Powerpoint Templates and Google slides for Vulnerability Mana
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Improve it security with vulnerability management powerpoint presentation slides
Improve it security with vulnerability management powerpoint presentation slidesDeliver this complete deck to your team members and other collaborators. Encompassed with stylized slides presenting various concepts, this Improve IT Security With Vulnerability Management Powerpoint Presentation Slides is the best tool you can utilize. Personalize its content and graphics to make it unique and thought-provoking. All the sixty one slides are editable and modifiable, so feel free to adjust them to your business setting. The font, color, and other components also come in an editable format making this PPT design the best choice for your next presentation. So, download now.
-
 Vulnerability Management Whitepaper Powerpoint Presentation Slides
Vulnerability Management Whitepaper Powerpoint Presentation SlidesIntroducing Vulnerability Management Whitepaper PowerPoint Presentation Slides. By downloading this complete PPT deck you will get access to 46 professional slides. Since they feature 100% customizability, you can edit any element including font, text, and color as per your choice. This PowerPoint slideshow can be viewed on Google Slides and converted to file formats like PDF, PNG, and JPG. Our PPT template deck is also available in dual screen formats, standard and widescreen.
-
 Enterprise Vulnerability Management Powerpoint Presentation Slides
Enterprise Vulnerability Management Powerpoint Presentation SlidesThis complete presentation has PPT slides on wide range of topics highlighting the core areas of your business needs. It has professionally designed templates with relevant visuals and subject driven content. This presentation deck has total of fourty six slides. Get access to the customizable templates. Our designers have created editable templates for your convenience. You can edit the colour, text and font size as per your need. You can add or delete the content if required. You are just a click to away to have this ready-made presentation. Click the download button now.
-
 Vulnerability Management Program Powerpoint Ppt Template Bundles
Vulnerability Management Program Powerpoint Ppt Template BundlesDeliver a lucid presentation by utilizing this Vulnerability Management Program Powerpoint Ppt Template Bundles. Use it to present an overview of the topic with the right visuals, themes, shapes, and graphics. This is an expertly designed complete deck that reinforces positive thoughts and actions. Use it to provide visual cues to your audience and help them make informed decisions. A wide variety of discussion topics can be covered with this creative bundle such as Threat And Vulnerability Management, Vulnerability Analysis, Risk Management Program, Vulnerability Identification Checklist, Threat Detection. All the seventeen slides are available for immediate download and use. They can be edited and modified to add a personal touch to the presentation. This helps in creating a unique presentation every time. Not only that, with a host of editable features, this presentation can be used by any industry or business vertical depending on their needs and requirements. The compatibility with Google Slides is another feature to look out for in the PPT slideshow.
-
 Enterprise Vulnerability Management Powerpoint PPT Template Bundles
Enterprise Vulnerability Management Powerpoint PPT Template BundlesDeliver a credible and compelling presentation by deploying this Enterprise Vulnerability Management Powerpoint PPT Template Bundles. Intensify your message with the right graphics, images, icons, etc. presented in this complete deck. This PPT template is a great starting point to convey your messages and build a good collaboration. The thirteen slides added to this PowerPoint slideshow helps you present a thorough explanation of the topic. You can use it to study and present various kinds of information in the form of stats, figures, data charts, and many more. This Enterprise Vulnerability Management Powerpoint PPT Template Bundles Industry Comparison PPT slideshow is available for use in standard and widescreen aspects ratios. So, you can use it as per your convenience. Apart from this, it can be downloaded in PNG, JPG, and PDF formats, all completely editable and modifiable. The most profound feature of this PPT design is that it is fully compatible with Google Slides making it suitable for every industry and business domain.
-
 Vulnerability Management Process Flow Powerpoint Ppt Template Bundles
Vulnerability Management Process Flow Powerpoint Ppt Template BundlesIntroduce your topic and host expert discussion sessions with this Vulnerability Management Process Flow Powerpoint Ppt Template Bundles. This template is designed using high-quality visuals, images, graphics, etc, that can be used to showcase your expertise. Different topics can be tackled using the Twelve slides included in this template. You can present each topic on a different slide to help your audience interpret the information more effectively. Apart from this, this PPT slideshow is available in two screen sizes, standard and widescreen making its delivery more impactful. This will not only help in presenting a birds-eye view of the topic but also keep your audience engaged. Since this PPT slideshow utilizes well-researched content, it induces strategic thinking and helps you convey your message in the best possible manner. The biggest feature of this design is that it comes with a host of editable features like color, font, background, etc. So, grab it now to deliver a unique presentation every time.
-
 Crisis Management Strategy Business Vulnerability Assessment Improvement Framework
Crisis Management Strategy Business Vulnerability Assessment Improvement FrameworkEngage buyer personas and boost brand awareness by pitching yourself using this prefabricated set. This Crisis Management Strategy Business Vulnerability Assessment Improvement Framework is a great tool to connect with your audience as it contains high-quality content and graphics. This helps in conveying your thoughts in a well-structured manner. It also helps you attain a competitive advantage because of its unique design and aesthetics. In addition to this, you can use this PPT design to portray information and educate your audience on various topics. With twelve slides, this is a great design to use for your upcoming presentations. Not only is it cost-effective but also easily pliable depending on your needs and requirements. As such color, font, or any other design component can be altered. It is also available for immediate download in different formats such as PNG, JPG, etc. So, without any further ado, download it now.
-
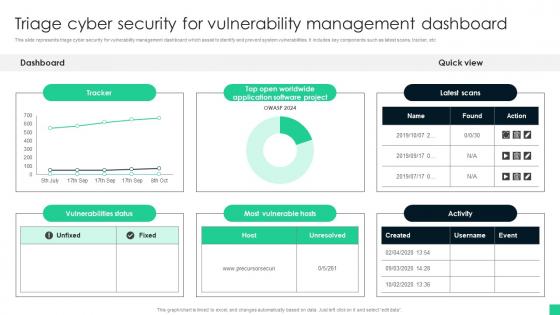 Triage Cyber Security For Vulnerability Management Dashboard
Triage Cyber Security For Vulnerability Management DashboardThis slide represents triage cyber security for vulnerability management dashboard which assist to identify and prevent system vulnerabilities. It includes key components such as latest scans, tracker, etc Introducing our Triage Cyber Security For Vulnerability Management Dashboard set of slides. The topics discussed in these slides are Most Vulnerable Hosts, Vulnerabilities Status This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Vulnerability Management Broken Shield Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Vulnerability Management Broken Shield Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis coloured powerpoint icon features a broken shield with a distressed texture. It is perfect for conveying a sense of vulnerability, fragility, or failure in presentations. It is available in a range of vibrant colours and can be used to highlight key points or draw attention to important concepts.
-
 Vulnerability Management Broken Shield Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Vulnerability Management Broken Shield Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone Powerpoint icon depicts a broken shield, representing a lack of protection or security. It is perfect for conveying a sense of vulnerability, fragility, or danger in presentations. It can also be used to illustrate a lack of trust or loyalty.
-
 How Incident Management Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V
How Incident Management Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS VThis slide showcases various ChatGPT use cases that can help organization in incident management and tackling cyber attacks. Its key elements are explore cyber attacks, decision support and post incident analysis Increase audience engagement and knowledge by dispensing information using How Incident Management Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V. This template helps you present information on three stages. You can also present information on Explore Cyber Attacks, Decision Support, Post Incident Analysis using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Solutions To Overcome Challenges In Effective Vulnerability Management For SAP Systems
Solutions To Overcome Challenges In Effective Vulnerability Management For SAP SystemsThis slide depicts the resolutions to challenges in effective vulnerability management for SAP systems. The purpose of this template is to help the business ensure it can overcome these challenges through the use of given solutions. It includes challenges such as lack of resources and budgets, lack of visibility, etc. Introducing our Solutions To Overcome Challenges In Effective Vulnerability Management For SAP Systems set of slides. The topics discussed in these slides are Lack Of Resources And Budgets, Lack Of Visibility, Determining Start Point. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
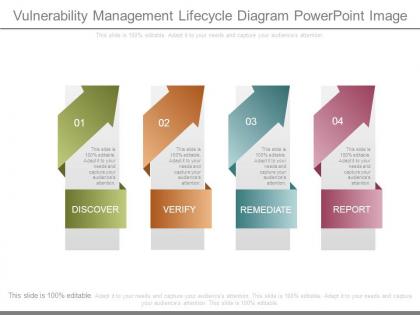 Vulnerability management lifecycle diagram powerpoint image
Vulnerability management lifecycle diagram powerpoint imagePresenting vulnerability management lifecycle diagram powerpoint image. This is a vulnerability management lifecycle diagram powerpoint image. This is a four stage process. The stages in this process are discover, verify, remediate, report.
-
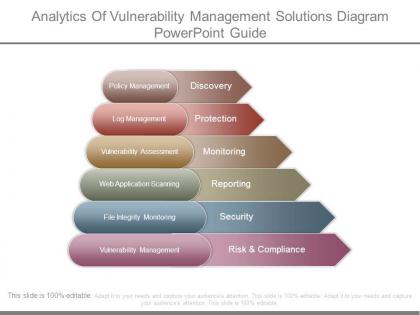 Analytics of vulnerability management solutions diagram powerpoint guide
Analytics of vulnerability management solutions diagram powerpoint guidePresenting analytics of vulnerability management solutions diagram powerpoint guide. This is a analytics of vulnerability management solutions diagram powerpoint guide. This is a six stage process. The stages in this process are discovery, protection, monitoring, reporting, security, risk and compliance.
-
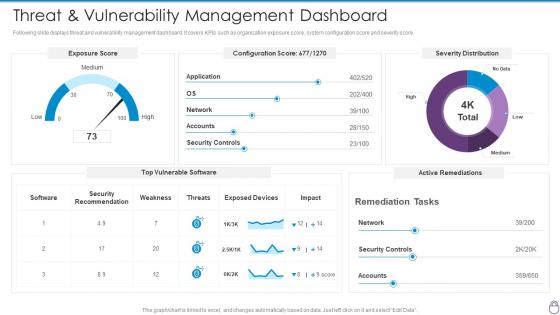 Cybersecurity Risk Management Framework Threat And Vulnerability Management Dashboard
Cybersecurity Risk Management Framework Threat And Vulnerability Management DashboardFollowing slide displays threat and vulnerability management dashboard. It covers KPIs such as organization exposure score, system configuration score and severity score. Present the topic in a bit more detail with this Cybersecurity Risk Management Framework Threat And Vulnerability Management Dashboard. Use it as a tool for discussion and navigation on Exposure Score, Configuration Score, Severity Distribution, Weakness, Threats. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Vulnerability Administration At Workplace Cyber Threats Management Dashboard
Vulnerability Administration At Workplace Cyber Threats Management DashboardThis slide portrays information regarding the dashboard that firm will use to manage cyber threats. The dashboard will provide clear picture of threats risks prevailing and how they are treated to technical engineers and board level executives. Deliver an outstanding presentation on the topic using this Vulnerability Administration At Workplace Cyber Threats Management Dashboard. Dispense information and present a thorough explanation of Management, Dashboard, Portrays Information using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
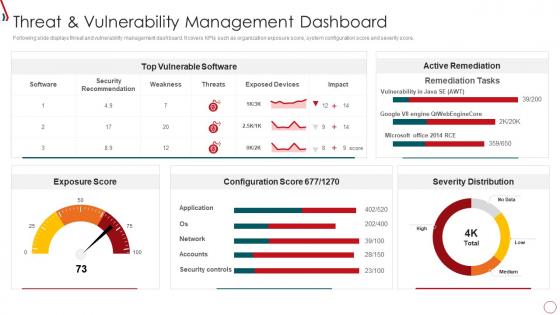 Risk Management Framework For Information Security Threat And Vulnerability
Risk Management Framework For Information Security Threat And VulnerabilityFollowing slide displays threat and vulnerability management dashboard. It covers KPIs such as organization exposure score, system configuration score and severity score. Present the topic in a bit more detail with this Risk Management Framework For Information Security Threat And Vulnerability. Use it as a tool for discussion and navigation on Exposure Score, Top Vulnerable Software, Severity Distribution, Active Remediation, Configuration Score. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
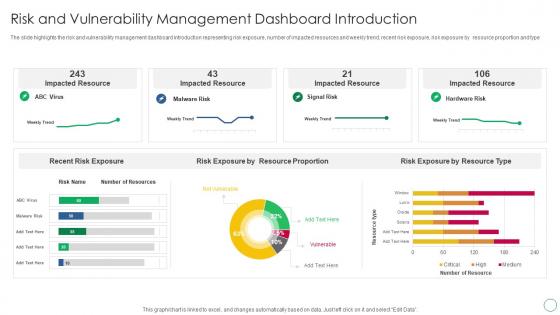 Risk And Vulnerability Management Dashboard Introduction
Risk And Vulnerability Management Dashboard IntroductionThe slide highlights the risk and vulnerability management dashboard introduction representing risk exposure, number of impacted resources and weekly trend, recent risk exposure, risk exposure by resource proportion and type. Presenting our well structured Risk And Vulnerability Management Dashboard Introduction. The topics discussed in this slide are Impacted Resource, Risk Exposure By Resource Proportion, Risk Exposure By Resource Type, Recent Risk Exposure. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
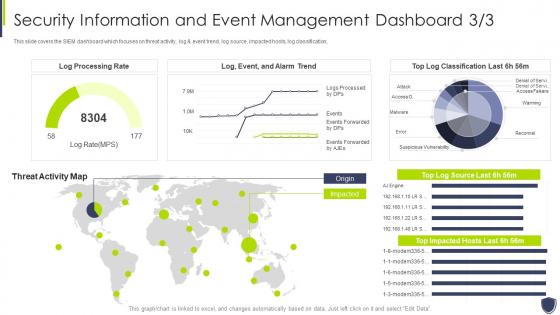 Improve it security vulnerability security information event management dashboard
Improve it security vulnerability security information event management dashboardThis slide covers the SIEM dashboard which focuses on threat activity, log and event trend, log source, impacted hosts, log classification, Deliver an outstanding presentation on the topic using this Improve It Security Vulnerability Security Information Event Management Dashboard. Dispense information and present a thorough explanation of Information, Management, Dashboard using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
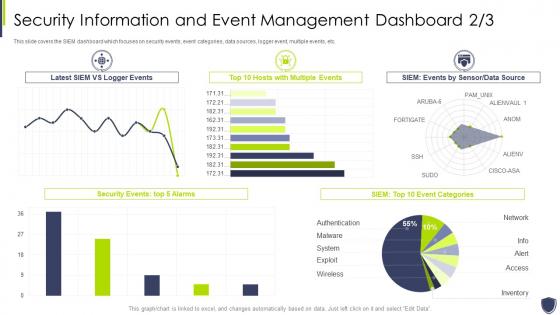 Improve it security with vulnerability event management dashboard snapshot
Improve it security with vulnerability event management dashboard snapshotThis slide covers the SIEM dashboard which focuses on security events, event categories, data sources, logger event, multiple events, etc. Deliver an outstanding presentation on the topic using this Improve It Security With Vulnerability Event Management Dashboard snapshot. Dispense information and present a thorough explanation of Information, Management, Dashboard using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
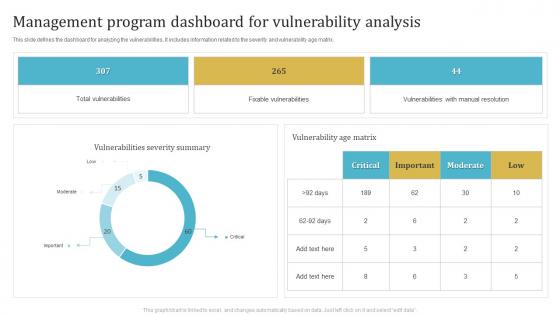 Management Program Dashboard For Vulnerability Analysis
Management Program Dashboard For Vulnerability AnalysisThis slide defines the dashboard for analyzing the vulnerabilities. It includes information related to the severity and vulnerability age matrix. Introducing our Management Program Dashboard For Vulnerability Analysis set of slides. The topics discussed in these slides are Total Vulnerabilities, Fixable Vulnerabilities, Vulnerabilities With Manual Resolution. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Threat And Vulnerability Management Program Analysis Dashboard
Threat And Vulnerability Management Program Analysis DashboardThis slide defines the dashboard for analyzing the threat and vulnerability program. It includes information related to the exposure, configuration and severity score. Presenting our well structured Threat And Vulnerability Management Program Analysis Dashboard. The topics discussed in this slide are Exposure Score, Top Vulnerable Software, Severity Distribution. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
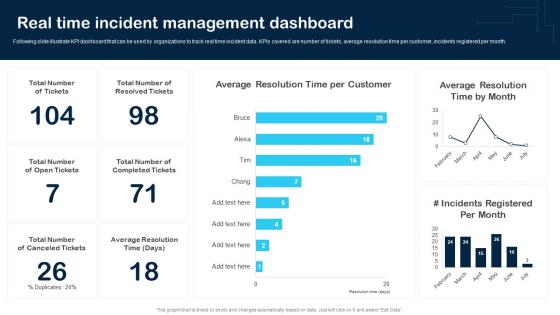 Real Time Incident Management Dashboard Cybersecurity Incident And Vulnerability
Real Time Incident Management Dashboard Cybersecurity Incident And VulnerabilityFollowing slide illustrate KPI dashboard that can be used by organizations to track real time incident data. KPIs covered are number of tickets, average resolution time per customer, incidents registered per month. Present the topic in a bit more detail with this Real Time Incident Management Dashboard Cybersecurity Incident And Vulnerability. Use it as a tool for discussion and navigation on Average Resolution, Customer, Incidents Registered. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Security information event management dashboard improve security vulnerability management
Security information event management dashboard improve security vulnerability managementThis slide covers the SIEM dashboard which focuses on server status, log sources, total logs, last log, collectors, log sources etc. Deliver an outstanding presentation on the topic using this Security Information Event Management Dashboard Improve Security Vulnerability Management. Dispense information and present a thorough explanation of Management, Dashboard, Information using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Vulnerability management system workforce diversity marketing communications planning cpb
Vulnerability management system workforce diversity marketing communications planning cpbPresenting this set of slides with name - Vulnerability Management System Workforce Diversity Marketing Communications Planning Cpb. This is an editable four stages graphic that deals with topics like Vulnerability Management System, Workforce Diversity, Marketing Communications Planning to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
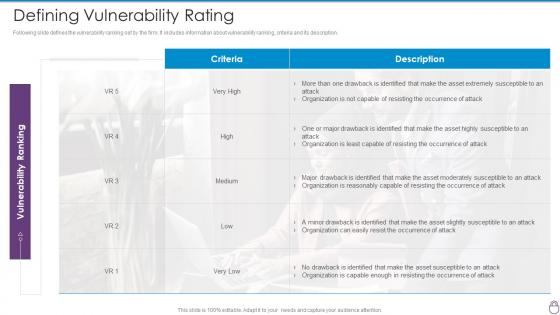 Cybersecurity Risk Management Framework Defining Vulnerability Rating
Cybersecurity Risk Management Framework Defining Vulnerability RatingFollowing slide defines the vulnerability ranking set by the firm. It includes information about vulnerability ranking, criteria and its description. Deliver an outstanding presentation on the topic using this Cybersecurity Risk Management Framework Defining Vulnerability Rating. Dispense information and present a thorough explanation of Occurrence Attack, Asset Moderately Susceptible, Asset Highly Susceptible using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
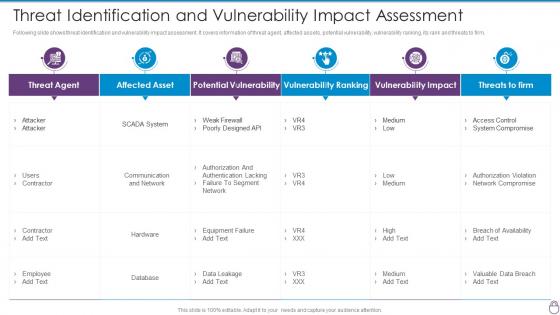 Cybersecurity Risk Management Framework Threat Identification And Vulnerability Impact
Cybersecurity Risk Management Framework Threat Identification And Vulnerability ImpactFollowing slide shows threat identification and vulnerability impact assessment. It covers information of threat agent, affected assets, potential vulnerability, vulnerability ranking, its rank and threats to firm. Deliver an outstanding presentation on the topic using this Cybersecurity Risk Management Framework Threat Identification And Vulnerability Impact. Dispense information and present a thorough explanation of Threat Agent, Affected Asset, Potential Vulnerability, Vulnerability Ranking, Vulnerability Impact using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
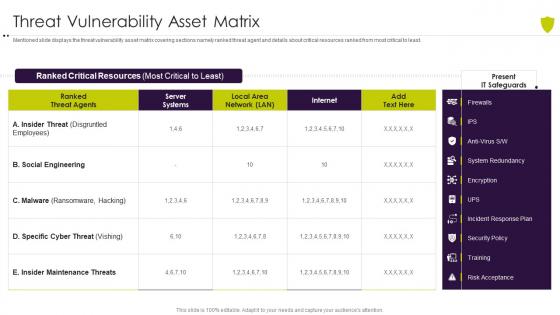 Threat vulnerability asset matrix managing cyber risk in a digital age
Threat vulnerability asset matrix managing cyber risk in a digital ageMentioned slide displays the threat vulnerability asset matrix covering sections namely ranked threat agent and details about critical resources ranked from most critical to least. Present the topic in a bit more detail with this Threat Vulnerability Asset Matrix Managing Cyber Risk In A Digital Age. Use it as a tool for discussion and navigation on Threat Vulnerability Asset Matrix. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
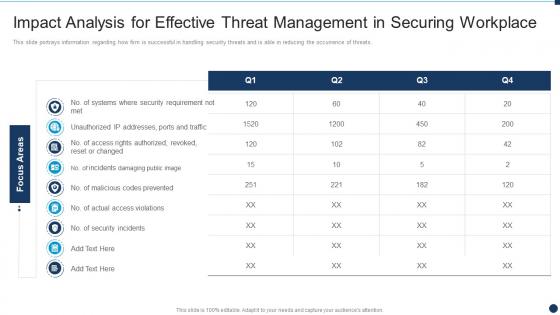 Impact Analysis For Effective Threat Management In Vulnerability Administration At Workplace
Impact Analysis For Effective Threat Management In Vulnerability Administration At WorkplaceThis slide portrays information regarding how firm is successful in handling security threats and is able in reducing the occurrence of threats. Present the topic in a bit more detail with this Impact Analysis For Effective Threat Management In Vulnerability Administration At Workplace. Use it as a tool for discussion and navigation on Management, Workplace, Information. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
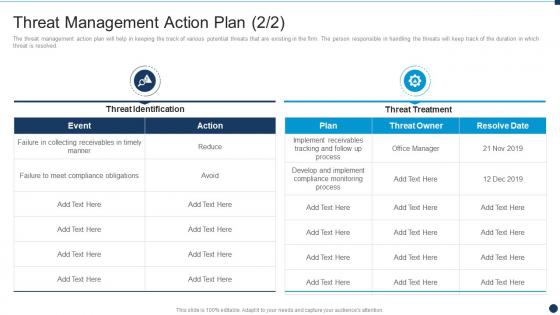 Threat Management Action Plan Vulnerability Administration At Workplace
Threat Management Action Plan Vulnerability Administration At WorkplaceThe threat management action plan will help in keeping the track of various potential threats that are existing in the firm. The person responsible in handling the threats will keep track of the duration in which threat is resolved. Deliver an outstanding presentation on the topic using this Threat Management Action Plan Vulnerability Administration At Workplace. Dispense information and present a thorough explanation of Threat Management Action Plan using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Vulnerability Administration At Workplace Budget For Effective Threat Management At Workplace
Vulnerability Administration At Workplace Budget For Effective Threat Management At WorkplaceFirm has prepared a budget for managing cybersecurity by optimizing various functional areas. It also provides information about the software used and the duration required for implementation. Deliver an outstanding presentation on the topic using this Vulnerability Administration At Workplace Budget For Effective Threat Management At Workplace. Dispense information and present a thorough explanation of Management, Workplace, Implementation using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
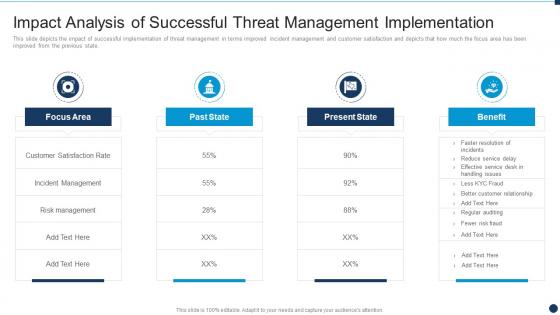 Vulnerability Administration At Workplace Impact Analysis Of Successful Management Implementation
Vulnerability Administration At Workplace Impact Analysis Of Successful Management ImplementationThis slide depicts the impact of successful implementation of threat management in terms improved incident management and customer satisfaction and depicts that how much the focus area has been improved from the previous state. Present the topic in a bit more detail with this Vulnerability Administration At Workplace Impact Analysis Of Successful Management Implementation. Use it as a tool for discussion and navigation on Analysis, Management, Implementation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
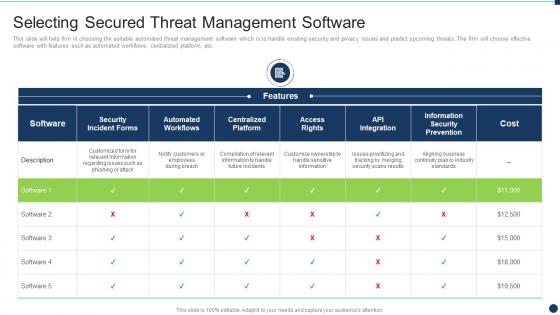 Vulnerability Administration At Workplace Selecting Secured Threat Management Software
Vulnerability Administration At Workplace Selecting Secured Threat Management SoftwareThis slide will help firm in choosing the suitable automated threat management software which is to handle existing security and privacy issues and predict upcoming threats. The firm will choose effective software with features such as automated workflows, centralized platform, etc. Present the topic in a bit more detail with this Vulnerability Administration At Workplace Selecting Secured Threat Management Software. Use it as a tool for discussion and navigation on Management, Software, Workflows. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
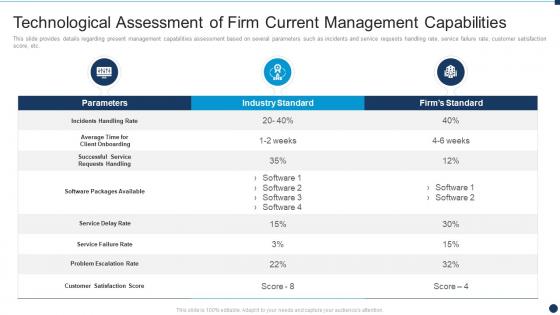 Vulnerability Administration At Workplace Technological Assessment Current Management Capabilities
Vulnerability Administration At Workplace Technological Assessment Current Management CapabilitiesThis slide provides details regarding present management capabilities assessment based on several parameters such as incidents and service requests handling rate, service failure rate, customer satisfaction score, etc. Present the topic in a bit more detail with this Vulnerability Administration At Workplace Technological Assessment Current Management Capabilities. Use it as a tool for discussion and navigation on Technological, Assessment, Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
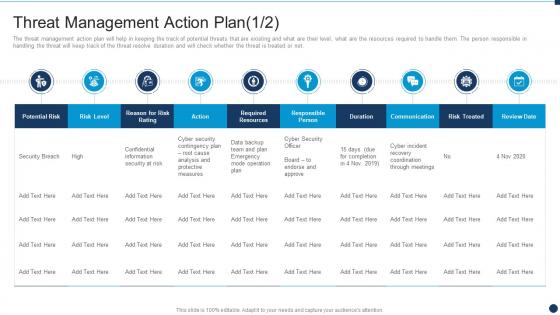 Vulnerability Administration At Workplace Threat Management Action Plan
Vulnerability Administration At Workplace Threat Management Action Planthem. The person responsible in handling the threat will keep track of the threat resolve duration and will check whether the threat is treated or not. Present the topic in a bit more detail with this Vulnerability Administration At Workplace Threat Management Action Plan. Use it as a tool for discussion and navigation on Threat Management Action Plan. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Vulnerability Administration At Workplace Threat Management Team Training Schedule
Vulnerability Administration At Workplace Threat Management Team Training ScheduleThe threat management team needs to have strong critical and creative thinking skills so that they become capable in taking key decisions without complete or conflicting information under immense tensed situations. The team will be trained by experts who will also use scenario based activities and costing will be per employee basis. Deliver an outstanding presentation on the topic using this Vulnerability Administration At Workplace Threat Management Team Training Schedule. Dispense information and present a thorough explanation of Management, Schedule, Employee using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Information Security Program Cybersecurity Management Threat Vulnerability Asset Matrix
Information Security Program Cybersecurity Management Threat Vulnerability Asset MatrixMentioned slide displays the threat vulnerability asset matrix covering sections namely ranked threat agent and details about critical resources ranked from most critical to least. Deliver an outstanding presentation on the topic using this Information Security Program Cybersecurity Management Threat Vulnerability Asset Matrix. Dispense information and present a thorough explanation of Threat Vulnerability Asset Matrix using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Vulnerability Management Cyber Security In Powerpoint And Google Slides Cpb
Vulnerability Management Cyber Security In Powerpoint And Google Slides CpbPresenting Vulnerability Management Cyber Security In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Vulnerability Management Cyber Security. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
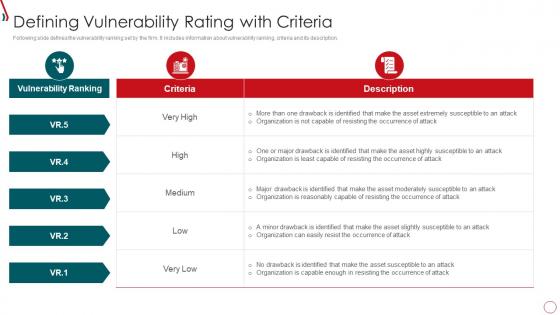 Risk Management Framework For Information Security Defining Vulnerability Rating With Criteria
Risk Management Framework For Information Security Defining Vulnerability Rating With CriteriaFollowing slide defines the vulnerability ranking set by the firm. It includes information about vulnerability ranking, criteria and its description. Present the topic in a bit more detail with this Risk Management Framework For Information Security Defining Vulnerability Rating With Criteria. Use it as a tool for discussion and navigation on Vulnerability Ranking, Organization, High, Low, Medium. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
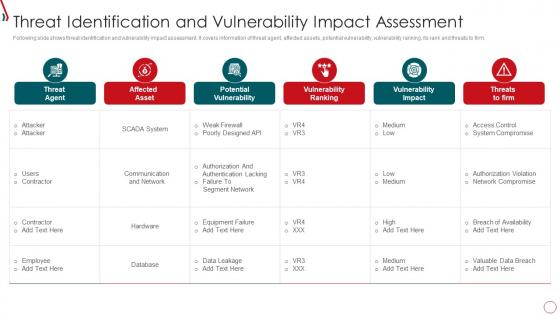 Risk Management Framework For Information Security Threat Identification And Vulnerability
Risk Management Framework For Information Security Threat Identification And VulnerabilityFollowing slide shows threat identification and vulnerability impact assessment. It covers information of threat agent, affected assets, potential vulnerability, vulnerability ranking, its rank and threats to firm. Deliver an outstanding presentation on the topic using this Risk Management Framework For Information Security Threat Identification And Vulnerability. Dispense information and present a thorough explanation of Communication And Network, Database, Failure To Segment Network using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
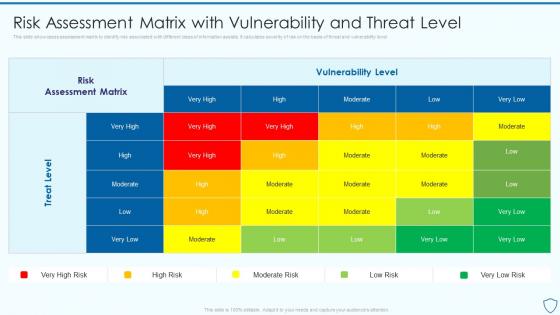 Risk Assessment Matrix With Vulnerability Risk Assessment And Management Plan For Information Security
Risk Assessment Matrix With Vulnerability Risk Assessment And Management Plan For Information SecurityThis slide showcases assessment matrix to identify risk associated with different class of information assists. It calculates severity of risk on the basis of threat and vulnerability level Present the topic in a bit more detail with this Risk Assessment Matrix With Vulnerability Risk Assessment And Management Plan For Information Security. Use it as a tool for discussion and navigation on Assessment, Vulnerability, Associated. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
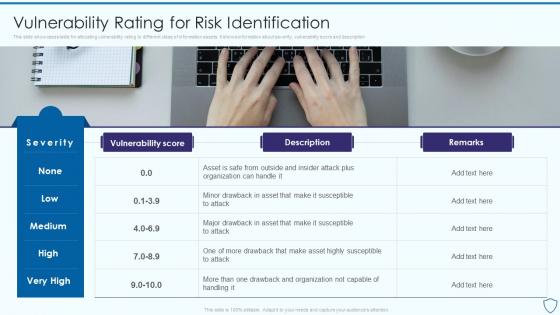 Vulnerability Rating For Risk Identification Risk Assessment And Management Plan For Information Security
Vulnerability Rating For Risk Identification Risk Assessment And Management Plan For Information SecurityThis slide showcases table for allocating vulnerability rating to different class of information assets. It shows information about severity, vulnerability score and description Present the topic in a bit more detail with this Vulnerability Rating For Risk Identification Risk Assessment And Management Plan For Information Security. Use it as a tool for discussion and navigation on Identification, Information, Vulnerability. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
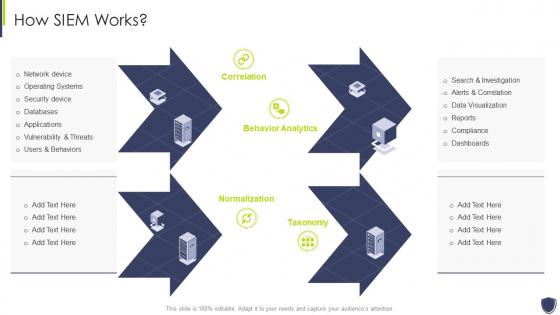 Improve it security with vulnerability management how siem works
Improve it security with vulnerability management how siem worksIncrease audience engagement and knowledge by dispensing information using Improve It Security With Vulnerability Management How Siem Works. This template helps you present information on four stages. You can also present information on Databases, Applications, Security Device using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
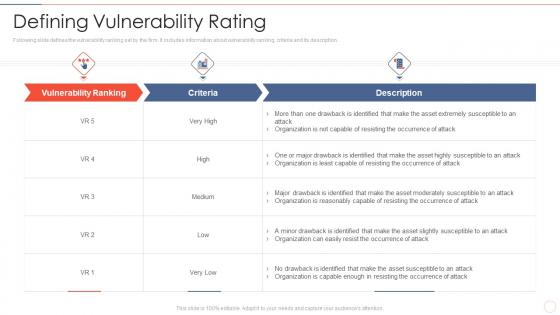 Defining vulnerability rating effective information security risk management process
Defining vulnerability rating effective information security risk management processFollowing slide defines the vulnerability ranking set by the firm. It includes information about vulnerability ranking, criteria and its description.Present the topic in a bit more detail with this Defining Vulnerability Rating Effective Information Security Risk Management Process. Use it as a tool for discussion and navigation on Occurrence Of Attack, Organization Is Reasonably, Organization Is Capable Enough. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Agenda of improve it security with vulnerability management
Agenda of improve it security with vulnerability managementIntroducing Agenda Of Improve It Security With Vulnerability Management to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Vulnerability, Management, Agenda, using this template. Grab it now to reap its full benefits.
-
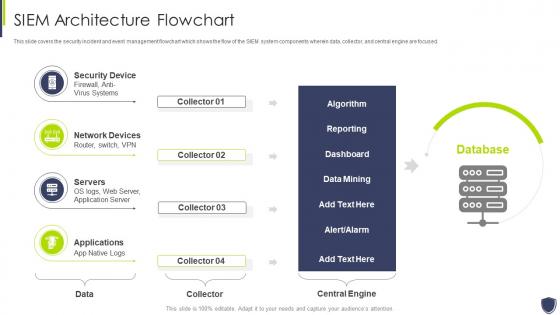 Architecture flowchart improve it security with vulnerability management
Architecture flowchart improve it security with vulnerability managementThis slide covers the security incident and event management flowchart which shows the flow of the SIEM system components wherein data, collector, and central engine are focused. Present the topic in a bit more detail with this Architecture Flowchart Improve It Security With Vulnerability Management. Use it as a tool for discussion and navigation on Security Device, Network Devices, Servers. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
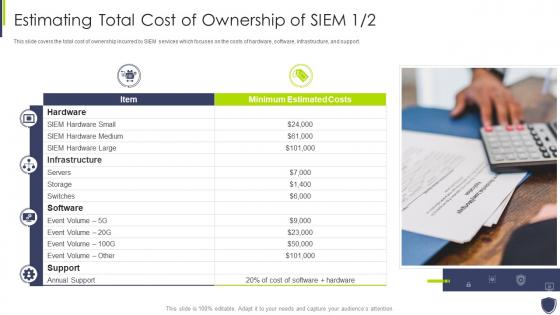 Estimating total cost of ownership improve it security vulnerability management
Estimating total cost of ownership improve it security vulnerability managementThis slide covers the total cost of ownership incurred by SIEM services which focuses on the costs of hardware, software, infrastructure, and support. Deliver an outstanding presentation on the topic using this Estimating Total Cost Of Ownership Improve It Security Vulnerability Management. Dispense information and present a thorough explanation of Estimating Total Cost Of Ownership Of SIEM using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Icons slide for improve it security with vulnerability management
Icons slide for improve it security with vulnerability managementIntroducing our well researched set of slides titled Icons Slide For Improve It Security With Vulnerability Management. It displays a hundred percent editable icons. You can use these icons in your presentation to captivate your audiences attention. Download now and use it multiple times.
-
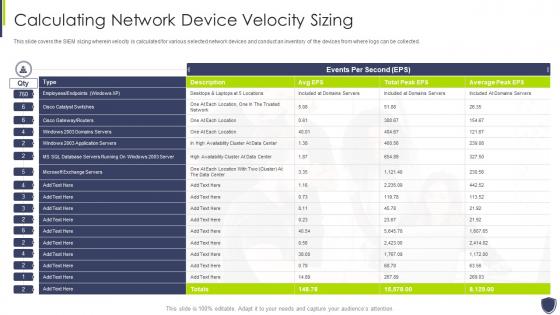 Improve it security vulnerability management calculating network device velocity sizing
Improve it security vulnerability management calculating network device velocity sizingThis slide covers the SIEM sizing wherein velocity is calculated for various selected network devices and conduct an inventory of the devices from where logs can be collected. Present the topic in a bit more detail with this Improve It Security Vulnerability Management Calculating Network Device Velocity Sizing. Use it as a tool for discussion and navigation on Calculating Network Device Velocity Sizing. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
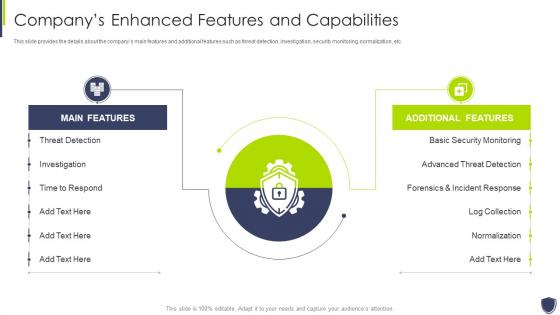 Improve it security vulnerability management companys enhanced features capabilities
Improve it security vulnerability management companys enhanced features capabilitiesThis slide provides the details about the companys main features and additional features such as threat detection, investigation, security monitoring, normalization, etc. Deliver an outstanding presentation on the topic using this Improve It Security Vulnerability Management Companys Enhanced Features Capabilities. Dispense information and present a thorough explanation of Threat Detection, Investigation, Time To Respond using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
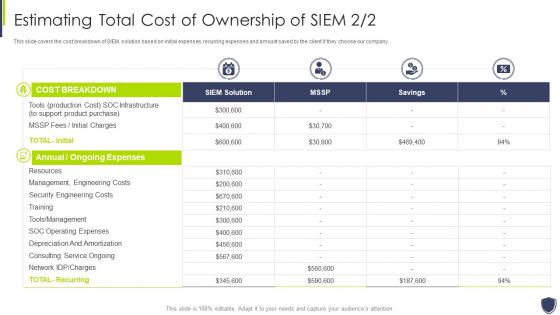 Improve it security vulnerability management estimating total cost ownership siem
Improve it security vulnerability management estimating total cost ownership siemThis slide covers the cost breakdown of SIEM solution based on initial expenses, recurring expenses and amount saved by the client if they choose our company. Present the topic in a bit more detail with this Improve It Security Vulnerability Management Estimating Total Cost Ownership Siem. Use it as a tool for discussion and navigation on Management, Engineering, Ownership. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
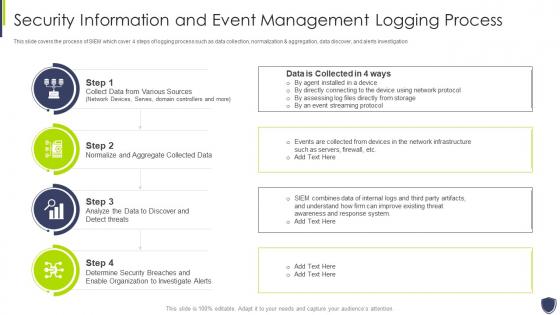 Improve it security with vulnerability information and event management logging process
Improve it security with vulnerability information and event management logging processThis slide covers the process of SIEM which cover 4 steps of logging process such as data collection, normalization and aggregation, data discover, and alerts investigation Introducing Improve It Security With Vulnerability Information And Event Management Logging Process to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Information, Management, Process, using this template. Grab it now to reap its full benefits.
-
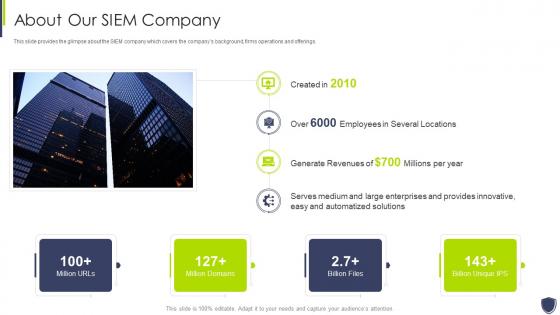 Improve it security with vulnerability management about our siem company
Improve it security with vulnerability management about our siem companyThis slide provides the glimpse about the SIEM company which covers the companys background, firms operations and offerings. Present the topic in a bit more detail with this Improve It Security With Vulnerability Management About Our Siem Company. Use it as a tool for discussion and navigation on Automatized, Solutions, Innovative. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
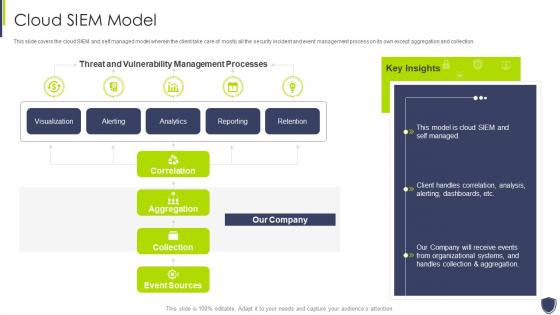 Improve it security with vulnerability management cloud siem model
Improve it security with vulnerability management cloud siem modelThis slide covers the cloud SIEM and self managed model wherein the client take care of mostly all the security incident and event management process on its own except aggregation and collection. Deliver an outstanding presentation on the topic using this Improve It Security With Vulnerability Management Cloud Siem Model. Dispense information and present a thorough explanation of Vulnerability, Management, Processes using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Improve it security with vulnerability management competitive advantage
Improve it security with vulnerability management competitive advantageThis slide covers the competitive advantage scoring for security information and event management based on different factors such as value, deployment, ease of use, support, etc. Present the topic in a bit more detail with this Improve It Security With Vulnerability Management Competitive Advantage. Use it as a tool for discussion and navigation on Siem Competitive Advantage. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Improve it security with vulnerability management event management services
Improve it security with vulnerability management event management servicesThis slide covers the SIEM services offered by our company such as data aggregation, correlation, security alerts, dashboards, retention, forensic analysis, IT compliance, threat detection, etc. Increase audience engagement and knowledge by dispensing information using Improve It Security With Vulnerability Management Event Management Services. This template helps you present information on eight stages. You can also present information on Data Aggregation, Data Correlation, Security Alert using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
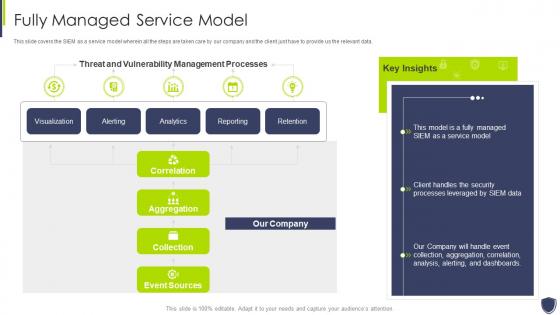 Improve it security with vulnerability management fully managed service model
Improve it security with vulnerability management fully managed service modelThis slide covers the SIEM as a service model wherein all the steps are taken care by our company and the client just have to provide us the relevant data. Deliver an outstanding presentation on the topic using this Improve It Security With Vulnerability Management Fully Managed Service Model. Dispense information and present a thorough explanation of Vulnerability, Management, Processes using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
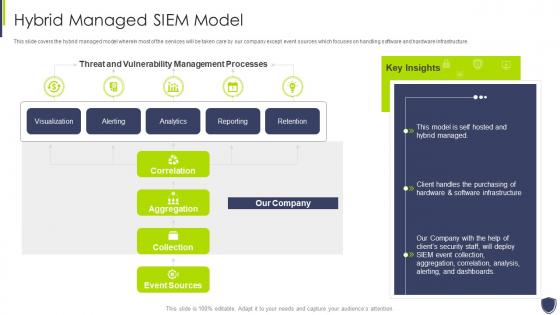 Improve it security with vulnerability management hybrid managed siem model
Improve it security with vulnerability management hybrid managed siem modelThis slide covers the hybrid managed model wherein most of the services will be taken care by our company except event sources which focuses on handling software and hardware infrastructure. Deliver an outstanding presentation on the topic using this Improve It Security With Vulnerability Management Hybrid Managed Siem Model. Dispense information and present a thorough explanation of Vulnerability, Management, Processes using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Improve it security with vulnerability management integrations
Improve it security with vulnerability management integrationsPresent the topic in a bit more detail with this Improve It Security With Vulnerability Management Integrations. Use it as a tool for discussion and navigation on Applications And Devices, Network Logs, Security Events. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
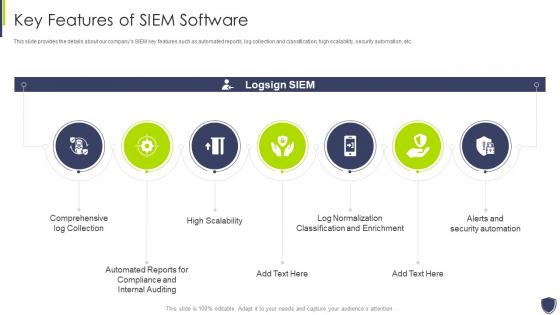 Improve it security with vulnerability management key features of siem software
Improve it security with vulnerability management key features of siem softwareThis slide provides the details about our companys SIEM key features such as automated reports, log collection and classification, high scalability, security automation, etc. Increase audience engagement and knowledge by dispensing information using Improve It Security With Vulnerability Management Key Features Of Siem Software. This template helps you present information on seven stages. You can also present information on Comprehensive, Compliance, Classification using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.


