Powerpoint Templates and Google slides for Security Responsibility
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Roles and responsibilities to ensure work environment with corporate security management
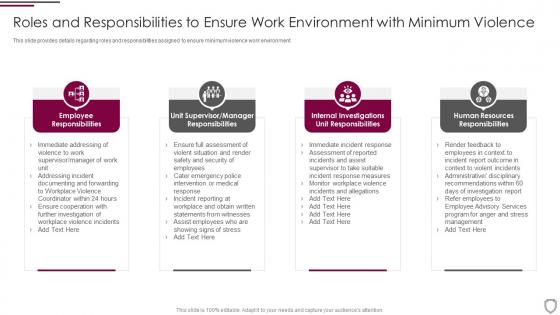
Roles and responsibilities to ensure work environment with corporate security managementThis slide provides details regarding roles and responsibilities assigned to ensure minimum violence work environment. Increase audience engagement and knowledge by dispensing information using Roles And Responsibilities To Ensure Work Environment With Corporate Security Management. This template helps you present information on four stages. You can also present information on Employee Responsibilities, Manager Responsibilities, Unit Responsibilities, Human Resources Responsibilities using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
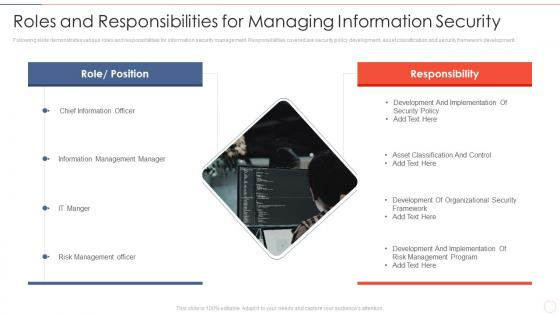 Roles and responsibilities effective information security risk management process
Roles and responsibilities effective information security risk management processFollowing slide demonstrates various roles and responsibilities for information security management. Responsibilities covered are security policy development, asset classification and security framework development.Increase audience engagement and knowledge by dispensing information using Roles And Responsibilities Effective Information Security Risk Management Process. This template helps you present information on one stage. You can also present information on Information Management Manager, Risk Management Officer, Development And Implementation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
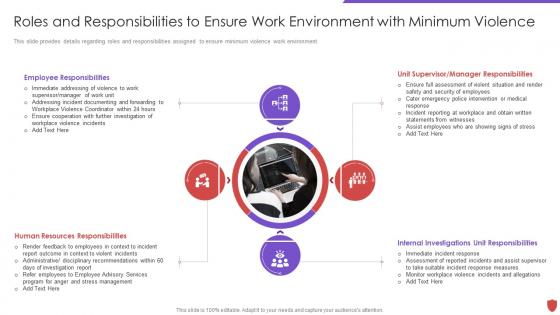 Cyber security risk management roles and responsibilities ensure work environment
Cyber security risk management roles and responsibilities ensure work environmentThis slide provides details regarding roles and responsibilities assigned to ensure minimum violence work environment. Increase audience engagement and knowledge by dispensing information using Cyber Security Risk Management Roles And Responsibilities Ensure Work Enviro. This template helps you present information on four stages. You can also present information on Employee Responsibilities, Unit Supervisor, Manager Responsibilities using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
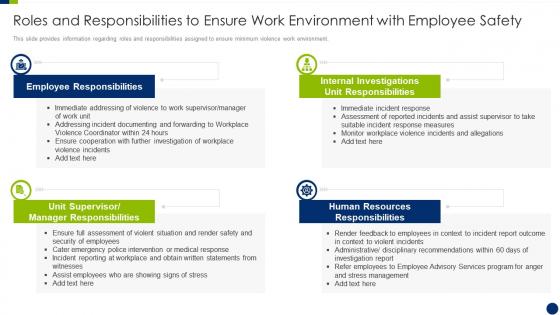 Enhancing overall project security it roles and responsibilities to ensure work environment
Enhancing overall project security it roles and responsibilities to ensure work environmentThis slide provides information regarding roles and responsibilities assigned to ensure minimum violence work environment. Introducing Enhancing Overall Project Security It Roles And Responsibilities To Ensure Work Environment to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Environment, Responsibilities, Resources, using this template. Grab it now to reap its full benefits.
-
 Information System Security And Risk Administration Plan Roles And Responsibilities Of Risk Management Team
Information System Security And Risk Administration Plan Roles And Responsibilities Of Risk Management TeamThis slide showcases responsibilities of major employees involved in information security risk management team. Key roles are information security manager, risk management officer and chief information officer. Introducing Information System Security And Risk Administration Plan Roles And Responsibilities Of Risk Management Team to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Information Security Manager, Risk Management Officer, Chief Information Officer, using this template. Grab it now to reap its full benefits.
-
 Roles And Responsibilities In Information Security Formulating Cybersecurity Plan
Roles And Responsibilities In Information Security Formulating Cybersecurity PlanThis slide showcases challenges involved in formulating risk management program for information security. It also shows solutions to tackle the challenges and impact of implementing them. Introducing Roles And Responsibilities In Information Security Formulating Cybersecurity Plan to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Information Security Manager, Risk Management Officer, Chief Information Officer, using this template. Grab it now to reap its full benefits.
-
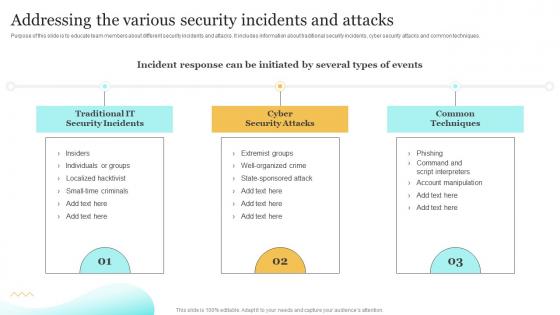 Addressing The Various Security Incidents Upgrading Cybersecurity With Incident Response Playbook
Addressing The Various Security Incidents Upgrading Cybersecurity With Incident Response PlaybookPurpose of this slide is to educate team members about different security incidents and attacks. It includes information about traditional security incidents, cyber security attacks and common techniques. Deliver an outstanding presentation on the topic using this Addressing The Various Security Incidents Upgrading Cybersecurity With Incident Response Playbook. Dispense information and present a thorough explanation of Individuals, Manipulation, Techniques using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
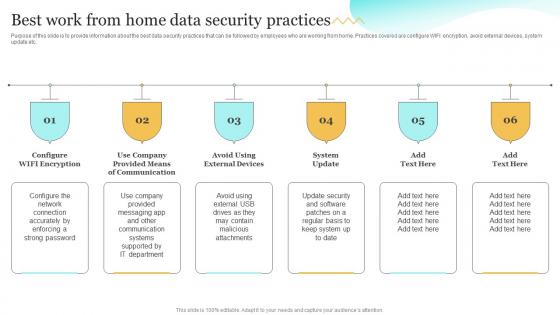 Best Work From Home Data Security Practices Upgrading Cybersecurity With Incident Response Playbook
Best Work From Home Data Security Practices Upgrading Cybersecurity With Incident Response PlaybookPurpose of this slide is to provide information about the best data security practices that can be followed by employees who are working from home. Practices covered are configure WIFI encryption, avoid external devices, system update etc. Introducing Best Work From Home Data Security Practices Upgrading Cybersecurity With Incident Response Playbook to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Communication, Attachments, Department, using this template. Grab it now to reap its full benefits.
-
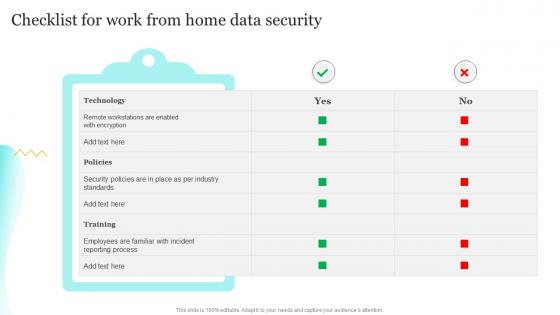 Checklist For Work From Home Data Security Upgrading Cybersecurity With Incident Response Playbook
Checklist For Work From Home Data Security Upgrading Cybersecurity With Incident Response PlaybookDeliver an outstanding presentation on the topic using this Checklist For Work From Home Data Security Upgrading Cybersecurity With Incident Response Playbook. Dispense information and present a thorough explanation of Process, Technology, Standards using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
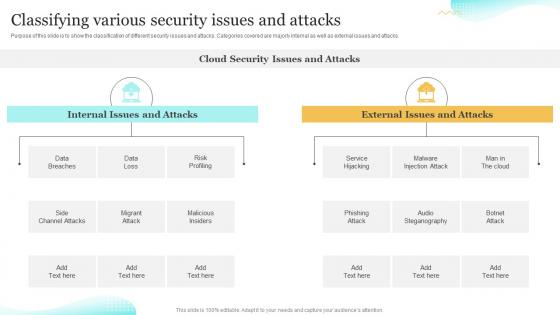 Classifying Various Security Issues And Attacks Upgrading Cybersecurity With Incident Response Playbook
Classifying Various Security Issues And Attacks Upgrading Cybersecurity With Incident Response PlaybookPurpose of this slide is to show the classification of different security issues and attacks. Categories covered are majorly internal as well as external issues and attacks. Deliver an outstanding presentation on the topic using this Classifying Various Security Issues And Attacks Upgrading Cybersecurity With Incident Response Playbook. Dispense information and present a thorough explanation of Classifying, Steganography, Classification using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
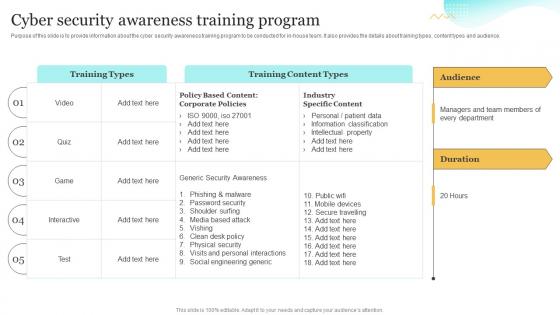 Cyber Security Awareness Training Program Upgrading Cybersecurity With Incident Response Playbook
Cyber Security Awareness Training Program Upgrading Cybersecurity With Incident Response PlaybookPurpose of this slide is to provide information about the cyber security awareness training program to be conducted for in-house team. It also provides the details about training types, content types and audience. Deliver an outstanding presentation on the topic using this Cyber Security Awareness Training Program Upgrading Cybersecurity With Incident Response Playbook. Dispense information and present a thorough explanation of Awareness, Information, Cyber Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Performing Cyber Training Exercises For Securing Upgrading Cybersecurity With Incident Response Playbook
Performing Cyber Training Exercises For Securing Upgrading Cybersecurity With Incident Response PlaybookPurpose of this slide is to address and perform various cyber training exercises in order to secure companys assets. Exercises covered are defense in depth, capture the flag etc. Present the topic in a bit more detail with this Performing Cyber Training Exercises For Securing Upgrading Cybersecurity With Incident Response Playbook Use it as a tool for discussion and navigation on Performing, Exercises, Securing. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
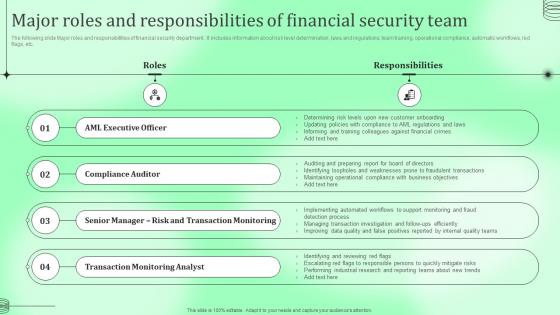 Major Roles And Responsibilities Financial Security Kyc Transaction Monitoring Tools For Business Safety
Major Roles And Responsibilities Financial Security Kyc Transaction Monitoring Tools For Business SafetyThe following slide Major roles and responsibilities of financial security department . It includes information about risk level determination, laws and regulations, team training, operational compliance, automatic workflows, red flags, etc. Present the topic in a bit more detail with this Major Roles And Responsibilities Financial Security Kyc Transaction Monitoring Tools For Business Safety. Use it as a tool for discussion and navigation on Responsibilities, Financial, Compliance Auditor . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Roles And Responsibilities Of Cyber Security Team Implementing Security Awareness Training
Roles And Responsibilities Of Cyber Security Team Implementing Security Awareness TrainingThe purpose of this slide is to outline various roles and responsibilities of key stakeholders involve in the security awareness team. Chief information security officer CISO, cyber risk committee, cyber risk manager and security operations manager are some of the major stakeholders which are highlighted in the slide. Introducing Roles And Responsibilities Of Cyber Security Team Implementing Security Awareness Training to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispence information on Chief Information Security, Cyber Risk Committee, Cyber Risk Manager, using this template. Grab it now to reap its full benefits.
-
 Key Personnel Roles And Responsibilities In Security Governance
Key Personnel Roles And Responsibilities In Security GovernanceThis slide highlights various roles and responsibilities of IT employees in data security governance. It includes key personnel such as senior manager, security professional, data owner, data custodian and auditor. Introducing our premium set of slides with Key Personnel Roles And Responsibilities In Security Governance. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Employee, Responsibilities, Role. So download instantly and tailor it with your information.
-
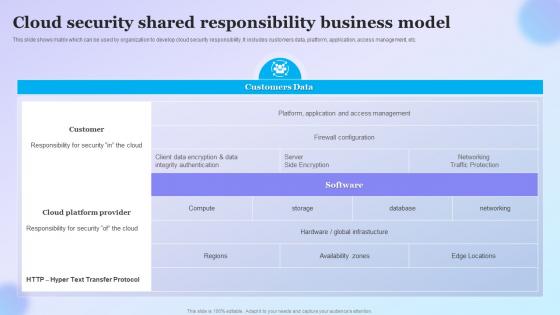 Cloud Security Shared Responsibility Business Model
Cloud Security Shared Responsibility Business ModelThis slide shows matrix which can be used by organization to develop cloud security responsibility. It includes customers data, platform, application, access management, etc. Introducing our Cloud Security Shared Responsibility Business Model set of slides. The topics discussed in these slides are Customer, Cloud Platform Provider, Software. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
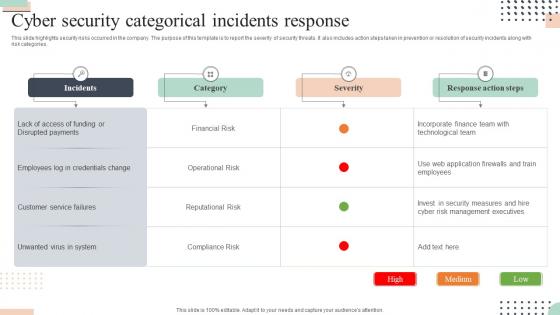 Cyber Security Categorical Incidents Response
Cyber Security Categorical Incidents ResponseThis slide highlights security risks occurred in the company. The purpose of this template is to report the severity of security threats. It also includes action steps taken in prevention or resolution of security incidents along with risk categories.Introducing our Cyber Security Categorical Incidents Response set of slides. The topics discussed in these slides are Disrupted Payments, Customer Service, Technological Team. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
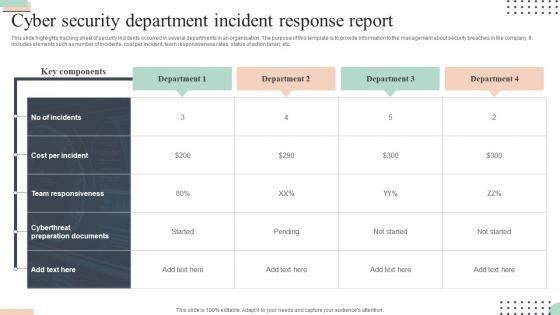 Cyber Security Department Incident Response Report
Cyber Security Department Incident Response ReportThis slide highlights tracking sheet of security incidents occurred in several departments in an organisation. The purpose of this template is to provide information to the management about security breaches in the company. It includes elements such as number of incidents, cost per incident, team responsiveness rates, status of action taken, etc.Presenting our well structured Cyber Security Department Incident Response Report. The topics discussed in this slide are Team Responsiveness, Preparation Documents, Cost Per Incident. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Cyber Security Incident Response Analysis Icon
Cyber Security Incident Response Analysis IconPresenting our well structured Cyber Security Incident Response Analysis Icon. The topics discussed in this slide are Cyber Security, Incident Response, Analysis Icon. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Cyber Security Incident Response Icon
Cyber Security Incident Response IconPresenting our set of slides with Cyber Security Incident Response Icon. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cyber Security, Incident Response Icon.
-
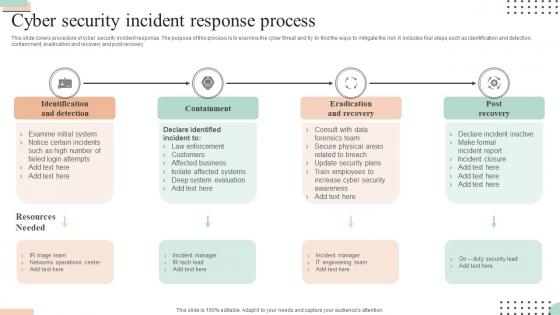 Cyber Security Incident Response Process
Cyber Security Incident Response ProcessThis slide covers procedure of cyber security incident response. The purpose of this process is to examine the cyber threat and try to find the ways to mitigate the risk. It includes four steps such as identification and detection, containment, eradication and recovery and post recovery.Introducing our premium set of slides with Cyber Security Incident Response Process. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Identification Detection, Eradication Recovery, Incident Manager. So download instantly and tailor it with your information.
-
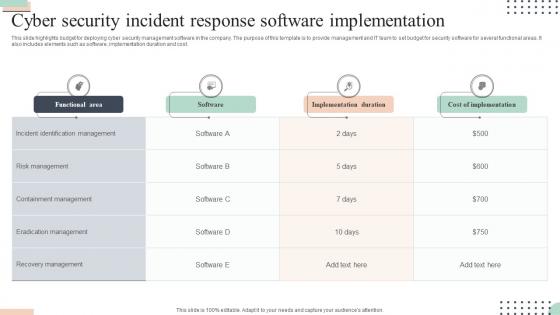 Cyber Security Incident Response Software Implementation
Cyber Security Incident Response Software ImplementationThis slide highlights budget for deploying cyber security management software in the company. The purpose of this template is to provide management and IT team to set budget for security software for several functional areas. It also includes elements such as software, implementation duration and cost.Introducing our Cyber Security Incident Response Software Implementation set of slides. The topics discussed in these slides are Identification Management, Risk Management, Containment Management. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Cyber Security Incident Response Team Icon
Cyber Security Incident Response Team IconPresenting our well structured Cyber Security Incident Response Team Icon. The topics discussed in this slide are Cyber Security, Incident Response, Team Icon. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
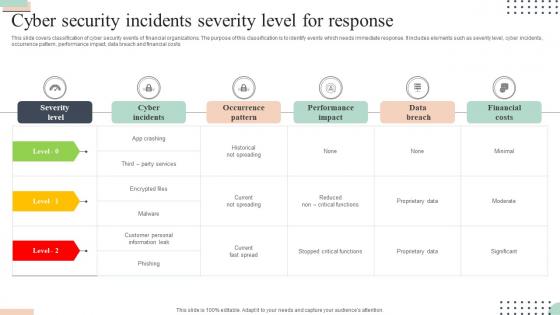 Cyber Security Incidents Severity Level For Response
Cyber Security Incidents Severity Level For ResponseThis slide covers classification of cyber security events of financial organizations. The purpose of this classification is to identify events which needs immediate response. It includes elements such as severity level, cyber incidents, occurrence pattern, performance impact, data breach and financial costs.Presenting our well structured Cyber Security Incidents Severity Level For Response. The topics discussed in this slide are Customer Personal, Information Leak, Performance Impact. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Gaming Cyber Security Incident Scorecard For Response
Gaming Cyber Security Incident Scorecard For ResponseThis slide highlights scorecard related to security breaches in gaming field. The purpose of this template is to rate the incidents based on severity. It includes elements such as account taken over, personal details posting on web, spyware, data breaches and cyber bullying.Introducing our Gaming Cyber Security Incident Scorecard For Response set of slides. The topics discussed in these slides are Confidential Information, Information Such, Account Takeover. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Training Plan For Cyber Security Incident Response Team
Training Plan For Cyber Security Incident Response TeamThis slide highlights schedule for training team to handle cyber security incidents in the company. The purpose of this template is to provide an overview on training program conducted by the company. It includes elements such as training topics covered, requirements along with duration of videos and certification post training.Presenting our set of slides with Training Plan For Cyber Security Incident Response Team. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Examination Incident, Response Scenarios Outcomes, Training Requirements.
-
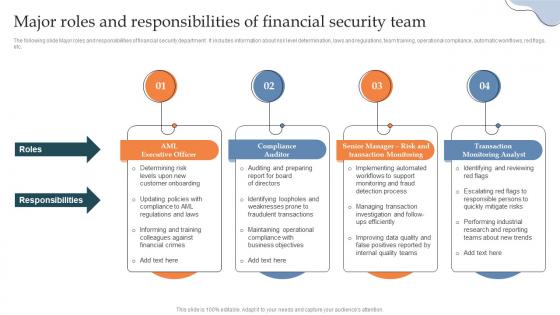 Major Roles And Responsibilities Of Financial Security Team Building AML And Transaction
Major Roles And Responsibilities Of Financial Security Team Building AML And TransactionThe following slide Major roles and responsibilities of financial security department . It includes information about risk level determination, laws and regulations, team training, operational compliance, automatic workflows, red flags, etc. Increase audience engagement and knowledge by dispensing information using Major Roles And Responsibilities Of Financial Security Team Building AML And Transaction. This template helps you present information on four stages. You can also present information on Compliance Auditor, Transaction Monitoring, Transaction Monitoring Analyst using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Enterprise Security Operation Center Team Roles And Responsibilities
Enterprise Security Operation Center Team Roles And ResponsibilitiesThis slide covers enterprise security operation center team roles and responsibilities. It involves key roles such as incident responder, security investigator, advanced security analyst and SOC manager. Introducing our Enterprise Security Operation Center Team Roles And Responsibilities set of slides. The topics discussed in these slides are Security Investigator, Incident Responder, Advanced Security Analyst. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Roles And Responsibilities Of Cyber Security Team Preventing Data Breaches Through Cyber Security
Roles And Responsibilities Of Cyber Security Team Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to outline various roles and responsibilities of key stakeholders involve in the security awareness team. Chief information security officer CISO, cyber risk committee, cyber risk manager and security operations manager are some of the major stakeholders which are highlighted in the slide. Introducing Roles And Responsibilities Of Cyber Security Team Preventing Data Breaches Through Cyber Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Cyber Risk Committee, Cyber Risk Manager, Security Operations Manager, using this template. Grab it now to reap its full benefits.
-
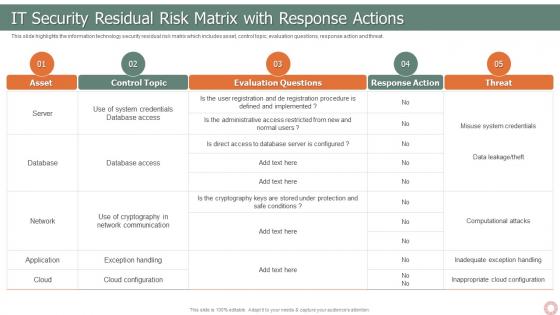 IT Risk Management Strategies IT Security Residual Risk Matrix With Response Actions
IT Risk Management Strategies IT Security Residual Risk Matrix With Response ActionsThis slide highlights the information technology security residual risk matrix which includes asset, control topic, evaluation questions, response action and threat. Deliver an outstanding presentation on the topic using this IT Risk Management Strategies IT Security Residual Risk Matrix With Response Actions. Dispense information and present a thorough explanation of Control Topic, Evaluation Question, Response Action, Threat using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
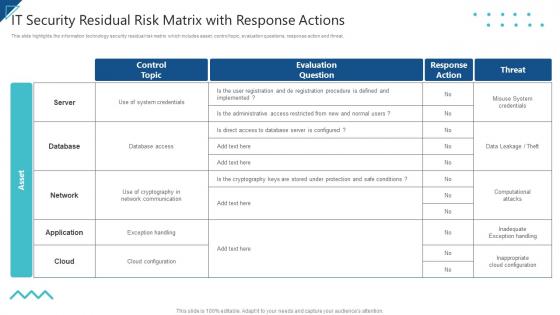 Enterprise Risk Management IT Security Residual Risk Matrix With Response Actions
Enterprise Risk Management IT Security Residual Risk Matrix With Response ActionsThis slide highlights the information technology security residual risk matrix which includes asset, control topic, evaluation questions, response action and threat. Present the topic in a bit more detail with this Enterprise Risk Management IT Security Residual Risk Matrix With Response Actions. Use it as a tool for discussion and navigation on Control Topic, Evaluation Question, Response Action, Threat. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Determining Roles And Responsibilities For Risk Handling Unified Endpoint Security
Determining Roles And Responsibilities For Risk Handling Unified Endpoint SecurityThis slide provides information regarding the roles and responsibilities of management in handling mobile device security risks. Key people involved in risk handling are chief risk officer, chief information security officer, senior management and executives and line managers. Introducing Determining Roles And Responsibilities For Risk Handling Unified Endpoint Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Chief Information, Executive Management, Development Implementation, using this template. Grab it now to reap its full benefits.
-
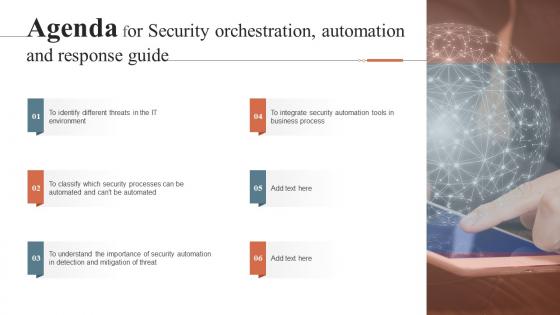 Agenda For Security Orchestration Automation And Response Guide Ppt Gallery Graphics Example
Agenda For Security Orchestration Automation And Response Guide Ppt Gallery Graphics ExampleIntroducing Agenda For Security Orchestration Automation And Response Guide Ppt Gallery Graphics Example to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Security Orchestration, Automation, Response Guide, using this template. Grab it now to reap its full benefits.
-
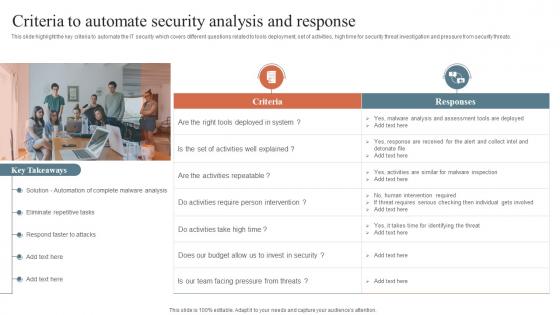 Criteria To Automate Security Analysis And Response Security Orchestration Automation
Criteria To Automate Security Analysis And Response Security Orchestration AutomationThis slide highlight the key criteria to automate the IT security which covers different questions related to tools deployment, set of activities, high time for security threat investigation and pressure from security threats. Increase audience engagement and knowledge by dispensing information using Criteria To Automate Security Analysis And Response Security Orchestration Automation. This template helps you present information on one stages. You can also present information on Malware Analysis, Eliminate Repetitive Tasks, Respond Faster To Attacks using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
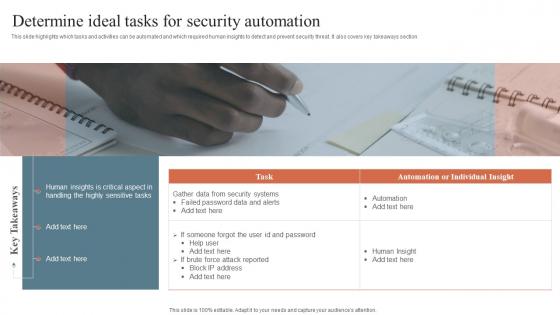 Determine Ideal Tasks For Security Automation Security Orchestration Automation And Response Guide
Determine Ideal Tasks For Security Automation Security Orchestration Automation And Response GuideThis slide highlights which tasks and activities can be automated and which required human insights to detect and prevent security threat. It also covers key takeaways section. Introducing Determine Ideal Tasks For Security Automation Security Orchestration Automation And Response Guide to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Determine Ideal, Tasks For Security, Automation, using this template. Grab it now to reap its full benefits.
-
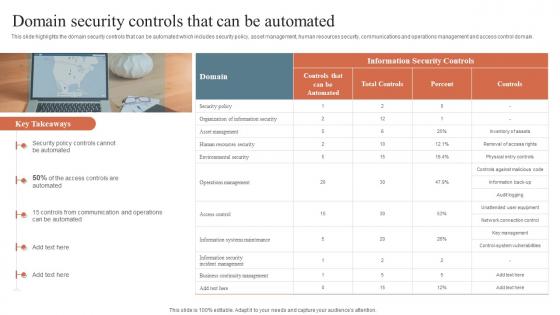 Domain Security Controls That Can Be Automated Security Orchestration Automation And Response Guide
Domain Security Controls That Can Be Automated Security Orchestration Automation And Response GuideThis slide highlights the domain security controls that can be automated which includes security policy, asset management, human resources security, communications and operations management and access control domain. Increase audience engagement and knowledge by dispensing information using Domain Security Controls That Can Be Automated Security Orchestration Automation And Response Guide. This template helps you present information on one stages. You can also present information on Security Policy, Communication And Operations, Security Controls using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
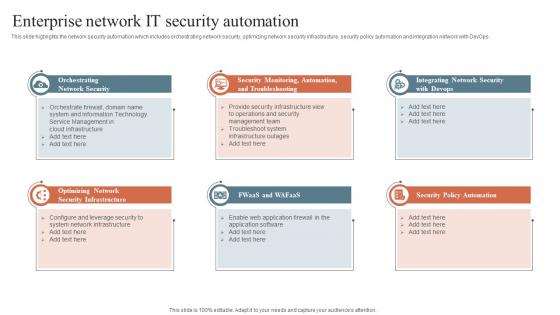 Enterprise Network It Security Automation Security Orchestration Automation And Response Guide
Enterprise Network It Security Automation Security Orchestration Automation And Response GuideThis slide highlights the network security automation which includes orchestrating network security, optimizing network security infrastructure, security policy automation and integration network with DevOps. Introducing Enterprise Network It Security Automation Security Orchestration Automation And Response Guide to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Network Security, Security Infrastructure, Security Policy Automation, using this template. Grab it now to reap its full benefits.
-
 Icons Slide For Security Orchestration Automation And Response Guide Ppt Gallery File Formats
Icons Slide For Security Orchestration Automation And Response Guide Ppt Gallery File FormatsIntroducing our well researched set of slides titled Icons Slide For Security Orchestration Automation And Response Guide Ppt Gallery File Formats. It displays a hundred percent editable icons. You can use these icons in your presentation to captivate your audiences attention. Download now and use it multiple times.
-
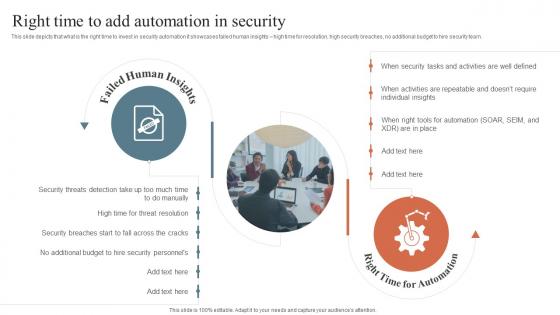 Right Time To Add Automation In Security Security Orchestration Automation And Response Guide
Right Time To Add Automation In Security Security Orchestration Automation And Response GuideThis slide depicts that what is the right time to invest in security automation it showcases failed human insights high time for resolution, high security breaches, no additional budget to hire security team. Introducing Right Time To Add Automation In Security Security Orchestration Automation And Response Guide to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Failed Human Insights, Right Time For Automation, Automation In Security, using this template. Grab it now to reap its full benefits.
-
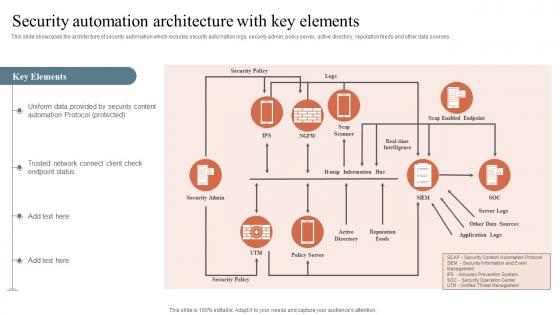 Security Automation Architecture With Key Elements Security Orchestration Automation And Response
Security Automation Architecture With Key Elements Security Orchestration Automation And ResponseThis slide showcases the architecture of security automation which includes security automation logs, security admin, policy server, active directory, reputation feeds and other data sources. Deliver an outstanding presentation on the topic using this Security Automation Architecture With Key Elements Security Orchestration Automation And Response. Dispense information and present a thorough explanation of Security Automation, Architecture, Trusted Network using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
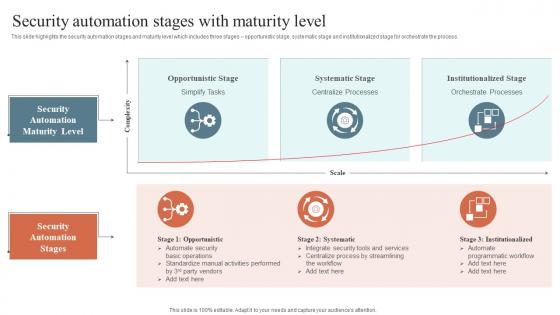 Security Automation Stages With Maturity Level Security Orchestration Automation And Response Guide
Security Automation Stages With Maturity Level Security Orchestration Automation And Response GuideThis slide highlights the security automation stages and maturity level which includes three stages opportunistic stage, systematic stage and institutionalized stage for orchestrate the process. Increase audience engagement and knowledge by dispensing information using Security Automation Stages With Maturity Level Security Orchestration Automation And Response Guide. This template helps you present information on two stages. You can also present information on Opportunistic Stage, Systematic Stage, Institutionalized Stage using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Security Orchestration Automation And Response Guide For Table Of Contents Ppt Gallery Format
Security Orchestration Automation And Response Guide For Table Of Contents Ppt Gallery FormatIntroducing Security Orchestration Automation And Response Guide For Table Of Contents Ppt Gallery Format to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Security Orchestration, Automation, Response Guide, using this template. Grab it now to reap its full benefits.
-
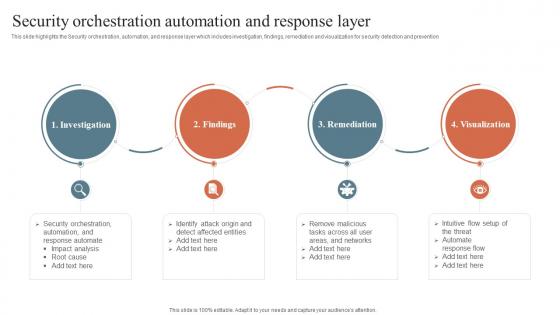 Security Orchestration Automation And Response Layer Security Orchestration Automation
Security Orchestration Automation And Response Layer Security Orchestration AutomationThis slide highlights the Security orchestration, automation, and response layer which includes investigation, findings, remediation and visualization for security detection and prevention. Increase audience engagement and knowledge by dispensing information using Security Orchestration Automation And Response Layer Security Orchestration Automation. This template helps you present information on four stages. You can also present information on Investigation, Remediation, Visualization, Findings using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
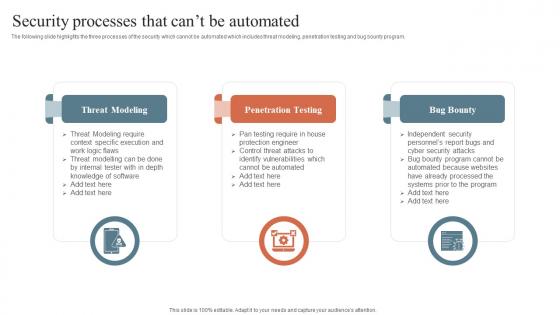 Security Processes That Cant Be Automated Security Orchestration Automation And Response Guide
Security Processes That Cant Be Automated Security Orchestration Automation And Response GuideThe following slide highlights the three processes of the security which cannot be automated which includes threat modeling, penetration testing and bug bounty program. Introducing Security Processes That Cant Be Automated Security Orchestration Automation And Response Guide to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Threat Modeling, Penetration Testing, Bug Bounty, using this template. Grab it now to reap its full benefits.
-
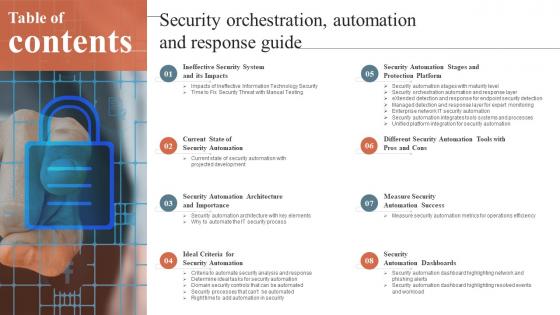 Table Of Contents For Security Orchestration Automation And Response Guide Ppt Gallery Gridlines
Table Of Contents For Security Orchestration Automation And Response Guide Ppt Gallery GridlinesIncrease audience engagement and knowledge by dispensing information using Table Of Contents For Security Orchestration Automation And Response Guide Ppt Gallery Gridlines. This template helps you present information on eight stages. You can also present information on Measure Security, Automation Success, Security Automation Dashboards using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
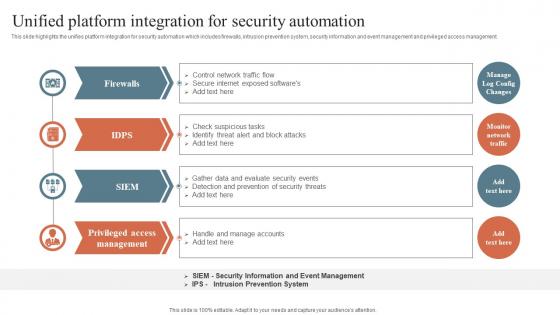 Unified Platform Integration For Security Automation Security Orchestration Automation And Response
Unified Platform Integration For Security Automation Security Orchestration Automation And ResponseThis slide highlights the unifies platform integration for security automation which includes firewalls, intrusion prevention system, security information and event management and privileged access management. Introducing Unified Platform Integration For Security Automation Security Orchestration Automation And Response to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Unified Platform, Integration For Security, Privileged Access, using this template. Grab it now to reap its full benefits.
-
 Why To Automate The It Security Process Security Orchestration Automation And Response Guide
Why To Automate The It Security Process Security Orchestration Automation And Response GuideThis slide highlights the benefits or importance of automation security process which includes better threat detection, faster containment, improve productivity, admin role delegation and incident response. Increase audience engagement and knowledge by dispensing information using Why To Automate The It Security Process Security Orchestration Automation And Response Guide. This template helps you present information on five stages. You can also present information on Better Threat Detection, Faster Containment, Improve Productivity using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
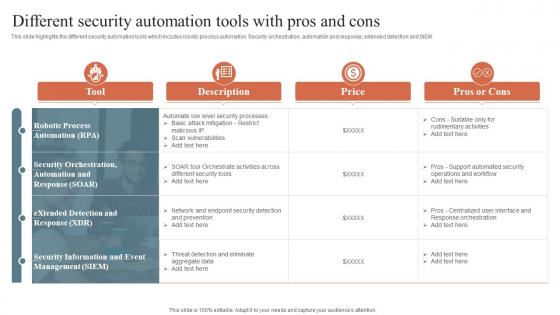 Security Orchestration Automation And Response Different Security Automation Tools With Pros And Cons
Security Orchestration Automation And Response Different Security Automation Tools With Pros And ConsThis slide highlights the security automation platform which showcases its key features it also showcases the importance and value of security tools, people and system procedures. Introducing Security Orchestration Automation And Response Different Security Automation Tools With Pros And Cons to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Security Automation, Integrates Tools, Systems And Processes, using this template. Grab it now to reap its full benefits.
-
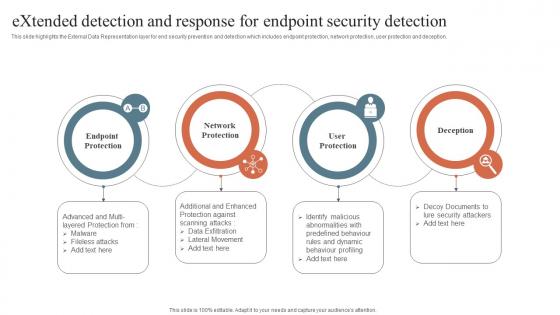 Security Orchestration Automation Extended Detection And Response For Endpoint Security Detection
Security Orchestration Automation Extended Detection And Response For Endpoint Security DetectionThis slide highlights the External Data Representation layer for end security prevention and detection which includes endpoint protection, network protection, user protection and deception. Introducing Security Orchestration Automation Extended Detection And Response For Endpoint Security Detection to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Network Protection, Endpoint Protection, User Protection, using this template. Grab it now to reap its full benefits.
-
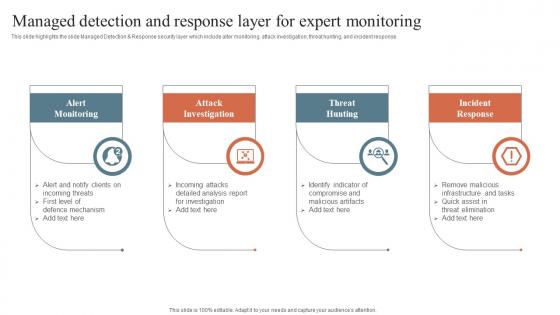 Security Orchestration Automation Managed Detection And Response Layer For Expert Monitoring
Security Orchestration Automation Managed Detection And Response Layer For Expert MonitoringThis slide highlights the slide Managed Detection and Response security layer which include alter monitoring, attack investigation, threat hunting, and incident response. Increase audience engagement and knowledge by dispensing information using Security Orchestration Automation Managed Detection And Response Layer For Expert Monitoring. This template helps you present information on four stages. You can also present information on Alert Monitoring, Attack Investigation, Threat Hunting using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 30 60 90 Days Plan Security Incident Response Playbook Ppt Slides Background Images
30 60 90 Days Plan Security Incident Response Playbook Ppt Slides Background ImagesIntroducing 30 60 90 Days Plan Security Incident Response Playbook Ppt Slides Background Images to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on 30 60 90 Days Plan, using this template. Grab it now to reap its full benefits.
-
 About Us Security Incident Response Playbook Ppt Slides Infographic Template
About Us Security Incident Response Playbook Ppt Slides Infographic TemplateIncrease audience engagement and knowledge by dispensing information using About Us Security Incident Response Playbook Ppt Slides Infographic Template. This template helps you present information on three stages. You can also present information on About Us using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
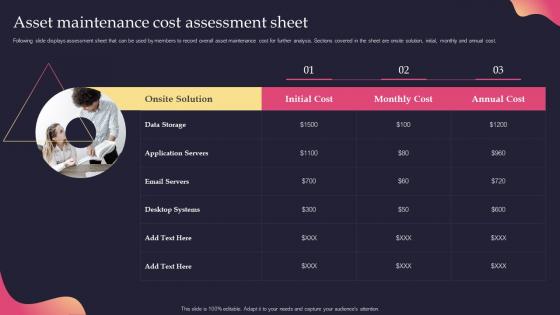 Asset Maintenance Cost Assessment Sheet Security Incident Response Playbook
Asset Maintenance Cost Assessment Sheet Security Incident Response PlaybookFollowing slide displays assessment sheet that can be used by members to record overall asset maintenance cost for further analysis. Sections covered in the sheet are onsite solution, initial, monthly and annual cost. Present the topic in a bit more detail with this Asset Maintenance Cost Assessment Sheet Security Incident Response Playbook. Use it as a tool for discussion and navigation on Assessment, Maintenance, Analysis. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Backup Methods For Cyber Defense Planning Security Incident Response Playbook
Backup Methods For Cyber Defense Planning Security Incident Response PlaybookFollowing slide shows various backup methods as well as backup options that can be chosen for cyber defense planning. Methods covered are full, differential and incremental. Deliver an outstanding presentation on the topic using this Backup Methods For Cyber Defense Planning Security Incident Response Playbook. Dispense information and present a thorough explanation of Planning, Incremental, Differential using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
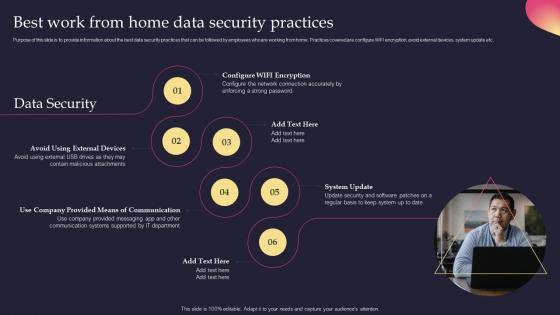 Best Work From Home Data Security Practices Security Incident Response Playbook
Best Work From Home Data Security Practices Security Incident Response PlaybookPurpose of this slide is to provide information about the best data security practices that can be followed by employees who are working from home. Practices covered are configure WIFI encryption, avoid external devices, system update etc. Introducing Best Work From Home Data Security Practices Security Incident Response Playbook to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on System Update, Communication, External Devices, using this template. Grab it now to reap its full benefits.
-
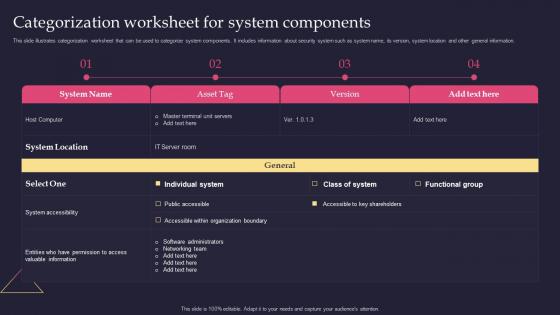 Categorization Worksheet For System Components Security Incident Response Playbook
Categorization Worksheet For System Components Security Incident Response PlaybookThis slide illustrates categorization worksheet that can be used to categorize system components. It includes information about security system such as system name, its version, system location and other general information. Present the topic in a bit more detail with this Categorization Worksheet For System Components Security Incident Response Playbook. Use it as a tool for discussion and navigation on Categorization, Worksheet, Components. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Checklist To Ensure Asset Protection From Internal Threats Security Incident Response Playbook
Checklist To Ensure Asset Protection From Internal Threats Security Incident Response PlaybookFollowing slide displays checklist having security control measures that can be used by members to ensure the safety of companys assets from any insider threat. Deliver an outstanding presentation on the topic using this Checklist To Ensure Asset Protection From Internal Threats Security Incident Response Playbook. Dispense information and present a thorough explanation of Protection, Measures, Ensure using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Classifying Various Security Issues And Attacks Security Incident Response Playbook
Classifying Various Security Issues And Attacks Security Incident Response PlaybookPurpose of this slide is to show the classification of different security issues and attacks. Categories covered are majorly internal as well as external issues and attacks. Present the topic in a bit more detail with this Classifying Various Security Issues And Attacks Security Incident Response Playbook. Use it as a tool for discussion and navigation on Classifying, Categories, Security. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Communication Plan For Effective Incident Management Security Incident Response Playbook
Communication Plan For Effective Incident Management Security Incident Response PlaybookThis slide portrays communication plan for successfully managing cyber incidents. Sections covered are deliverable info, recipient, delivery method, schedule and responsible person. Deliver an outstanding presentation on the topic using this Communication Plan For Effective Incident Management Security Incident Response Playbook. Dispense information and present a thorough explanation of Management, Communication, Successfully using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Comparison Security Incident Response Playbook Ppt Slides Background Designs
Comparison Security Incident Response Playbook Ppt Slides Background DesignsIntroducing Comparison Security Incident Response Playbook Ppt Slides Background Designs to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Comparison, using this template. Grab it now to reap its full benefits.