Powerpoint Templates and Google slides for Security Technology Roadmap
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Checklist To Improve Information Technology Security
Checklist To Improve Information Technology SecurityThis slide shows comprehensive checklist used to enhance information technology security. It includes email phishing training, anti virus and malware use, password changes etc. Presenting our set of slides with Checklist To Improve Information Technology Security. This exhibits information on one stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Change Passwords Frequently, Email Phishing Training, Regular Firewall Holes Checking.
-
 Information Technology Security Icon To Reduce Threats
Information Technology Security Icon To Reduce ThreatsIntroducing our premium set of slides with Information Technology Security Icon To Reduce Threats. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Information Technology Security Icon, Reduce Threats. So download instantly and tailor it with your information.
-
 Security Automation Tools With Functions And Cost
Security Automation Tools With Functions And CostThe following slide highlights various tools that can assist company to automate security process. The various tools could be Robotic process automation security orchestration, automation and response and extended detection Introducing our premium set of slides with Security Automation Tools With Functions And Cost. Elucidate the one stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Expected Cost, Key Functions. So download instantly and tailor it with your information.
-
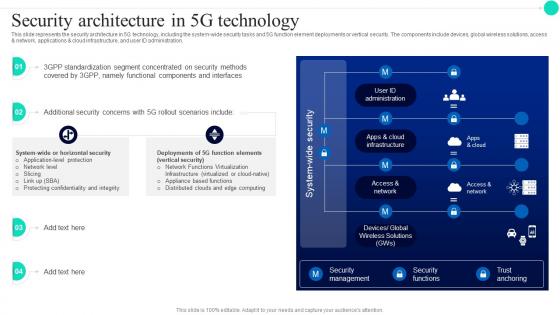 Security Architecture In 5G Technology Architecture And Functioning Of 5G
Security Architecture In 5G Technology Architecture And Functioning Of 5GThis slide represents the security architecture in 5G technology, including the system-wide security tasks and 5G function element deployments or vertical security. The components include devices, global wireless solutions, access and network, applications and cloud infrastructure, and user ID administration. Deliver an outstanding presentation on the topic using this Security Architecture In 5G Technology Architecture And Functioning Of 5G. Dispense information and present a thorough explanation of User ID Administration, Apps And Cloud Infrastructure, Access And Network using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Security In 5G Technology Architecture Architecture And Functioning Of 5G
Security In 5G Technology Architecture Architecture And Functioning Of 5GThis slide depicts the security in 5G architecture, including the standards detailed by 3GPP 3rd Generation Partnership Project, such as SUPI, unified authentication, extensible authentication standards, and flexible security policies. Present the topic in a bit more detail with this Security In 5G Technology Architecture Architecture And Functioning Of 5G. Use it as a tool for discussion and navigation on Service Delivery Process, Mobile Technologys, Security Procedures. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
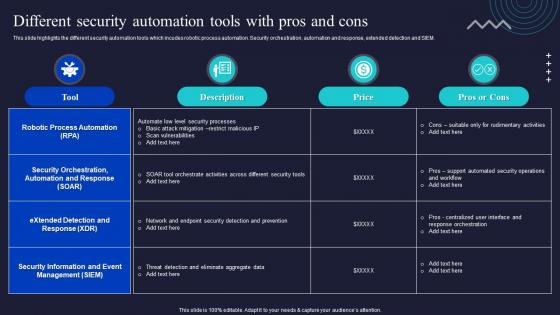 Different Security Automation Tools With Pros And Cons Enabling Automation In Cyber Security Operations
Different Security Automation Tools With Pros And Cons Enabling Automation In Cyber Security OperationsThis slide highlights the different security automation tools which incudes robotic process automation. Security orchestration, automation and response, extended detection and SIEM. Present the topic in a bit more detail with this Different Security Automation Tools With Pros And Cons Enabling Automation In Cyber Security Operations. Use it as a tool for discussion and navigation on Security Information, Management, Automation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
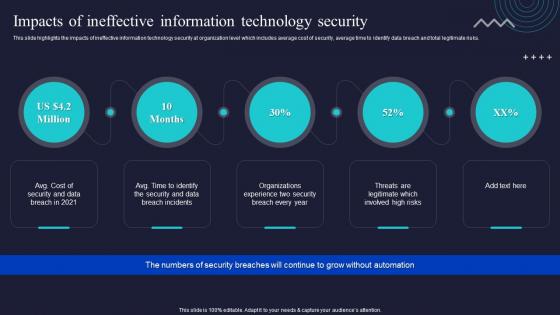 Impacts Of Ineffective Information Technology Security Enabling Automation In Cyber Security Operations
Impacts Of Ineffective Information Technology Security Enabling Automation In Cyber Security OperationsThis slide highlights the impacts of ineffective information technology security at organization level which includes average cost of security, average time to identify data breach and total legitimate risks. Increase audience engagement and knowledge by dispensing information using Impacts Of Ineffective Information Technology Security Enabling Automation In Cyber Security Operations. This template helps you present information on four stages. You can also present information on Ineffective, Information, Technology using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
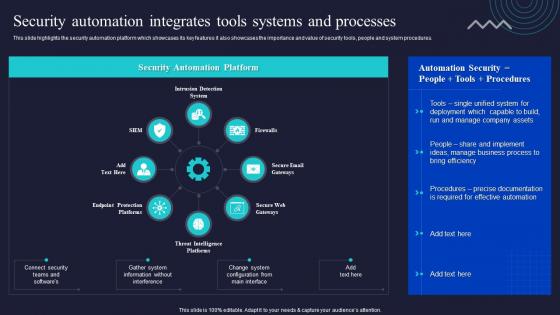 Security Automation Integrates Tools Systems And Processes Enabling Automation In Cyber Security Operations
Security Automation Integrates Tools Systems And Processes Enabling Automation In Cyber Security OperationsThis slide highlights the security automation platform which showcases its key features it also showcases the importance and value of security tools, people and system procedures. Present the topic in a bit more detail with this Security Automation Integrates Tools Systems And Processes Enabling Automation In Cyber Security Operations. Use it as a tool for discussion and navigation on Security Automation, Integrates, Processes. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
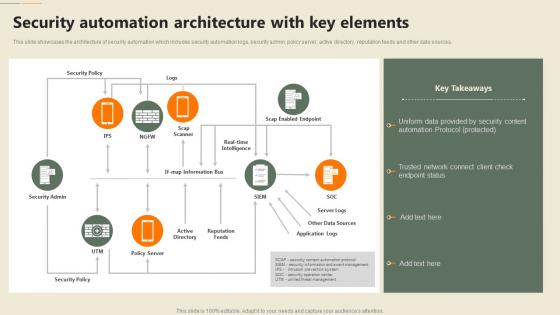 F651 Security Automation In Information Technology Security Automation Architecture With Key Elements
F651 Security Automation In Information Technology Security Automation Architecture With Key ElementsThis slide showcases the architecture of security automation which includes security automation logs, security admin, policy server, active directory, reputation feeds and other data sources. Present the topic in a bit more detail with this F651 Security Automation In Information Technology Security Automation Architecture With Key Elements. Use it as a tool for discussion and navigation on Security, Automation, Architecture. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
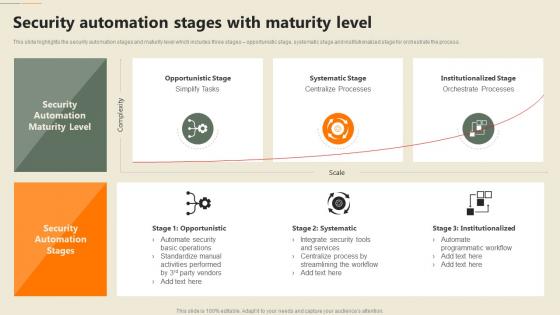 F653 Security Automation In Information Technology Security Automation Stages With Maturity Level
F653 Security Automation In Information Technology Security Automation Stages With Maturity LevelThis slide highlights the security automation stages and maturity level which includes three stages opportunistic stage, systematic stage and institutionalized stage for orchestrate the process. Present the topic in a bit more detail with this F653 Security Automation In Information Technology Security Automation Stages With Maturity Level. Use it as a tool for discussion and navigation on Systematic Stage, Institutionalized Stage, Opportunistic Stage. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
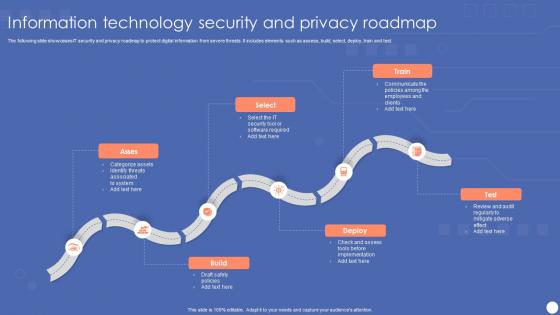 Information Technology Security And Privacy Roadmap
Information Technology Security And Privacy RoadmapThe following slide showcases IT security and privacy roadmap to protect digital information from severe threats. It includes elements such as assess, build, select, deploy, train and test. Introducing our premium set of slides with name Information Technology Security And Privacy Roadmap. Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Categorize Assets, Security Tool, Software Required. So download instantly and tailor it with your information.
-
 Security And Privacy Issues In Cloud Technology
Security And Privacy Issues In Cloud TechnologyThe following slide depicts some security and privacy concerns associated with clout network to meet compliance and protect individual interest. It includes elements such as underdeveloped saas safety, infrastructure, control etc. Introducing our premium set of slides with name Security And Privacy Issues In Cloud Technology. Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Underdeveloped Laas And Saas Security, Rapid Changes And Delivery, Responsibility Security Model. So download instantly and tailor it with your information.
-
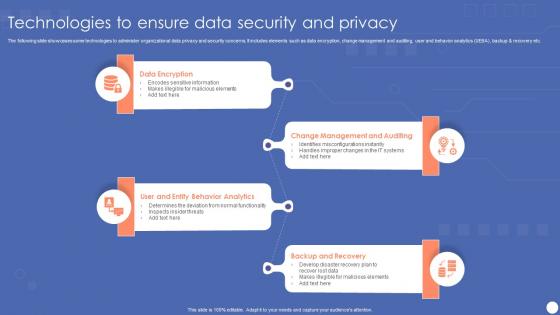 Technologies To Ensure Data Security And Privacy
Technologies To Ensure Data Security And PrivacyThe following slide showcases some technologies to administer organizational data privacy and security concerns. It includes elements such as data encryption, change management and auditing, user and behavior analytics UEBA, backup and recovery etc. Introducing our premium set of slides with name Technologies To Ensure Data Security And Privacy. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Data Encryption, Change Management And Auditing, Backup And Recovery. So download instantly and tailor it with your information.
-
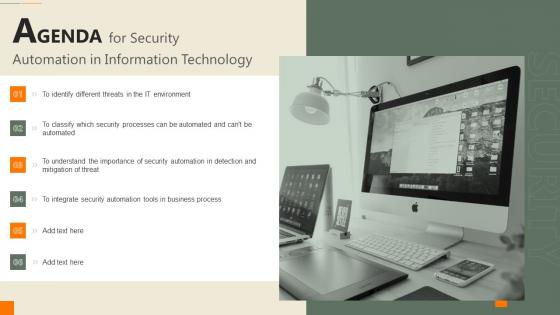 Agenda For Security Automation In Information Technology
Agenda For Security Automation In Information TechnologyIncrease audience engagement and knowledge by dispensing information using Agenda For Security Automation In Information Technology. This template helps you present information on six stages. You can also present information on Business, Process, Importance using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Determine Ideal Tasks For Security Automation Security Automation In Information Technology
Determine Ideal Tasks For Security Automation Security Automation In Information Technologyslide highlights which tasks and activities can be automated and which required human insights to detect and prevent security threat. It also covers key takeaways section. Present the topic in a bit more detail with this Determine Ideal Tasks For Security Automation Security Automation In Information Technology. Use it as a tool for discussion and navigation on Security Automation, Determine, Sensitive Tasks. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
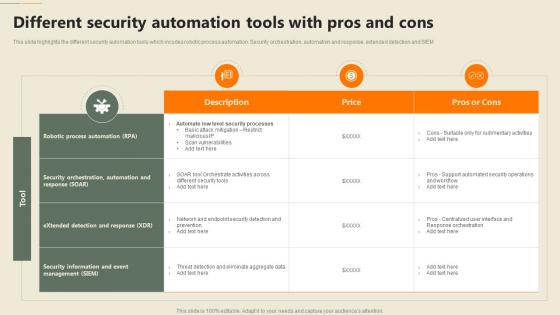 Different Security Automation Tools With Pros And Cons Security Automation In Information Technology
Different Security Automation Tools With Pros And Cons Security Automation In Information TechnologyThis slide highlights the different security automation tools which incudes robotic process automation. Security orchestration, automation and response, extended detection and SIEM Deliver an outstanding presentation on the topic using this Different Security Automation Tools With Pros And Cons Security Automation In Information Technology. Dispense information and present a thorough explanation of Automation, Security Orchestration, Process Automation using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
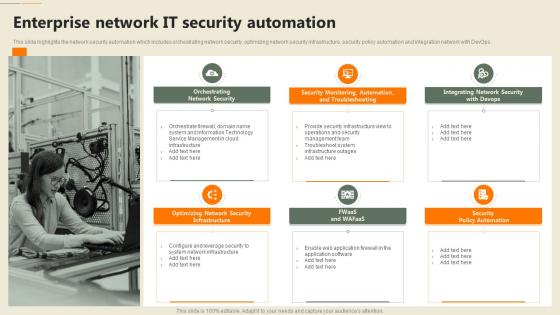 Enterprise Network It Security Automation Security Automation In Information Technology
Enterprise Network It Security Automation Security Automation In Information TechnologyThis slide highlights the network security automation which includes orchestrating network security, optimizing network security infrastructure, security policy automation and integration network with DevOps. Increase audience engagement and knowledge by dispensing information using Enterprise Network It Security Automation Security Automation In Information Technology. This template helps you present information on six stages. You can also present information on Orchestrating Network Security, Security Policy Automation, Infrastructure using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations
-
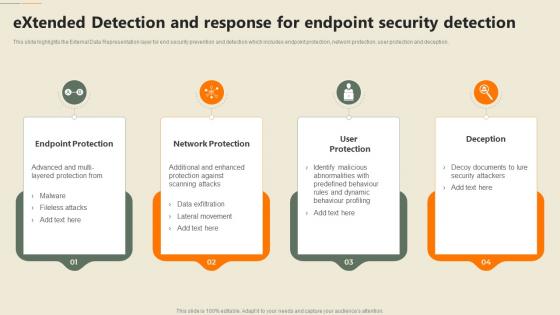 Extended Detection And Response For Endpoint Security Detection Security Automation In Information Technology
Extended Detection And Response For Endpoint Security Detection Security Automation In Information TechnologyThis slide highlights the External Data Representation layer for end security prevention and detection which includes endpoint protection, network protection, user protection and deception. Increase audience engagement and knowledge by dispensing information using Extended Detection And Response For Endpoint Security Detection Security Automation In Information Technology. This template helps you present information on four stages. You can also present information on Endpoint Protection, Network Protection, Deception using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Icons Slide Security Automation In Information Technology
Icons Slide Security Automation In Information TechnologyPresent the topic in a bit more detail with this Icons Slide Security Automation In Information Technology. Use it as a tool for discussion and navigation on Icons. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
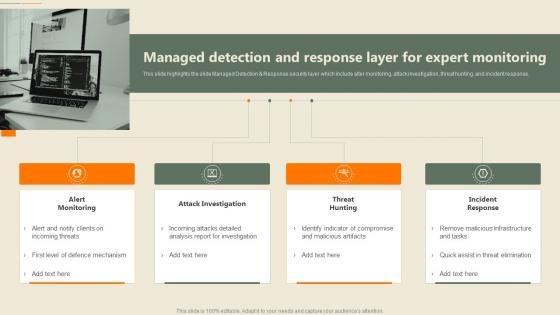 Managed Detection And Response Layer For Expert Monitoring Security Automation In Information Technology
Managed Detection And Response Layer For Expert Monitoring Security Automation In Information TechnologyThis slide highlights the slide Managed Detection and Response security layer which include alter monitoring, attack investigation, threat hunting, and incident response Increase audience engagement and knowledge by dispensing information using Managed Detection And Response Layer For Expert Monitoring Security Automation In Information Technology. This template helps you present information on four stages. You can also present information on Attack Investigation, Incident Response, Threat Hunting using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations
-
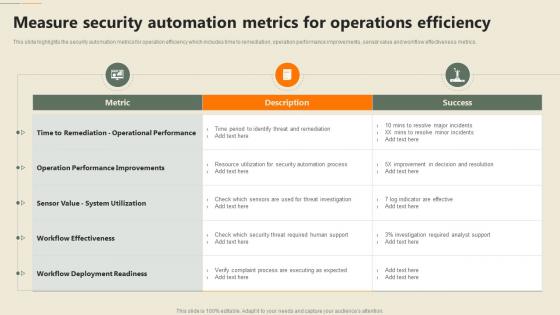 Measure Security Automation Metrics For Operations Efficiency Security Automation In Information Technology
Measure Security Automation Metrics For Operations Efficiency Security Automation In Information TechnologyThis slide highlights the security automation metrics for operation efficiency which includes time to remediation, operation performance improvements, sensor value and workflow effectiveness metrics. Present the topic in a bit more detail with this Measure Security Automation Metrics For Operations Efficiency Security Automation In Information Technology. Use it as a tool for discussion and navigation on Automation, Operations Efficiency, Performance Improvements. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
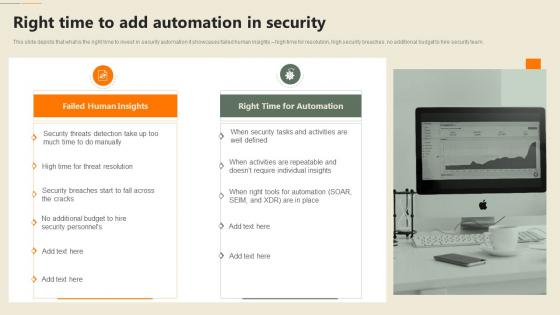 Right Time To Add Automation In Security Security Automation In Information Technology
Right Time To Add Automation In Security Security Automation In Information TechnologyThis slide depicts that what is the right time to invest in security automation it showcases failed human insights high time for resolution, high security breaches, no additional budget to hire security team. Deliver an outstanding presentation on the topic using this Right Time To Add Automation In Security Security Automation In Information Technology. Dispense information and present a thorough explanation of Individual, Insights, Automation using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
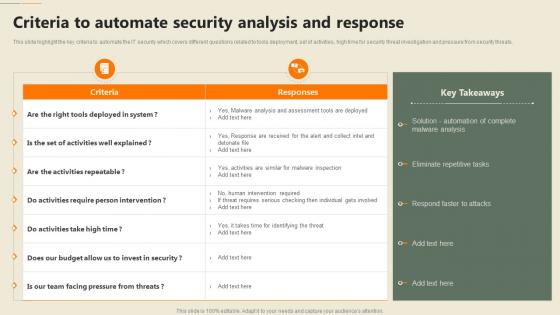 Security Automation In Information Technology Criteria To Automate Security Analysis And Response
Security Automation In Information Technology Criteria To Automate Security Analysis And ResponseThis slide highlight the key criteria to automate the IT security which covers different questions related to tools deployment, set of activities, high time for security threat investigation and pressure from security threats. Present the topic in a bit more detail with this Security Automation In Information Technology Criteria To Automate Security Analysis And Response. Use it as a tool for discussion and navigation on Analysis, Eliminate Repetitive Tasks, Respond Faster To Attacks. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Security Automation In Information Technology Impacts Of Ineffective Information Technology Security
Security Automation In Information Technology Impacts Of Ineffective Information Technology SecurityThis slide highlights the impacts of ineffective information technology security at organization level which includes average cost of security, average time to identify data breach and total legitimate risks. Increase audience engagement and knowledge by dispensing information using Security Automation In Information Technology Impacts Of Ineffective Information Technology Security. This template helps you present information on five stages. You can also present information on Information, Technology, Automation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations
-
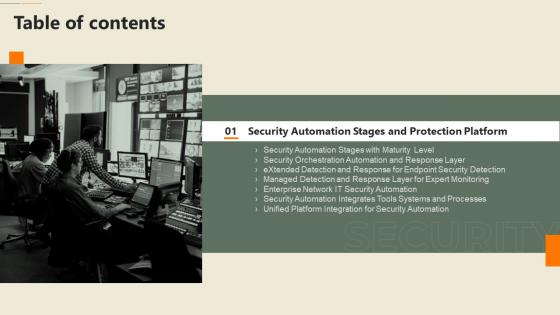 Security Automation In Information Technology Table Of Contents
Security Automation In Information Technology Table Of ContentsIncrease audience engagement and knowledge by dispensing information using Security Automation In Information Technology Table Of Contents. This template helps you present information on one stages. You can also present information on Security Automation, Processes, Security Detection using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations
-
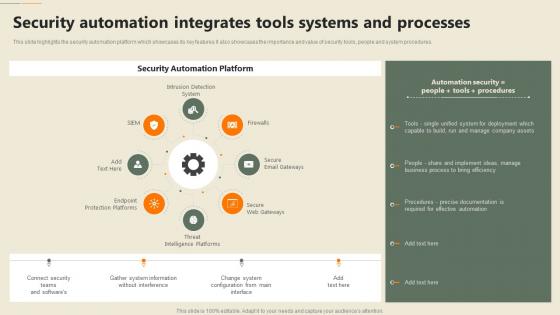 Security Automation Integrates Tools Systems And Processes Security Automation In Information Technology
Security Automation Integrates Tools Systems And Processes Security Automation In Information TechnologyThis slide highlights the security automation platform which showcases its key features it also showcases the importance and value of security tools, people and system procedures. Increase audience engagement and knowledge by dispensing information using Security Automation Integrates Tools Systems And Processes Security Automation In Information Technology. This template helps you present information on eight stages. You can also present information on Automation, Integrates, Processes using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations
-
 Security Processes That Cant Be Automated Security Automation In Information Technology
Security Processes That Cant Be Automated Security Automation In Information TechnologyThe following slide highlights the three processes of the security which cannot be automated which includes threat modeling, penetration testing and bug bounty program. Increase audience engagement and knowledge by dispensing information using Security Processes That Cant Be Automated Security Automation In Information Technology. This template helps you present information on three stages. You can also present information on Threat Modeling, Penetration Testing, Bug Bounty using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Table Of Contents Security Automation In Information Technology
Table Of Contents Security Automation In Information TechnologyPresent the topic in a bit more detail with this Table Of Contents Security Automation In Information Technology. Use it as a tool for discussion and navigation on Security Automation, Architecture And Importance, Automation Dashboards. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
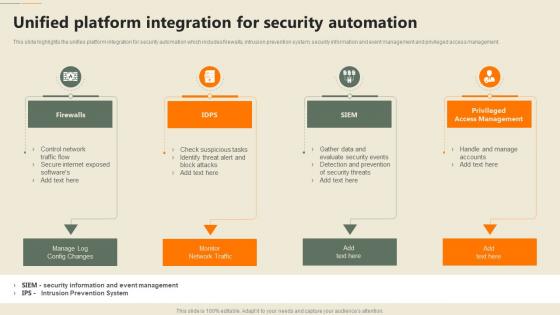 Unified Platform Integration For Security Automation Security Automation In Information Technology
Unified Platform Integration For Security Automation Security Automation In Information TechnologyThis slide highlights the unifies platform integration for security automation which includes firewalls, intrusion prevention system, security information and event management and privileged access management. Increase audience engagement and knowledge by dispensing information using Unified Platform Integration For Security Automation Security Automation In Information Technology. This template helps you present information on four stages. You can also present information on Access Management, Security Automation, Firewalls using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations
-
 Why To Automate The It Security Process Security Automation In Information Technology
Why To Automate The It Security Process Security Automation In Information TechnologyThis slide highlights the benefits or importance of automation security process which includes better threat detection, faster containment, improve productivity, admin role delegation and incident response. Increase audience engagement and knowledge by dispensing information using Why To Automate The It Security Process Security Automation In Information Technology. This template helps you present information on five stages. You can also present information on Better Threat Detection, Faster Containment, Improve Productivity using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
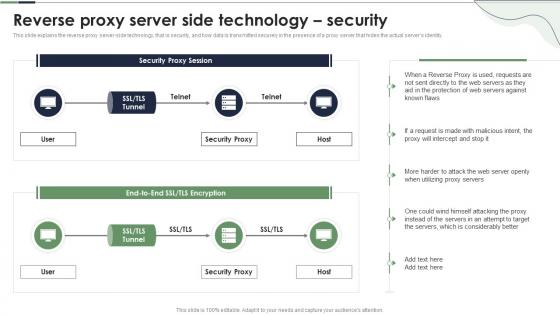 Reverse Proxy Server Side Technology Security Ppt Powerpoint Presentation Infographic Template Examples
Reverse Proxy Server Side Technology Security Ppt Powerpoint Presentation Infographic Template ExamplesThis slide explains the reverse proxy server side technology, that is security, and how data is transmitted securely in the presence of a proxy server that hides the actual servers identity. Present the topic in a bit more detail with this Reverse Proxy Server Side Technology Security Ppt Powerpoint Presentation Infographic Template Examples. Use it as a tool for discussion and navigation on Security Proxy, Reverse Proxy, Technology. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
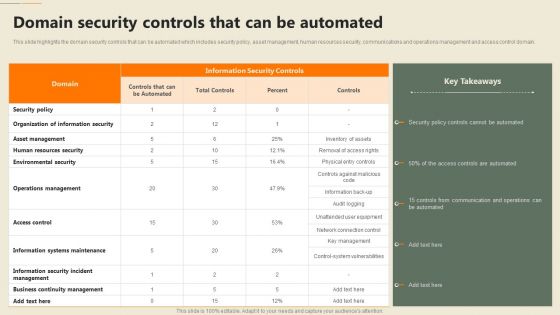 Security Automation In Information Technology Domain Security Controls That Can Be Automated
Security Automation In Information Technology Domain Security Controls That Can Be AutomatedThis slide highlights the domain security controls that can be automated which includes security policy, asset management, human resources security, communications and operations management and access control domain. Present the topic in a bit more detail with this Security Automation In Information Technology Domain Security Controls That Can Be Automated. Use it as a tool for discussion and navigation on Information Security, Organization, Operations Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
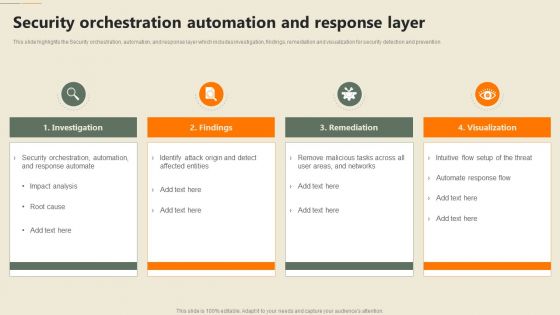 Security Automation In Information Technology Security Orchestration Automation And Response Layer
Security Automation In Information Technology Security Orchestration Automation And Response LayerThis slide highlights the Security orchestration, automation, and response layer which includes investigation, findings, remediation and visualization for security detection and prevention Increase audience engagement and knowledge by dispensing information using Security Automation In Information Technology Security Orchestration Automation And Response Layer. This template helps you present information on four stages. You can also present information on Investigation, Remediation, Visualization using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations
-
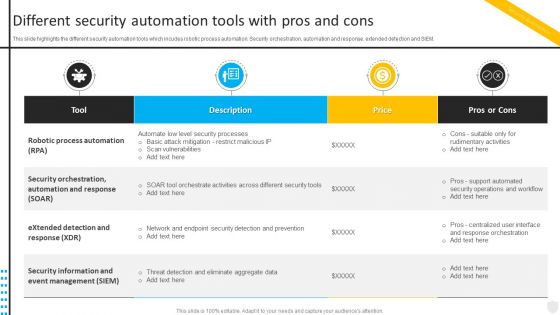 Different Security Automation Tools With Pros Security Automation To Investigate And Remediate Cyberthreats
Different Security Automation Tools With Pros Security Automation To Investigate And Remediate CyberthreatsThis slide highlights the different security automation tools which incudes robotic process automation. Security orchestration, automation and response, extended detection and SIEM. Present the topic in a bit more detail with this Different Security Automation Tools With Pros Security Automation To Investigate And Remediate Cyberthreats. Use it as a tool for discussion and navigation on Automation, Security Orchestration, Response. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
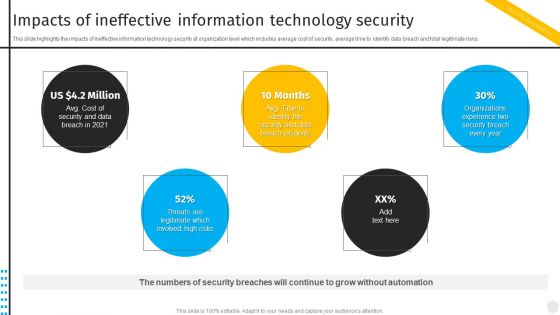 Impacts Of Ineffective Information Technology Security Automation To Investigate And Remediate Cyberthreats
Impacts Of Ineffective Information Technology Security Automation To Investigate And Remediate CyberthreatsThis slide highlights the impacts of ineffective information technology security at organization level which includes average cost of security, average time to identify data breach and total legitimate risks. Increase audience engagement and knowledge by dispensing information using Impacts Of Ineffective Information Technology Security Automation To Investigate And Remediate Cyberthreats. This template helps you present information on five stages. You can also present information on Ineffective, Information, Technology using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Security Automation Integrates Tools Systems And Security Automation To Investigate And Remediate Cyberthreats
Security Automation Integrates Tools Systems And Security Automation To Investigate And Remediate CyberthreatsThis slide highlights the security automation platform which showcases its key features it also showcases the importance and value of security tools, people and system procedures. Increase audience engagement and knowledge by dispensing information using Security Automation Integrates Tools Systems And Security Automation To Investigate And Remediate Cyberthreats. This template helps you present information on eight stages. You can also present information on Automation, Processes, System Procedures using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
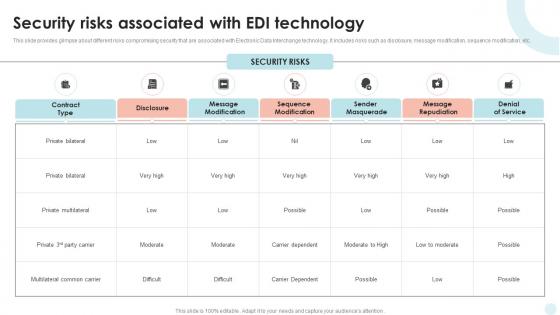 Security Risks Associated With EDI Technology
Security Risks Associated With EDI TechnologyThis slide provides glimpse about different risks compromising security that are associated with Electronic Data Interchange technology. It includes risks such as disclosure, message modification, sequence modification, etc. Introducing our Security Risks Associated With EDI Technology set of slides. The topics discussed in these slides are Security Risks Associated, EDI Technology. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
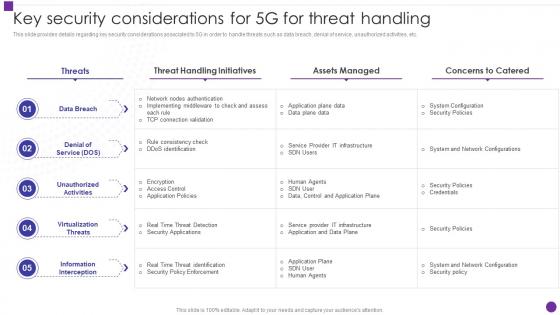 Key Security Considerations For 5g For Threat Handling Developing 5g Transformative Technology
Key Security Considerations For 5g For Threat Handling Developing 5g Transformative TechnologyThis slide provides details regarding key security considerations associated to 5G in order to handle threats such as data breach, denial of service, unauthorized activities, etc. Deliver an outstanding presentation on the topic using this Key Security Considerations For 5g For Threat Handling Developing 5g Transformative Technology. Dispense information and present a thorough explanation of Considerations, Unauthorized Activities, Unauthorized Activities using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Comparative Assessment Of Cyber Security Incident Response Tools
Comparative Assessment Of Cyber Security Incident Response ToolsThis slide covers comparative assessment of cyber security incident response tools. It involves features such as advanced threat hunting ability, net flow analysis, user behavior analytics and superior forensic analysis. Introducing our premium set of slides with name Comparative Assessment Of Cyber Security Incident Response Tools. Ellicudate the one stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Comparative Assessment, Cyber Security, Incident Response Tools. So download instantly and tailor it with your information.
-
 Applications Of Confidential Computing Security Technology
Applications Of Confidential Computing Security TechnologyThe following slide contains the area of benefits where confidential computing is used to ensure data is secured and encrypted against malware attacks. Key uses are data protection, guard business process, collaboration and customer satisfaction. Presenting our set of slides with name Applications Of Confidential Computing Security Technology. This exhibits information on four stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Data Protection, Guard Business Process, Collaboration, Customer Satisfaction.
-
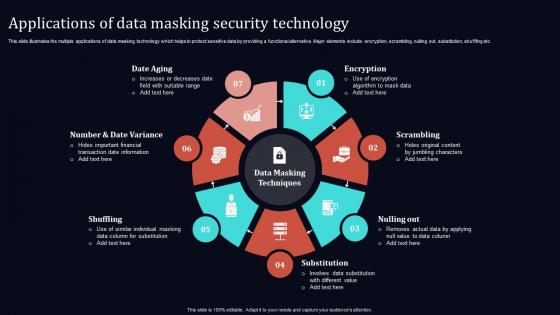 Applications Of Data Masking Security Technology
Applications Of Data Masking Security TechnologyThis slide illustrates the multiple applications of data masking technology which helps to protect sensitive data by providing a functional alternative. Major elements include encryption, scrambling, nulling out, substitution, shuffling etc. Introducing our premium set of slides with Applications Of Data Masking Security Technology. Elucidate the seven stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Date Aging, Encryption, Scrambling, Nulling Out, Substitution. So download instantly and tailor it with your information.
-
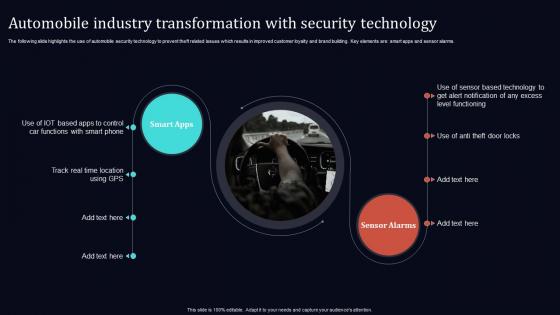 Automobile Industry Transformation With Security Technology
Automobile Industry Transformation With Security TechnologyThe following slide highlights the use of automobile security technology to prevent theft related issues which results in improved customer loyalty and brand building. Key elements are smart apps and sensor alarms. Introducing our Automobile Industry Transformation With Security Technology set of slides. The topics discussed in these slides are Smart Apps, Sensor Alarms. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
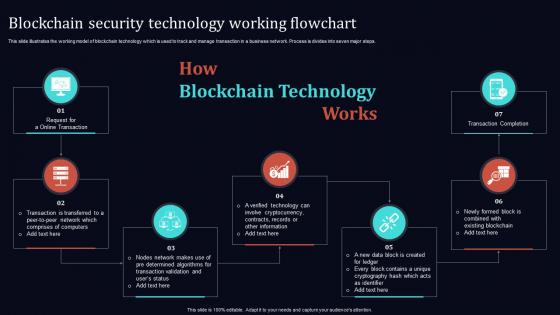 Blockchain Security Technology Working Flowchart
Blockchain Security Technology Working FlowchartThis slide illustrates the working model of blockchain technology which is used to track and manage transaction in a business network. Process is divides into seven major steps. Introducing our premium set of slides with Blockchain Security Technology Working Flowchart. Elucidate the seven stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Blockchain Security, Technology, Working Flowchart. So download instantly and tailor it with your information.
-
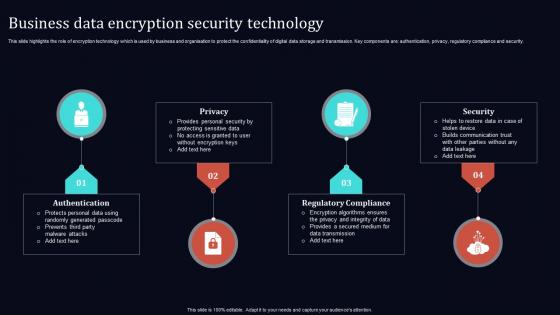 Business Data Encryption Security Technology
Business Data Encryption Security TechnologyThis slide highlights the role of encryption technology which is used by business and organisation to protect the confidentiality of digital data storage and transmission. Key components are authentication, privacy, regulatory compliance and security. Presenting our set of slides with name Business Data Encryption Security Technology. This exhibits information on four stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Privacy, Authentication, Regulatory Compliance, Security.
-
 Cloud Computing Security Technology Framework
Cloud Computing Security Technology FrameworkThis slide illustrates a strategic framework for cloud security technology which is used in various aspects of data and network protection. Key components are disaster recovery, governance, monitoring, user access management, data security etc. Introducing our premium set of slides with Cloud Computing Security Technology Framework. Elucidate the eight stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Data Security, Network Security, Others, Monitoring, Governance. So download instantly and tailor it with your information.
-
 Cloud Deployment Security Technology Icon
Cloud Deployment Security Technology IconPresenting our set of slides with name Cloud Deployment Security Technology Icon. This exhibits information on three stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cloud Deployment Security, Technology, Icon.
-
 Cyber Security Management Technology Framework
Cyber Security Management Technology FrameworkThis slide provides a strategic framework for cyber security management used by organisations to implement and monitor the essential activities. Key components are to identify, protect, detect, respond and recover. Introducing our premium set of slides with Cyber Security Management Technology Framework. Elucidate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Protect, Identify, Detect, Respond, Recover. So download instantly and tailor it with your information.
-
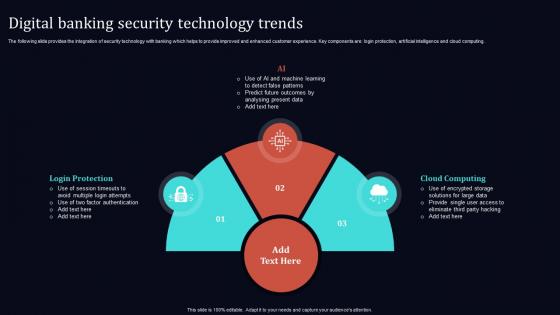 Digital Banking Security Technology Trends
Digital Banking Security Technology TrendsThe following slide provides the integration of security technology with banking which helps to provide improved and enhanced customer experience. Key components are login protection, artificial intelligence and cloud computing. Presenting our set of slides with name Digital Banking Security Technology Trends. This exhibits information on three stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Login Protection, Cloud Computing, AI.
-
 Firewall Data Network Security Technology
Firewall Data Network Security TechnologyThe below slide highlights the benefit of using firewall security technology to ensure the safe connection over internet. Key elements include packet filtering, proxy service, unified threat management UTM, stateful inspection and next-generation firewall. Introducing our premium set of slides with Firewall Data Network Security Technology. Elucidate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Packet Filtering, Proxy Service, UTM, Stateful Inspection, Next Gen Firewall. So download instantly and tailor it with your information.
-
 Information Technology Operations Security Icon
Information Technology Operations Security IconPresenting our set of slides with name Information Technology Operations Security Icon. This exhibits information on three stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Information Technology, Operations Security, Icon.
-
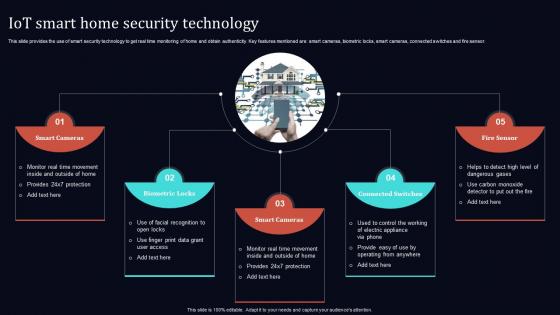 IOT Smart Home Security Technology
IOT Smart Home Security TechnologyThis slide provides the use of smart security technology to get real time monitoring of home and obtain authenticity. Key features mentioned are smart cameras, biometric locks, smart cameras, connected switches and fire sensor. Introducing our premium set of slides with IOT Smart Home Security Technology. Elucidate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Biometric Locks, Smart Cameras, Connected Switches, Fire Sensor. So download instantly and tailor it with your information.
-
 Mobile Application Security Technology Icon
Mobile Application Security Technology IconIntroducing our premium set of slides with Mobile Application Security Technology Icon. Elucidate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Mobile Application, Security, Technology, Icon. So download instantly and tailor it with your information.
-
 User Authentication And Authorization Security Technology
User Authentication And Authorization Security TechnologyThis slide provides the use of multiple authentication and authorization technology which are used to protect systems and user information. Key categories are password based, multi factor, certificate based, biometrics and token based. Presenting our set of slides with name User Authentication And Authorization Security Technology. This exhibits information on five stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Password Based, Multi Factor, Certificate Based, Biometrics, Token Based.
-
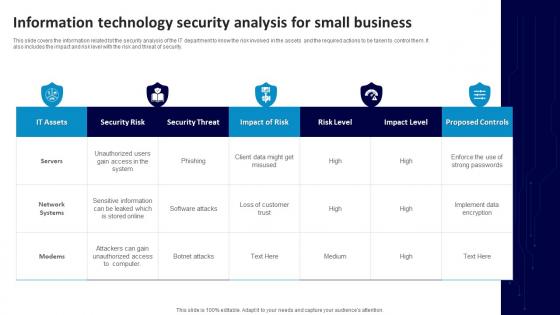 Information Technology Security Analysis For Small Business
Information Technology Security Analysis For Small BusinessThis slide covers the information related tot the security analysis of the IT department to know the risk involved in the assets and the required actions to be taken to control them. It also includes the impact and risk level with the risk and threat of security. Introducing our Information Technology Security Analysis For Small Business set of slides. The topics discussed in these slides are IT Assets, Security Risk, Security Threat. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
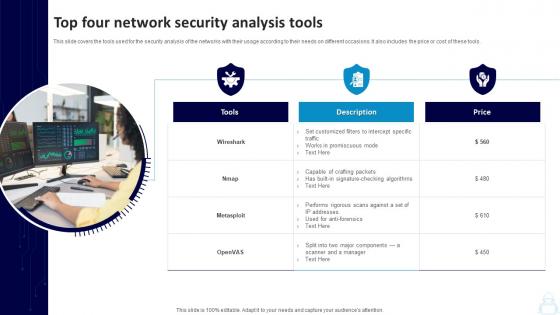 Top Four Network Security Analysis Tools
Top Four Network Security Analysis ToolsThis slide covers the tools used for the security analysis of the networks with their usage according to their needs on different occasions. It also includes the price or cost of these tools. Presenting our set of slides with Top Four Network Security Analysis Tools. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Tools, Price, Crafting Packets, Set Customized Filters.
-
 IOT Security Lock For Safe Fleet Management Using IOT Technologies For Better Logistics
IOT Security Lock For Safe Fleet Management Using IOT Technologies For Better LogisticsThe following slide illustrates internet of things IoT security lock for safe fleet management. It provides information about unlocking methods, Bluetooth, QR code, power saving, alarm notifications, large memory, etc. Present the topic in a bit more detail with this IOT Security Lock For Safe Fleet Management Using IOT Technologies For Better Logistics. Use it as a tool for discussion and navigation on Multiple Positioning, Multiple Alarm, Behavior Alarm. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
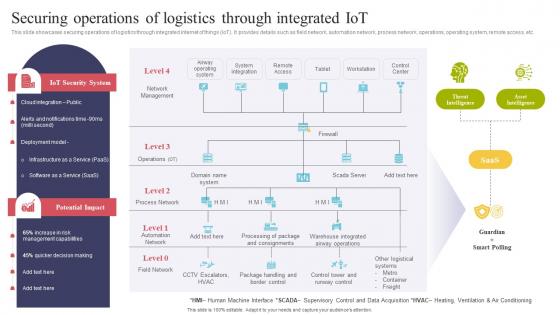 Securing Operations Of Logistics Through Integrated IOT Using IOT Technologies For Better Logistics
Securing Operations Of Logistics Through Integrated IOT Using IOT Technologies For Better LogisticsThis slide showcases securing operations of logistics through integrated internet of things IoT. It provides details such as field network, automation network, process network, operations, operating system, remote access, etc.Deliver an outstanding presentation on the topic using this Securing Operations Of Logistics Through Integrated IOT Using IOT Technologies For Better Logistics. Dispense information and present a thorough explanation of System Integration, Management Capabilities, Quicker Decision using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
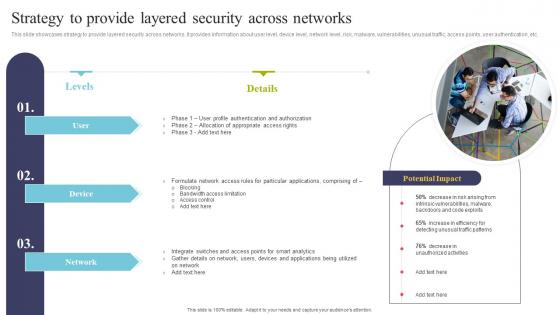 Strategy To Provide Layered Security Across Networks Using IOT Technologies For Better Logistics
Strategy To Provide Layered Security Across Networks Using IOT Technologies For Better LogisticsThis slide showcases strategy to provide layered security across networks. It provides information about user level, device level, network level, risk, malware, vulnerabilities, unusual traffic, access points, user authentication, etc. Present the topic in a bit more detail with this Strategy To Provide Layered Security Across Networks Using IOT Technologies For Better Logistics. Use it as a tool for discussion and navigation on Profile Authentication, Allocation Appropriate, Particular Applications. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
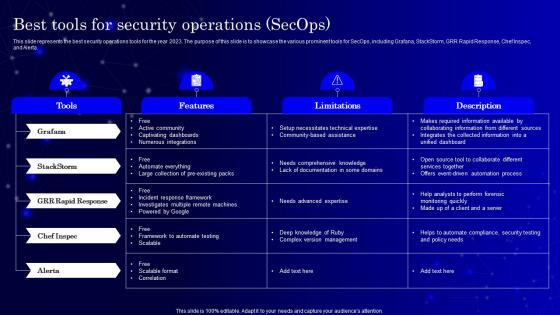 Best Tools For Security Operations Secops Ppt Powerpoint Presentation Diagram Templates
Best Tools For Security Operations Secops Ppt Powerpoint Presentation Diagram TemplatesThis slide represents the best security operations tools for the year 2023. The purpose of this slide is to showcase the various prominent tools for SecOps, including Grafana, StackStorm, GRR Rapid Response, Chef Inspec, and Alerta. Deliver an outstanding presentation on the topic using this Best Tools For Security Operations Secops Ppt Powerpoint Presentation Diagram Templates. Dispense information and present a thorough explanation of Grafana, Stackstorm using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
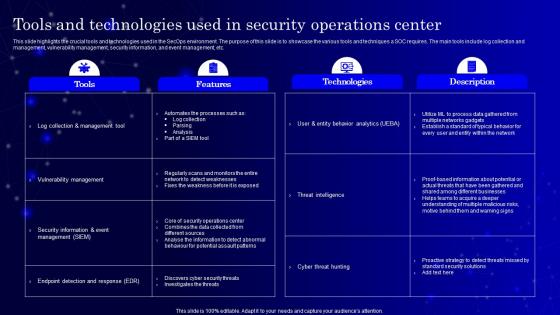 SecOps Tools And Technologies Used In Security Operations Center Ppt Summary
SecOps Tools And Technologies Used In Security Operations Center Ppt SummaryThis slide highlights the crucial tools and technologies used in the SecOps environment. The purpose of this slide is to showcase the various tools and techniques a SOC requires. The main tools include log collection and management, vulnerability management, security information, and event management, etc. Deliver an outstanding presentation on the topic using this SecOps Tools And Technologies Used In Security Operations Center Ppt Summary. Dispense information and present a thorough explanation of Features, Technologies, Description using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.



