Powerpoint Templates and Google slides for Security Threats
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Icon For Email Security Threats And Attacks
Icon For Email Security Threats And AttacksIntroducing our premium set of slides with Icon For Email Security Threats And Attacks. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Icon, Email Security, Threats And Attacks. So download instantly and tailor it with your information.
-
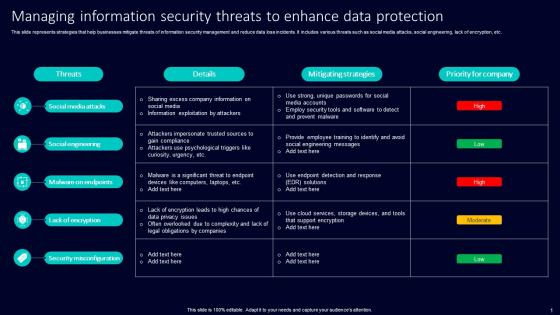 Managing Information Security Threats To Enhance Data Protection
Managing Information Security Threats To Enhance Data ProtectionThis slide represents strategies that help businesses mitigate threats of information security management and reduce data loss incidents. It includes various threats such as social media attacks, social engineering, lack of encryption, etc. Presenting our well structured Managing Information Security Threats To Enhance Data Protection. The topics discussed in this slide are Social Media Attacks, Social Engineering, Malware On Endpoints. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Performing Threat Assessment For Cause Identification Hands On Blockchain Security Risk BCT SS V
Performing Threat Assessment For Cause Identification Hands On Blockchain Security Risk BCT SS VThe following slide illustrates brief introduction of phishing attacks impacting Blockchain to minimize theft of user data. It includes elements such as sharing personal information, sending fake links through emails, stealing private keys, gaining access to account details, data breach, etc. Introducing Performing Threat Assessment For Cause Identification Hands On Blockchain Security Risk BCT SS V to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Security Threats, Attack Vectors, Causes, using this template. Grab it now to reap its full benefits.
-
 National Security Threat In Powerpoint And Google Slides Cpb
National Security Threat In Powerpoint And Google Slides CpbPresenting our National Security Threat In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on National Security Threat This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
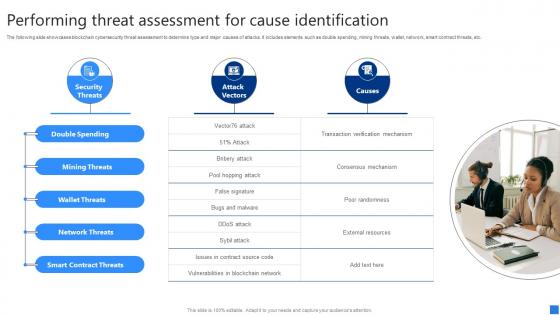 Performing Threat Assessment Securing Blockchain Transactions A Beginners Guide BCT SS V
Performing Threat Assessment Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide showcases blockchain cybersecurity threat assessment to determine type and major causes of attacks. It includes elements such as double spending, mining threats, wallet, network, smart contract threats, etc. Increase audience engagement and knowledge by dispensing information using Performing Threat Assessment Securing Blockchain Transactions A Beginners Guide BCT SS V. This template helps you present information on one stages. You can also present information on Double Spending, Mining Threats, Wallet Threats using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
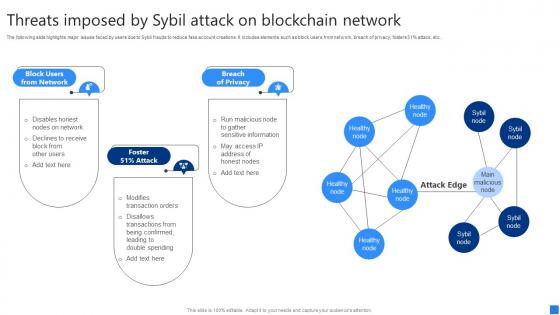 Threats Imposed By Sybil Attack Securing Blockchain Transactions A Beginners Guide BCT SS V
Threats Imposed By Sybil Attack Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide highlights major issues faced by users due to Sybil frauds to reduce fake account creations. It includes elements such as block users from network, breach of privacy, fosters 51percent attack, etc. Introducing Threats Imposed By Sybil Attack Securing Blockchain Transactions A Beginners Guide BCT SS V to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Block Users Network, Foster Attack, Breach Privacy, using this template. Grab it now to reap its full benefits.
-
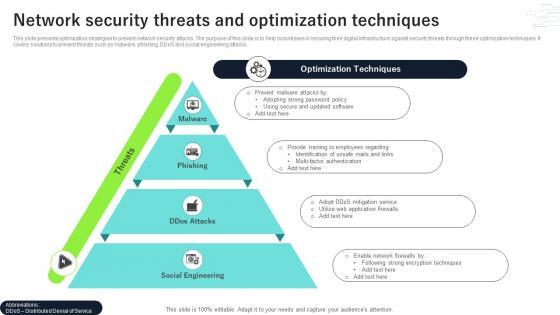 Network Security Threats And Optimization Techniques
Network Security Threats And Optimization TechniquesThis slide presents optimization strategies to prevent network security attacks. The purpose of this slide is to help businesses in securing their digital infrastructure against security threats through these optimization techniques. It covers solutions to prevent threats such as malware, phishing, DDoS and social engineering attacks. Introducing our premium set of slides with Network Security Threats And Optimization Techniques. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Secure, Software, Employees. So download instantly and tailor it with your information.
-
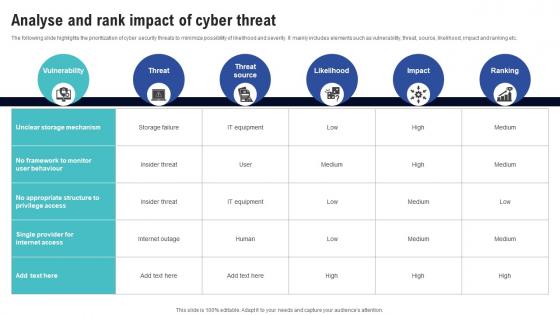 Analyse And Rank Impact Of Cyber Threat Creating Cyber Security Awareness
Analyse And Rank Impact Of Cyber Threat Creating Cyber Security AwarenessThe following slide highlights the prioritization of cyber security threats to minimize possibility of likelihood and severity. It mainly includes elements such as vulnerability, threat, source, likelihood, impact and ranking etc. Present the topic in a bit more detail with this Analyse And Rank Impact Of Cyber Threat Creating Cyber Security Awareness Use it as a tool for discussion and navigation on Likelihood, Impact, Ranking This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Determine Cyber Security Risks And Threats Creating Cyber Security Awareness
Determine Cyber Security Risks And Threats Creating Cyber Security AwarenessThe following slide highlights cyber security risks and threats identified within the company to analyze and protect from potential loss. It includes elements such as objectives, issue identifier, malware, phishing, ransomware, weak credentials, data breach etc. Present the topic in a bit more detail with this Determine Cyber Security Risks And Threats Creating Cyber Security Awareness Use it as a tool for discussion and navigation on Human Errors, Factor Authentication This template is free to edit as deemed fit for your organization. Therefore download it now.
-
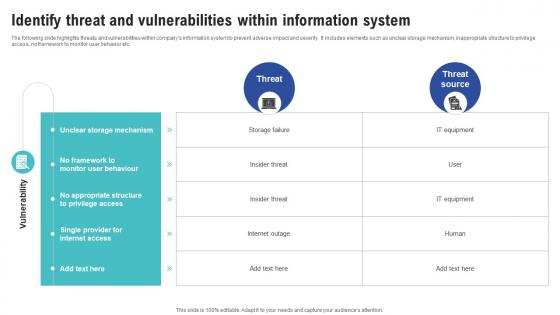 Identify Threat And Vulnerabilities Within Information System Creating Cyber Security Awareness
Identify Threat And Vulnerabilities Within Information System Creating Cyber Security AwarenessThe following slide highlights threats and vulnerabilities within companys information system to prevent adverse impact and severity. It includes elements such as unclear storage mechanism, inappropriate structure to privilege access, no framework to monitor user behavior etc. Deliver an outstanding presentation on the topic using this Identify Threat And Vulnerabilities Within Information System Creating Cyber Security Awareness Dispense information and present a thorough explanation of Unclear Storage Mechanism, Monitor User Behaviour, No Appropriate Structure using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Security Icon For Threat Identification
Cyber Security Icon For Threat IdentificationIntroducing our premium set of slides with Cyber Security Icon For Threat Identification. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cyber Security Icon, Threat Identification. So download instantly and tailor it with your information.
-
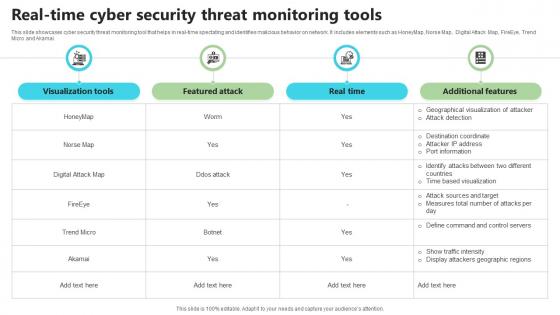 Real Time Cyber Security Threat Monitoring Tools
Real Time Cyber Security Threat Monitoring ToolsThis slide showcases cyber security threat monitoring tool that helps in real-time spectating and identifies malicious behavior on network. It includes elements such as HoneyMap, Norse Map, Digital Attack Map, FireEye, Trend Micro and Akamai. Presenting our well structured Real Time Cyber Security Threat Monitoring Tools. The topics discussed in this slide are Visualization Tools, Real Time, Additional Features. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
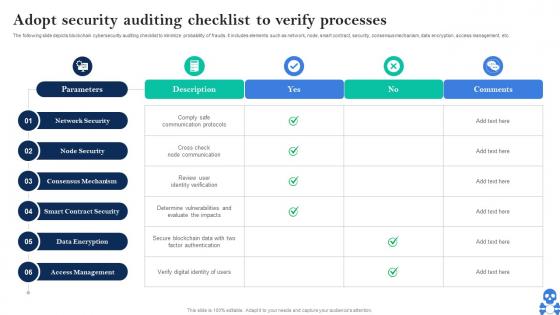 Cyber Threats In Blockchain Adopt Security Auditing Checklist To Verify Processes BCT SS V
Cyber Threats In Blockchain Adopt Security Auditing Checklist To Verify Processes BCT SS VThe following slide depicts blockchain cybersecurity auditing checklist to minimize probability of frauds. It includes elements such as network, node, smart contract, security, consensus mechanism, data encryption, access management, etc. Deliver an outstanding presentation on the topic using this Cyber Threats In Blockchain Adopt Security Auditing Checklist To Verify Processes BCT SS V Dispense information and present a thorough explanation of Consensus Mechanism, Smart Contract Security, Data Encryption using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Threats In Blockchain Backing Up Data To Enhance Security And Efficiency BCT SS V
Cyber Threats In Blockchain Backing Up Data To Enhance Security And Efficiency BCT SS VThe following slide illustrates some methods to regularly backing up data to prevent primary data failures. It includes elements such as regularly backing up, offsite, automated backup and constantly monitoring, etc. Introducing Cyber Threats In Blockchain Backing Up Data To Enhance Security And Efficiency BCT SS V to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Regularly Backup, Automated Backup, Track Backup using this template. Grab it now to reap its full benefits.
-
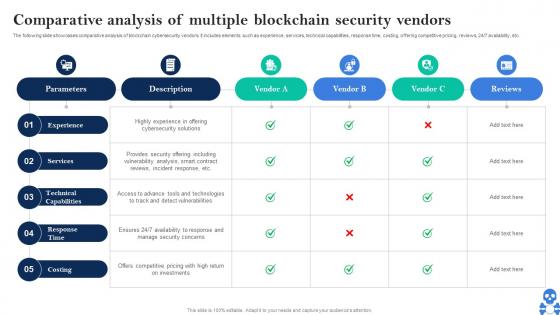 Cyber Threats In Blockchain Comparative Analysis Of Multiple Blockchain Security Vendors BCT SS V
Cyber Threats In Blockchain Comparative Analysis Of Multiple Blockchain Security Vendors BCT SS VThe following slide showcases comparative analysis of blockchain cybersecurity vendors. It includes elements such as experience, services, technical capabilities, response time, costing, offering competitive pricing, reviews, 247 availability, etc. Deliver an outstanding presentation on the topic using this Cyber Threats In Blockchain Comparative Analysis Of Multiple Blockchain Security Vendors BCT SS V Dispense information and present a thorough explanation of Experience, Services, Technical Capabilities using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
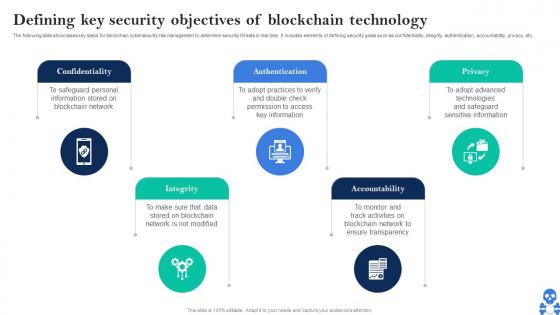 Cyber Threats In Blockchain Defining Key Security Objectives Of Blockchain Technology BCT SS V
Cyber Threats In Blockchain Defining Key Security Objectives Of Blockchain Technology BCT SS VThe following slide showcases key steps for blockchain cybersecurity risk management to determine security threats in real time. It includes elements of defining security goals such as confidentiality, integrity, authentication, accountability, privacy, etc. Introducing Cyber Threats In Blockchain Defining Key Security Objectives Of Blockchain Technology BCT SS V to increase your presentation threshold. Encompassed with Five stages, this template is a great option to educate and entice your audience. Dispence information on Confidentiality, Integrity, Authentication using this template. Grab it now to reap its full benefits.
-
 Cyber Threats In Blockchain Methods To Ensure Smart Contract Security BCT SS V
Cyber Threats In Blockchain Methods To Ensure Smart Contract Security BCT SS VThe following slide showcases some tips and practices to ensure smart contract security. It includes elements such as careful rollouts, keeping them simple, updating and monitoring new developments, reviewing fundamental tradeoffs, etc. Introducing Cyber Threats In Blockchain Methods To Ensure Smart Contract Security BCT SS V to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Careful Rollouts, Contracts Simple, Monitor New Advancements using this template. Grab it now to reap its full benefits.
-
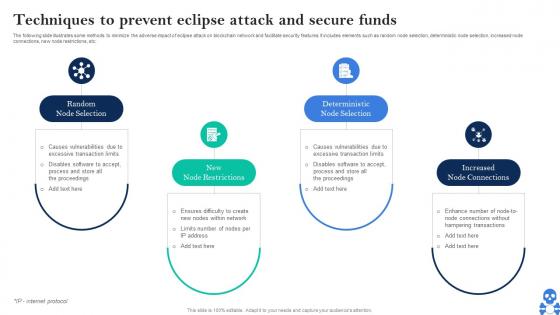 Cyber Threats In Blockchain Techniques To Prevent Eclipse Attack And Secure Funds BCT SS V
Cyber Threats In Blockchain Techniques To Prevent Eclipse Attack And Secure Funds BCT SS VThe following slide illustrates some methods to minimize the adverse impact of eclipse attack on blockchain network and facilitate security features. It includes elements such as random node selection, deterministic node selection, increased node connections, new node restrictions, etc. Introducing Cyber Threats In Blockchain Techniques To Prevent Eclipse Attack And Secure Funds BCT SS V to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Mining Capability, Mining Capabilities, Much Faster Rate using this template. Grab it now to reap its full benefits.
-
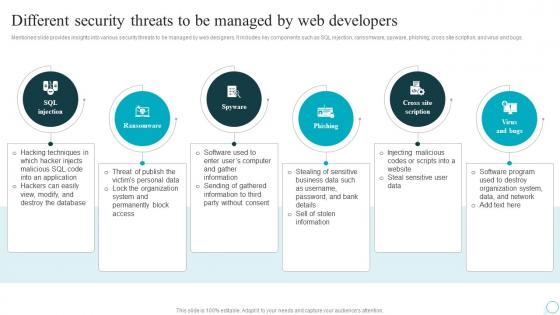 Different Security Threats To Be Managed By Web Strategic Guide For Web Design Company
Different Security Threats To Be Managed By Web Strategic Guide For Web Design CompanyMentioned slide provides insights into various security threats to be managed by web designers. It includes key components such as SQL injection, ransomware, spyware, phishing, cross site scription, and virus and bugs. Increase audience engagement and knowledge by dispensing information using Different Security Threats To Be Managed By Web Strategic Guide For Web Design Company. This template helps you present information on six stages. You can also present information on Injection, Scription, Developers using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
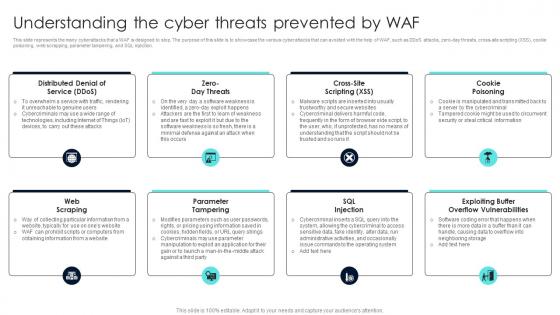 Firewall Network Security Understanding The Cyber Threats Prevented By Waf
Firewall Network Security Understanding The Cyber Threats Prevented By WafThis slide represents the many cyberattacks that a WAF is designed to stop. The purpose of this slide is to showcase the various cyber attacks that can avoided with the help of WAF, such as DDoS attacks, zero-day threats, cross-site scripting XSS, cookie poisoning, web scrapping, parameter tampering, and SQL injection. Introducing Firewall Network Security Understanding The Cyber Threats Prevented By Waf to increase your presentation threshold. Encompassed with Eight stages, this template is a great option to educate and entice your audience. Dispence information on Cookie Poisoning, Sql Injection, Parameter Tampering using this template. Grab it now to reap its full benefits.
-
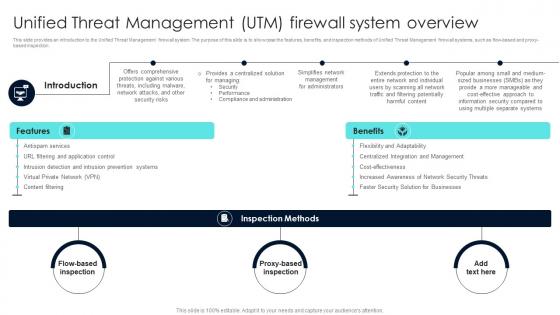 Firewall Network Security Unified Threat Management UTM Firewall System Overview
Firewall Network Security Unified Threat Management UTM Firewall System OverviewThis slide provides an introduction to the Unified Threat Management firewall system. The purpose of this slide is to showcase the features, benefits, and inspection methods of Unified Threat Management firewall systems, such as flow-based and proxy-based inspection. Increase audience engagement and knowledge by dispensing information using Firewall Network Security Understanding Critical Risks Of Firewall Absence This template helps you present information on Three stages. You can also present information on Content Filtering, Faster Security, Flexibility And Adaptability using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
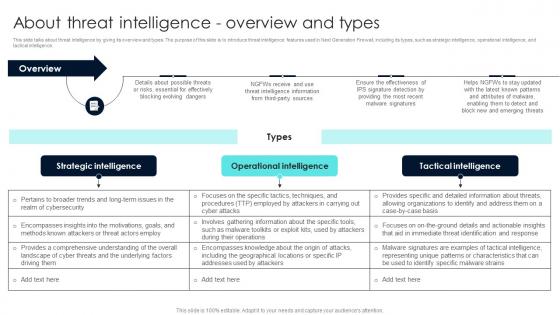 Firewall Network Security About Threat Intelligence Overview And Types
Firewall Network Security About Threat Intelligence Overview And TypesThis slide talks about threat intelligence by giving its overview and types. The purpose of this slide is to introduce threat intelligence features used in Next Generation Firewall, including its types, such as strategic intelligence, operational intelligence, and tactical intelligence. Present the topic in a bit more detail with this Firewall Network Security About Threat Intelligence Overview And Types Use it as a tool for discussion and navigation on Strategic Intelligence, Operational Intelligence, Tactical Intelligence This template is free to edit as deemed fit for your organization. Therefore download it now.
-
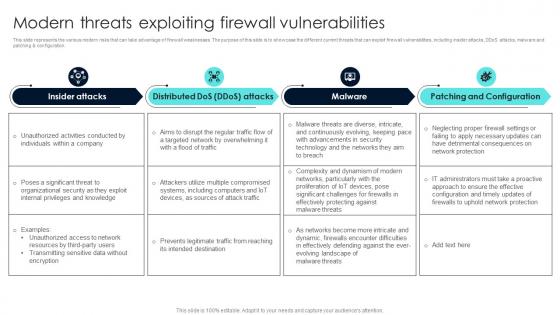 Firewall Network Security Modern Threats Exploiting Firewall Vulnerabilities
Firewall Network Security Modern Threats Exploiting Firewall VulnerabilitiesThis slide represents the various modern risks that can take advantage of firewall weaknesses. The purpose of this slide is to showcase the different current threats that can exploit firewall vulnerabilities, including insider attacks, DDoS attacks, malware and patching and configuration. Introducing Firewall Network Security Modern Threats Exploiting Firewall Vulnerabilities to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Requested Data, NAT Firewall, Forwarding Table using this template. Grab it now to reap its full benefits.
-
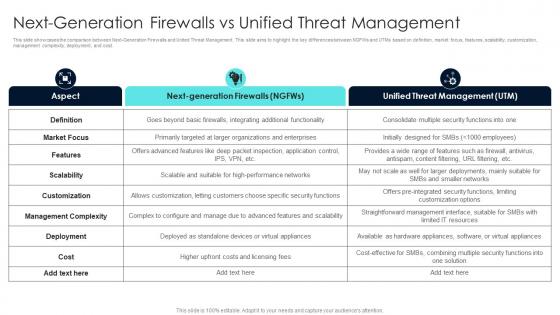 Firewall Network Security Next Generation Firewalls Vs Unified Threat Management
Firewall Network Security Next Generation Firewalls Vs Unified Threat ManagementThis slide showcases the comparison between Next-Generation Firewalls and United Threat Management. This slide aims to highlight the key differences between NGFWs and UTMs based on definition, market focus, features, scalability, customization, management complexity, deployment, and cost. Present the topic in a bit more detail with this Firewall Network Security Next Generation Firewalls Vs Unified Threat Management Use it as a tool for discussion and navigation on Firewall, Features, Providers This template is free to edit as deemed fit for your organization. Therefore download it now.
-
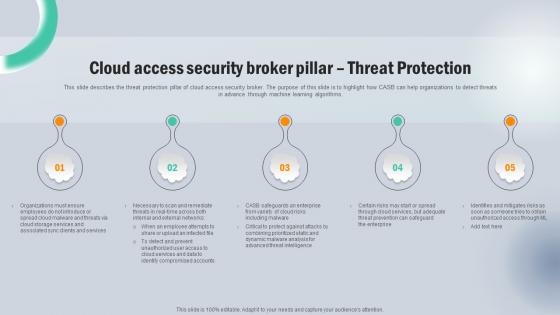 Cloud Access Security Broker Pillar Threat Protection Next Generation CASB
Cloud Access Security Broker Pillar Threat Protection Next Generation CASBThis slide describes the threat protection pillar of cloud access security broker. The purpose of this slide is to highlight how CASB can help organizations to detect threats in advance through machine learning algorithms. Increase audience engagement and knowledge by dispensing information using Cloud Access Security Broker Pillar Threat Protection Next Generation CASB This template helps you present information on five stages. You can also present information on Services, Cloud Storage, Compromised Accounts using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Emerging Cloud Security Risks And Threats Next Generation CASB
Emerging Cloud Security Risks And Threats Next Generation CASBThis slide represents the emerging cloud security risks, and threats organizations can encounter. The purpose of this slide is to highlight the various threats that CASB deployment can help overcome, including VPNs, system misconfiguration, non-zero security permissions, and so on. Present the topic in a bit more detail with this Emerging Cloud Security Risks And Threats Next Generation CASB Use it as a tool for discussion and navigation on Virtual Private Networks, System Misconfigurations, Perimeter Security This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Determine Cyber Security Risks And Threats Implementing Cyber Risk Management Process
Determine Cyber Security Risks And Threats Implementing Cyber Risk Management ProcessThe following slide highlights cyber security risks and threats identified within the company to analyze and protect from potential loss. It includes elements such as objectives, issue identifier, malware, phishing, ransomware, weak credentials, data breach etc. Present the topic in a bit more detail with this Determine Cyber Security Risks And Threats Implementing Cyber Risk Management Process. Use it as a tool for discussion and navigation on Details, Objectives, Issue Identifier. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Security Management Strategies To Mitigate Threats
Cyber Security Management Strategies To Mitigate ThreatsThis slide highlights different strategies that can help businesses in reducing cyber security threats. It further covers attributes such as priority level, description, mitigating strategies, etc. Presenting our well structured Cyber Security Management Strategies To Mitigate Threats. The topics discussed in this slide are Information Disclosure, Service Denial, Tampering. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Impact Analysis Of Cyber Security Threats In Automotive Industry
Impact Analysis Of Cyber Security Threats In Automotive IndustryThis slide highlights influence assessment cyber security risks in automobile industry. The purpose of this slide is to aid businesses in evaluating potential consequences of digital factors. It includes elements such as data privacy, supply chain disruption, etc. Introducing our premium set of slides with Impact Analysis Of Cyber Security Threats In Automotive Industry Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Data Privacy, Intellectual Property, Supply Chain Disruption So download instantly and tailor it with your information.
-
 Application Security Implementation Plan Existing IT Security Infrastructure Threats
Application Security Implementation Plan Existing IT Security Infrastructure ThreatsThis slide highlights the components of the current IT security infrastructure, which are prone to several functionality concerns. Deliver an outstanding presentation on the topic using this Application Security Implementation Plan Existing IT Security Infrastructure Threats. Dispense information and present a thorough explanation of Broken Authentication, Cross Site Scripting, Denial Of Service, Infrastructure Threats using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Implementing Effective Tokenization Existing IT Security Infrastructure Threats
Implementing Effective Tokenization Existing IT Security Infrastructure ThreatsThis slide highlights the components of the current IT security infrastructure, which are prone to several functionality concerns. Present the topic in a bit more detail with this Implementing Effective Tokenization Existing IT Security Infrastructure Threats. Use it as a tool for discussion and navigation on Compliance Challenges, Resource Intensiveness, Faced Security Vulnerabilities. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Top Web Application Security Threats Ppt File Example Topics
Top Web Application Security Threats Ppt File Example TopicsThis slide discusses the vulnerabilities and security threats in web application such as SQL injection, cross-site scripting, etc. Deliver an outstanding presentation on the topic using this Top Web Application Security Threats Ppt File Example Topics. Dispense information and present a thorough explanation of Cross Site Request Forgery, Insecure Direct Object References, Web Application Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Threat Detection Icon Indicator Visualization Security
Threat Detection Icon Indicator Visualization SecurityIntroducing our premium set of slides with Threat Detection Icon Indicator Visualization Security. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Threat Detection, Indicator Visualization Security. So download instantly and tailor it with your information.
-
 Triage Cyber Security To Identify Cyber Threats Icon
Triage Cyber Security To Identify Cyber Threats IconIntroducing our premium set of slides with name Triage Cyber Security To Identify Cyber Threats Icon Ellicudate the Three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Triage Cyber Security, Identify Cyber Threats Icon. So download instantly and tailor it with your information.
-
 Emergency Response Plan Icon For Security Threats
Emergency Response Plan Icon For Security ThreatsPresenting our set of slides with name Emergency Response Plan Icon For Security Threats. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Emergency Response Plan, Icon For Security Threats.
-
 Cyber Security Threat Icon To Prevent Gap
Cyber Security Threat Icon To Prevent GapPresenting our set of slides with name Cyber Security Threat Icon To Prevent Gap. This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cyber Security Threat, Icon Prevent Gap.
-
 Threat Detection Icon To Manage Security Gap
Threat Detection Icon To Manage Security GapPresenting our set of slides with name Threat Detection Icon To Manage Security Gap. This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Threat Detection Icon, Manage Security Gap.
-
 Threat landscape operational security behavioral analytics technologies
Threat landscape operational security behavioral analytics technologiesIf you require a professional template with great design, then this Threat Landscape Operational Security Behavioral Analytics Technologies is an ideal fit for you. Deploy it to enthrall your audience and increase your presentation threshold with the right graphics, images, and structure. Portray your ideas and vision using nine slides included in this complete deck. This template is suitable for expert discussion meetings presenting your views on the topic. With a variety of slides having the same thematic representation, this template can be regarded as a complete package. It employs some of the best design practices, so everything is well-structured. Not only this, it responds to all your needs and requirements by quickly adapting itself to the changes you make. This PPT slideshow is available for immediate download in PNG, JPG, and PDF formats, further enhancing its usability. Grab it by clicking the download button.
-
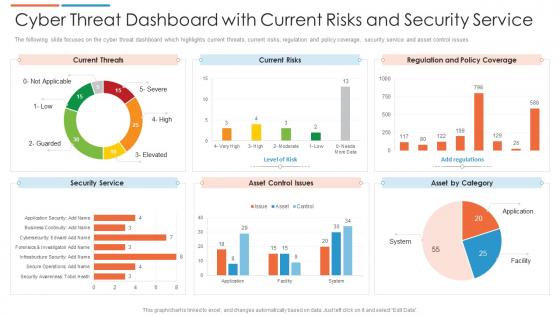 Cyber threat dashboard with current risks and security service
Cyber threat dashboard with current risks and security serviceThe following slide focuses on the cyber threat dashboard which highlights current threats, current risks, regulation and policy coverage, security service and asset control issues. Presenting our well structured Cyber Threat Dashboard With Current Risks And Security Service. The topics discussed in this slide are Current Risks, Current Threats, Security Service. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
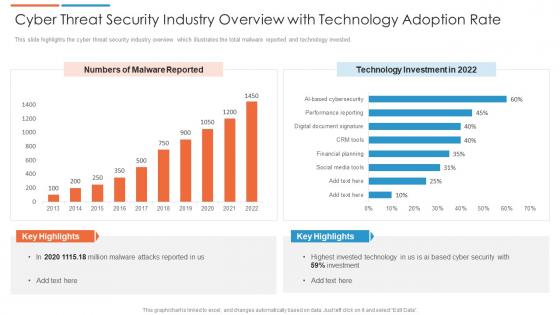 Cyber threat security industry overview with technology adoption rate
Cyber threat security industry overview with technology adoption rateThis slide highlights the cyber threat security industry overview which illustrates the total malware reported and technology invested. Presenting our well structured Cyber Threat Security Industry Overview With Technology Adoption Rate. The topics discussed in this slide are Technology Investment. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
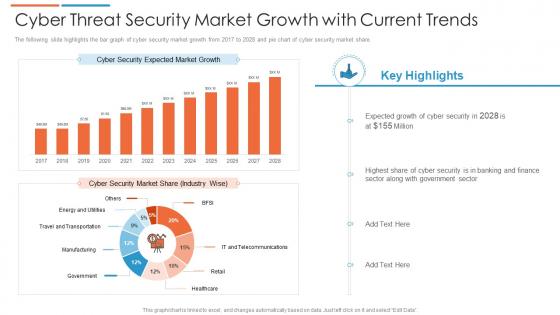 Cyber threat security market growth with current trends
Cyber threat security market growth with current trendsThe following slide highlights the bar graph of cyber security market growth from 2017 to 2028 and pie chart of cyber security market share. Introducing our Cyber Threat Security Market Growth With Current Trends set of slides. The topics discussed in these slides are Cyber Security Market Share, Market Growth, Banking And Finance. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
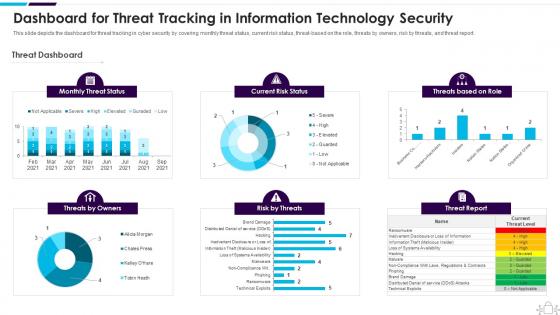 Information Technology Security Dashboard Snapshot Threat Tracking Information Technology Security
Information Technology Security Dashboard Snapshot Threat Tracking Information Technology SecurityThis slide depicts the dashboard for threat tracking in cyber security by covering monthly threat status, current risk status, threat-based on the role, threats by owners, risk by threats, and threat report. Present the topic in a bit more detail with this Information Technology Security Dashboard Threat Tracking Information Technology Security. Use it as a tool for discussion and navigation on Dashboard, Information, Technology. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
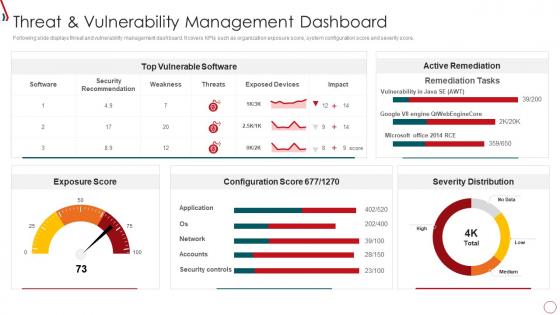 Risk Management Framework For Information Security Threat And Vulnerability
Risk Management Framework For Information Security Threat And VulnerabilityFollowing slide displays threat and vulnerability management dashboard. It covers KPIs such as organization exposure score, system configuration score and severity score. Present the topic in a bit more detail with this Risk Management Framework For Information Security Threat And Vulnerability. Use it as a tool for discussion and navigation on Exposure Score, Top Vulnerable Software, Severity Distribution, Active Remediation, Configuration Score. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Security Threat Activity Discovery Dashboard
Cyber Security Threat Activity Discovery DashboardThe following slide highlights the dashboard for cyber security threat activity discovery to monitor the threats and their management, it includes remote activity security, active remote sessions, threat action, compliance, software patch, asset alarm and threat discovery. Presenting our well structured Cyber Security Threat Activity Discovery Dashboard. The topics discussed in this slide are Cyber Security, Threat Activity, Discovery Dashboard. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Security Hacker Dashboard For Threat Tracking Ppt Powerpoint Presentation Professional File
Security Hacker Dashboard For Threat Tracking Ppt Powerpoint Presentation Professional FileThis slide depicts the dashboard for threat tracking through cyber security measures and ethical hackers by covering monthly threat status, current risk status, threat based on the role, threats by owners, risk by threats, and threat report. Present the topic in a bit more detail with this Security Hacker Dashboard For Threat Tracking Ppt Powerpoint Presentation Professional File. Use it as a tool for discussion and navigation on Threat Dashboard, Current Risk Status, Threats Based On Role. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
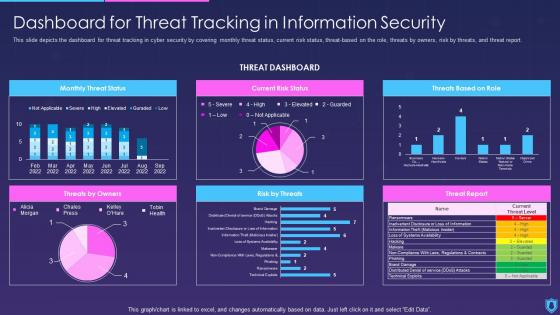 Information Security Dashboard Snapshot For Threat Tracking In Information Security
Information Security Dashboard Snapshot For Threat Tracking In Information SecurityThis slide depicts the dashboard snapshot for threat tracking in cyber security by covering monthly threat status, current risk status, threat based on the role, threats by owners, risk by threats, and threat report. Deliver an outstanding presentation on the topic using this Information Security Dashboard For Threat Tracking In Information Security. Dispense information and present a thorough explanation of Dashboard, Information, Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
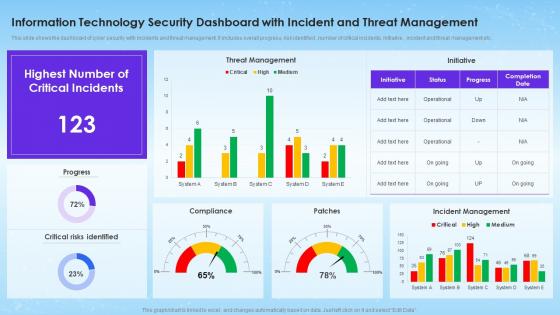 Information Technology Security Dashboard With Incident And Threat Management
Information Technology Security Dashboard With Incident And Threat ManagementThis slide shows the dashboard of cyber security with incidents and threat management. It includes overall progress, risk identified , number of critical incidents, initiative , incident and threat management etc. Introducing our Information Technology Security Dashboard With Incident And Threat Management set of slides. The topics discussed in these slides are Threat Management, Incident Management, Critical Risks Identified. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
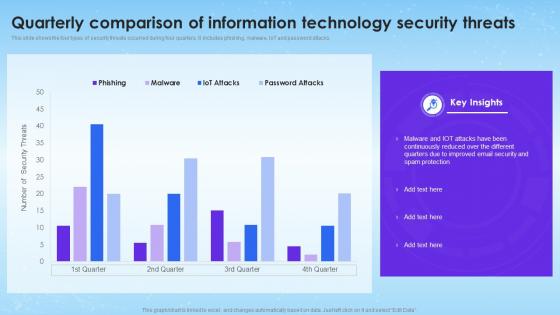 Quarterly Comparison Of Information Technology Security Threats
Quarterly Comparison Of Information Technology Security ThreatsThis slide shows the four types of security threats occurred during four quarters. It includes phishing, malware, IoT and password attacks. Introducing our Quarterly Comparison Of Information Technology Security Threats set of slides. The topics discussed in these slides are Quarterly Comparison, Information Technology, Security Threats. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
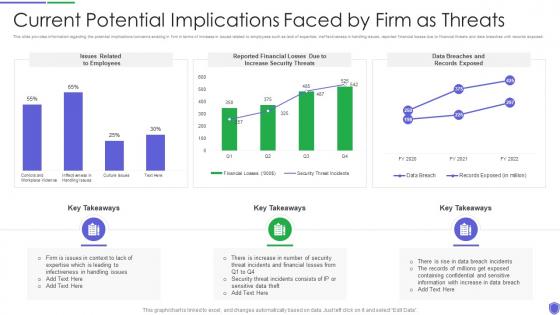 Current potential implications managing critical threat vulnerabilities and security threats
Current potential implications managing critical threat vulnerabilities and security threatsThis slide provides information regarding the potential implications concerns existing in firm in terms of increase in issues related to employees such as lack of expertise, ineffectiveness in handling issues, reported financial losses due to financial threats and data breaches with records exposed. Deliver an outstanding presentation on the topic using this Current Potential Implications Managing Critical Threat Vulnerabilities And Security Threats. Dispense information and present a thorough explanation of Increase Security Threats, Employees using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
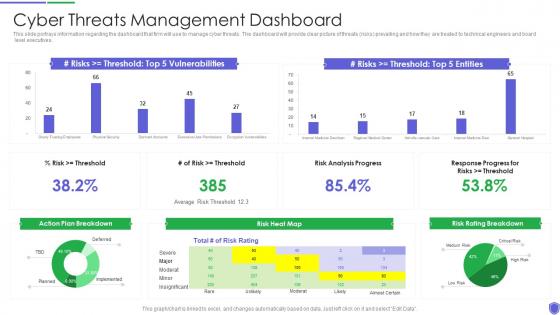 Cyber threats management managing critical threat vulnerabilities and security threats
Cyber threats management managing critical threat vulnerabilities and security threatsThis slide portrays information regarding the dashboard that firm will use to manage cyber threats. The dashboard will provide clear picture of threats risks prevailing and how they are treated to technical engineers and board level executives. Present the topic in a bit more detail with this Cyber Threats Management Managing Critical Threat Vulnerabilities And Security Threats. Use it as a tool for discussion and navigation on Cyber Threats Management Dashboard. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
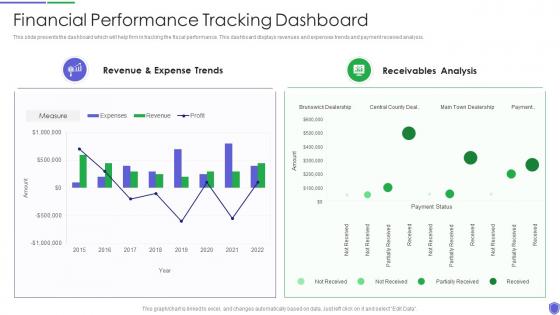 Financial performance tracking managing critical threat vulnerabilities and security threats
Financial performance tracking managing critical threat vulnerabilities and security threatsThis slide presents the dashboard which will help firm in tracking the fiscal performance. This dashboard displays revenues and expenses trends and payment received analysis. Present the topic in a bit more detail with this Financial Performance Tracking Managing Critical Threat Vulnerabilities And Security Threats. Use it as a tool for discussion and navigation on Revenue And Expense Trends, Receivables Analysis. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
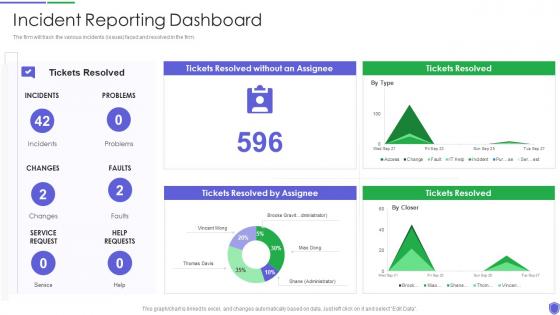 Incident reporting dashboard managing critical threat vulnerabilities and security threats
Incident reporting dashboard managing critical threat vulnerabilities and security threatsThe firm will track the various incidents issues faced and resolved in the firm. Present the topic in a bit more detail with this Incident Reporting Dashboard Managing Critical Threat Vulnerabilities And Security Threats. Use it as a tool for discussion and navigation on Incident Reporting Dashboard. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
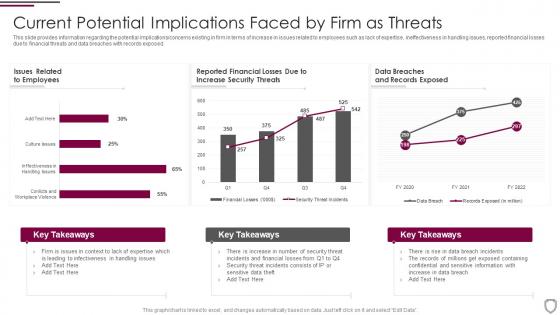 Current potential implications faced by firm as threats corporate security management
Current potential implications faced by firm as threats corporate security managementThis slide provides information regarding the potential implications concerns existing in firm in terms of increase in issues related to employees such as lack of expertise, ineffectiveness in handling issues, reported financial losses due to financial threats and data breaches with records exposed. Present the topic in a bit more detail with this Current Potential Implications Faced By Firm As Threats Corporate Security Management. Use it as a tool for discussion and navigation on Employees, Increase Security Threats. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
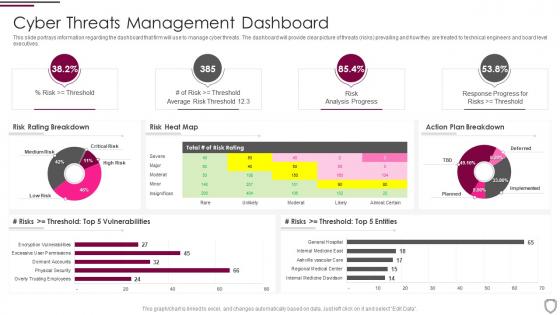 Cyber threats management dashboard corporate security management
Cyber threats management dashboard corporate security managementThis slide portrays information regarding the dashboard that firm will use to manage cyber threats. The dashboard will provide clear picture of threats risks prevailing and how they are treated to technical engineers and board level executives. Deliver an outstanding presentation on the topic using this Cyber Threats Management Dashboard Corporate Security Management. Dispense information and present a thorough explanation of Cyber Threats Management Dashboard using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Statistics associated to workplace threats corporate security management
Statistics associated to workplace threats corporate security managementThis slide provides details regarding statistics associated to workplace threats that firms face in terms of data records theft, workplace violence, financial phishing, etc. Present the topic in a bit more detail with this Statistics Associated To Workplace Threats Corporate Security Management. Use it as a tool for discussion and navigation on Cyber Attacks Costs, Organizations, Data Records. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
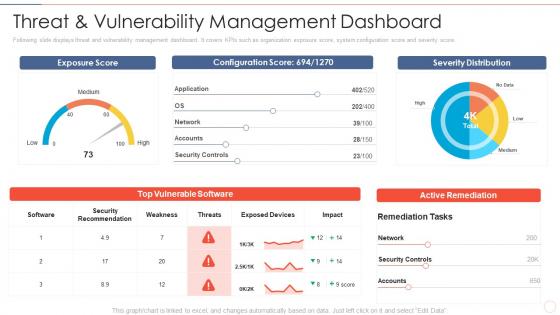 Threat and dashboard effective information security risk management process
Threat and dashboard effective information security risk management processFollowing slide displays threat and vulnerability management dashboard. It covers KPIs such as organization exposure score, system configuration score and severity score. Present the topic in a bit more detail with this Threat And Dashboard Effective Information Security Risk Management Process. Use it as a tool for discussion and navigation on Security Recommendation, Security Controls, Active Remediation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
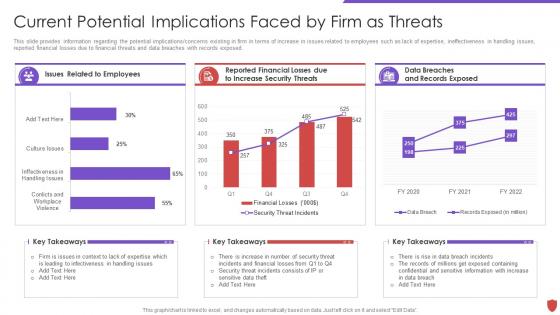 Cyber security risk management current potential implications faced by firm threats
Cyber security risk management current potential implications faced by firm threatsThis slide provides information regarding the potential implications or concerns existing in firm in terms of increase in issues related to employees such as lack of expertise, ineffectiveness in handling issues, reported financial losses due to financial threats and data breaches with records exposed. Present the topic in a bit more detail with this Cyber Security Risk Management Current Potential Implications Faced By Firm Threats. Use it as a tool for discussion and navigation on Issues Related, Employees, Data Breaches, Records Exposed, Reported Financial. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
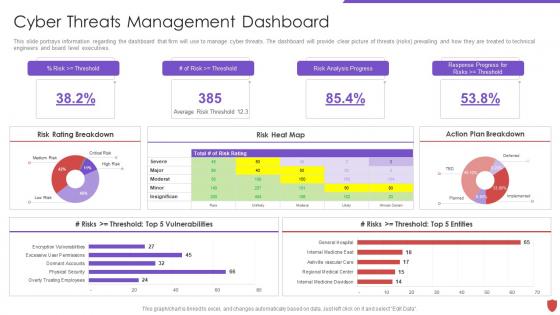 Cyber security risk management cyber threats management dashboard
Cyber security risk management cyber threats management dashboardThis slide portrays information regarding the dashboard that firm will use to manage cyber threats. The dashboard will provide clear picture of threats risks prevailing and how they are treated to technical engineers and board level executives. Deliver an outstanding presentation on the topic using this Cyber Security Risk Management Cyber Threats Management Dashboard. Dispense information and present a thorough explanation of Risk Rating Breakdown, Risk Heat Map, Action Plan Breakdown, Risks, Threshold Top 5 Entities using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
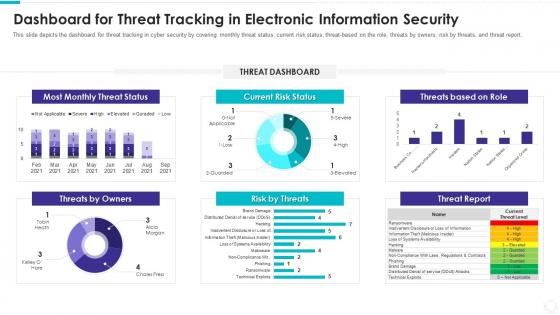 Dashboard snapshot threat tracking electronic information security
Dashboard snapshot threat tracking electronic information securityThis slide depicts the dashboard for threat tracking in cyber security by covering monthly threat status, current risk status, threat based on the role, threats by owners, risk by threats, and threat report. Present the topic in a bit more detail with this Dashboard Snapshot Threat Tracking Electronic Information Security. Use it as a tool for discussion and navigation on Most Monthly Threat Status, Threat Dashboard, Current Risk Status, Threats Based Role, Risk By Threats, Threat Report, Threats Owners. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
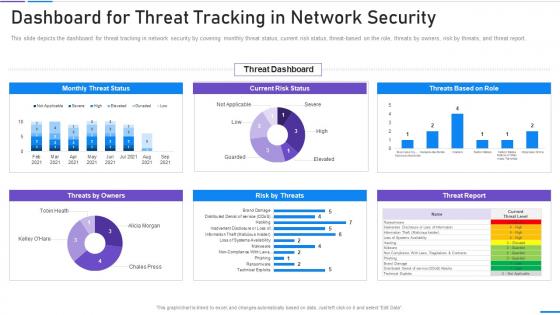 Network Security Dashboard For Threat Tracking In Network Security
Network Security Dashboard For Threat Tracking In Network SecurityThis slide depicts the dashboard for threat tracking in network security by covering monthly threat status, current risk status, threat based on the role, threats by owners, risk by threats, and threat report. Present the topic in a bit more detail with this Network Security Dashboard For Threat Tracking In Network Security. Use it as a tool for discussion and navigation on Dashboard For Threat Tracking In Network Security. This template is free to edit as deemed fit for your organization. Therefore download it now.



