Powerpoint Templates and Google slides for Vulnerable
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
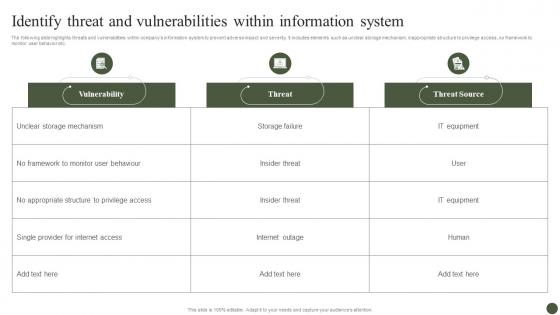 Identify Threat And Vulnerabilities Within Information Implementing Cyber Risk Management Process
Identify Threat And Vulnerabilities Within Information Implementing Cyber Risk Management ProcessThe following slide highlights threats and vulnerabilities within companys information system to prevent adverse impact and severity. It includes elements such as unclear storage mechanism, inappropriate structure to privilege access, no framework to monitor user behavior etc. Present the topic in a bit more detail with this Identify Threat And Vulnerabilities Within Information Implementing Cyber Risk Management Process. Use it as a tool for discussion and navigation on Vulnerability, Threat, Threat Source. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Solutions To Overcome Challenges In Effective Vulnerability Management For SAP Systems
Solutions To Overcome Challenges In Effective Vulnerability Management For SAP SystemsThis slide depicts the resolutions to challenges in effective vulnerability management for SAP systems. The purpose of this template is to help the business ensure it can overcome these challenges through the use of given solutions. It includes challenges such as lack of resources and budgets, lack of visibility, etc. Introducing our Solutions To Overcome Challenges In Effective Vulnerability Management For SAP Systems set of slides. The topics discussed in these slides are Lack Of Resources And Budgets, Lack Of Visibility, Determining Start Point. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
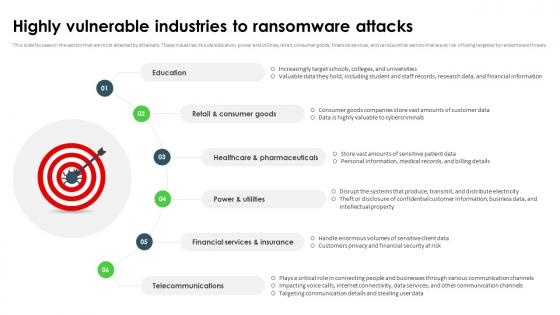 Ransomware In Digital Age Highly Vulnerable Industries To Ransomware Attacks
Ransomware In Digital Age Highly Vulnerable Industries To Ransomware AttacksThis slide focuses on the sectors that are most attacked by attackers. These industries include education, power and utilities, retail, consumer goods, financial services, and various other sectors that are at risk of being targeted by ransomware threats. Increase audience engagement and knowledge by dispensing information using Ransomware In Digital Age Highly Vulnerable Industries To Ransomware Attacks. This template helps you present information on six stages. You can also present information on Retail And Consumer Goods, Healthcare And Pharmaceuticals, Financial Services And Insurance, Telecommunications using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Keyhole Vulnerability Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Keyhole Vulnerability Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis coloured PowerPoint icon features a keyhole design, perfect for adding a touch of creativity to your presentations. The vibrant colors and detailed design make it eye-catching and easy to spot. Use it to represent security, access, or any other relevant concept in your slides.
-
 Keyhole Vulnerability Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Keyhole Vulnerability Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone powerpoint icon on door Key Hole is the perfect addition to any presentation. Its sleek design and simple yet eye-catching image will make your presentation stand out. With its high-quality resolution, it is sure to impress your audience and add a professional touch to your slides.
-
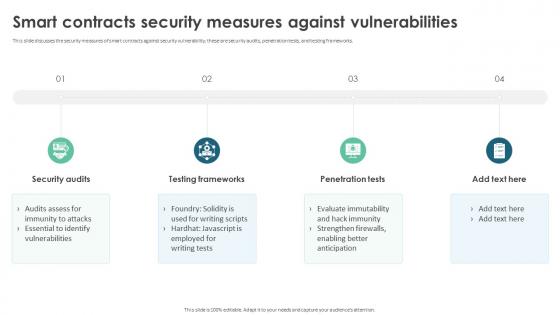 Smart Contracts Security Measures Against Vulnerabilities Ppt File Outfit
Smart Contracts Security Measures Against Vulnerabilities Ppt File OutfitThis slide discusses the security measures of smart contracts against security vulnerability, these are security audits, penetration tests, and testing frameworks. Introducing Smart Contracts Security Measures Against Vulnerabilities Ppt File Outfit to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Security Audits, Testing Frameworks, Penetration Tests, Against Vulnerabilities, using this template. Grab it now to reap its full benefits.
-
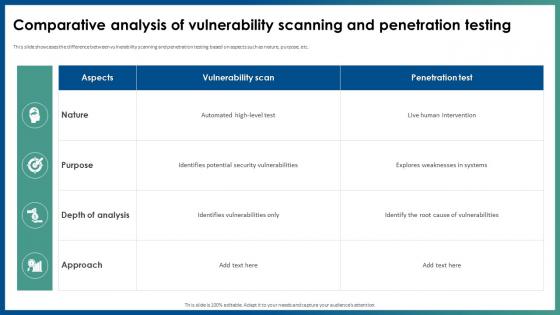 Application Security Comparative Analysis Of Vulnerability Scanning And Penetration Testing
Application Security Comparative Analysis Of Vulnerability Scanning And Penetration TestingThis slide showcases the difference between vulnerability scanning and penetration testing based on aspects such as nature, purpose, etc. Present the topic in a bit more detail with this Application Security Comparative Analysis Of Vulnerability Scanning And Penetration Testing. Use it as a tool for discussion and navigation on Explores Weaknesses In Systems, Comparative Analysis, Vulnerability Scanning, Penetration Testing. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
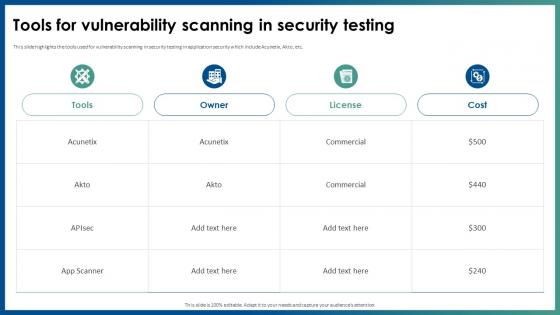 Application Security Tools For Vulnerability Scanning In Security Testing
Application Security Tools For Vulnerability Scanning In Security TestingThis slide highlights the tools used for vulnerability scanning in security testing in application security which include Acunetix, Akto, etc. Present the topic in a bit more detail with this Application Security Tools For Vulnerability Scanning In Security Testing. Use it as a tool for discussion and navigation on Tools For Vulnerability, Scanning In Security Testing, Application Security. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
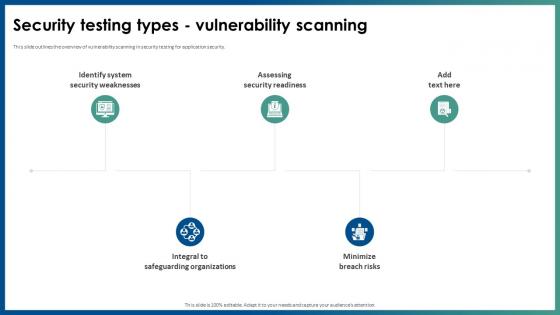 Security Testing Types Vulnerability Scanning Application Security
Security Testing Types Vulnerability Scanning Application SecurityThis slide outlines the overview of vulnerability scanning in security testing for application security. Introducing Security Testing Types Vulnerability Scanning Application Security to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Assessing Security Readiness, Integral To Safeguarding Organizations, Identify System Security Weaknesses, using this template. Grab it now to reap its full benefits.
-
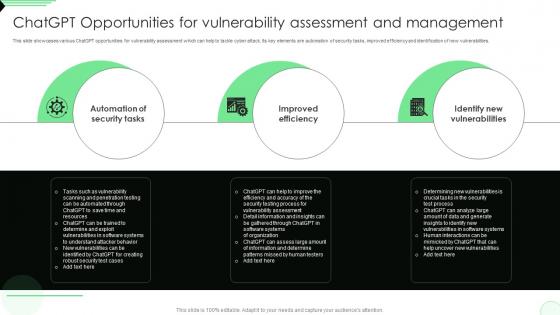 ChatGPT Opportunities For Vulnerability Assessment Opportunities And Risks Of ChatGPT AI SS V
ChatGPT Opportunities For Vulnerability Assessment Opportunities And Risks Of ChatGPT AI SS VThis slide showcases various ChatGPT opportunities for vulnerability assessment which can help to tackle cyber attack. Its key elements are automation of security tasks, improved efficiency and identification of new vulnerabilities. Increase audience engagement and knowledge by dispensing information using ChatGPT Opportunities For Vulnerability Assessment Opportunities And Risks Of ChatGPT AI SS V. This template helps you present information on three stages. You can also present information on Automation Of Security Tasks, Improved Efficiency, Identify New Vulnerabilities using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
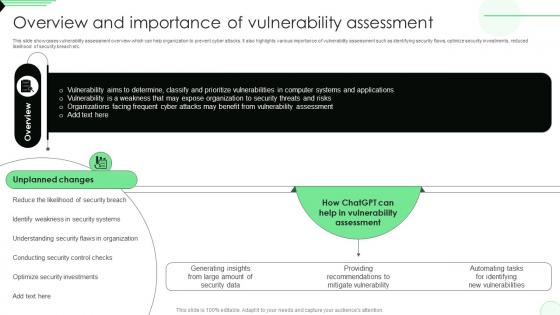 Overview And Importance Of Vulnerability Opportunities And Risks Of ChatGPT AI SS V
Overview And Importance Of Vulnerability Opportunities And Risks Of ChatGPT AI SS VThis slide showcases vulnerability assessment overview which can help organization to prevent cyber attacks. It also highlights various importance of vulnerability assessment such as identifying security flaws, optimize security investments, reduced likelihood of security breach etc. Deliver an outstanding presentation on the topic using this Overview And Importance Of Vulnerability Opportunities And Risks Of ChatGPT AI SS V. Dispense information and present a thorough explanation of Vulnerability Assessment, Computer Systems And Applications, Security Threats And Risks using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
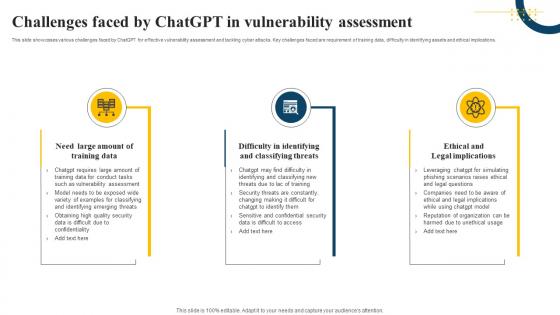 Challenges Faced By ChatGPT In Vulnerability Assessment Impact Of Generative AI SS V
Challenges Faced By ChatGPT In Vulnerability Assessment Impact Of Generative AI SS VThis slide showcases various challenges faced by ChatGPT for effective vulnerability assessment and tackling cyber attacks. Key challenges faced are requirement of training data, difficulty in identifying assets and ethical implications. Introducing Challenges Faced By ChatGPT In Vulnerability Assessment Impact Of Generative AI SS V to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Training Data, Classifying Threats, Legal Implications, using this template. Grab it now to reap its full benefits.
-
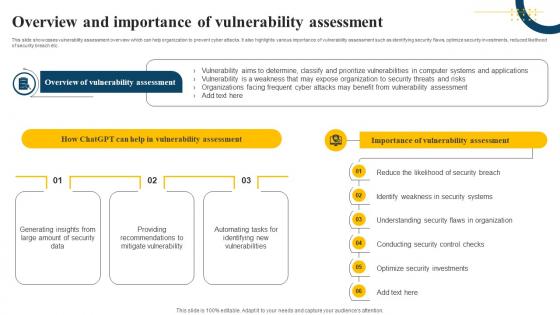 Overview And Importance Of Vulnerability Assessment Impact Of Generative AI SS V
Overview And Importance Of Vulnerability Assessment Impact Of Generative AI SS VThis slide showcases vulnerability assessment overview which can help organization to prevent cyber attacks. It also highlights various importance of vulnerability assessment such as identifying security flaws, optimize security investments, reduced likelihood of security breach etc. Increase audience engagement and knowledge by dispensing information using Overview And Importance Of Vulnerability Assessment Impact Of Generative AI SS V. This template helps you present information on three stages. You can also present information on Amount Of Security, Mitigate Vulnerability, New Vulnerabilities using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
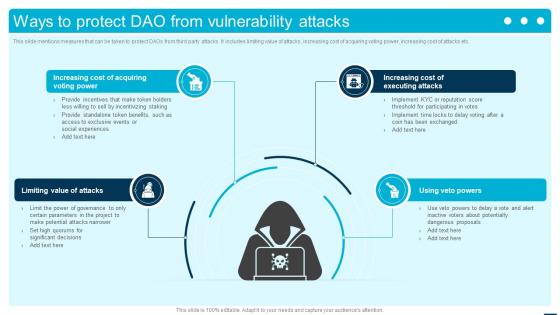 Ways To Protect DAO From Vulnerability Attacks Introduction To Decentralized Autonomous BCT SS
Ways To Protect DAO From Vulnerability Attacks Introduction To Decentralized Autonomous BCT SSThis slide mentions measures that can be taken to protect DAOs from third party attacks. It includes limiting value of attacks, increasing cost of acquiring voting power, increasing cost of attacks etc. Introducing Ways To Protect DAO From Vulnerability Attacks Introduction To Decentralized Autonomous BCT SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Limiting Value Of Attacks, Increasing Cost Of Acquiring Voting Power, Increasing Cost Of Executing Attacks, using this template. Grab it now to reap its full benefits.
-
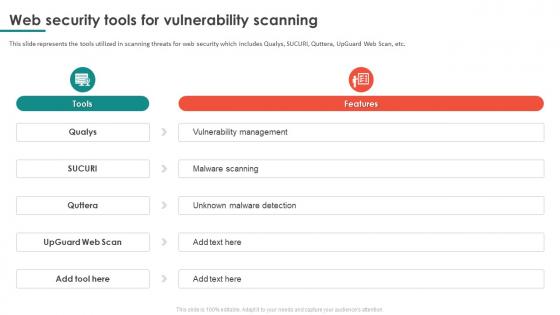 Web Security Tools For Vulnerability Scanning
Web Security Tools For Vulnerability ScanningThis slide represents the tools utilized in scanning threats for web security which includes Qualys, SUCURI, Quttera, UpGuard Web Scan, etc. Introducing our Web Security Tools For Vulnerability Scanning set of slides. The topics discussed in these slides are Vulnerability Scanning, Vulnerability Management, Unknown Malware Detection. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
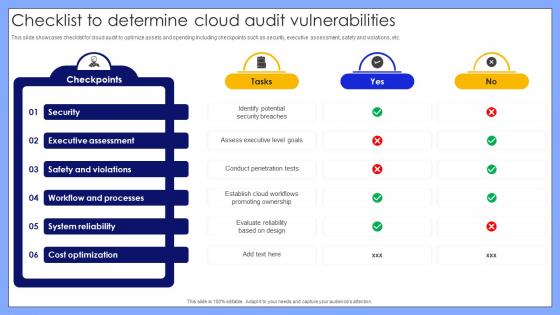 Checklist To Determine Cloud Audit Vulnerabilities
Checklist To Determine Cloud Audit VulnerabilitiesThis slide showcases checklist for cloud audit to optimize assets and spending including checkpoints such as security, executive assessment, safety and violations, etc. Presenting our well structured Checklist To Determine Cloud Audit Vulnerabilities. The topics discussed in this slide are Security, Executive Assessment, Safety And Violations, Workflow And Processes. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
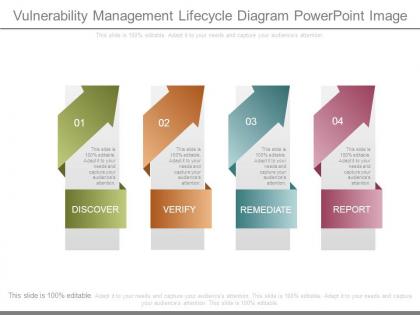 Vulnerability management lifecycle diagram powerpoint image
Vulnerability management lifecycle diagram powerpoint imagePresenting vulnerability management lifecycle diagram powerpoint image. This is a vulnerability management lifecycle diagram powerpoint image. This is a four stage process. The stages in this process are discover, verify, remediate, report.
-
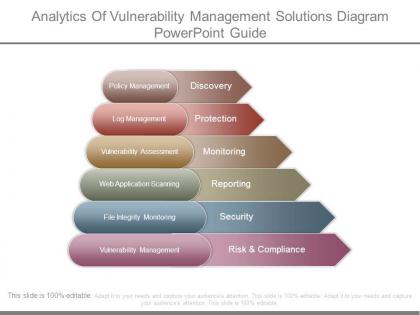 Analytics of vulnerability management solutions diagram powerpoint guide
Analytics of vulnerability management solutions diagram powerpoint guidePresenting analytics of vulnerability management solutions diagram powerpoint guide. This is a analytics of vulnerability management solutions diagram powerpoint guide. This is a six stage process. The stages in this process are discovery, protection, monitoring, reporting, security, risk and compliance.
-
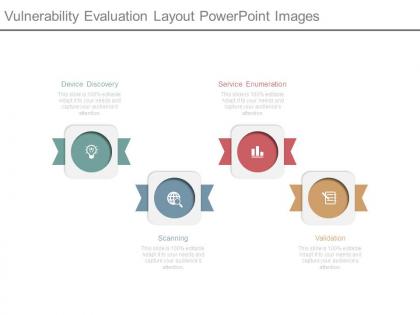 Vulnerability evaluation layout powerpoint images
Vulnerability evaluation layout powerpoint imagesPresenting vulnerability evaluation layout powerpoint images. This is a vulnerability evaluation layout powerpoint images. This is a four stage process. The stages in this process are device discovery, service enumeration, scanning, validation.
-
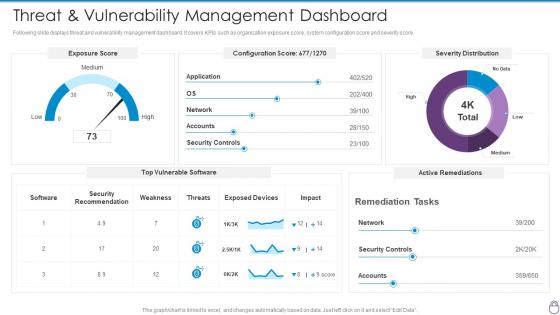 Cybersecurity Risk Management Framework Threat And Vulnerability Management Dashboard
Cybersecurity Risk Management Framework Threat And Vulnerability Management DashboardFollowing slide displays threat and vulnerability management dashboard. It covers KPIs such as organization exposure score, system configuration score and severity score. Present the topic in a bit more detail with this Cybersecurity Risk Management Framework Threat And Vulnerability Management Dashboard. Use it as a tool for discussion and navigation on Exposure Score, Configuration Score, Severity Distribution, Weakness, Threats. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
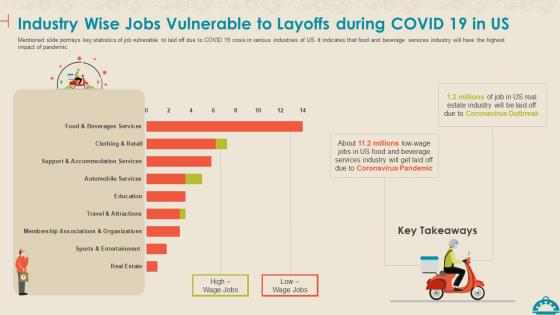 Coronavirus Mitigation Strategies Food Service Industry Jobs Vulnerable Layoffs During Covid 19
Coronavirus Mitigation Strategies Food Service Industry Jobs Vulnerable Layoffs During Covid 19Mentioned slide portrays key statistics of job vulnerable to laid off due to COVID 19 crisis in various industries of US. It indicates that food and beverage services industry will have the highest impact of pandemic. Present the topic in a bit more detail with this Coronavirus Mitigation Strategies Food Service Industry Jobs Vulnerable Layoffs During Covid 19. Use it as a tool for discussion and navigation on Industry Wise Jobs Vulnerable To Layoffs During COVID 19 In US. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Incident Reporting Dashboard Snapshot Vulnerability Administration At Workplace
Incident Reporting Dashboard Snapshot Vulnerability Administration At WorkplaceThe firm will track the various incidents issues faced and resolved in the firm. Deliver an outstanding presentation on the topic using this Incident Reporting Dashboard Snapshot Vulnerability Administration At Workplace. Dispense information and present a thorough explanation of Incident Reporting Dashboard using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Vulnerability Administration At Workplace Current Potential Implications Faced By Firm As Threats
Vulnerability Administration At Workplace Current Potential Implications Faced By Firm As ThreatsThis slide provides information regarding the potential implications or concerns existing in firm in terms of increase in issues related to employees such as lack of expertise, ineffectiveness in handling issues, reported financial losses due to financial threats and data breaches with records exposed. Deliver an outstanding presentation on the topic using this Vulnerability Administration At Workplace Current Potential Implications Faced By Firm As Threats. Dispense information and present a thorough explanation of Potential, Implications, Ineffectiveness using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Vulnerability Administration At Workplace Cyber Threats Management Dashboard
Vulnerability Administration At Workplace Cyber Threats Management DashboardThis slide portrays information regarding the dashboard that firm will use to manage cyber threats. The dashboard will provide clear picture of threats risks prevailing and how they are treated to technical engineers and board level executives. Deliver an outstanding presentation on the topic using this Vulnerability Administration At Workplace Cyber Threats Management Dashboard. Dispense information and present a thorough explanation of Management, Dashboard, Portrays Information using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
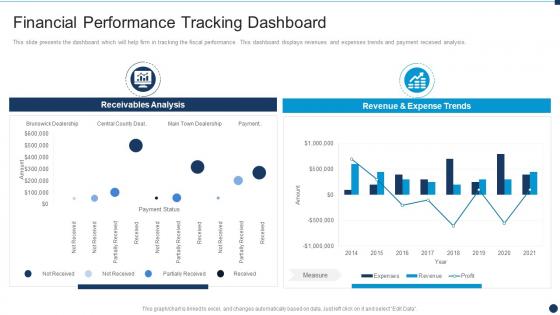 Vulnerability Administration At Workplace Financial Performance Tracking Dashboard
Vulnerability Administration At Workplace Financial Performance Tracking DashboardThis slide presents the dashboard which will help firm in tracking the fiscal performance. This dashboard displays revenues and expenses trends and payment received analysis. Deliver an outstanding presentation on the topic using this Vulnerability Administration At Workplace Financial Performance Tracking Dashboard. Dispense information and present a thorough explanation of Financial, Performance, Dashboard using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Vulnerability Administration At Workplace Statistics Associated To Workplace Threats
Vulnerability Administration At Workplace Statistics Associated To Workplace ThreatsThis slide provides details regarding statistics associated to workplace threats that firms face in terms of data records theft, workplace violence, financial phishing, etc. Present the topic in a bit more detail with this Vulnerability Administration At Workplace Statistics Associated To Workplace Threats. Use it as a tool for discussion and navigation on Cyber Attacks Costs, Organizations, Organizations Have. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
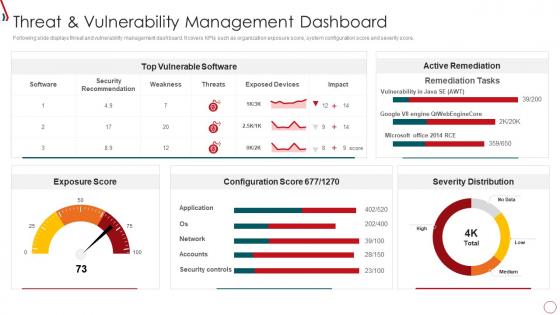 Risk Management Framework For Information Security Threat And Vulnerability
Risk Management Framework For Information Security Threat And VulnerabilityFollowing slide displays threat and vulnerability management dashboard. It covers KPIs such as organization exposure score, system configuration score and severity score. Present the topic in a bit more detail with this Risk Management Framework For Information Security Threat And Vulnerability. Use it as a tool for discussion and navigation on Exposure Score, Top Vulnerable Software, Severity Distribution, Active Remediation, Configuration Score. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
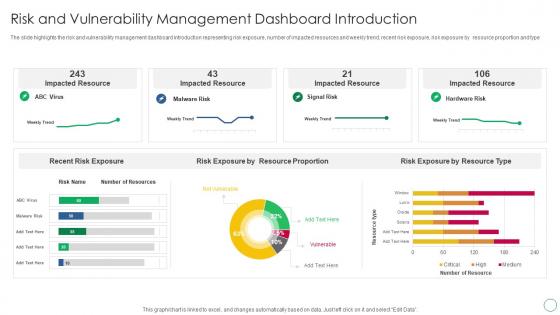 Risk And Vulnerability Management Dashboard Introduction
Risk And Vulnerability Management Dashboard IntroductionThe slide highlights the risk and vulnerability management dashboard introduction representing risk exposure, number of impacted resources and weekly trend, recent risk exposure, risk exposure by resource proportion and type. Presenting our well structured Risk And Vulnerability Management Dashboard Introduction. The topics discussed in this slide are Impacted Resource, Risk Exposure By Resource Proportion, Risk Exposure By Resource Type, Recent Risk Exposure. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
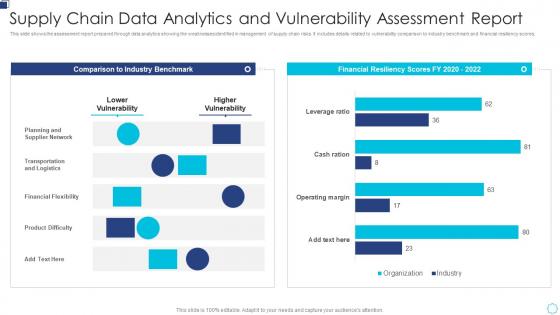 Supply Chain Data Analytics And Vulnerability Assessment Report
Supply Chain Data Analytics And Vulnerability Assessment ReportThis slide shows the assessment report prepared through data analytics showing the weaknesses identified in management of supply chain risks. It includes details related to vulnerability comparison to industry benchmark and financial resiliency scores. Introducing our Supply Chain Data Analytics And Vulnerability Assessment Report set of slides. The topics discussed in these slides are Planning And Supplier Network, Transportation And Logistics, Financial Flexibility. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
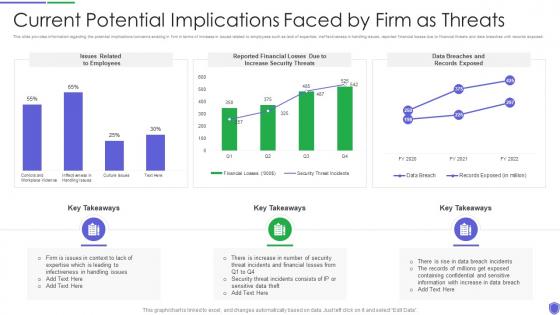 Current potential implications managing critical threat vulnerabilities and security threats
Current potential implications managing critical threat vulnerabilities and security threatsThis slide provides information regarding the potential implications concerns existing in firm in terms of increase in issues related to employees such as lack of expertise, ineffectiveness in handling issues, reported financial losses due to financial threats and data breaches with records exposed. Deliver an outstanding presentation on the topic using this Current Potential Implications Managing Critical Threat Vulnerabilities And Security Threats. Dispense information and present a thorough explanation of Increase Security Threats, Employees using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
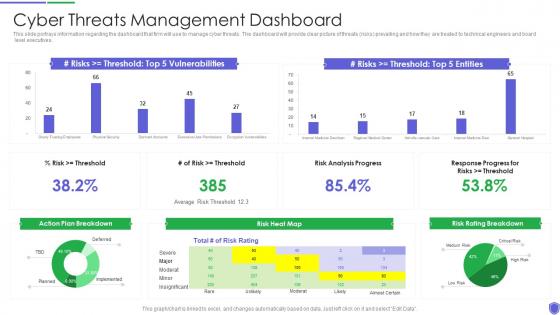 Cyber threats management managing critical threat vulnerabilities and security threats
Cyber threats management managing critical threat vulnerabilities and security threatsThis slide portrays information regarding the dashboard that firm will use to manage cyber threats. The dashboard will provide clear picture of threats risks prevailing and how they are treated to technical engineers and board level executives. Present the topic in a bit more detail with this Cyber Threats Management Managing Critical Threat Vulnerabilities And Security Threats. Use it as a tool for discussion and navigation on Cyber Threats Management Dashboard. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
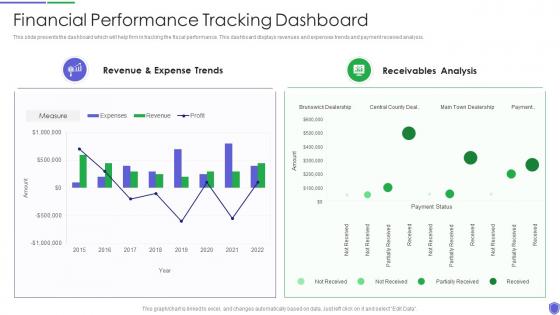 Financial performance tracking managing critical threat vulnerabilities and security threats
Financial performance tracking managing critical threat vulnerabilities and security threatsThis slide presents the dashboard which will help firm in tracking the fiscal performance. This dashboard displays revenues and expenses trends and payment received analysis. Present the topic in a bit more detail with this Financial Performance Tracking Managing Critical Threat Vulnerabilities And Security Threats. Use it as a tool for discussion and navigation on Revenue And Expense Trends, Receivables Analysis. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
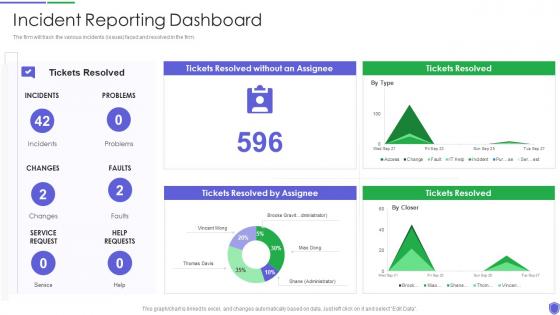 Incident reporting dashboard managing critical threat vulnerabilities and security threats
Incident reporting dashboard managing critical threat vulnerabilities and security threatsThe firm will track the various incidents issues faced and resolved in the firm. Present the topic in a bit more detail with this Incident Reporting Dashboard Managing Critical Threat Vulnerabilities And Security Threats. Use it as a tool for discussion and navigation on Incident Reporting Dashboard. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
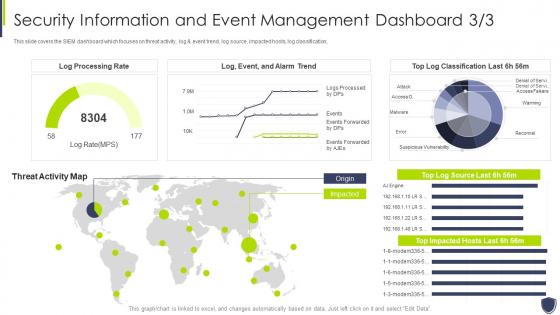 Improve it security vulnerability security information event management dashboard
Improve it security vulnerability security information event management dashboardThis slide covers the SIEM dashboard which focuses on threat activity, log and event trend, log source, impacted hosts, log classification, Deliver an outstanding presentation on the topic using this Improve It Security Vulnerability Security Information Event Management Dashboard. Dispense information and present a thorough explanation of Information, Management, Dashboard using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
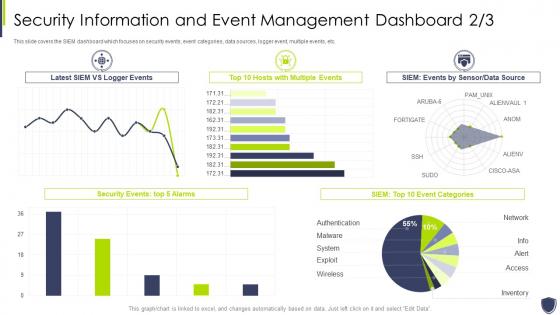 Improve it security with vulnerability event management dashboard snapshot
Improve it security with vulnerability event management dashboard snapshotThis slide covers the SIEM dashboard which focuses on security events, event categories, data sources, logger event, multiple events, etc. Deliver an outstanding presentation on the topic using this Improve It Security With Vulnerability Event Management Dashboard snapshot. Dispense information and present a thorough explanation of Information, Management, Dashboard using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
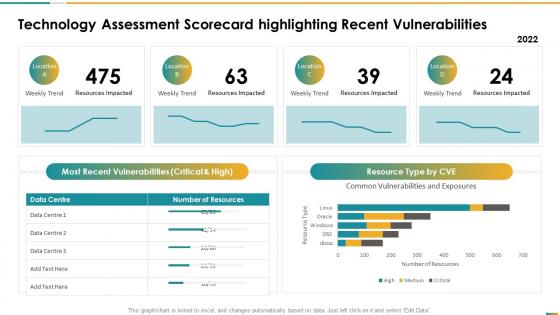 Technology assessment scorecard highlighting recent vulnerabilities
Technology assessment scorecard highlighting recent vulnerabilitiesThis graph or chart is linked to excel, and changes automatically based on data. Just left click on it and select Edit Data Deliver an outstanding presentation on the topic using this Technology Assessment Scorecard Highlighting Recent Vulnerabilities. Dispense information and present a thorough explanation of Weekly Trend, Resources Impacted, Data Centre, Number Resources using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
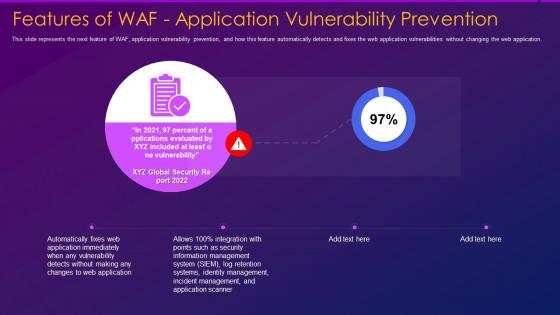 Features of waf application vulnerability prevention web application firewall waf it
Features of waf application vulnerability prevention web application firewall waf itThis slide represents the next feature of WAF, application vulnerability prevention, and how this feature automatically detects and fixes the web application vulnerabilities without changing the web application. Present the topic in a bit more detail with this Features Of Waf Application Vulnerability Prevention Web Application Firewall Waf It. Use it as a tool for discussion and navigation on Automatically, Management, Information. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
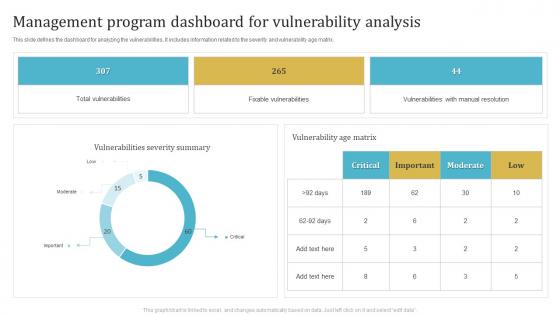 Management Program Dashboard For Vulnerability Analysis
Management Program Dashboard For Vulnerability AnalysisThis slide defines the dashboard for analyzing the vulnerabilities. It includes information related to the severity and vulnerability age matrix. Introducing our Management Program Dashboard For Vulnerability Analysis set of slides. The topics discussed in these slides are Total Vulnerabilities, Fixable Vulnerabilities, Vulnerabilities With Manual Resolution. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Threat And Vulnerability Management Program Analysis Dashboard
Threat And Vulnerability Management Program Analysis DashboardThis slide defines the dashboard for analyzing the threat and vulnerability program. It includes information related to the exposure, configuration and severity score. Presenting our well structured Threat And Vulnerability Management Program Analysis Dashboard. The topics discussed in this slide are Exposure Score, Top Vulnerable Software, Severity Distribution. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
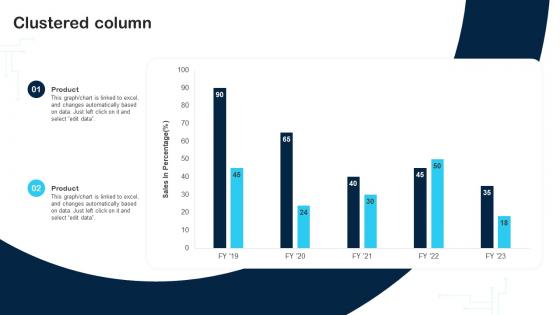 Clustered Column Cybersecurity Incident And Vulnerability Response Playbook
Clustered Column Cybersecurity Incident And Vulnerability Response PlaybookDeliver an outstanding presentation on the topic using this Clustered Column Cybersecurity Incident And Vulnerability Response Playbook. Dispense information and present a thorough explanation of Product, Clustered Column, Sales using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Determining The Ransom Payment Paid By Organizations Over Cybersecurity Incident And Vulnerability
Determining The Ransom Payment Paid By Organizations Over Cybersecurity Incident And VulnerabilityDeliver an outstanding presentation on the topic using this Determining The Ransom Payment Paid By Organizations Over Cybersecurity Incident And Vulnerability. Dispense information and present a thorough explanation of Payments, Response Approaches using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
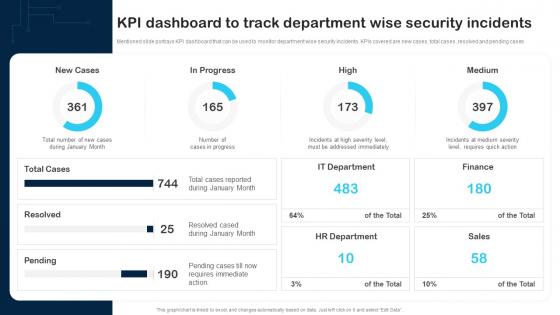 KPI Dashboard To Track Department Wise Security Incidents Cybersecurity Incident And Vulnerability
KPI Dashboard To Track Department Wise Security Incidents Cybersecurity Incident And VulnerabilityMentioned slide portrays KPI dashboard that can be used to monitor department wise security incidents. KPIs covered are new cases, total cases, resolved and pending cases. Present the topic in a bit more detail with this KPI Dashboard To Track Department Wise Security Incidents Cybersecurity Incident And Vulnerability. Use it as a tool for discussion and navigation on New Cases, In Progress, IT Department. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Line Chart Cybersecurity Incident And Vulnerability Response Playbook
Line Chart Cybersecurity Incident And Vulnerability Response PlaybookDeliver an outstanding presentation on the topic using this Line Chart Cybersecurity Incident And Vulnerability Response Playbook. Dispense information and present a thorough explanation of Line Chart using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
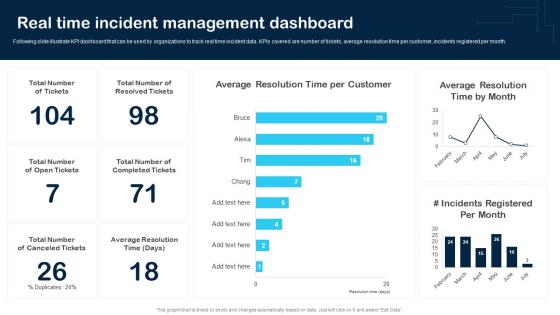 Real Time Incident Management Dashboard Cybersecurity Incident And Vulnerability
Real Time Incident Management Dashboard Cybersecurity Incident And VulnerabilityFollowing slide illustrate KPI dashboard that can be used by organizations to track real time incident data. KPIs covered are number of tickets, average resolution time per customer, incidents registered per month. Present the topic in a bit more detail with this Real Time Incident Management Dashboard Cybersecurity Incident And Vulnerability. Use it as a tool for discussion and navigation on Average Resolution, Customer, Incidents Registered. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
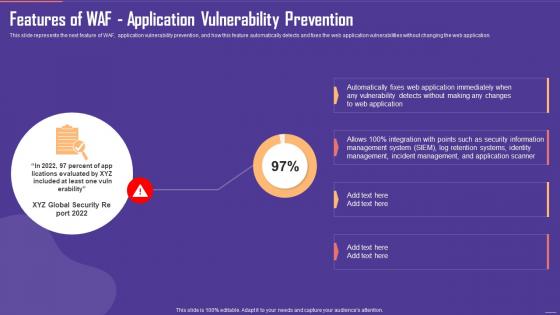 Application Firewall Features of WAF Application Vulnerability Prevention
Application Firewall Features of WAF Application Vulnerability PreventionThis slide represents the next feature of WAF, application vulnerability prevention, and how this feature automatically detects and fixes the web application vulnerabilities without changing the web application. Present the topic in a bit more detail with this Application Firewall Features of WAF Application Vulnerability Prevention. Use it as a tool for discussion and navigation on Identity Management, Incident Management, Application Scanner. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
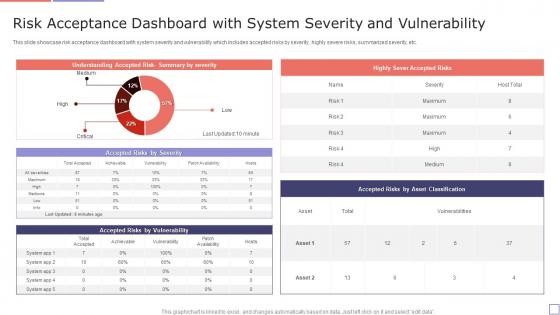 Risk Acceptance Dashboard With System Severity And Vulnerability
Risk Acceptance Dashboard With System Severity And VulnerabilityThis slide showcase risk acceptance dashboard with system severity and vulnerability which includes accepted risks by severity, highly severe risks, summarized severity, etc. Presenting our well-structured Risk Acceptance Dashboard With System Severity And Vulnerability. The topics discussed in this slide are Risk Acceptance, Dashboard, System Severity, Vulnerability. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Vulnerabilities Tracking Dashboard For Secops Ppt Powerpoint Presentation Layouts Topics
Vulnerabilities Tracking Dashboard For Secops Ppt Powerpoint Presentation Layouts TopicsThis slide represents the vulnerabilities tracking dashboard for SecOps. The purpose of this slide is to demonstrate the tracking of vulnerabilities of an organizations assets, services with the most vulnerabilities, mean time to remediate, and the average age of vulnerabilities. Present the topic in a bit more detail with this Vulnerabilities Tracking Dashboard For Secops Ppt Powerpoint Presentation Layouts Topics. Use it as a tool for discussion and navigation on Average Vulnerabilities Asset, Average Age Vulnerabilities. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
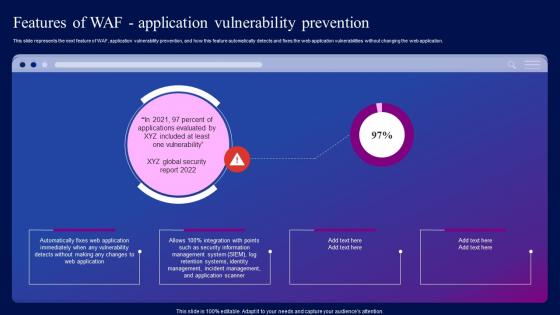 Features Of WAF Application Vulnerability Prevention Ppt Information
Features Of WAF Application Vulnerability Prevention Ppt InformationThis slide represents the next feature of WAF, application vulnerability prevention, and how this feature automatically detects and fixes the web application vulnerabilities without changing the web application. Deliver an outstanding presentation on the topic using this Features Of WAF Application Vulnerability Prevention Ppt Information. Dispense information and present a thorough explanation of Application, Vulnerability, Prevention using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
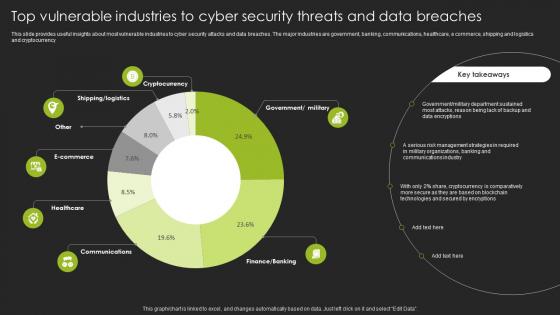 Top Vulnerable Industries To Cyber Security Threats And Data Breaches
Top Vulnerable Industries To Cyber Security Threats And Data BreachesThis slide provides useful insights about most vulnerable industries to cyber security attacks and data breaches. The major industries are government, banking, communications, healthcare, e commerce, shipping and logistics and cryptocurrency Introducing our Top Vulnerable Industries To Cyber Security Threats And Data Breaches set of slides. The topics discussed in these slides are Government, Department. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
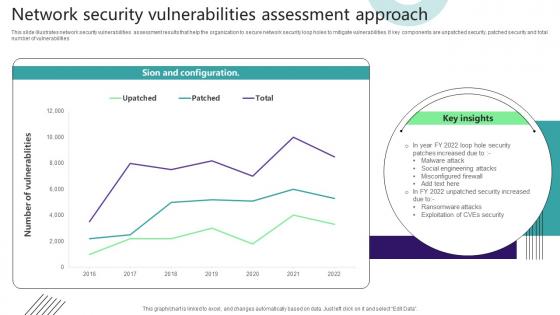 Network Security Vulnerabilities Assessment Approach
Network Security Vulnerabilities Assessment ApproachThis slide illustrates network security vulnerabilities assessment results that help the organization to secure network security loop holes to mitigate vulnerabilities. It key components are unpatched security, patched security and total number of vulnerabilities. Introducing our Network Security Vulnerabilities Assessment Approach set of slides. The topics discussed in these slides are Sion And Configuration. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Security information event management dashboard improve security vulnerability management
Security information event management dashboard improve security vulnerability managementThis slide covers the SIEM dashboard which focuses on server status, log sources, total logs, last log, collectors, log sources etc. Deliver an outstanding presentation on the topic using this Security Information Event Management Dashboard Improve Security Vulnerability Management. Dispense information and present a thorough explanation of Management, Dashboard, Information using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Risk governance network vulnerabilities strategy implementation software development cpb
Risk governance network vulnerabilities strategy implementation software development cpbPresenting this set of slides with name - Risk Governance Network Vulnerabilities Strategy Implementation Software Development Cpb. This is an editable three stages graphic that deals with topics like Risk Governance, Network Vulnerabilities, Strategy Implementation, Software Development to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
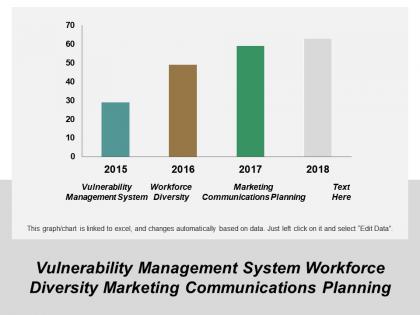 Vulnerability management system workforce diversity marketing communications planning cpb
Vulnerability management system workforce diversity marketing communications planning cpbPresenting this set of slides with name - Vulnerability Management System Workforce Diversity Marketing Communications Planning Cpb. This is an editable four stages graphic that deals with topics like Vulnerability Management System, Workforce Diversity, Marketing Communications Planning to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Web security vulnerabilities click image
Web security vulnerabilities click imagePresenting this set of slides with name Web Security Vulnerabilities Click Image. The topics discussed in these slides are Web Security, Computer, Networking. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
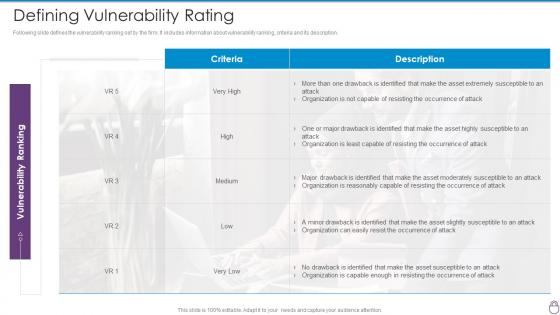 Cybersecurity Risk Management Framework Defining Vulnerability Rating
Cybersecurity Risk Management Framework Defining Vulnerability RatingFollowing slide defines the vulnerability ranking set by the firm. It includes information about vulnerability ranking, criteria and its description. Deliver an outstanding presentation on the topic using this Cybersecurity Risk Management Framework Defining Vulnerability Rating. Dispense information and present a thorough explanation of Occurrence Attack, Asset Moderately Susceptible, Asset Highly Susceptible using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
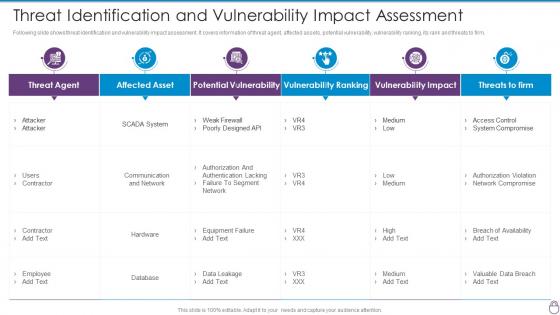 Cybersecurity Risk Management Framework Threat Identification And Vulnerability Impact
Cybersecurity Risk Management Framework Threat Identification And Vulnerability ImpactFollowing slide shows threat identification and vulnerability impact assessment. It covers information of threat agent, affected assets, potential vulnerability, vulnerability ranking, its rank and threats to firm. Deliver an outstanding presentation on the topic using this Cybersecurity Risk Management Framework Threat Identification And Vulnerability Impact. Dispense information and present a thorough explanation of Threat Agent, Affected Asset, Potential Vulnerability, Vulnerability Ranking, Vulnerability Impact using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
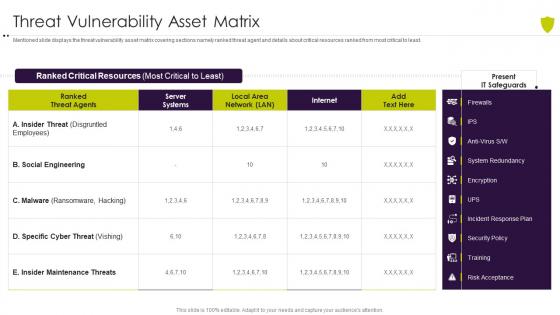 Threat vulnerability asset matrix managing cyber risk in a digital age
Threat vulnerability asset matrix managing cyber risk in a digital ageMentioned slide displays the threat vulnerability asset matrix covering sections namely ranked threat agent and details about critical resources ranked from most critical to least. Present the topic in a bit more detail with this Threat Vulnerability Asset Matrix Managing Cyber Risk In A Digital Age. Use it as a tool for discussion and navigation on Threat Vulnerability Asset Matrix. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
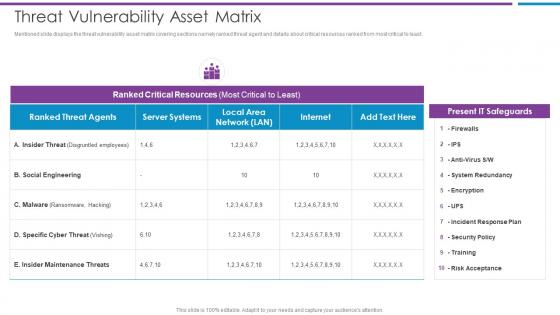 Threat Vulnerability Asset Matrix Risk Based Methodology To Cyber
Threat Vulnerability Asset Matrix Risk Based Methodology To CyberMentioned slide displays the threat vulnerability asset matrix covering sections namely ranked threat agent and details about critical resources ranked from most critical to least.Present the topic in a bit more detail with this Threat Vulnerability Asset Matrix Risk Based Methodology To Cyber Use it as a tool for discussion and navigation on Social Engineering, Ranked Critical Resources, Present IT Safeguards This template is free to edit as deemed fit for your organization. Therefore download it now.
-
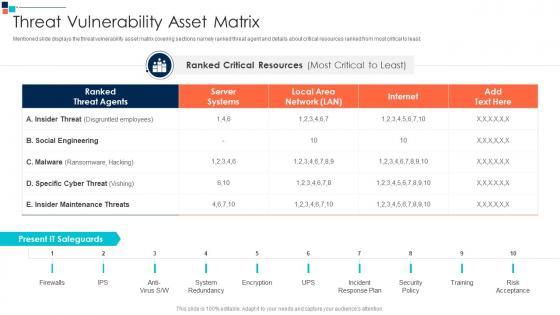 Threat Vulnerability Asset Matrix Introducing A Risk Based Approach To Cyber Security
Threat Vulnerability Asset Matrix Introducing A Risk Based Approach To Cyber SecurityMentioned slide displays the threat vulnerability asset matrix covering sections namely ranked threat agent and details about critical resources ranked from most critical to least.Present the topic in a bit more detail with this Threat Vulnerability Asset Matrix Introducing A Risk Based Approach To Cyber Security Use it as a tool for discussion and navigation on System Redundancy, Incident Response Plan, Security Policy This template is free to edit as deemed fit for your organization. Therefore download it now.
-
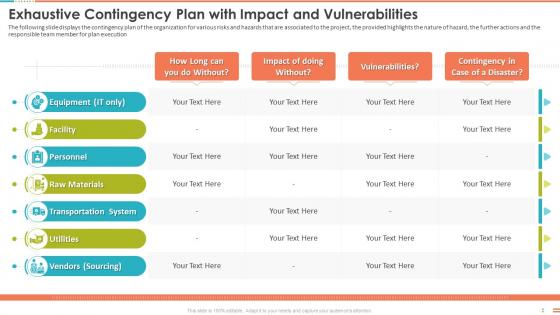 Exhaustive Contingency Plan With Impact And Vulnerabilities Project Management Bundle
Exhaustive Contingency Plan With Impact And Vulnerabilities Project Management BundleThe following slide displays the contingency plan of the organization for various risks and hazards that are associated to the project, the provided highlights the nature of hazard, the further actions and the responsible team member for plan execution. Deliver an outstanding presentation on the topic using this Exhaustive Contingency Plan With Impact And Vulnerabilities Project Management Bundle. Dispense information and present a thorough explanation of Transportation System, Raw Materials, Personnel, Facility, Utilities using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.



