Powerpoint Templates and Google slides for Security Technology Roadmap
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
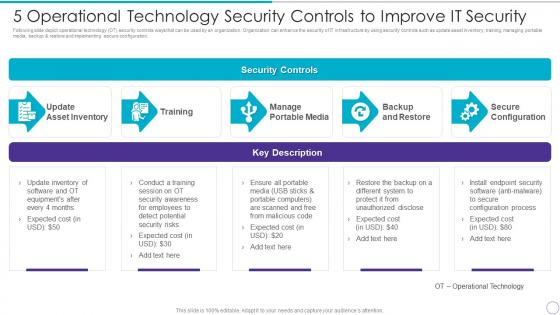 5 Operational Technology Security Controls To Improve It Security
5 Operational Technology Security Controls To Improve It SecurityFollowing slide depict operational technology OT security controls ways that can be used by an organization. Organization can enhance the security of IT infrastructure by using security controls such as update asset inventory, training, managing portable media, backup and restore and implementing secure configuration. Present the topic in a bit more detail with this 5 Operational Technology Security Controls To Improve IT Security. Use it as a tool for discussion and navigation on Update Asset Inventory, Training Manage, Portable Media, Backup And Restore, Secure Configuration. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
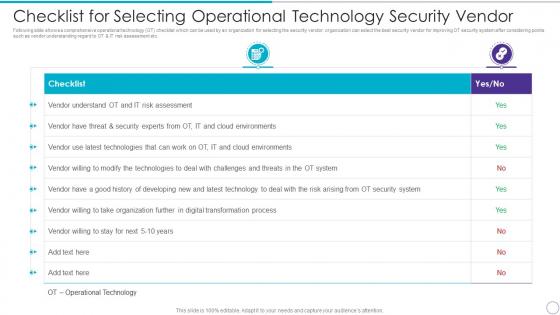 Checklist For Selecting Operational Technology Security Vendor
Checklist For Selecting Operational Technology Security VendorFollowing slide shows a comprehensive operational technology OT checklist which can be used by an organization for selecting the security vendor. organization can select the best security vendor for improving OT security system after considering points such as vendor understanding regard to OT and IT risk assessment etc. Deliver an outstanding presentation on the topic using this Checklist For Selecting Operational Technology Security Vendor. Dispense information and present a thorough explanation of Checklist, Vendor Understand OT, IT Risk Assessment, Digital Transformation Process using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
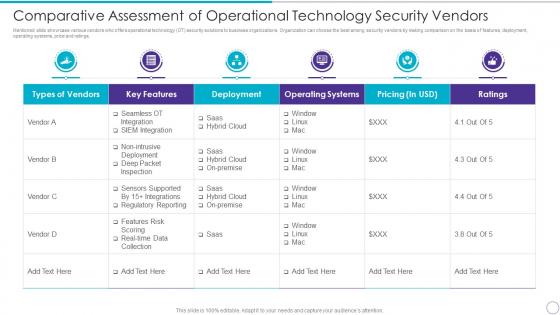 Comparative Assessment Of Operational Technology Security Vendors
Comparative Assessment Of Operational Technology Security VendorsMentioned slide showcase various vendors who offers operational technology OT security solutions to business organizations. Organization can choose the best among security vendors by making comparison on the basis of features, deployment, operating systems, price and ratings. Present the topic in a bit more detail with this Comparative Assessment Of Operational Technology Security Vendors. Use it as a tool for discussion and navigation on Types Vendors, Key Features, Deployment, Operating Systems, Pricing In USD, Ratings. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Icon For Operational Technology Security
Icon For Operational Technology SecurityIntroducing Icon For Operational Technology Security to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Icon For Operational Technology Security, using this template. Grab it now to reap its full benefits.
-
 Operational Technology Icon For Security Threat Detection
Operational Technology Icon For Security Threat DetectionIntroducing Operational Technology Icon For Security Threat Detection to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Operational Technology Icon For Security Threat Detection, using this template. Grab it now to reap its full benefits.
-
 Operational Technology Security Challenges And Solutions To Overcome
Operational Technology Security Challenges And Solutions To OvercomeMentioned slide illustrates various operational technology OT security challenges. It also cover information about the multiple solutions which will assist organization to overcome challenges and build a strong security IT system. Introducing Operational Technology Security Challenges And Solutions To Overcome to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Challenges, Solutions, Employees, using this template. Grab it now to reap its full benefits.
-
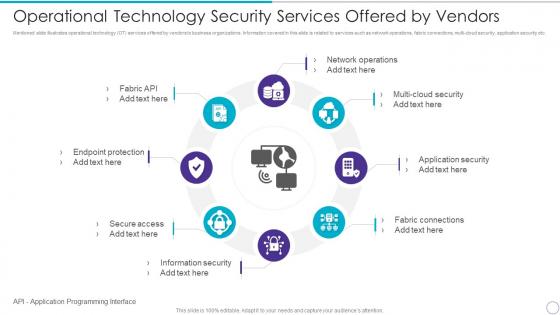 Operational Technology Security Services Offered By Vendors
Operational Technology Security Services Offered By VendorsMentioned slide illustrates operational technology OT services offered by vendors to business organizations. Information covered in this slide is related to services such as network operations, fabric connections, multi-cloud security, application security etc. Increase audience engagement and knowledge by dispensing information using Operational Technology Security Services Offered By Vendors. This template helps you present information on eight stages. You can also present information on Network Operations, Multi Cloud Security, Application Security, Fabric Connections, Information Security, Secure Access, Endpoint Protection, Fabric API using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Security Technology In Use Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Security Technology In Use Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Security technology in use colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Security Technology In Use Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Security Technology In Use Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Security technology in use monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
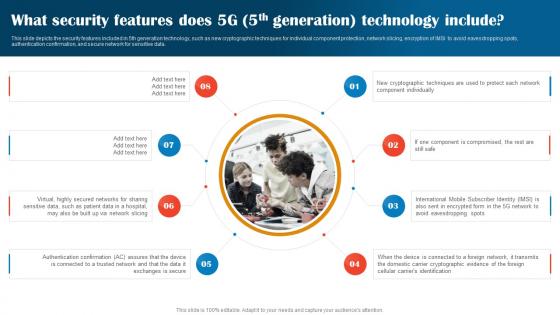 1G To 5G Technology What Security Features Does 5G 5th Generation Technology Include
1G To 5G Technology What Security Features Does 5G 5th Generation Technology IncludeThis slide depicts the security features included in 5th generation technology, such as new cryptographic techniques for individual component protection, network slicing, encryption of IMSI to avoid eavesdropping spots, authentication confirmation, and secure network for sensitive data. Introducing 1G To 5G Technology What Security Features Does 5G 5th Generation Technology Include Technology to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Security Features, Technology Include, Authentication Confirmation, using this template. Grab it now to reap its full benefits.
-
 Security Architecture In 5G Technology Ppt Powerpoint Presentation Infographic
Security Architecture In 5G Technology Ppt Powerpoint Presentation InfographicThis slide represents the security architecture in 5G technology, including the system wide security tasks and 5G function element deployments or vertical security. The components include devices, global wireless solutions, access and network, applications and cloud infrastructure, and user ID administration. Deliver an outstanding presentation on the topic using this Security Architecture In 5G Technology Ppt Powerpoint Presentation Infographic. Dispense information and present a thorough explanation of Security Functions, Security Management, Global Wireless Solutions using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Security In 5G Technology Architecture Ppt Powerpoint Presentation Slides Template
Security In 5G Technology Architecture Ppt Powerpoint Presentation Slides TemplateThis slide depicts the security in 5G architecture, including the standards detailed by 3GPP 3rd Generation Partnership Project, such as SUPI, unified authentication, extensible authentication standards, and flexible security policies. Increase audience engagement and knowledge by dispensing information using Security In 5G Technology Architecture Ppt Powerpoint Presentation Slides Template. This template helps you present information on four stages. You can also present information on Security Procedures, Mobile Technology, Service Delivery Process using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Is Blockchain Technology Secure Cryptographic Ledger IT
Is Blockchain Technology Secure Cryptographic Ledger ITThis slide defines the security of blockchain technology and how hash codes are helpful to maintain data integrity and security in blockchain.Present the topic in a bit more detail with this Is Blockchain Technology Secure Cryptographic Ledger IT. Use it as a tool for discussion and navigation on Generated Math Algorithms, Weaknesses Blockchain, Networks Nevertheless. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
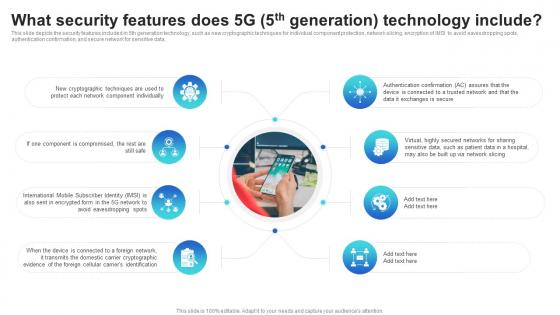 What Security Features Does 5g 5th Generation Technology Include Mobile Communication Standards 1g To 5g
What Security Features Does 5g 5th Generation Technology Include Mobile Communication Standards 1g To 5gThis slide depicts the security features included in 5th generation technology, such as new cryptographic techniques for individual component protection, network slicing, encryption of IMSI to avoid eavesdropping spots, authentication confirmation, and secure network for sensitive data. Introducing What Security Features Does 5g 5th Generation Technology Include Mobile Communication Standards 1g To 5g to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on 5g Network, 5g Technology, using this template. Grab it now to reap its full benefits.
-
 Icon For Payment Security Technology In Investor Transactions
Icon For Payment Security Technology In Investor TransactionsPresenting our set of slides with Icon For Payment Security Technology In Investor Transactions. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Icon, Payment Security Technology, Investor Transactions.
-
 Investor Technology And Digitalization Trends In Securities And Capital Market
Investor Technology And Digitalization Trends In Securities And Capital MarketThis slide showcases transformation brought by digitalization and technology to increase transparency for investors. It includes information such as smart phones and tablets, innovative fintech, etc. Introducing our premium set of slides with Investor Technology And Digitalization Trends In Securities And Capital Market. Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Smart Phones, Tablets, Digitalization. So download instantly and tailor it with your information.
-
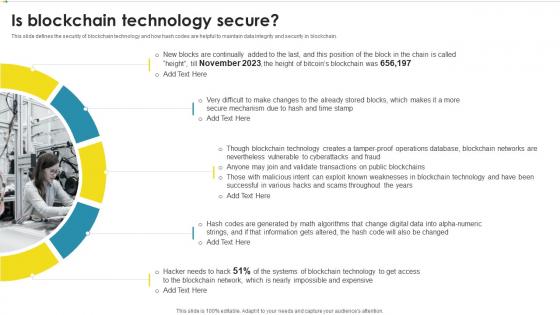 Is Blockchain Technology Secure Peer To Peer Ledger Ppt Powerpoint Presentation Gallery Backgrounds
Is Blockchain Technology Secure Peer To Peer Ledger Ppt Powerpoint Presentation Gallery BackgroundsThis slide defines the security of blockchain technology and how hash codes are helpful to maintain data integrity and security in blockchain. Introducing Is Blockchain Technology Secure Peer To Peer Ledger Ppt Powerpoint Presentation Gallery Backgrounds to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Blockchain Network, Blockchain Technology, using this template. Grab it now to reap its full benefits.
-
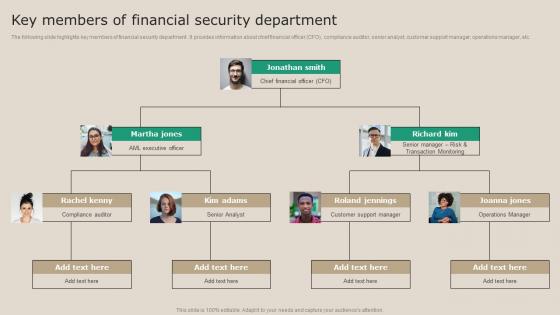 Key Members Of Financial Security Department Real Time Transaction Monitoring Tools
Key Members Of Financial Security Department Real Time Transaction Monitoring ToolsThe following slide highlights key members of financial security department. It provides information about chief financial officer CFO, compliance auditor, senior analyst, customer support manager, operations manager, etc. Increase audience engagement and knowledge by dispensing information using Key Members Of Financial Security Department Real Time Transaction Monitoring Tools. This template helps you present information on two stages. You can also present information on Compliance Auditor, Senior Analyst, Operations Manager using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
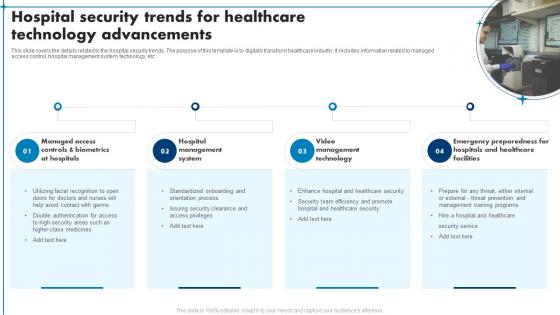 Hospital Security Trends For Healthcare Technology Advancements
Hospital Security Trends For Healthcare Technology AdvancementsThis slide covers the details related to the hospital security trends. The purpose of this template is to digitally transform healthcare industry. It includes information related to managed access control, hospital management system, technology, etc. Introducing our premium set of slides with name Hospital Security Trends For Healthcare Technology Advancements. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Management System, Management Technology, Healthcare Facilities. So download instantly and tailor it with your information.
-
 Key Members Of Financial Security Department Kyc Transaction Monitoring Tools For Business Safety
Key Members Of Financial Security Department Kyc Transaction Monitoring Tools For Business SafetyThe following slide highlights key members of financial security department . It provides information about chief financial officer CFO, compliance auditor, senior analyst, customer support manager, operations manager, etc. Present the topic in a bit more detail with this Key Members Of Financial Security Department Kyc Transaction Monitoring Tools For Business Safety. Use it as a tool for discussion and navigation on Financial, Department, Compliance. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
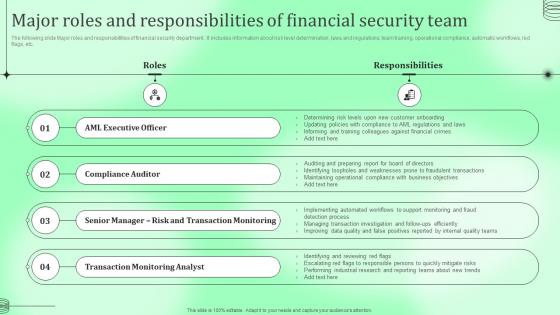 Major Roles And Responsibilities Financial Security Kyc Transaction Monitoring Tools For Business Safety
Major Roles And Responsibilities Financial Security Kyc Transaction Monitoring Tools For Business SafetyThe following slide Major roles and responsibilities of financial security department . It includes information about risk level determination, laws and regulations, team training, operational compliance, automatic workflows, red flags, etc. Present the topic in a bit more detail with this Major Roles And Responsibilities Financial Security Kyc Transaction Monitoring Tools For Business Safety. Use it as a tool for discussion and navigation on Responsibilities, Financial, Compliance Auditor . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Comparative Analysis Of Various Cloud Security Tools
Comparative Analysis Of Various Cloud Security ToolsThis slide shows comparison amongst various cloud security tools which can be used by the organization to select the best suitable tool. it also includes details about features, price and ratings. Introducing our Comparative Analysis Of Various Cloud Security Tools set of slides. The topics discussed in these slides are Comparative Analysis, Various, Cloud Security Tools. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
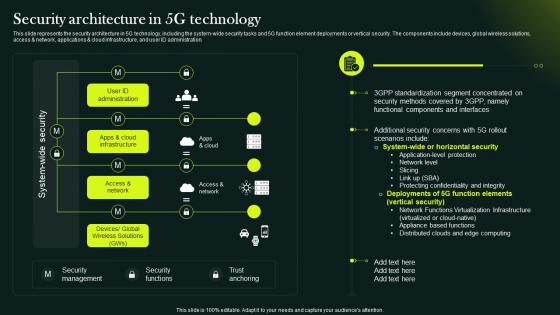 5G Network Technology Architecture Security Architecture In 5G Technology
5G Network Technology Architecture Security Architecture In 5G TechnologyThis slide represents the security architecture in 5G technology, including the system wide security tasks and 5G function element deployments or vertical security. The components include devices, global wireless solutions, access and network, applications and cloud infrastructure, and user ID administration. Present the topic in a bit more detail with this 5G Network Technology Architecture Security Architecture In 5G Technology. Use it as a tool for discussion and navigation on System Wide Security, Security Functions, Trust Anchoring. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 5G Network Technology Architecture Security In 5G Technology Architecture
5G Network Technology Architecture Security In 5G Technology ArchitectureThis slide depicts the security in 5G architecture, including the standards detailed by 3GPP 3rd Generation Partnership Project, such as SUPI, unified authentication, extensible authentication standards, and flexible security policies. Introducing 5G Network Technology Architecture Security In 5G Technology Architecture to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Mobile Technologys Security, Service Delivery Process, 5G Security Features, using this template. Grab it now to reap its full benefits.
-
 Blockchain Technology For Business Security Icon
Blockchain Technology For Business Security IconIntroducing our Blockchain Technology For Business Security Icon set of slides. The topics discussed in these slides are Blockchain Technology, Business Security Icon. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
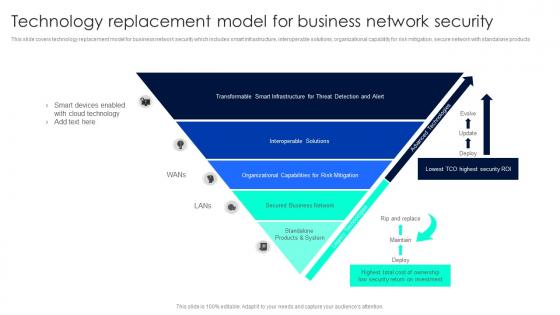 Technology Replacement Model For Business Network Security
Technology Replacement Model For Business Network SecurityThis slide covers technology replacement model for business network security which includes smart infrastructure, interoperable solutions, organizational capability for risk mitigation, secure network with standalone products. Introducing our premium set of slides with name Technology Replacement Model For Business Network Security. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Interoperable Solutions, Secured Business, Standalone Products. So download instantly and tailor it with your information.
-
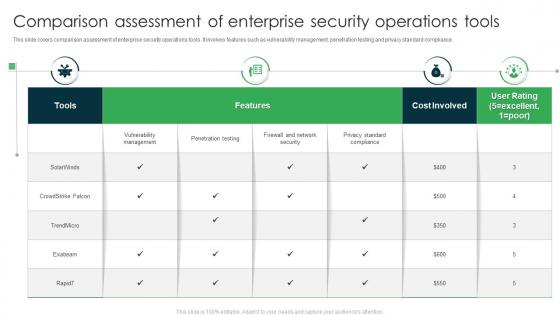 Comparison Assessment Of Enterprise Security Operations Tools
Comparison Assessment Of Enterprise Security Operations ToolsThis slide covers comparison assessment of enterprise security operations tools. It involves features such as vulnerability management, penetration testing and privacy standard compliance. Introducing our Comparison Assessment Of Enterprise Security Operations Tools set of slides. The topics discussed in these slides are Features, Cost Involved, User Rating. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Digital Ledger It Is Blockchain Technology Secure Ppt Styles Professional
Digital Ledger It Is Blockchain Technology Secure Ppt Styles ProfessionalThis slide defines the security of blockchain technology and how hash codes are helpful to maintain data integrity and security in blockchain. Increase audience engagement and knowledge by dispensing information using Digital Ledger It Is Blockchain Technology Secure Ppt Styles Professional. This template helps you present information on five stages. You can also present information on Blockchain Technology Secure, Secure Mechanism, Operations Database using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyber Security Tools Technologies In Powerpoint And Google Slides Cpb
Cyber Security Tools Technologies In Powerpoint And Google Slides CpbPresenting our Cyber Security Tools Technologies In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Cyber Security Tools Technologies. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
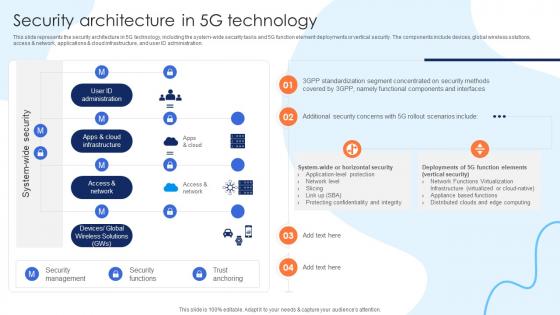 Security Architecture In 5G Technology Working Of 5G Technology IT Ppt Topics
Security Architecture In 5G Technology Working Of 5G Technology IT Ppt TopicsThis slide represents the security architecture in 5G technology, including the system wide security tasks and 5G function element deployments or vertical security. The components include devices, global wireless solutions, access and network, applications and cloud infrastructure, and user ID administration. Present the topic in a bit more detail with this Security Architecture In 5G Technology Working Of 5G Technology IT Ppt Topics. Use it as a tool for discussion and navigation on Security Architecture, Technology, Security Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
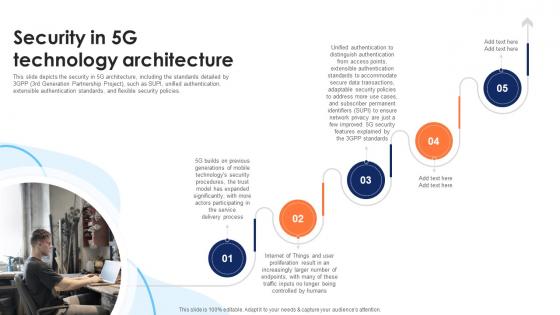 Security In 5G Technology Architecture Working Of 5G Technology IT Ppt Ideas
Security In 5G Technology Architecture Working Of 5G Technology IT Ppt IdeasThis slide depicts the security in 5G architecture, including the standards detailed by 3GPP 3rd Generation Partnership Project, such as SUPI, unified authentication, extensible authentication standards, and flexible security policies. Increase audience engagement and knowledge by dispensing information using Security In 5G Technology Architecture Working Of 5G Technology IT Ppt Ideas. This template helps you present information on five stages. You can also present information on Mobile Technologys, Service, Delivery Process using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
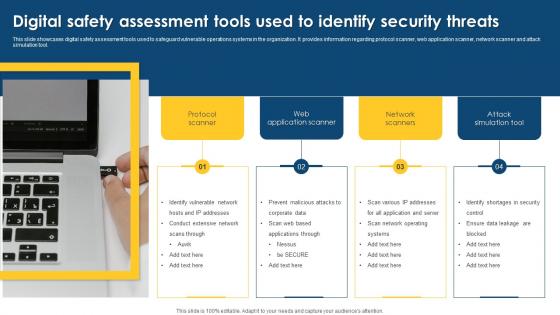 Digital Safety Assessment Tools Used To Identify Security Threats
Digital Safety Assessment Tools Used To Identify Security ThreatsThis slide showcases digital safety assessment tools used to safeguard vulnerable operations systems in the organization. It provides information regarding protocol scanner, web application scanner, network scanner and attack simulation tool. Presenting our well structured Digital Safety Assessment Tools Used To Identify Security Threats. The topics discussed in this slide are Assessment, Application, Identify Vulnerable. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Agenda Enterprise Risk Management And Information Technology Security
Agenda Enterprise Risk Management And Information Technology SecurityIntroducing Agenda Enterprise Risk Management And Information Technology Security to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Organization, IT Networks, IT Risk Management, using this template. Grab it now to reap its full benefits.
-
 Enterprise Risk Management And Information Technology Security Table Of Contents
Enterprise Risk Management And Information Technology Security Table Of ContentsIncrease audience engagement and knowledge by dispensing information using Enterprise Risk Management And Information Technology Security Table Of Contents. This template helps you present information on one stages. You can also present information on Security Criteria, Control Measures, IT System Vulnerabilities using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Icons Slide For Enterprise Risk Management And Information Technology Security
Icons Slide For Enterprise Risk Management And Information Technology SecurityIntroducing our well researched set of slides titled Icons Slide For Enterprise Risk Management And Information Technology Security. It displays a hundred percent editable icons. You can use these icons in your presentation to captivate your audiences attention. Download now and use it multiple times.
-
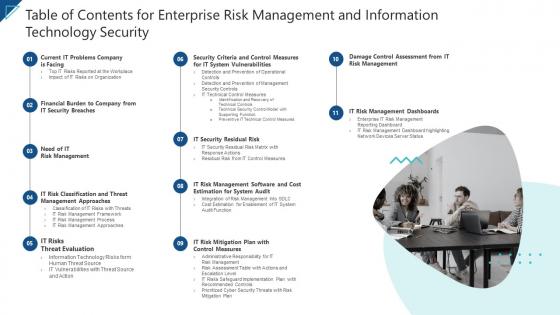 Table Of Contents For Enterprise Risk Management And Information Technology Security
Table Of Contents For Enterprise Risk Management And Information Technology SecurityIntroducing Table Of Contents For Enterprise Risk Management And Information Technology Security to increase your presentation threshold. Encompassed with eleven stages, this template is a great option to educate and entice your audience. Dispence information on IT Risks, Threat Evaluation, IT Risk Management, Cost Estimation, using this template. Grab it now to reap its full benefits.
-
 Blockchain Security Technology For Healthcare Industry
Blockchain Security Technology For Healthcare IndustryThis slide highlights the importance of blockchain technology in healthcare industry which is used to preserve data and promote workflow authenticity. Key components are supply chain, electronic health records, safety access and staff verification. Presenting our set of slides with name Blockchain Security Technology For Healthcare Industry. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Blockchain Security, Technology, Healthcare Industry.
-
 Information Security Policy For Employees Information Technology Policy
Information Security Policy For Employees Information Technology PolicyThis slide depicts the information security policy that critical topics covered in this policy. It also covers the reasons for frequent changes in the policy. Introducing Information Security Policy For Employees Information Technology Policy to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Company Infrastructure, IT Infrastructure, Data Processing Activities And Purposes, using this template. Grab it now to reap its full benefits.
-
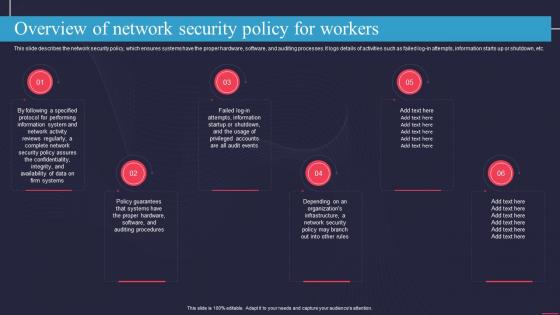 Overview Of Network Security Policy For Workers Information Technology Policy
Overview Of Network Security Policy For Workers Information Technology PolicyThis slide describes the network security policy, which ensures systems have the proper hardware, software, and auditing processes. It logs details of activities such as failed log in attempts, information starts up or shutdown, etc. Introducing Overview Of Network Security Policy For Workers Information Technology Policy to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Organizations, Network Security, Information, using this template. Grab it now to reap its full benefits.
-
 Security Awareness And Training Policy Overview Information Technology Policy
Security Awareness And Training Policy Overview Information Technology PolicyThis slide represents the security awareness and training policy. It covers that the training program should be designed by management, and employees will sign a confidentiality agreement after getting the training. Increase audience engagement and knowledge by dispensing information using Security Awareness And Training Policy Overview Information Technology Policy. This template helps you present information on six stages. You can also present information on Corporate Data, Security, Employees using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Future Cyber Security Technologies In Powerpoint And Google Slides Cpb
Future Cyber Security Technologies In Powerpoint And Google Slides CpbPresenting our Future Cyber Security Technologies In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Future Cyber Security Technologies This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
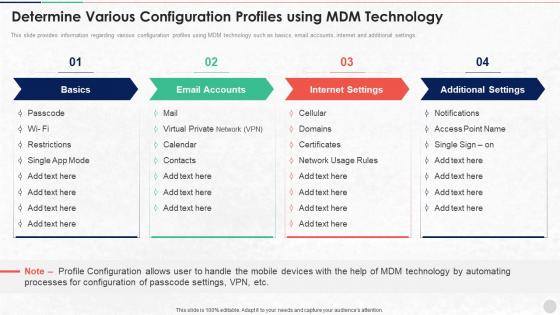 Determine Various Configuration Profiles Using MDM Technology Unified Endpoint Security
Determine Various Configuration Profiles Using MDM Technology Unified Endpoint SecurityThis slide provides information regarding various configuration profiles using MDM technology such as basics, email accounts, internet and additional settings. Present the topic in a bit more detail with this Determine Various Configuration Profiles Using MDM Technology Unified Endpoint Security. Use it as a tool for discussion and navigation on Internet Settings, Processes Configuration, Profile Configuration. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
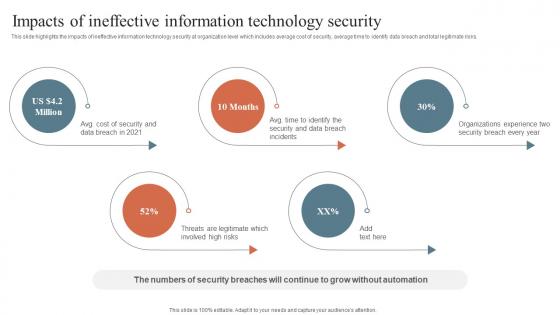 Impacts Of Ineffective Information Technology Security Security Orchestration Automation
Impacts Of Ineffective Information Technology Security Security Orchestration AutomationThis slide highlights the impacts of ineffective information technology security at organization level which includes average cost of security, average time to identify data breach and total legitimate risks. Introducing Impacts Of Ineffective Information Technology Security Security Orchestration Automation to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Impacts Of Ineffective, Information Technology, Security, using this template. Grab it now to reap its full benefits.
-
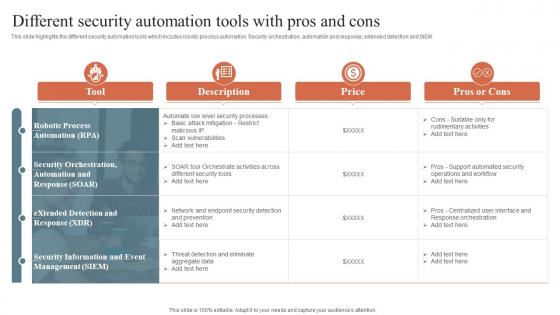
 Security Orchestration Automation Security Automation Integrates Tools Systems And Processes
Security Orchestration Automation Security Automation Integrates Tools Systems And ProcessesThis slide highlights the different security automation tools which incudes robotic process automation. Security orchestration, automation and response, extended detection and SIEM. Deliver an outstanding presentation on the topic using this Security Orchestration Automation Security Automation Integrates Tools Systems And Processes. Dispense information and present a thorough explanation of Security Automation, Robotic Process, Security Information using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
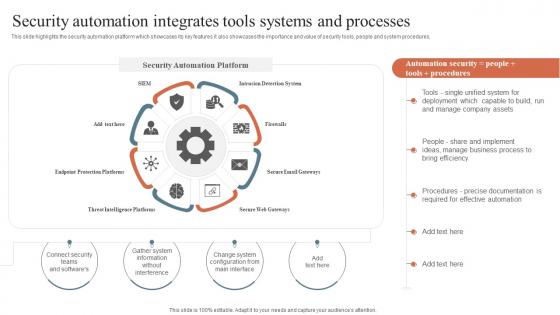
 Security Orchestration Automation And Response Different Security Automation Tools With Pros And Cons
Security Orchestration Automation And Response Different Security Automation Tools With Pros And ConsThis slide highlights the security automation platform which showcases its key features it also showcases the importance and value of security tools, people and system procedures. Introducing Security Orchestration Automation And Response Different Security Automation Tools With Pros And Cons to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Security Automation, Integrates Tools, Systems And Processes, using this template. Grab it now to reap its full benefits.
-
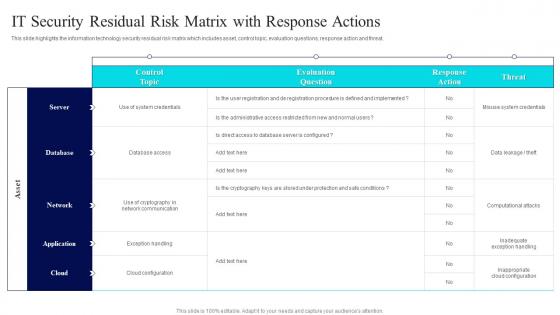 IT Security Residual Risk Matrix With Risk Management Guide For Information Technology Systems
IT Security Residual Risk Matrix With Risk Management Guide For Information Technology SystemsThis slide highlights the information technology security residual risk matrix which includes asset, control topic, evaluation questions, response action and threat. Deliver an outstanding presentation on the topic using this IT Security Residual Risk Matrix With Risk Management Guide For Information Technology Systems. Dispense information and present a thorough explanation of Database Access, Evaluation Question, Response Action using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
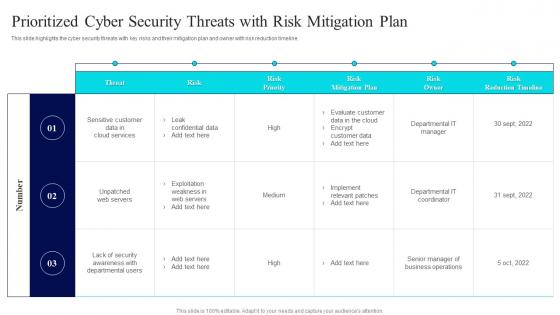 Prioritized Cyber Security Threats With Risk Risk Management Guide For Information Technology Systems
Prioritized Cyber Security Threats With Risk Risk Management Guide For Information Technology SystemsThis slide highlights the cyber security threats with key risks and their mitigation plan and owner with risk reduction timeline. Present the topic in a bit more detail with this Prioritized Cyber Security Threats With Risk Risk Management Guide For Information Technology Systems. Use it as a tool for discussion and navigation on Threat Risk, Risk Mitigation Plan, Risk Owner. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
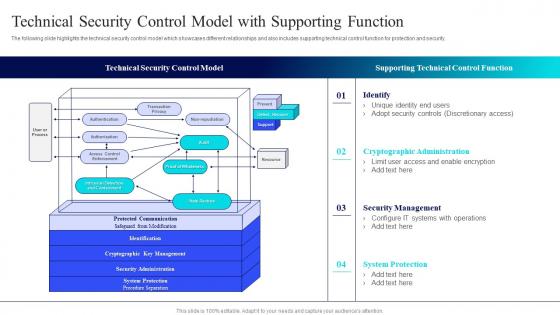 Technical Security Control Model With Isk Management Guide For Information Technology Systems
Technical Security Control Model With Isk Management Guide For Information Technology SystemsThe following slide highlights the technical security control model which showcases different relationships and also includes supporting technical control function for protection and security. Deliver an outstanding presentation on the topic using this Technical Security Control Model With Isk Management Guide For Information Technology Systems. Dispense information and present a thorough explanation of Technical Security, Control Model, Supporting Technical, Control Function using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
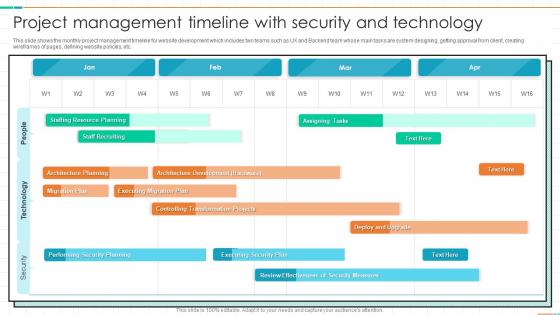 Project Management Timeline With Security And Technology
Project Management Timeline With Security And TechnologyThis slide shows the monthly project management timeline for website development which includes two teams such as UX and Backend team whose main tasks are system designing, getting approval from client, creating wireframes of pages, defining website policies, etc. Presenting our well structured Project Management Timeline With Security And Technology. The topics discussed in this slide are Security, Technology, People. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Cyber Security Elements IT Tools Used For Cyber Security Goals Ppt Brochure
Cyber Security Elements IT Tools Used For Cyber Security Goals Ppt BrochureThis slide outlines the tools used to achieve cyber security goals such as confidentiality, integrity, and availability. The tools for confidentiality include encryption, access control, authentication, authentication, authorization, and physical security. Increase audience engagement and knowledge by dispensing information using Cyber Security Elements IT Tools Used For Cyber Security Goals Ppt Brochure. This template helps you present information on one stage. You can also present information on Tools For Confidentiality, Tools For Integrity, Tools For Availability using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyber Security Risk Management Icon In Information Technology
Cyber Security Risk Management Icon In Information TechnologyPresent the topic in a bit more detail with this Cyber Security Risk Management Icon In Information Technology. Use it as a tool for discussion and navigation on Cyber Security, Risk Management, Icon In Information Technology. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
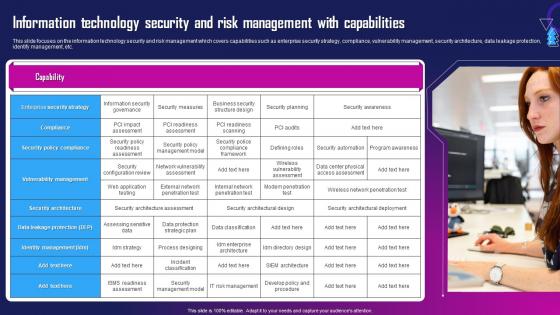 Information Technology Security And Risk Management With Capabilities
Information Technology Security And Risk Management With CapabilitiesThis slide focuses on the information technology security and risk management which covers capabilities such as enterprise security strategy, compliance, vulnerability management, security architecture, data leakage protection, identify management, etc. Deliver an outstanding presentation on the topic using this Information Technology Security And Risk Management With Capabilities. Dispense information and present a thorough explanation of Security Policy Compliance, Compliance, Enterprise Security Strategy using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Model For Information Technology Security Risk Management
Model For Information Technology Security Risk ManagementThis slide shows the model that depicts IT security risk management which focuses on identification, protection, detection, response and recovery planning with security asset management, governance, data security, detection processes, risk analysis and planning, etc. Introducing Model For Information Technology Security Risk Management to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Identifying, Protecting, Detecting, using this template. Grab it now to reap its full benefits.
-
 Risk Management Matrix For Information Technology Security
Risk Management Matrix For Information Technology SecurityThis slide shows the risk management matrix for information technology security which covers the business workflow and technical systems with IT risks and threats such as software security, business controls, control risk modelling, penetration testing, attack modelling, etc. Present the topic in a bit more detail with this Risk Management Matrix For Information Technology Security. Use it as a tool for discussion and navigation on Corporate Workflow, Risks, Threats. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Risk Management Methodology In Information Technology Security
Risk Management Methodology In Information Technology SecurityThis slide focuses on the risk management methodology in information technology security which includes three different phases such as assessment, mitigation and continual evaluation assessment that are helpful in effective management of security risks and hazards. Deliver an outstanding presentation on the topic using this Risk Management Methodology In Information Technology Security. Dispense information and present a thorough explanation of Assessment, Mitigation, Continual Evaluation Assessment using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Applications Of Security Technologies In Business Industry
Applications Of Security Technologies In Business IndustryThe following slide highlights security technology applications in business industry to protect system from malicious codes, virus attacks and block data from unreliable sources. It includes applications such as intrusive detection system, security incident and event management, firewall, antivirus and data loss prevention. Presenting our set of slides with Applications Of Security Technologies In Business Industry. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Security Incident And Event Management, Intrusive Detection System, Firewall.
-
 IOT Security Through Blockchain Technology
IOT Security Through Blockchain TechnologyThis slide covers steps for processing crypto currency transactions using block chain P2P technology. The purpose of this slide is to provide information on securing financial transactions. It includes steps from requesting transaction, transferring it on P2P network, validating transactions, creation of new data block, etc. Introducing our premium set of slides with IOT Security Through Blockchain Technology. Elucidate the seven stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like IOT Security Through, Blockchain Technology. So download instantly and tailor it with your information.
-
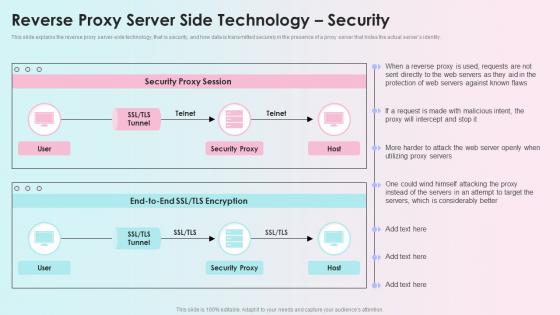 Reverse Proxy Server Side Technology Security Reverse Proxy Load Balancer Ppt Elements
Reverse Proxy Server Side Technology Security Reverse Proxy Load Balancer Ppt ElementsThis slide explains the reverse proxy server side technology, that is security, and how data is transmitted securely in the presence of a proxy server that hides the actual servers identity. Present the topic in a bit more detail with this Reverse Proxy Server Side Technology Security Reverse Proxy Load Balancer Ppt Elements. Use it as a tool for discussion and navigation on Security Proxy Session, Reverse Proxy Server, Technology Security. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Comparative Assessment Of Security Incident Management Tools
Comparative Assessment Of Security Incident Management ToolsPresenting our well structured Comparative Assessment Of Security Incident Management Tools. The topics discussed in this slide are Customized Workflows, User Friendly Interface, Threat Intelligence Integration. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Icon Showing Data Security Through Blockchain Technology In Supply Chain
Icon Showing Data Security Through Blockchain Technology In Supply ChainPresenting our well structured Icon Showing Data Security Through Blockchain Technology In Supply Chain. The topics discussed in this slide are Icon Showing Data Security, Blockchain Technology, Supply Chain. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.



