
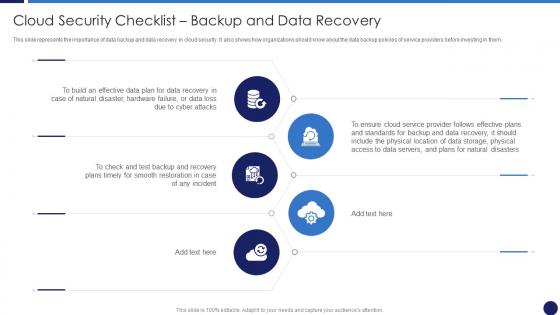 Cloud Security Checklist Backup And Data Recovery Cloud Data Protection
Cloud Security Checklist Backup And Data Recovery Cloud Data ProtectionThis slide represents the importance of data backup and data recovery in cloud security. It also shows how organizations should know about the data backup policies of service providers before investing in them. Increase audience engagement and knowledge by dispensing information using Cloud Security Checklist Backup And Data Recovery Cloud Data Protection. This template helps you present information on five stages. You can also present information on Data Servers, Location, Effective Data Plan using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
 Cloud Security Checklist Data Encryption Cloud Data Protection
Cloud Security Checklist Data Encryption Cloud Data ProtectionThis slide represents the importance of data encryption in cloud security and what type of data should always be encrypted through private keys. Introducing Cloud Security Checklist Data Encryption Cloud Data Protection to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispense information on Data Servers, Network, Cloud, using this template. Grab it now to reap its full benefits.
-
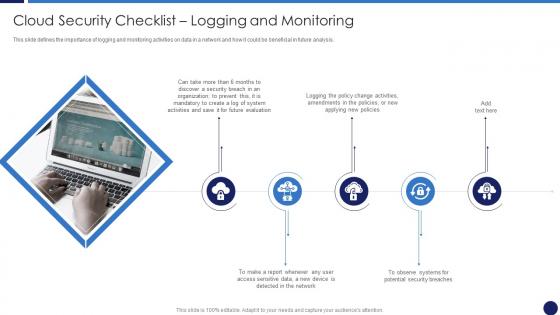 Cloud Security Checklist Logging And Monitoring Cloud Data Protection
Cloud Security Checklist Logging And Monitoring Cloud Data ProtectionThis slide defines the importance of logging and monitoring activities on data in a network and how it could be beneficial in future analysis. Increase audience engagement and knowledge by dispensing information using Cloud Security Checklist Logging And Monitoring Cloud Data Protection. This template helps you present information on five stages. You can also present information on Organization, Network, Security using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
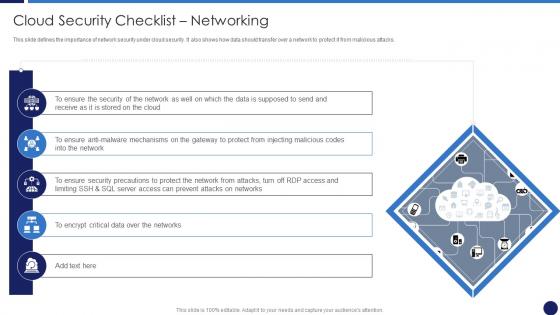 Cloud Security Checklist Networking Cloud Data Protection
Cloud Security Checklist Networking Cloud Data ProtectionThis slide defines the importance of network security under cloud security. It also shows how data should transfer over a network to protect it from malicious attacks. Introducing Cloud Security Checklist Networking Cloud Data Protection to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispense information on Ensure Security, Network, Critical Data, using this template. Grab it now to reap its full benefits.
-
 Cloud Security Checklist Policies And Procedures Cloud Data Protection
Cloud Security Checklist Policies And Procedures Cloud Data ProtectionThis slide depicts the policies and procedures of the cloud security checklist. It also represents how it is essential to create new and update the current policies in an organization. Increase audience engagement and knowledge by dispensing information using Cloud Security Checklist Policies And Procedures Cloud Data Protection. This template helps you present information on five stages. You can also present information on Organization, On Boarding Employees, Cloud Security using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
 Cloud Security Checklist Security Patches And Updates Cloud Data Protection
Cloud Security Checklist Security Patches And Updates Cloud Data ProtectionThis slide depicts the importance of security patches and timely updates of security technologies. It also shows how it is crucial to scan systems, servers, and frameworks regularly. Introducing Cloud Security Checklist Security Patches And Updates Cloud Data Protection to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispense information on Technologies, Organization, Servers, using this template. Grab it now to reap its full benefits.
-
 Effective Mobile Device Management Ensuring Checklist For Mobile Security Deployment
Effective Mobile Device Management Ensuring Checklist For Mobile Security DeploymentThis slide provides information regarding mobile device security deployment checklist in terms of device security, protection against malicious codes. Present the topic in a bit more detail with this Effective Mobile Device Management Ensuring Checklist For Mobile Security Deployment. Use it as a tool for discussion and navigation on Ensuring Checklist For Mobile Security Deployment. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Ai Transformation Playbook Stage Five Security Breach Readiness Checklist
Ai Transformation Playbook Stage Five Security Breach Readiness ChecklistPurpose of this slide is to illustrate readiness checklist that will assist businesses in countering any security breach in advance. Readiness level will be evaluated based on different questions.Present the topic in a bit more detail with this Ai Transformation Playbook Stage Five Security Breach Readiness Checklist Use it as a tool for discussion and navigation on Proper Risk Management, Each Organizational, Governance Procedures This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Information Security Program Cybersecurity Checklist Effectively Managing Asset Security
Information Security Program Cybersecurity Checklist Effectively Managing Asset SecurityFollowing slide displays system management checklist that company will use for effectively managing asset security. It also includes system management activities and frequency of performing them. Present the topic in a bit more detail with this Information Security Program Cybersecurity Checklist Effectively Managing Asset Security. Use it as a tool for discussion and navigation on Checklist For Effectively Managing Asset Security. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
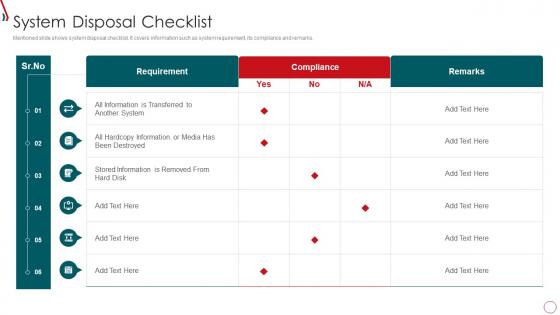 Risk Management Framework For Information Security System Disposal Checklist
Risk Management Framework For Information Security System Disposal ChecklistMentioned slide shows system disposal checklist. It covers information such as system requirement, its compliance and remarks. Deliver an outstanding presentation on the topic using this Risk Management Framework For Information Security System Disposal Checklist. Dispense information and present a thorough explanation of Stored Information, Requirement, All Information using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
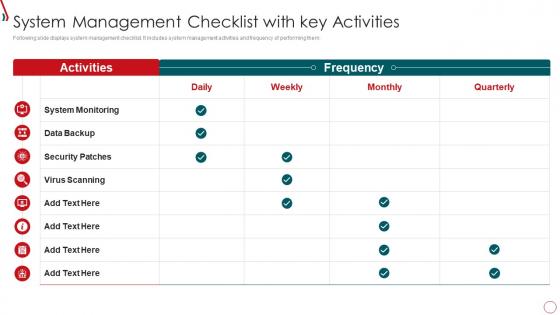 Risk Management Framework For Information Security System Management Checklist
Risk Management Framework For Information Security System Management ChecklistFollowing slide displays system management checklist. It includes system management activities and frequency of performing them. Present the topic in a bit more detail with this Risk Management Framework For Information Security System Management Checklist. Use it as a tool for discussion and navigation on System Monitoring, Data Backup, Security Patches, Virus Scanning. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Checklist For Monthly Site Visit Security Report
Checklist For Monthly Site Visit Security ReportThis slide shows checklist which can be used to prepare monthly site visit security report. It includes points such as security officers wear inform, security officers have license, site have security cameras or not, etc. Introducing our Checklist For Monthly Site Visit Security Report set of slides. The topics discussed in these slides are Security Officers, Working Properly, Full Uniform. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.