Powerpoint Templates and Google slides for Security Analysis
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
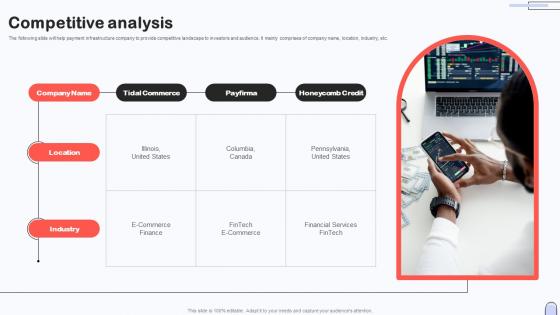 Competitive Analysis Investor Capital Pitch Deck For Secure Digital Payment Platform
Competitive Analysis Investor Capital Pitch Deck For Secure Digital Payment PlatformThe following slide will help payment infrastructure company to provide competitive landscape to investors and audience. It mainly comprises of company name, location, industry, etc. Increase audience engagement and knowledge by dispensing information using Competitive Analysis Investor Capital Pitch Deck For Secure Digital Payment Platform This template helps you present information on four stages. You can also present information on Tidal Commerce, Payfirma, Honeycomb Credit using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Devsecops Best Practices For Secure Global Devsecops Market Research Analysis
Devsecops Best Practices For Secure Global Devsecops Market Research AnalysisThis slide highlights the global market analysis of DevSecOps. The purpose of this slide is to discuss the market factors that provide market analysis, these are market insight, market drivers, geographical analysis, and key companies. Increase audience engagement and knowledge by dispensing information using Devsecops Best Practices For Secure Global Devsecops Market Research Analysis. This template helps you present information on five stages. You can also present information on Rising Internet Penetration Rate, Online Platform, Geographical Analysis, Market Research Analysis using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
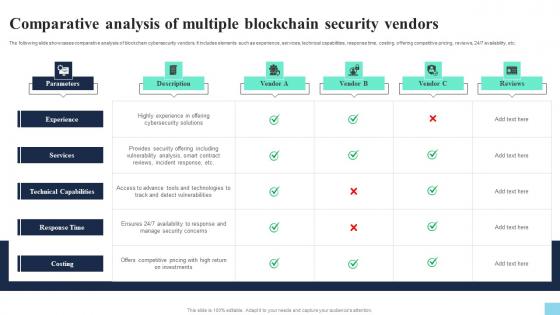 Comparative Analysis Of Multiple Blockchain Security Vendors Hands On Blockchain Security Risk BCT SS V
Comparative Analysis Of Multiple Blockchain Security Vendors Hands On Blockchain Security Risk BCT SS VThe following slide showcases comparative analysis of blockchain cybersecurity vendors. It includes elements such as experience, services, technical capabilities, response time, costing, offering competitive pricing, reviews, 24 7 availability, etc. Deliver an outstanding presentation on the topic using this Comparative Analysis Of Multiple Blockchain Security Vendors Hands On Blockchain Security Risk BCT SS V. Dispense information and present a thorough explanation of Description, Parameters, Experience using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
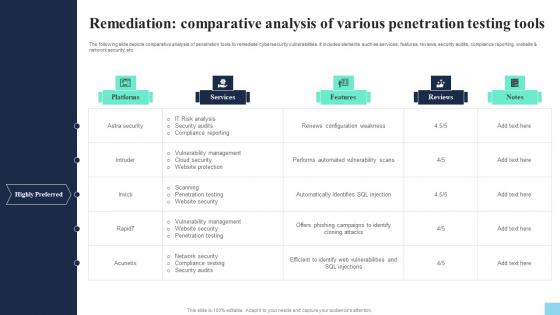 Remediation Comparative Analysis Of Various Penetration Hands On Blockchain Security Risk BCT SS V
Remediation Comparative Analysis Of Various Penetration Hands On Blockchain Security Risk BCT SS VThe following slide depicts comparative analysis of penetration tools to remediate cybersecurity vulnerabilities. It includes elements such as services, features, reviews, security audits, compliance reporting, website and network security, etc. Deliver an outstanding presentation on the topic using this Remediation Comparative Analysis Of Various Penetration Hands On Blockchain Security Risk BCT SS V. Dispense information and present a thorough explanation of Platforms, Services, Features using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Classify Incident Report Template For Cyber Security Analysis
Classify Incident Report Template For Cyber Security AnalysisThis slide exhibits cyber report template categorization for ensuring quick and effective understanding of incident nature, impact and implication. It includes elements such as Michigan, sysnets security, techtargets and thycotics template. Presenting our set of slides with Classify Incident Report Template For Cyber Security Analysis. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Michigan Template, Sysnets Security Template, Thycotics Template.
-
 Comparative Analysis Multiple Securing Blockchain Transactions A Beginners Guide BCT SS V
Comparative Analysis Multiple Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide showcases comparative analysis of blockchain cybersecurity vendors. It includes elements such as experience, services, technical capabilities, response time, costing, offering competitive pricing, reviews, 24 7 availability, etc. Deliver an outstanding presentation on the topic using this Comparative Analysis Multiple Securing Blockchain Transactions A Beginners Guide BCT SS V. Dispense information and present a thorough explanation of Highly Experience Offering, Cybersecurity Solutions, Services using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
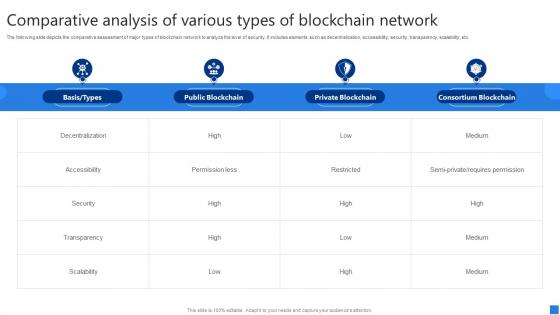 Comparative Analysis Various Securing Blockchain Transactions A Beginners Guide BCT SS V
Comparative Analysis Various Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide depicts the comparative assessment of major types of blockchain network to analyze the level of security. It includes elements such as decentralization, accessibility, security, transparency, scalability, etc. Present the topic in a bit more detail with this Comparative Analysis Various Securing Blockchain Transactions A Beginners Guide BCT SS V. Use it as a tool for discussion and navigation on Decentralization, Accessibility, Security. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Remediation Comparative Analysis Securing Blockchain Transactions A Beginners Guide BCT SS V
Remediation Comparative Analysis Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide depicts comparative analysis of penetration tools to remediate cybersecurity vulnerabilities. It includes elements such as services, features, reviews, security audits, compliance reporting, website and network security, etc. Deliver an outstanding presentation on the topic using this Remediation Comparative Analysis Securing Blockchain Transactions A Beginners Guide BCT SS V. Dispense information and present a thorough explanation of Astra Security, Intruder, Invicti using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
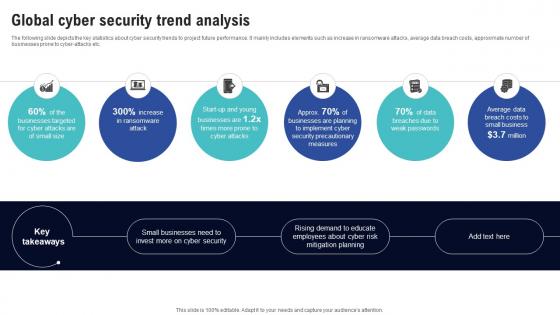 Global Cyber Security Trend Analysis Creating Cyber Security Awareness
Global Cyber Security Trend Analysis Creating Cyber Security AwarenessThe following slide depicts the key statistics about cyber security trends to project future performance. It mainly includes elements such as increase in ransomware attacks, average data breach costs, approximate number of businesses prone to cyber-attacks etc. Introducing Global Cyber Security Trend Analysis Creating Cyber Security Awareness to increase your presentation threshold. Encompassed with Six stages, this template is a great option to educate and entice your audience. Dispence information on Parameters, Probability, Risk Score using this template. Grab it now to reap its full benefits.
-
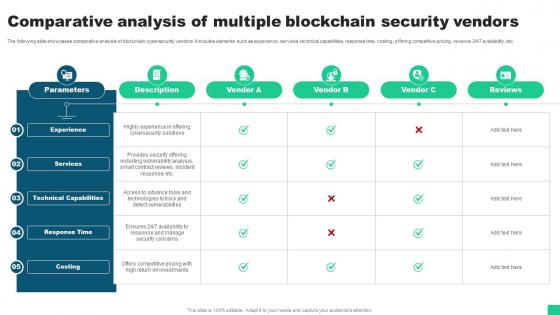 Comparative Analysis Of Multiple Blockchain Security Vendors Guide For Blockchain BCT SS V
Comparative Analysis Of Multiple Blockchain Security Vendors Guide For Blockchain BCT SS VThe following slide showcases comparative analysis of blockchain cybersecurity vendors. It includes elements such as experience, services, technical capabilities, response time, costing, offering competitive pricing, reviews, 24 or 7 availability, etc. Deliver an outstanding presentation on the topic using this Comparative Analysis Of Multiple Blockchain Security Vendors Guide For Blockchain BCT SS V Dispense information and present a thorough explanation of Experience, Services, Technical Capabilities using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
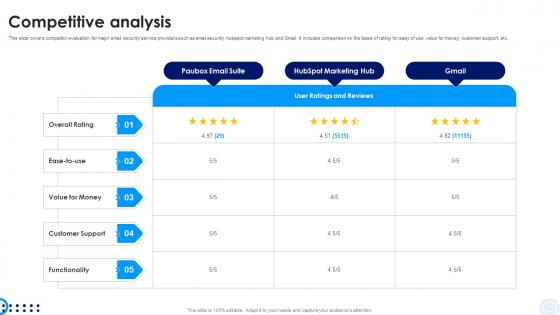 Competitive Analysis Investor Capital Pitch Deck For Pauboxs Secure Email Platform
Competitive Analysis Investor Capital Pitch Deck For Pauboxs Secure Email PlatformThis slide covers competitor evaluation for major email security service providers such as email security, hubspot marketing hub and Gmail. It includes comparison on the basis of rating for easy of use, value for money, customer support, etc. Present the topic in a bit more detail with this Competitive Analysis Investor Capital Pitch Deck For Pauboxs Secure Email Platform Use it as a tool for discussion and navigation on Rating, Value For Money, Customer Support This template is free to edit as deemed fit for your organization. Therefore download it now.
-
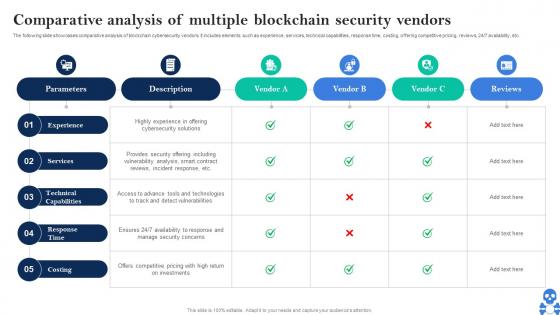 Cyber Threats In Blockchain Comparative Analysis Of Multiple Blockchain Security Vendors BCT SS V
Cyber Threats In Blockchain Comparative Analysis Of Multiple Blockchain Security Vendors BCT SS VThe following slide showcases comparative analysis of blockchain cybersecurity vendors. It includes elements such as experience, services, technical capabilities, response time, costing, offering competitive pricing, reviews, 247 availability, etc. Deliver an outstanding presentation on the topic using this Cyber Threats In Blockchain Comparative Analysis Of Multiple Blockchain Security Vendors BCT SS V Dispense information and present a thorough explanation of Experience, Services, Technical Capabilities using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
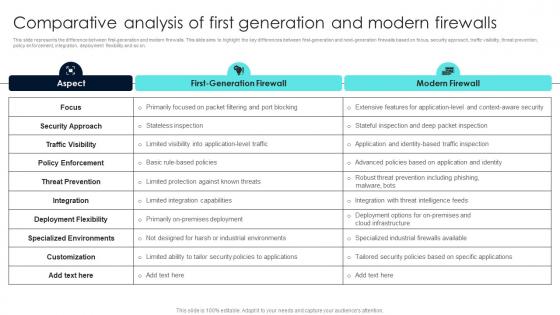 Firewall Network Security Comparative Analysis Of First Generation And Modern Firewalls
Firewall Network Security Comparative Analysis Of First Generation And Modern FirewallsThis slide represents the difference between first-generation and modern firewalls. This slide aims to highlight the key differences between first-generation and next-generation firewalls based on focus, security approach, traffic visibility, threat prevention, policy enforcement, integration, deployment flexibility and so on. Deliver an outstanding presentation on the topic using this Firewall Network Security Comparative Analysis Of First Generation And Modern Firewalls Dispense information and present a thorough explanation of First Generation Firewall, Modern Firewall using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
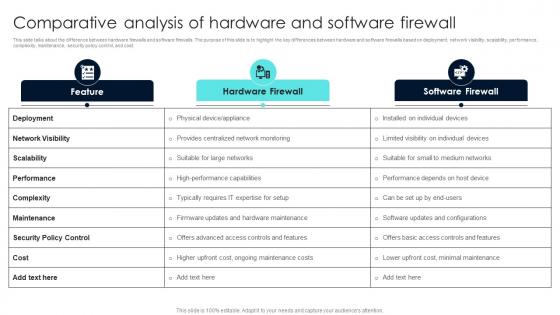 Firewall Network Security Comparative Analysis Of Hardware And Software Firewall
Firewall Network Security Comparative Analysis Of Hardware And Software FirewallThis slide talks about the difference between hardware firewalls and software firewalls. The purpose of this slide is to highlight the key differences between hardware and software firewalls based on deployment, network visibility, scalability, performance, complexity, maintenance, security policy control, and cost. Present the topic in a bit more detail with this Firewall Network Security Comparative Analysis Of Hardware And Software Firewall Use it as a tool for discussion and navigation on Hardware Firewall, Software Firewall, Feature This template is free to edit as deemed fit for your organization. Therefore download it now.
-
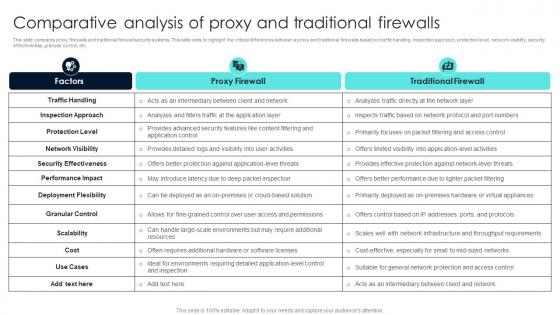 Firewall Network Security Comparative Analysis Of Proxy And Traditional Firewalls
Firewall Network Security Comparative Analysis Of Proxy And Traditional FirewallsThis slide compares proxy firewalls and traditional firewall security systems. This slide aims to highlight the critical differences between a proxy and traditional firewalls based on traffic handling, inspection approach, protection level, network visibility, security effectiveness, granular control, etc. Deliver an outstanding presentation on the topic using this Firewall Network Security Comparative Analysis Of Proxy And Traditional Firewalls Dispense information and present a thorough explanation of Proxy Firewall, Traditional Firewall using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
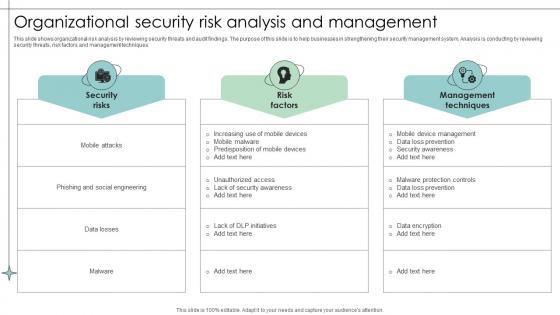 Organizational Security Risk Analysis And Management
Organizational Security Risk Analysis And ManagementThis slide shows organizational risk analysis by reviewing security threats and audit findings. The purpose of this slide is to help businesses in strengthening their security management system. Analysis is conducting by reviewing security threats, risk factors and management techniques. Presenting our well structured Organizational Security Risk Analysis And Management. The topics discussed in this slide are Security, Factors, Management. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
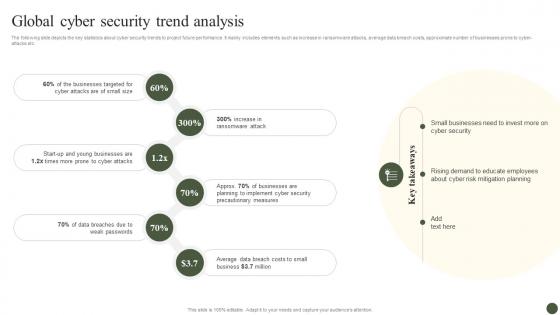 Global Cyber Security Trend Analysis Implementing Cyber Risk Management Process
Global Cyber Security Trend Analysis Implementing Cyber Risk Management ProcessThe following slide depicts the key statistics about cyber security trends to project future performance. It mainly includes elements such as increase in ransomware attacks, average data breach costs, approximate number of businesses prone to cyber-attacks etc. Introducing Global Cyber Security Trend Analysis Implementing Cyber Risk Management Process to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Businesses Targeted, Ransomware Attack, Cyber Attacks, using this template. Grab it now to reap its full benefits.
-
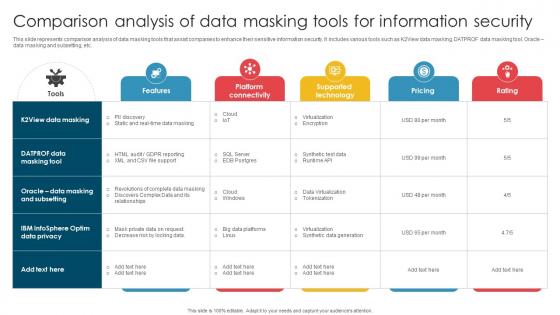 Comparison Analysis Of Data Masking Tools For Information Security
Comparison Analysis Of Data Masking Tools For Information SecurityThis slide represents comparison analysis of data masking tools that assist companies to enhance their sensitive information security. It includes various tools such as K2View data masking, DATPROF data masking tool, Oracle data masking and subsetting, etc. Presenting our well structured Comparison Analysis Of Data Masking Tools For Information Security. The topics discussed in this slide are Virtualization, Synthetic Data Generation, Tokenization. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Impact Analysis Of Cyber Security Threats In Automotive Industry
Impact Analysis Of Cyber Security Threats In Automotive IndustryThis slide highlights influence assessment cyber security risks in automobile industry. The purpose of this slide is to aid businesses in evaluating potential consequences of digital factors. It includes elements such as data privacy, supply chain disruption, etc. Introducing our premium set of slides with Impact Analysis Of Cyber Security Threats In Automotive Industry Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Data Privacy, Intellectual Property, Supply Chain Disruption So download instantly and tailor it with your information.
-
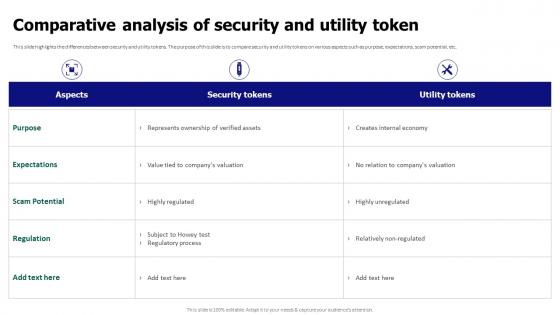 Comparative Analysis Of Security And Utility Token Tokenization For Improved Data Security
Comparative Analysis Of Security And Utility Token Tokenization For Improved Data SecurityThis slide highlights the differences between security and utility tokens. The purpose of this slide is to compare security and utility tokens on various aspects such as purpose, expectations, scam potential, etc. Present the topic in a bit more detail with this Comparative Analysis Of Security And Utility Token Tokenization For Improved Data Security. Use it as a tool for discussion and navigation on Comparative Analysis, Security And Utility Token, Expectations, Scam Potential. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
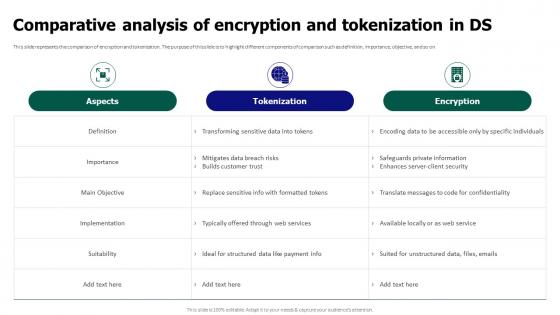 Tokenization For Improved Data Security Comparative Analysis Of Encryption And Tokenization In Ds
Tokenization For Improved Data Security Comparative Analysis Of Encryption And Tokenization In DsThis slide represents the comparison of encryption and tokenization. The purpose of this slide is to highlight different components of comparison such as definition, importance, objective, and so on. Deliver an outstanding presentation on the topic using this Tokenization For Improved Data Security Comparative Analysis Of Encryption And Tokenization In Ds. Dispense information and present a thorough explanation of Comparative Analysis, Encryption And Tokenization, Safeguards Private Information using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
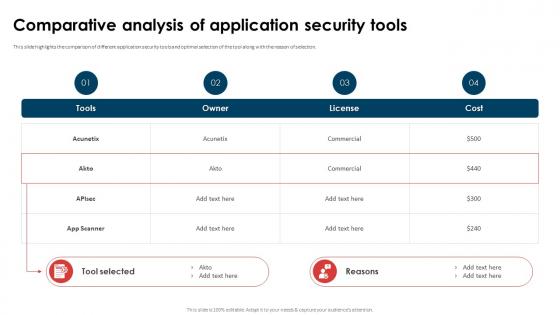 Application Security Implementation Plan Comparative Analysis Of Application Security Tools
Application Security Implementation Plan Comparative Analysis Of Application Security ToolsThis slide highlights the comparison of different application security tools and optimal selection of the tool along with the reason of selection. Deliver an outstanding presentation on the topic using this Application Security Implementation Plan Comparative Analysis Of Application Security Tools. Dispense information and present a thorough explanation of Comparative Analysis, Application Security Tools, Commercial, License using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
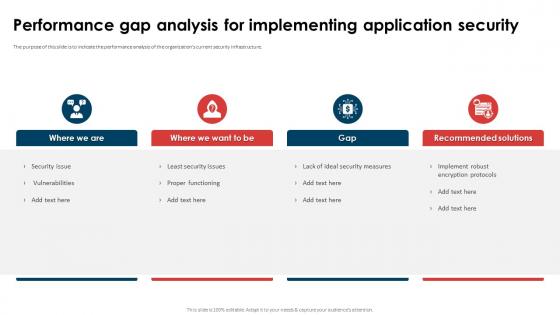 Application Security Implementation Plan Performance Gap Analysis For Implementing Application Security
Application Security Implementation Plan Performance Gap Analysis For Implementing Application SecurityThe purpose of this slide is to indicate the performance analysis of the organizations current security infrastructure. Increase audience engagement and knowledge by dispensing information using Application Security Implementation Plan Performance Gap Analysis For Implementing Application Security. This template helps you present information on four stages. You can also present information on Proper Functioning, Implement Robust Encryption Protocols, Lack Of Ideal Security Measures using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
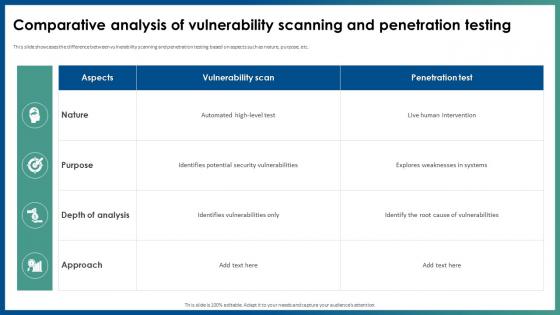 Application Security Comparative Analysis Of Vulnerability Scanning And Penetration Testing
Application Security Comparative Analysis Of Vulnerability Scanning And Penetration TestingThis slide showcases the difference between vulnerability scanning and penetration testing based on aspects such as nature, purpose, etc. Present the topic in a bit more detail with this Application Security Comparative Analysis Of Vulnerability Scanning And Penetration Testing. Use it as a tool for discussion and navigation on Explores Weaknesses In Systems, Comparative Analysis, Vulnerability Scanning, Penetration Testing. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
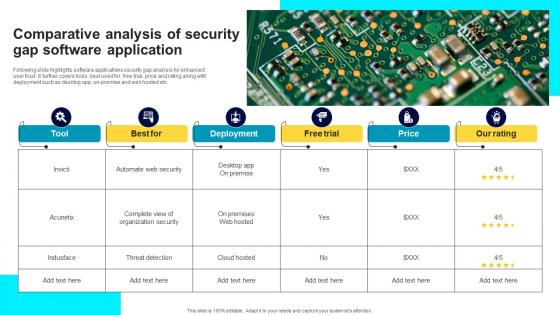 Comparative Analysis Of Security Gap Software Application
Comparative Analysis Of Security Gap Software ApplicationFollowing slide highlights software applications security gap analysis for enhanced user trust. It further covers tools, best used for, free trial, price and rating along with deployment such as desktop app, on-premise and web hosted etc. Introducing our Comparative Analysis Of Security Gap Software Application set of slides. The topics discussed in these slides are Tool, Deployment, Free Trial, Price, Our Rating. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
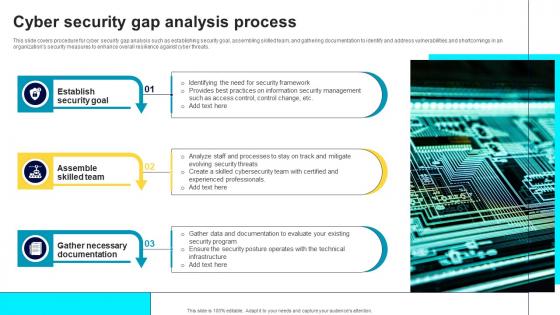 Cyber Security Gap Analysis Process
Cyber Security Gap Analysis ProcessThis slide covers procedure for cyber security gap analysis such as establishing security goal, assembling skilled team, and gathering documentation to identify and address vulnerabilities and shortcomings in an organizations security measures to enhance overall resilience against cyber threats. Presenting our set of slides with name Cyber Security Gap Analysis Process. This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Establish Security Goal, Assemble Skilled Team, Gather Necessary Documentation.
-
 Security Gap Analysis Icon For IT Team
Security Gap Analysis Icon For IT TeamPresenting our set of slides with name Security Gap Analysis Icon For IT Team. This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Security Gap Analysis Icon, IT Team.
-
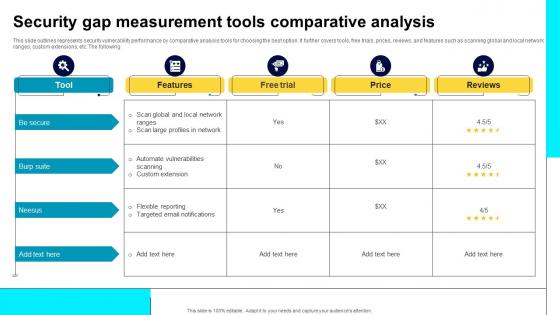 Security Gap Measurement Tools Comparative Analysis
Security Gap Measurement Tools Comparative AnalysisThis slide outlines represents security vulnerability performance by comparative analysis tools for choosing the best option. It further covers tools, free trials, prices, reviews, and features such as scanning global and local network ranges, custom extensions, etc. The following. Introducing our Security Gap Measurement Tools Comparative Analysis set of slides. The topics discussed in these slides are Scan Global, Local Network Ranges, Automate Vulnerabilities, Custom Extension. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
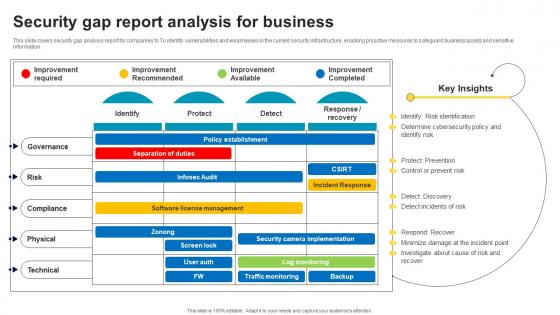 Security Gap Report Analysis For Business
Security Gap Report Analysis For BusinessThis slide covers security gap analysis report for companies to To identify vulnerabilities and weaknesses in the current security infrastructure, enabling proactive measures to safeguard business assets and sensitive information. Introducing our Security Gap Report Analysis For Business set of slides. The topics discussed in these slides are Improvement Required, Improvement Recommended, Improvement Available, Improvement Completed. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
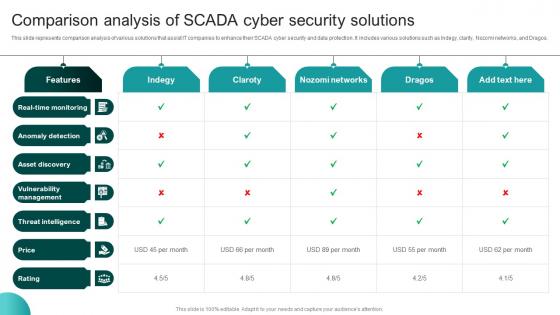 Comparison Analysis Of SCADA Cyber Security Solutions
Comparison Analysis Of SCADA Cyber Security SolutionsThis slide represents comparison analysis of various solutions that assist IT companies to enhance their SCADA cyber security and data protection. It includes various solutions such as Indegy, clarity, Nozomi networks, and Dragos. Presenting our well structured Comparison Analysis Of SCADA Cyber Security Solutions The topics discussed in this slide are Anomaly Detection, Asset Discovery, Vulnerability Management. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Comparative Analysis Of Mobile Security Tools
Comparative Analysis Of Mobile Security ToolsThis slide showcases mobile security software applications comparison matrix and includes anti-theft protection, remote SMS control, call blocking, web protection, and wi-fi protection. Introducing our Comparative Analysis Of Mobile Security Tools set of slides. The topics discussed in these slides are Anti- Theft Protection, Remote Sms Control, Call Blocking, Web Protection. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
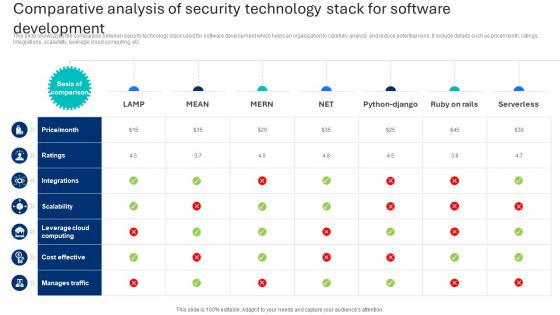 Comparative Analysis Of Security Technology Stack For Software Development
Comparative Analysis Of Security Technology Stack For Software DevelopmentThis slide showcases the comparison between security technology stack used for software development which helps an organization to carefully analyze and reduce potential risks. It include details such as pricemonth, ratings, integrations, scalability, leverage cloud computing, etc. Introducing our Comparative Analysis Of Security Technology Stack For Software Development set of slides. The topics discussed in these slides are Scalability, Cost Effective, Manages Traffic. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
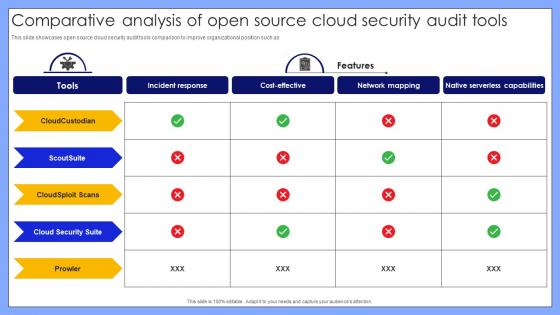 Comparative Analysis Of Open Source Cloud Security Audit Tools
Comparative Analysis Of Open Source Cloud Security Audit ToolsThis slide showcases open source cloud security audit tools comparison to improve organizational position such as. Introducing our Comparative Analysis Of Open Source Cloud Security Audit Tools set of slides. The topics discussed in these slides are Comparative Analysis, Cloud Security Audit Tools, Audit Tools Comparison, Organizational Position. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Comparative Analysis Of ATP Cyber Security Tools
Comparative Analysis Of ATP Cyber Security ToolsThis slide depicts the comparative analysis of ATP cyber security tools. Its aim is to use the tools to protect the system from advanced threats. This slide include Microsoft defender, ESET endpoint, Palo Alto network, Fortinet sandbox. Presenting our set of slides with name Comparative Analysis Of ATP Cyber Security Tools. This exhibits information on Four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Microsoft Defender, ESET Endpoint, Palo Alto Network, Fortinet Sandbox.
-
 Competitive Analysis Smart Farming Technology Pitch Deck For Food Security
Competitive Analysis Smart Farming Technology Pitch Deck For Food SecurityFollowing slide represents competitive analysis of company. It includes information about company names, founded year, growth score, location, total funding etc.Deliver an outstanding presentation on the topic using this Competitive Analysis Smart Farming Technology Pitch Deck For Food Security Dispense information and present a thorough explanation of Description, Founded Year, Growth Score using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
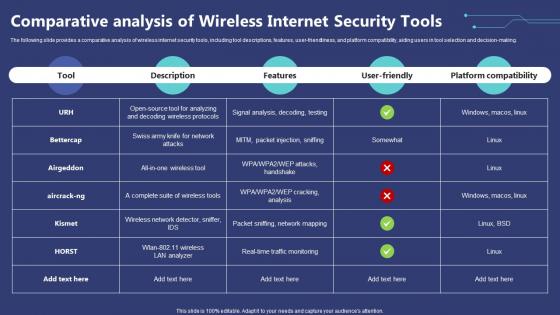 Comparative Analysis Of Wireless Internet Security Tools
Comparative Analysis Of Wireless Internet Security ToolsThe following slide provides a comparative analysis of wireless internet security tools, including tool descriptions, features, user-friendliness, and platform compatibility, aiding users in tool selection and decision-making. Introducing our Comparative Analysis Of Wireless Internet Security Tools set of slides. The topics discussed in these slides are Comparative, Analysis, Security Tools. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Comparative Analysis Of Csirt And Soc Cyber Security
Comparative Analysis Of Csirt And Soc Cyber SecurityThis slide showcases difference between CSIRT and SOC cyber security. The main purpose of this template is assisting business in determining most suitable approach for cyber security. This I Introducing our premium set of slides with Comparative Analysis Of Csirt And Soc Cyber Security. Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Through Investigation, Analysis And Improvement, Forensics Analysis. So download instantly and tailor it with your information.
-
 Comparative Analysis Of Server Security Tools
Comparative Analysis Of Server Security ToolsFollowing slide showcases server security comparative tools to choose best option, also including tools, file backup, unified dashboard, starting price, and multiple platform support. Introducing our Comparative Analysis Of Server Security Tools set of slides. The topics discussed in these slides are Avast Server Antivirus, Syxsense Cortex, Platform Support. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Strategic leadership for managing cyber security risks analysis powerpoint slide designs
Strategic leadership for managing cyber security risks analysis powerpoint slide designsPresenting strategic leadership for managing cyber security risks analysis powerpoint slide designs. This is a strategic leadership for managing cyber security risks analysis powerpoint slide designs. This is a three stage process. The stages in this process are threat agents, attack methods, attacker objectives.
-
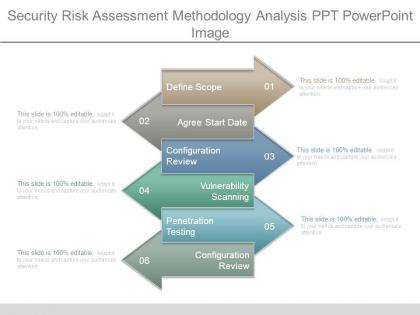 Security risk assessment methodology analysis ppt powerpoint image
Security risk assessment methodology analysis ppt powerpoint imagePresenting security risk assessment methodology analysis ppt powerpoint image. This is a security risk assessment methodology analysis ppt powerpoint image. This is a six stage process. The stages in this process are define scope, agree start date, configuration review, vulnerability scanning, penetration testing, configuration review.
-
 Security analysis diagram template powerpoint slide backgrounds
Security analysis diagram template powerpoint slide backgroundsPresenting security analysis diagram template powerpoint slide backgrounds. This is a security analysis diagram template powerpoint slide backgrounds. This is a four stage process. The stages in this process are level of technology, sector selection, financial analysis, company analysis.
-
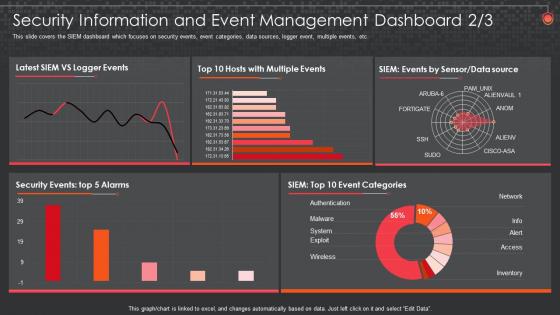 Information And Event Management Dashboard Snapshot Siem For Security Analysis
Information And Event Management Dashboard Snapshot Siem For Security AnalysisThis slide covers the SIEM dashboard which focuses on security events, event categories, data sources, logger event, multiple events, etc. Deliver an outstanding presentation on the topic using this Information And Event Management Dashboard Snapshot Siem For Security Analysis. Dispense information and present a thorough explanation of Information, Management, Dashboard using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
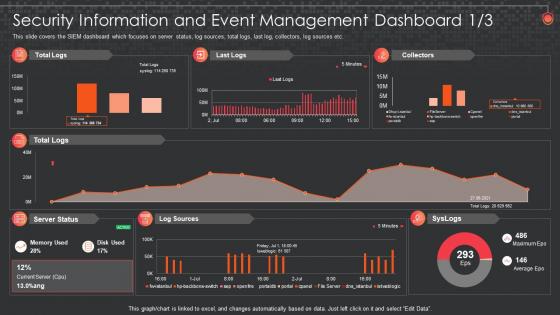 Security Information And Event Management Dashboard Siem For Security Analysis
Security Information And Event Management Dashboard Siem For Security AnalysisThis slide covers the SIEM dashboard which focuses on server status, log sources, total logs, last log, collectors, log sources etc. Deliver an outstanding presentation on the topic using this Security Information And Event Management Dashboard Siem For Security Analysis. Dispense information and present a thorough explanation of Information, Management, Dashboard using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
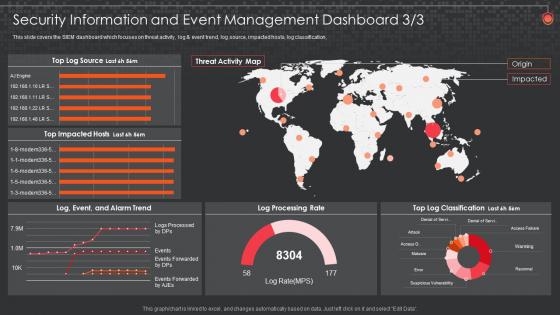 Siem For Security Analysis And Event Management Dashboard
Siem For Security Analysis And Event Management DashboardThis slide covers the SIEM dashboard which focuses on threat activity, log and event trend, log source, impacted hosts, log classification Deliver an outstanding presentation on the topic using this Siem For Security Analysis And Event Management Dashboard. Dispense information and present a thorough explanation of Information, Management, Dashboard using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
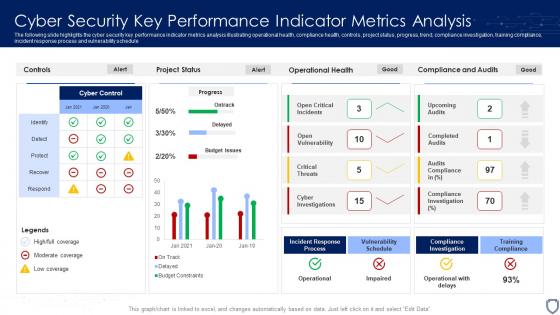 Cyber Security Key Performance Indicator Metrics Analysis
Cyber Security Key Performance Indicator Metrics AnalysisThe following slide highlights the cyber security key performance indicator metrics analysis illustrating operational health, compliance health, controls, project status, progress, trend, compliance investigation, training compliance, incident response process and vulnerability schedule. Presenting our well structured Cyber Security Key Performance Indicator Metrics Analysis. The topics discussed in this slide are Incident Response Process, Vulnerability Schedule, Training Compliance. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
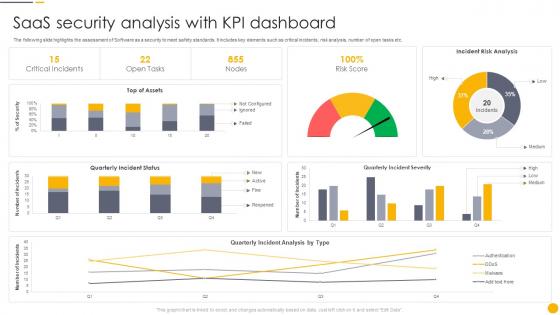 Saas Security Analysis With Kpi Dashboard
Saas Security Analysis With Kpi DashboardThe following slide highlights the assessment of Software as a security to meet safety standards. It includes key elements such as critical incidents, risk analysis, number of open tasks etc. Introducing our Saas Security Analysis With Kpi Dashboard set of slides. The topics discussed in these slides are Analysis, Dashboard, Assessment. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
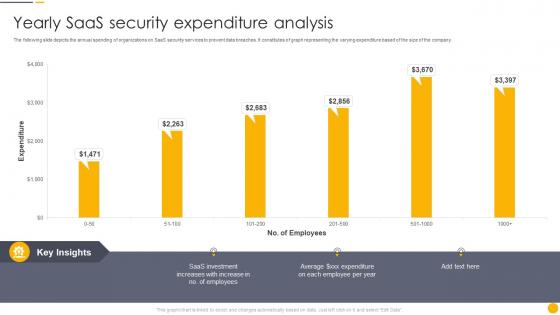 Yearly Saas Security Expenditure Analysis
Yearly Saas Security Expenditure AnalysisThe following slide depicts the annual spending of organizations on SaaS security services to prevent data breaches. It constitutes of graph representing the varying expenditure based of the size of the company. Introducing our Yearly Saas Security Expenditure Analysis set of slides. The topics discussed in these slides are Security, Expenditure, Analysis. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
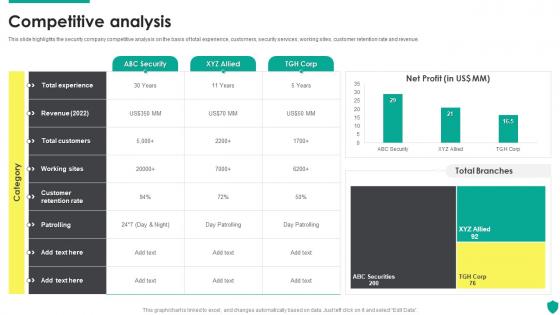 Competitive Analysis Security Guard Service Company Profile
Competitive Analysis Security Guard Service Company ProfileThis slide highlights the security company competitive analysis on the basis of total experience, customers, security services, working sites, customer retention rate and revenue. Present the topic in a bit more detail with this Competitive Analysis Security Guard Service Company Profile. Use it as a tool for discussion and navigation on Total Experience, Revenue 2022, Total Customers. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
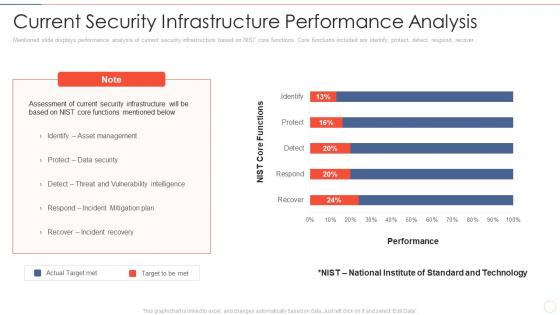 Effective information security current security infrastructure performance analysis
Effective information security current security infrastructure performance analysisMentioned slide displays performance analysis of current security infrastructure based on NIST core functions. Core functions included are identify, protect, detect, respond, recover. Deliver an outstanding presentation on the topic using this Effective Information Security Current Security Infrastructure Performance Analysis. Dispense information and present a thorough explanation of Performance, Actual Target Met, Target To Be Met, Asset Management, Data Security, Incident Recovery using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
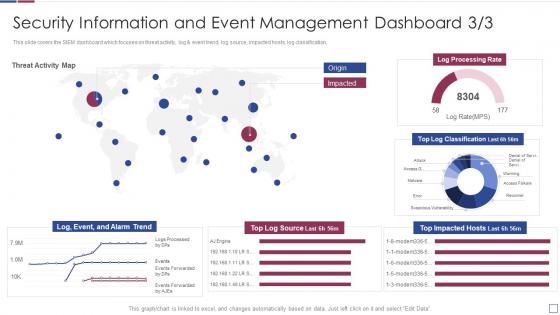 Real time analysis of security alerts event management dashboard
Real time analysis of security alerts event management dashboardThis slide covers the SIEM dashboard which focuses on threat activity, log and event trend, log source, impacted hosts, log classification, Deliver an outstanding presentation on the topic using this Real Time Analysis Of Security Alerts Event Management Dashboard. Dispense information and present a thorough explanation of Information, Management, Dashboard using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
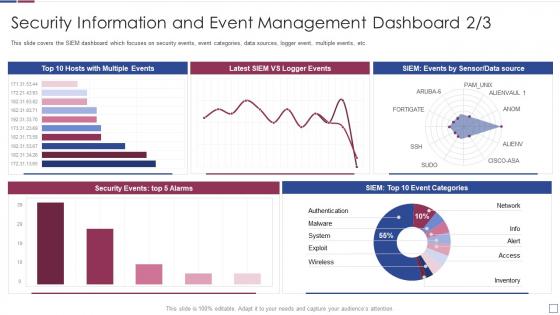 Real time analysis of security alerts information and event management dashboard
Real time analysis of security alerts information and event management dashboardThis slide covers the SIEM dashboard which focuses on security events, event categories, data sources, logger event, multiple events, etc. Deliver an outstanding presentation on the topic using this Real Time Analysis Of Security Alerts Information And Event Management Dashboard. Dispense information and present a thorough explanation of Information, Management, Dashboard using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
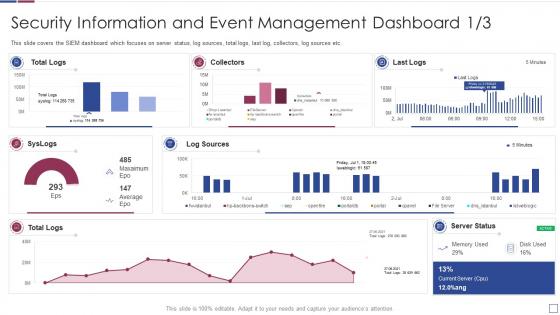 Security information and event management dashboard real time analysis of security alerts
Security information and event management dashboard real time analysis of security alertsThis slide covers the SIEM dashboard which focuses on server status, log sources, total logs, last log, collectors, log sources etc. Deliver an outstanding presentation on the topic using this Security Information And Event Management Dashboard Real Time Analysis Of Security Alerts. Dispense information and present a thorough explanation of Information, Management, Dashboard using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Dashboard For Data Security Risk Management Cybersecurity Risk Analysis And Management Plan
Dashboard For Data Security Risk Management Cybersecurity Risk Analysis And Management PlanThis slide showcases dashboard that can help organization in managing the data security risks. Its key elements are enterprise risk, risk by objectives, data protection finding and overdue actions by status Present the topic in a bit more detail with this Dashboard For Data Security Risk Management Cybersecurity Risk Analysis And Management Plan. Use it as a tool for discussion and navigation on Dashboard, Security, Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
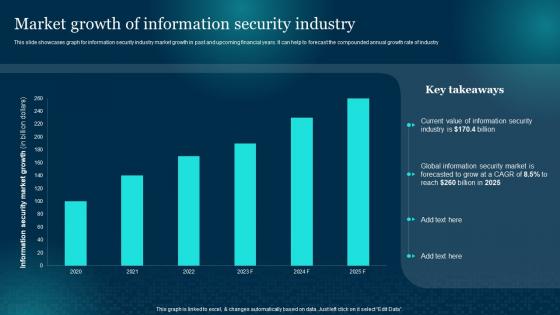 Market Growth Of Information Security Industry Cybersecurity Risk Analysis And Management Plan
Market Growth Of Information Security Industry Cybersecurity Risk Analysis And Management PlanThis slide showcases graph for information security industry market growth in past and upcoming financial years. It can help to forecast the compounded annual growth rate of industry Deliver an outstanding presentation on the topic using this Market Growth Of Information Security Industry Cybersecurity Risk Analysis And Management Plan. Dispense information and present a thorough explanation of Growth, Information, Security Industry using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Rising Number Of Information Security Attacks Cybersecurity Risk Analysis And Management Plan
Rising Number Of Information Security Attacks Cybersecurity Risk Analysis And Management PlanThis slide showcases number of cybersecurity attacks faced by organizations in past financial years. It includes malware, DoS attack, phishing and SQL injection Present the topic in a bit more detail with this Rising Number Of Information Security Attacks Cybersecurity Risk Analysis And Management Plan. Use it as a tool for discussion and navigation on Information, Security Attacks, Organizations. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
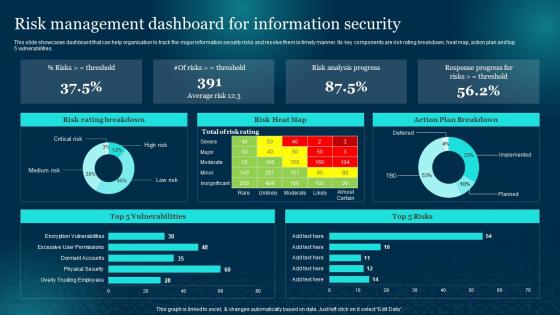 Risk Management Dashboard For Information Security Cybersecurity Risk Analysis And Management Plan
Risk Management Dashboard For Information Security Cybersecurity Risk Analysis And Management PlanThis slide showcases dashboard that can help organization to track the major information security risks and resolve them in timely manner. Its key components are risk rating breakdown, heat map, action plan and top 5 vulnerabilities. Deliver an outstanding presentation on the topic using this Risk Management Dashboard For Information Security Cybersecurity Risk Analysis And Management Plan. Dispense information and present a thorough explanation of Management, Dashboard, Information using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
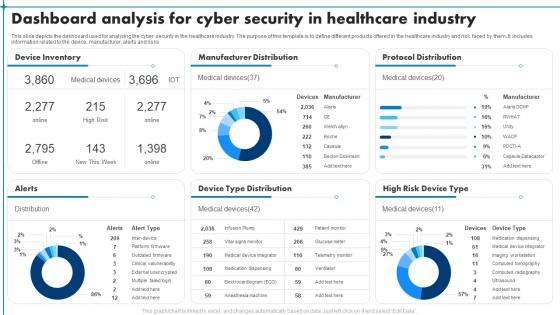 Dashboard Analysis For Cyber Security In Healthcare Industry
Dashboard Analysis For Cyber Security In Healthcare IndustryThis slide depicts the dashboard used for analyzing the cyber security in the healthcare industry. The purpose of this template is to define different products offered in the healthcare industry and risk faced by them. It includes information related to the device, manufacturer, alerts and risks. Introducing our Dashboard Analysis For Cyber Security In Healthcare Industry set of slides. The topics discussed in these slides are Device Inventory, Manufacturer Distribution, Protocol Distribution. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
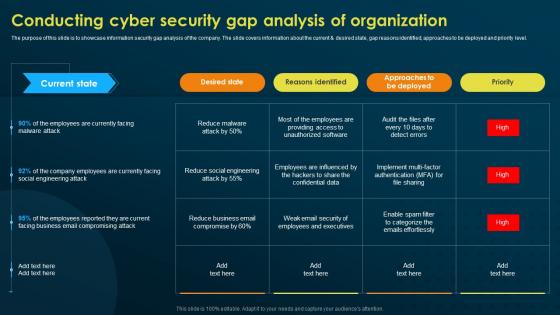 Conducting Cyber Security Gap Analysis Of Organization Implementing Security Awareness Training
Conducting Cyber Security Gap Analysis Of Organization Implementing Security Awareness TrainingThe purpose of this slide is to showcase information security gap analysis of the company. The slide covers information about the current and desired state, gap reasons identified, approaches to be deployed and priority level. Present the topic in a bit more detail with this Conducting Cyber Security Gap Analysis Of Organization Implementing Security Awareness Training. Use it as a tool for discussion and navigation on Desired State, Reasons Identified, Approaches To Be Deployed. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
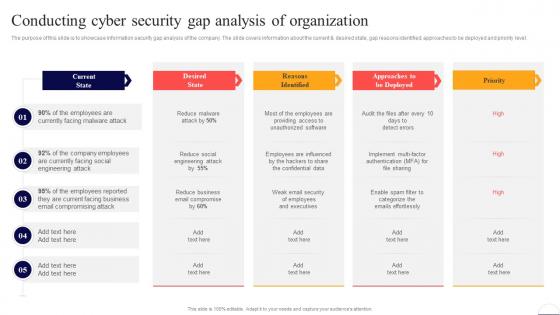 Conducting Cyber Security Gap Analysis Of Organization Preventing Data Breaches Through Cyber Security
Conducting Cyber Security Gap Analysis Of Organization Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to showcase information security gap analysis of the company. The slide covers information about the current and desired state, gap reasons identified, approaches to be deployed and priority level. Deliver an outstanding presentation on the topic using this Conducting Cyber Security Gap Analysis Of Organization Preventing Data Breaches Through Cyber Security. Dispense information and present a thorough explanation of Current State, Email, Business using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
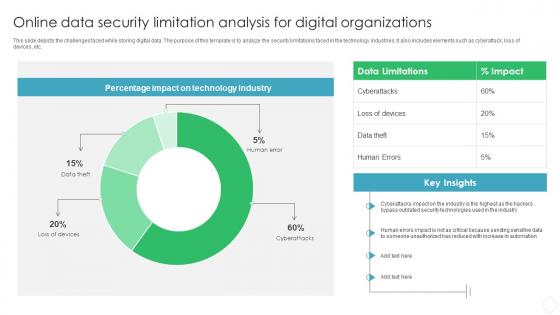 Online Data Security Limitation Analysis For Digital Organizations
Online Data Security Limitation Analysis For Digital OrganizationsThis slide depicts the challenges faced while storing digital data. The purpose of this template is to analyze the security limitations faced in the technology industries. It also includes elements such as cyberattack, loss of devices, etc. Introducing our Online Data Security Limitation Analysis For Digital Organizations set of slides. The topics discussed in these slides are Data Limitations, Impact, Technology Industry. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.