Powerpoint Templates and Google slides for Security Threats
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Threat Identification And Vulnerability Assessment For Information System Security And Risk Administration Plan
Threat Identification And Vulnerability Assessment For Information System Security And Risk Administration PlanThis slide showcases identification of threat and assessment of vulnerability and can help organization to identify the information breach risk. Its key components are vulnerability, severity, threat, threat source, likelihood, impact and risk rating. Deliver an outstanding presentation on the topic using this Threat Identification And Vulnerability Assessment For Information System Security And Risk Administration Plan. Dispense information and present a thorough explanation of Vulnerability Severity, Threat Source, Risk Rating using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Security Threats Online Business In Powerpoint And Google Slides Cpb
Security Threats Online Business In Powerpoint And Google Slides CpbPresenting Security Threats Online Business In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Security Threats Online Business. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
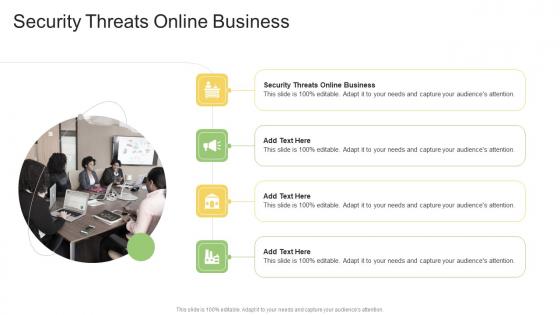
 Information System Security And Risk Administration Plan Identifying Information Security Threats And Impact
Information System Security And Risk Administration Plan Identifying Information Security Threats And ImpactThis slide showcases various threats that can be faced by organization and can result in financial plus reputational loss. It also showcases impact of threats on operational capability of organization. Increase audience engagement and knowledge by dispensing information using Information System Security And Risk Administration Plan Identifying Information Security Threats And Impact. This template helps you present information on one stages. You can also present information on Employee Sabotage, Physical Infrastructure Loss, Threats using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
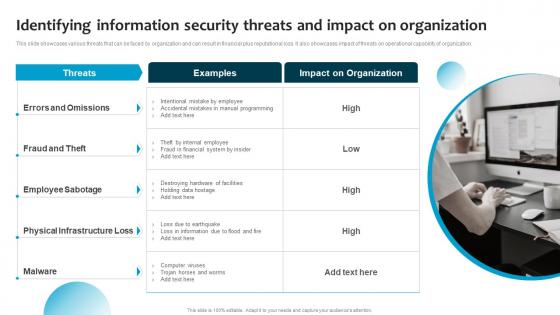
 Information System Security And Risk Administration Risk Assessment Matrix With Vulnerability And Threat Level
Information System Security And Risk Administration Risk Assessment Matrix With Vulnerability And Threat LevelThis slide showcases assessment matrix to identify risk associated with different class of information assets. It calculates severity of risk on the basis of threat and vulnerability level. Present the topic in a bit more detail with this Information System Security And Risk Administration Risk Assessment Matrix With Vulnerability And Threat Level. Use it as a tool for discussion and navigation on Treat Level, Vulnerability Level, Risk Assessment Matrix. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Security Threats Cases In Powerpoint And Google Slides Cpb
Security Threats Cases In Powerpoint And Google Slides CpbPresenting our Security Threats Cases In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Security Threats Cases This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 It Security Threat And Weakness Analysis
It Security Threat And Weakness AnalysisThe following slide highlights the IT security assessment to verify the safety status of assets and networks. It includes elements such as threats, weakness, impact and level of risk, current and proposed controls etc. Introducing our premium set of slides with It Security Threat And Weakness Analysis. Ellicudate the one stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Risk, Threats, Weakness. So download instantly and tailor it with your information.
-
 Threat Mitigation Strategies Required Network Security In Powerpoint And Google Slides Cpb
Threat Mitigation Strategies Required Network Security In Powerpoint And Google Slides CpbPresenting our Threat Mitigation Strategies Required Network Security In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Threat Mitigation Strategies Required Network Security This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Security Threats Ecommerce In Powerpoint And Google Slides Cpb
Security Threats Ecommerce In Powerpoint And Google Slides CpbPresenting our Security Threats Ecommerce In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases six stages. It is useful to share insightful information on Security Threats Ecommerce This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
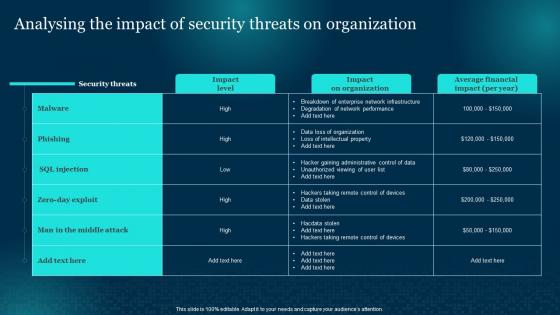 Cybersecurity Risk Analysis And Management Plan Analysing The Impact Of Security Threats
Cybersecurity Risk Analysis And Management Plan Analysing The Impact Of Security ThreatsPresent the topic in a bit more detail with this Cybersecurity Risk Analysis And Management Plan Analysing The Impact Of Security Threats. Use it as a tool for discussion and navigation on Analysing, Organization, Security Threats. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Identifying Information Security Threats And Impact Cybersecurity Risk Analysis And Management Plan
Identifying Information Security Threats And Impact Cybersecurity Risk Analysis And Management PlanThis slide showcases various threats that can be faced by organization and can result in financial plus reputational loss. It also showcases impact of threats on operational capability of organization Present the topic in a bit more detail with this Identifying Information Security Threats And Impact Cybersecurity Risk Analysis And Management Plan. Use it as a tool for discussion and navigation on Identifying, Information, Organization. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
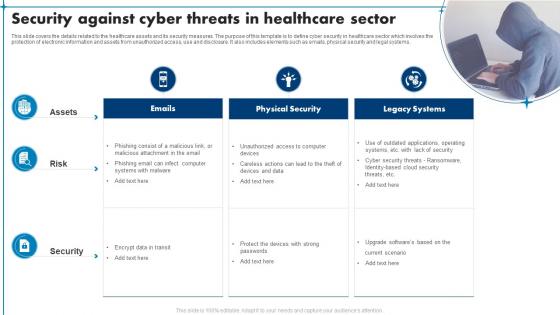 Security Against Cyber Threats In Healthcare Sector
Security Against Cyber Threats In Healthcare SectorThis slide covers the details related to the healthcare assets and its security measures. The purpose of this template is to define cyber security in healthcare sector which involves the protection of electronic information and assets from unauthorized access, use and disclosure. It also includes elements such as emails, physical security and legal systems. Introducing our premium set of slides with name Security Against Cyber Threats In Healthcare Sector. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Emails, Physical Security, Legacy Systems. So download instantly and tailor it with your information.
-
 Security Threats Commerce Attacking Methods In Powerpoint And Google Slides Cpb
Security Threats Commerce Attacking Methods In Powerpoint And Google Slides CpbPresenting Security Threats Commerce Attacking Methods In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase five stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Security Threats Commerce Attacking Methods. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Commerce Security Threats In Powerpoint And Google Slides Cpb
Commerce Security Threats In Powerpoint And Google Slides CpbPresenting our Commerce Security Threats In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Commerce Security Threats. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Analysing The Impact Of Security Threats On Organization Formulating Cybersecurity Plan
Analysing The Impact Of Security Threats On Organization Formulating Cybersecurity PlanPresent the topic in a bit more detail with this Analysing The Impact Of Security Threats On Organization Formulating Cybersecurity Plan. Use it as a tool for discussion and navigation on Organization, Average Financial, Analysing. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Identifying Information Security Threats And Impact Formulating Cybersecurity Plan
Identifying Information Security Threats And Impact Formulating Cybersecurity PlanThis slide showcases various threats that can be faced by organization and can result in financial plus reputational loss. It also showcases impact of threats on operational capability of organization. Introducing Identifying Information Security Threats And Impact Formulating Cybersecurity Plan to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Errors And Omissions, Fraud And Theft, Employee Sabotage, using this template. Grab it now to reap its full benefits.
-
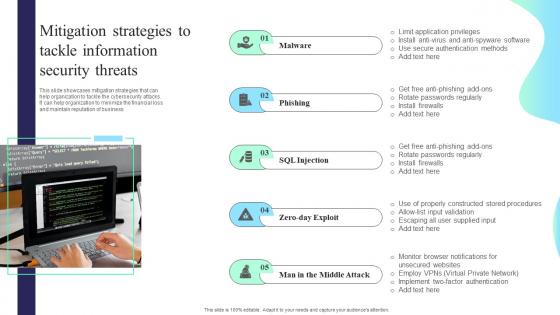 Mitigation Strategies To Tackle Information Security Threats Formulating Cybersecurity Plan
Mitigation Strategies To Tackle Information Security Threats Formulating Cybersecurity PlanThis slide showcases mitigation strategies that can help organization to tackle the cybersecurity attacks. It can help organization to minimize the financial loss and maintain reputation of business. Increase audience engagement and knowledge by dispensing information using Mitigation Strategies To Tackle Information Security Threats Formulating Cybersecurity Plan. This template helps you present information on five stages. You can also present information on Malware, Phishing, Mitigation Strategies using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 New Cyber Security Threats In Powerpoint And Google Slides Cpb
New Cyber Security Threats In Powerpoint And Google Slides CpbPresenting our New Cyber Security Threats In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases five stages. It is useful to share insightful information on New Cyber Security Threats This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Insider Threats Information Security In Powerpoint And Google Slides Cpb
Insider Threats Information Security In Powerpoint And Google Slides CpbPresenting our Insider Threats Information Security In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Insider Threats Information Security. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Cyber Security Checklist To Mitigate Threats Of Attack
Cyber Security Checklist To Mitigate Threats Of AttackThe given slide provides the key activities to be done to alleviate the effects of cyber threats. It includes managing social media profiles, backing up the data, crosschecking privacy and security settings etc. Introducing our premium set of slides with Cyber Security Checklist To Mitigate Threats Of Attack. Ellicudate the seven stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cyber Security Checklist, Mitigate Threats Attack. So download instantly and tailor it with your information.
-
 E Security Steps To Mitigate Cyber Threats
E Security Steps To Mitigate Cyber ThreatsThis slide mentions the e-security steps implemented to mitigate cyber threats and protect user data. It includes using strong password, device protection, additional authentication, storing essential data and reviewing third party integrations. Introducing our premium set of slides with E Security Steps To Mitigate Cyber Threats. Elucidate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Additional Authentication, Device Protection, Store Essential Data. So download instantly and tailor it with your information.
-
 E Security Threats And Solutions For Ecommerce Business
E Security Threats And Solutions For Ecommerce BusinessThis slide mentions Esecurity threats and solutions for ecommerce business to ensure protection from cyber attacks. The basis include financial frauds, phishing, DdoS attacks and brute force attacks. Presenting our well structured E Security Threats And Solutions For Ecommerce Business. The topics discussed in this slide are Financial Frauds, Phishing, Brute Force Attacks. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
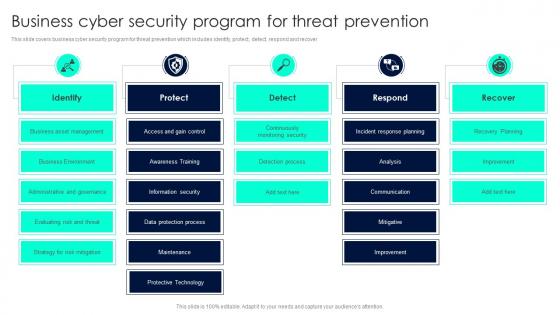 Business Cyber Security Program For Threat Prevention
Business Cyber Security Program For Threat PreventionThis slide covers business cyber security program for threat prevention which includes identify, protect, detect, respond and recover. Presenting our well structured Business Cyber Security Program For Threat Prevention. The topics discussed in this slide are Business Cyber, Security Program, Threat Prevention. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
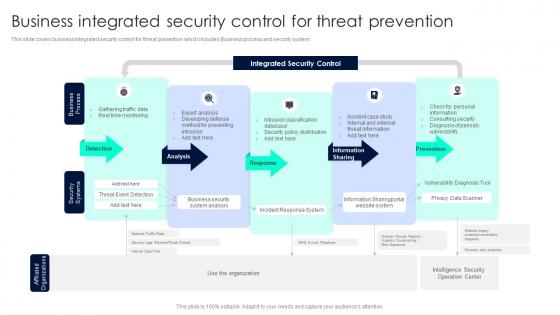 Business Integrated Security Control For Threat Prevention
Business Integrated Security Control For Threat PreventionThis slide covers business integrated security control for threat prevention which includes Business process and security system. Introducing our Business Integrated Security Control For Threat Prevention set of slides. The topics discussed in these slides are Integrated Security, Detection, Analysis. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
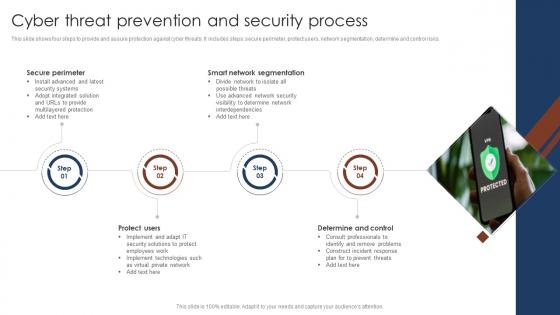 Cyber Threat Prevention And Security Process
Cyber Threat Prevention And Security ProcessThis slide shows four steps to provide and assure protection against cyber threats. It includes steps secure perimeter, protect users, network segmentation, determine and control risks. Introducing our premium set of slides with name Cyber Threat Prevention And Security Process. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Secure Perimeter, Smart Network Segmentation, Determine And Control. So download instantly and tailor it with your information.
-
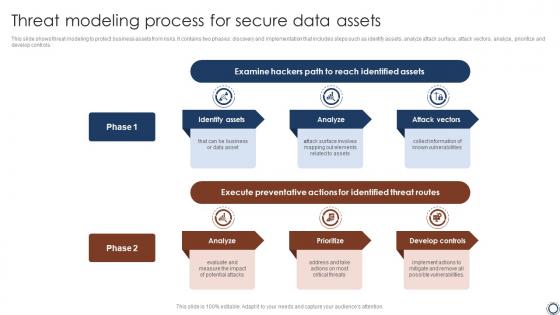 Threat Modeling Process For Secure Data Assets
Threat Modeling Process For Secure Data AssetsThis slide shows threat modeling to protect business assets from risks. It contains two phases discovery and implementation that includes steps such as identify assets, analyze attack surface, attack vectors, analyze, prioritize and develop controls. Introducing our premium set of slides with name Threat Modeling Process For Secure Data Assets. Ellicudate the two stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Hackers Path, Identified Assets, Threat Routes. So download instantly and tailor it with your information.
-
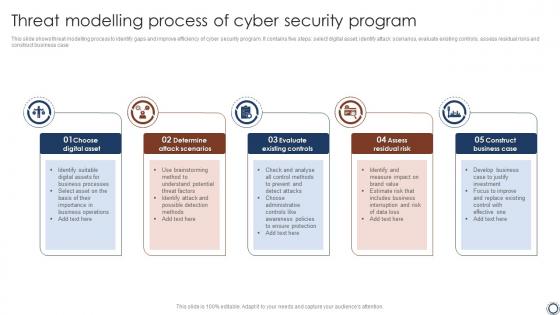 Threat Modelling Process Of Cyber Security Program
Threat Modelling Process Of Cyber Security ProgramThis slide shows threat modelling process to identify gaps and improve efficiency of cyber security program. It contains five steps select digital asset, identify attack scenarios, evaluate existing controls, assess residual risks and construct business case. Presenting our set of slides with name Threat Modelling Process Of Cyber Security Program. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Threat Modelling, Cyber Security, Assess Residual Risk .
-
 Four Workplace Safety And Security Threats
Four Workplace Safety And Security ThreatsThis slide shows the types of workplace security threats. It includes theft, IT failure, cyber attacks and supply chain disruption. Presenting our set of slides with Four Workplace Safety And Security Threats. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Physical Or Intellectual Assets Theft, Cctvs Installation, Communication Network.
-
 Emerging Cyber Security Threats In Powerpoint And Google Slides Cpb
Emerging Cyber Security Threats In Powerpoint And Google Slides CpbPresenting Emerging Cyber Security Threats In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Emerging Cyber Security Threats. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
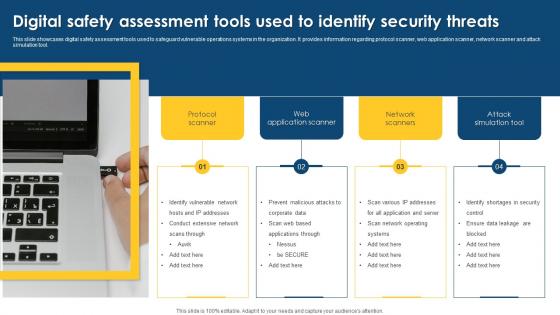 Digital Safety Assessment Tools Used To Identify Security Threats
Digital Safety Assessment Tools Used To Identify Security ThreatsThis slide showcases digital safety assessment tools used to safeguard vulnerable operations systems in the organization. It provides information regarding protocol scanner, web application scanner, network scanner and attack simulation tool. Presenting our well structured Digital Safety Assessment Tools Used To Identify Security Threats. The topics discussed in this slide are Assessment, Application, Identify Vulnerable. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 IT Risk Management Strategies Prioritized Cyber Security Threats With Risk Mitigation Plan
IT Risk Management Strategies Prioritized Cyber Security Threats With Risk Mitigation PlanThis slide highlights the cyber security threats with key risks and their mitigation plan and owner with risk reduction timeline. Increase audience engagement and knowledge by dispensing information using IT Risk Management Strategies Prioritized Cyber Security Threats With Risk Mitigation Plan. This template helps you present information on one stages. You can also present information on Threat, Risk, Risk Priority, Risk Reduction Timeline using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
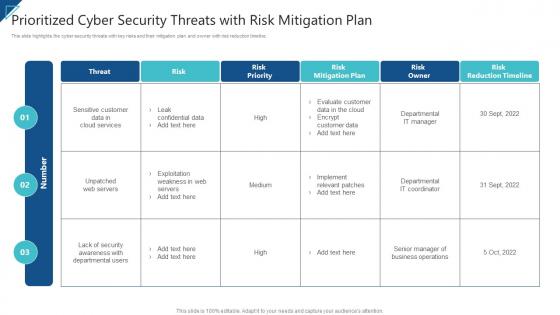 Enterprise Risk Management Prioritized Cyber Security Threats With Risk Mitigation Plan
Enterprise Risk Management Prioritized Cyber Security Threats With Risk Mitigation PlanThis slide highlights the cyber security threats with key risks and their mitigation plan and owner with risk reduction timeline. Present the topic in a bit more detail with this Enterprise Risk Management Prioritized Cyber Security Threats With Risk Mitigation Plan. Use it as a tool for discussion and navigation on Threat, Risk, Risk Priority, Risk Reduction Timeline. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Security Threats Challenges In Powerpoint And Google Slides Cpb
Cyber Security Threats Challenges In Powerpoint And Google Slides CpbPresenting Cyber Security Threats Challenges In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Cyber Security Threats Challenges. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
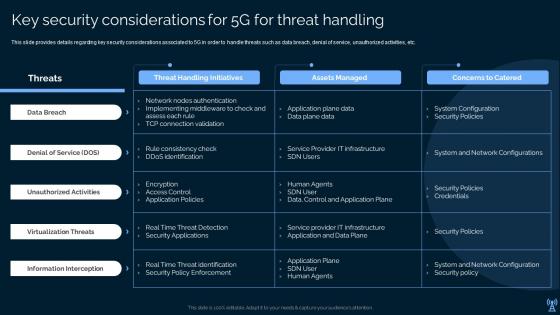 Key Security Considerations For 5g For Threat Handling Leading And Preparing For 5g World
Key Security Considerations For 5g For Threat Handling Leading And Preparing For 5g WorldPresent the topic in a bit more detail with this Key Security Considerations For 5g For Threat Handling Leading And Preparing For 5g World. Use it as a tool for discussion and navigation on Data Breach, Denial Of Service, Unauthorized Activities . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Checklist To Ensure Asset Protection From Internal Threats Security Incident Response Playbook
Checklist To Ensure Asset Protection From Internal Threats Security Incident Response PlaybookFollowing slide displays checklist having security control measures that can be used by members to ensure the safety of companys assets from any insider threat. Deliver an outstanding presentation on the topic using this Checklist To Ensure Asset Protection From Internal Threats Security Incident Response Playbook. Dispense information and present a thorough explanation of Protection, Measures, Ensure using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Threat Facts Figures And Statistics Security Incident Response Playbook
Cyber Threat Facts Figures And Statistics Security Incident Response PlaybookThis slide portrays statistical information about cyber threats. Information covered is related data breach, ransomware attacks, cyberthreat complaints and phishing attack. Increase audience engagement and knowledge by dispensing information using Cyber Threat Facts Figures And Statistics Security Incident Response Playbook. This template helps you present information on six stages. You can also present information on Cyberattacks, Ransomware, Statistics using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyber Security Threats In Powerpoint And Google Slides Cpb
Cyber Security Threats In Powerpoint And Google Slides CpbPresenting our Cyber Security Threats In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases five stages. It is useful to share insightful information on Cyber Security Threats This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
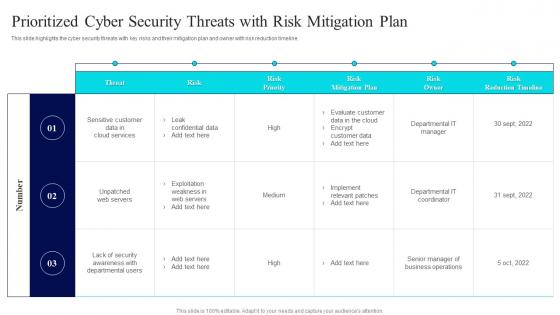 Prioritized Cyber Security Threats With Risk Risk Management Guide For Information Technology Systems
Prioritized Cyber Security Threats With Risk Risk Management Guide For Information Technology SystemsThis slide highlights the cyber security threats with key risks and their mitigation plan and owner with risk reduction timeline. Present the topic in a bit more detail with this Prioritized Cyber Security Threats With Risk Risk Management Guide For Information Technology Systems. Use it as a tool for discussion and navigation on Threat Risk, Risk Mitigation Plan, Risk Owner. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Major Types Of E Banking Security Threats E Banking Management And Services
Major Types Of E Banking Security Threats E Banking Management And ServicesThis slide represents types of e banking security threats. It includes brute force, phishing, pharming, cross site scripting and trojan horse. Present the topic in a bit more detail with this Major Types Of E Banking Security Threats E Banking Management And Services. Use it as a tool for discussion and navigation on Pharming, Mitigation Strategies, E Banking Security Threats. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Future Cyber Security Threats In Powerpoint And Google Slides Cpb
Future Cyber Security Threats In Powerpoint And Google Slides CpbPresenting Future Cyber Security Threats In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase five stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Future Cyber Security Threats. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Information Technology Security Icon To Reduce Threats
Information Technology Security Icon To Reduce ThreatsIntroducing our premium set of slides with Information Technology Security Icon To Reduce Threats. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Information Technology Security Icon, Reduce Threats. So download instantly and tailor it with your information.
-
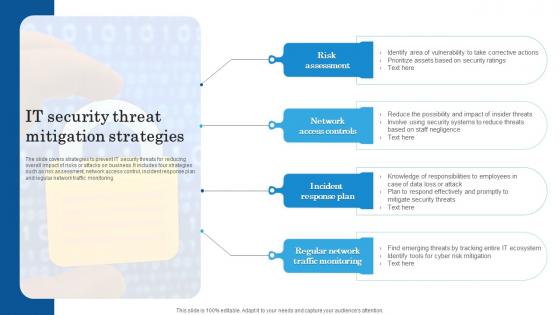 IT Security Threat Mitigation Strategies
IT Security Threat Mitigation StrategiesThe slide covers strategies to prevent IT security threats for reducing overall impact of risks or attacks on business. It includes four strategies such as risk assessment, network access control, incident response plan and regular network traffic monitoring Introducing our premium set of slides with IT Security Threat Mitigation Strategies. Elucidate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Risk Assessment, Network Access Controls, Incident Response Plan, Regular Network Traffic Monitoring. So download instantly and tailor it with your information.
-
 B132 Table Of Contents For Enterprise Mobile Security For On Device Threat Detection
B132 Table Of Contents For Enterprise Mobile Security For On Device Threat DetectionIntroducing B132 Table Of Contents For Enterprise Mobile Security For On Device Threat Detection to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispence information on Determine Standard, Various Configuration, Features Associated, using this template. Grab it now to reap its full benefits.
-
 Icons Slide For Enterprise Mobile Security For On Device Threat Detection
Icons Slide For Enterprise Mobile Security For On Device Threat DetectionPresenting our well crafted Icons Slide For Enterprise Mobile Security For On Device Threat Detection set of slides. The slides include icons that are innovatively designed by our team of experts. The icons are easy to edit so you can conveniently increase or decrease their size without any loss in resolution. Therefore, grab them instantly
-
 Table Of Contents For Enterprise Mobile Security For On Device Threat Detection
Table Of Contents For Enterprise Mobile Security For On Device Threat DetectionPresent the topic in a bit more detail with this Table Of Contents For Enterprise Mobile Security For On Device Threat Detection. Use it as a tool for discussion and navigation on Impact Assessment, Dashboard Assessment, Device Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Prioritized Cyber Security Threats With Risk Mitigation Plan Risk Assessment Of It Systems
Prioritized Cyber Security Threats With Risk Mitigation Plan Risk Assessment Of It SystemsThis slide highlights the cyber security threats with key risks and their mitigation plan and owner with risk reduction timeline. Present the topic in a bit more detail with this Prioritized Cyber Security Threats With Risk Mitigation Plan Risk Assessment Of It Systems. Use it as a tool for discussion and navigation on Mitigation Plan, Prioritized, Security Threats. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data Security Threats Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Data Security Threats Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Data security threats colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Data Security Threats Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Data Security Threats Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Data security threats monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
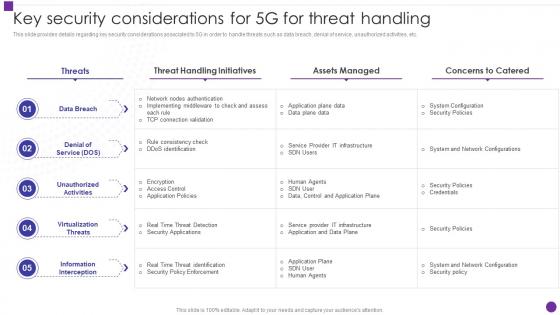 Key Security Considerations For 5g For Threat Handling Developing 5g Transformative Technology
Key Security Considerations For 5g For Threat Handling Developing 5g Transformative TechnologyThis slide provides details regarding key security considerations associated to 5G in order to handle threats such as data breach, denial of service, unauthorized activities, etc. Deliver an outstanding presentation on the topic using this Key Security Considerations For 5g For Threat Handling Developing 5g Transformative Technology. Dispense information and present a thorough explanation of Considerations, Unauthorized Activities, Unauthorized Activities using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
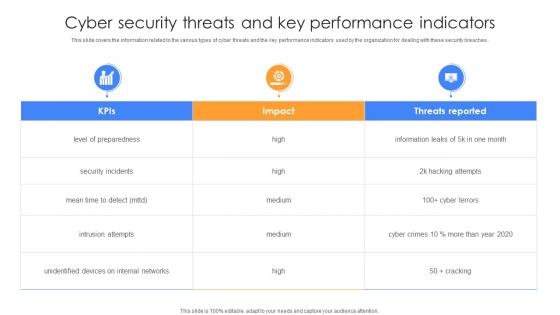 Cyber Security Threats And Key Performance Indicators
Cyber Security Threats And Key Performance IndicatorsThis slide covers the information related to the various types of cyber threats and the key performance indicators used by the organization for dealing with these security breaches. Introducing our Cyber Security Threats And Key Performance Indicators set of slides. The topics discussed in these slides are Security Incidents, Intrusion Attempts, Unidentified Devices. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Analysing The Impact Of Security Threats On Organization Information Security Risk Management
Analysing The Impact Of Security Threats On Organization Information Security Risk ManagementDeliver an outstanding presentation on the topic using this Analysing The Impact Of Security Threats On Organization Information Security Risk Management. Dispense information and present a thorough explanation of Analysing, Security Threats, Organization using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Identifying Information Security Threats And Impact Information Security Risk Management
Identifying Information Security Threats And Impact Information Security Risk ManagementThis slide showcases various threats that can be faced by organization and can result in financial plus reputational loss. It also showcases impact of threats on operational capability of organization. Increase audience engagement and knowledge by dispensing information using Identifying Information Security Threats And Impact Information Security Risk Management. This template helps you present information on one stage. You can also present information on Errors And Omissions, Employee Sabotage, Physical Infrastructure Loss using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
 Matrix For Threat Solution And Risk Management Information Security Risk Management
Matrix For Threat Solution And Risk Management Information Security Risk ManagementThis slide showcases matrix that can help organization to formulate solutions for different types of information security attacks. It can help organization to mitigate the risks and safeguard information in case of any attack. Introducing Matrix For Threat Solution And Risk Management Information Security Risk Management to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispense information on Monitor Database Activity, Validate Database Protocols, Capture Detailed Transactions, using this template. Grab it now to reap its full benefits.
-
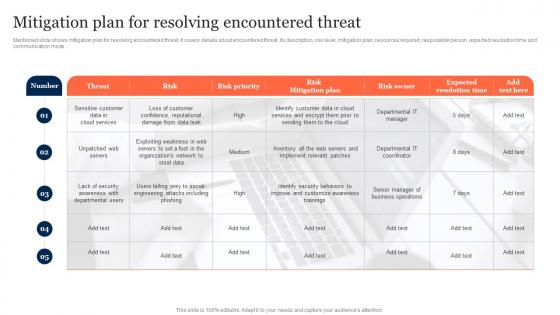 Mitigation Plan For Resolving Encountered Threat Information Security Risk Management
Mitigation Plan For Resolving Encountered Threat Information Security Risk ManagementMentioned slide shows mitigation plan for resolving encountered threat. It covers details about encountered threat, its description, risk level, mitigation plan, resources required, responsible person, expected resolution time and communication mode. Deliver an outstanding presentation on the topic using this Mitigation Plan For Resolving Encountered Threat Information Security Risk Management. Dispense information and present a thorough explanation of Risk Mitigation Plan, Expected Resolution Time, Mitigation Plan using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Mitigation Strategies To Tackle Information Security Threats Information Security Risk Management
Mitigation Strategies To Tackle Information Security Threats Information Security Risk ManagementThis slide showcases mitigation strategies that can help organization to tackle the cybersecurity attacks. It can help organization to minimize the financial loss and maintain reputation of business. Increase audience engagement and knowledge by dispensing information using Mitigation Strategies To Tackle Information Security Threats Information Security Risk Management. This template helps you present information on five stages. You can also present information on Mitigation Strategies, Tackle Information, Security Threats using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
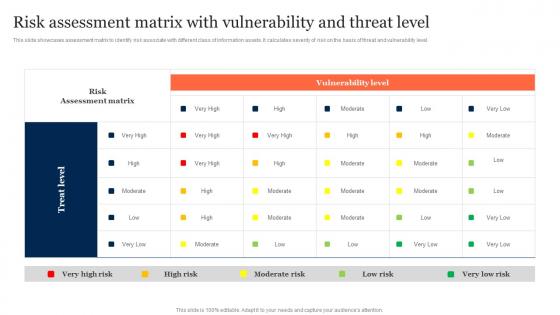 Risk Assessment Matrix With Vulnerability And Threat Level Information Security Risk Management
Risk Assessment Matrix With Vulnerability And Threat Level Information Security Risk ManagementThis slide showcases assessment matrix to identify risk associate with different class of information assets. It calculates severity of risk on the basis of threat and vulnerability level. Deliver an outstanding presentation on the topic using this Risk Assessment Matrix With Vulnerability And Threat Level Information Security Risk Management. Dispense information and present a thorough explanation of Risk Assessment Matrix, Vulnerability Level, Threat Level using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
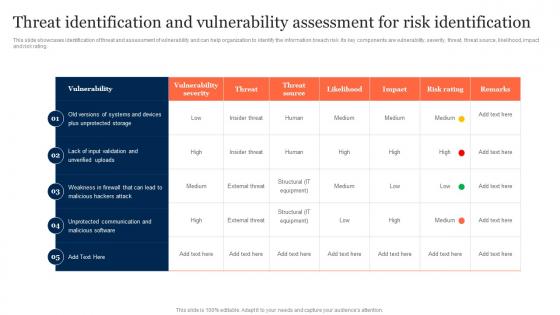 Threat Identification And Vulnerability Assessment Information Security Risk Management
Threat Identification And Vulnerability Assessment Information Security Risk ManagementThis slide showcases identification of threat and assessment of vulnerability and can help organization to identify the information breach risk. Its key components are vulnerability, severity, threat, threat source, likelihood, impact and risk rating. Present the topic in a bit more detail with this Threat Identification And Vulnerability Assessment Information Security Risk Management. Use it as a tool for discussion and navigation on Threat Identification, Vulnerability Assessment, Risk Identification. This template is free to edit as deemed fit for your organization. Therefore download it now
-
 Cyber Security Strategy Best Practices To Defend Against Threats
Cyber Security Strategy Best Practices To Defend Against ThreatsThis slide represents cyber security strategy best practices to defend against threats such a development of insider threat program, training employees, maintaining compliance etc. Presenting our set of slides with name Cyber Security Strategy Best Practices To Defend Against Threats. This exhibits information on eight stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Training Employees, Initiating Phishing Stimulations, Maintaining Compliance.
-
 Security Analysis Plan With Threats And Solutions
Security Analysis Plan With Threats And SolutionsThis slide contains the information related to the plan made for the security analysis of the organization and its clients. It also includes the solutions for treating the threats and vulnerabilities. Presenting our well structured Security Analysis Plan With Threats And Solutions. The topics discussed in this slide are Threat, Vulnerability, Asset And Consequences, Risk. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Security Analysis To Prevent Insider Threats
Security Analysis To Prevent Insider ThreatsThis slide covers the data on the security by using the technologies to protect the data from the insider threats. It includes the analysis with risk model, CWE, OWASP, SQL injection, misconfiguration, etc. Introducing our premium set of slides with Security Analysis To Prevent Insider Threats. Ellicudate the one stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Risk Model, Misconfiguration, Commond Injection. So download instantly and tailor it with your information.
-
 Data Folder Security Threats Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Data Folder Security Threats Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Data folder security threats colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.